Introduction to Communication Networks 67594 Dr Michael Schapira
- Slides: 86
Introduction to Communication Networks – 67594 Dr. Michael Schapira Rothberg A 411
Chapter 4 Network Layer A note on the use of these ppt slides: We’re making these slides freely available to all (faculty, students, readers). They’re in Power. Point form so you can add, modify, and delete slides (including this one) and slide content to suit your needs. They obviously represent a lot of work on our part. In return for use, we only ask the following: q If you use these slides (e. g. , in a class) in substantially unaltered form, that you mention their source (after all, we’d like people to use our book!) q If you post any slides in substantially unaltered form on a www site, that you note that they are adapted from (or perhaps identical to) our slides, and note our copyright of this material. Computer Networking: A Top Down Approach 5 th edition. Jim Kurose, Keith Ross Addison-Wesley, April 2009. Thanks and enjoy! JFK/KWR All material copyright 1996 -2009 J. F Kurose and K. W. Ross, All Rights Reserved Netw 4 -2 ork
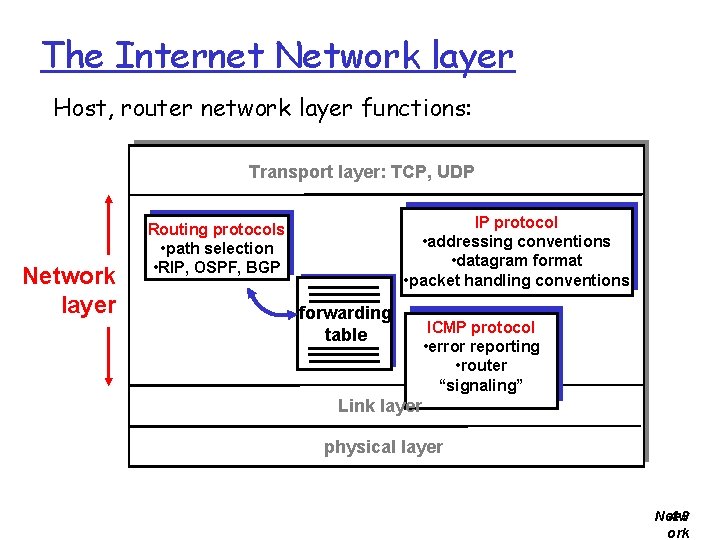
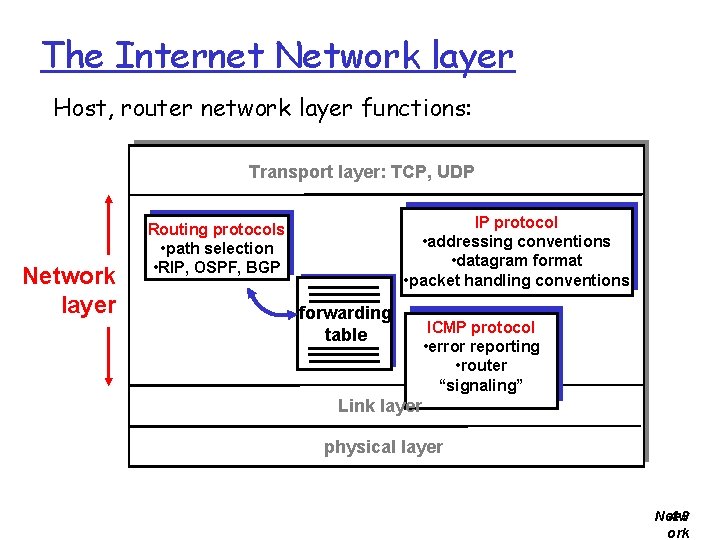
The Internet Network layer Host, router network layer functions: Transport layer: TCP, UDP Network layer IP protocol • addressing conventions • datagram format • packet handling conventions Routing protocols • path selection • RIP, OSPF, BGP forwarding table ICMP protocol • error reporting • router “signaling” Link layer physical layer Netw 4 -3 ork
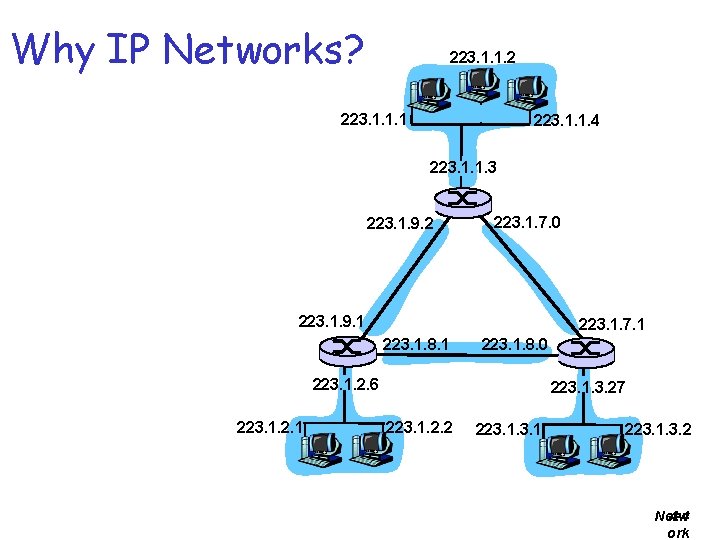
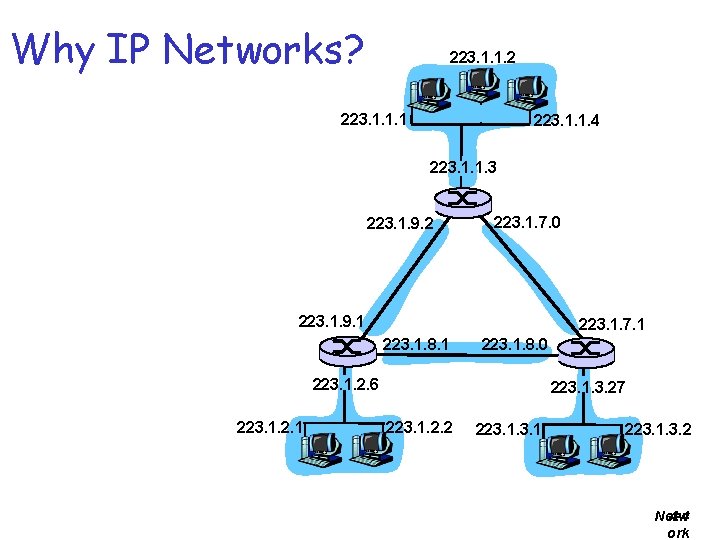
Why IP Networks? 223. 1. 1. 2 223. 1. 1. 1 223. 1. 1. 4 223. 1. 1. 3 223. 1. 9. 2 223. 1. 7. 0 223. 1. 9. 1 223. 1. 7. 1 223. 1. 8. 0 223. 1. 2. 6 223. 1. 2. 1 223. 1. 3. 27 223. 1. 2. 2 223. 1. 3. 2 Netw 4 -4 ork
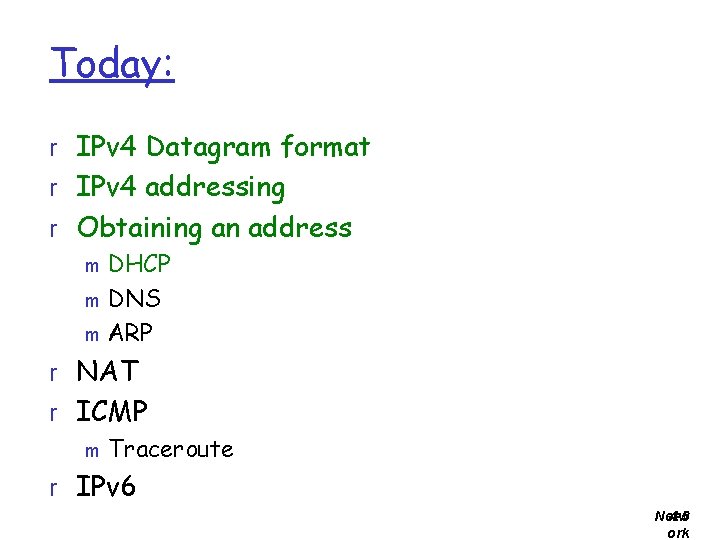
Today: r IPv 4 Datagram format r IPv 4 addressing r Obtaining an address m DHCP m DNS m ARP r NAT r ICMP m Traceroute r IPv 6 Netw 4 -5 ork
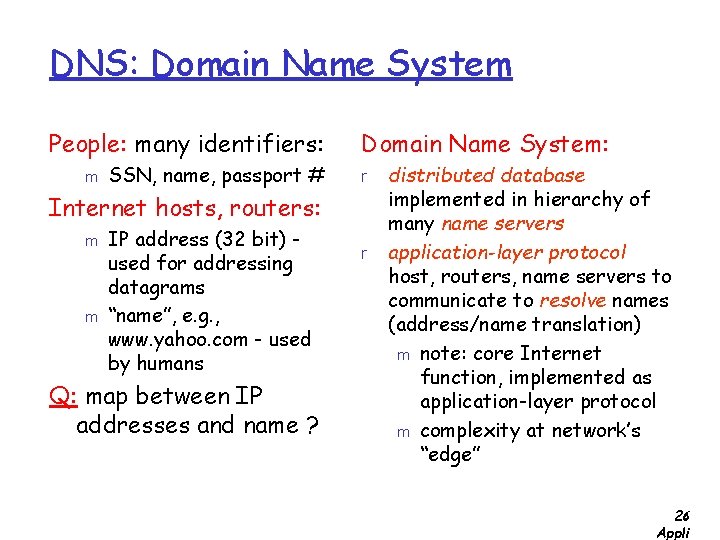
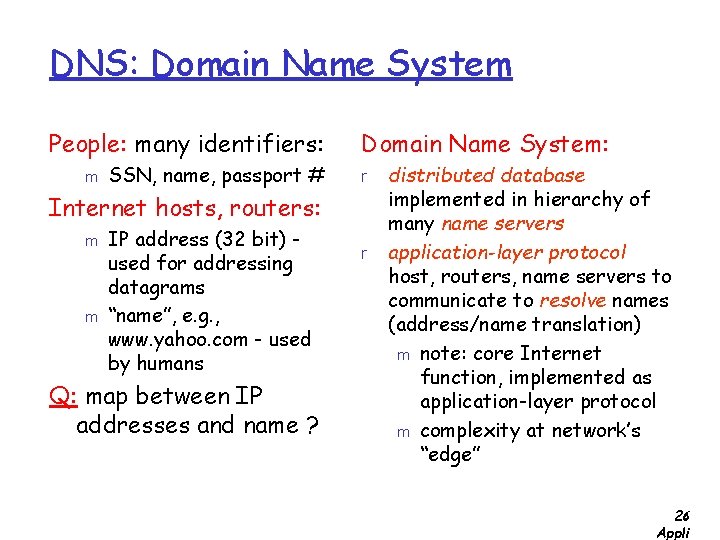
DNS: Domain Name System People: many identifiers: m SSN, name, passport # Domain Name System: r Internet hosts, routers: m m IP address (32 bit) used for addressing datagrams “name”, e. g. , www. yahoo. com - used by humans Q: map between IP addresses and name ? r distributed database implemented in hierarchy of many name servers application-layer protocol host, routers, name servers to communicate to resolve names (address/name translation) m note: core Internet function, implemented as application-layer protocol m complexity at network’s “edge” 2: 6 Appli
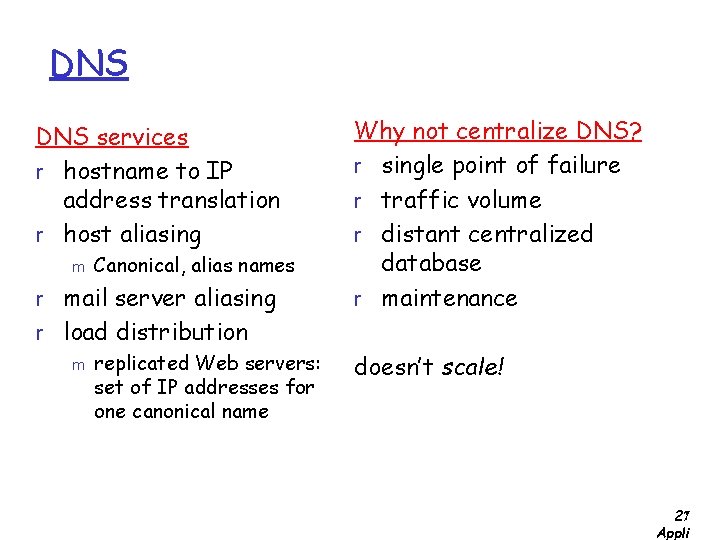
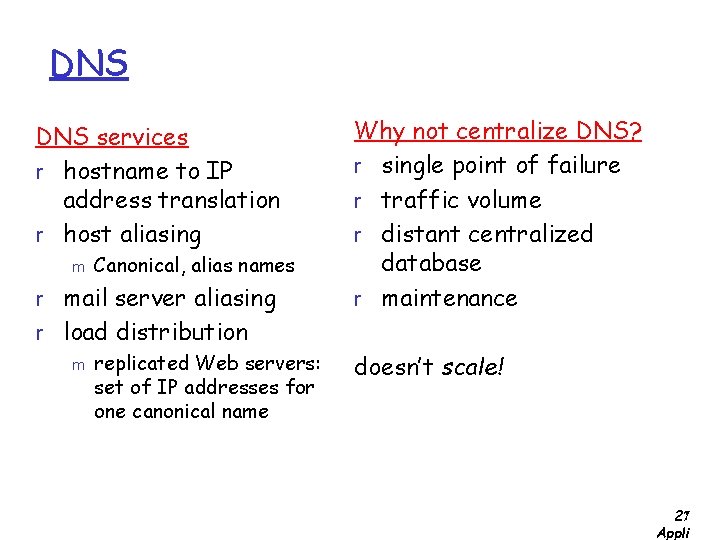
DNS services r hostname to IP address translation r host aliasing m Canonical, alias names r mail server aliasing r load distribution m replicated Web servers: set of IP addresses for one canonical name Why not centralize DNS? r single point of failure r traffic volume r distant centralized database r maintenance doesn’t scale! 2: 7 Appli
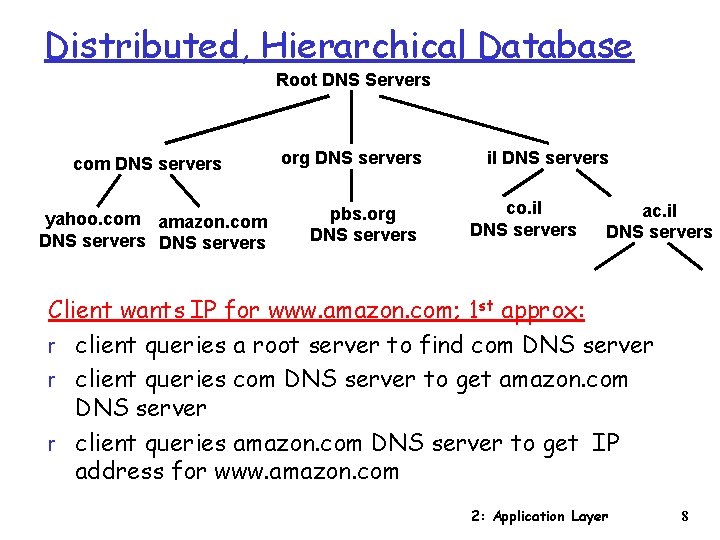
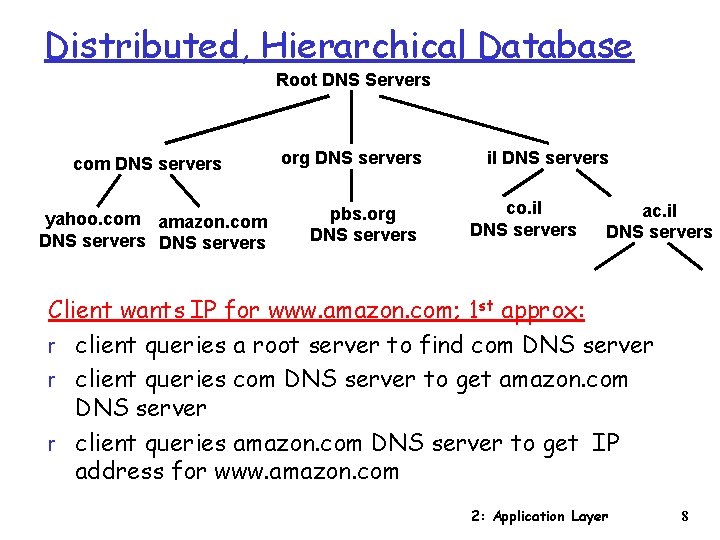
Distributed, Hierarchical Database Root DNS Servers com DNS servers yahoo. com amazon. com DNS servers org DNS servers pbs. org DNS servers il DNS servers co. il DNS servers ac. il DNS servers Client wants IP for www. amazon. com; 1 st approx: r client queries a root server to find com DNS server r client queries com DNS server to get amazon. com DNS server r client queries amazon. com DNS server to get IP address for www. amazon. com 2: Application Layer 8
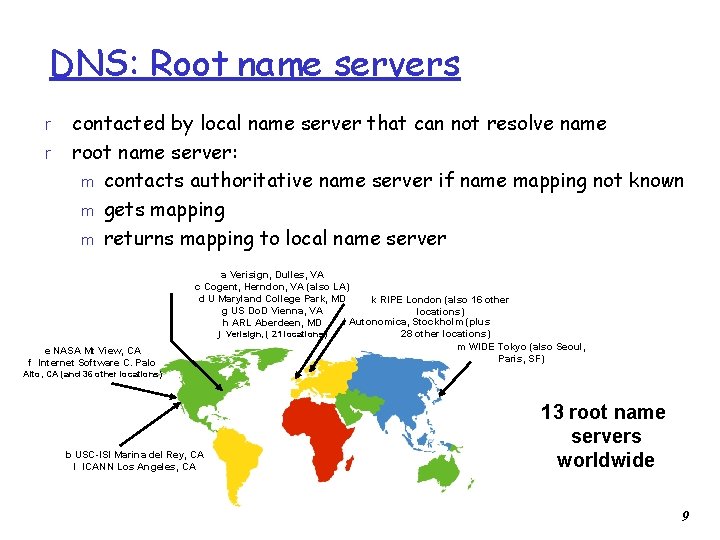
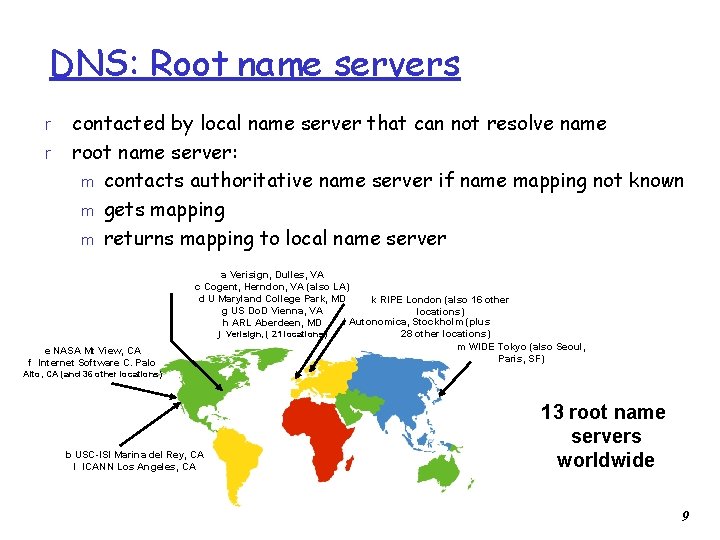
DNS: Root name servers r r contacted by local name server that can not resolve name root name server: m contacts authoritative name server if name mapping not known m gets mapping m returns mapping to local name server e NASA Mt View, CA f Internet Software C. Palo a Verisign, Dulles, VA c Cogent, Herndon, VA (also LA) d U Maryland College Park, MD k RIPE London (also 16 other g US Do. D Vienna, VA locations) i Autonomica, Stockholm (plus h ARL Aberdeen, MD j Verisign, ( 21 locations) 28 other locations) m WIDE Tokyo (also Seoul, Paris, SF) Alto, CA (and 36 other locations) b USC-ISI Marina del Rey, CA l ICANN Los Angeles, CA 13 root name servers worldwide 9
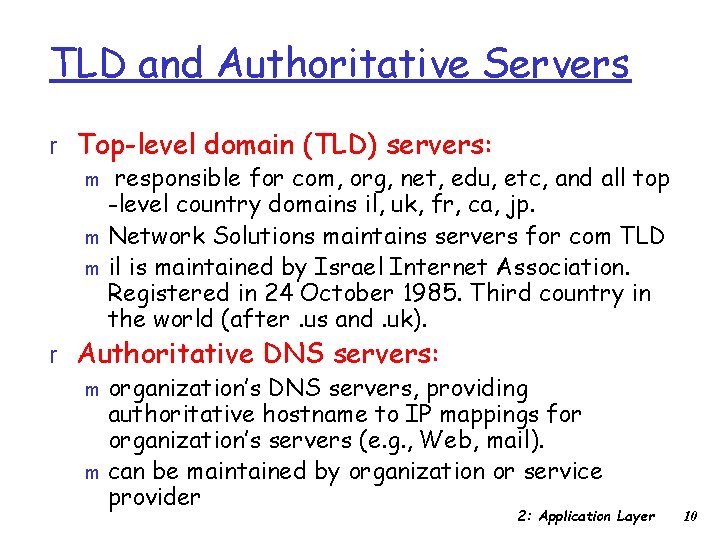
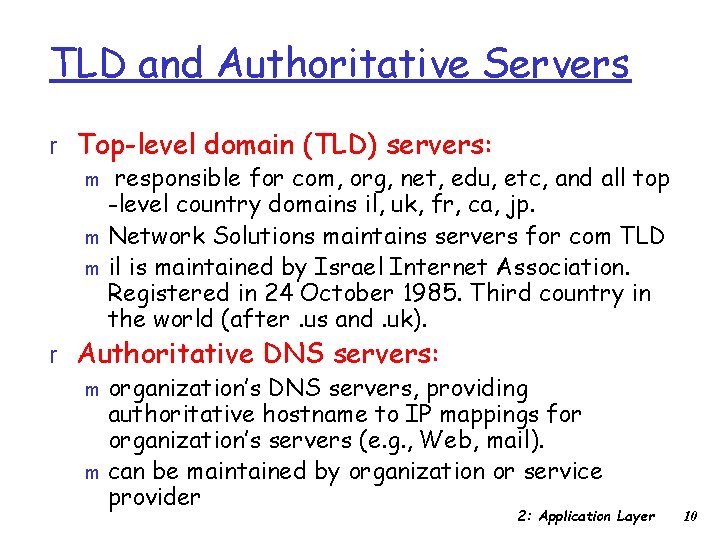
TLD and Authoritative Servers r Top-level domain (TLD) servers: m responsible for com, org, net, edu, etc, and all top -level country domains il, uk, fr, ca, jp. m Network Solutions maintains servers for com TLD m il is maintained by Israel Internet Association. Registered in 24 October 1985. Third country in the world (after. us and. uk). r Authoritative DNS servers: m organization’s DNS servers, providing authoritative hostname to IP mappings for organization’s servers (e. g. , Web, mail). m can be maintained by organization or service provider 2: Application Layer 10
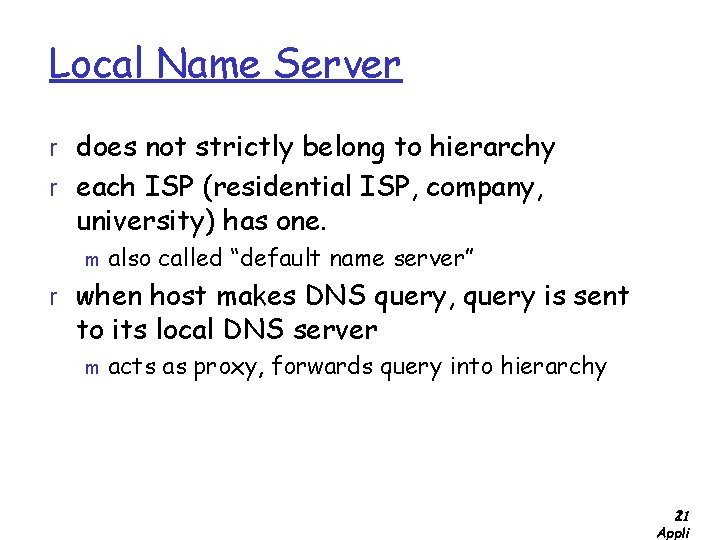
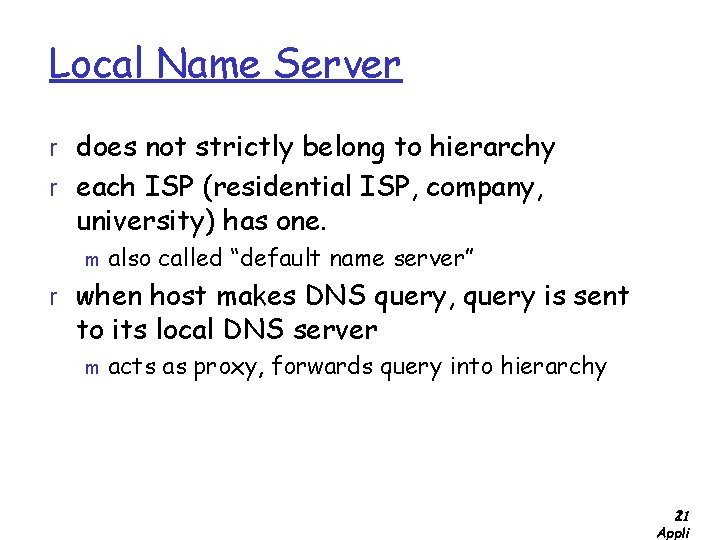
Local Name Server r does not strictly belong to hierarchy r each ISP (residential ISP, company, university) has one. m also called “default name server” r when host makes DNS query, query is sent to its local DNS server m acts as proxy, forwards query into hierarchy 2: 11 Appli
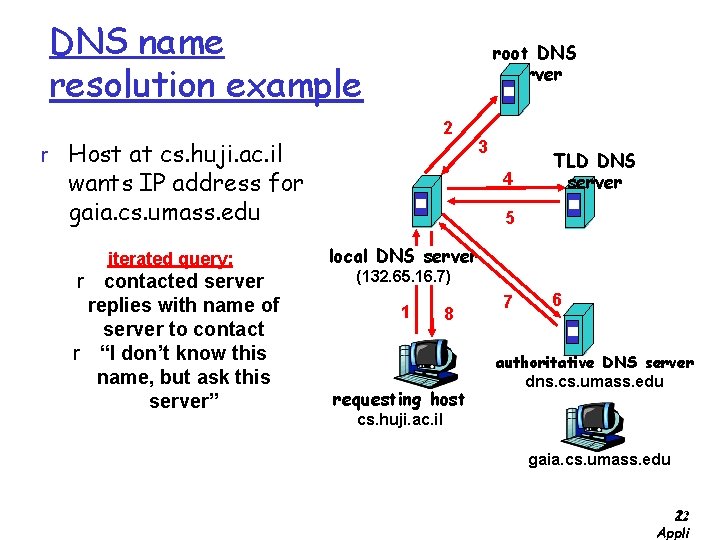
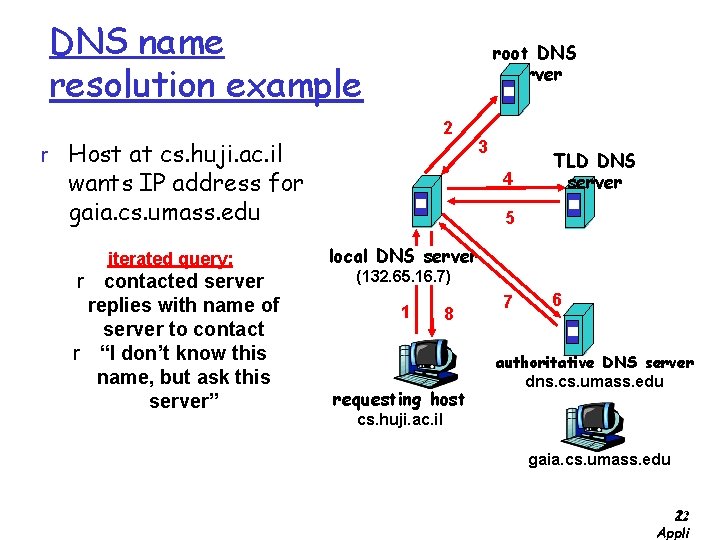
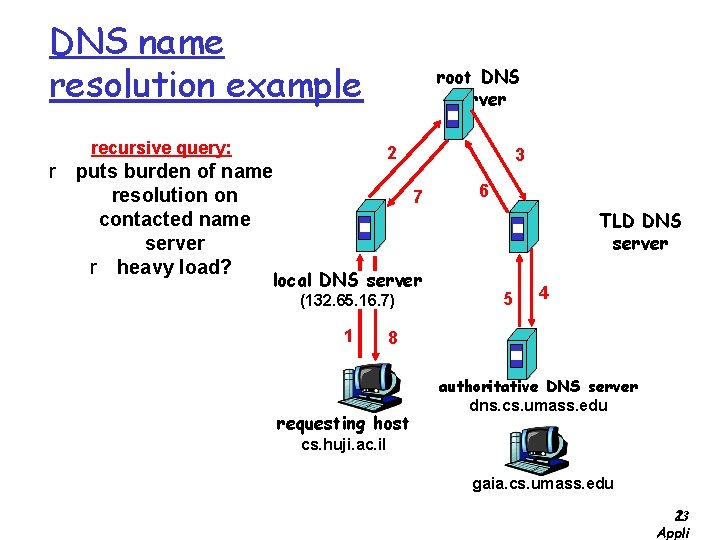
DNS name resolution example root DNS server 2 r Host at cs. huji. ac. il 3 wants IP address for gaia. cs. umass. edu iterated query: r contacted server replies with name of server to contact r “I don’t know this name, but ask this server” 4 TLD DNS server 5 local DNS server (132. 65. 16. 7) 1 8 requesting host 7 6 authoritative DNS server dns. cs. umass. edu cs. huji. ac. il gaia. cs. umass. edu 2: 12 Appli
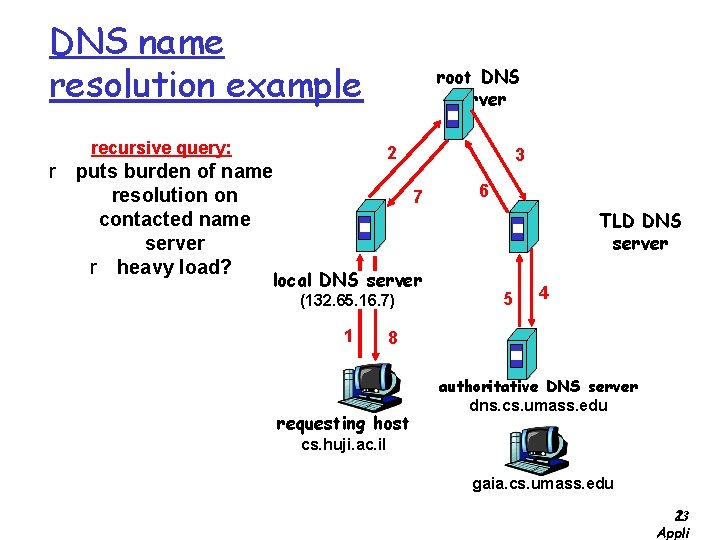
DNS name resolution example recursive query: root DNS server 2 r puts burden of name resolution on contacted name server r heavy load? 3 7 local DNS server (132. 65. 16. 7) 1 6 TLD DNS server 5 4 8 requesting host authoritative DNS server dns. cs. umass. edu cs. huji. ac. il gaia. cs. umass. edu 2: 13 Appli
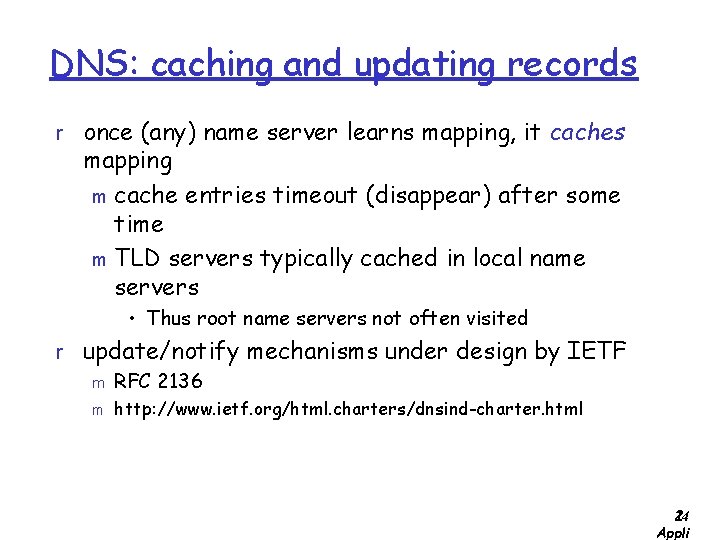
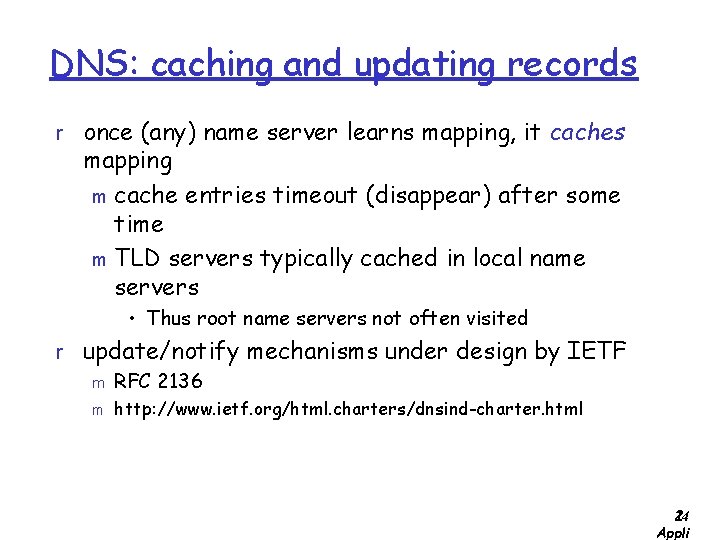
DNS: caching and updating records r once (any) name server learns mapping, it caches mapping m cache entries timeout (disappear) after some time m TLD servers typically cached in local name servers • Thus root name servers not often visited r update/notify mechanisms under design by IETF m RFC 2136 m http: //www. ietf. org/html. charters/dnsind-charter. html 2: 14 Appli
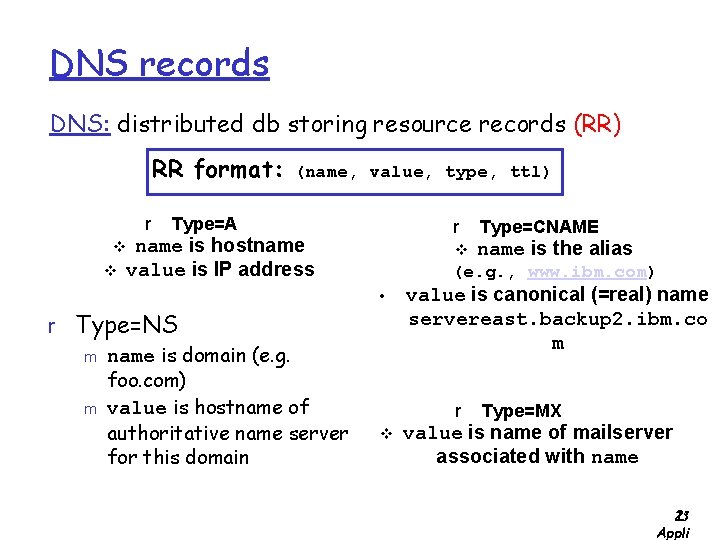
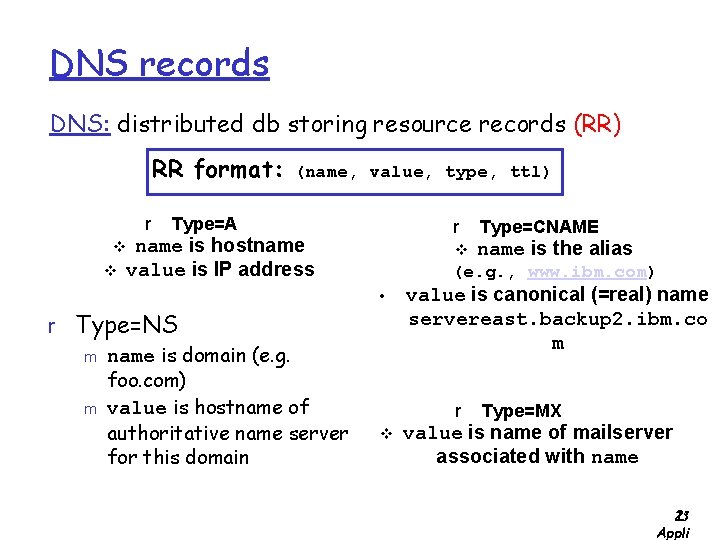
DNS records DNS: distributed db storing resource records (RR) RR format: r (name, value, type, ttl) Type=A r name is hostname value is IP address v v v name is the alias (e. g. , www. ibm. com) • r Type=NS m name is domain (e. g. foo. com) m value is hostname of authoritative name server for this domain Type=CNAME value is canonical (=real) name servereast. backup 2. ibm. co m r v Type=MX value is name of mailserver associated with name 2: 15 Appli
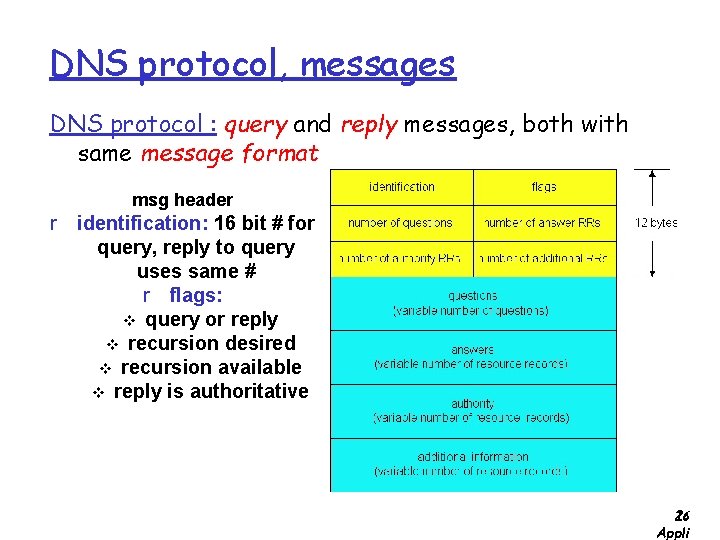
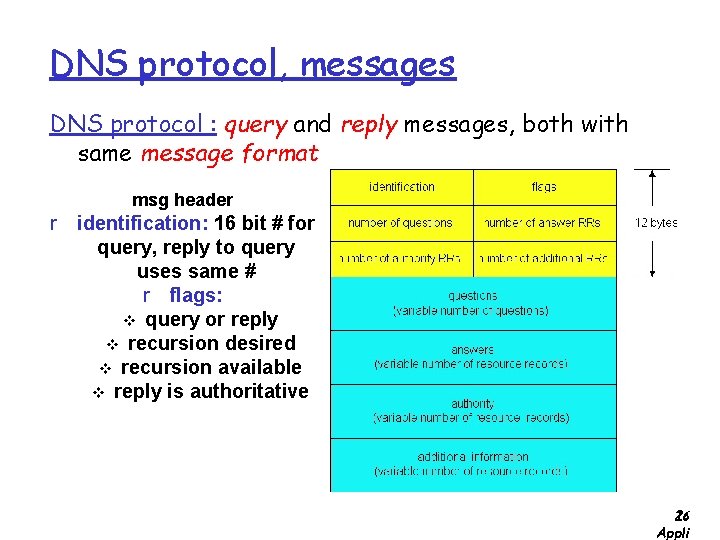
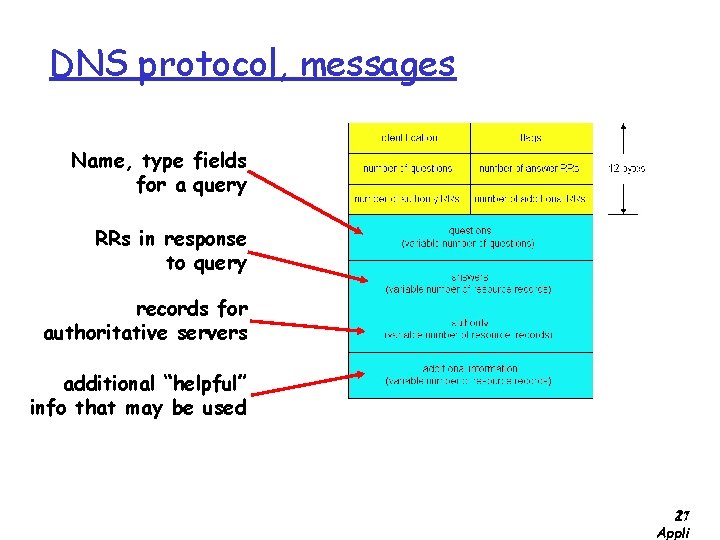
DNS protocol, messages DNS protocol : query and reply messages, both with same message format msg header r identification: 16 bit # for query, reply to query uses same # r flags: v query or reply v recursion desired v recursion available v reply is authoritative 2: 16 Appli
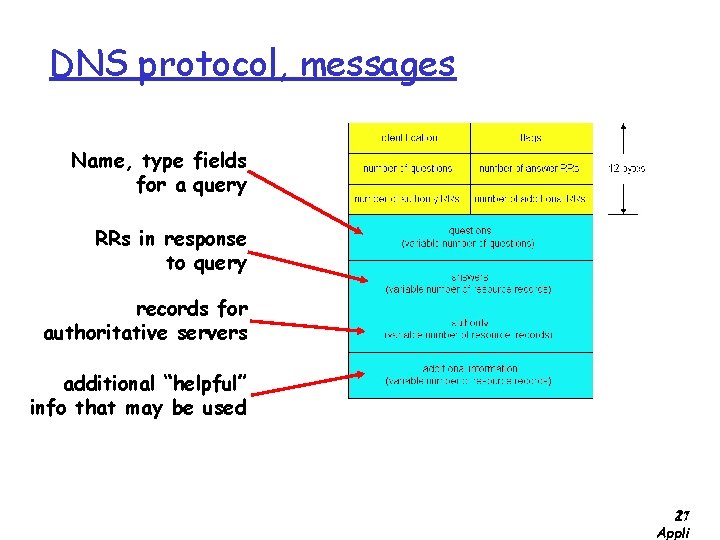
DNS protocol, messages Name, type fields for a query RRs in response to query records for authoritative servers additional “helpful” info that may be used 2: 17 Appli
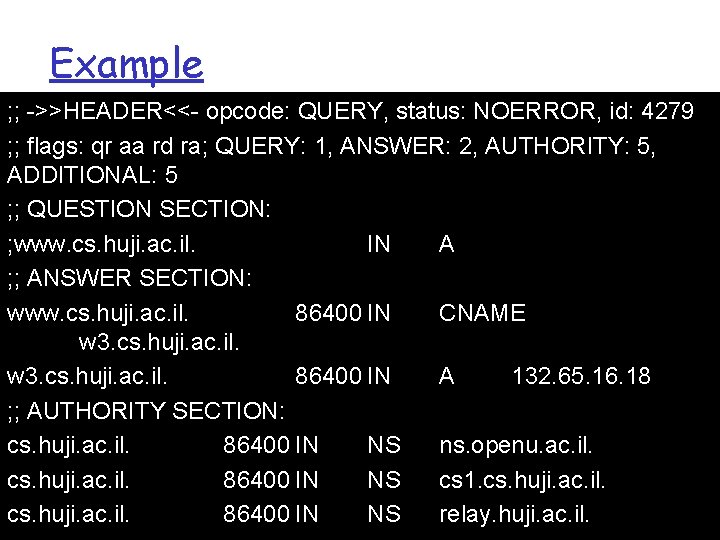
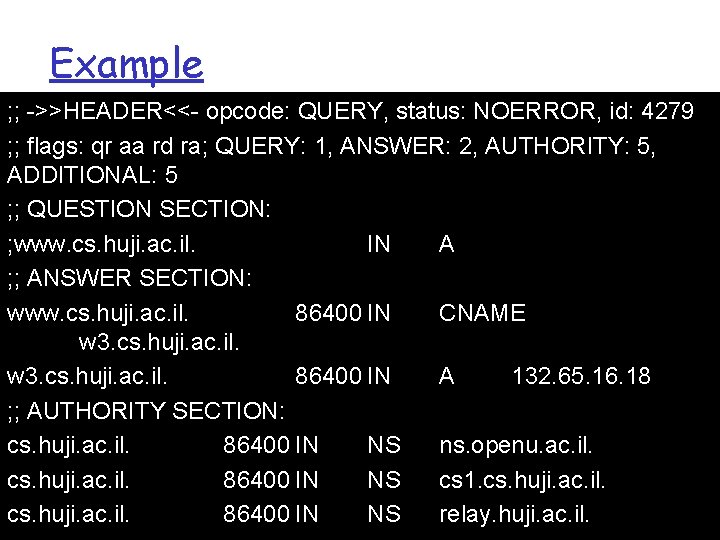
Example ; ; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 4279 ; ; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 5, ADDITIONAL: 5 ; ; QUESTION SECTION: ; www. cs. huji. ac. il. IN A ; ; ANSWER SECTION: www. cs. huji. ac. il. 86400 IN CNAME w 3. cs. huji. ac. il. 86400 IN A 132. 65. 16. 18 ; ; AUTHORITY SECTION: cs. huji. ac. il. 86400 IN NS ns. openu. ac. il. cs. huji. ac. il. 86400 IN NS cs 1. cs. huji. ac. il. 5 -18 cs. huji. ac. il. 86400 IN NS relay. huji. ac. il.
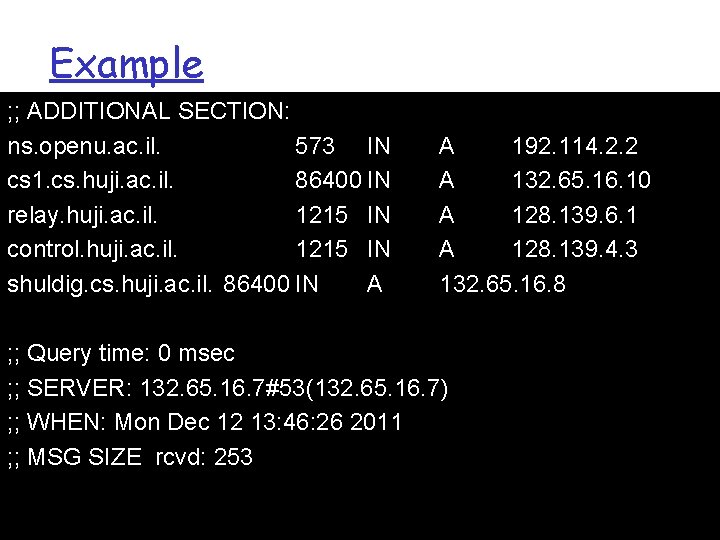
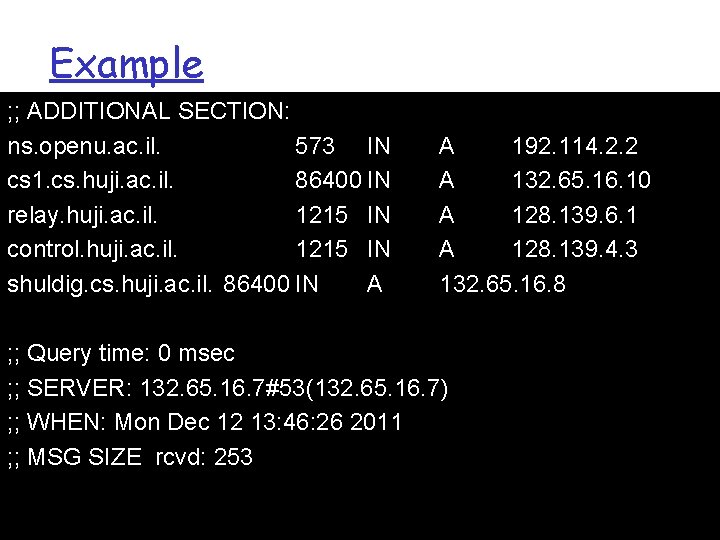
Example ; ; ADDITIONAL SECTION: ns. openu. ac. il. 573 IN cs 1. cs. huji. ac. il. 86400 IN relay. huji. ac. il. 1215 IN control. huji. ac. il. 1215 IN shuldig. cs. huji. ac. il. 86400 IN A A 192. 114. 2. 2 A 132. 65. 16. 10 A 128. 139. 6. 1 A 128. 139. 4. 3 132. 65. 16. 8 ; ; Query time: 0 msec ; ; SERVER: 132. 65. 16. 7#53(132. 65. 16. 7) ; ; WHEN: Mon Dec 12 13: 46: 26 2011 ; ; MSG SIZE rcvd: 253 5 -19
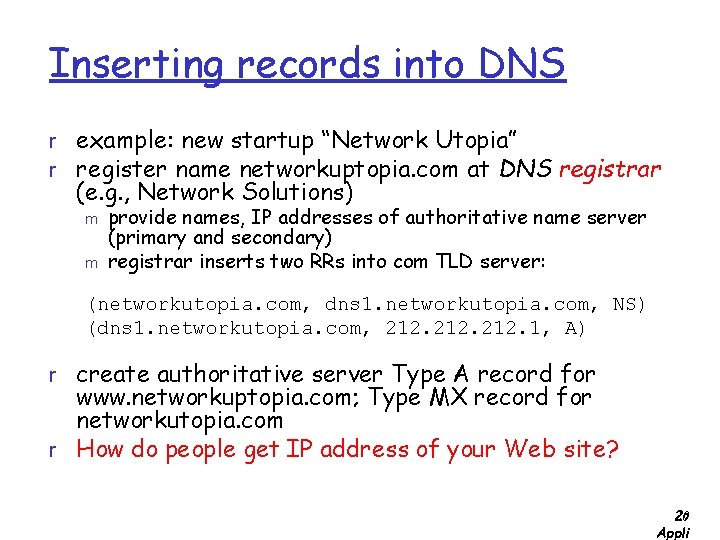
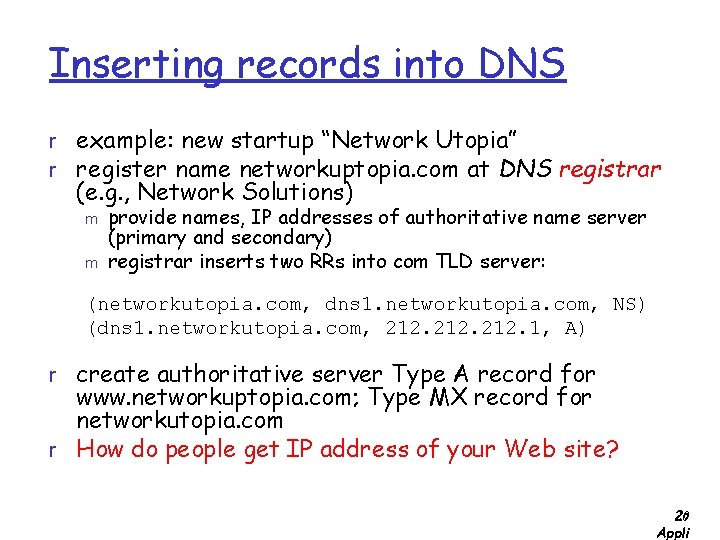
Inserting records into DNS r example: new startup “Network Utopia” r register name networkuptopia. com at DNS registrar (e. g. , Network Solutions) m m provide names, IP addresses of authoritative name server (primary and secondary) registrar inserts two RRs into com TLD server: (networkutopia. com, dns 1. networkutopia. com, NS) (dns 1. networkutopia. com, 212. 1, A) r create authoritative server Type A record for www. networkuptopia. com; Type MX record for networkutopia. com r How do people get IP address of your Web site? 2: 20 Appli
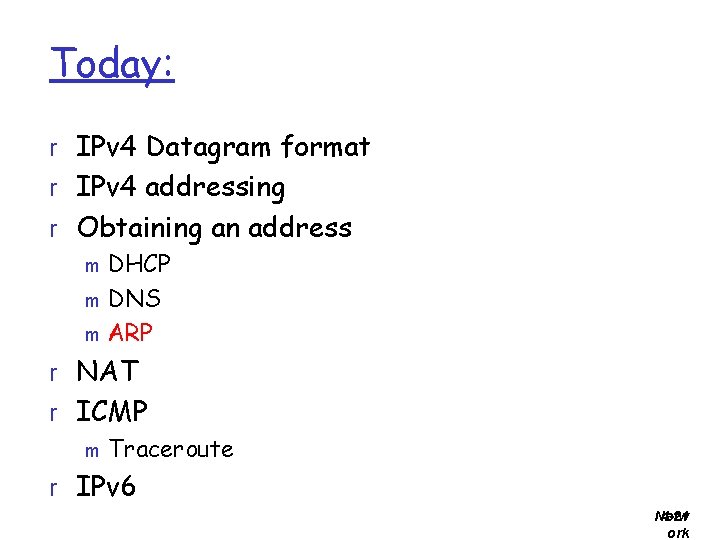
Today: r IPv 4 Datagram format r IPv 4 addressing r Obtaining an address m DHCP m DNS m ARP r NAT r ICMP m Traceroute r IPv 6 Netw 4 -21 ork
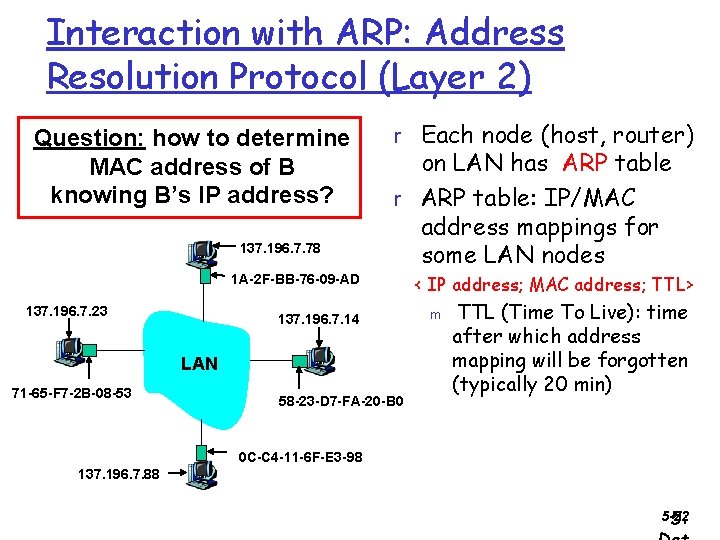
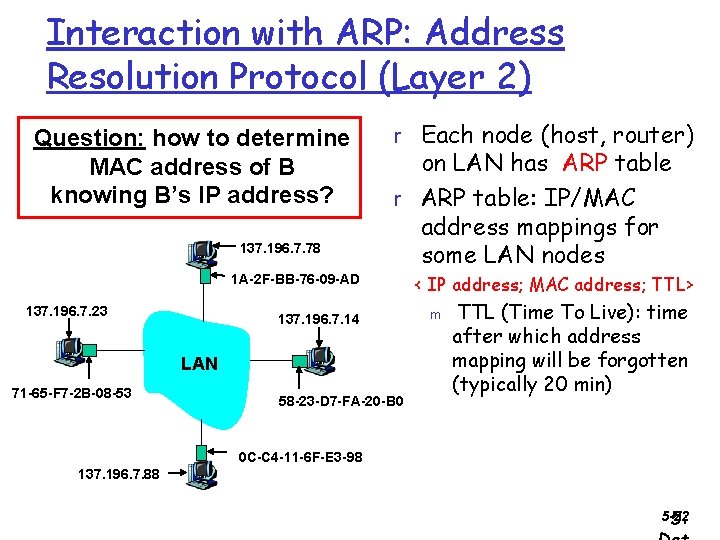
Interaction with ARP: Address Resolution Protocol (Layer 2) Question: how to determine MAC address of B knowing B’s IP address? 137. 196. 7. 78 r Each node (host, router) on LAN has ARP table r ARP table: IP/MAC address mappings for some LAN nodes 1 A-2 F-BB-76 -09 -AD 137. 196. 7. 23 137. 196. 7. 14 LAN 71 -65 -F 7 -2 B-08 -53 58 -23 -D 7 -FA-20 -B 0 < IP address; MAC address; TTL> m TTL (Time To Live): time after which address mapping will be forgotten (typically 20 min) 0 C-C 4 -11 -6 F-E 3 -98 137. 196. 7. 88 5 -22 5:
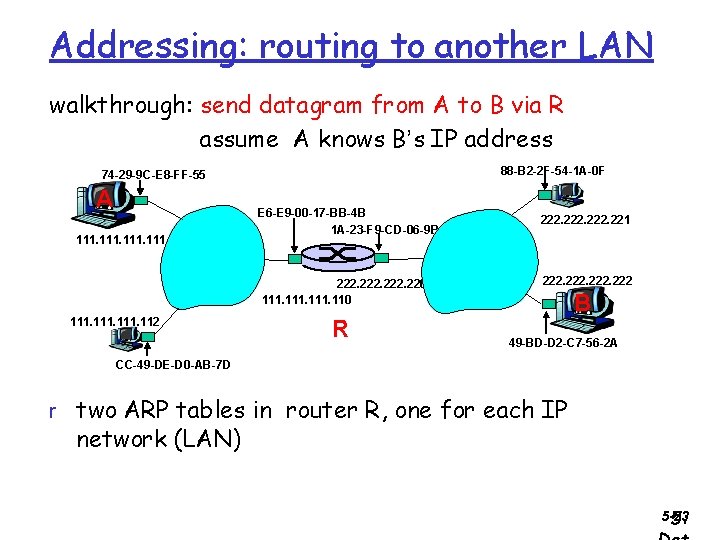
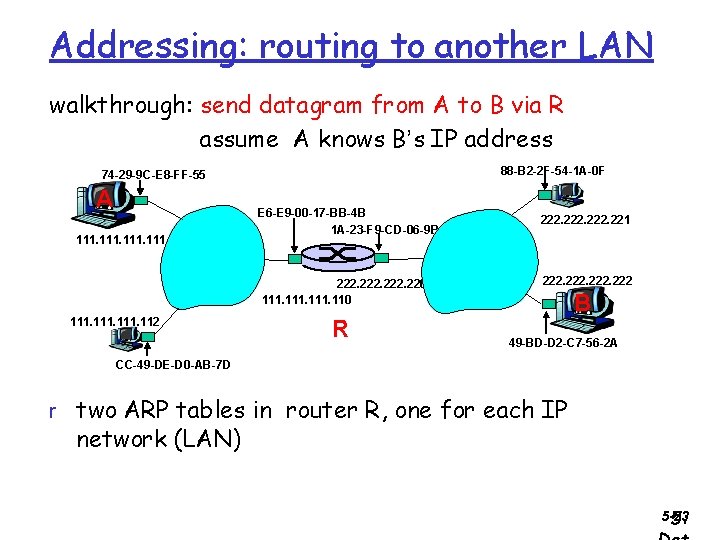
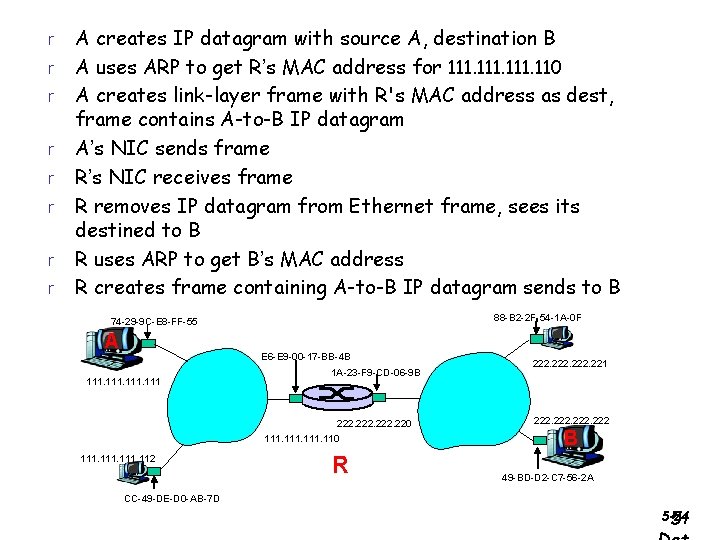
Addressing: routing to another LAN walkthrough: send datagram from A to B via R assume A knows B’s IP address 88 -B 2 -2 F-54 -1 A-0 F 74 -29 -9 C-E 8 -FF-55 A 111 E 6 -E 9 -00 -17 -BB-4 B 1 A-23 -F 9 -CD-06 -9 B 222. 220 111. 112 R 222. 221 222 B 49 -BD-D 2 -C 7 -56 -2 A CC-49 -DE-D 0 -AB-7 D r two ARP tables in router R, one for each IP network (LAN) 5 -23 5:
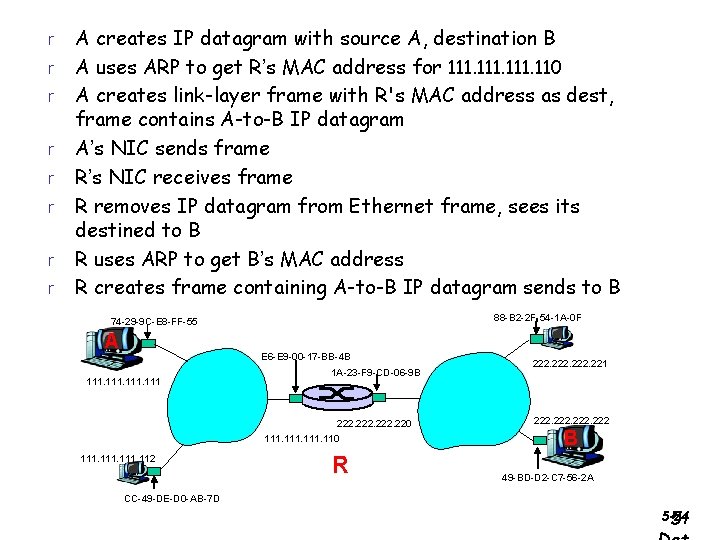
r r r r A creates IP datagram with source A, destination B A uses ARP to get R’s MAC address for 111. 110 A creates link-layer frame with R's MAC address as dest, frame contains A-to-B IP datagram A’s NIC sends frame R’s NIC receives frame R removes IP datagram from Ethernet frame, sees its destined to B R uses ARP to get B’s MAC address R creates frame containing A-to-B IP datagram sends to B 88 -B 2 -2 F-54 -1 A-0 F 74 -29 -9 C-E 8 -FF-55 A E 6 -E 9 -00 -17 -BB-4 B 111 1 A-23 -F 9 -CD-06 -9 B 222. 220 111. 112 R 222. 221 222 B 49 -BD-D 2 -C 7 -56 -2 A CC-49 -DE-D 0 -AB-7 D 5 -24 5:
Today: r IPv 4 Datagram format r IPv 4 addressing r Obtaining an address m DHCP m DNS m ARP r NAT r ICMP m Traceroute r IPv 6 Netw 4 -25 ork
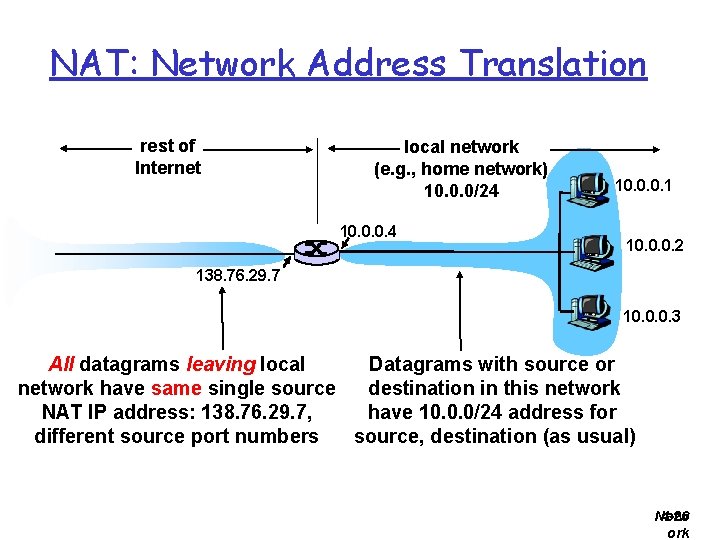
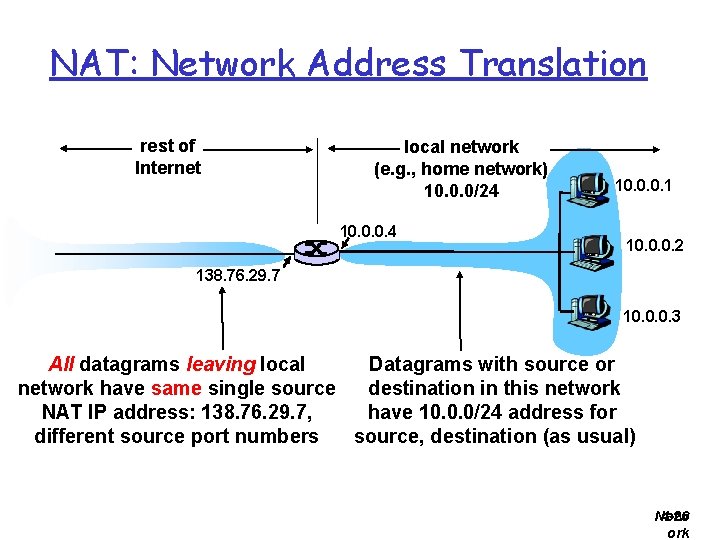
NAT: Network Address Translation rest of Internet local network (e. g. , home network) 10. 0. 0/24 10. 0. 0. 1 10. 0. 0. 2 138. 76. 29. 7 10. 0. 0. 3 Datagrams with source or All datagrams leaving local destination in this network have same single source have 10. 0. 0/24 address for NAT IP address: 138. 76. 29. 7, source, destination (as usual) different source port numbers Netw 4 -26 ork
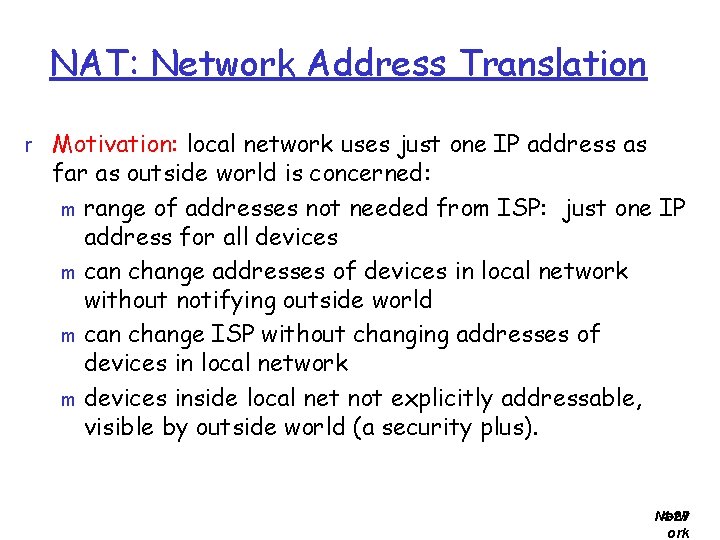
NAT: Network Address Translation r Motivation: local network uses just one IP address as far as outside world is concerned: m range of addresses not needed from ISP: just one IP address for all devices m can change addresses of devices in local network without notifying outside world m can change ISP without changing addresses of devices in local network m devices inside local net not explicitly addressable, visible by outside world (a security plus). Netw 4 -27 ork
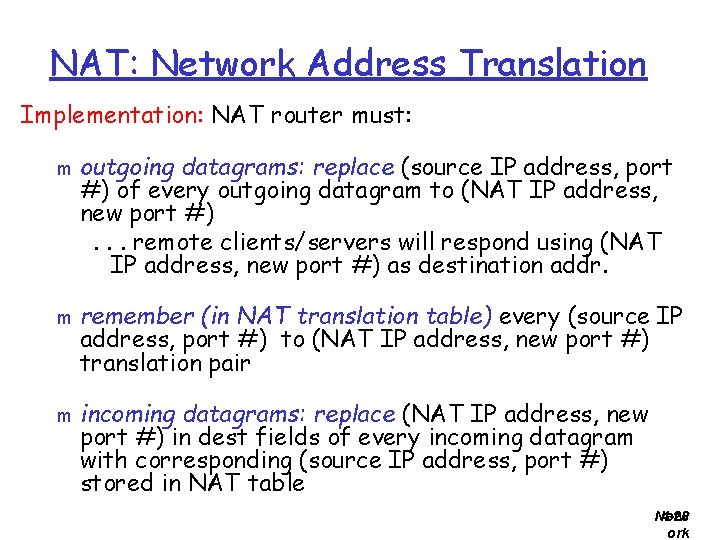
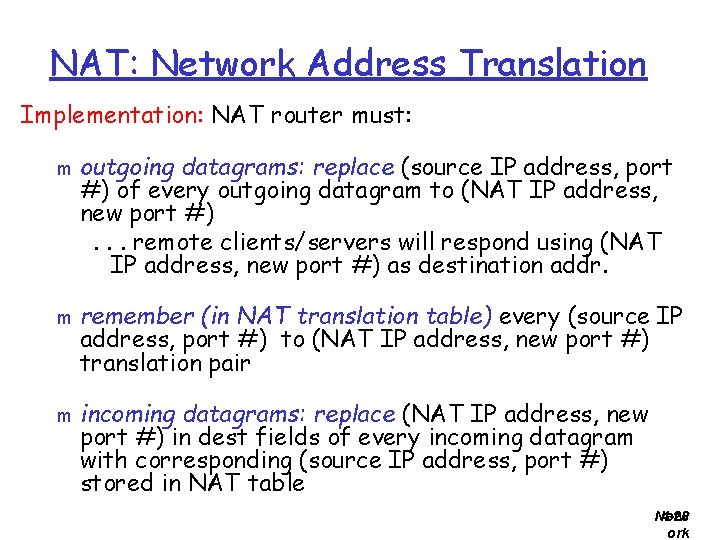
NAT: Network Address Translation Implementation: NAT router must: m m m outgoing datagrams: replace (source IP address, port #) of every outgoing datagram to (NAT IP address, new port #). . . remote clients/servers will respond using (NAT IP address, new port #) as destination addr. remember (in NAT translation table) every (source IP address, port #) to (NAT IP address, new port #) translation pair incoming datagrams: replace (NAT IP address, new port #) in dest fields of every incoming datagram with corresponding (source IP address, port #) stored in NAT table Netw 4 -28 ork
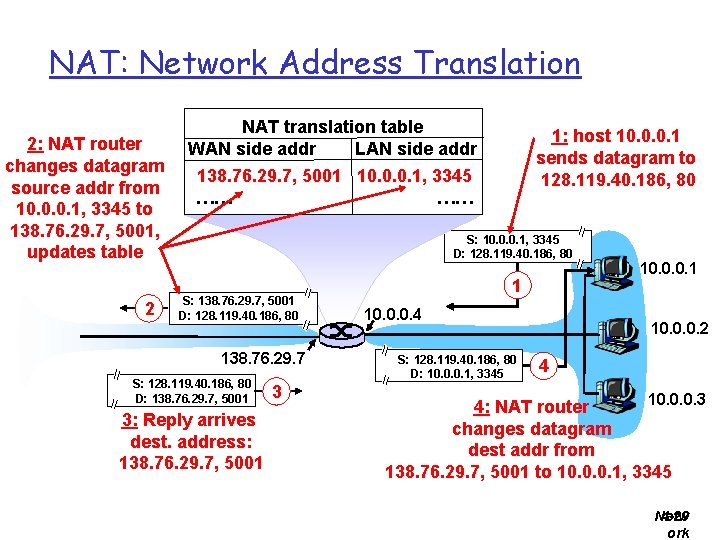
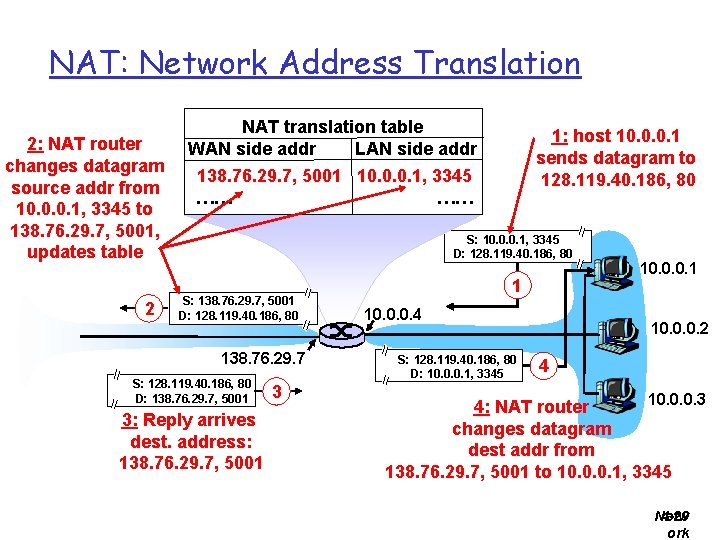
NAT: Network Address Translation 2: NAT router changes datagram source addr from 10. 0. 0. 1, 3345 to 138. 76. 29. 7, 5001, updates table 2 NAT translation table WAN side addr LAN side addr 1: host 10. 0. 0. 1 sends datagram to 128. 119. 40. 186, 80 138. 76. 29. 7, 5001 10. 0. 0. 1, 3345 …… …… S: 10. 0. 0. 1, 3345 D: 128. 119. 40. 186, 80 S: 138. 76. 29. 7, 5001 D: 128. 119. 40. 186, 80 138. 76. 29. 7 S: 128. 119. 40. 186, 80 D: 138. 76. 29. 7, 5001 3: Reply arrives dest. address: 138. 76. 29. 7, 5001 3 1 10. 0. 0. 4 S: 128. 119. 40. 186, 80 D: 10. 0. 0. 1, 3345 10. 0. 0. 1 10. 0. 0. 2 4 10. 0. 0. 3 4: NAT router changes datagram dest addr from 138. 76. 29. 7, 5001 to 10. 0. 0. 1, 3345 Netw 4 -29 ork
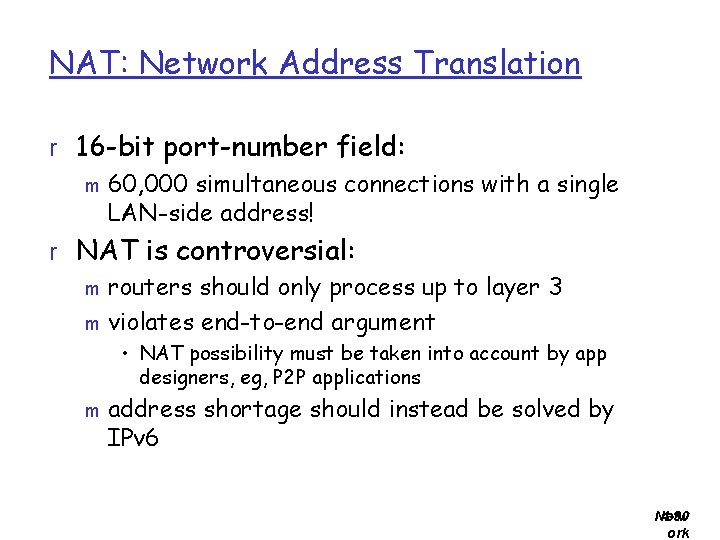
NAT: Network Address Translation r 16 -bit port-number field: m 60, 000 simultaneous connections with a single LAN-side address! r NAT is controversial: m routers should only process up to layer 3 m violates end-to-end argument • NAT possibility must be taken into account by app designers, eg, P 2 P applications m address shortage should instead be solved by IPv 6 Netw 4 -30 ork
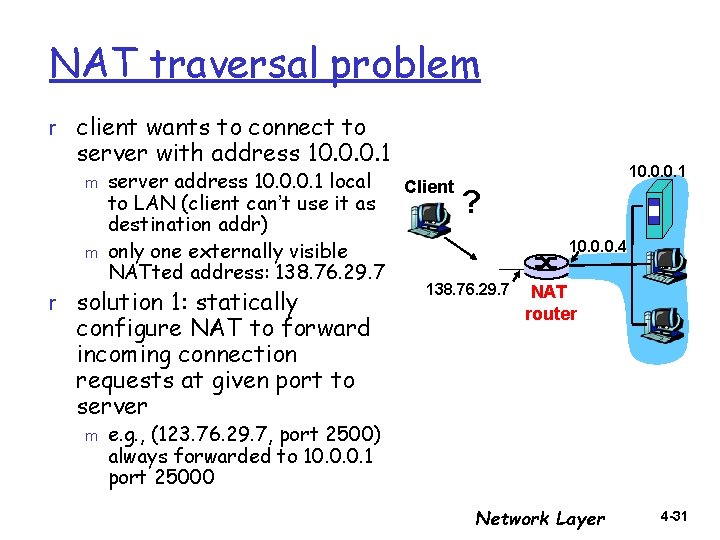
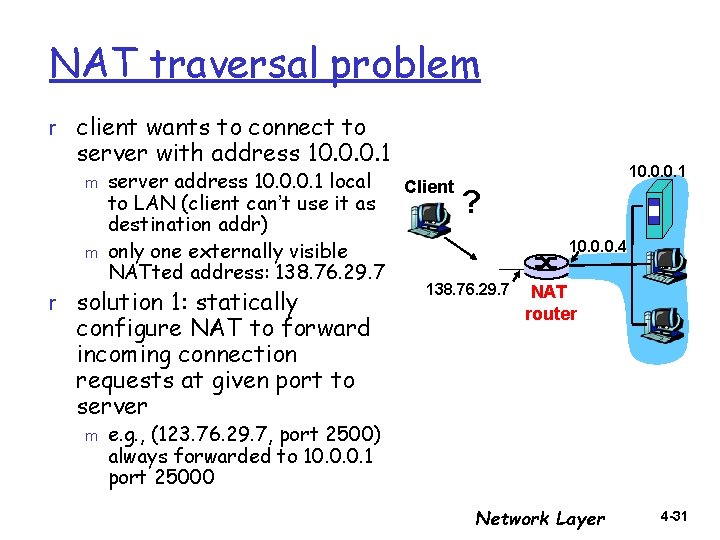
NAT traversal problem r client wants to connect to server with address 10. 0. 0. 1 m m server address 10. 0. 0. 1 local Client to LAN (client can’t use it as destination addr) only one externally visible NATted address: 138. 76. 29. 7 r solution 1: statically configure NAT to forward incoming connection requests at given port to server m 10. 0. 0. 1 ? 10. 0. 0. 4 138. 76. 29. 7 NAT router e. g. , (123. 76. 29. 7, port 2500) always forwarded to 10. 0. 0. 1 port 25000 Network Layer 4 -31
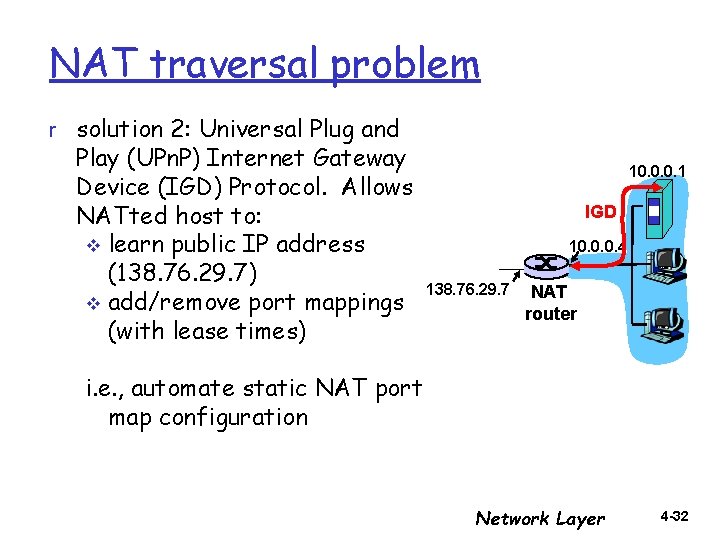
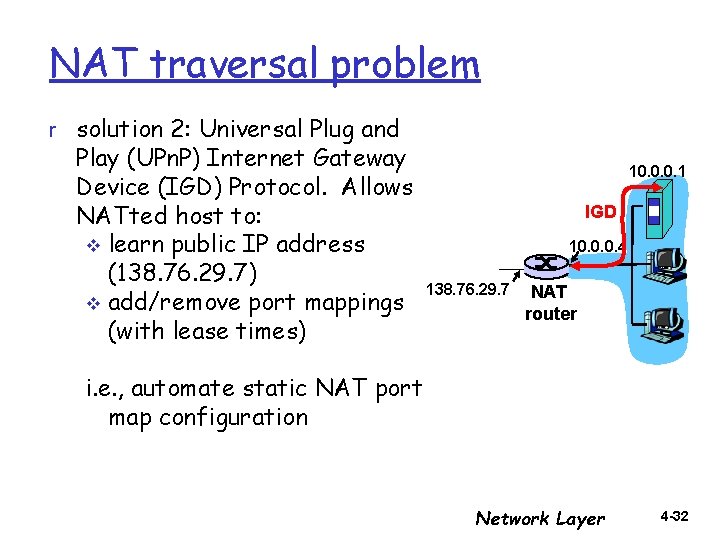
NAT traversal problem r solution 2: Universal Plug and Play (UPn. P) Internet Gateway Device (IGD) Protocol. Allows NATted host to: v learn public IP address (138. 76. 29. 7) v add/remove port mappings (with lease times) 10. 0. 0. 1 IGD 10. 0. 0. 4 138. 76. 29. 7 NAT router i. e. , automate static NAT port map configuration Network Layer 4 -32
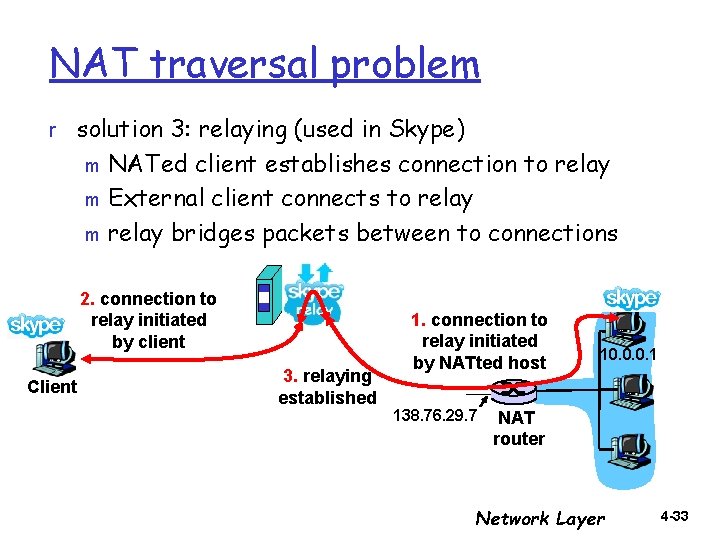
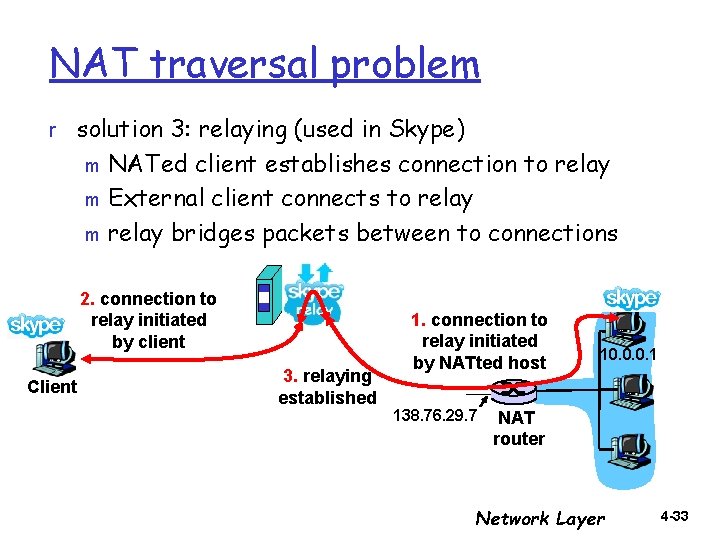
NAT traversal problem r solution 3: relaying (used in Skype) NATed client establishes connection to relay m External client connects to relay m relay bridges packets between to connections m 2. connection to relay initiated by client Client 3. relaying established 1. connection to relay initiated by NATted host 138. 76. 29. 7 10. 0. 0. 1 NAT router Network Layer 4 -33
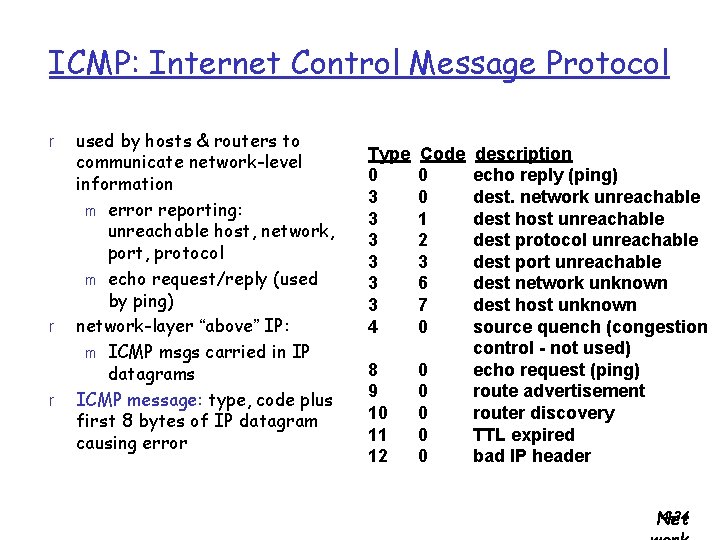
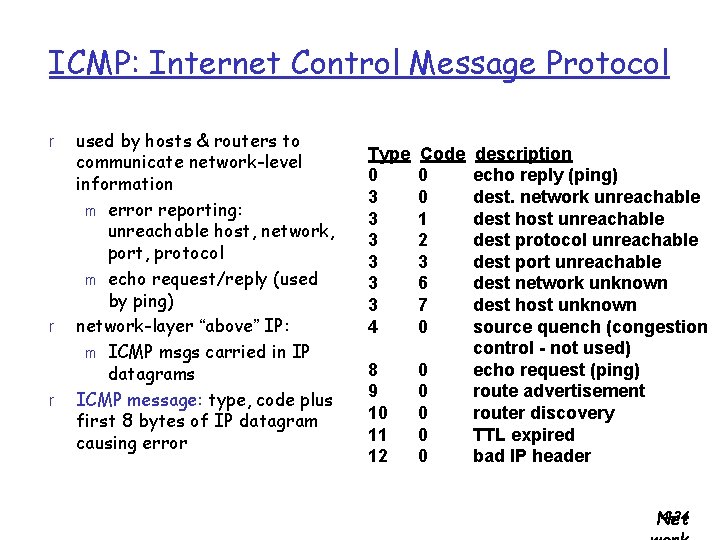
ICMP: Internet Control Message Protocol r r r used by hosts & routers to communicate network-level information m error reporting: unreachable host, network, port, protocol m echo request/reply (used by ping) network-layer “above” IP: m ICMP msgs carried in IP datagrams ICMP message: type, code plus first 8 bytes of IP datagram causing error Type 0 3 3 3 4 Code 0 0 1 2 3 6 7 0 8 9 10 11 12 0 0 0 description echo reply (ping) dest. network unreachable dest host unreachable dest protocol unreachable dest port unreachable dest network unknown dest host unknown source quench (congestion control - not used) echo request (ping) route advertisement router discovery TTL expired bad IP header 4 -34 Net
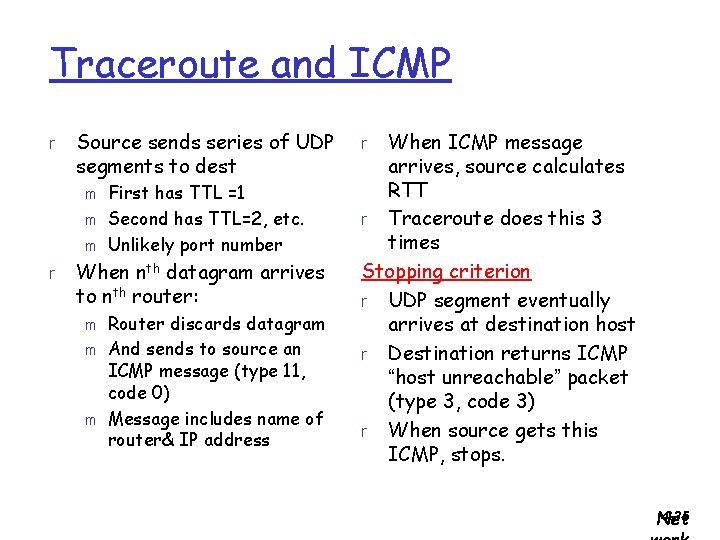
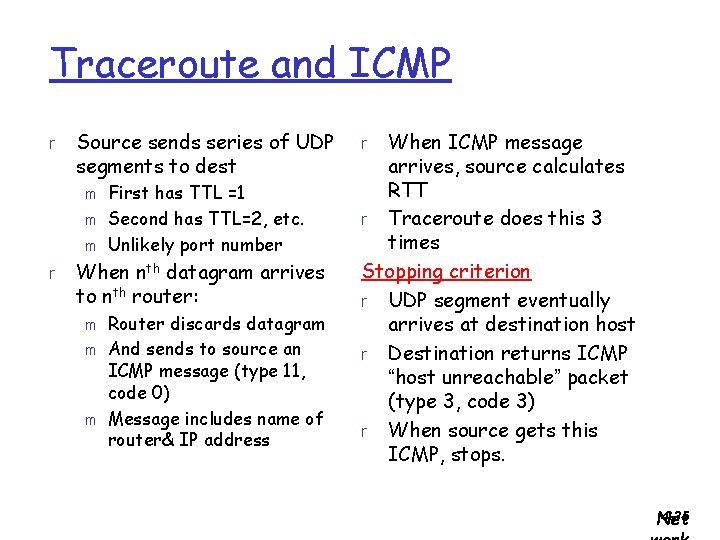
Traceroute and ICMP r Source sends series of UDP segments to dest m m m r First has TTL =1 Second has TTL=2, etc. Unlikely port number When nth datagram arrives to nth router: m m m Router discards datagram And sends to source an ICMP message (type 11, code 0) Message includes name of router& IP address When ICMP message arrives, source calculates RTT r Traceroute does this 3 times Stopping criterion r UDP segment eventually arrives at destination host r Destination returns ICMP “host unreachable” packet (type 3, code 3) r When source gets this ICMP, stops. r 4 -35 Net
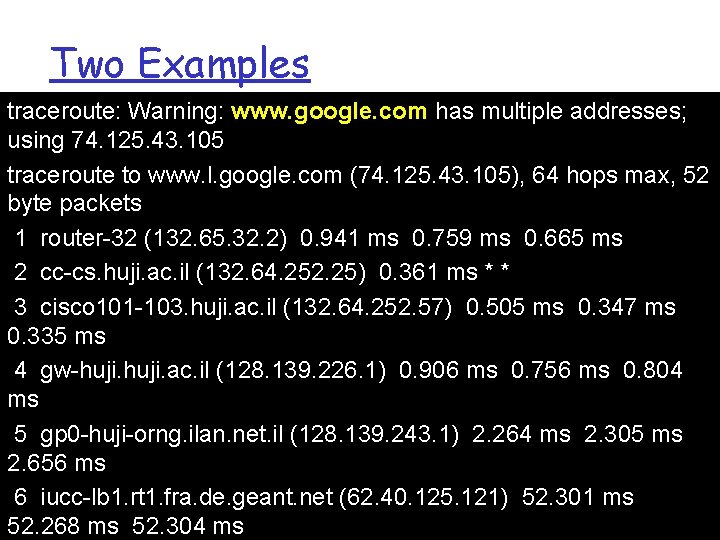
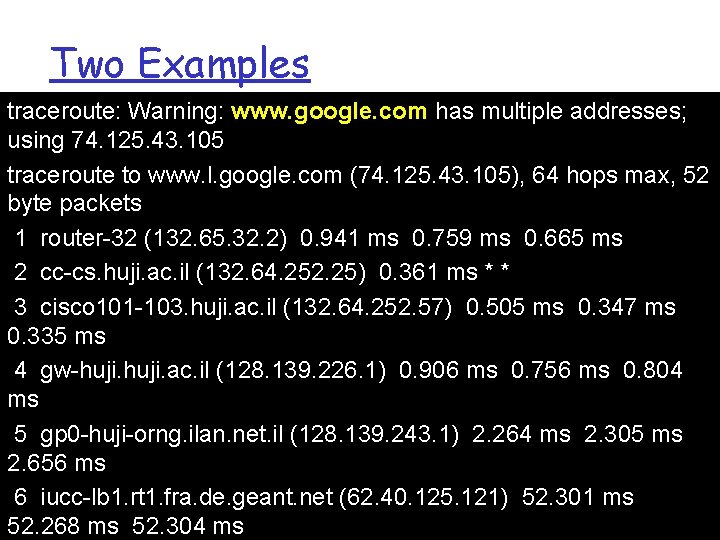
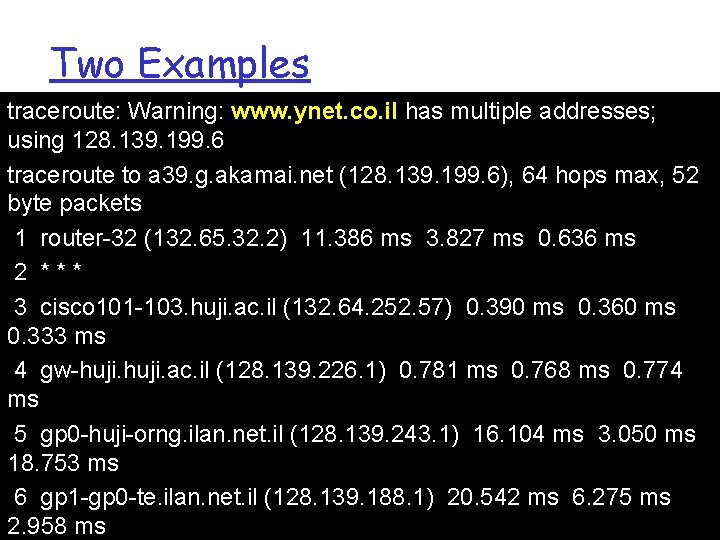
Two Examples traceroute: Warning: www. google. com has multiple addresses; using 74. 125. 43. 105 traceroute to www. l. google. com (74. 125. 43. 105), 64 hops max, 52 byte packets 1 router-32 (132. 65. 32. 2) 0. 941 ms 0. 759 ms 0. 665 ms 2 cc-cs. huji. ac. il (132. 64. 252. 25) 0. 361 ms * * 3 cisco 101 -103. huji. ac. il (132. 64. 252. 57) 0. 505 ms 0. 347 ms 0. 335 ms 4 gw-huji. ac. il (128. 139. 226. 1) 0. 906 ms 0. 756 ms 0. 804 ms 5 gp 0 -huji-orng. ilan. net. il (128. 139. 243. 1) 2. 264 ms 2. 305 ms 2. 656 ms 6 iucc-lb 1. rt 1. fra. de. geant. net (62. 40. 125. 121) 52. 301 ms 5 -36 52. 268 ms 52. 304 ms
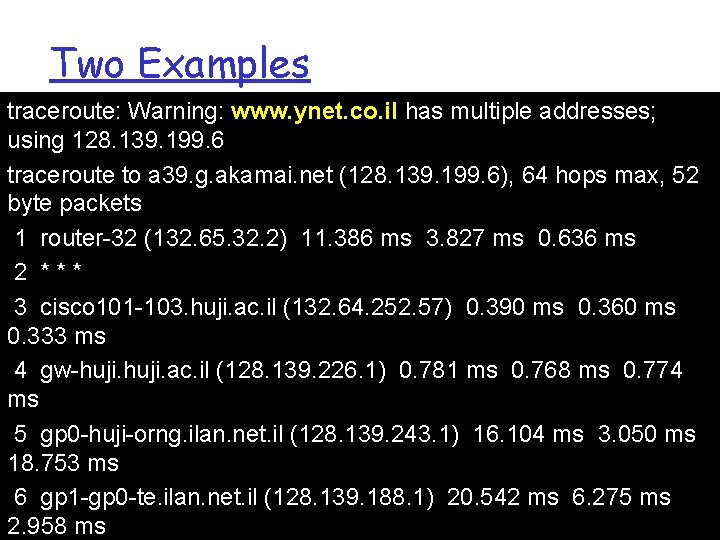
Two Examples traceroute: Warning: www. ynet. co. il has multiple addresses; using 128. 139. 199. 6 traceroute to a 39. g. akamai. net (128. 139. 199. 6), 64 hops max, 52 byte packets 1 router-32 (132. 65. 32. 2) 11. 386 ms 3. 827 ms 0. 636 ms 2 *** 3 cisco 101 -103. huji. ac. il (132. 64. 252. 57) 0. 390 ms 0. 360 ms 0. 333 ms 4 gw-huji. ac. il (128. 139. 226. 1) 0. 781 ms 0. 768 ms 0. 774 ms 5 gp 0 -huji-orng. ilan. net. il (128. 139. 243. 1) 16. 104 ms 3. 050 ms 18. 753 ms 6 gp 1 -gp 0 -te. ilan. net. il (128. 139. 188. 1) 20. 542 ms 6. 275 ms 5 -37 2. 958 ms
IPv 6 r Initial motivation: 32 -bit address space soon to be completely allocated. r Additional motivation: header format helps speed processing/forwarding m header changes to facilitate Qo. S IPv 6 datagram format: m fixed-length 40 byte header m no fragmentation allowed m 4 -38 Net
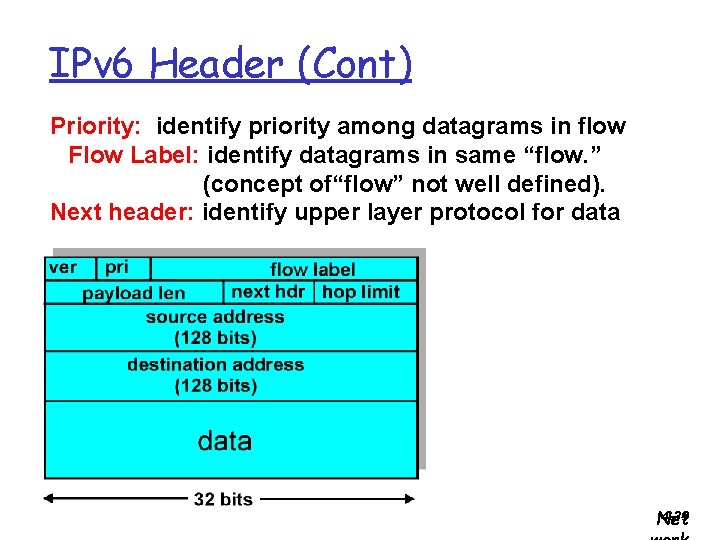
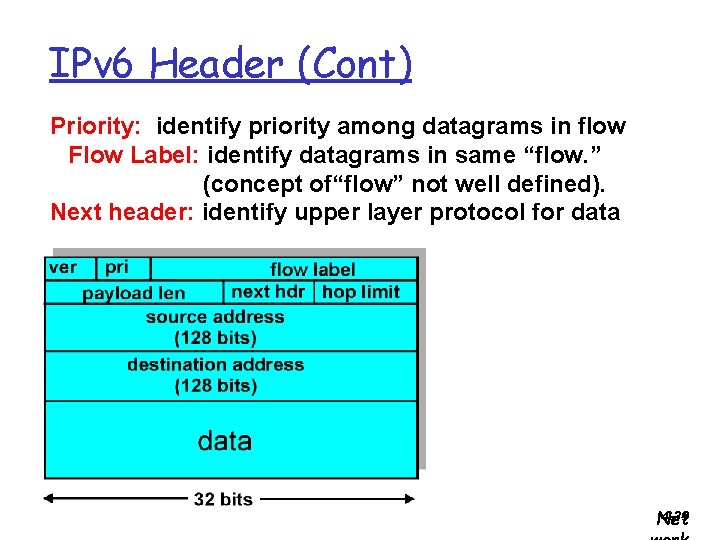
IPv 6 Header (Cont) Priority: identify priority among datagrams in flow Flow Label: identify datagrams in same “flow. ” (concept of“flow” not well defined). Next header: identify upper layer protocol for data 4 -39 Net
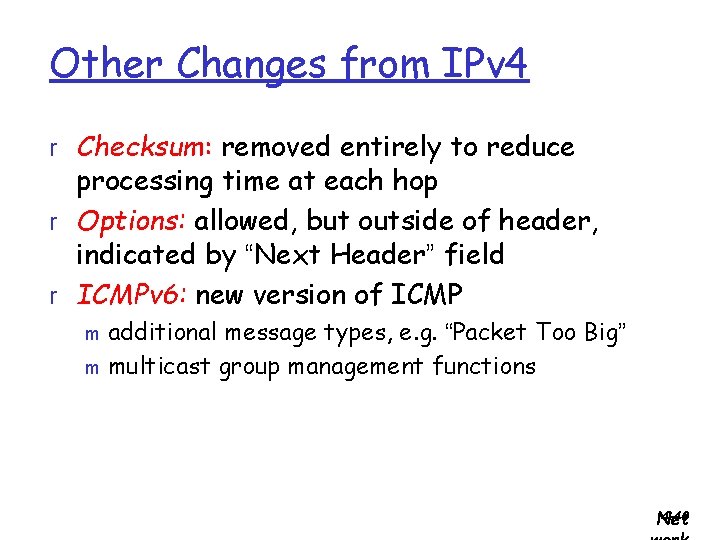
Other Changes from IPv 4 r Checksum: removed entirely to reduce processing time at each hop r Options: allowed, but outside of header, indicated by “Next Header” field r ICMPv 6: new version of ICMP additional message types, e. g. “Packet Too Big” m multicast group management functions m 4 -40 Net
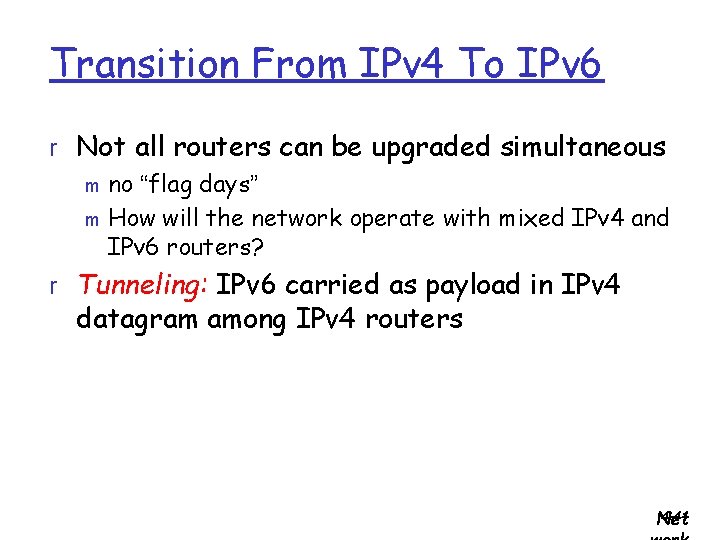
Transition From IPv 4 To IPv 6 r Not all routers can be upgraded simultaneous m no “flag days” m How will the network operate with mixed IPv 4 and IPv 6 routers? r Tunneling: IPv 6 carried as payload in IPv 4 datagram among IPv 4 routers 4 -41 Net
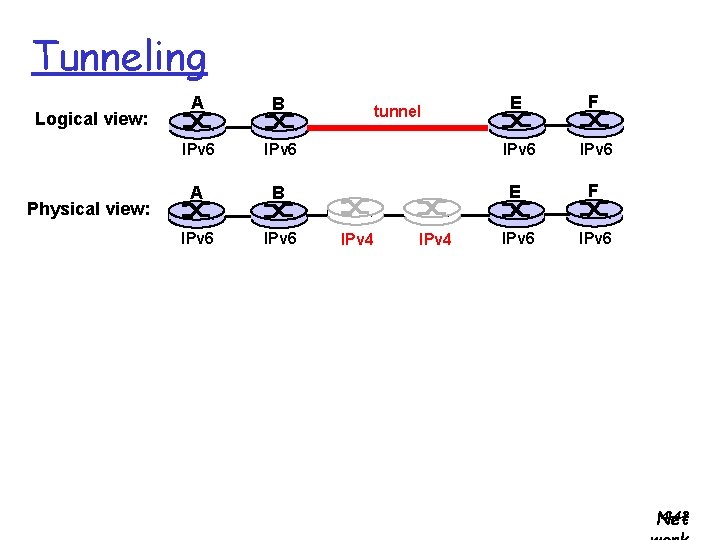
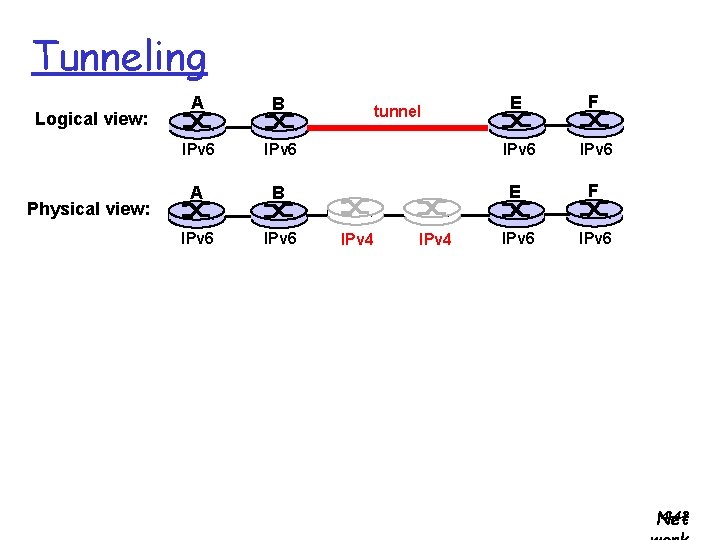
Tunneling Logical view: Physical view: E F IPv 6 IPv 6 A B IPv 6 tunnel IPv 4 4 -42 Net
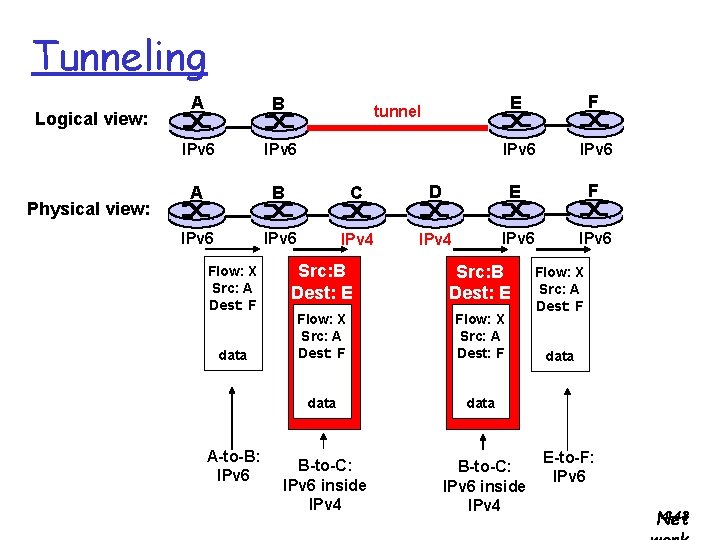
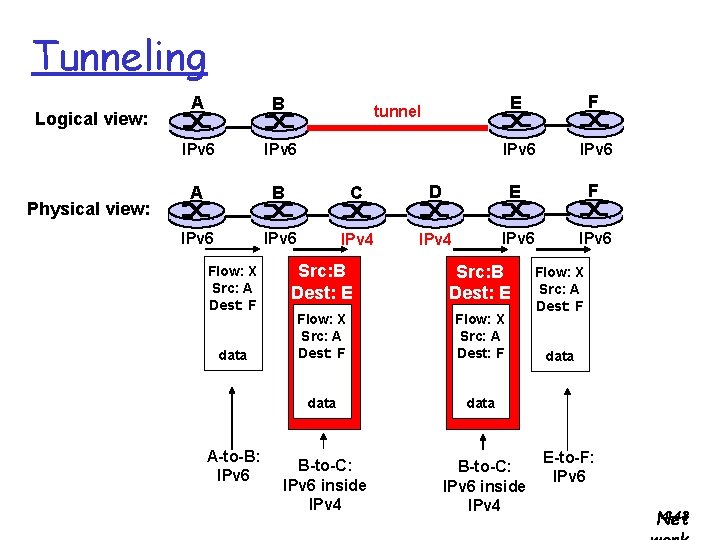
Tunneling Logical view: Physical view: A B IPv 6 A B C IPv 6 IPv 4 Flow: X Src: A Dest: F data A-to-B: IPv 6 E F IPv 6 D E F IPv 4 IPv 6 tunnel Src: B Dest: E Flow: X Src: A Dest: F data B-to-C: IPv 6 inside IPv 4 Flow: X Src: A Dest: F data E-to-F: IPv 6 4 -43 Net
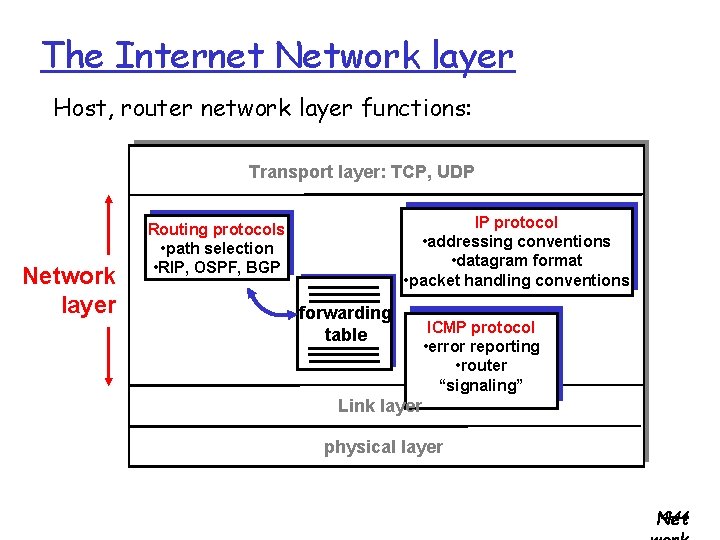
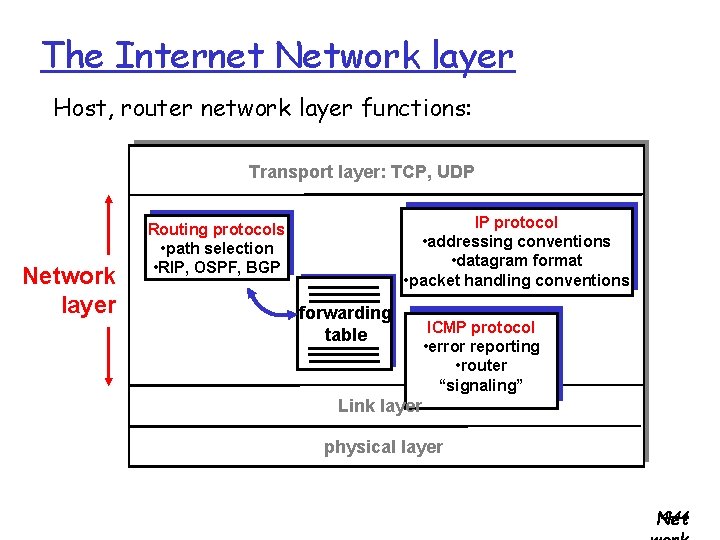
The Internet Network layer Host, router network layer functions: Transport layer: TCP, UDP Network layer IP protocol • addressing conventions • datagram format • packet handling conventions Routing protocols • path selection • RIP, OSPF, BGP forwarding table ICMP protocol • error reporting • router “signaling” Link layer physical layer 4 -44 Net
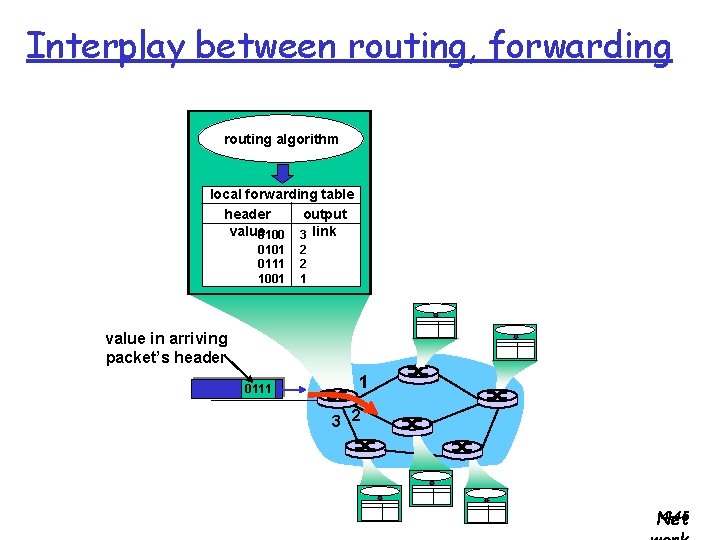
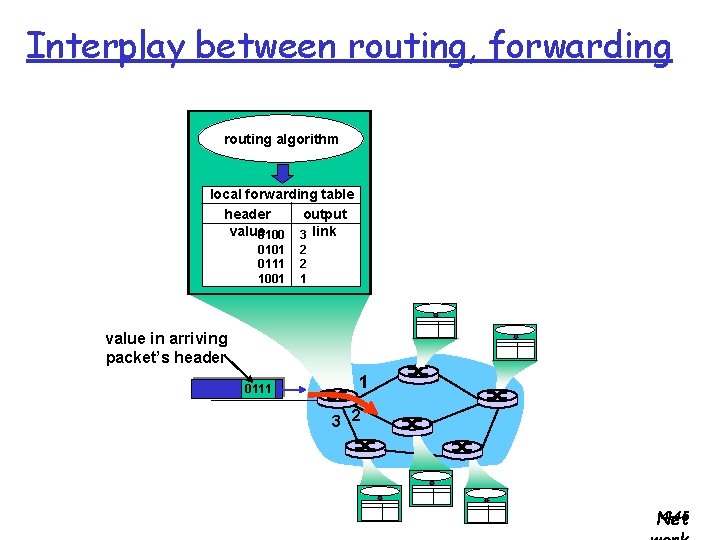
Interplay between routing, forwarding routing algorithm local forwarding table header output value 0100 3 link 0101 0111 1001 2 2 1 value in arriving packet’s header 0111 1 3 2 4 -45 Net
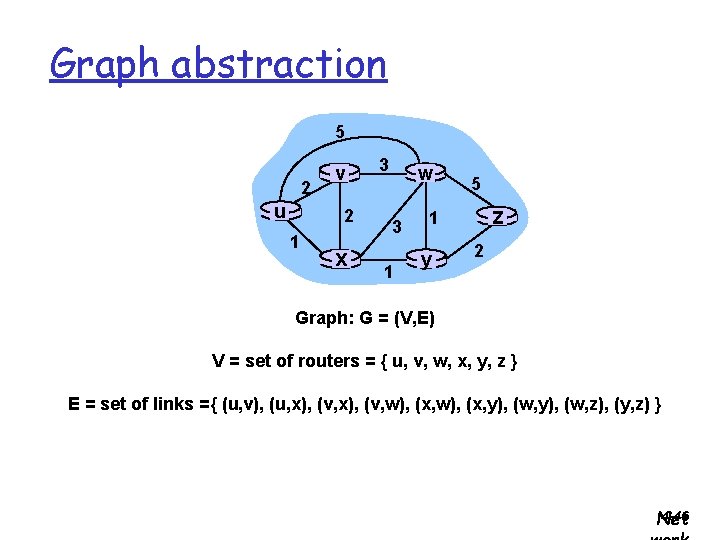
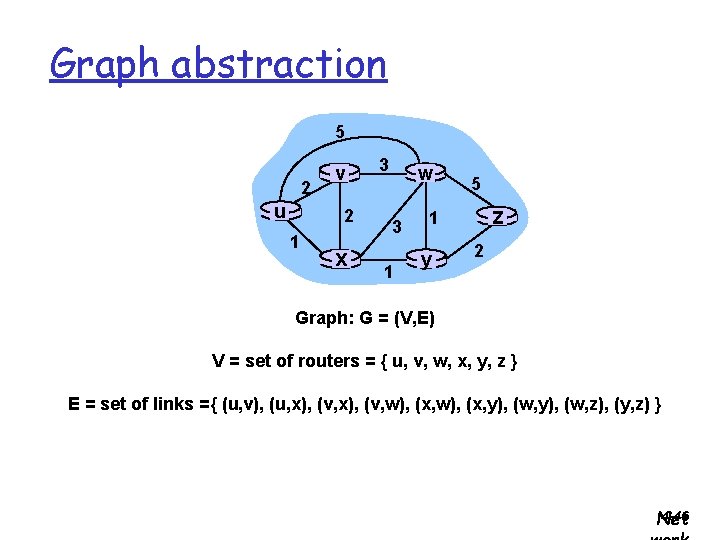
Graph abstraction 5 2 u v 2 1 x 3 w 3 1 5 z 1 y 2 Graph: G = (V, E) V = set of routers = { u, v, w, x, y, z } E = set of links ={ (u, v), (u, x), (v, w), (x, y), (w, z), (y, z) } 4 -46 Net
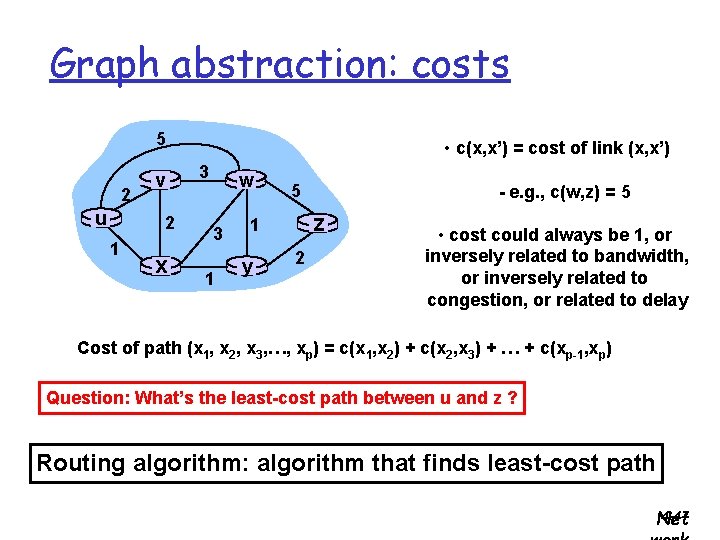
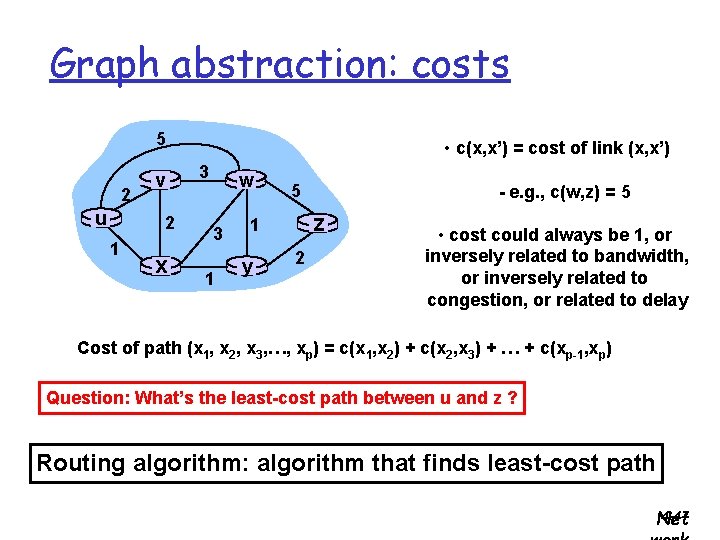
Graph abstraction: costs 5 2 u v 2 1 x • c(x, x’) = cost of link (x, x’) 3 w 3 1 5 z 1 y - e. g. , c(w, z) = 5 2 • cost could always be 1, or inversely related to bandwidth, or inversely related to congestion, or related to delay Cost of path (x 1, x 2, x 3, …, xp) = c(x 1, x 2) + c(x 2, x 3) + … + c(xp-1, xp) Question: What’s the least-cost path between u and z ? Routing algorithm: algorithm that finds least-cost path 4 -47 Net
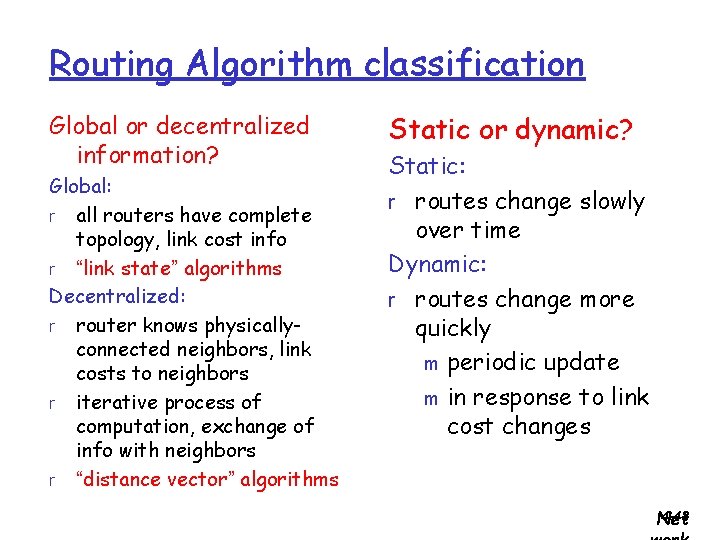
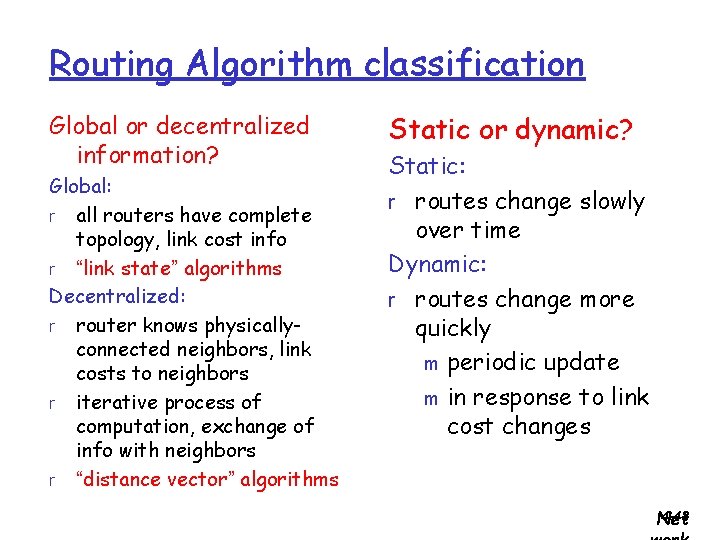
Routing Algorithm classification Global or decentralized information? Global: r all routers have complete topology, link cost info r “link state” algorithms Decentralized: r router knows physicallyconnected neighbors, link costs to neighbors r iterative process of computation, exchange of info with neighbors r “distance vector” algorithms Static or dynamic? Static: r routes change slowly over time Dynamic: r routes change more quickly m periodic update m in response to link cost changes 4 -48 Net
Agenda r 4. 5 Routing algorithms m Link state m Distance Vector r 4. 6 Routing in the Internet m m RIP OSPF 4 -49 Net
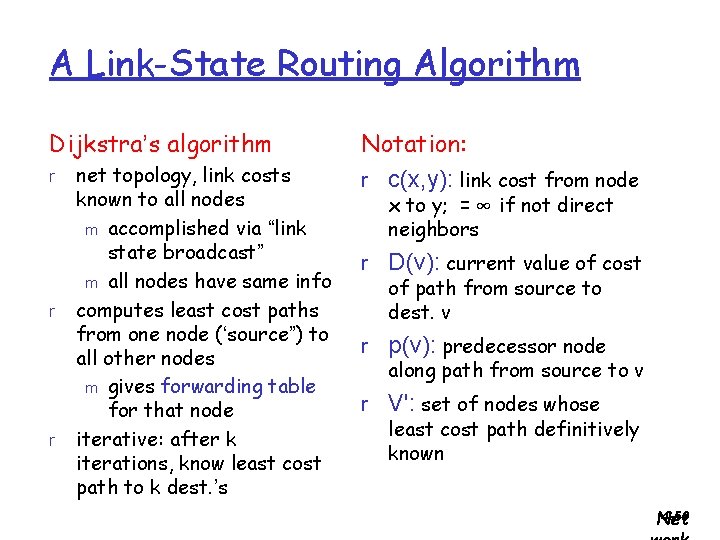
A Link-State Routing Algorithm Dijkstra’s algorithm r r r net topology, link costs known to all nodes m accomplished via “link state broadcast” m all nodes have same info computes least cost paths from one node (‘source”) to all other nodes m gives forwarding table for that node iterative: after k iterations, know least cost path to k dest. ’s Notation: r c(x, y): link cost from node x to y; = ∞ if not direct neighbors r D(v): current value of cost of path from source to dest. v r p(v): predecessor node along path from source to v r V': set of nodes whose least cost path definitively known 4 -50 Net
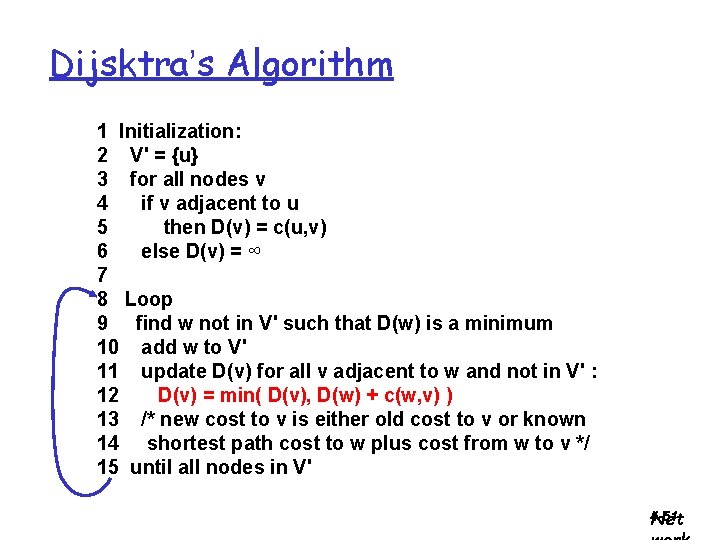
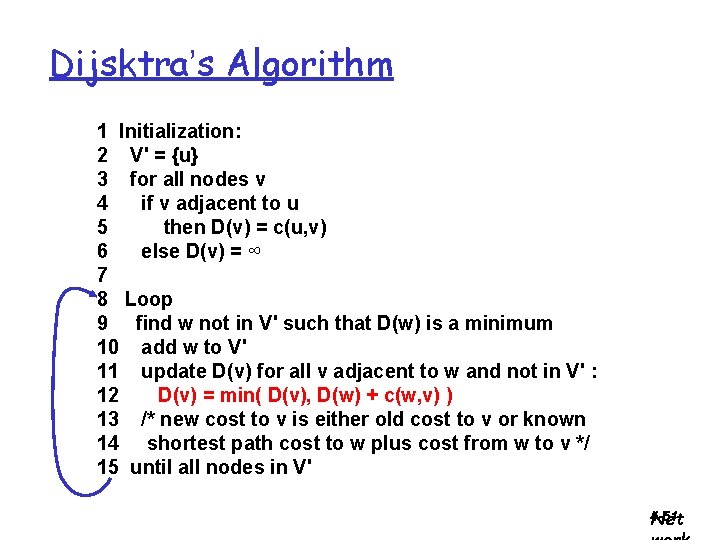
Dijsktra’s Algorithm 1 Initialization: 2 V' = {u} 3 for all nodes v 4 if v adjacent to u 5 then D(v) = c(u, v) 6 else D(v) = ∞ 7 8 Loop 9 find w not in V' such that D(w) is a minimum 10 add w to V' 11 update D(v) for all v adjacent to w and not in V' : 12 D(v) = min( D(v), D(w) + c(w, v) ) 13 /* new cost to v is either old cost to v or known 14 shortest path cost to w plus cost from w to v */ 15 until all nodes in V' 4 -51 Net
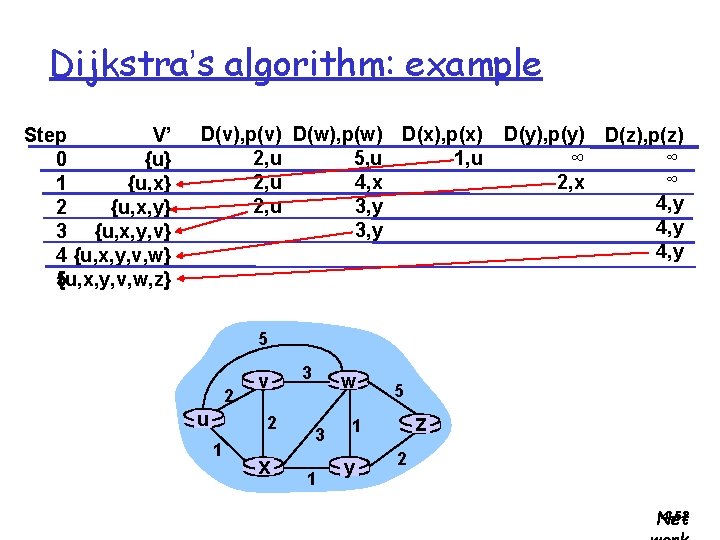
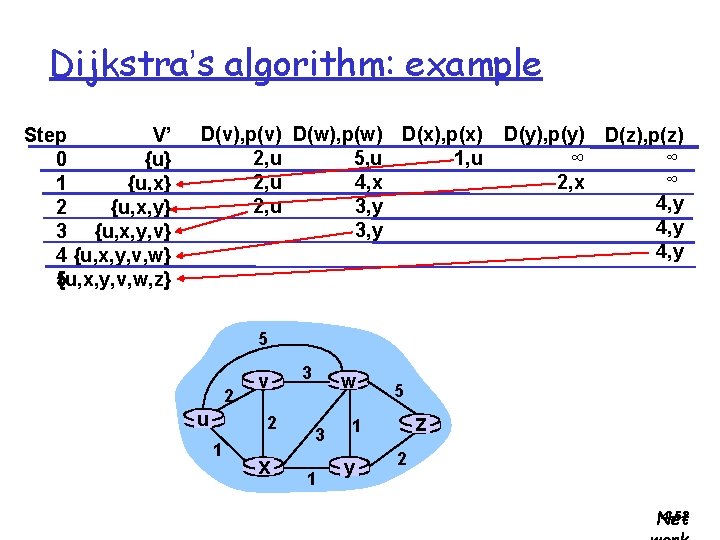
Dijkstra’s algorithm: example Step V’ 0 {u} 1 {u, x} 2 {u, x, y} 3 {u, x, y, v} 4 {u, x, y, v, w} 5 {u, x, y, v, w, z} D(v), p(v) D(w), p(w) D(x), p(x) 2, u 1, u 5, u 2, u 4, x 2, u 3, y D(y), p(y) D(z), p(z) ∞ ∞ ∞ 2, x 4, y 5 2 u v 2 1 x 3 w 3 1 5 z 1 y 2 4 -52 Net
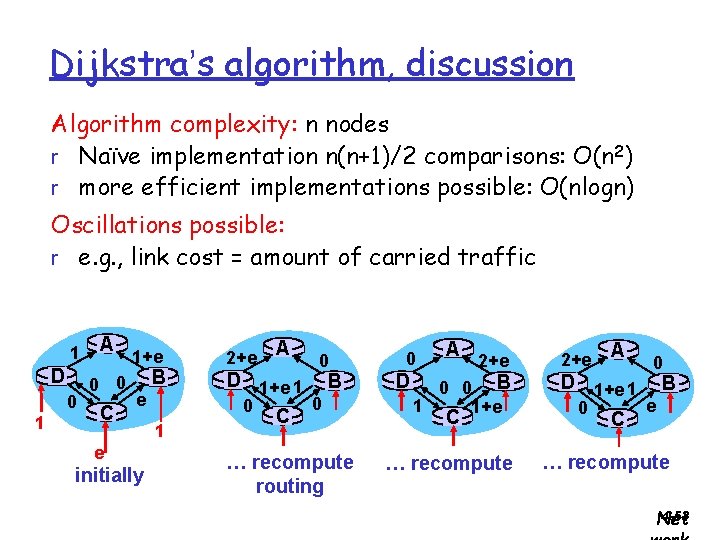
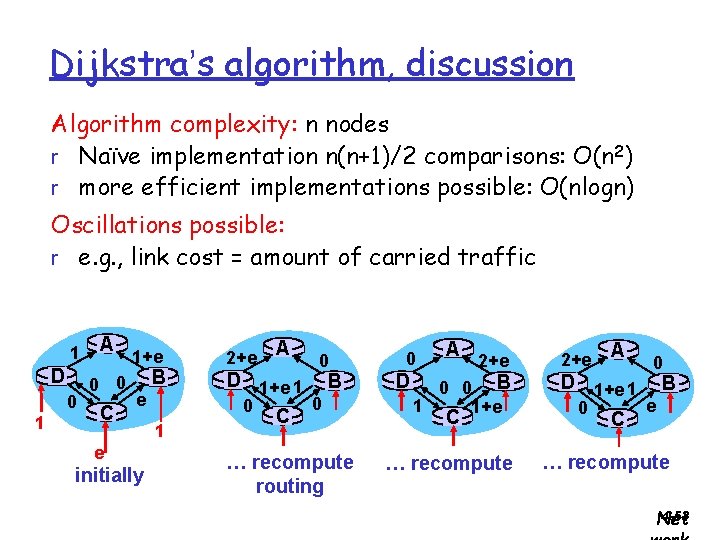
Dijkstra’s algorithm, discussion Algorithm complexity: n nodes r Naïve implementation n(n+1)/2 comparisons: O(n 2) r more efficient implementations possible: O(nlogn) Oscillations possible: r e. g. , link cost = amount of carried traffic 1 D 0 1 A 0 0 C A 1+e 2+e e D 1+e 1 B 0 0 C B e initially 1 0 … recompute routing 0 D A 2+e 0 0 B 1 1+e C … recompute 2+e A 0 D 1+e 1 B e 0 C … recompute 4 -53 Net
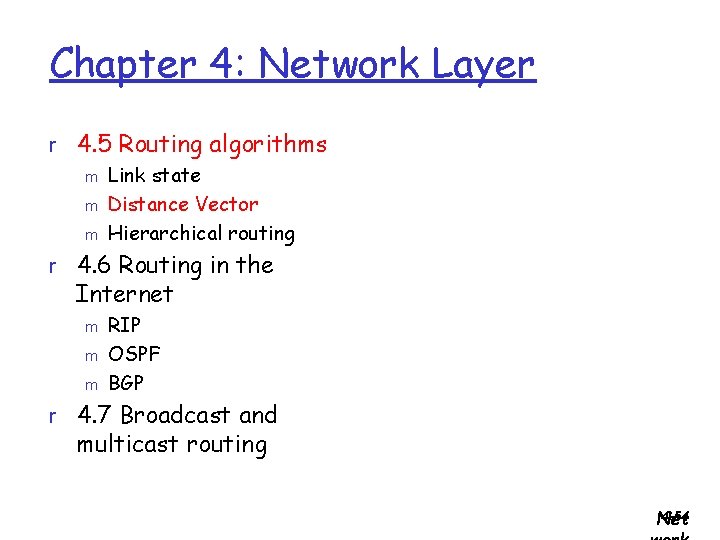
Chapter 4: Network Layer r 4. 5 Routing algorithms m Link state m Distance Vector m Hierarchical routing r 4. 6 Routing in the Internet m m m RIP OSPF BGP r 4. 7 Broadcast and multicast routing 4 -54 Net
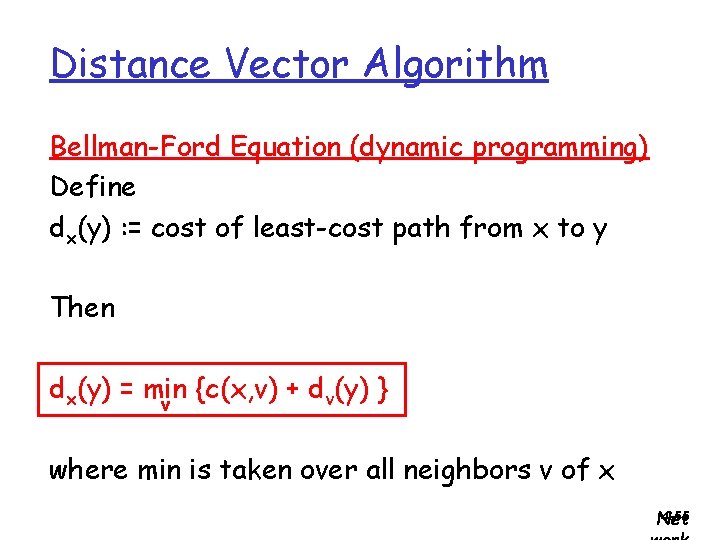
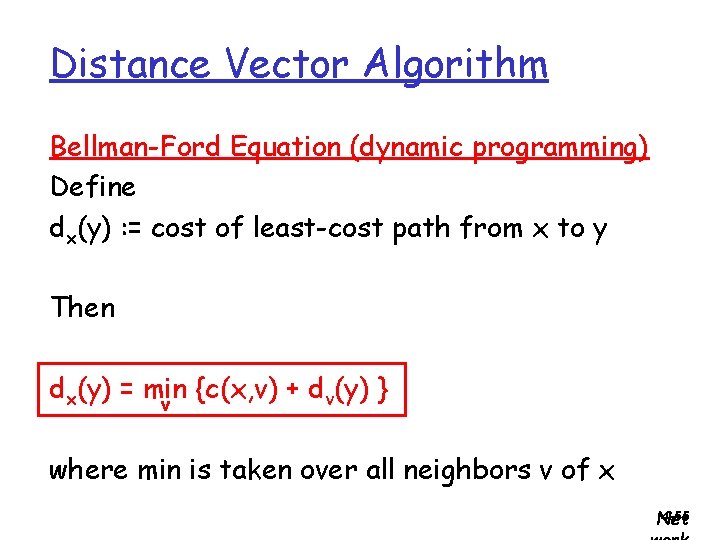
Distance Vector Algorithm Bellman-Ford Equation (dynamic programming) Define dx(y) : = cost of least-cost path from x to y Then dx(y) = min {c(x, v) + dv(y) } v where min is taken over all neighbors v of x 4 -55 Net
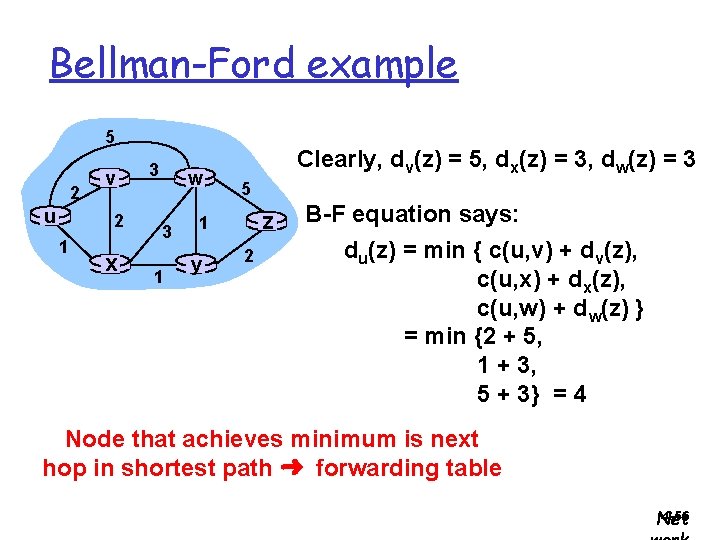
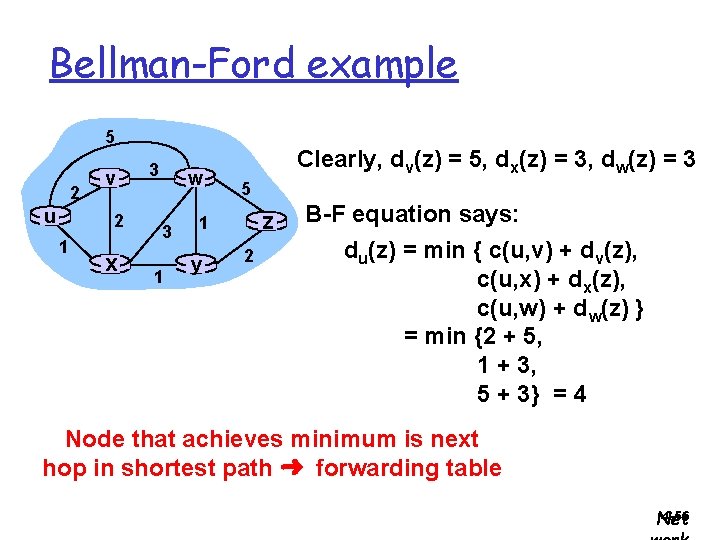
Bellman-Ford example 5 2 u v 2 1 x 3 w 3 1 Clearly, dv(z) = 5, dx(z) = 3, dw(z) = 3 5 z 1 y 2 B-F equation says: du(z) = min { c(u, v) + dv(z), c(u, x) + dx(z), c(u, w) + dw(z) } = min {2 + 5, 1 + 3, 5 + 3} = 4 Node that achieves minimum is next hop in shortest path ➜ forwarding table 4 -56 Net
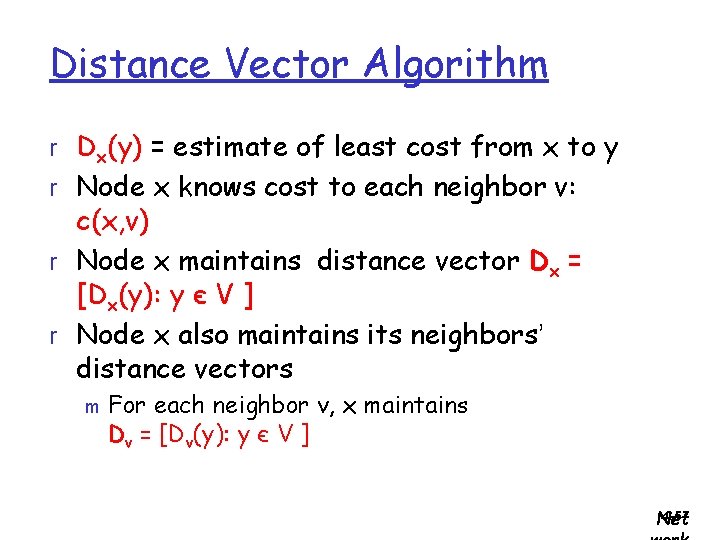
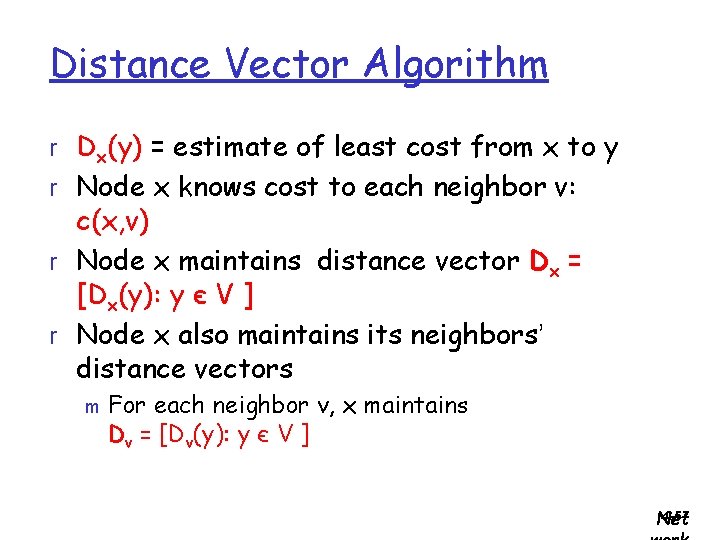
Distance Vector Algorithm r Dx(y) = estimate of least cost from x to y r Node x knows cost to each neighbor v: c(x, v) r Node x maintains distance vector Dx = [Dx(y): y є V ] r Node x also maintains its neighbors’ distance vectors m For each neighbor v, x maintains Dv = [Dv(y): y є V ] 4 -57 Net
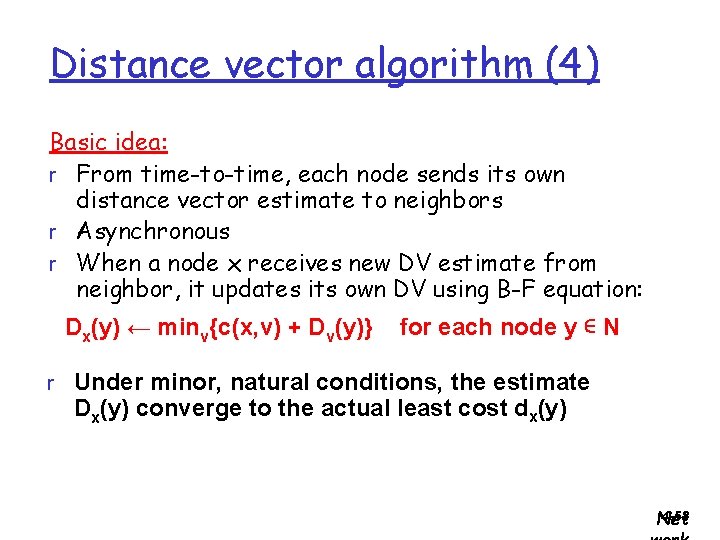
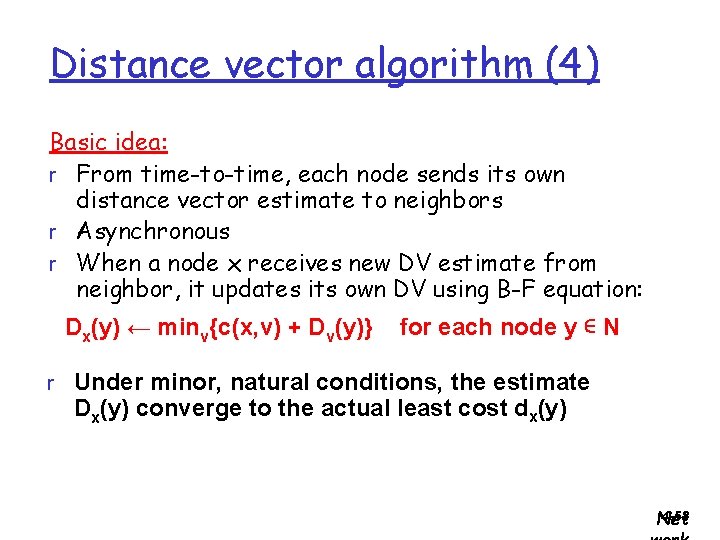
Distance vector algorithm (4) Basic idea: r From time-to-time, each node sends its own distance vector estimate to neighbors r Asynchronous r When a node x receives new DV estimate from neighbor, it updates its own DV using B-F equation: Dx(y) ← minv{c(x, v) + Dv(y)} for each node y ∊ N r Under minor, natural conditions, the estimate Dx(y) converge to the actual least cost dx(y) 4 -58 Net
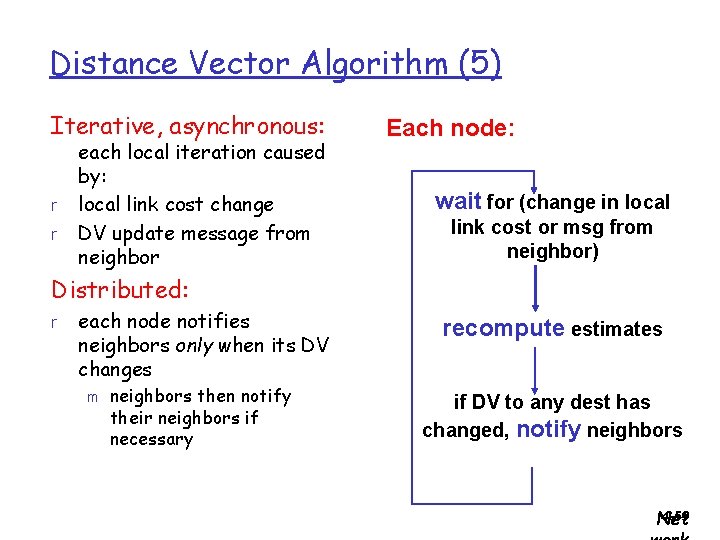
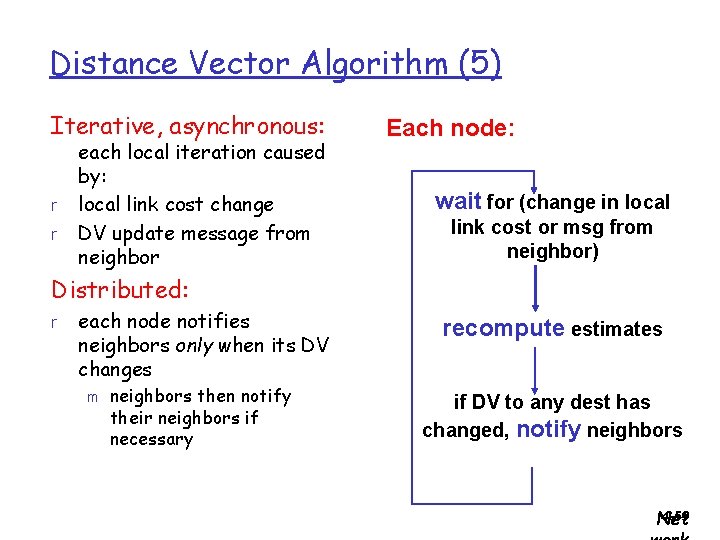
Distance Vector Algorithm (5) Iterative, asynchronous: r r each local iteration caused by: local link cost change DV update message from neighbor Each node: wait for (change in local link cost or msg from neighbor) Distributed: r each node notifies neighbors only when its DV changes recompute estimates neighbors then notify their neighbors if necessary if DV to any dest has changed, notify neighbors m 4 -59 Net
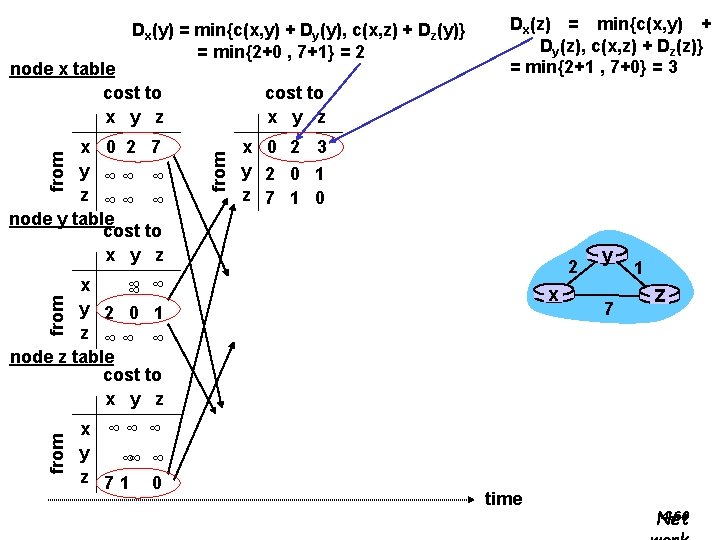
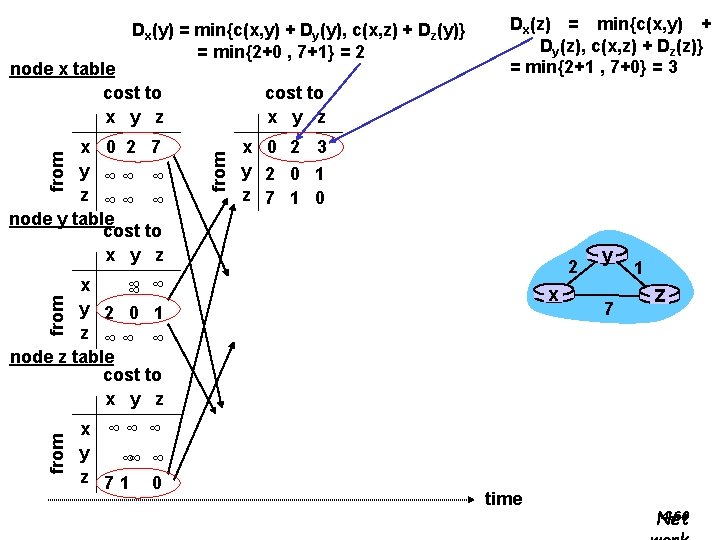
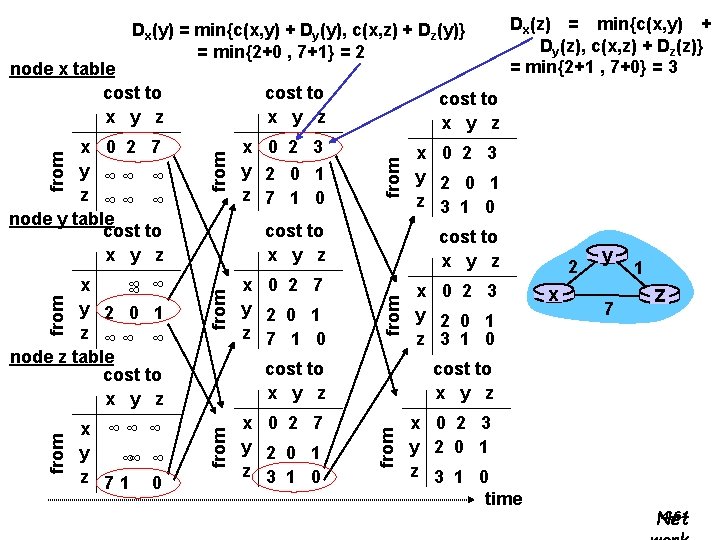
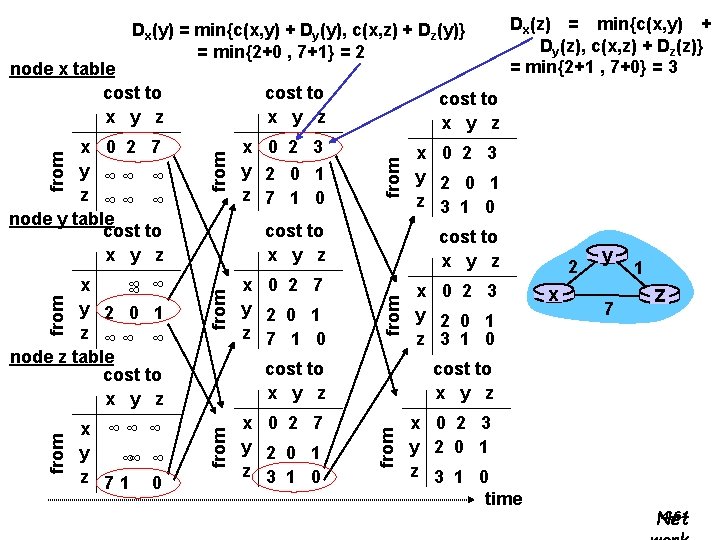
Dx(y) = min{c(x, y) + Dy(y), c(x, z) + Dz(y)} = min{2+0 , 7+1} = 2 node x table cost to x y z from x 0 2 7 y ∞∞ ∞ z ∞∞ ∞ node y table cost to x y z Dx(z) = min{c(x, y) + Dy(z), c(x, z) + Dz(z)} = min{2+1 , 7+0} = 3 x 0 2 3 y 2 0 1 z 7 1 0 2 x ∞ ∞ ∞ y 2 0 1 z ∞∞ ∞ node z table cost to x y z from x x ∞∞ ∞ y ∞∞ ∞ z 71 0 time y 7 1 z 4 -60 Net
Dx(y) = min{c(x, y) + Dy(y), c(x, z) + Dz(y)} = min{2+0 , 7+1} = 2 x ∞∞ ∞ y ∞∞ ∞ z 71 0 x 0 2 3 y 2 0 1 z 7 1 0 x 0 2 3 y 2 0 1 z 3 1 0 from cost to x y z x 0 2 7 y 2 0 1 z 7 1 0 x 0 2 3 y 2 0 1 z 3 1 0 from cost to x y z x 0 2 7 y 2 0 1 z 3 1 0 2 x y 7 1 z cost to x y z from x ∞ ∞ ∞ y 2 0 1 z ∞∞ ∞ node z table cost to x y z from x 0 2 7 y ∞∞ ∞ z ∞∞ ∞ node y table cost to x y z from node x table cost to x y z Dx(z) = min{c(x, y) + Dy(z), c(x, z) + Dz(z)} = min{2+1 , 7+0} = 3 x 0 2 3 y 2 0 1 z 3 1 0 time 4 -61 Net
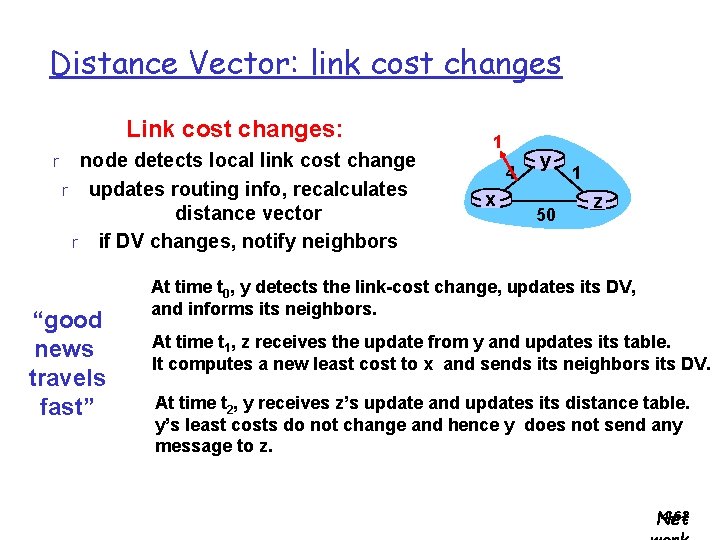
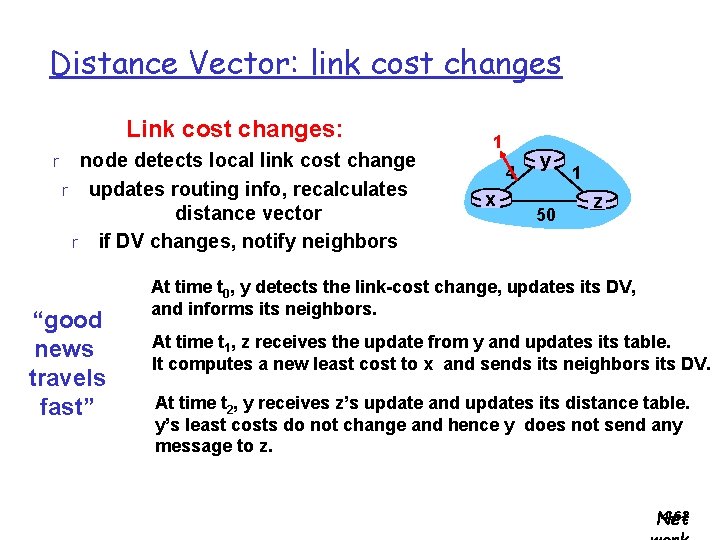
Distance Vector: link cost changes Link cost changes: r node detects local link cost change r updates routing info, recalculates distance vector r if DV changes, notify neighbors “good news travels fast” 1 4 x y 50 1 z At time t 0, y detects the link-cost change, updates its DV, and informs its neighbors. At time t 1, z receives the update from y and updates its table. It computes a new least cost to x and sends its neighbors its DV. At time t 2, y receives z’s update and updates its distance table. y’s least costs do not change and hence y does not send any message to z. 4 -62 Net
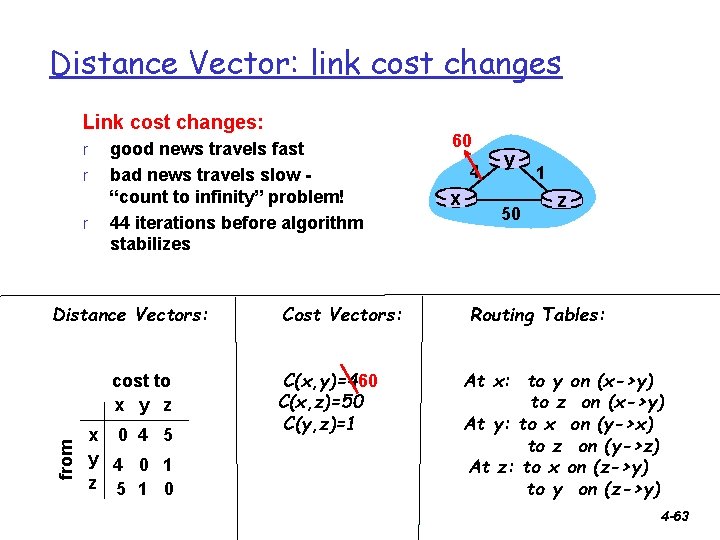
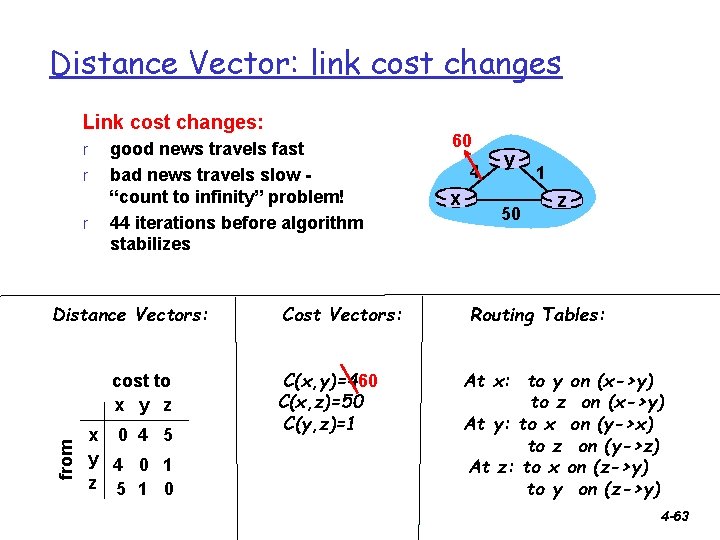
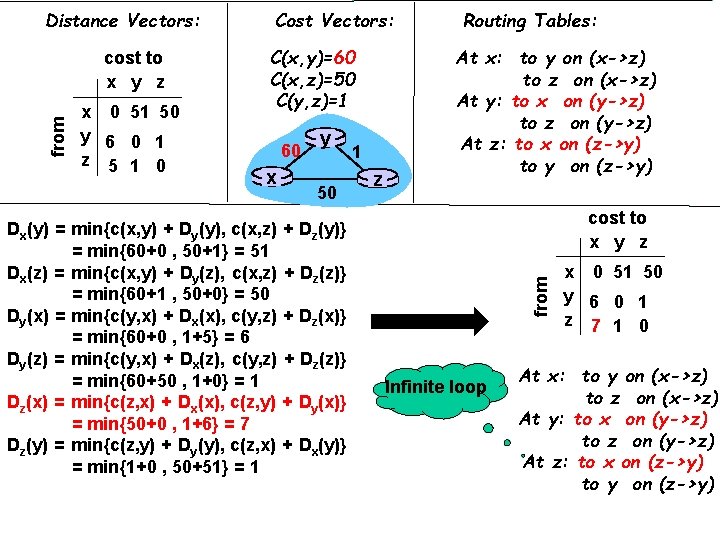
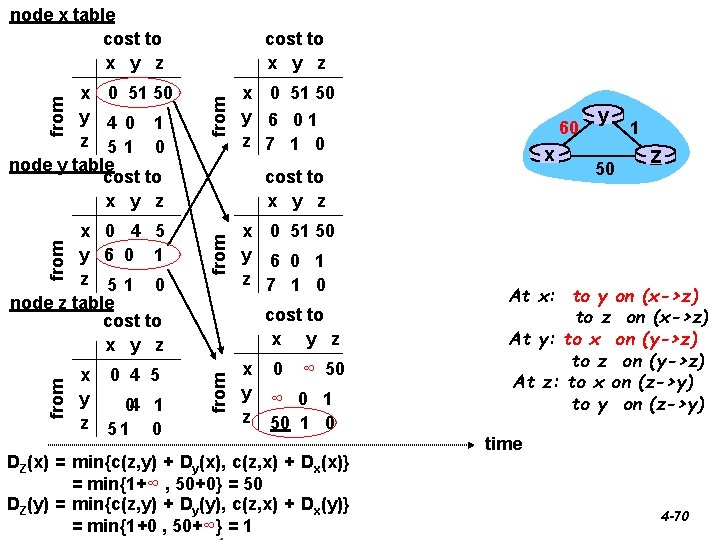
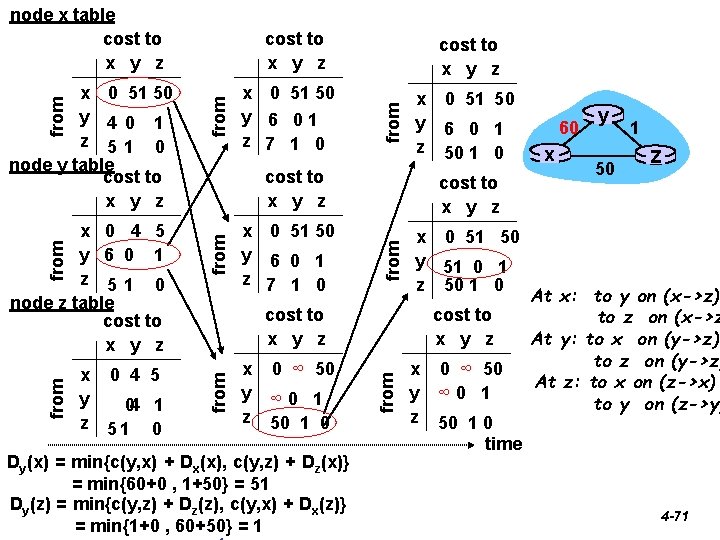
Distance Vector: link cost changes Link cost changes: r r r good news travels fast bad news travels slow “count to infinity” problem! 44 iterations before algorithm stabilizes Distance Vectors: from cost to x y z x 0 4 5 y 4 0 1 z 5 1 0 Cost Vectors: C(x, y)=460 C(x, z)=50 C(y, z)=1 60 4 x y 50 1 z Routing Tables: At x: to y on (x->y) to z on (x->y) At y: to x on (y->x) to z on (y->z) At z: to x on (z->y) to y on (z->y) 4 -63
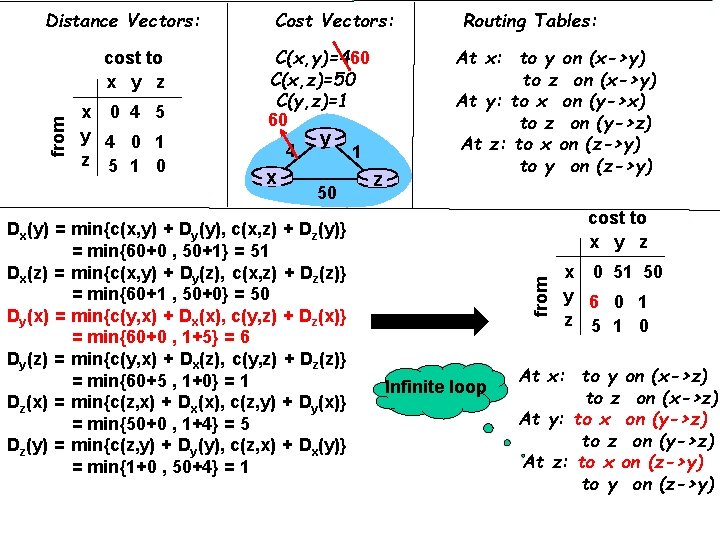
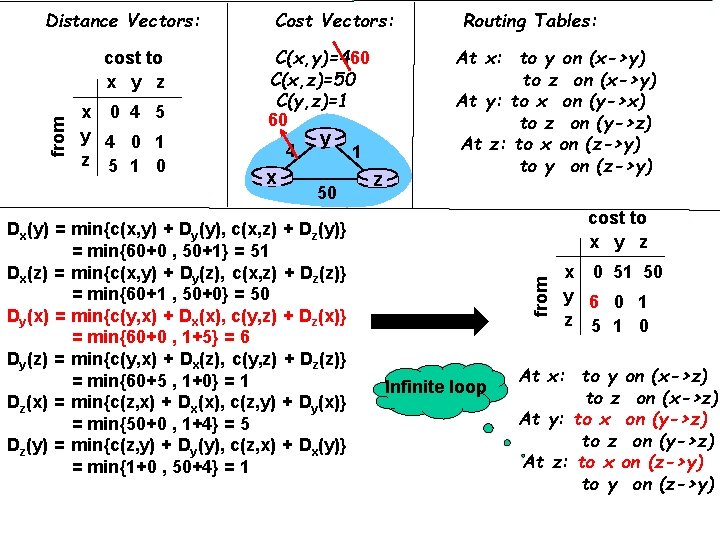
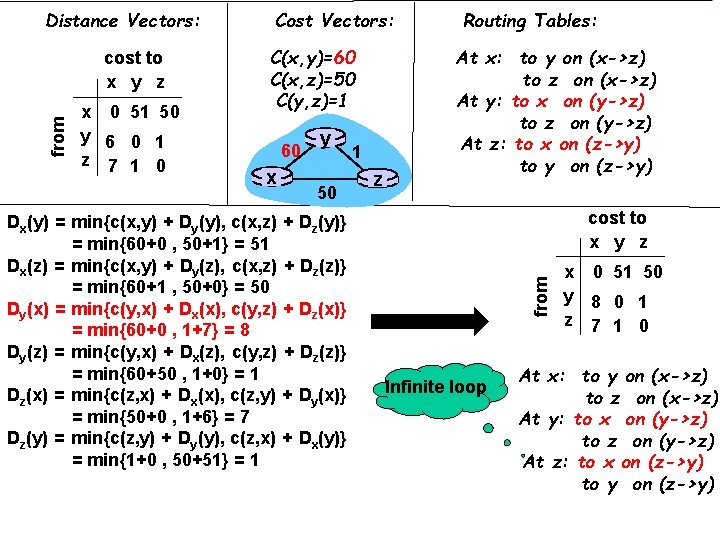
from cost to x y z x 0 4 5 y 4 0 1 z 5 1 0 Cost Vectors: C(x, y)=460 C(x, z)=50 C(y, z)=1 60 4 x y 50 Dx(y) = min{c(x, y) + Dy(y), c(x, z) + Dz(y)} = min{60+0 , 50+1} = 51 Dx(z) = min{c(x, y) + Dy(z), c(x, z) + Dz(z)} = min{60+1 , 50+0} = 50 Dy(x) = min{c(y, x) + Dx(x), c(y, z) + Dz(x)} = min{60+0 , 1+5} = 6 Dy(z) = min{c(y, x) + Dx(z), c(y, z) + Dz(z)} = min{60+5 , 1+0} = 1 Dz(x) = min{c(z, x) + Dx(x), c(z, y) + Dy(x)} = min{50+0 , 1+4} = 5 Dz(y) = min{c(z, y) + Dy(y), c(z, x) + Dx(y)} = min{1+0 , 50+4} = 1 1 z Routing Tables: At x: to y on (x->y) to z on (x->y) At y: to x on (y->x) to z on (y->z) At z: to x on (z->y) to y on (z->y) cost to x y z from Distance Vectors: Infinite loop x 0 51 50 y 6 0 1 z 5 1 0 At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->y) to y on (z->y)
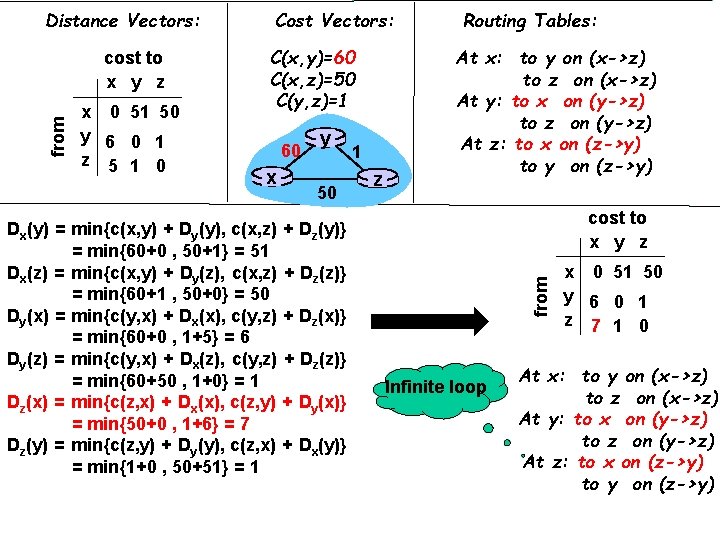
from cost to x y z x 0 51 50 y 6 0 1 z 5 1 0 Cost Vectors: C(x, y)=60 C(x, z)=50 C(y, z)=1 60 x y 50 Dx(y) = min{c(x, y) + Dy(y), c(x, z) + Dz(y)} = min{60+0 , 50+1} = 51 Dx(z) = min{c(x, y) + Dy(z), c(x, z) + Dz(z)} = min{60+1 , 50+0} = 50 Dy(x) = min{c(y, x) + Dx(x), c(y, z) + Dz(x)} = min{60+0 , 1+5} = 6 Dy(z) = min{c(y, x) + Dx(z), c(y, z) + Dz(z)} = min{60+50 , 1+0} = 1 Dz(x) = min{c(z, x) + Dx(x), c(z, y) + Dy(x)} = min{50+0 , 1+6} = 7 Dz(y) = min{c(z, y) + Dy(y), c(z, x) + Dx(y)} = min{1+0 , 50+51} = 1 1 z Routing Tables: At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->y) to y on (z->y) cost to x y z from Distance Vectors: Infinite loop x 0 51 50 y 6 0 1 z 7 1 0 At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->y) to y on (z->y)
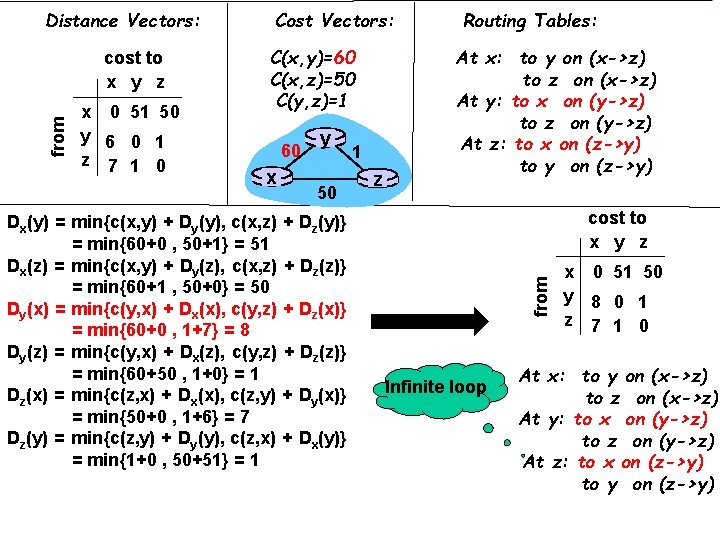
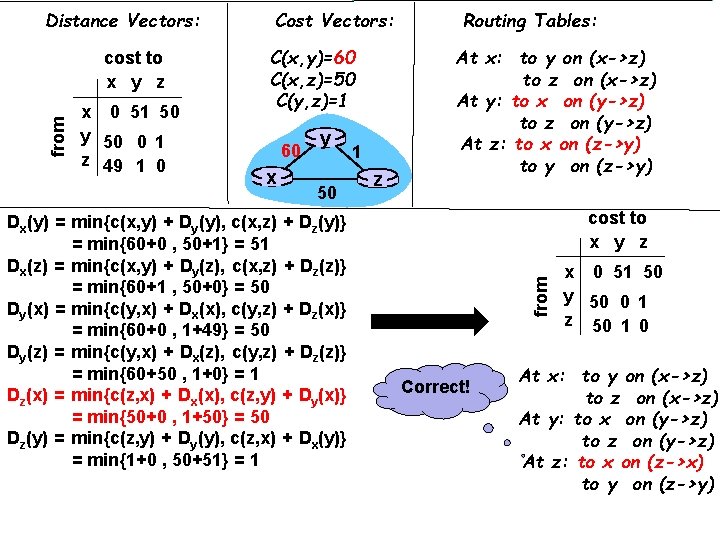
from cost to x y z x 0 51 50 y 6 0 1 z 7 1 0 Cost Vectors: C(x, y)=60 C(x, z)=50 C(y, z)=1 60 x y 50 Dx(y) = min{c(x, y) + Dy(y), c(x, z) + Dz(y)} = min{60+0 , 50+1} = 51 Dx(z) = min{c(x, y) + Dy(z), c(x, z) + Dz(z)} = min{60+1 , 50+0} = 50 Dy(x) = min{c(y, x) + Dx(x), c(y, z) + Dz(x)} = min{60+0 , 1+7} = 8 Dy(z) = min{c(y, x) + Dx(z), c(y, z) + Dz(z)} = min{60+50 , 1+0} = 1 Dz(x) = min{c(z, x) + Dx(x), c(z, y) + Dy(x)} = min{50+0 , 1+6} = 7 Dz(y) = min{c(z, y) + Dy(y), c(z, x) + Dx(y)} = min{1+0 , 50+51} = 1 1 z Routing Tables: At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->y) to y on (z->y) cost to x y z from Distance Vectors: Infinite loop x 0 51 50 y 8 0 1 z 7 1 0 At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->y) to y on (z->y)
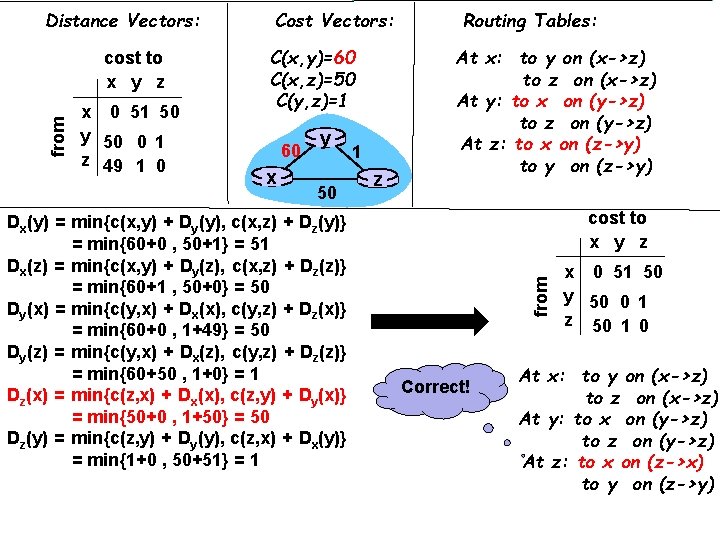
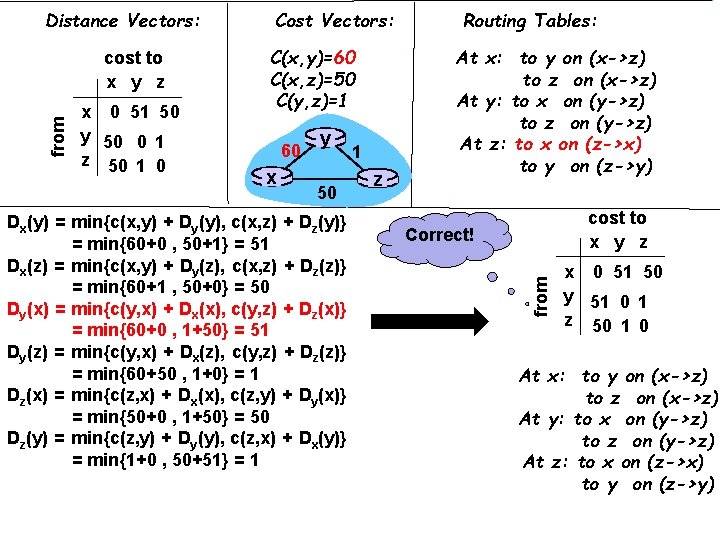
from cost to x y z x 0 51 50 y 50 0 1 z 49 1 0 Cost Vectors: C(x, y)=60 C(x, z)=50 C(y, z)=1 60 x y 50 Dx(y) = min{c(x, y) + Dy(y), c(x, z) + Dz(y)} = min{60+0 , 50+1} = 51 Dx(z) = min{c(x, y) + Dy(z), c(x, z) + Dz(z)} = min{60+1 , 50+0} = 50 Dy(x) = min{c(y, x) + Dx(x), c(y, z) + Dz(x)} = min{60+0 , 1+49} = 50 Dy(z) = min{c(y, x) + Dx(z), c(y, z) + Dz(z)} = min{60+50 , 1+0} = 1 Dz(x) = min{c(z, x) + Dx(x), c(z, y) + Dy(x)} = min{50+0 , 1+50} = 50 Dz(y) = min{c(z, y) + Dy(y), c(z, x) + Dx(y)} = min{1+0 , 50+51} = 1 1 z Routing Tables: At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->y) to y on (z->y) cost to x y z from Distance Vectors: Correct! x 0 51 50 y 50 0 1 z 50 1 0 At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->x) to y on (z->y)
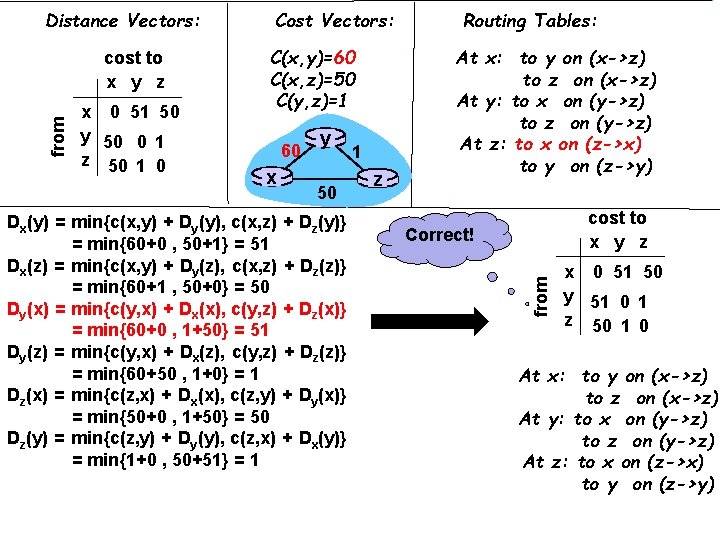
from cost to x y z x 0 51 50 y 50 0 1 z 50 1 0 Cost Vectors: C(x, y)=60 C(x, z)=50 C(y, z)=1 60 x y 50 Dx(y) = min{c(x, y) + Dy(y), c(x, z) + Dz(y)} = min{60+0 , 50+1} = 51 Dx(z) = min{c(x, y) + Dy(z), c(x, z) + Dz(z)} = min{60+1 , 50+0} = 50 Dy(x) = min{c(y, x) + Dx(x), c(y, z) + Dz(x)} = min{60+0 , 1+50} = 51 Dy(z) = min{c(y, x) + Dx(z), c(y, z) + Dz(z)} = min{60+50 , 1+0} = 1 Dz(x) = min{c(z, x) + Dx(x), c(z, y) + Dy(x)} = min{50+0 , 1+50} = 50 Dz(y) = min{c(z, y) + Dy(y), c(z, x) + Dx(y)} = min{1+0 , 50+51} = 1 1 z Routing Tables: At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->x) to y on (z->y) cost to x y z Correct! from Distance Vectors: x 0 51 50 y 51 0 1 z 50 1 0 At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->x) to y on (z->y)
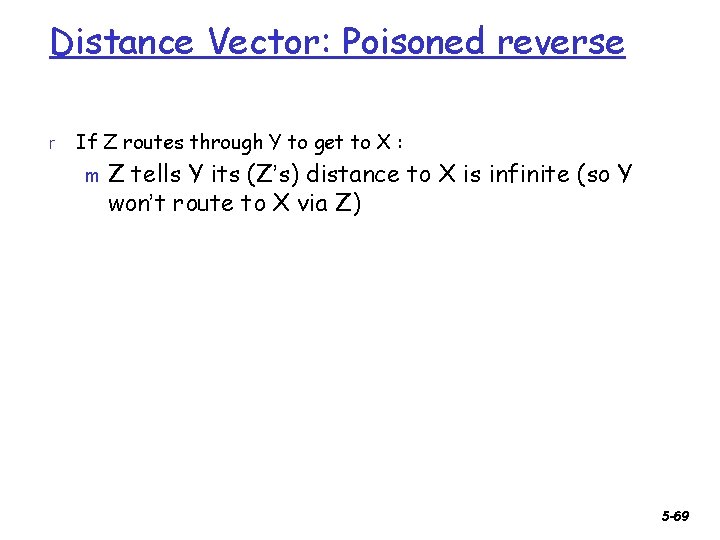
Distance Vector: Poisoned reverse r If Z routes through Y to get to X : m Z tells Y its (Z’s) distance to X is infinite (so Y won’t route to X via Z) 5 -69
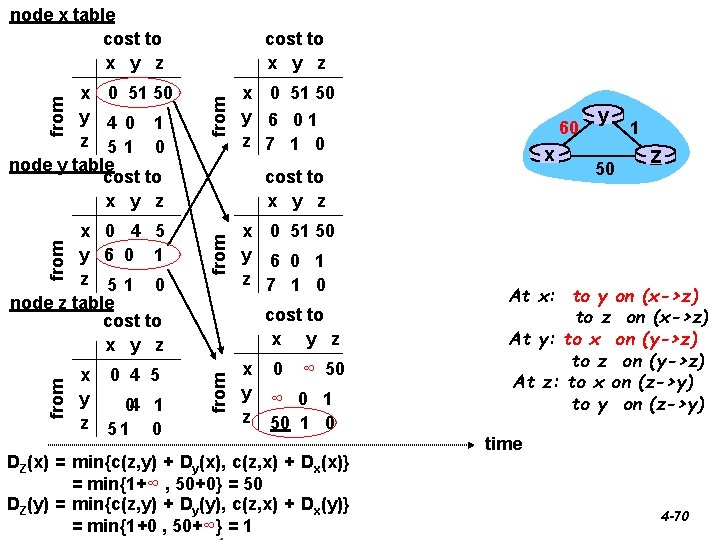
node x table cost to x y z from x 0 4 5 y 04 1 z 51 0 from x 0 4 5 y 6 0 1 z 51 0 node z table cost to x y z x 0 51 50 y 6 01 z 7 1 0 60 x cost to x y z x 0 51 50 y 6 0 1 z 7 1 0 cost to x y z from x 0 51 50 y 4 0 1 z 51 0 node y table cost to x y z 0 ∞ 50 ∞ 0 1 50 1 0 DZ(x) = min{c(z, y) + Dy(x), c(z, x) + Dx(x)} = min{1+∞ , 50+0} = 50 DZ(y) = min{c(z, y) + Dy(y), c(z, x) + Dx(y)} = min{1+0 , 50+∞} = 1 y 50 1 z At x: to y on (x->z) to z on (x->z) At y: to x on (y->z) to z on (y->z) At z: to x on (z->y) to y on (z->y) time 4 -70
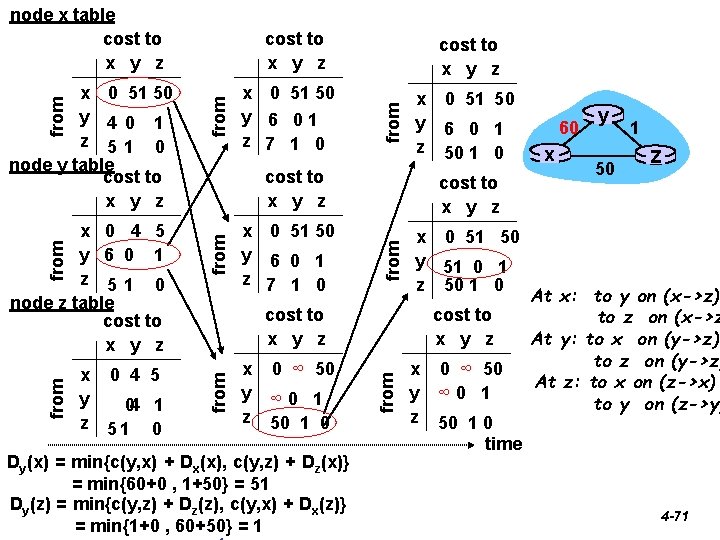
node x table cost to x y z x 0 4 5 y 04 1 z 51 0 from x y z from x 0 51 50 y 6 0 1 z 7 1 0 0 ∞ 50 ∞ 0 1 50 1 0 Dy(x) = min{c(y, x) + Dx(x), c(y, z) + Dz(x)} = min{60+0 , 1+50} = 51 Dy(z) = min{c(y, z) + Dz(z), c(y, x) + Dx(z)} = min{1+0 , 60+50} = 1 6 0 1 50 1 0 x 0 51 50 y 51 0 1 z 50 1 0 cost to x y z 0 51 50 cost to x y z from x 0 4 5 y 6 0 1 z 51 0 node z table cost to x y z x 0 51 50 y 6 01 z 7 1 0 cost to x y z from x 0 51 50 y 4 0 1 z 51 0 node y table cost to x y z 0 ∞ 50 ∞ 0 1 50 1 0 time 60 x y 50 1 z At x: to y on (x->z) to z on (x->z At y: to x on (y->z) to z on (y->z) At z: to x on (z->x) to y on (z->y) 4 -71
Distance Vector: Poisoned reverse r If Z routes through Y to get to X : Z tells Y its (Z’s) distance to X is infinite (so Y won’t route to X via Z) r Will this completely solve count to infinity problem? m NO! What about longer loops? 5 -72
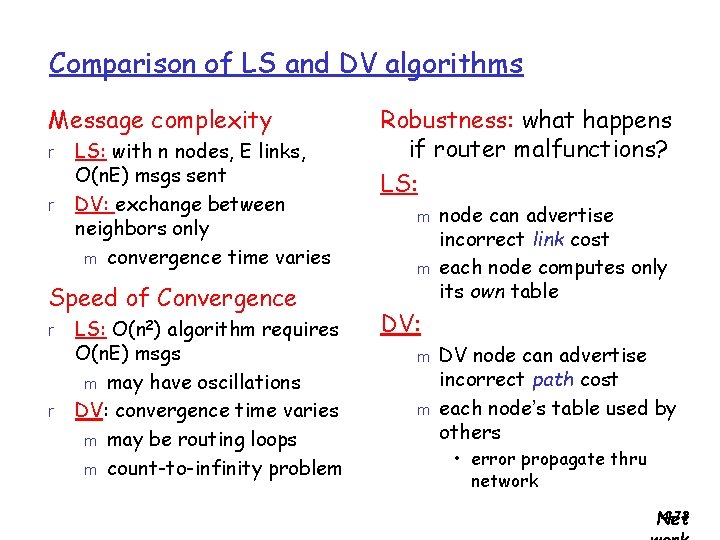
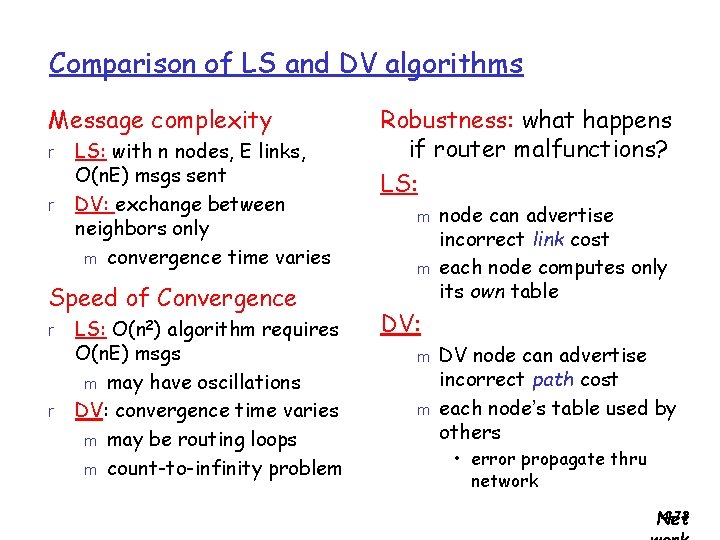
Comparison of LS and DV algorithms Message complexity r r LS: with n nodes, E links, O(n. E) msgs sent DV: exchange between neighbors only m convergence time varies Speed of Convergence r r LS: O(n 2) algorithm requires O(n. E) msgs m may have oscillations DV: convergence time varies m may be routing loops m count-to-infinity problem Robustness: what happens if router malfunctions? LS: m m node can advertise incorrect link cost each node computes only its own table DV: m m DV node can advertise incorrect path cost each node’s table used by others • error propagate thru network 4 -73 Net
Chapter 4: Network Layer r 4. 5 Routing algorithms m Link state m Distance Vector m Hierarchical routing r 4. 6 Routing in the Internet m m RIP OSPF Netw 4 -74 ork
Chapter 4: Network Layer r 4. 5 Routing algorithms m Link state m Distance Vector m Hierarchical routing r 4. 6 Routing in the Internet m m RIP OSPF Netw 4 -75 ork
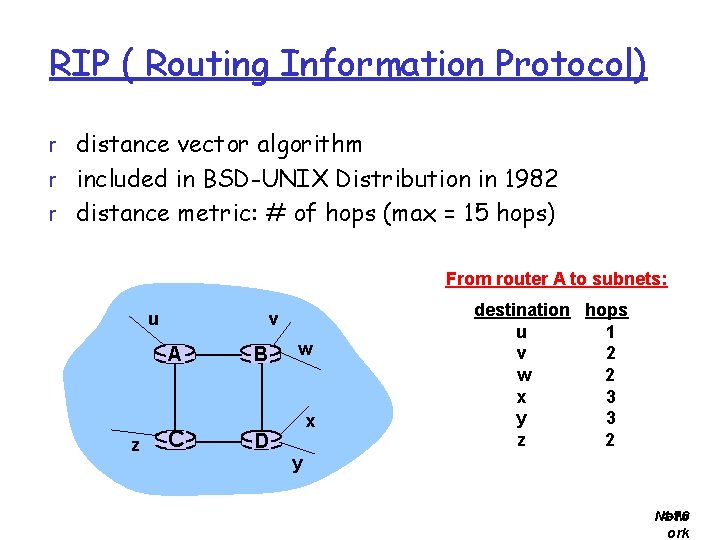
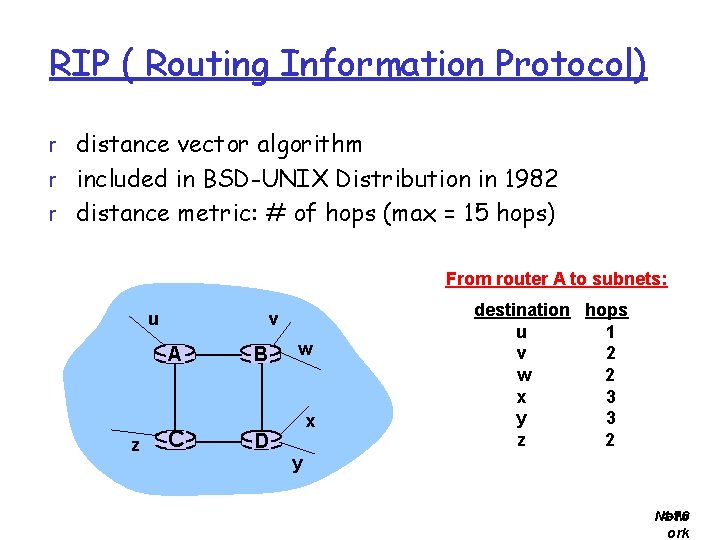
RIP ( Routing Information Protocol) r distance vector algorithm r included in BSD-UNIX Distribution in 1982 r distance metric: # of hops (max = 15 hops) From router A to subnets: u v A z C B w x D destination hops u 1 v 2 w 2 x 3 y 3 z 2 y Netw 4 -76 ork
RIP advertisements r distance vectors: exchanged among neighbors every 30 sec via Response Message (also called advertisement) r each advertisement: list of up to 25 destination subnets within AS Netw 4 -77 ork
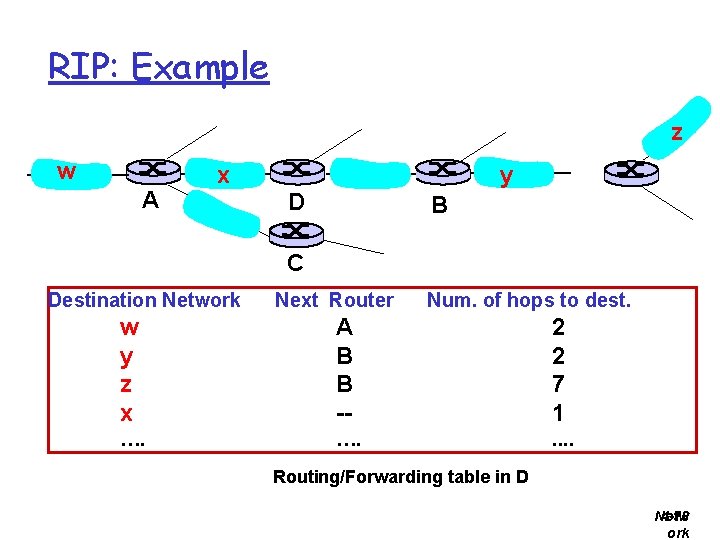
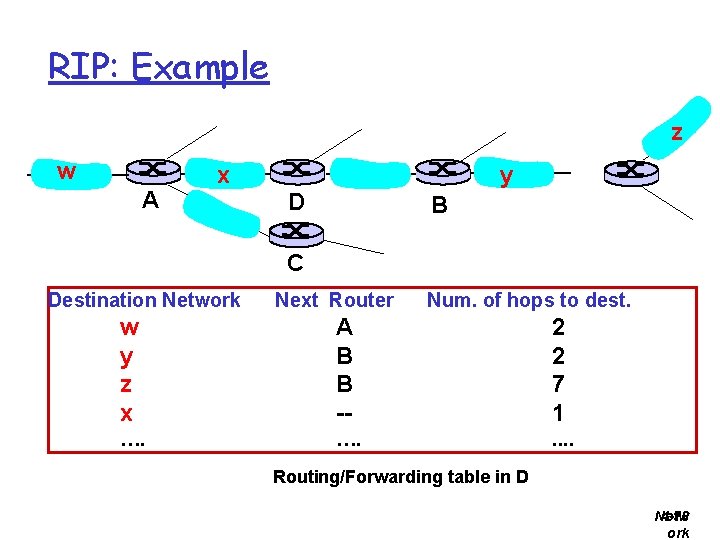
RIP: Example z w A x y D B C Destination Network Next Router Num. of hops to dest. w y z x A B B -- 2 2 7 1 …. . . Routing/Forwarding table in D Netw 4 -78 ork
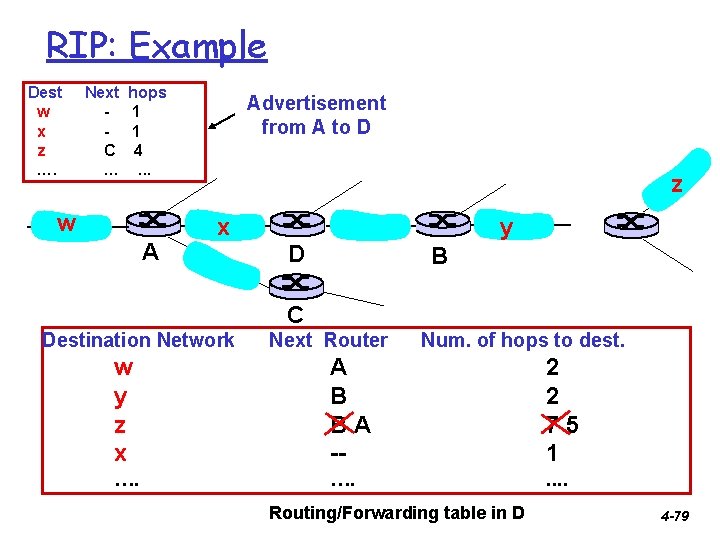
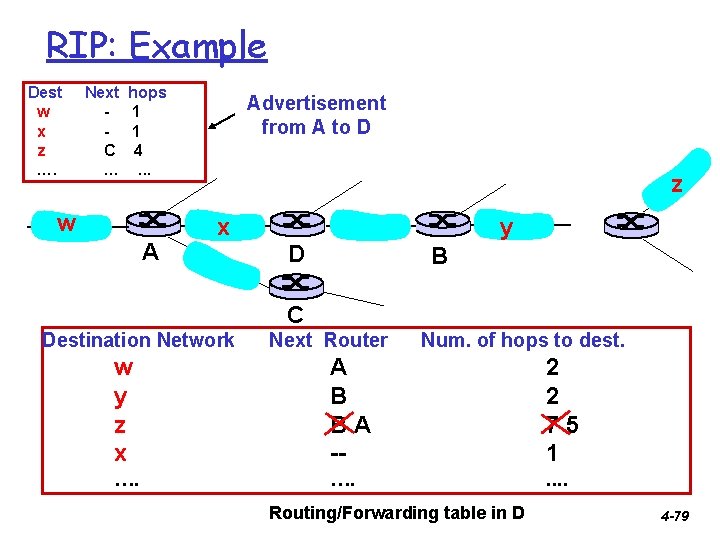
RIP: Example Dest w x z …. Next C … hops 1 1 4. . . w A Advertisement from A to D z x y D B C Destination Network Next Router Num. of hops to dest. w y z x A B BA -- 2 2 75 1 …. . . Routing/Forwarding table in D 4 -79
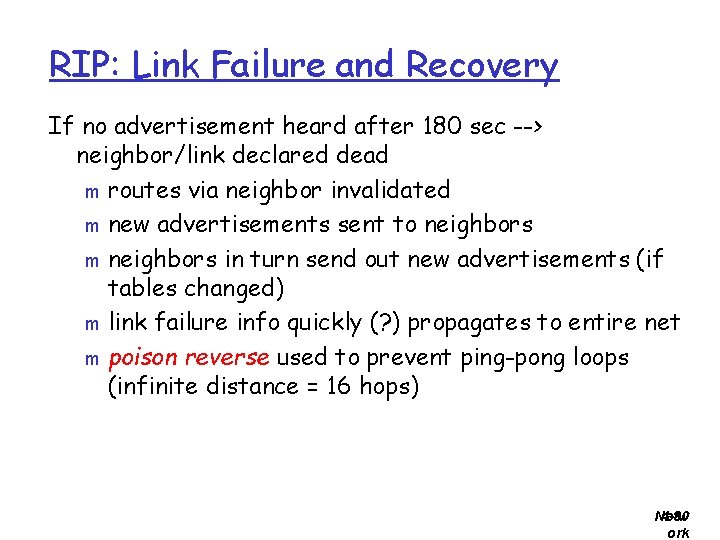
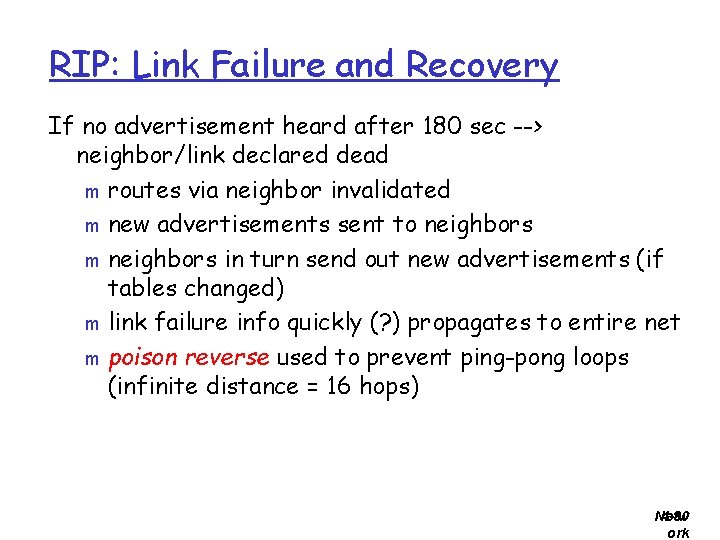
RIP: Link Failure and Recovery If no advertisement heard after 180 sec --> neighbor/link declared dead m routes via neighbor invalidated m new advertisements sent to neighbors m neighbors in turn send out new advertisements (if tables changed) m link failure info quickly (? ) propagates to entire net m poison reverse used to prevent ping-pong loops (infinite distance = 16 hops) Netw 4 -80 ork
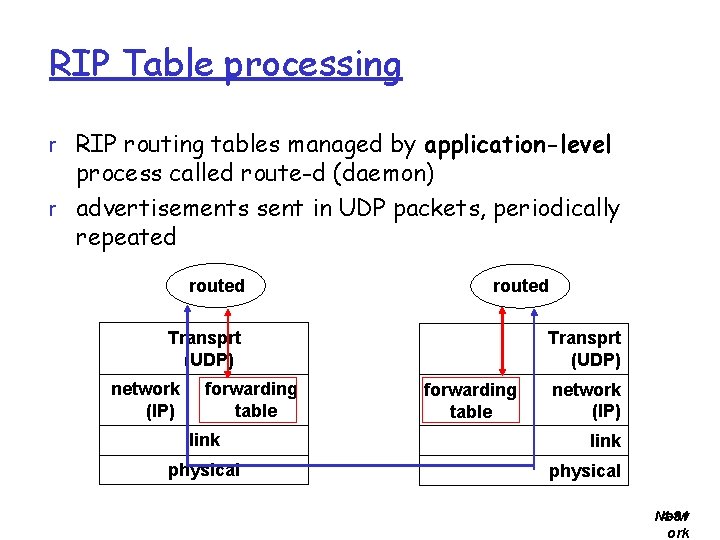
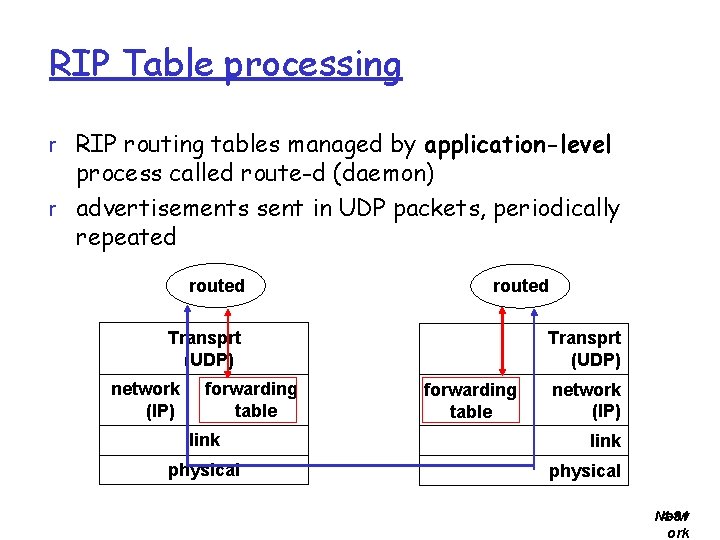
RIP Table processing r RIP routing tables managed by application-level process called route-d (daemon) r advertisements sent in UDP packets, periodically repeated routed Transprt (UDP) network (IP) forwarding table link physical Transprt (UDP) forwarding table network (IP) link physical Netw 4 -81 ork
Chapter 4: Network Layer r 4. 5 Routing algorithms m Link state m Distance Vector m Hierarchical routing r 4. 6 Routing in the Internet m m m RIP OSPF BGP r 4. 7 Broadcast and multicast routing Netw 4 -82 ork
OSPF (Open Shortest Path First) r “open”: publicly available r uses Link State algorithm m LS packet dissemination m topology map at each node m route computation using Dijkstra’s algorithm r OSPF advertisement carries one entry per neighbor router r advertisements disseminated to entire AS (via flooding) m carried in OSPF messages directly over IP (rather than TCP or UDP Netw 4 -83 ork
OSPF “advanced” features (not in RIP) r security: all OSPF messages authenticated (to r r prevent malicious intrusion) multiple same-cost paths allowed (only one path in RIP) For each link, multiple cost metrics for different TOS (e. g. , satellite link cost set “low” for best effort; high for real time) integrated uni- and multicast support: m Multicast OSPF (MOSPF) uses same topology data base as OSPF hierarchical OSPF in large domains. Netw 4 -84 ork
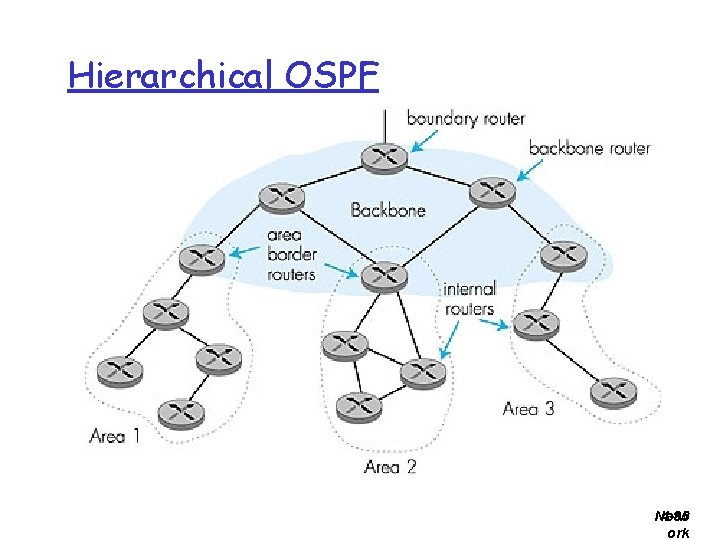
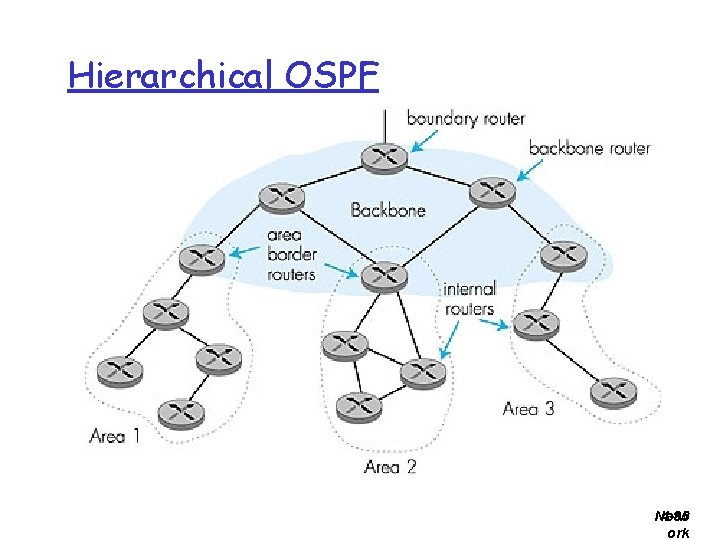
Hierarchical OSPF Netw 4 -85 ork
Hierarchical OSPF r two-level hierarchy: local area, backbone. Link-state advertisements only in area m each nodes has detailed area topology; only know direction (shortest path) to nets in other areas. r area border routers: “summarize” distances to nets in own area, advertise to other Area Border routers. r backbone routers: run OSPF routing limited to backbone. r boundary routers: connect to other AS’s. m Netw 4 -86 ork