Detecting DGA Botnets Using DNS Traffic Han Zhang
Detecting DGA Botnets Using DNS Traffic Han Zhang (Salesforce) Christos Papadopoulos (Colorado State University) Calvin Ardi (University of Southern California/ISI) John Heidemann (University of Southern California/ISI)
Outline • Introduction • Why Use DNS for Bot Detection • Bot. Digger Methodology • Bot. Digger Deployment • Discussion • Future Work 1
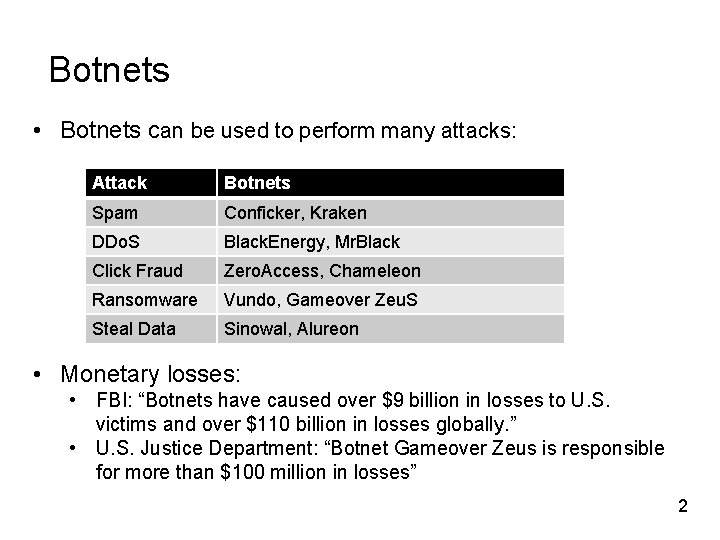
Botnets • Botnets can be used to perform many attacks: Attack Botnets Spam Conficker, Kraken DDo. S Black. Energy, Mr. Black Click Fraud Zero. Access, Chameleon Ransomware Vundo, Gameover Zeu. S Steal Data Sinowal, Alureon • Monetary losses: • FBI: “Botnets have caused over $9 billion in losses to U. S. victims and over $110 billion in losses globally. ” • U. S. Justice Department: “Botnet Gameover Zeus is responsible for more than $100 million in losses” 2
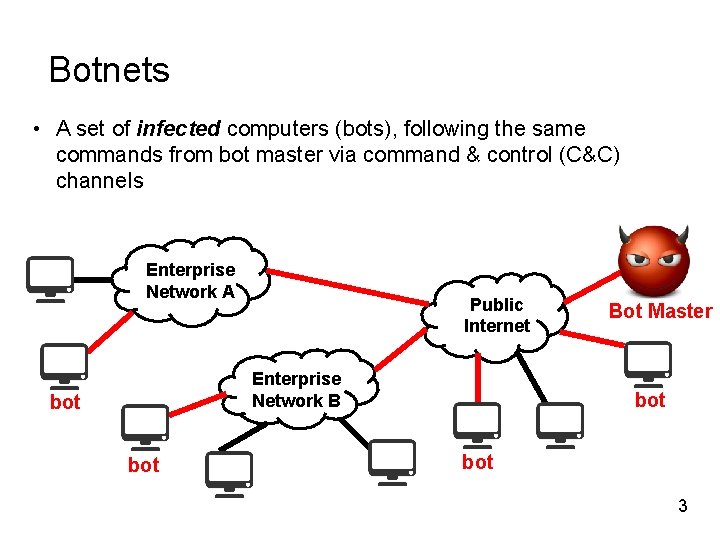
Botnets • A set of infected computers (bots), following the same commands from bot master via command & control (C&C) channels Enterprise Network A Public Internet Enterprise Network B bot Bot Master bot 3
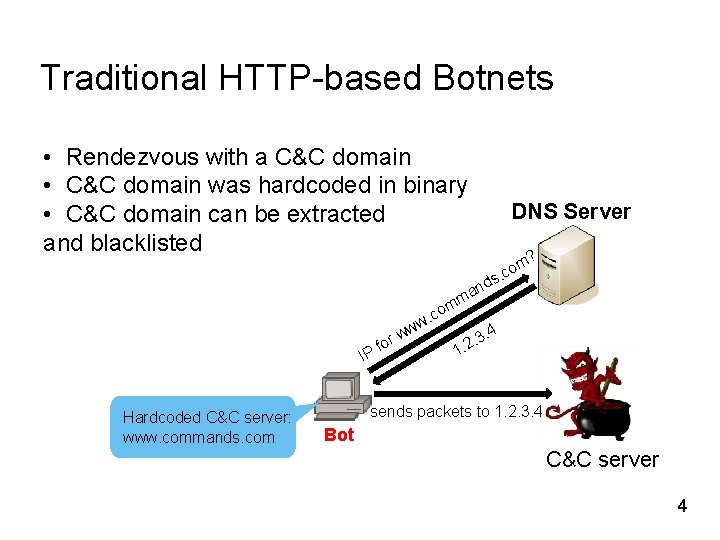
Traditional HTTP-based Botnets • Rendezvous with a C&C domain • C&C domain was hardcoded in binary • C&C domain can be extracted and blacklisted DNS Server ? ds n ma m. co m w IP Hardcoded C&C server: www. commands. com w for co w. . 4 . 3 2. 1 sends packets to 1. 2. 3. 4 Bot C&C server 4
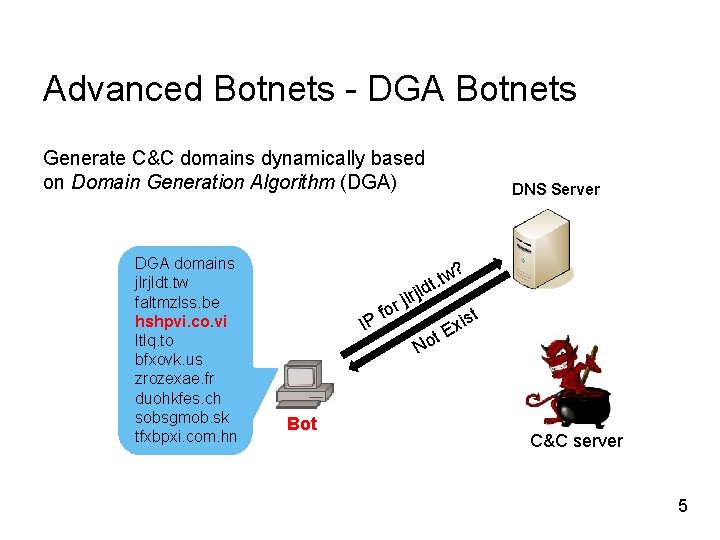
Advanced Botnets - DGA Botnets Generate C&C domains dynamically based on Domain Generation Algorithm (DGA) DGA domains jlrjldt. tw faltmzlss. be hshpvi. co. vi ltlq. to bfxovk. us zrozexae. fr duohkfes. ch sobsgmob. sk tfxbpxi. com. hn DNS Server ? tw dt. rjl jl or f IP Bot t No t is Ex C&C server 5
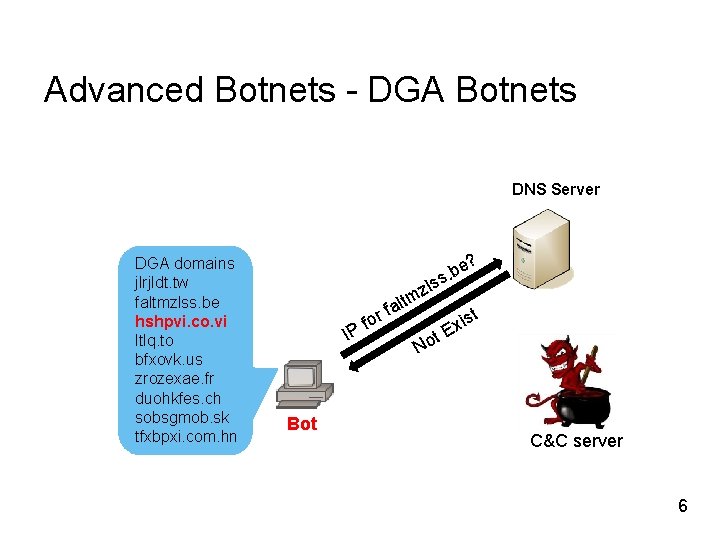
Advanced Botnets - DGA Botnets DNS Server DGA domains jlrjldt. tw faltmzlss. be hshpvi. co. vi ltlq. to bfxovk. us zrozexae. fr duohkfes. ch sobsgmob. sk tfxbpxi. com. hn e? b. s zls m o Pf lt a f r I Bot t No t is Ex C&C server 6
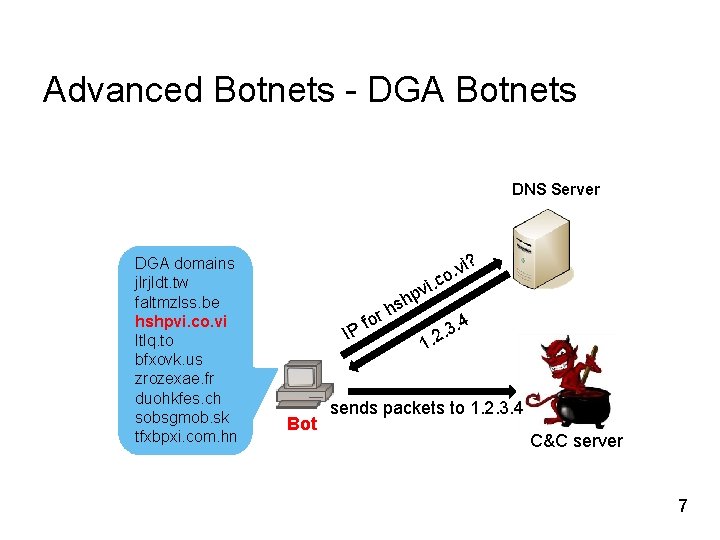
Advanced Botnets - DGA Botnets DNS Server DGA domains jlrjldt. tw faltmzlss. be hshpvi. co. vi ltlq. to bfxovk. us zrozexae. fr duohkfes. ch sobsgmob. sk tfxbpxi. com. hn . v o c i. i? pv or f IP Bot h hs 3. 4. 2 1. sends packets to 1. 2. 3. 4 C&C server 7
Using DNS to Detect DGA Botnets 8
Why DNS? • DGA bots have to query IPs for the C&C domains • DGA bots have unique DNS traffic pattern • Amount of DNS traffic is relatively small, enabling sophisticated analysis compared to deep packet analysis • Bots can be detected immediately after they are infected 9
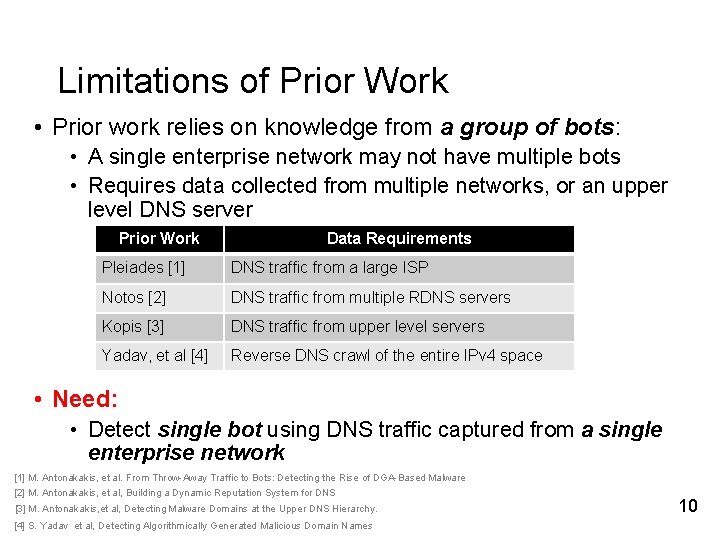
Limitations of Prior Work • Prior work relies on knowledge from a group of bots: • A single enterprise network may not have multiple bots • Requires data collected from multiple networks, or an upper level DNS server Prior Work Data Requirements Pleiades [1] DNS traffic from a large ISP Notos [2] DNS traffic from multiple RDNS servers Kopis [3] DNS traffic from upper level servers Yadav, et al [4] Reverse DNS crawl of the entire IPv 4 space • Need: • Detect single bot using DNS traffic captured from a single enterprise network [1] M. Antonakakis, et al. From Throw-Away Traffic to Bots: Detecting the Rise of DGA-Based Malware [2] M. Antonakakis, et al, Building a Dynamic Reputation System for DNS [3] M. Antonakakis, et al, Detecting Malware Domains at the Upper DNS Hierarchy. [4] S. Yadav et al, Detecting Algorithmically Generated Malicious Domain Names 10
Methodology 11
Ideas behind Bot. Digger • DGA bots have unique DNS traffic pattern • Quantity: • Query a large number of NXDomains • Temporal: • Different rates of querying suspicious NXDomains • Linguistic: • DGA NXDomains and C&C domains have similar linguistic attributes 12
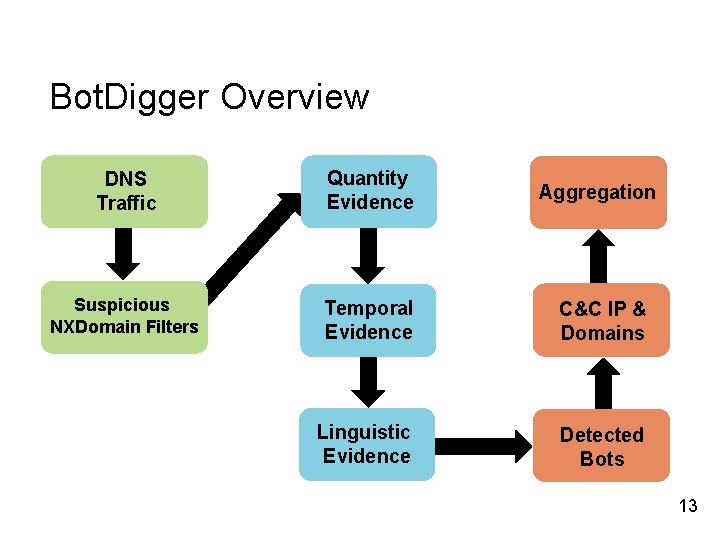
Bot. Digger Overview DNS Traffic Quantity Evidence Aggregation Suspicious NXDomain Filters Temporal Evidence C&C IP & Domains Linguistic Evidence Detected Bots 13
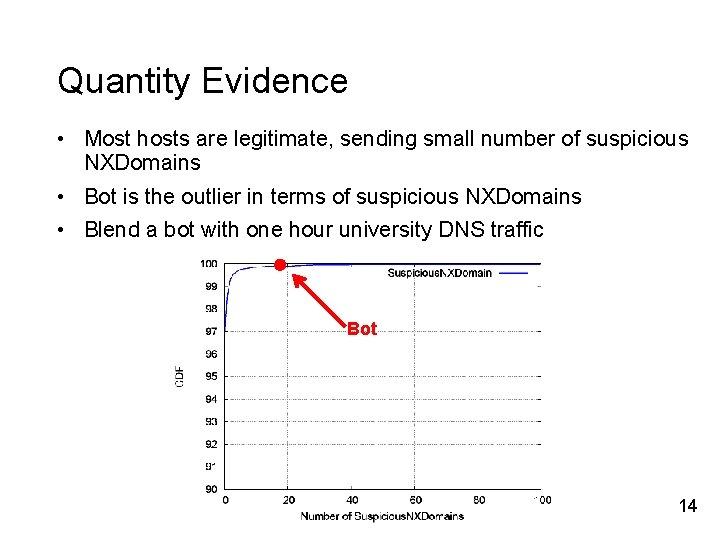
Quantity Evidence • Most hosts are legitimate, sending small number of suspicious NXDomains • Bot is the outlier in terms of suspicious NXDomains • Blend a bot with one hour university DNS traffic Bot 14
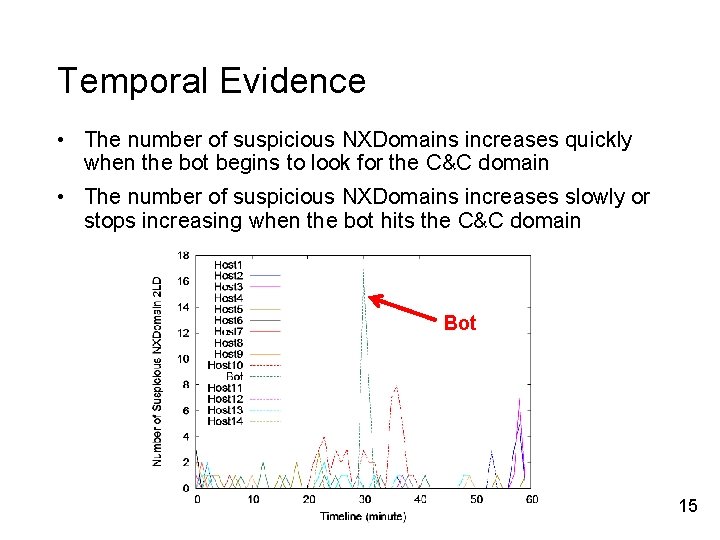
Temporal Evidence • The number of suspicious NXDomains increases quickly when the bot begins to look for the C&C domain • The number of suspicious NXDomains increases slowly or stops increasing when the bot hits the C&C domain Bot 15
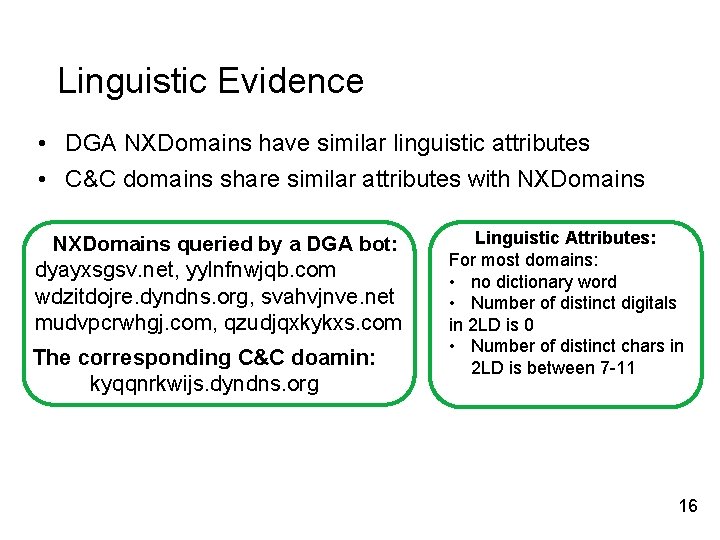
Linguistic Evidence • DGA NXDomains have similar linguistic attributes • C&C domains share similar attributes with NXDomains queried by a DGA bot: dyayxsgsv. net, yylnfnwjqb. com wdzitdojre. dyndns. org, svahvjnve. net mudvpcrwhgj. com, qzudjqxkykxs. com The corresponding C&C doamin: kyqqnrkwijs. dyndns. org Linguistic Attributes: For most domains: • no dictionary word • Number of distinct digitals in 2 LD is 0 • Number of distinct chars in 2 LD is between 7 -11 16
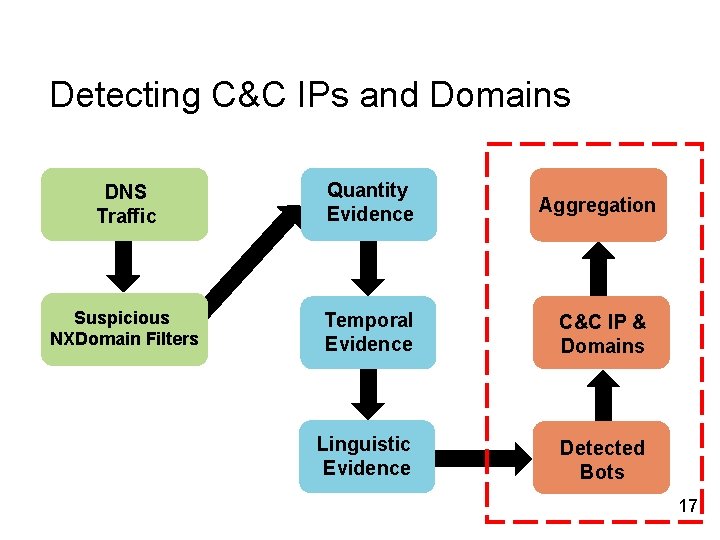
Detecting C&C IPs and Domains DNS Traffic Quantity Evidence Aggregation Suspicious NXDomain Filters Temporal Evidence C&C IP & Domains Linguistic Evidence Detected Bots 17
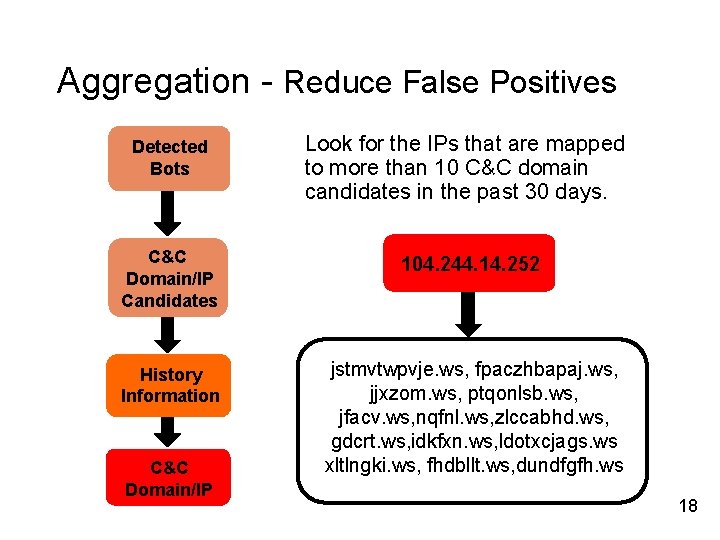
Aggregation - Reduce False Positives Detected Bots Look for the IPs that are mapped to more than 10 C&C domain candidates in the past 30 days. C&C Domain/IP Candidates 104. 244. 14. 252 History Information jstmvtwpvje. ws, fpaczhbapaj. ws, jjxzom. ws, ptqonlsb. ws, jfacv. ws, nqfnl. ws, zlccabhd. ws, gdcrt. ws, idkfxn. ws, ldotxcjags. ws xltlngki. ws, fhdbllt. ws, dundfgfh. ws C&C Domain/IP 18
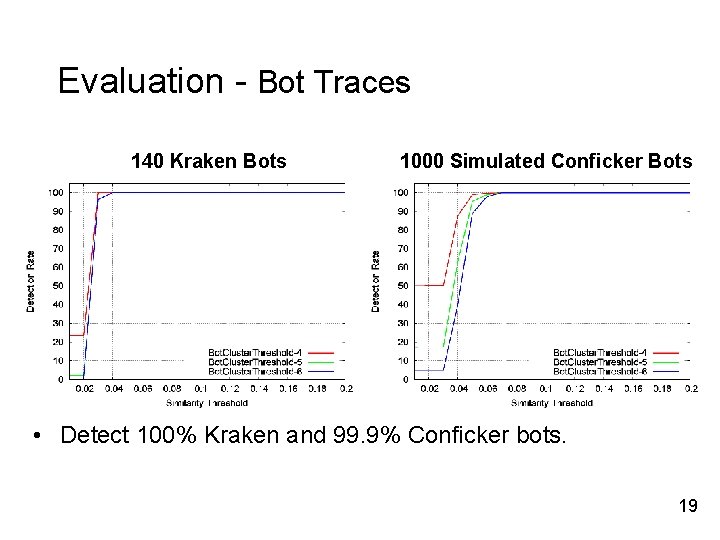
Evaluation - Bot Traces 140 Kraken Bots 1000 Simulated Conficker Bots • Detect 100% Kraken and 99. 9% Conficker bots. 19
Evaluation - University Trace • Dataset: one week of campus DNS traffic • Results: • 33 out of 20682 (0. 16%) hosts labeled as bot candidates • Validation: • Check C&C domain candidates and IP addresses through Virus. Total and Trusted. Source • 22 out of 33 bot candidates labeled suspicious • False positives are at most 11 hosts 20
Bot. Digger Deployment 21
Bot. Digger Deployment • Deployed at Colorado State University, USC/ISI, LANL, and Northrop Grumman • Open source on Git. Hub • https: //github. com/hanzhang 0116/Bot. Digger • Modes of Operation • Real-time detection • Offline-line detection • Deployment is easy, Bot. Digger only needs DNS traffic from a single network 22
Deployment at Colorado State University • Deployed at CSU at December, 2016 • Operated by Net. Sec group at CSU • CSU network has more than 20, 000 users • Detected 3630 C&C domains 23
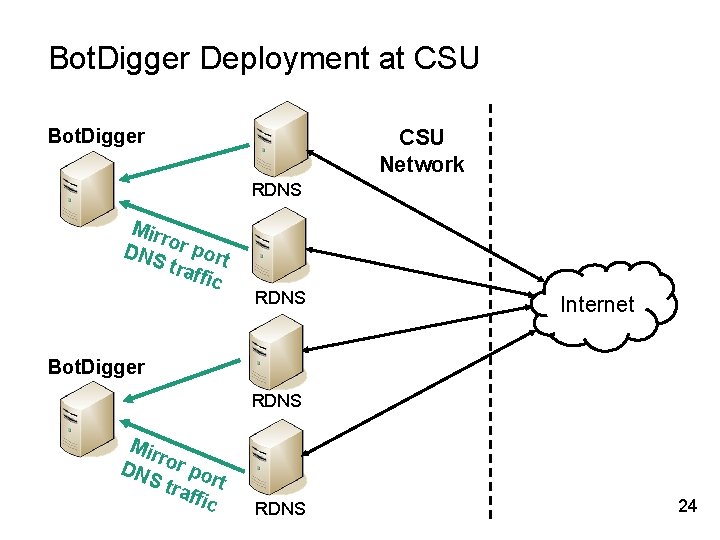
Bot. Digger Deployment at CSU Bot. Digger CSU Network RDNS Mirr o DNS r port traf fic RDNS Internet Bot. Digger RDNS Mir r DN or po S tr r affi t c RDNS 24
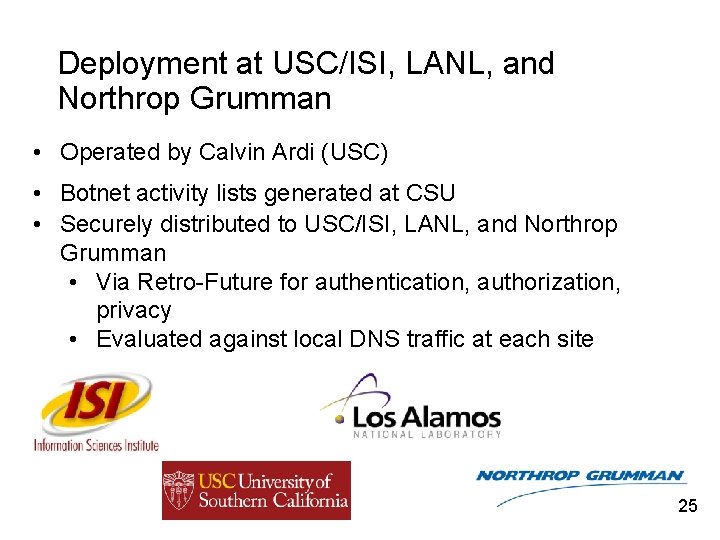
Deployment at USC/ISI, LANL, and Northrop Grumman • Operated by Calvin Ardi (USC) • Botnet activity lists generated at CSU • Securely distributed to USC/ISI, LANL, and Northrop Grumman • Via Retro-Future for authentication, authorization, privacy • Evaluated against local DNS traffic at each site 25
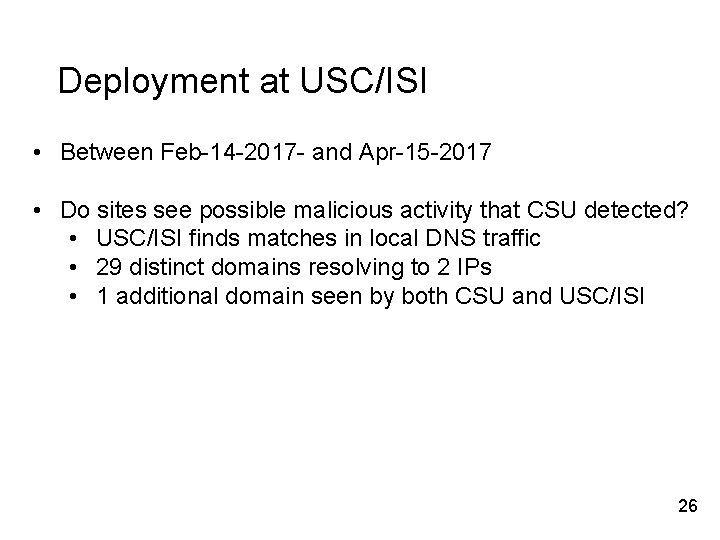
Deployment at USC/ISI • Between Feb-14 -2017 - and Apr-15 -2017 • Do sites see possible malicious activity that CSU detected? • USC/ISI finds matches in local DNS traffic • 29 distinct domains resolving to 2 IPs • 1 additional domain seen by both CSU and USC/ISI 26

Discussion 27
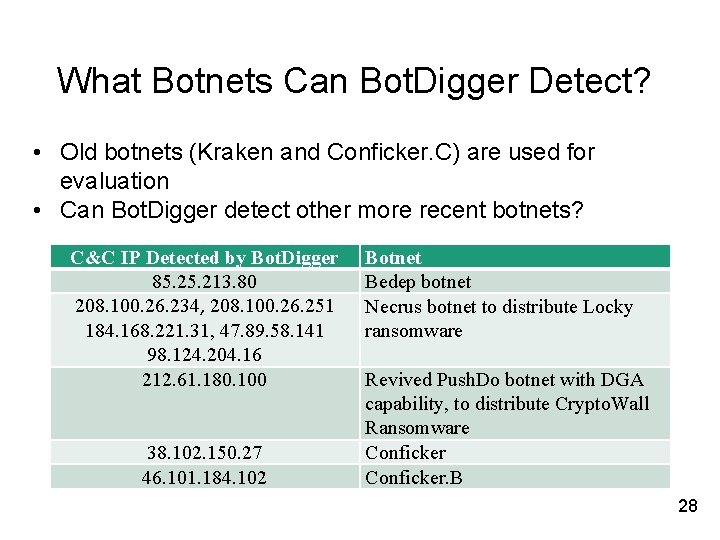
What Botnets Can Bot. Digger Detect? • Old botnets (Kraken and Conficker. C) are used for evaluation • Can Bot. Digger detect other more recent botnets? C&C IP Detected by Bot. Digger 85. 213. 80 208. 100. 26. 234, 208. 100. 26. 251 184. 168. 221. 31, 47. 89. 58. 141 98. 124. 204. 16 212. 61. 180. 100 38. 102. 150. 27 46. 101. 184. 102 Botnet Bedep botnet Necrus botnet to distribute Locky ransomware Revived Push. Do botnet with DGA capability, to distribute Crypto. Wall Ransomware Conficker. B 28
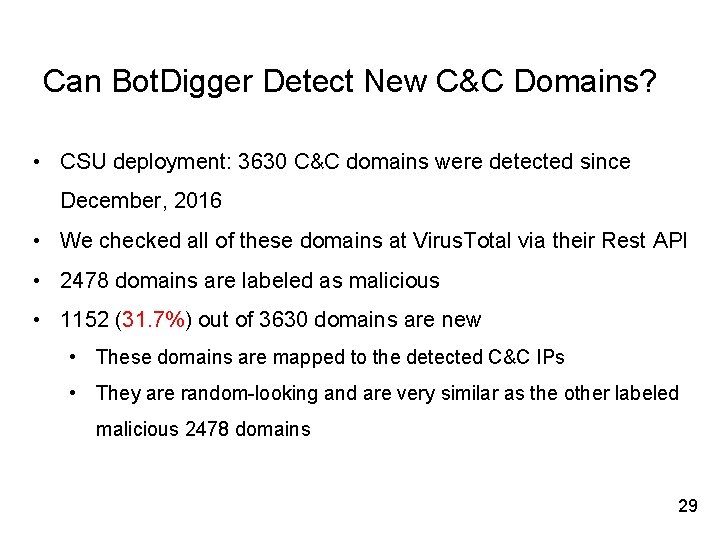
Can Bot. Digger Detect New C&C Domains? • CSU deployment: 3630 C&C domains were detected since December, 2016 • We checked all of these domains at Virus. Total via their Rest API • 2478 domains are labeled as malicious • 1152 (31. 7%) out of 3630 domains are new • These domains are mapped to the detected C&C IPs • They are random-looking and are very similar as the other labeled malicious 2478 domains 29
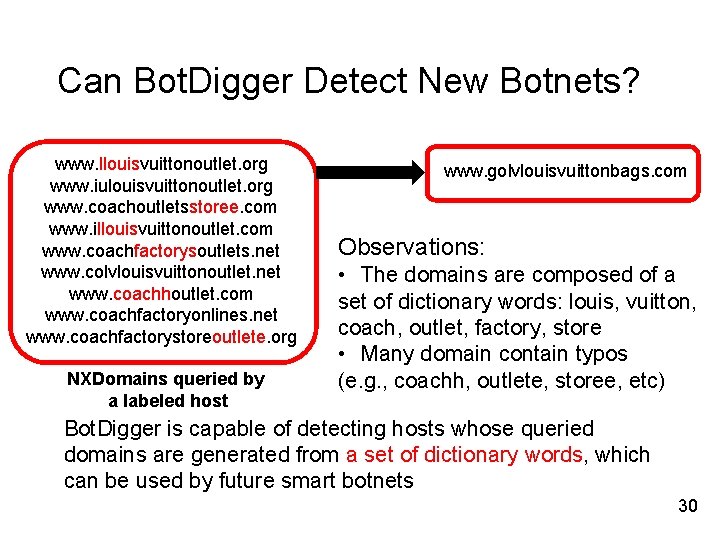
Can Bot. Digger Detect New Botnets? www. llouisvuittonoutlet. org www. iulouisvuittonoutlet. org www. coachoutletsstoree. com www. illouisvuittonoutlet. com www. coachfactorysoutlets. net www. colvlouisvuittonoutlet. net www. coachhoutlet. com www. coachfactoryonlines. net www. coachfactorystoreoutlete. org NXDomains queried by a labeled host www. golvlouisvuittonbags. com Observations: • The domains are composed of a set of dictionary words: louis, vuitton, coach, outlet, factory, store • Many domain contain typos (e. g. , coachh, outlete, storee, etc) Bot. Digger is capable of detecting hosts whose queried domains are generated from a set of dictionary words, which can be used by future smart botnets 30
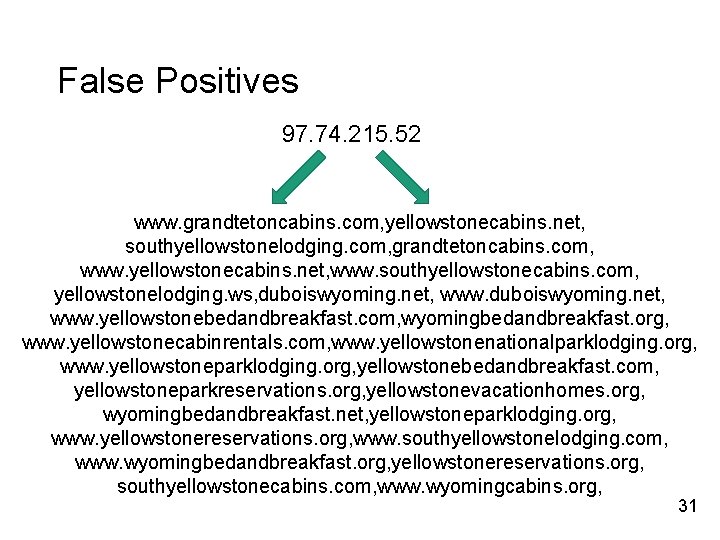
False Positives 97. 74. 215. 52 www. grandtetoncabins. com, yellowstonecabins. net, southyellowstonelodging. com, grandtetoncabins. com, www. yellowstonecabins. net, www. southyellowstonecabins. com, yellowstonelodging. ws, duboiswyoming. net, www. yellowstonebedandbreakfast. com, wyomingbedandbreakfast. org, www. yellowstonecabinrentals. com, www. yellowstonenationalparklodging. org, www. yellowstoneparklodging. org, yellowstonebedandbreakfast. com, yellowstoneparkreservations. org, yellowstonevacationhomes. org, wyomingbedandbreakfast. net, yellowstoneparklodging. org, www. yellowstonereservations. org, www. southyellowstonelodging. com, www. wyomingbedandbreakfast. org, yellowstonereservations. org, southyellowstonecabins. com, www. wyomingcabins. org, 31
Future Work • Reduce false positives • Deploy Bot. Digger at more enterprises and universities • Continue sharing the bot lists • Build a platform for information sharing (e. g. , C&C domains and IPs) • Research and Education Networking Information Sharing and Analysis Center (REN-ISAC) • Support more formats (e. g. , dns. log) 32
Bot. Digger is available at Git. Hub: https: //github. com/hanzhang 0116/Bot. Digger Sharing bot lists captured from multiple networks: hzhang@salesforce. com calvin@isi. edu Thanks 33
- Slides: 34