ACCESS CONTROL LIST 2 nd semester 1436 1437
- Slides: 21
ACCESS CONTROL LIST 2 nd semester 1436 -1437
OUTLINE What is an ACL? Purpose of ACLs Router and ACL Packet Filtering Inbound and Outbound ACLs Standard and Extended ACLs ACL Placement
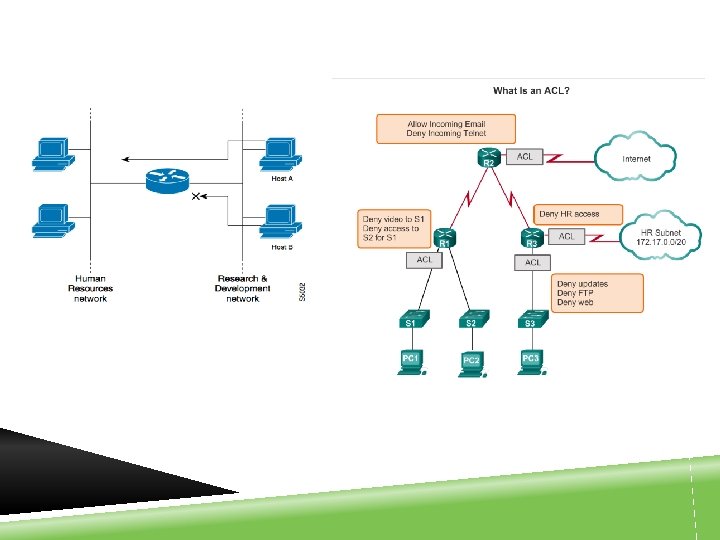
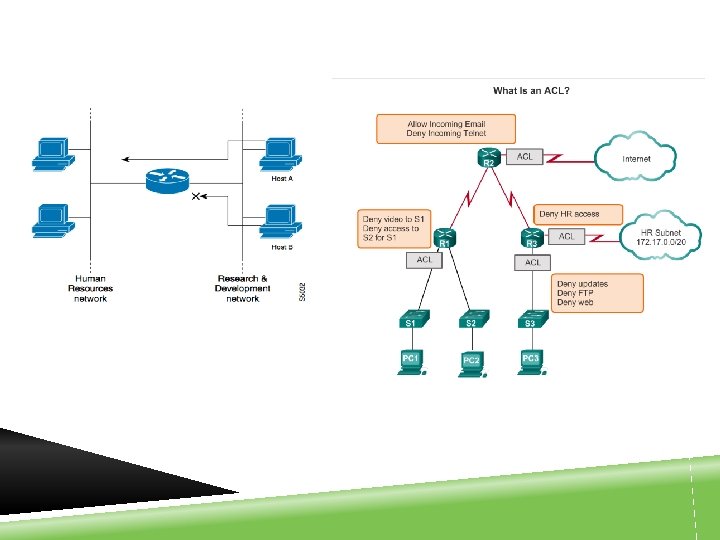
WHAT IS AN ACL? Access Control lists (ACL) is is a series of commands that enable a router to filter network traffic based on information found in the packets. Filter permit specific traffic / stop specific traffic a router forwards / drops packets based on addresses or upper-layer protocols (type of traffic) ACLs provide a powerful way to control traffic into and out of a network.
WHAT IS AN ACL? In addition to either permitting or denying traffic, ACLs can be used for selecting types of traffic to be analyzed or processed in other ways. For example, ACLs can be used to classify traffic to enable priority processing. The most important reason to configure ACLs is to provide security for a network.
PURPOSE OF ACLS ACLs perform the following tasks: Provide a basic level of security for network access. Screen hosts to permit or deny access to network services Filter traffic based on traffic type. Increase network performance by limiting some network traffic Provide traffic flow control.
ROUTER AND ACL By default, a router does not have ACLs configured. Traffic that enters the router is routed solely based on information within the routing table. However, when an ACL is applied to an interface, the router performs the additional task of evaluating all network packets as they pass through the interface to determine if the packet can be forwarded.
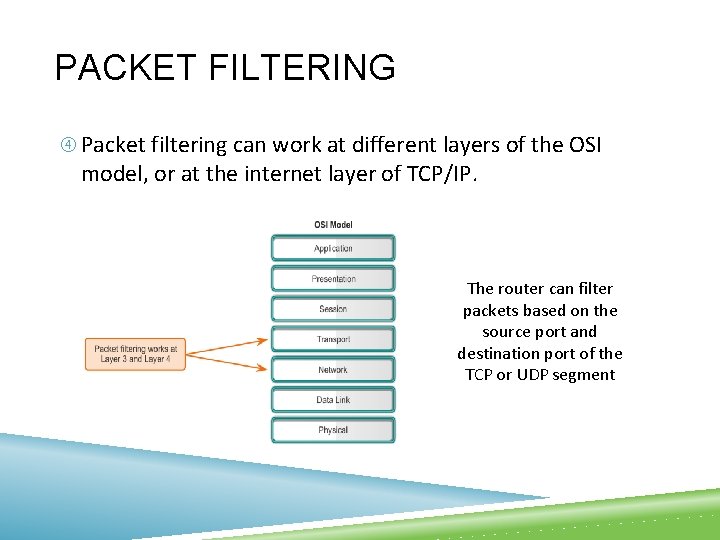
PACKET FILTERING Packet filtering, sometimes called static packet filtering, controls access to a network by analyzing the incoming and outgoing packets and passing or dropping them based on given criteria, such as the source IP address, destination IP addresses, and the protocol carried within the packet. A router acts as a packet filter when it forwards or denies packets according to filtering rules.
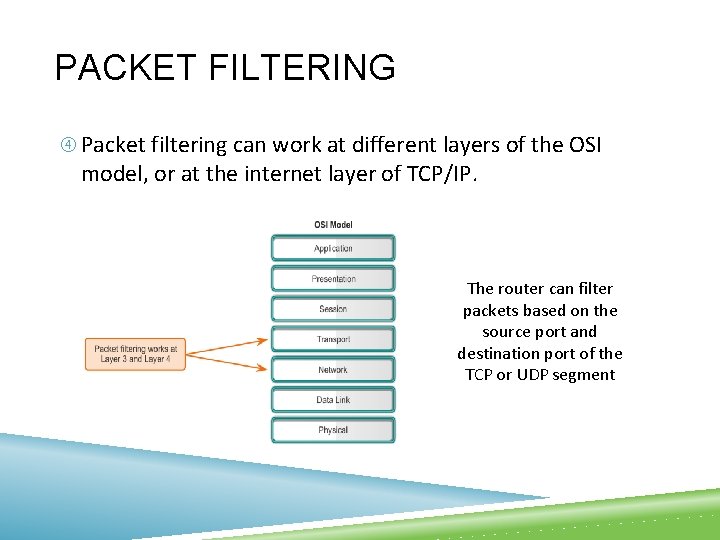
PACKET FILTERING Packet filtering can work at different layers of the OSI model, or at the internet layer of TCP/IP. The router can filter packets based on the source port and destination port of the TCP or UDP segment
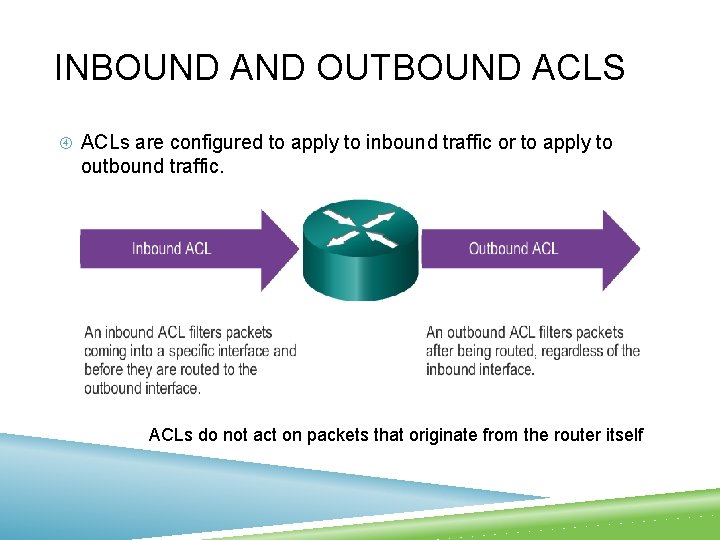
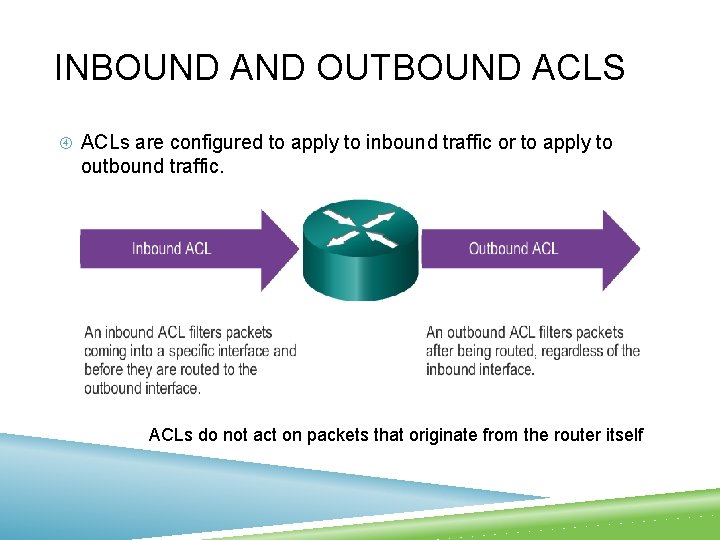
INBOUND AND OUTBOUND ACLS ACLs are configured to apply to inbound traffic or to apply to outbound traffic. ACLs do not act on packets that originate from the router itself
INBOUND ACLS Incoming packets are processed before they are routed to the outbound interface. An inbound ACL is efficient because it saves the overhead of routing lookups if the packet is discarded. If the packet is permitted by the tests, it is then processed for routing. Inbound ACLs are best used to filter packets when the network attached to an inbound interface is the only source of the packets needed to be examined.
OUTBOUND ACLS Incoming packets are routed to the outbound interface, and then they are processed through the outbound ACL. Outbound ACLs are best used when the same filter will be applied to packets coming from multiple inbound interfaces before exiting the same outbound interface.
STANDARD AND EXTENDED ACLS The two types of ACLs are standard and extended. Standard ACLs can be used to permits or denies packets based on source IP address. The destination of the packet and the ports involved are not evaluated.
STANDARD AND EXTENDED ACLS Extended ACLs filter packets based on several attributes: Protocol type Source IP address Destination IP address Source TCP or UDP ports Destination TCP or UDP ports Optional protocol type information for finer control
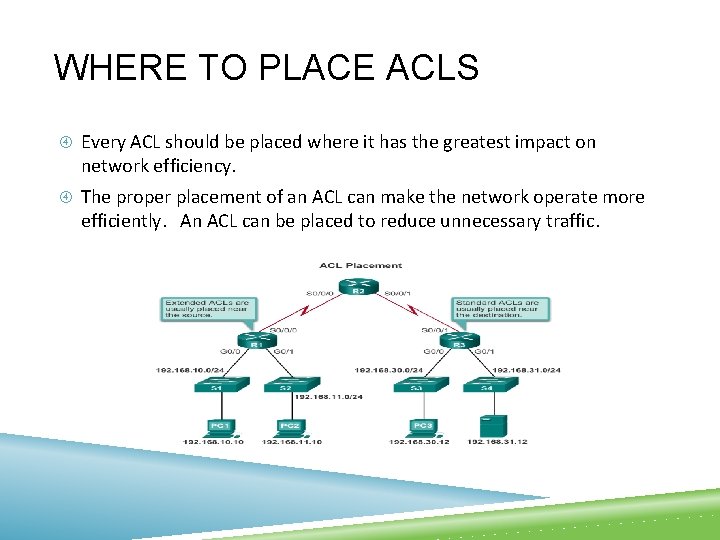
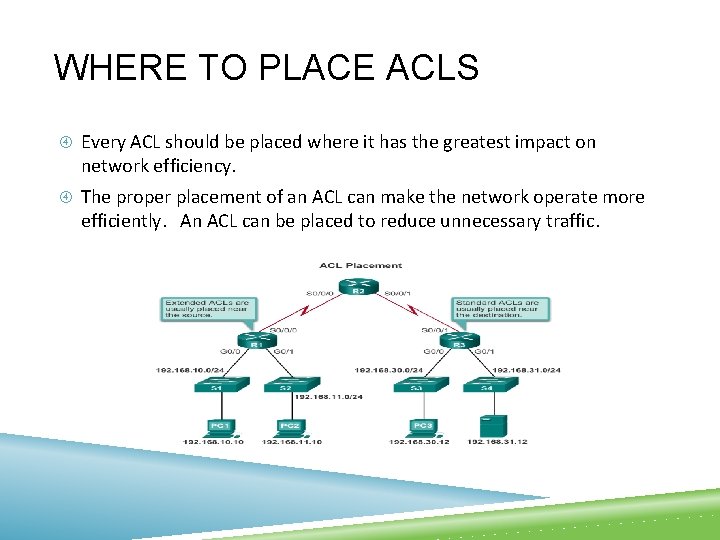
WHERE TO PLACE ACLS Every ACL should be placed where it has the greatest impact on network efficiency. The proper placement of an ACL can make the network operate more efficiently. An ACL can be placed to reduce unnecessary traffic.
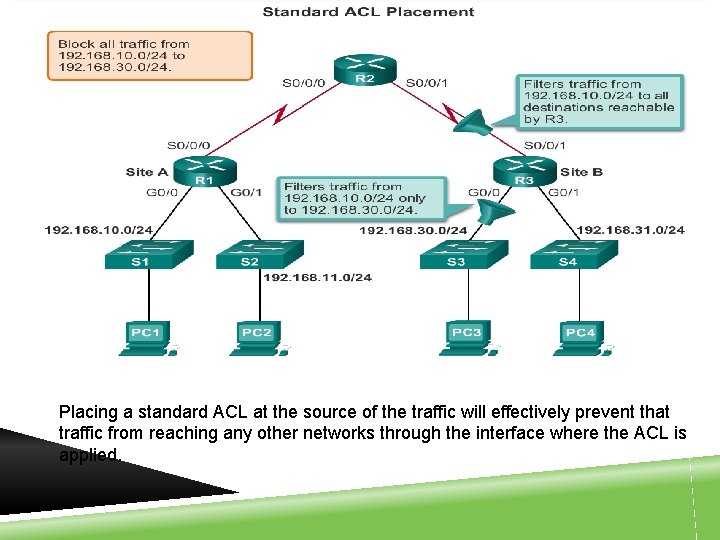
STANDARD ACL PLACEMENT A standard ACL can only filter traffic based on a source address. The basic rule for placement of a standard ACL is to place the ACL as close as possible to the destination network. This allows the traffic to reach all other networks except the network where the packets will be filtered.
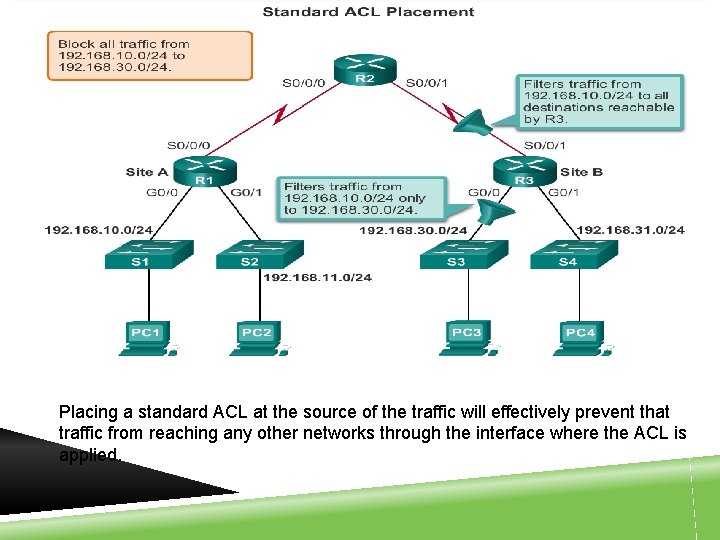
Placing a standard ACL at the source of the traffic will effectively prevent that traffic from reaching any other networks through the interface where the ACL is applied.
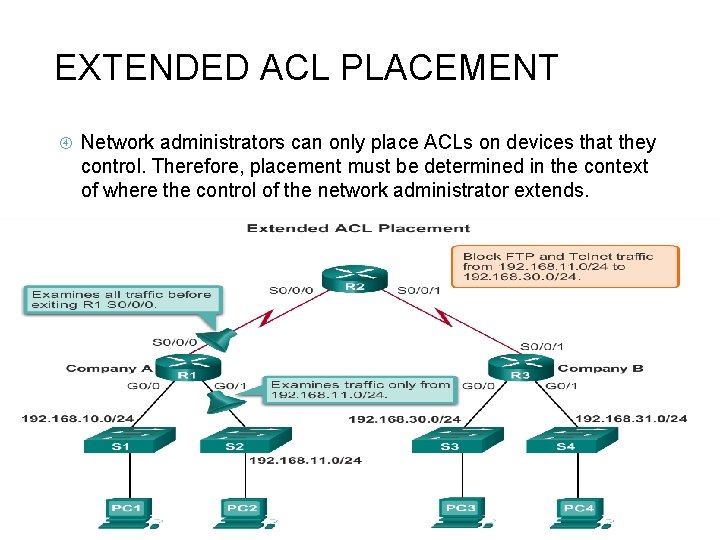
EXTENDED ACL PLACEMENT Like a standard ACL, an extended ACL can filter traffic based on the source address. However, an extended ACL can also filter traffic based on the destination address, protocol, and port number. This allows network administrators more flexibility in the type of traffic that can be filtered and where to place the ACL. The basic rule for placing an extended ACL is to place it as close to the source as possible. This prevents unwanted traffic from being sent across multiple networks only to be denied when it reaches its destination.
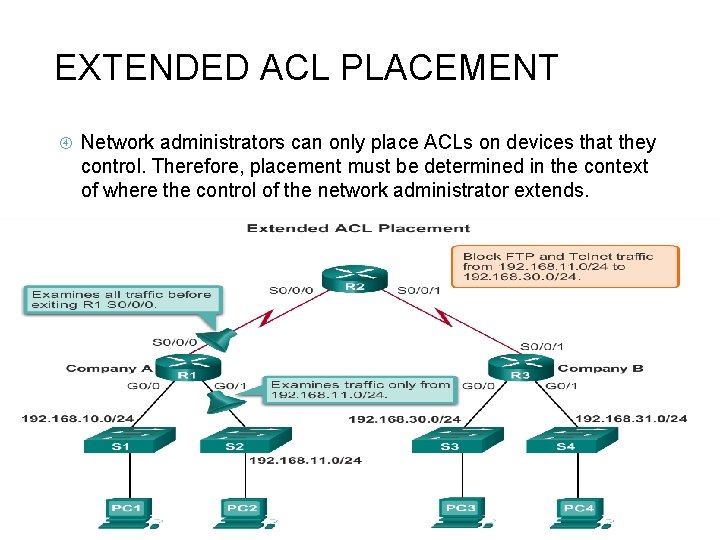
EXTENDED ACL PLACEMENT Network administrators can only place ACLs on devices that they control. Therefore, placement must be determined in the context of where the control of the network administrator extends.
ACL PLACEMENT Placement of the ACL and therefore the type of ACL used may also depend on: The extent of the network administrator’s control Bandwidth of the networks involved Ease of configuration
GUIDELINES FOR ACLS Access lists should be used in firewall routers, which are often positioned between your internal network and an external network such as the Internet. You can also use access lists on a router positioned between two parts of your network, to control traffic entering or exiting a specific part of your internal network.