Botnets by Mohammad Mehedy Masud GUEST LECTURE Botnets
Botnets by Mohammad Mehedy Masud GUEST LECTURE
Botnets ● ● ● Introduction History How to they spread? What do they do? Why care about them? Detection and Prevention
Bot ● ● The term 'bot' comes from 'robot'. In computing paradigm, 'bot' usually refers to an automated process. There are good bots and bad bots. Example of good bots: – Google bot Game bot – Malicious software that steals information – ● Example of bad bots:
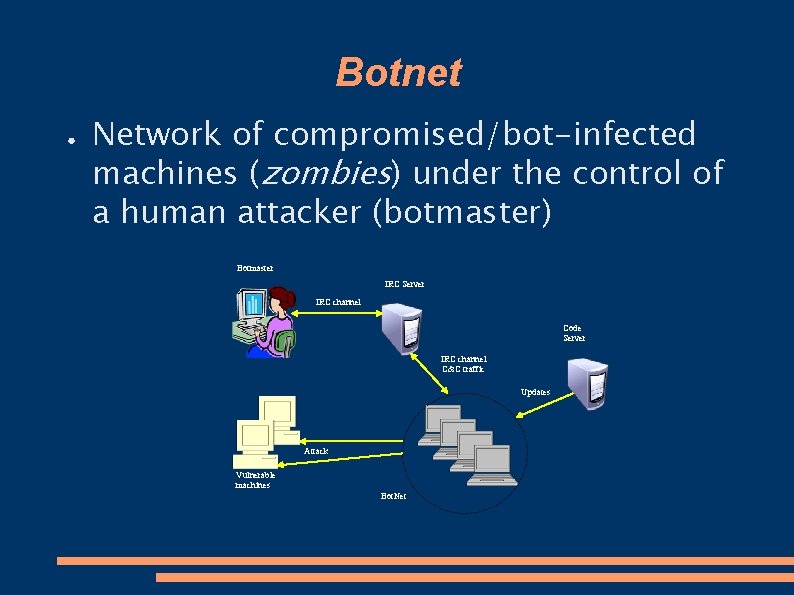
Botnet ● Network of compromised/bot-infected machines (zombies) under the control of a human attacker (botmaster) Botmaster IRC Server IRC channel Code Server IRC channel C&C traffic Updates Attack Vulnerable machines Bot. Net
History ● In the beginning, there were only good bots. – ● Later, bad people thought of creating bad bots so that they may – – – ● Send Spam and Phishing emails Control others pc Launch attacks to servers (DDOS) Many malicious bots were created – ● ex: google bot, game bot etc. SDBot/Agobot/Phatbot etc. Botnets started to emerge
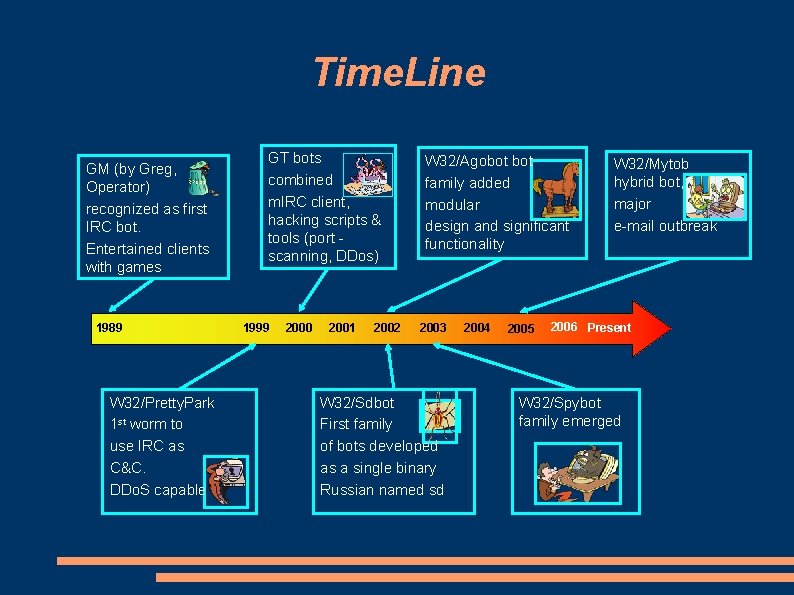
Time. Line GM (by Greg, Operator) recognized as first IRC bot. Entertained clients with games RPCSS 1989 W 32/Pretty. Park 1 st worm to use IRC as C&C. DDo. S capable GT bots combined m. IRC client, hacking scripts & tools (port scanning, DDos) 1999 2000 2001 2002 W 32/Agobot family added modular design and significant functionality 2003 W 32/Sdbot First family of bots developed as a single binary Russian named sd 2004 2005 W 32/Mytob hybrid bot, major e-mail outbreak 2006 Present W 32/Spybot family emerged
Cases in the news ● Axel Gembe – – – ● Author or Agobot (aka Gaobot, Polybot) 21 yrs old Arrested from Germany in 2004 under Germany’s computer Sabotage law Jeffry Parson – – Released a variation of Blaster Worm Infected 48, 000 computers worldwide 18 yrs old Arrested , sentenced to 18 month & 3 yrs of supervised released
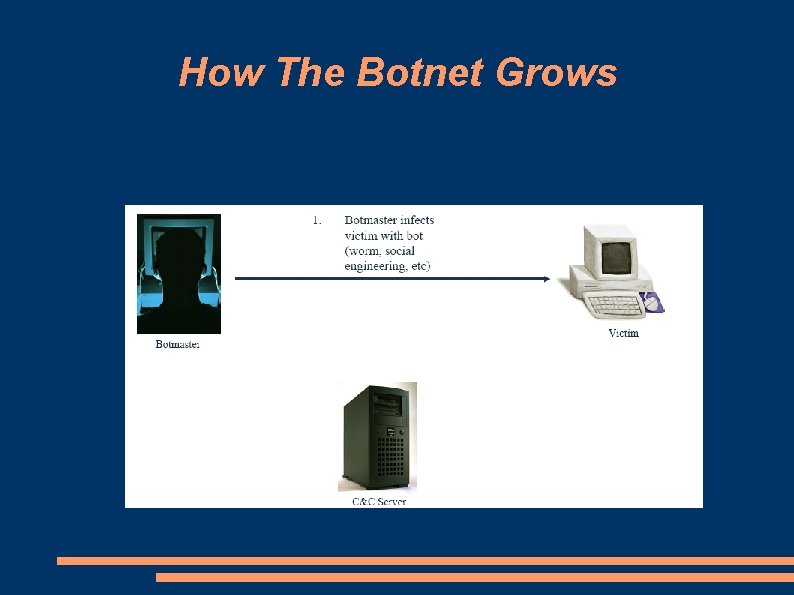
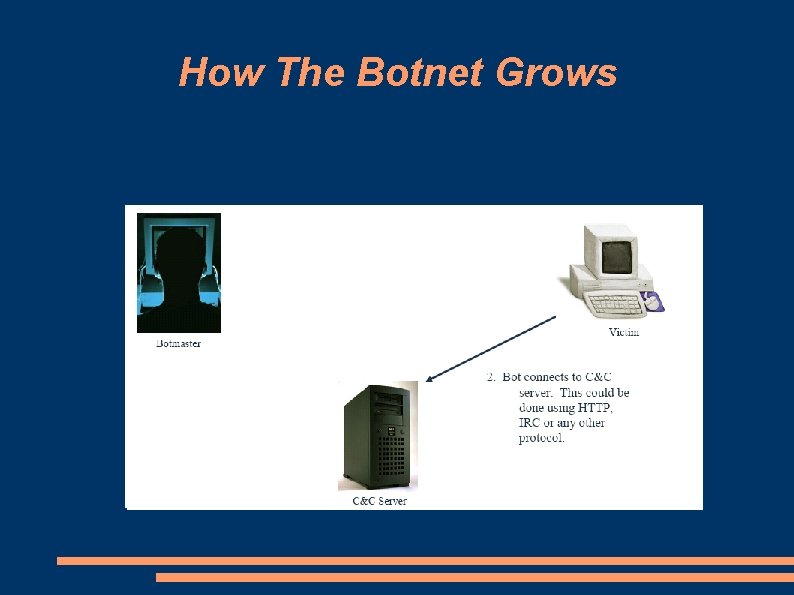
How The Botnet Grows
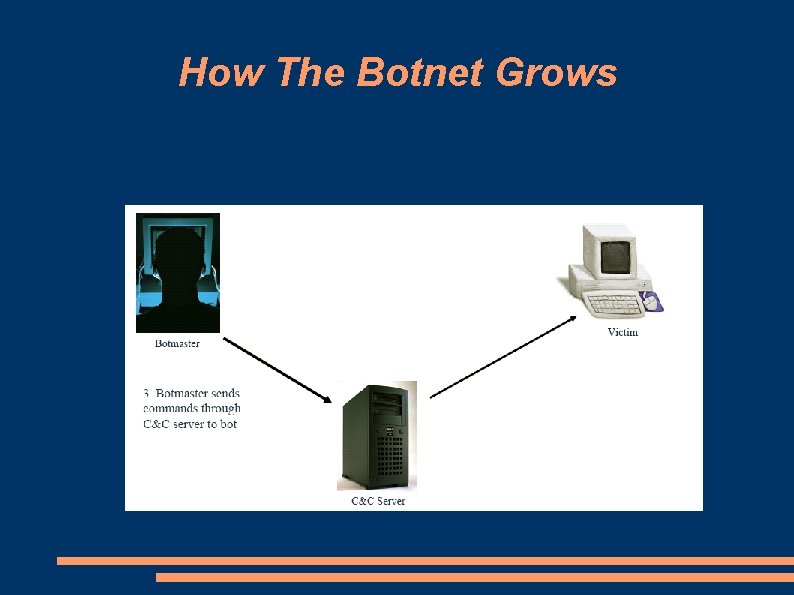
How The Botnet Grows
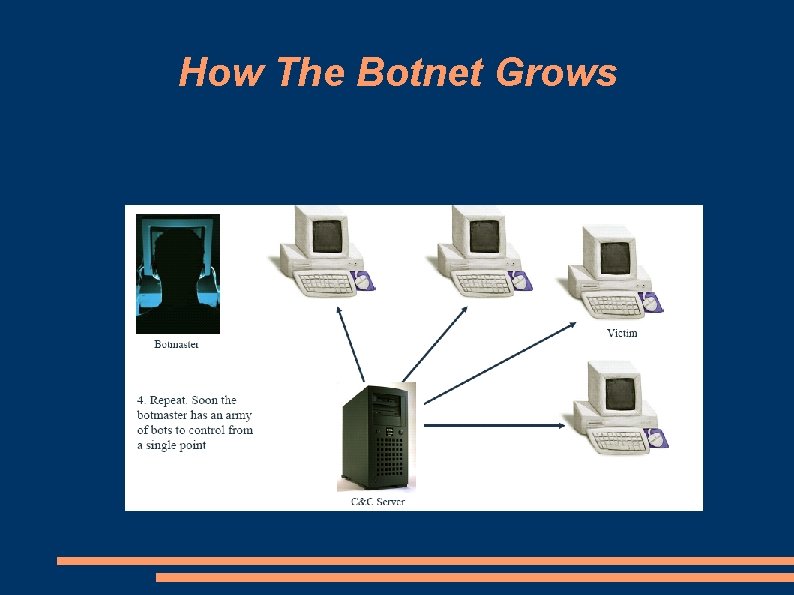
How The Botnet Grows
How The Botnet Grows
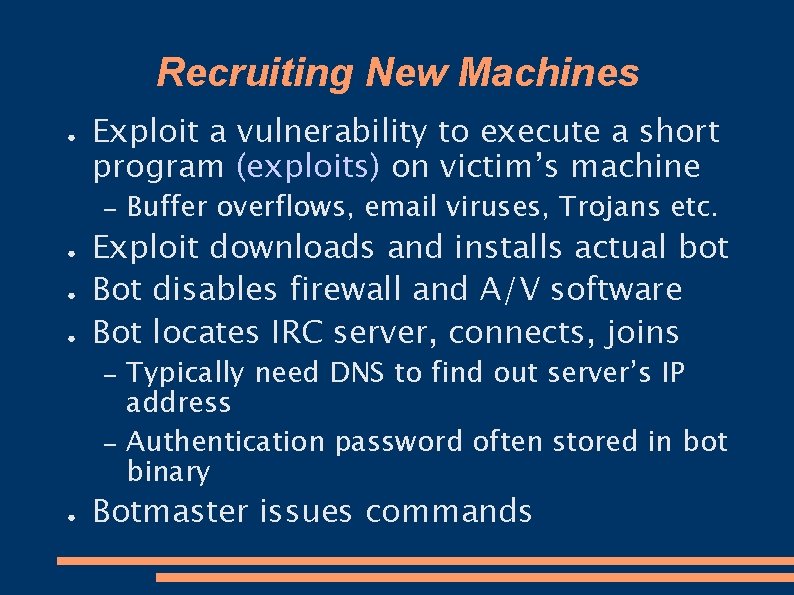
Recruiting New Machines ● Exploit a vulnerability to execute a short program (exploits) on victim’s machine – ● ● ● Exploit downloads and installs actual bot Bot disables firewall and A/V software Bot locates IRC server, connects, joins – – ● Buffer overflows, email viruses, Trojans etc. Typically need DNS to find out server’s IP address Authentication password often stored in bot binary Botmaster issues commands
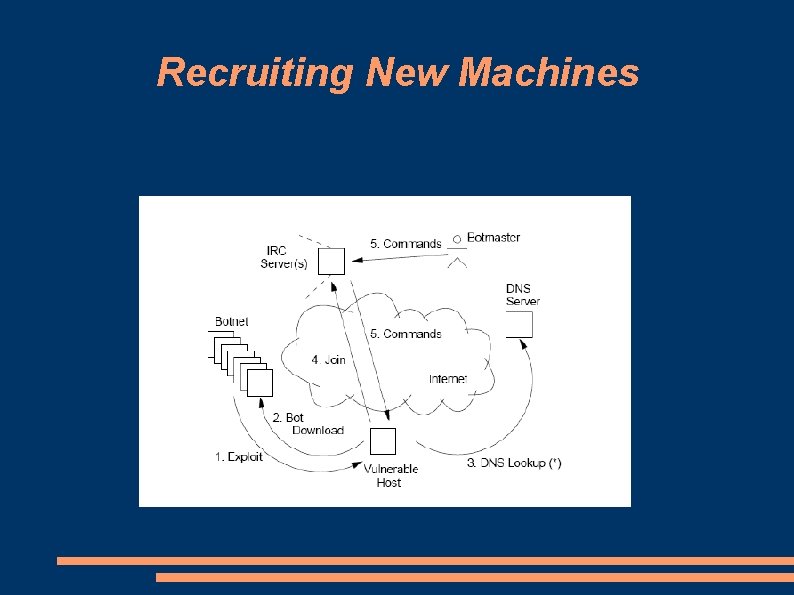
Recruiting New Machines
What Is It Used For ● Botnets are mainly used for only one thing
How Are They Used ● ● ● Distributed Denial of Service (DDo. S) attacks Sending Spams Phishing (fake websites) Addware (Trojan horse) Spyware (keylogging, information harvesting) Storing pirated materials
Example : SDBot ● ● Open-source Malware Aliases – ● Infection – – ● Mcafee: IRC-SDBot, Symantec: Backdoor. Sdbot Mostly through network shares Try to connect using password guessing (exploits weak passwords) Signs of Compromise – – SDBot copies itself to System folder - Known filenames: Aim 95. exe, Syscfg 32. exe etc. . Registry entries modified Unexpected traffic : port 6667 or 7000 Known IRC channels: Zxcvbnmas. i 989. net etc. .
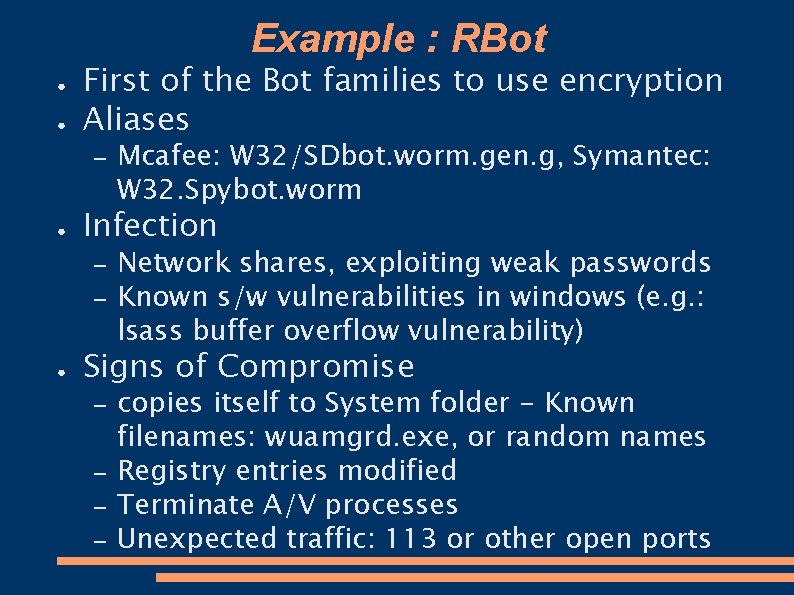
Example : RBot ● ● First of the Bot families to use encryption Aliases – ● Infection – – ● Mcafee: W 32/SDbot. worm. gen. g, Symantec: W 32. Spybot. worm Network shares, exploiting weak passwords Known s/w vulnerabilities in windows (e. g. : lsass buffer overflow vulnerability) Signs of Compromise – – copies itself to System folder - Known filenames: wuamgrd. exe, or random names Registry entries modified Terminate A/V processes Unexpected traffic: 113 or other open ports
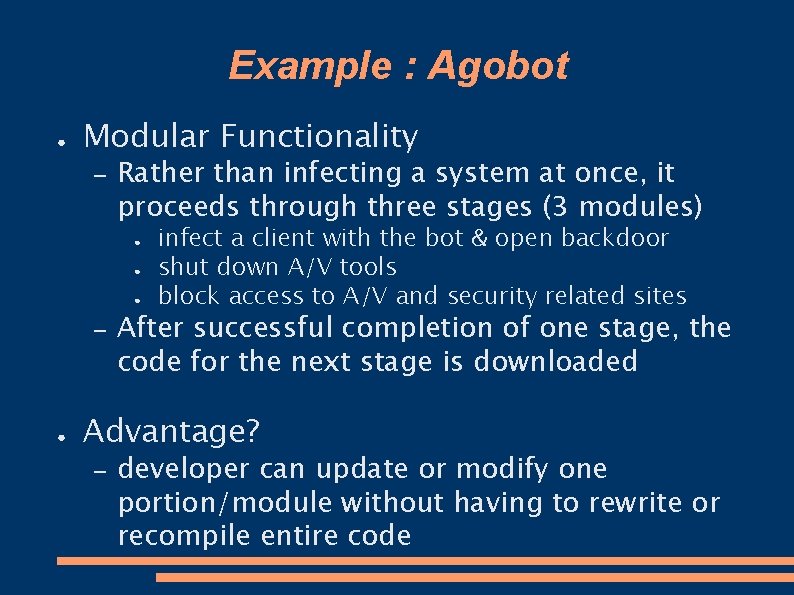
Example : Agobot ● Modular Functionality – Rather than infecting a system at once, it proceeds through three stages (3 modules) ● ● ● – ● infect a client with the bot & open backdoor shut down A/V tools block access to A/V and security related sites After successful completion of one stage, the code for the next stage is downloaded Advantage? – developer can update or modify one portion/module without having to rewrite or recompile entire code
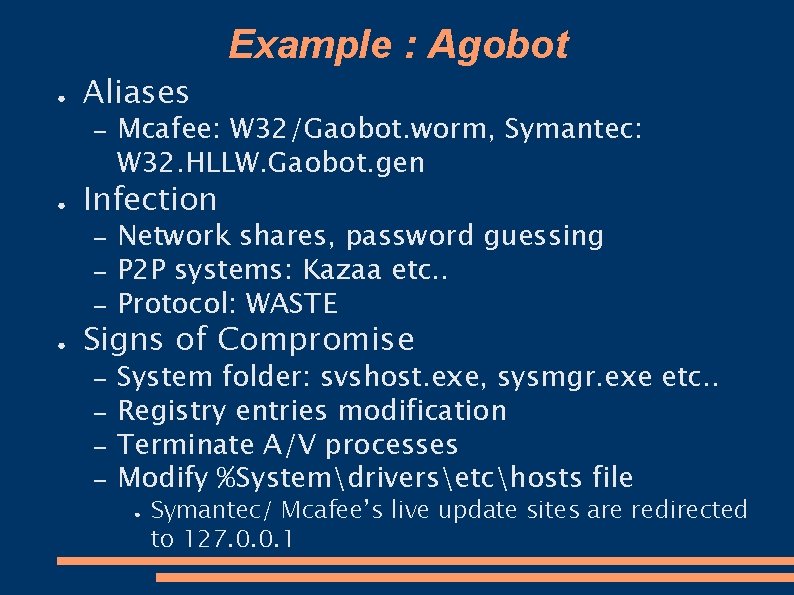
Example : Agobot ● Aliases – ● Infection – – – ● Mcafee: W 32/Gaobot. worm, Symantec: W 32. HLLW. Gaobot. gen Network shares, password guessing P 2 P systems: Kazaa etc. . Protocol: WASTE Signs of Compromise – – System folder: svshost. exe, sysmgr. exe etc. . Registry entries modification Terminate A/V processes Modify %Systemdriversetchosts file ● Symantec/ Mcafee’s live update sites are redirected to 127. 0. 0. 1
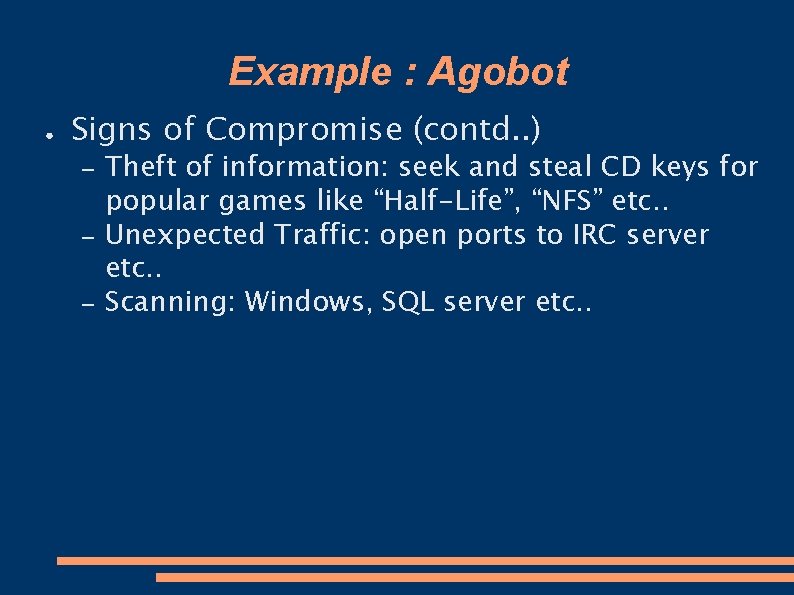
Example : Agobot ● Signs of Compromise (contd. . ) – – – Theft of information: seek and steal CD keys for popular games like “Half-Life”, “NFS” etc. . Unexpected Traffic: open ports to IRC server etc. . Scanning: Windows, SQL server etc. .
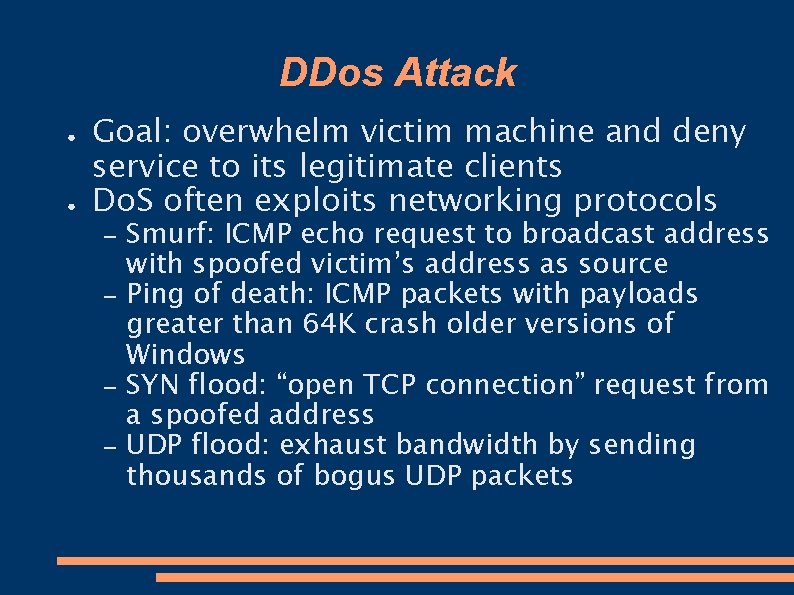
DDos Attack ● ● Goal: overwhelm victim machine and deny service to its legitimate clients Do. S often exploits networking protocols – – Smurf: ICMP echo request to broadcast address with spoofed victim’s address as source Ping of death: ICMP packets with payloads greater than 64 K crash older versions of Windows SYN flood: “open TCP connection” request from a spoofed address UDP flood: exhaust bandwidth by sending thousands of bogus UDP packets
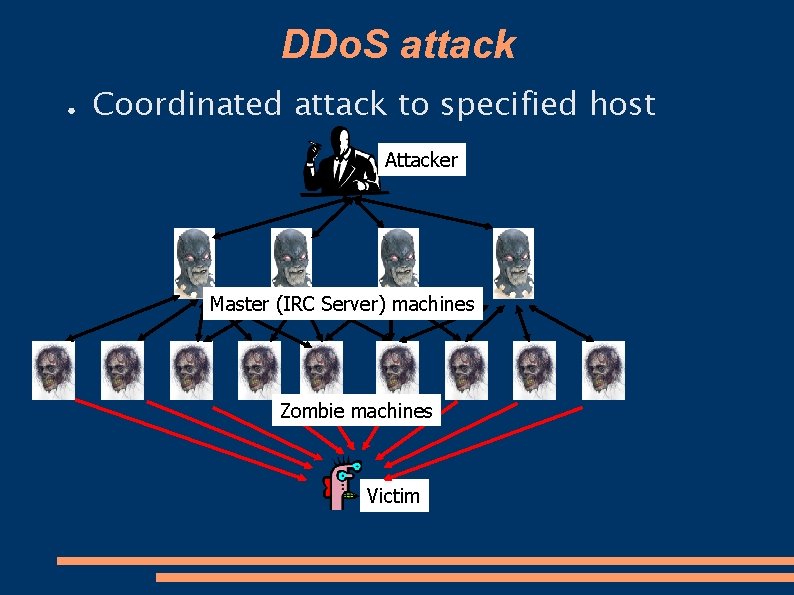
DDo. S attack ● Coordinated attack to specified host Attacker Master (IRC Server) machines Zombie machines Victim
Why DDo. S attack? ● Extortion – – ● Take down systems until they pay Works sometimes too! Example: 180 Solutions – Aug 2005 – – – Botmaster used bots to distribute 180 solutions addware 180 solution shutdown botmaster Botmaster threatened to take down 180 solutions if not paid When not paid, botmaster use DDo. S 180 Solutions filed Civil Lawsuit against hackers
Botnet Detection ● ● ● Host Based Intrusion Detection Systems (IDS) Anomaly Detection IRC Nicknames Honey. Pot and Honey. Net
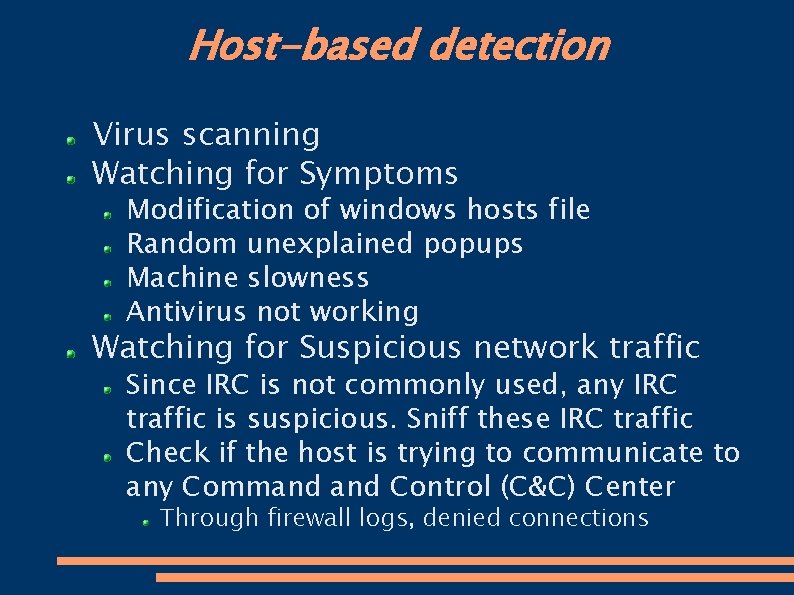
Host-based detection Virus scanning Watching for Symptoms Modification of windows hosts file Random unexplained popups Machine slowness Antivirus not working Watching for Suspicious network traffic Since IRC is not commonly used, any IRC traffic is suspicious. Sniff these IRC traffic Check if the host is trying to communicate to any Command Control (C&C) Center Through firewall logs, denied connections
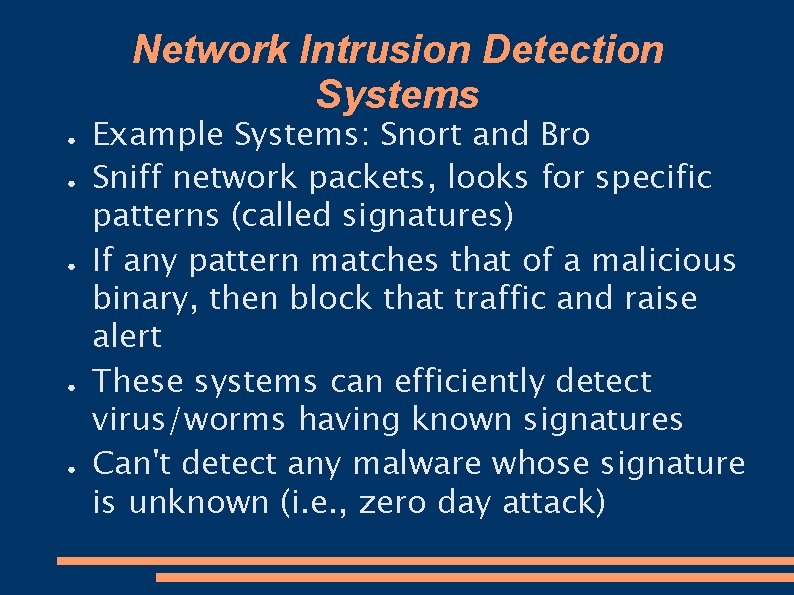
Network Intrusion Detection Systems ● ● ● Example Systems: Snort and Bro Sniff network packets, looks for specific patterns (called signatures) If any pattern matches that of a malicious binary, then block that traffic and raise alert These systems can efficiently detect virus/worms having known signatures Can't detect any malware whose signature is unknown (i. e. , zero day attack)
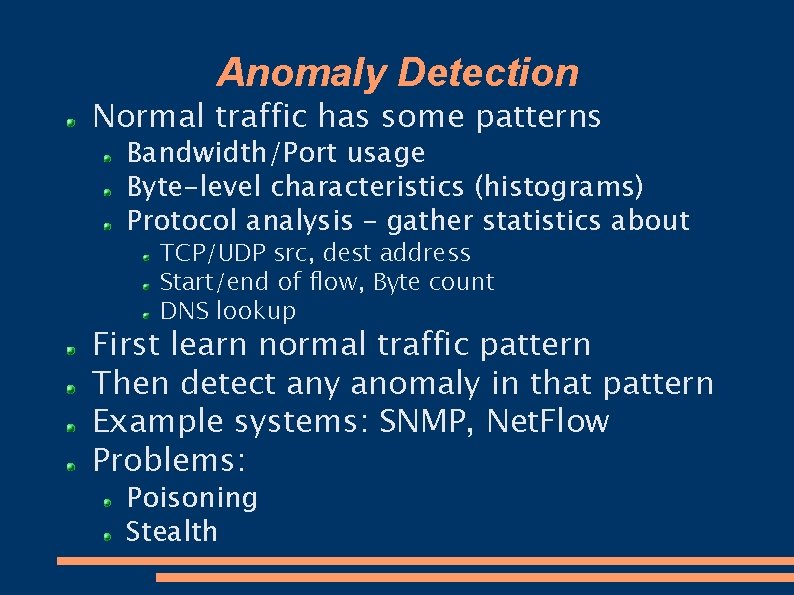
Anomaly Detection Normal traffic has some patterns Bandwidth/Port usage Byte-level characteristics (histograms) Protocol analysis – gather statistics about TCP/UDP src, dest address Start/end of flow, Byte count DNS lookup First learn normal traffic pattern Then detect any anomaly in that pattern Example systems: SNMP, Net. Flow Problems: Poisoning Stealth
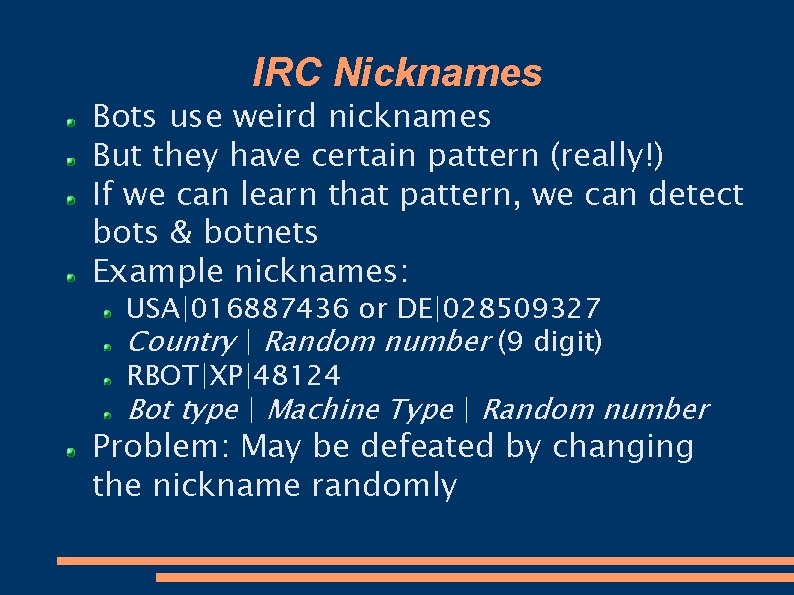
IRC Nicknames Bots use weird nicknames But they have certain pattern (really!) If we can learn that pattern, we can detect bots & botnets Example nicknames: USA|016887436 or DE|028509327 Country | Random number (9 digit) RBOT|XP|48124 Bot type | Machine Type | Random number Problem: May be defeated by changing the nickname randomly
Honey. Pot and Honey. Net Honey. Pot is a vulnerable machine, ready to be attacked Example: unpatched windows 2000 or windows XP Once attacked, the malware is caught inside The malware is analyzed, its activity is monitored When it connects to the C&C server, the server’s identity is revealed
Honey. Pot and Honey. Net Thus many information about the bot is obtained C&C server address, master commands Channel, Nickname, Password Now Do the following make a fake bot join the same IRC channel with the same nickname/password Monitor who else are in the channel, thus observer the botnet Collect statistics – how many bots Collect sensitive information – who is being attacked, when etc. .
Honey. Pot and Honey. Net Finally, take down the botnet Honey. Net: a network of honeypots (see the ‘Honey. Net Project’) Very effective, worked in many cases They also pose great security risk If not maintained properly - Hacker may use them to attack others Must be monitored cautiously
Summary Today we have learned What is botnet How / why they are used How to detect / prevent
Questions ?
- Slides: 33