Botnets An Introduction Into the World of Botnets
Botnets An Introduction Into the World of Botnets Tyler Hudak tyler@hudakville. com
What will we cover? w What are botnets? w History w How do they work? w What are they used for? w Who cares? w Detection and Prevention Methods
Botnets w “Collection of software robots, or bots, which run autonomously” 1 w A group of programs, installed on different computers, all running under one command control structure (C&C) w Typically controlled by one person or a group of people (aka. The botmaster)
History w Originally used in IRC as a way to allow automated tasks to be done n Protect a channel, kick a user out of a channel, etc w Eventually evolved into a way to automate malicious tasks w Started with Do. S/DDo. S against servers n TFN, stacheldraht, trinoo (1999)
History w Attackers created easier ways to control bots n IRC, HTTP, P 2 P w Bots started to become payloads for worms n n Allowed for faster compromises, bigger botnets Sobig/SDBot/Rbot/Agobot/Phatbot… w Today, botnets are big business! w Over 10, 000 bots have been reported in a single botnet.
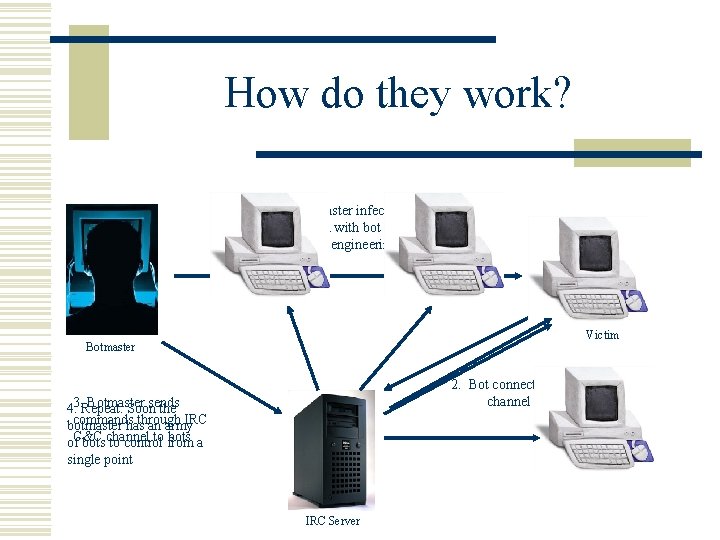
How do they work? 1. Botmaster infects victim with bot (worm, social engineering, etc) Victim Botmaster 2. Bot connects to IRC C&C channel Botmaster sends 4. 3. Repeat. Soon the commands through IRC botmaster has an army to from bots a of. C&C bots channel to control single point IRC Server
How are they spread? w Exploiting known vulnerabilities w Social Engineering n n Spam/Phishing Website Downloads Instant Messaging P 2 P networks
Command Control w Number of different ways to control bots w Dynamic DNS services often used w Most common is through IRC (public or private) n n Bots log into a specific IRC channel Bots are written to accept specific commands and execute them (sometimes from specific users) w Disadvantages with IRC n Usually unencrypted, easy to get into and take over or shut down
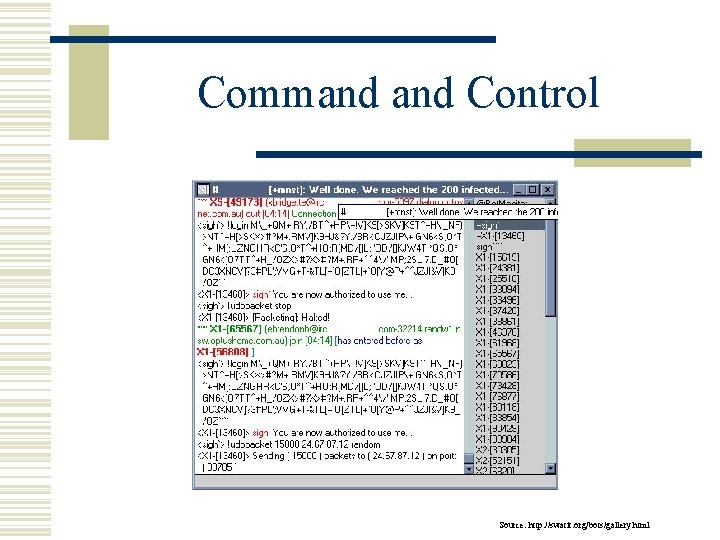
Command Control Source: http: //swatit. org/bots/gallery. html
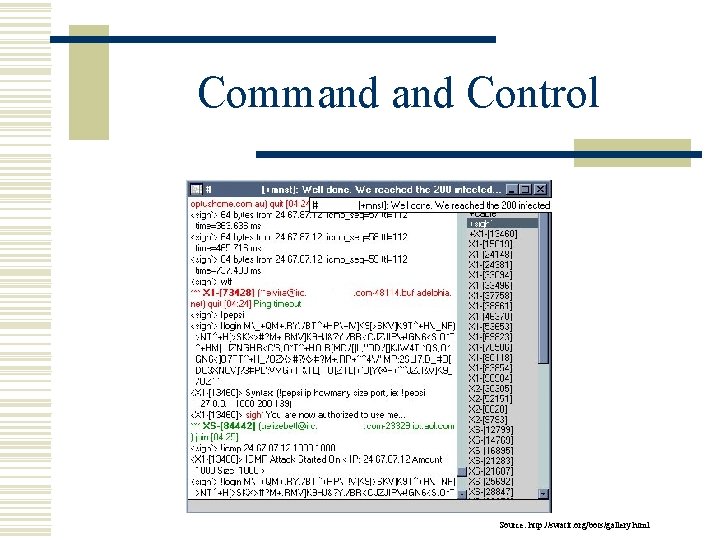
Command Control Source: http: //swatit. org/bots/gallery. html
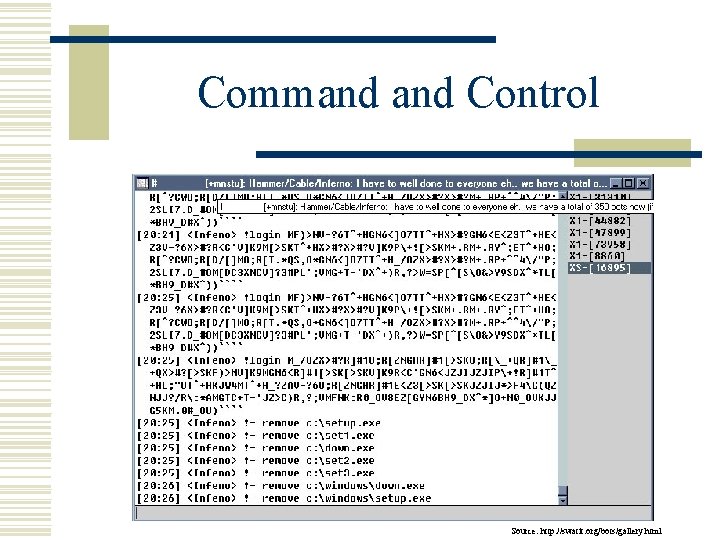
Command Control Source: http: //swatit. org/bots/gallery. html
Command Control w C&C interfaces starting to become more complex w HTTP C&C interface w Advantages: n n IRC not always allowed through corporate firewalls, HTTP almost always is Websites are found everywhere
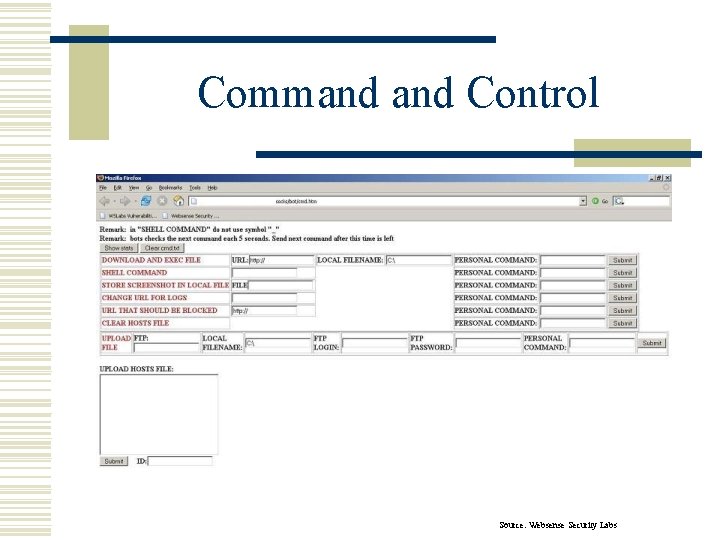
Command Control Source: Websense Security Labs
Command Control w More C&C interfaces emerging w Phatbot/Nugache worm uses encrypted P 2 P network (WASTE) n Much more difficult to find botmaster or shut down botnet
What are they used for? w Phishing w Spam w Distributed Denial of Service w Click Fraud w Adware/Spyware Installation w Identity Theft w Making Additional Income!!!
DDo. S & Botnets w DDo. S has been available in bots since the beginning w All too common w Used for extortion n Take down systems until they pay – threats work too! w Take out competition n Blue. Security anti-spam service
Additional Income? ? ? w Botnets can be very profitable n n n Extortion Fraud Identity Theft Adware Renting out botnets!
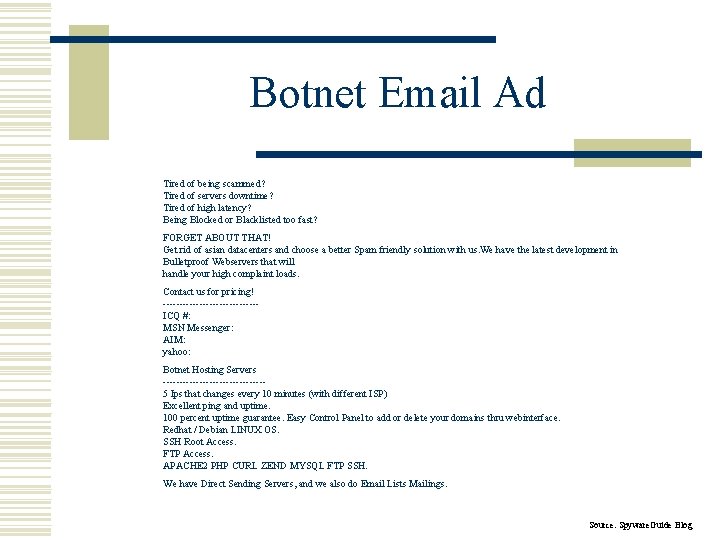
Botnet Email Ad Tired of being scammed? Tired of servers downtime? Tired of high latency? Being Blocked or Blacklisted too fast? FORGET ABOUT THAT! Get rid of asian datacenters and choose a better Spam friendly solution with us. We have the latest development in Bulletproof Webservers that will handle your high complaint loads. Contact us for pricing! --------------ICQ #: MSN Messenger: AIM: yahoo: Botnet Hosting Servers ---------------5 Ips that changes every 10 minutes (with different ISP) Excellent ping and uptime. 100 percent uptime guarantee. Easy Control Panel to add or delete your domains thru webinterface. Redhat / Debian LINUX OS. SSH Root Access. FTP Access. APACHE 2 PHP CURL ZEND MYSQL FTP SSH. We have Direct Sending Servers, and we also do Email Lists Mailings. Source: Spyware. Guide Blog
Why should you care? w Botnets are becoming more common w Once a bot is on your machine (or your company’s machines) you no longer own that box w Do you really want your machine to be used to attack others?
Detection Methods w Watch anti-virus/anti-spyware logs w Use IDS to watch for: n n n IRC/P 2 P activity Do. S traffic coming FROM your network Attacks coming from your network w Network flow analysis
Prevention w Patch, patch w Teach users safe computing habits w Use updated anti-virus
Additional Resources w Know Your Enemy: Botnets w Swatit Botnets Resource w Shadowserver group w Google
Thank you! Any questions? http: //www. hudakville. com/infosec
- Slides: 23