11032015 Nawras Alkassab 813 Internet Security Design and
11/03/2015 Nawras Alkassab 813 - Internet Security Design and Implementation of Cross. Domain Cooperative Firewall (CDCF) Jerry Cheng, Hao Yang, Starsky H. Y. Wong, Petros Zerfos, Songwu Lu
Terminologies u
VPN ( Virtual Private Network ) u What is VPN? It is a point-to-point connection which uses a virtual tunneling protocol across private or public network u There are two types of VPN connections: * Remote access VPN * Site-to- site VPN u VPN connections have the following properties: * Encapsulation * Authentication * Data encryption
VPN protocols u PPTP ( Point-to-Point Tunneling Protocol) u L 2 TP ( Layer Two Tunneling Protocol) u SSTP ( Secure Socket Tunneling Protocol) u Open. VPN u GRE tunnels
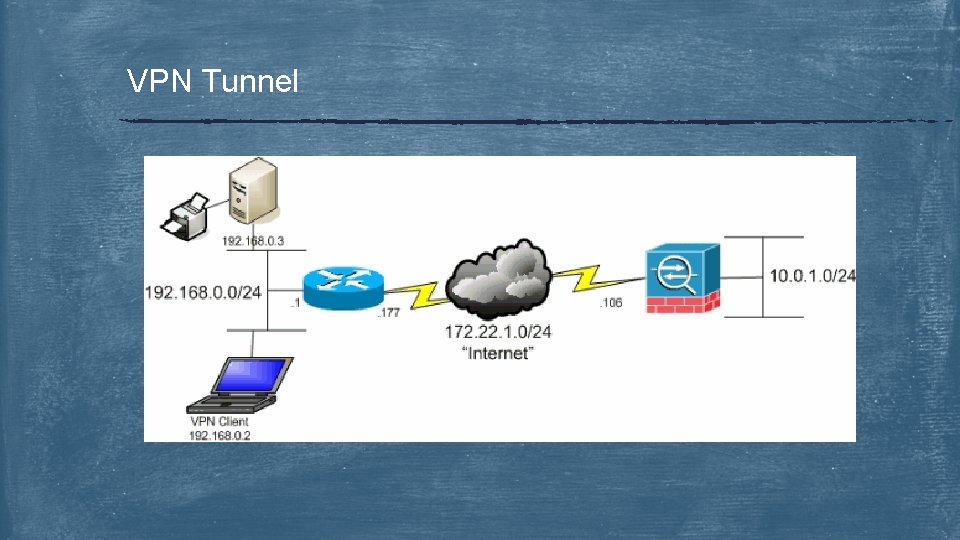
VPN Tunnel
Security concerns in VPN u Once the VPN client connects to the remote network, the client doesn’t only open the resources in the remote network but also can redirect his/her internet traffic through VPN tunnel to the remote network. u The problem here is the firewall in the remote network is unable to regulate the traffic because it’s encrypted through the VPN tunnel. Consequently, if there is a policy to block some connection (i. e downloading pirated applications) in the foreign network, this policy can not be applied to the VPN traffic which leaves the foreign (remote) network widely opened to various security threats from the internet.
Security concerns in VPN tunnels and cooperative firewalls u To alleviate this problem we have 2 options: 1 - Users reveal their traffic to the foreign network ( foreign firewall can decrypt their traffic). In this case, the foreign router knows how to decrypt their traffic, or: 2 - Foreign firewall reveal its firewall rules to tunnel endpoints. Whereas, the firewall publish its rules to the client to self-regulate his/her traffic at the tunnel end-point( i. e. VPN server, Router) Both solutions ignore privacy which is a major feature of VPN tunnels because both the client and the firewall are opened to each other.
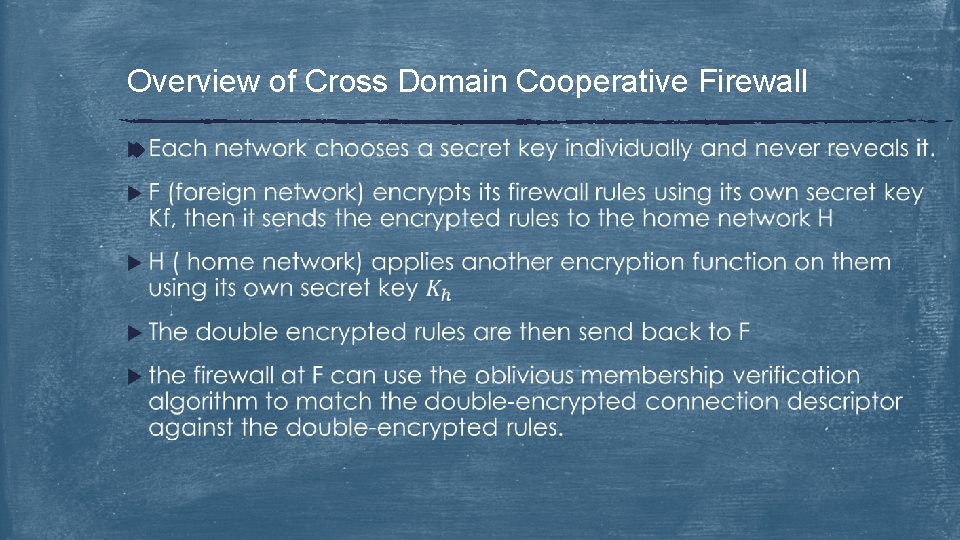
Overview of Cross Domain Cooperative Firewall u
Overview of Cross Domain Cooperative Firewall (cont. ) u
Overview of Cross Domain Cooperative Firewall (cont. ) u In CDCF, when the VPN client connects to a VPN server in the foreign network, the tunnel endpoint can regulate the traffic and enforce the firewall rules without knowing these rules. u CDCF enables the distribution of firewall primitives across network domains u CDCF uses a technique of efficient “oblivious membership verification”
Privacy issues with cross-domain firewalls: u To perform joint traffic filtering, we need to know: 1 - The home network’s firewall rules 2 - The foreign network’s firewall rules 3 - User connection descriptor u Ideally, if these information are shared, the firewalls at both the home network and the foreign network can regulate the traffic. u Practically, it’s undesired because remote users tend to not trust the foreign network. On the other hand, IT admins can not reveal their firewall rules for security and policy concerns.
Privacy issues with cross-domain firewalls (cont. ) u To address this problem, we should ask ourselves the following questions : 1 - How can we keep the firewall rules confidential? 2 - Does every packet need to be revealed? 3 - In which direction the information should be revealed? Shoud the user reveal its traffic to the foreign network ? Or should the foreign network reveal its firewall rules to the user?
System settings u Both home and foreign networks deploy firewall to monitor and regulate the traffic. u The firewall is static packet-filtering firewall that filters traffic based on IP header ( src_IP, src_port, dst_IP, dst_Port) u We can employ “deny-all” rule to increase security u Joint regulation on the remote user’s traffic is implemented in cooperative firewalls. Hence, they are called “cooperative”
Cut it down ! u Decoupling u Oblivious u Privacy Firewall Operations Comparison Enhancement Techniques
Cross Domain Cooperative Firewall (CDCF) architecture: u Bootstrapping: prepare firewall rules to be encrypted ( oblivious comparison) in which the encrypted rule set will be stored at the foreign firewall to match the rules ( rule matching) u Per-connection evaluation phase: each new connection is first compared with the home network’s firewall rules. The traffic allowed by the home network will then be compared against the foreign firewall rules. The comparison result and firewall verdict are stored in the home network for (verdict enforcement) u Per-packet enforcement phase: each subsequent packet is either passed through or dropped by the home network according to the verdict that was stored in the previous stage
Decoupling Firewall Operations u Usually, ”rule-matching” and “verdict enforcement” are coupled together (i. e Iptables). u Decomposing “rule-matching” and “verdict enforcement” in which “rulematching” operation will be held on the foreign network and “verdict enforcement” will be maintained by the home network. u For each new connection, the foreign network needs to know the first packet. Therefore; the foreign network will know about user traffic information
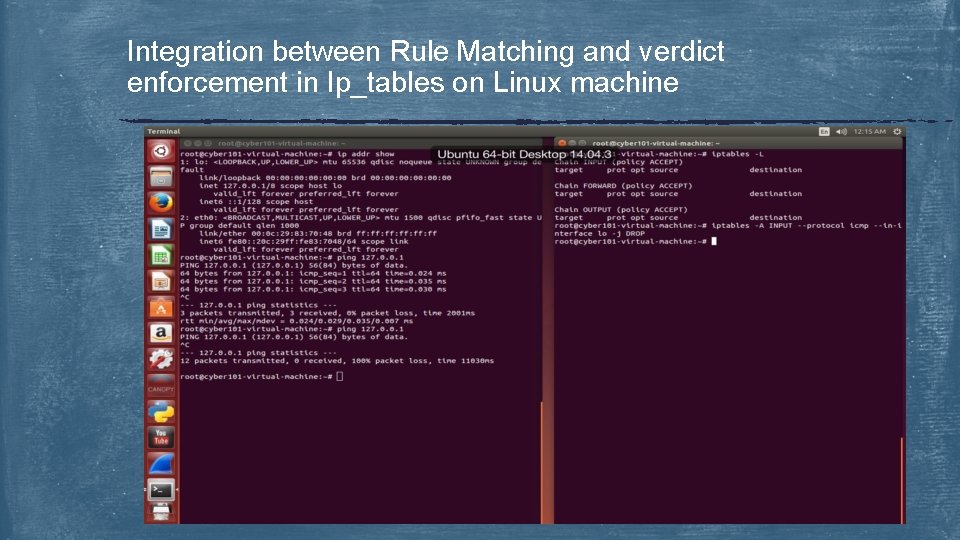
Integration between Rule Matching and verdict enforcement in Ip_tables on Linux machine
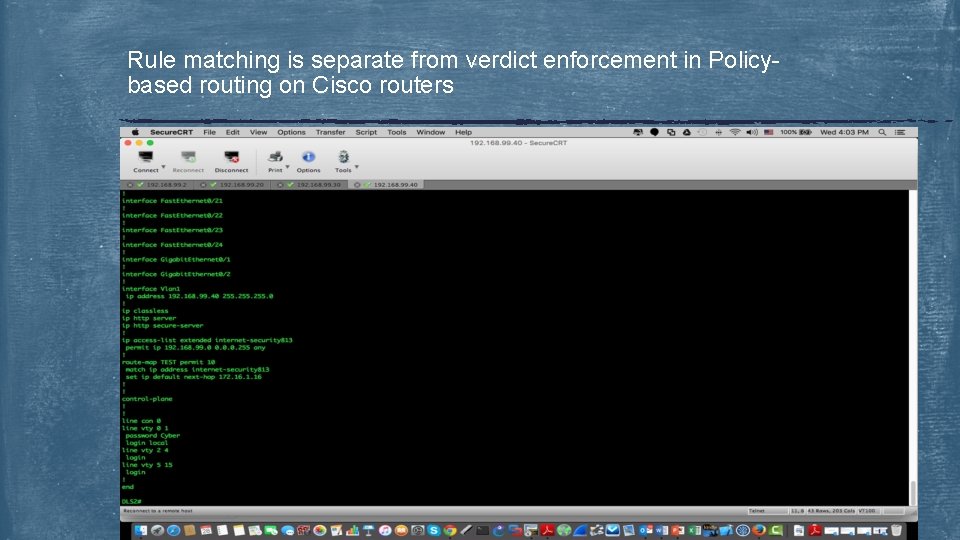
Rule matching is separate from verdict enforcement in Policybased routing on Cisco routers
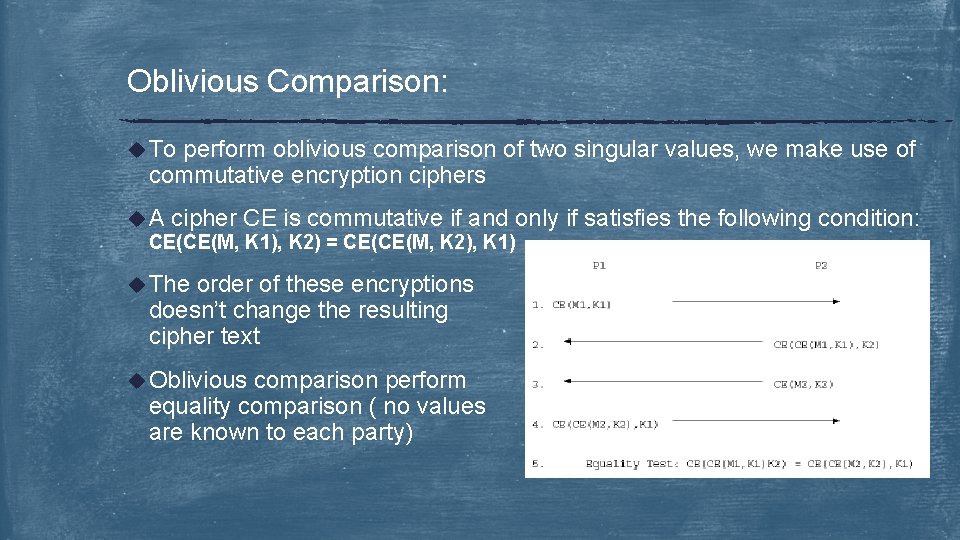
Oblivious Comparison: u To perform oblivious comparison of two singular values, we make use of commutative encryption ciphers u A cipher CE is commutative if and only CE(CE(M, K 1), K 2) = CE(CE(M, K 2), K 1) u The order of these encryptions doesn’t change the resulting cipher text u Oblivious comparison perform equality comparison ( no values are known to each party) if satisfies the following condition:
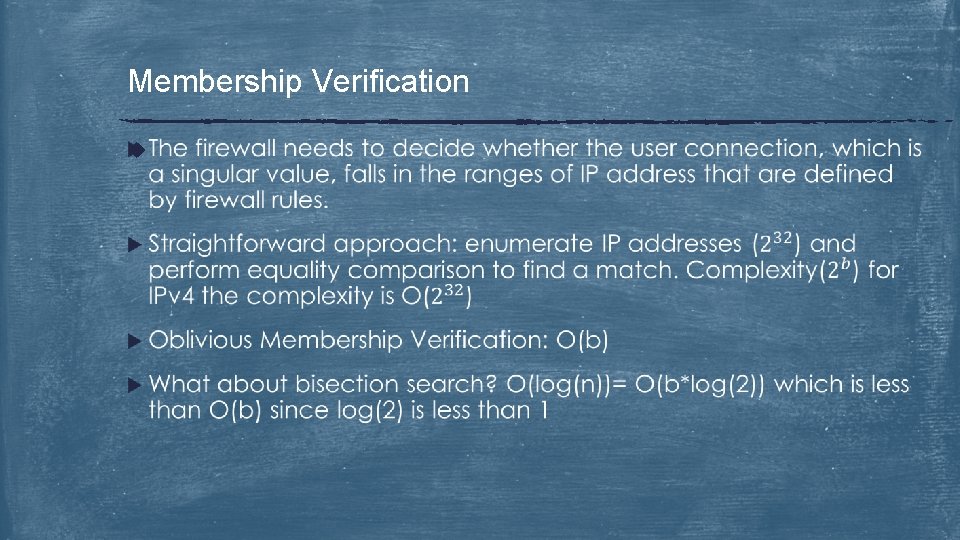
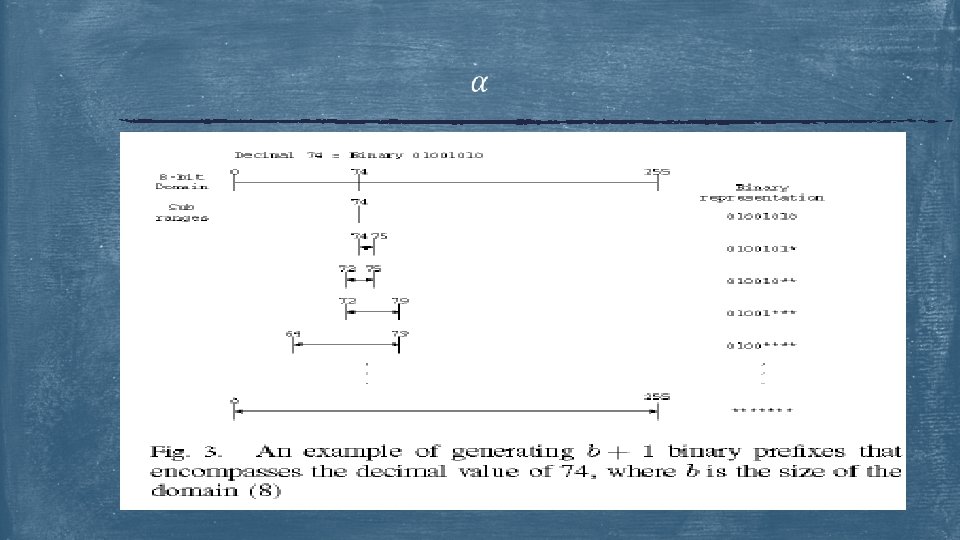
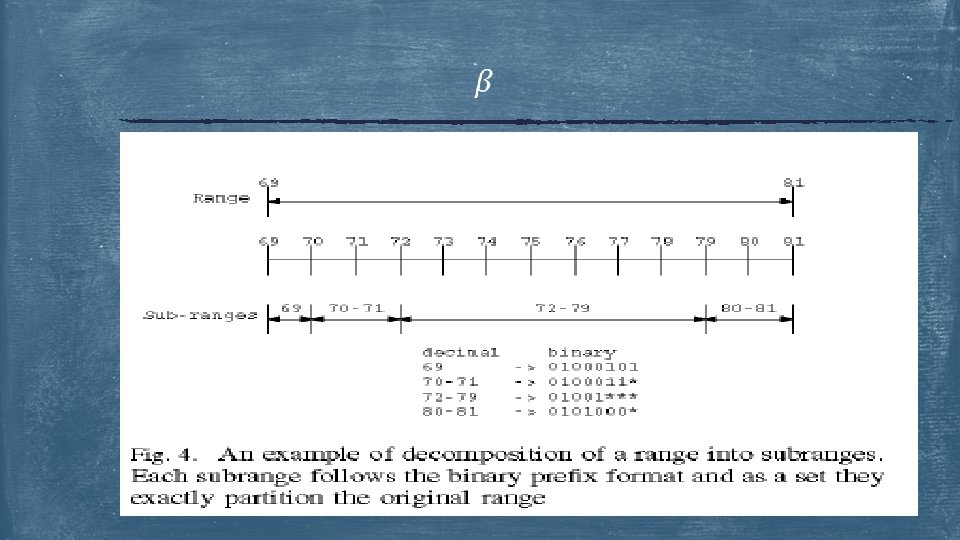
Membership Verification u
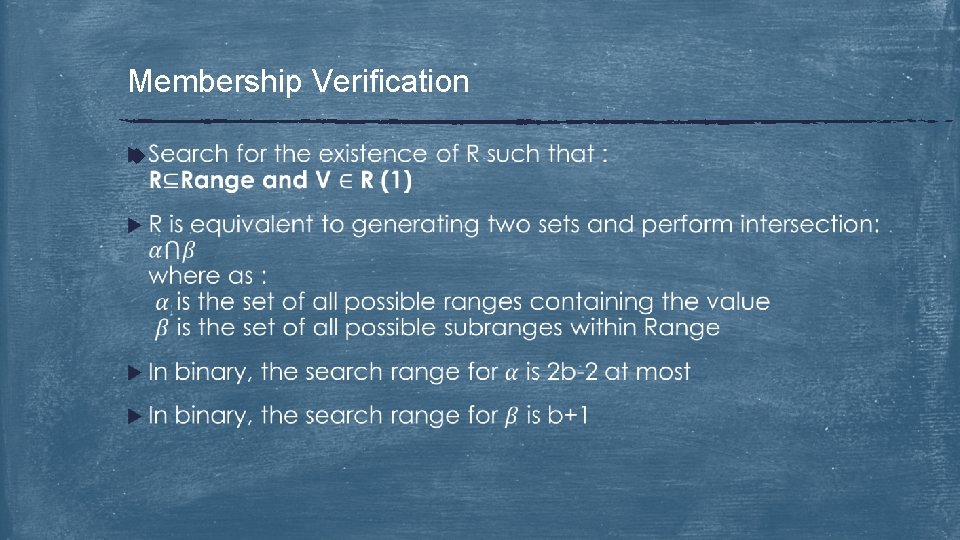
Membership Verification u
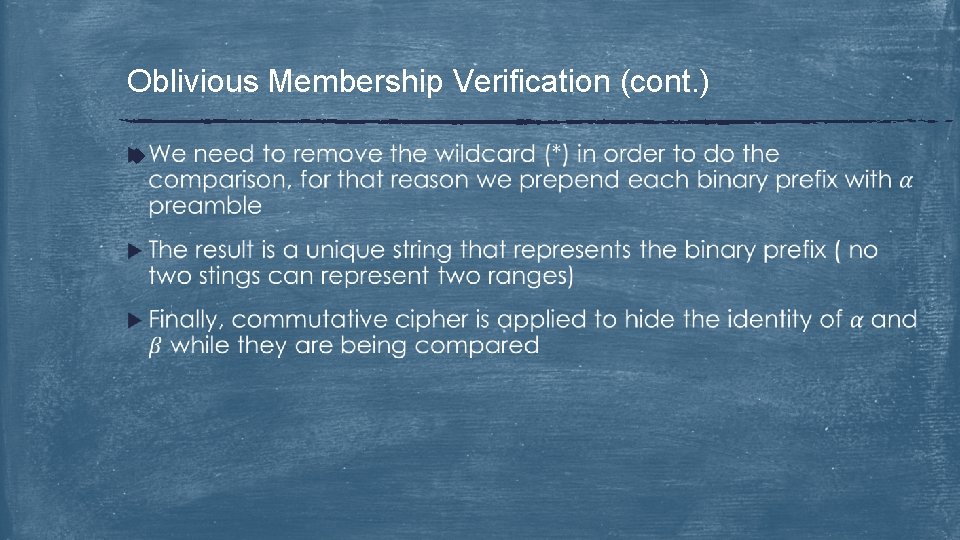
Oblivious Membership Verification (cont. ) u
Privacy Enhancement Techniques u User Connection Privacy: rule matching is performed by foreign network. The foreign network can study the representation of the rule or it can determine the identity of the rules based on their logical order. Consequently, this user’s privacy is leaked. u Enhancements: u Foreign 1 - Dummy Fields/Rules 2 - Dummy connections Network Privacy
Dummy Fields/Rules u
Dummy connections u Alternatively, connections. we can preserve the user privacy by using dummy u These connections look real ( normal queries and valid fields ), but randomly generated by the home network instead of being extracted by the user. u The foreign network is unable to distinguish between the real connections and the artificially generated ones
Foreign Network Privacy: u Foreign network firewall release its encrypted rules. Therefore; the home network can not infer these rules and foreign network privacy is preserved. u However, Home network can perform range probing through probing the firewall with especially constructed queries that include some ranges. If there is any match the privacy of the foreign firewall is revealed. u In CDCF, The foreign network can identify range probing attempts through a challenge/response mechanism ( explain later !! )
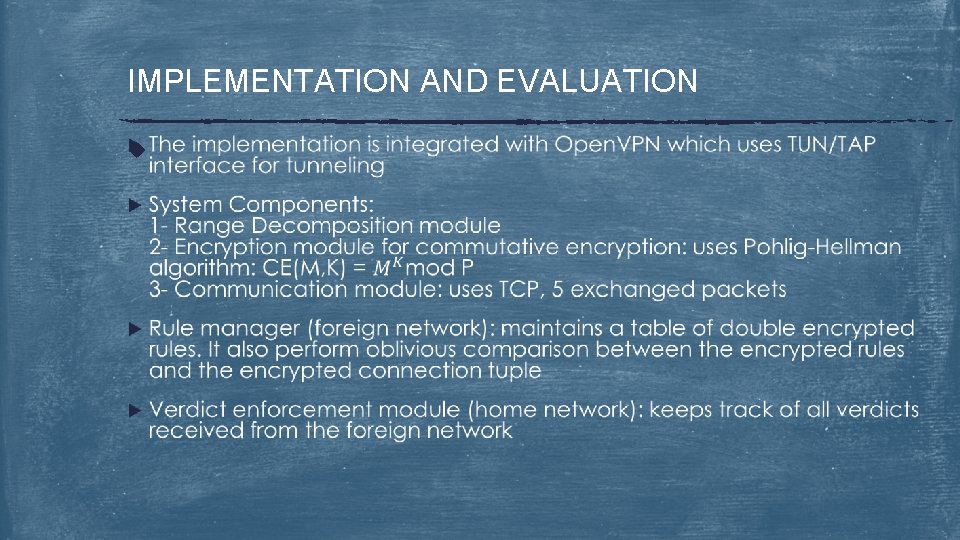
IMPLEMENTATION AND EVALUATION u
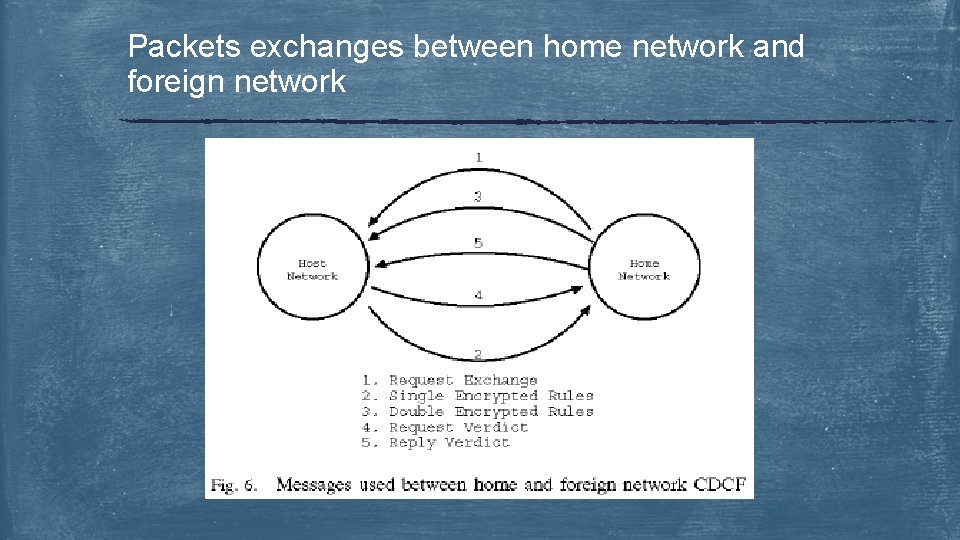
Packets exchanges between home network and foreign network
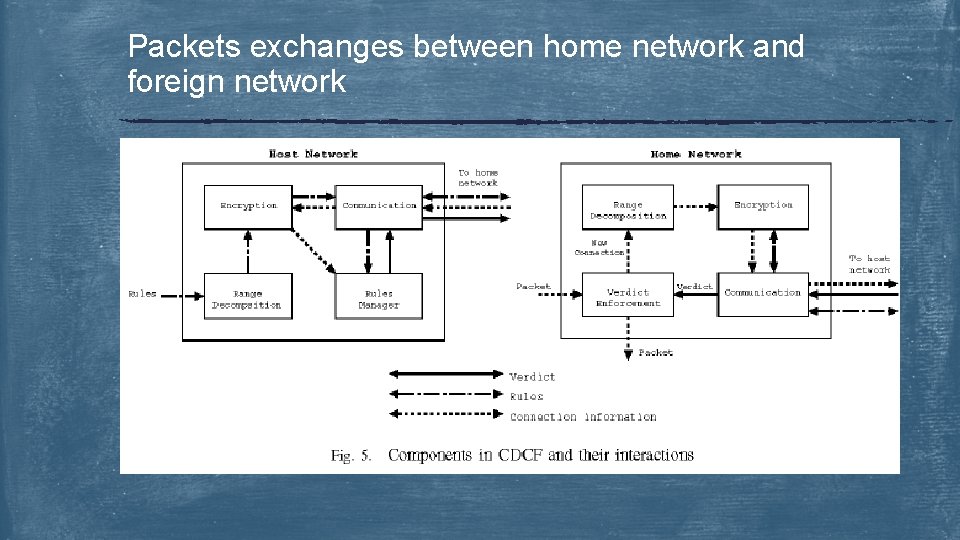
Packets exchanges between home network and foreign network
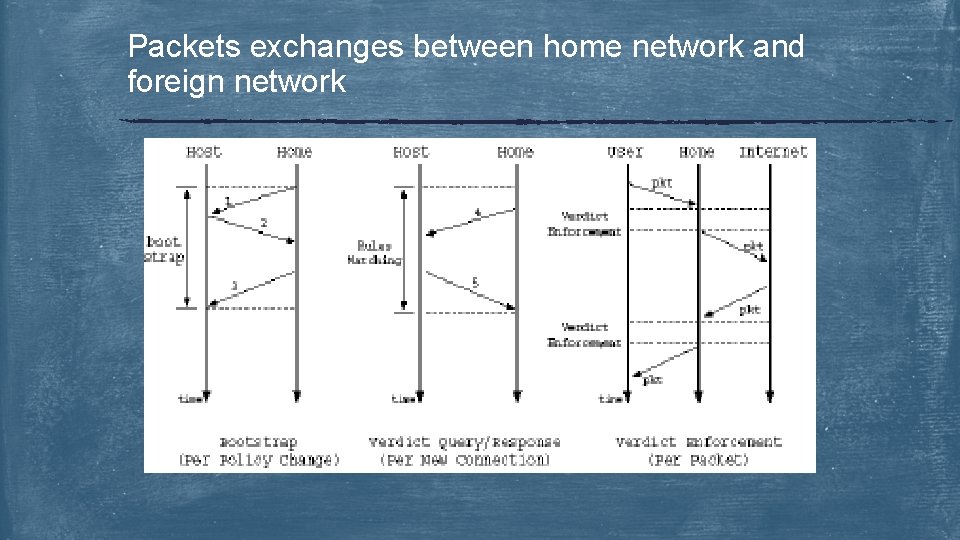
Packets exchanges between home network and foreign network
Experiment Results u CDCF overhead which includes the following : 1 - Overhead of Bootstrapping Phase 2 - Overhead of the Verdict Query/Reply Phase 3 - Overhead of the Verdict Enforcement Phase u Storage Requirements u Privacy Evaluation
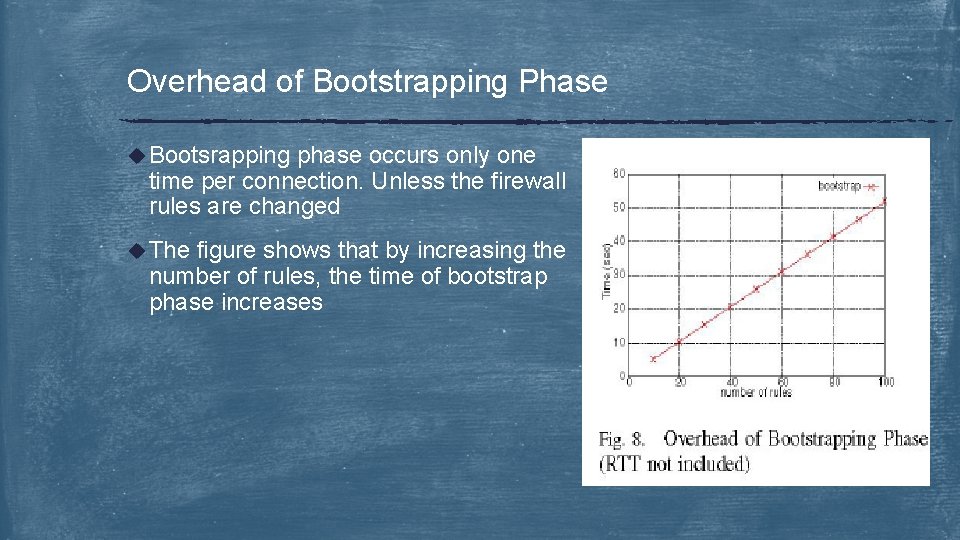
Overhead of Bootstrapping Phase u Bootsrapping phase occurs only one time per connection. Unless the firewall rules are changed u The figure shows that by increasing the number of rules, the time of bootstrap phase increases
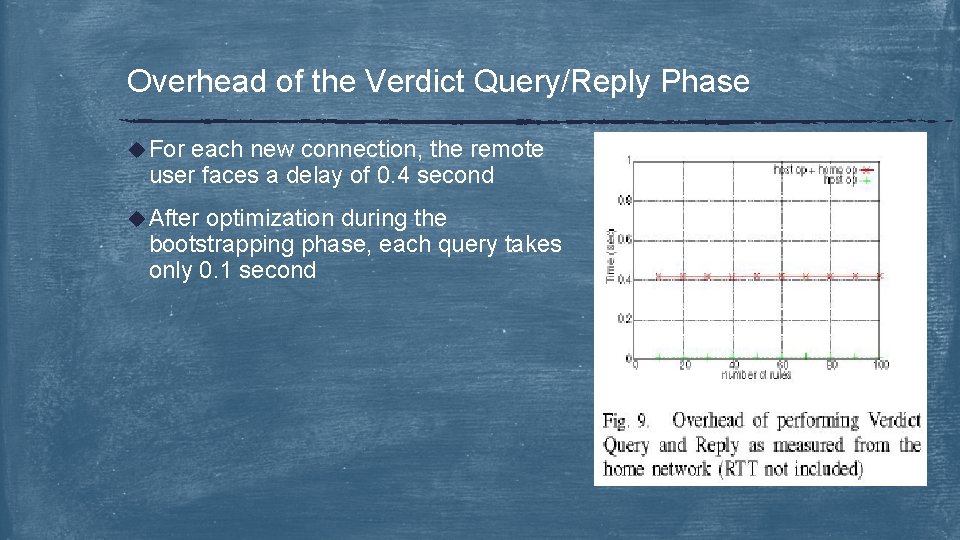
Overhead of the Verdict Query/Reply Phase u For each new connection, the remote user faces a delay of 0. 4 second u After optimization during the bootstrapping phase, each query takes only 0. 1 second
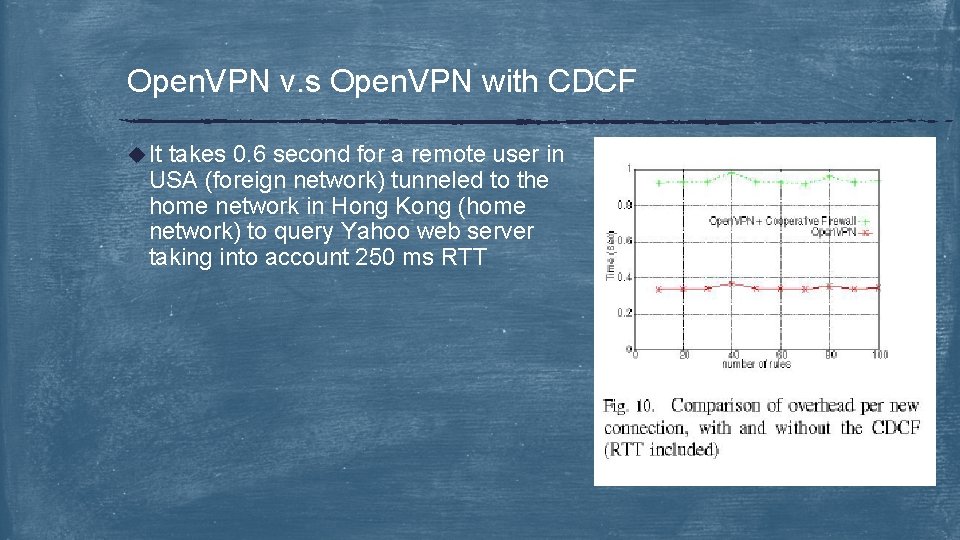
Open. VPN v. s Open. VPN with CDCF u It takes 0. 6 second for a remote user in USA (foreign network) tunneled to the home network in Hong Kong (home network) to query Yahoo web server taking into account 250 ms RTT
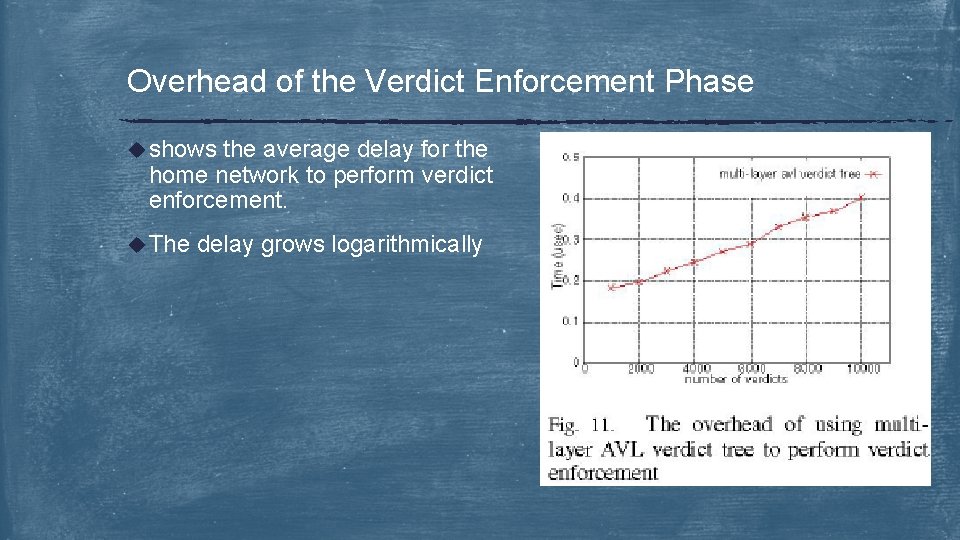
Overhead of the Verdict Enforcement Phase u shows the average delay for the home network to perform verdict enforcement. u The delay grows logarithmically
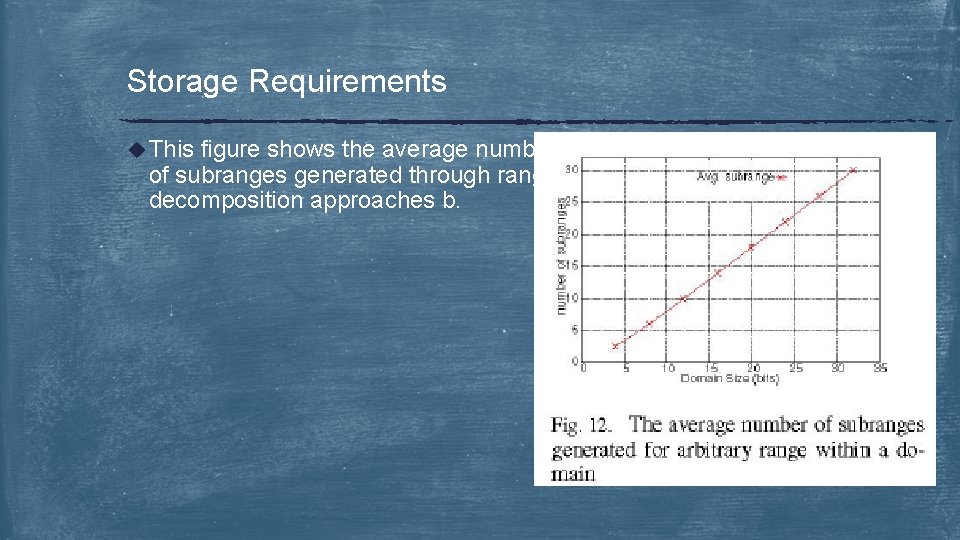
Storage Requirements u This figure shows the average number of subranges generated through range decomposition approaches b.
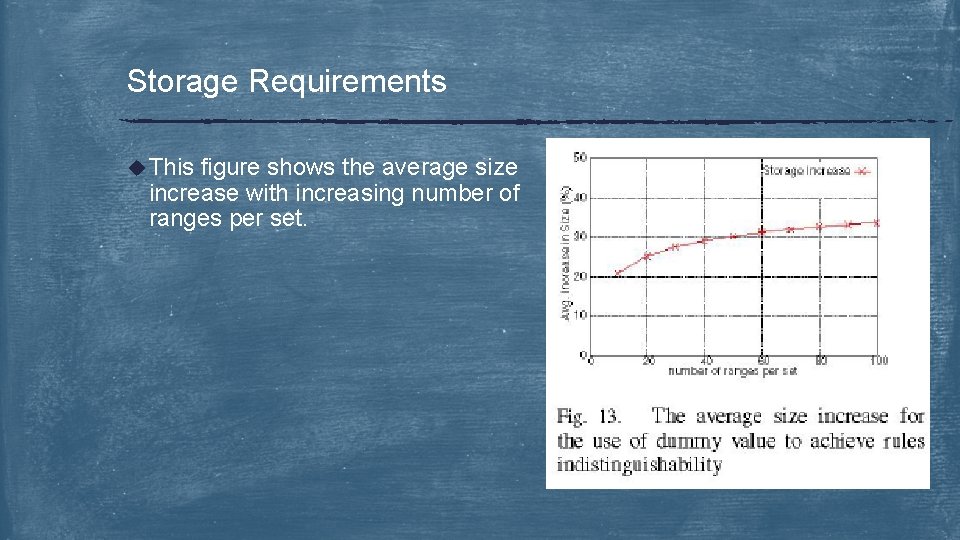
Storage Requirements u This figure shows the average size increase with increasing number of ranges per set.
Privacy evaluation u The home network never reveals its firewall rules u The foreign network reveals its firewall rules during the bootstrapping phase in encrypted form and the encryption key is never revealed u Rule matching is performed by the foreign network on the double encrypted traffic information. Therefore; the home network can not cache the rules and predict the decisions. u The privacy of the user depends on the foreign network firewall rules and user usage pattern. To protect user information traffic the home network send dummy queries when the foreign network firewall rules are minimal
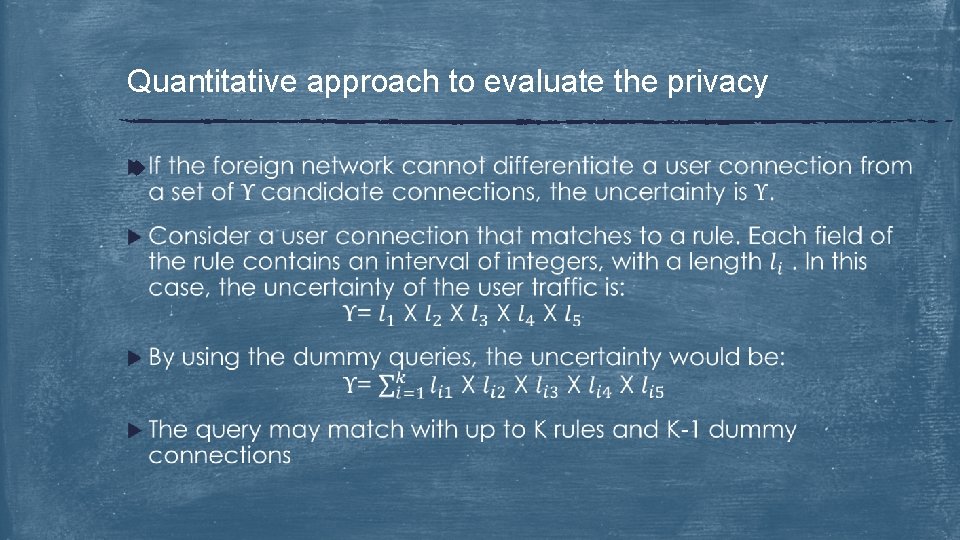
Quantitative approach to evaluate the privacy u
Issues with CDCF u Firewall u Transit u User Rules Network Firewalls Traffic Privacy u Firewall Ruleset Privacy
Issues with CDCF – Firewall rules u In the current CDCF design, the firewall rule is a 4 tuples (src_IP), (dst_IP), (src_port), (dst_port). The rules can be extended to include other fields such as payload or scan for certain IP options. u The downside here is every rule is double encrypted and the encryption is done on every byte. Meaning that if we have a packet with 1000 byte, we need to perform 1000 encryptions
Issues with CDCF – Transit Network Firewalls u CDCF considers only 2 networks ( home network and foreign network). However, CDCF can be applied to transit networks to enforce their policies as well. u The u home network considers transit networks as foreign networks. One additional bootstrapping phase is added for every transit network and is performed by the home network. To increase efficiency, the home network can send queries to transit networks on parallel.
Issues with CDCF – User Traffic Privacy u If the number of concurrent user connections is small, the dummy technique is not very effective. u Why ? u Because even randomly generated numbers can have non-trivial success probability
Issues with CDCF -- Firewall Ruleset Privacy u CDCF design doesn’t guarantee perfect privacy for the foreign network in the presence of probing. u The remote user can perform probing through brute-force trail/error technique to learn about the firewall rules. u Since we are trying to protect the foreign network from the home network and since the remote users can perform probing. The home network can not do better than what the users can do ( brute-force probing)
![Related Work u [22] "Firewall policy advisor for anomaly detection and rule editing” and Related Work u [22] "Firewall policy advisor for anomaly detection and rule editing” and](http://slidetodoc.com/presentation_image_h2/55ec1e12cb0394f4474e6414e4daac73/image-47.jpg)
Related Work u [22] "Firewall policy advisor for anomaly detection and rule editing” and [23] "Discovery of policy anomalies in distributed firewalls” provide identification and modeling of rule conflicts between different firewalls u [17] "Implementing a distributed firewall” shows the difference between cross-domain firewall, distributed firewall, and multilayer firewall u [18] "A security scheme for protecting security policies in firewall”. This paper presents securing the firewall rules through encrypting them but never share them with other firewalls
Questions & Discussion Thank you !
- Slides: 48