Chapter 11 ECommerce Security and Fraud Issues and
- Slides: 38
Chapter 11 E-Commerce Security and Fraud Issues and Protections
Learning Objectives 1. Understand the importance and scope of security of information systems for EC. 2. Describe the major concepts and terminology of EC security. 3. Understand about the major EC security threats, vulnerabilities, and technical attacks. 4. Understand Internet fraud, phishing, and spam. 5. Describe the information assurance security principles. 6. Describe the major technologies for protection of EC networks, including access control. 7. Describe various types of controls and special defense mechanisms. 8. Describe consumer and seller protection from fraud. 9. Discuss enterprisewide implementation issues for EC security. 10. Understand why it is so difficult to stop computer crimes. 11. Discuss the future of EC.
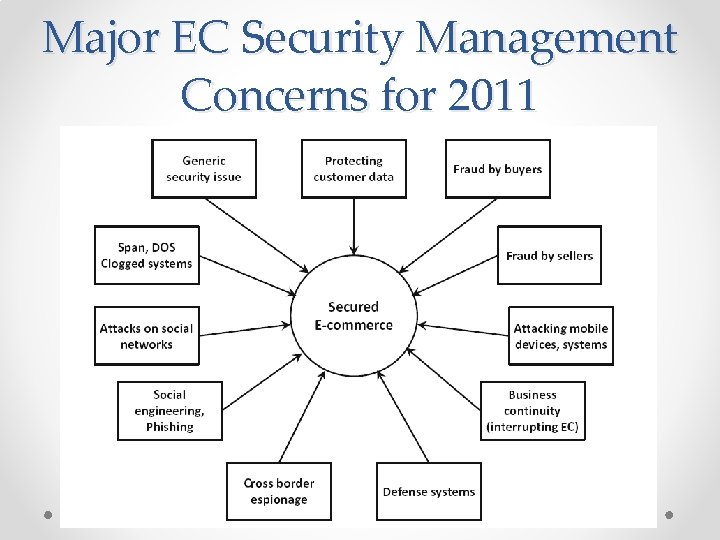
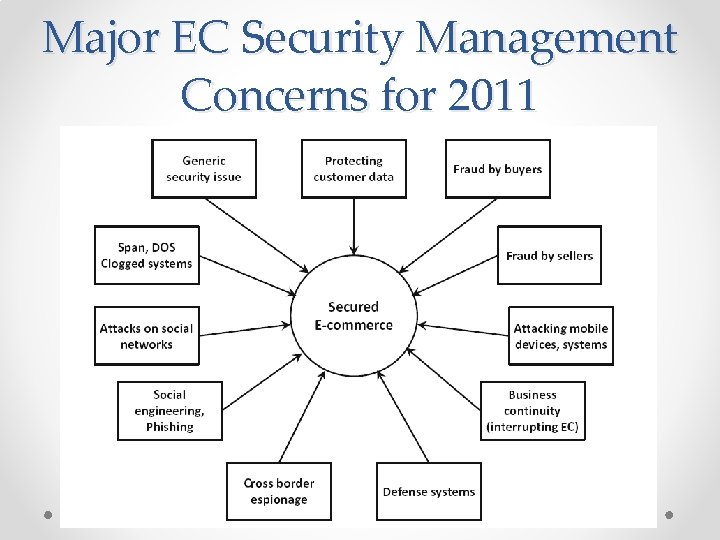
Major EC Security Management Concerns for 2011
The Information Security Problem • Cyberwars and Cyberespionage Across Borders o Cyberwarefare o Attacking Information Systems o Types of Attacks 1. Corporate espionage 2. Political espionage and warfare
The Information Security Problem • The Drivers of EC Security Problems o The Internet’s Vulnerable Design o The Shift to Profit-Induced Crimes o The Increased Volume of Wireless Activities and the Number of Mobile Devices o The Globalization of the Attackers o The *Darknet o *Internet Underground Economy • The Internet Silk Road • *Keystroke logging (keylogging) o o The Explosion of Social Networking The Dynamic Nature of EC Systems and the Acts of Insiders The Sophistication of the Attacks The Cost of Cyber Crime
Basic E-Commerce Security Issues and Landscape • Basic Security Terminology o o o *Business continuity plan *Cybercrime *Cybercriminal *Exposure *Fraud *Malware (malicious software) *Phishing *Risk *Social engineering *Spam *Vulnerability *Zombie
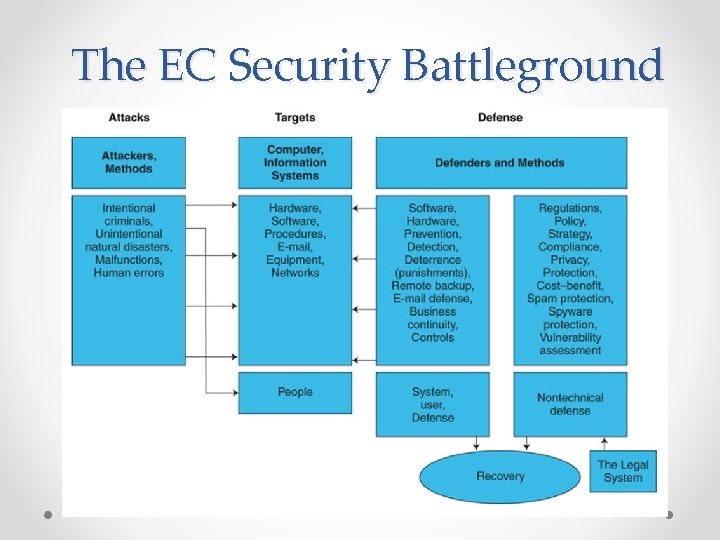
Basic E-Commerce Security Issues and Landscape • The EC Security Battleground o The attacks, the attackers, and their strategies o The assets that are being attacked (the targets) in vulnerable areas o The security defense, the defenders, and their methods and strategy
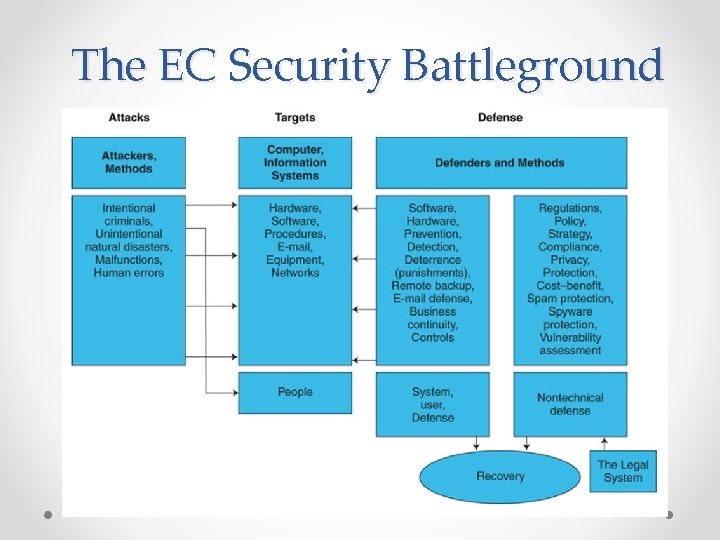
The EC Security Battleground
Basic E-Commerce Security Issues and Landscape • The Threats, Attacks, and Attackers o Unintentional Threats • Human Error • Environmental Hazards • Malfunctions in the Computer System o Intentional Attacks and Crimes o The Criminals and Methods • *Hacker • *Cracker
Basic E-Commerce Security Issues and Landscape • The Targets of the Attacks in Vulnerable Areas o Vulnerable Areas Are Being Attacked • Vulnerability Information • Attacking E-Mail • Attacking Smartphones and Wireless Systems • The Vulnerability of RFID Chips o The Vulnerabilities in Business IT and EC Systems o Pirated Videos, Music, and Other Copyrighted Material
Basic E-Commerce Security Issues and Landscape • EC Security Requirements o *Authentication o o *Authorization Auditing Availability *Nonrepudiation
Basic E-Commerce Security Issues and Landscape • The Defense: Defenders, Strategy, and Methods o EC Defense Programs and Strategy • • • *EC security strategy *Deterrent methods *Prevention measures *Detection measures *Information assurance (IA) o Possible Punishment o Defense Methods and Technologies • Recovery
Technical Malware Attack Methods: From Viruses to Denial of Service • Technical and Nontechnical Attacks: An Overview o The Major Technical Attack Methods o Malware (Malicious Code): Viruses, Worms, and Trojan Horses o * Viruses o * Worms
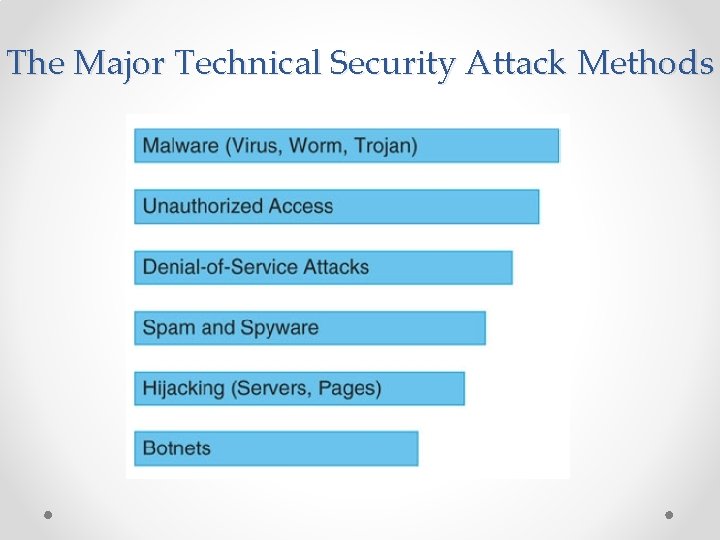
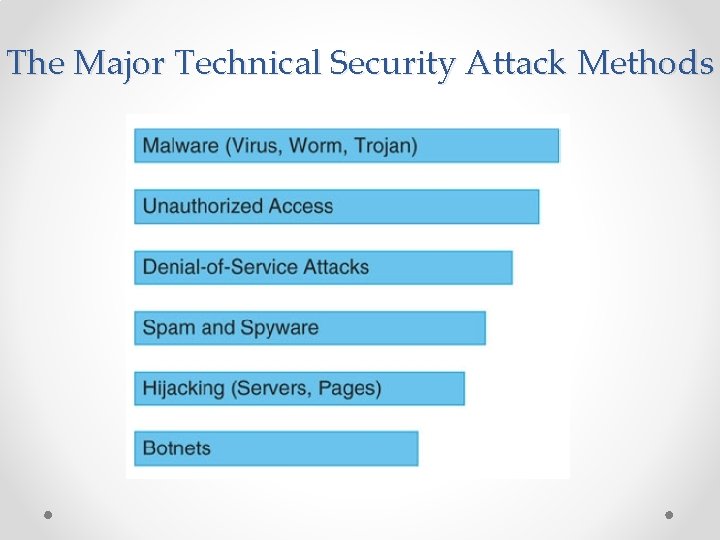
The Major Technical Security Attack Methods
Technical Malware Attack Methods: From Viruses to Denial of Service o * Macro virus (macro worm) o * Trojan horse o Some Recent Security Bugs: Heartbleed and Crytolocker o * Denial-of-service (Do. S) attack o Web Server and Web Page Hijacking • * Page hijacking o * Botnets o Malvertising
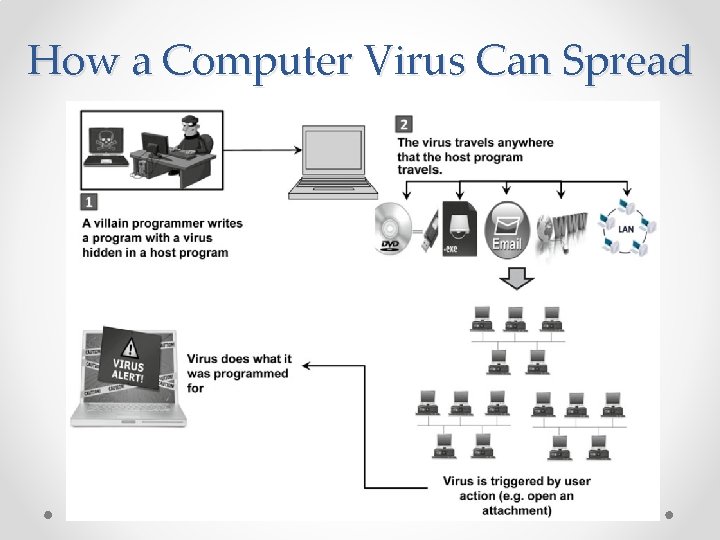
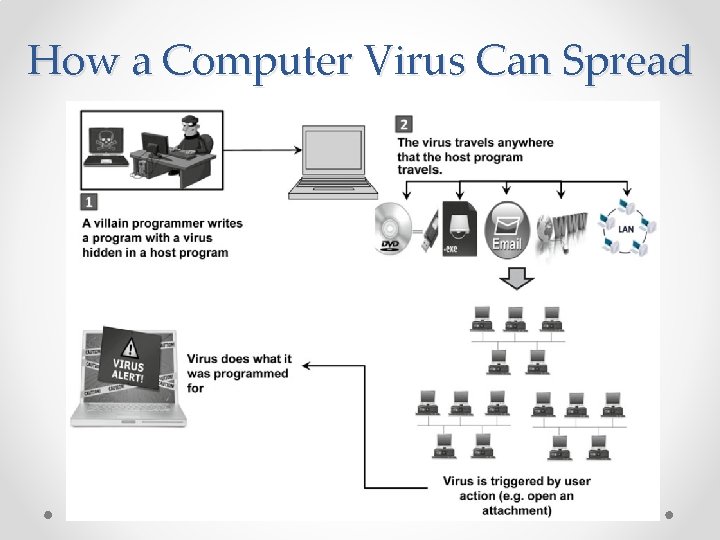
How a Computer Virus Can Spread
Nontechnical Methods: From Phishing to Spam and Fraud • Social Engineering and Fraud • Social Phishing o *Pharming • Fraud and Scams on The Internet o o Examples of Typical Online Fraud Attacks E-Mail Scams Top 10 Attacks and Remedies *Identity Theft and Identify Fraud • Cyber Bank Robberies
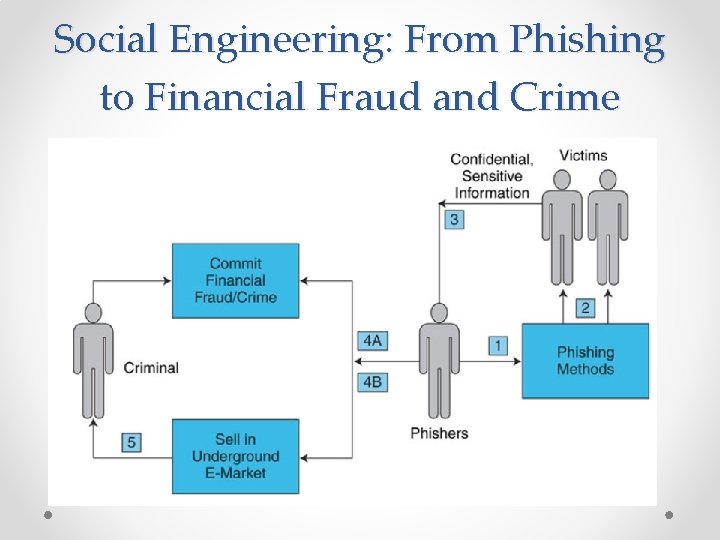
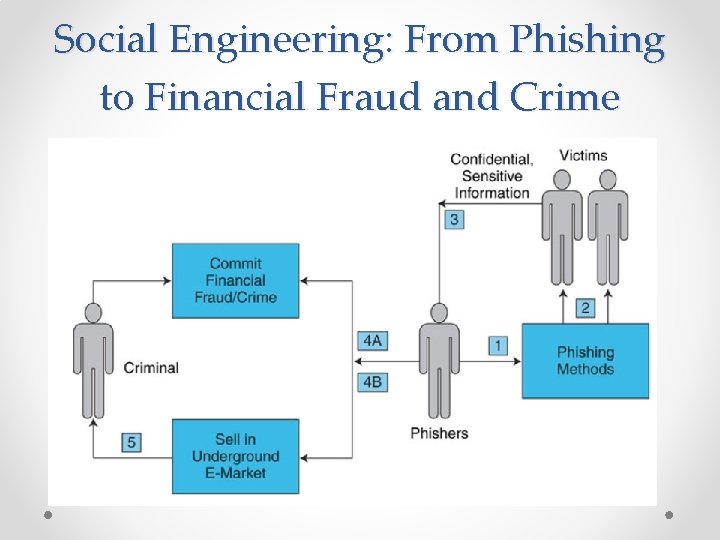
Social Engineering: From Phishing to Financial Fraud and Crime
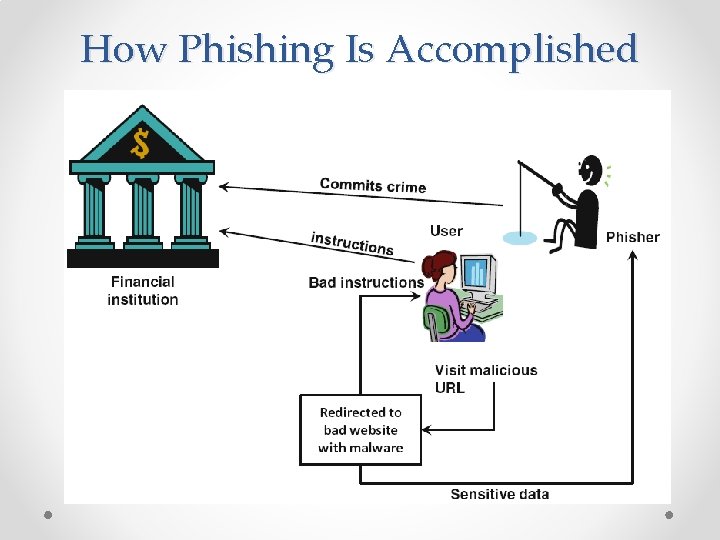
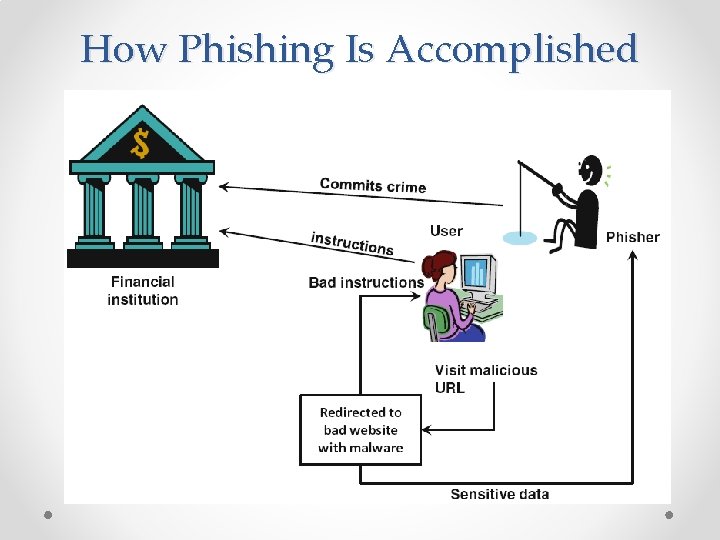
How Phishing Is Accomplished
Nontechnical Methods: From Phishing to Spam and Fraud • Spam Attacks o *E-mail spam o Typical Examples of Spamming o *Spyware • Social Networking Makes Social Engineering Easy o o How Hackers Are Attacking Social Networks Spam in Social Networks and in the Web 2. 0 Environment *Search engine spam *Splog • *Data Breach (Leak)
The Information Assurance Model And Defense Strategy • Confidentiality, Integrity, and Availability 1. *Confidentiality 2. *Integrity 3. *Availability • Authentication, Authorization, and Nonrepudiation
The Information Assurance Model And Defense Strategy • E-Commerce Security Strategy o The Phases of Security Defense 1. 2. 3. 4. 5. 6. 7. 8. Prevention and deterrence (preparation) Initial response Detection Containment (contain the damage) Eradication Recovery Correction Awareness and compliance o Security Spending Versus Needs Gap
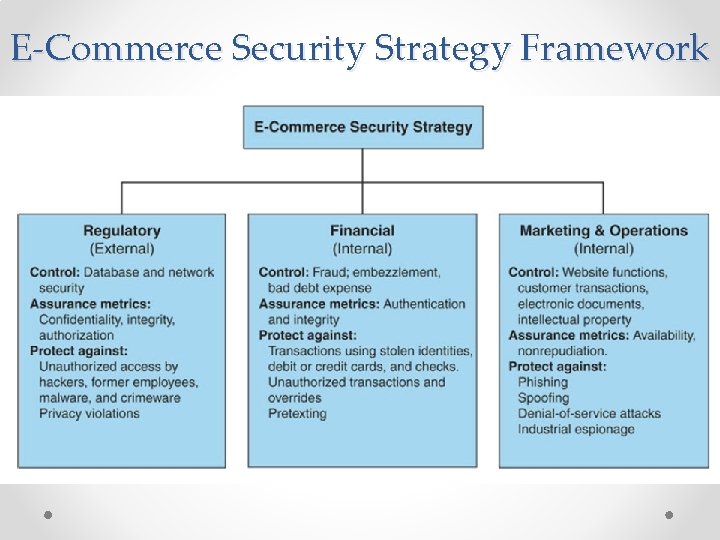
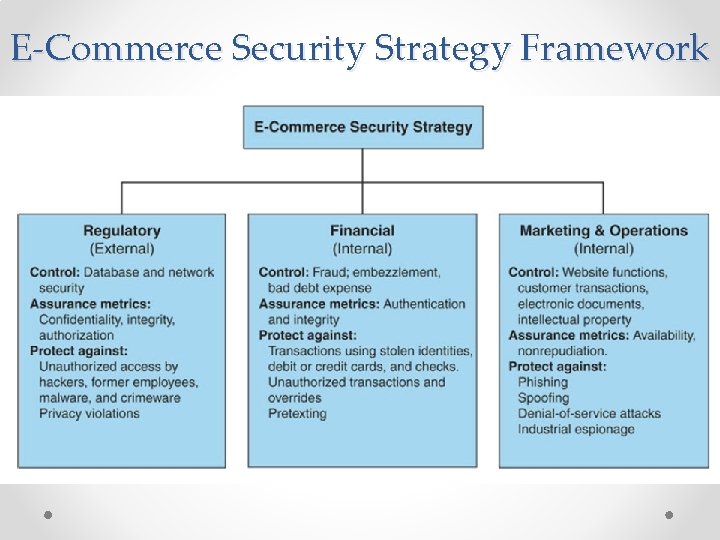
E-Commerce Security Strategy Framework
The Information Assurance Model And Defense Strategy • The Defense Side of EC Systems 1. Defending access to computing systems, data flow, and EC transactions 2. Defending EC networks 3. General, administrative, and application controls 4. Protection against social engineering and fraud 5. Disaster preparation, business continuity, and risk management 6. Implementing enterprisewide security programs 7. Conduct a vulnerability assessment and a penetration test o Assessing Vulnerabilities and Security Needs • *Vulnerability assessment o *Penetration test (pen test)
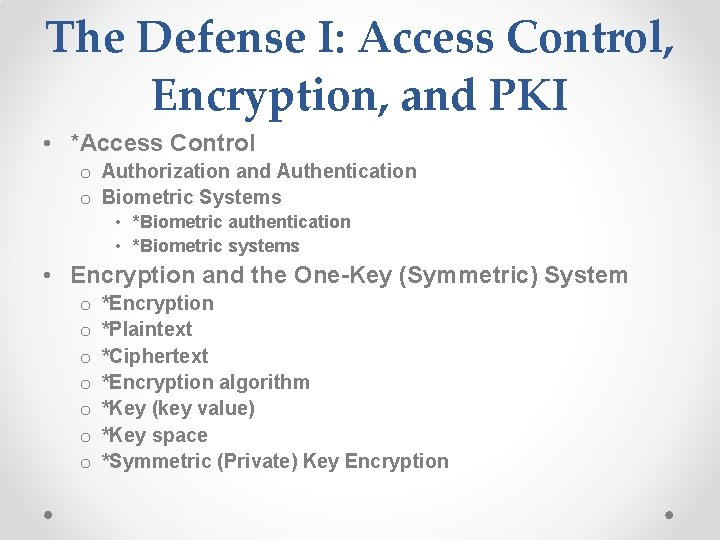
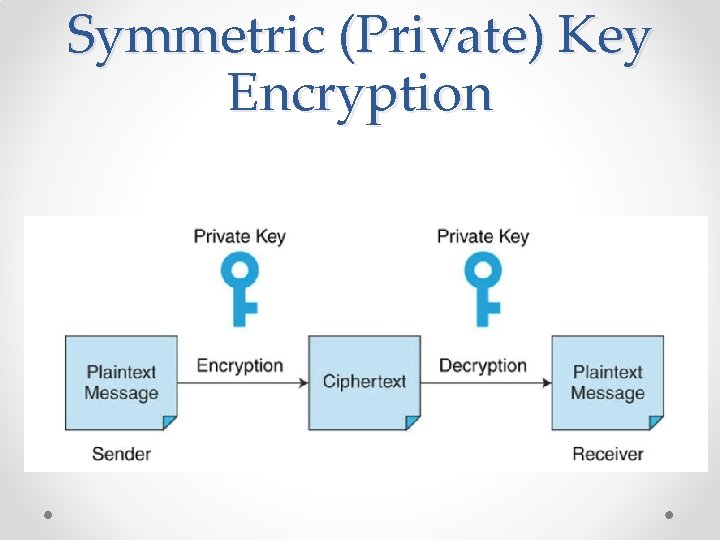
The Defense I: Access Control, Encryption, and PKI • *Access Control o Authorization and Authentication o Biometric Systems • *Biometric authentication • *Biometric systems • Encryption and the One-Key (Symmetric) System o o o o *Encryption *Plaintext *Ciphertext *Encryption algorithm *Key (key value) *Key space *Symmetric (Private) Key Encryption
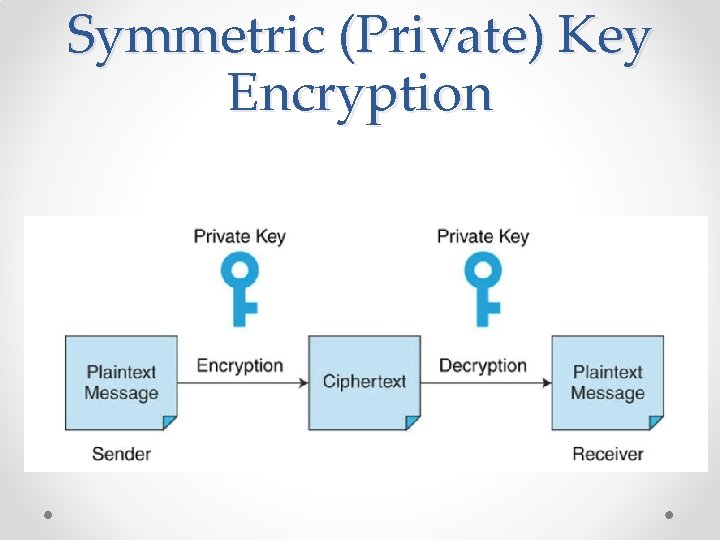
Symmetric (Private) Key Encryption
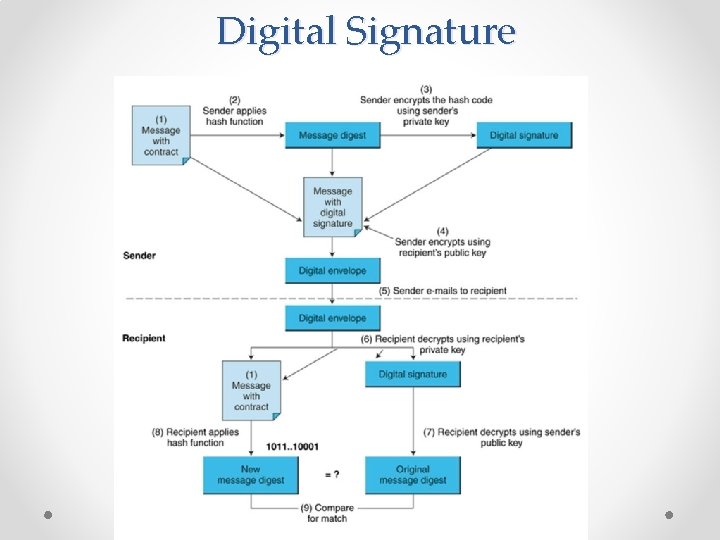
The Defense I: Access Control, Encryption, and PKI • *Public key infrastructure (PKI) o *Public (asymmetric) key encryption • *Public key • *Private key o The PKI Process: Digital Signatures and Certificate Authorities • • • *Digital signatures *Hash function *Message digest *Digital envelope *Certificate authorities (CAs) o Secure Socket Layer (SSL) • Other Topics and Methods of Defense
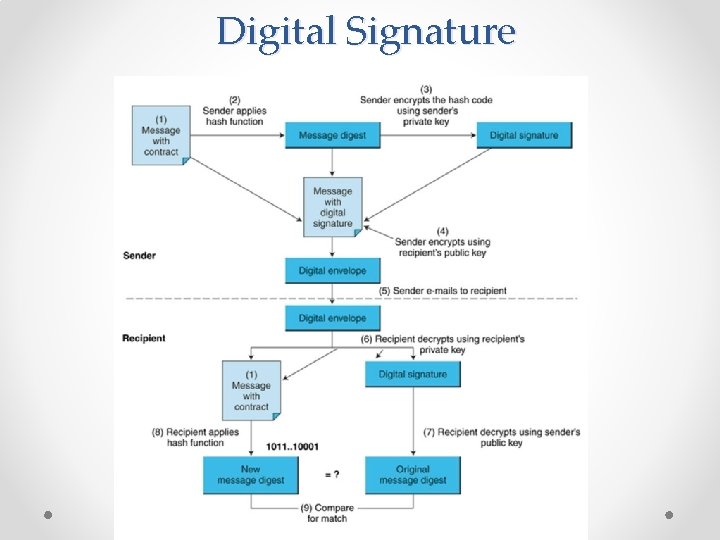
Digital Signature
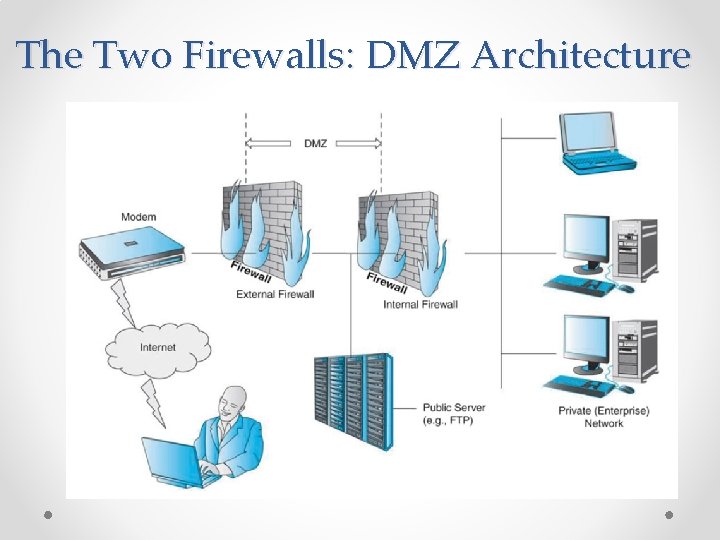
The Defense II: Securing E-Commerce Networks • *Firewalls o *Packets o The Dual Firewall Architecture: The DMZ o *Personal Firewalls • *Virtual private network (VPN) o *Protocol tunneling • *Intrusion Detection Systems (IDS) o Cloud Computing Prevents Do. S Attacks • Honeynets and Honeypots o *Honeynet o *Honeypots o E-Mail Security
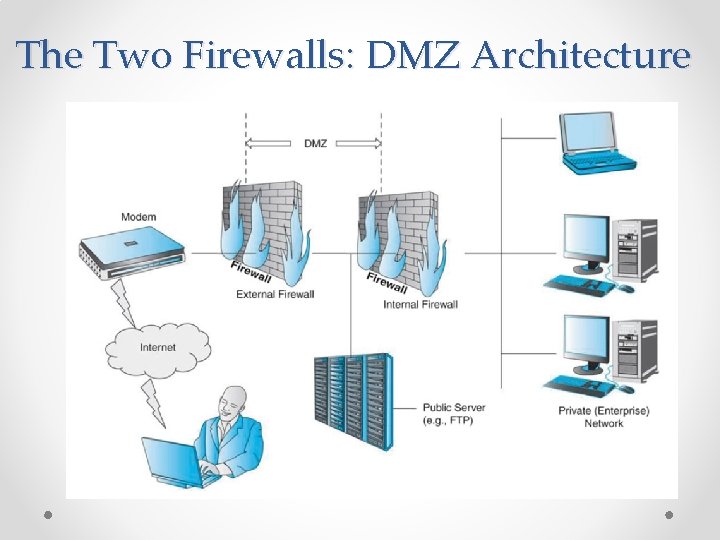
The Two Firewalls: DMZ Architecture
The Defense III: General Controls, Spam, Pop Ups, Fraud, And Social Engineering Controls • *General controls • *Application controls • General, Administrative, and Other Controls o Physical Controls o Administrative Controls • Protecting Against Spam o *CAN-SPAM Act
The Defense III: General Controls, Spam, Pop Ups, Fraud, And Social Engineering Controls • Protecting Your Computer from Pop-Up Ads o Tools for Stopping or at Least Minimizing Pop-Ups • Protecting against Other Social Engineering Attacks o Protecting against Phishing o Protecting against Malvertising • Protecting Against Spyware • Protecting Against Cyberwars
The Defense III: General Controls, Spam, Pop Ups, Fraud, And Social Engineering Controls • Fraud Protection • Business Continuity, Disaster Recovery, and Risk Management o Risk-Management and Cost-Benefit Analysis
Implementing Enterprisewide E-Commerce Security • The Drivers of EC Security Management • Senior Management Commitment and Support • EC Security Policies and Training o Cyber Threat Intelligence (CTI) • EC Risk Analysis and Ethical Issues o *Business impact analysis (BIA) o Ethical Issues
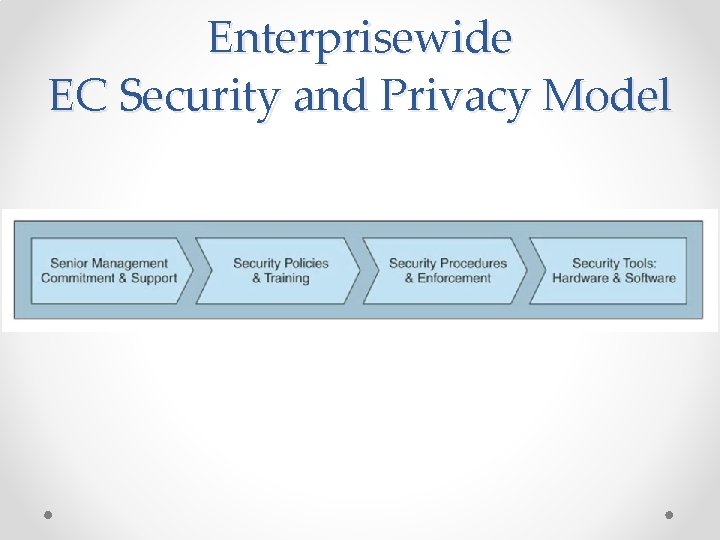
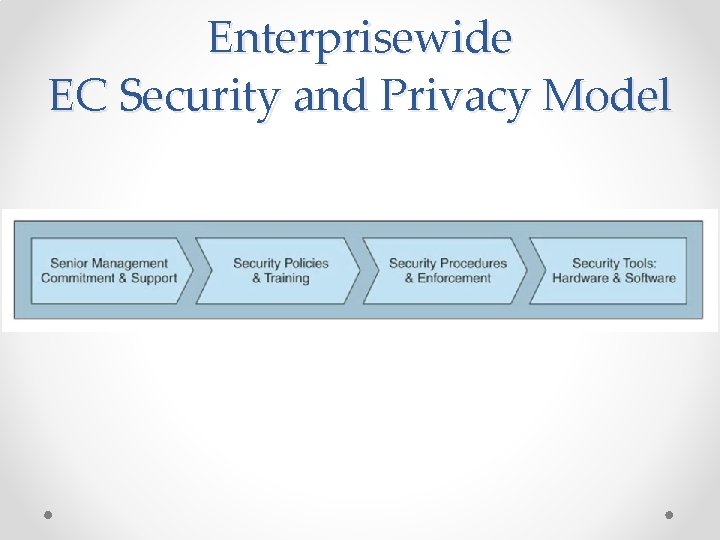
Enterprisewide EC Security and Privacy Model
Implementing Enterprisewide E-Commerce Security • Why Is It Difficult to Stop Internet Crime? o o o Making Shopping Inconvenient Lack of Cooperation by Business Partners Shoppers’ Negligence Ignoring EC Security Best Practices Design and Architecture Issues Lack of Due Care in Business Practices • *Standard of due care • Protecting Mobile Devices, Networks, and Applications o Mobile Security Issues o The Defense
Managerial Issues 1. What steps should businesses follow in establishing a security plan? 2. Should organizations be concerned with internal security threats? 3. What is the key to establishing strong e-commerce security? 4. What should we do in case we are victims of ransomware?
1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Summary The importance and scope of EC information security. Basic EC security issues. Threats, vulnerabilities, and technical attacks. Internet fraud, phishing, and spam. Information assurance. Securing EC access control and communications The different controls and special defense mechanisms Fraud on the Internet and how to protect consumers and sellers against it. 11. Enterprisewide EC security. 12. Why is it so difficult to stop computer crimes? 13. The future of EC