Security Program and Policies Principles and Practices by
Security Program and Policies Principles and Practices by Sari Stern Greene Chapter 8: Communications and Operations Security
Objectives q q q q q Author useful standard operating procedures Implement change control processes Understand the importance of patch management Protect information systems against malware Consider data backup and replication strategies Recognize the security requirements of email and email systems Appreciate the value of log data and analysis Evaluate service provider relationships Write policies and procedures to support operational and communications security Copyright 2014 Pearson Education, Inc. 2
Standard Operating Procedures (SOPs) q SOPs- what is SOP? n n q are detailed explanations of how to perform a task. provide direction to improve communication, reduce training time, and improve work consistency Alternative name: std. operating protocols It communicates who, how, where, when a task will be performed what materials needed. Why SOP? SOPs should be documented to protect the company from the pitfalls of institutional knowledge n If a business process is only known by one employee, and that employee becomes unavailable, how is this process going to be performed successfully? Copyright 2014 Pearson Education, Inc. 3
Standard Operating Procedures Cont. n n n After a procedure has been researched, documented, reviewed, and tested, it should be authorized by the process owner. Reviewer: analyses the document for readability and clarity Verifier: tests to check correctness of steps Process owner : authorizes, publishes and distributes. The integrity of the SOP documents must be protected so that employees don’t follow instructions that have been maliciously tampered with, or using some wrong version! Copyright 2014 Pearson Education, Inc. 4
Standard Operating Procedures Cont. developing SOPs n n n SOPs should be written in as simple a style as possible for all to clearly understand the procedures SOPs should include all steps of a given procedure SOPs should not be overly detailed and should remain clear Copyright 2014 Pearson Education, Inc. 5
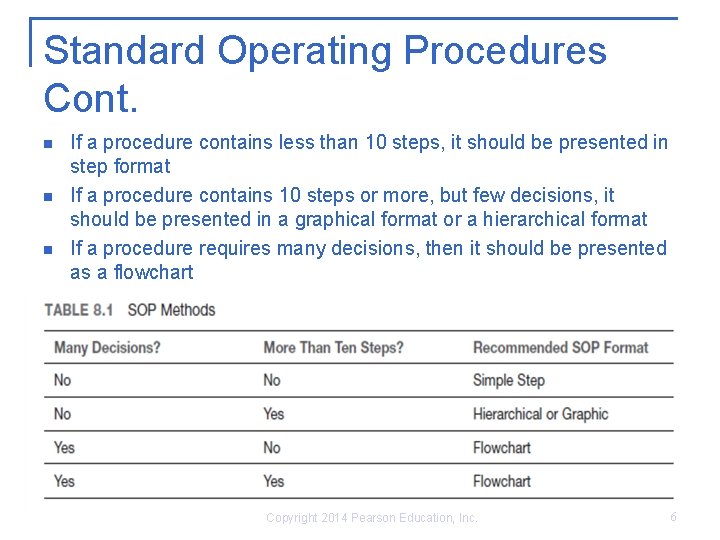
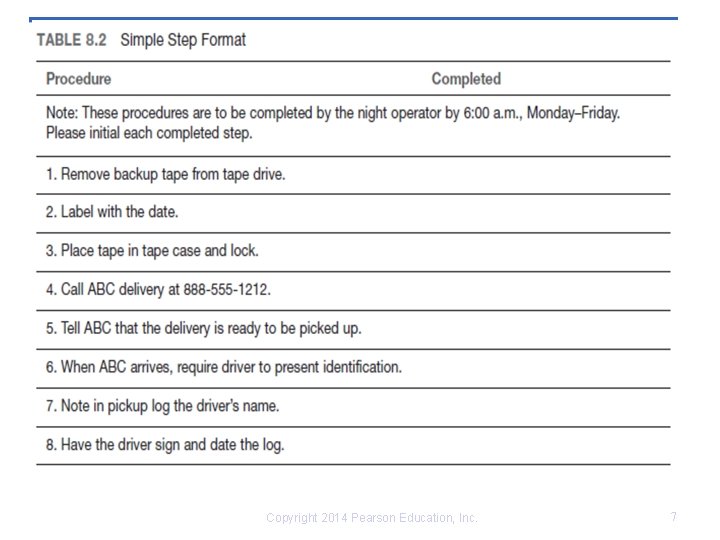
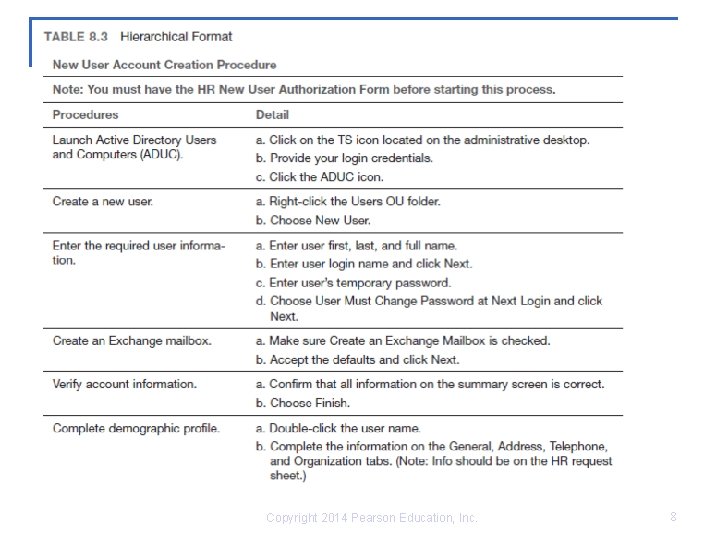
Standard Operating Procedures Cont. n n n If a procedure contains less than 10 steps, it should be presented in step format If a procedure contains 10 steps or more, but few decisions, it should be presented in a graphical format or a hierarchical format If a procedure requires many decisions, then it should be presented as a flowchart Copyright 2014 Pearson Education, Inc. 6
Copyright 2014 Pearson Education, Inc. 7
Copyright 2014 Pearson Education, Inc. 8
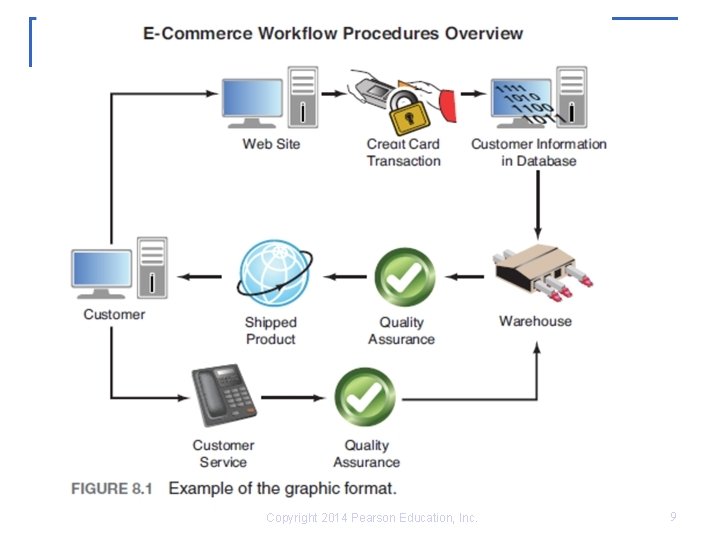
Copyright 2014 Pearson Education, Inc. 9
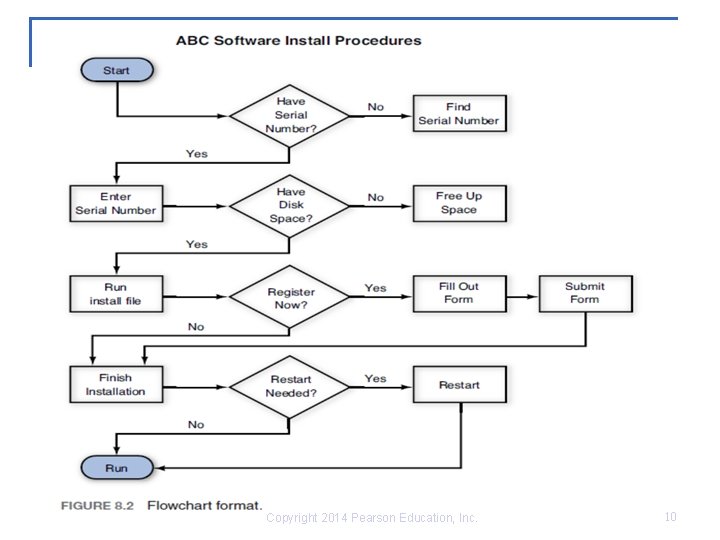
Copyright 2014 Pearson Education, Inc. 10
Standard Operating Procedures Cont. n n The change management process must be defined so that the SOPs mirror the evolution of the business processes All revisions of the SOP documents must be reviewed and approved by the process owner Copyright 2014 Pearson Education, Inc. 11
Operational Change Control n n Change control: Internal procedure by which only authorized changes are made to software, hardware, network access privileges, or business processes Objective of information security policy in change control is to ensure stability while maintaining CIA Change management process establishes an orderly mechanism for submission evaluation, approval, prioritization , scheduling, communication, implementation, monitoring, and organizational acceptance of change. Change control process q Starts with a Request for Change (RFC) q q q q Description of the proposed change Justification why the change should be implemented Impact of not implementing the change Alternatives Cost Resource requirements and timeframe The change is then evaluated and if approved implemented Copyright 2014 Pearson Education, Inc. 12
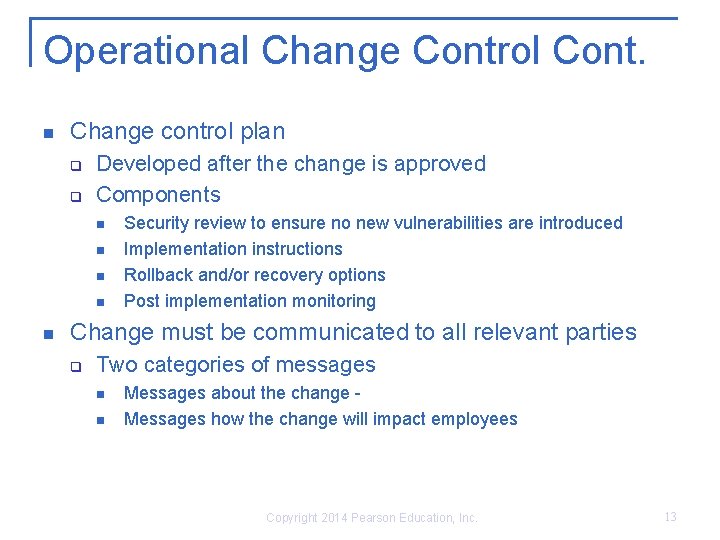
Operational Change Control Cont. n Change control plan q q Developed after the change is approved Components n n n Security review to ensure no new vulnerabilities are introduced Implementation instructions Rollback and/or recovery options Post implementation monitoring Change must be communicated to all relevant parties q Two categories of messages n n Messages about the change - Messages how the change will impact employees Copyright 2014 Pearson Education, Inc. 13
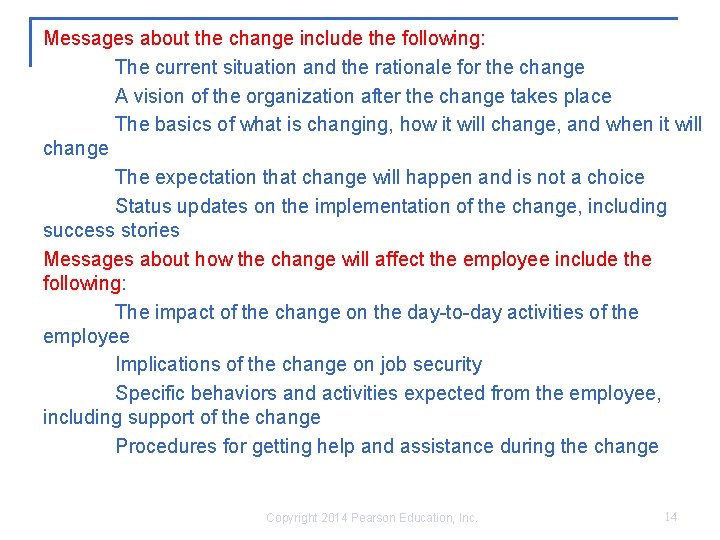
Messages about the change include the following: The current situation and the rationale for the change A vision of the organization after the change takes place The basics of what is changing, how it will change, and when it will change The expectation that change will happen and is not a choice Status updates on the implementation of the change, including success stories Messages about how the change will affect the employee include the following: The impact of the change on the day-to-day activities of the employee Implications of the change on job security Specific behaviors and activities expected from the employee, including support of the change Procedures for getting help and assistance during the change Copyright 2014 Pearson Education, Inc. 14
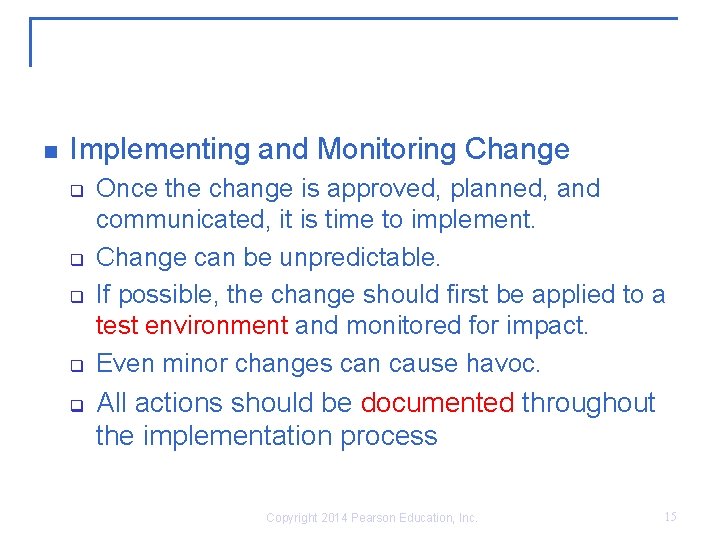
n Implementing and Monitoring Change q q q Once the change is approved, planned, and communicated, it is time to implement. Change can be unpredictable. If possible, the change should first be applied to a test environment and monitored for impact. Even minor changes can cause havoc. All actions should be documented throughout the implementation process Copyright 2014 Pearson Education, Inc. 15
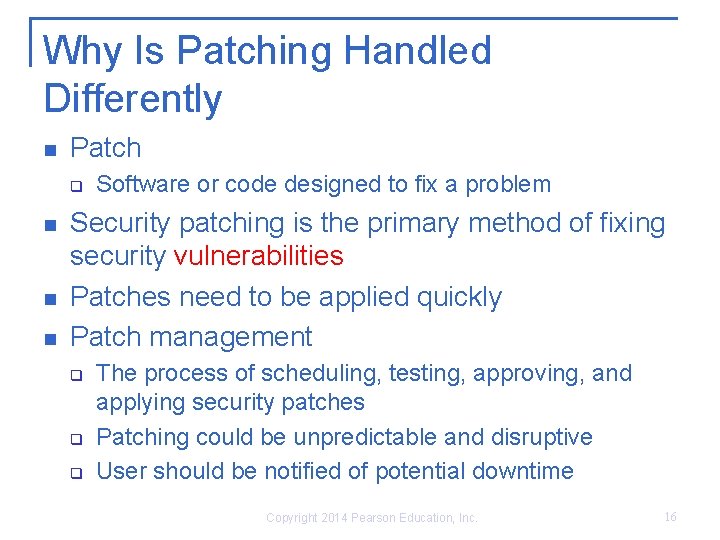
Why Is Patching Handled Differently n Patch q n n n Software or code designed to fix a problem Security patching is the primary method of fixing security vulnerabilities Patches need to be applied quickly Patch management q q q The process of scheduling, testing, approving, and applying security patches Patching could be unpredictable and disruptive User should be notified of potential downtime Copyright 2014 Pearson Education, Inc. 16
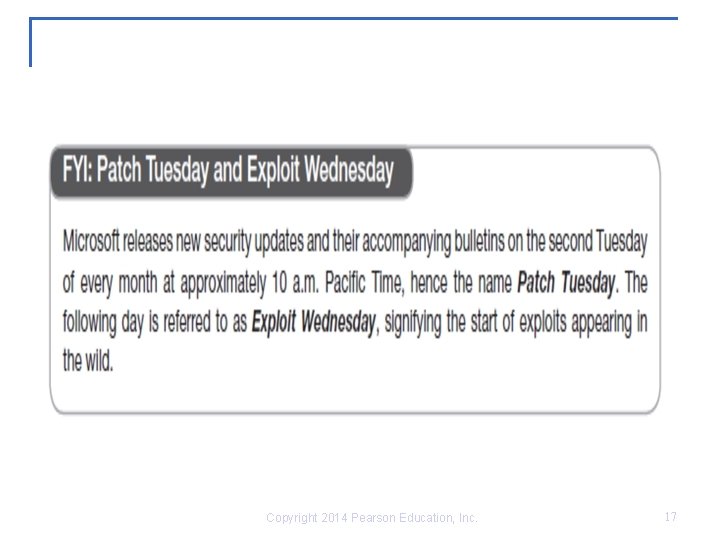
Copyright 2014 Pearson Education, Inc. 17
Malware Protection n Malware q q Short for malicious software Software designed to disrupt computer operation, gather sensitive information, or gain unauthorized access to computer systems and mobile devices It can be bundled with other programs or selfreplicated Typically requires user interaction Copyright 2014 Pearson Education, Inc. 18
Malware Protection cont. n Malware categories q q q q Virus Worm Trojans Bots Ransomware Rootkits Spyware/adware Hybrid Copyright 2014 Pearson Education, Inc. 19
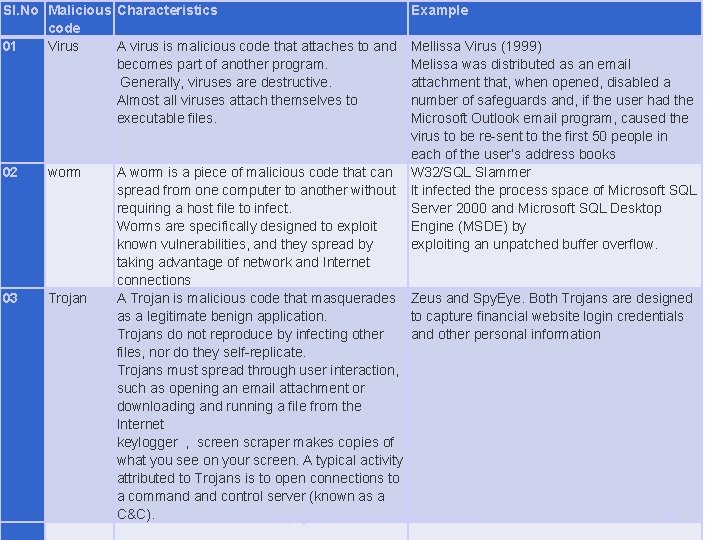
Sl. No Malicious Characteristics code 01 Virus A virus is malicious code that attaches to and becomes part of another program. Generally, viruses are destructive. Almost all viruses attach themselves to executable files. 02 worm 03 Trojan Example Mellissa Virus (1999) Melissa was distributed as an email attachment that, when opened, disabled a number of safeguards and, if the user had the Microsoft Outlook email program, caused the virus to be re-sent to the first 50 people in each of the user’s address books A worm is a piece of malicious code that can W 32/SQL Slammer spread from one computer to another without It infected the process space of Microsoft SQL requiring a host file to infect. Server 2000 and Microsoft SQL Desktop Worms are specifically designed to exploit Engine (MSDE) by known vulnerabilities, and they spread by exploiting an unpatched buffer overflow. taking advantage of network and Internet connections A Trojan is malicious code that masquerades Zeus and Spy. Eye. Both Trojans are designed as a legitimate benign application. to capture financial website login credentials Trojans do not reproduce by infecting other and other personal information files, nor do they self-replicate. Trojans must spread through user interaction, such as opening an email attachment or downloading and running a file from the Internet keylogger , screen scraper makes copies of what you see on your screen. A typical activity attributed to Trojans is to open connections to a command control server (known as a C&C). 20 Copyright 2014 Pearson Education, Inc.
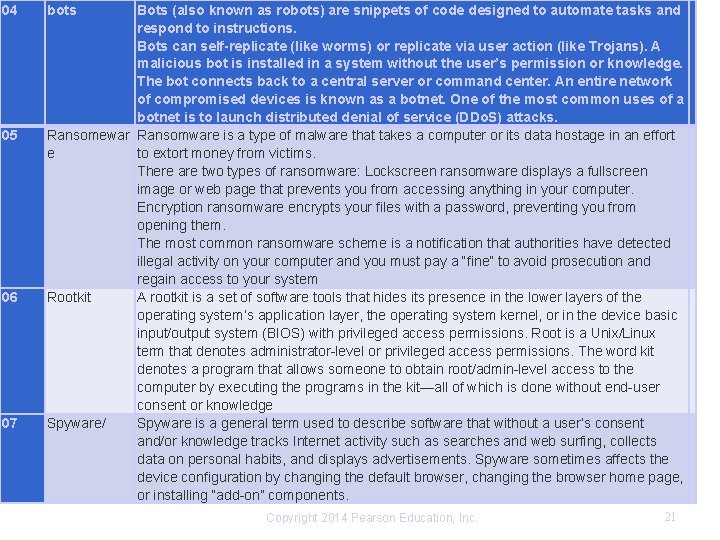
04 05 06 07 bots Bots (also known as robots) are snippets of code designed to automate tasks and respond to instructions. Bots can self-replicate (like worms) or replicate via user action (like Trojans). A malicious bot is installed in a system without the user’s permission or knowledge. The bot connects back to a central server or command center. An entire network of compromised devices is known as a botnet. One of the most common uses of a botnet is to launch distributed denial of service (DDo. S) attacks. Ransomewar Ransomware is a type of malware that takes a computer or its data hostage in an effort e to extort money from victims. There are two types of ransomware: Lockscreen ransomware displays a fullscreen image or web page that prevents you from accessing anything in your computer. Encryption ransomware encrypts your files with a password, preventing you from opening them. The most common ransomware scheme is a notification that authorities have detected illegal activity on your computer and you must pay a “fine” to avoid prosecution and regain access to your system Rootkit A rootkit is a set of software tools that hides its presence in the lower layers of the operating system’s application layer, the operating system kernel, or in the device basic input/output system (BIOS) with privileged access permissions. Root is a Unix/Linux term that denotes administrator-level or privileged access permissions. The word kit denotes a program that allows someone to obtain root/admin-level access to the computer by executing the programs in the kit—all of which is done without end-user consent or knowledge Spyware/ Spyware is a general term used to describe software that without a user’s consent and/or knowledge tracks Internet activity such as searches and web surfing, collects data on personal habits, and displays advertisements. Spyware sometimes affects the device configuration by changing the default browser, changing the browser home page, or installing “add-on” components. Copyright 2014 Pearson Education, Inc. 21
How Is Malware Controlled n Prevention controls q n Stop an attack before it occurs Detection controls q Identify the presence of malware, alert the user, and prevent the malware from carrying out its mission Copyright 2014 Pearson Education, Inc. 22
Prevention controls Impact the distribution channel by training users not to clinks embedded in email, open unexpected email attachments, irresponsibly surf the Web, download games or music, participate in peer-to-peer (P 2 P) networks, and allow remote access to their desktop. n Configure the firewall to restrict access. n Do not allow users to install software on company-provided devices. n Do not allow users to make changes to configuration settings. ■ Do not allow users to have administrative rights to their workstations. Malware runs in the security context of the logged-in user. n Do not allow users to disable (even temporarily) anti-malware software and controls. n Disable remote desktop connections. n Apply operating system and application security patches expediently. n Enable browser-based controls, including pop-up blocking, download screening, and automatic updates. n Implement an enterprise-wide antivirus/anti-malware application. It is important that the antimalware solutions be configured to update as frequently as possible because many new pieces of malicious code are released daily. 23 Copyright 2014 Pearson Education, Inc. n
Detection controls n n n Real-time firewall detection of suspicious file downloads. Real-time firewall detection of suspicious network connections. Host and network-based intrusion detection systems or intrusion prevention systems (IDS/IPS). Review and analysis of firewalls, IDS, operating systems, and application logs for indicators of compromise. User awareness to recognize and report suspicious activity. Help desk (or equivalent) training to respond to malware incidents. Copyright 2014 Pearson Education, Inc. 24
What Is Antivirus Software? n n Used to detect, contain, and in some cases eliminate malicious software Most AV software employs two techniques q q n Signature-based recognition Behavior-based (heuristic) recognition The core of AV software is known as the “engine. ” It is the basic program. The program relies on virus definition files (known as DAT files) to identify malware. A blended threat occurs when multiple variants of malware (worms, viruses, bots, and so on) are used in concert to exploit system vulnerabilities. Blended threats are specifically designed to circumvent AV and behavioral-based defenses n Copyright 2014 Pearson Education, Inc. 25
Data Replication n Data Replication q n Data backup q n The process of copying data to a second location that is available for immediate or near-time use The process of copying and storing data that can be restored to its original location Failure to back up threatens data availability and data integrity q Lost/corrupt data can also have a negative impact on the company: n Financially Legally n PR-wise n Copyright 2014 Pearson Education, Inc. 26
Is There a Recommended Backup or Replication Strategy? q The following aspects should be considered when the strategy is designed: n n n q Reliability Speed Simplicity Ease of use Security of the stored information Backed-up or replicated data should be stored at an off-site location in an environment secured from theft, the elements, and natural disasters Copyright 2014 Pearson Education, Inc. 27
The Importance of Testing q q If the company relies on backup to protect data integrity and availability, then it needs to be sure that the information stored on the backup media is restorable in case of an incident Just as it is important that a backup would take place according to a set schedule, test restores should also be officially scheduled Copyright 2014 Pearson Education, Inc. 28
Securing Messaging q q q E-mail is, by default, an insecure way to transmit information Unless optional encryption is added to the e-mail solution, no confidential information should EVER be sent via e-mail Inherently, e-mail does not employ ANY encryption, and all information sent is sent in clear text Encrypted email is often referred to as “secure email. ” SMTP, - msg transport standard, POP, IMAP – mail access protocols Copyright 2014 Pearson Education, Inc. 29
Securing Messaging Cont. n n Employees should not commit any information to email that they would not feel comfortable writing on company letterhead Employees must be trained to understand the risks and responsibilities associated with using e-mail as a business tool in a corporate environment Copyright 2014 Pearson Education, Inc. 30
Securing Messaging Cont. n Documents sent as e-mail attachments might contain more information than the sender intended to share q Metadata n n Details about a file that describes or identifies it, such as title, author name, subjects, and keywords E-mail is an effective method of distributing malware q q Can be embedded in an attachment – attackers sending email to deliver zero day attacks. Sent as a hyperlink Copyright 2014 Pearson Education, Inc. 31
Securing Messaging Cont. n Incoming attachments may contain a malicious payload: q q q n n Virus Worm Trojan Other malicious scripts Hoax- fabricated false news-eg: whatsapp will stop functioningupdate from this link!! Users must be trained to be suspicious toward attachments Access to personal email accounts should not be allowed from the corporate network Copyright 2014 Pearson Education, Inc. 32
Securing Messaging Cont. n Common e-mail-related mistakes q q q n Hitting the wrong button: using “reply all” as opposed to “reply” or “forward” instead of “reply” Sending an e-mail to the wrong e-mail address because it is close to the intended recipient’s Leaving an entire string of replies in an e-mail forwarded to a third person who should not have been privy to some of the information discussed in earlier e-mails Training users is paramount to e-mail security Copyright 2014 Pearson Education, Inc. 33
Are E-Mail Servers at Risk? n Compromising the e-mail server – threats- relay abuse and Do. S q Relay abuse n q q Involves using the mail server to distribute spam and malware A denial of service attack against an e-mail is an attack against the availability of the service The e-mail server should be set up so that it does not allow an open mail relay of SMTP traffic. Failure to do so implies two issues: n n The e-mail server will be used by unscrupulous spammers The domain name used for e-mail purposes will be blacklisted Copyright 2014 Pearson Education, Inc. 34
Activity Monitoring and Log Analysis n n n Log: A record of the events occurring within an organization’s systems and networks Almost every device and application on the network can log activity Log management q q Configuring the log sources, including log generation, storage, and security Performing analysis of log data Initiating appropriate responses to identified events Managing the long-term storage of log data Copyright 2014 Pearson Education, Inc. 35
Log management software n n n 1. Syslog based logging software- centralized 2. SIEM- security information and event management Which data to log? q Is based on device criticality, data protection requirements, vulnerability to exploit, regulatory requirements Copyright 2014 Pearson Education, Inc. 36
Analyzing Logs n Log analysis techniques q q Correlation-based on relations Sequencing-based on patterns Signature-compares log data to known bad activity Trend analysis - activity over time- in isolation may appear normal Copyright 2014 Pearson Education, Inc. 37
Service Provider Oversight n n Service providers include vendors, contractors, business partners and affiliates who store, process, transmit, or access company information on company information systems Service providers internal controls should meet or exceed those of the contracting organization Due diligence is the process used to assess the adequacy of service providers- check history, qualification, financial status, technology etc SSAE 16 (Standards for attestation engagements) audit reports are the most widely accepted due diligence documentation 38 Copyright 2014 Pearson Education, Inc.
Summary n n n Day-to-day activities can have a huge impact on the security of the network and the data it contains. SOPs are important in providing a consistent framework across the company. Change must be managed. Two mandatory components of a change management process are RFC documents and a change control plan. Malware is becoming the tool of choice for criminals to exploit devices, operating systems, applications, and user vulnerabilities. Many types of malware exist and companies should protect against them. Sound backup strategies should be developed, tested, authorized and implemented. E-mail, while being a fantastic business tool, is also a double-edge sword because of its inherent lack of built-in security and must be treated as such. Operational security extends to service providers. Service provider controls should meet or exceed those of the company. Copyright 2014 Pearson Education, Inc. 39
- Slides: 39