UNIT 5 Password Management Firewall Design Principles NETWORK

- Slides: 52
UNIT -5 Password Management Firewall Design Principles.

NETWORK SECURITY By: Homera Durani PASSWORD MANAGEMENT 2
PASSWORD PROTECTION User ID and password: User authorized to gain access to the system Privileges accorded to the user Discretionary access control NETWORK SECURITY By: Homera Durani 3
PASSWORD PROTECTION Unix system (user ID, cipher text password, plain text salt) � � password 8 printable characters - 56 -bit value (7 -bit ASCII) encryption routine (crypt(3)) based on DES modified DES algorithm with 12 -bit salt value (related to time of password assignment) 25 encryptions with 64 -bit block of zeros input 64 -bit - 11 character sequence NETWORK SECURITY By: Homera Durani � 4
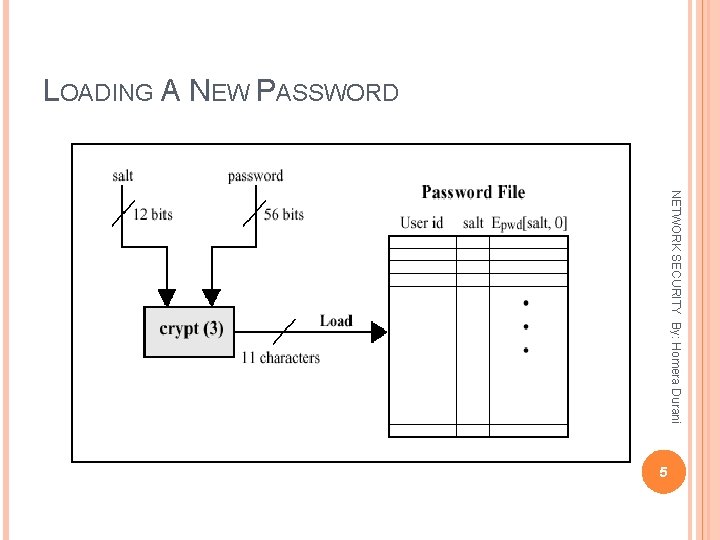
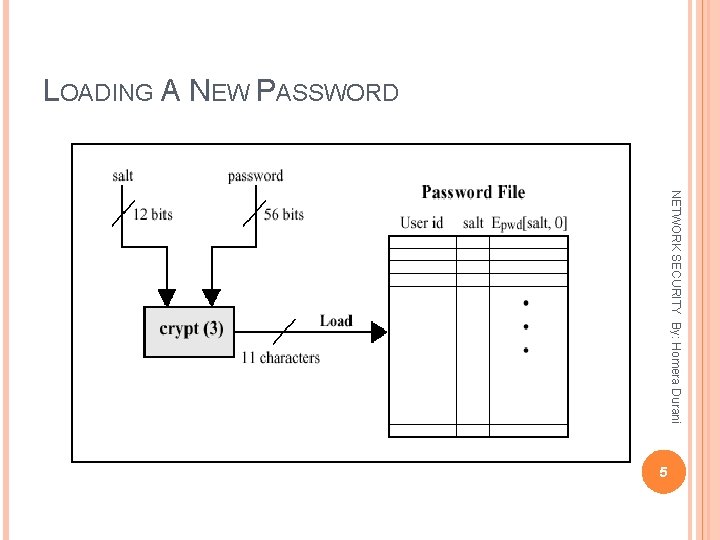
LOADING A NEW PASSWORD NETWORK SECURITY By: Homera Durani 5
PASSWORD PROTECTION Purposes of salt: Prevents duplicate passwords from being visible Effectively increases password length without the user needing to remember additional 2 characters (possible passwords increased by 4096) Prevent use of hardware DES implementation for a brute-force guessing attack NETWORK SECURITY By: Homera Durani 6
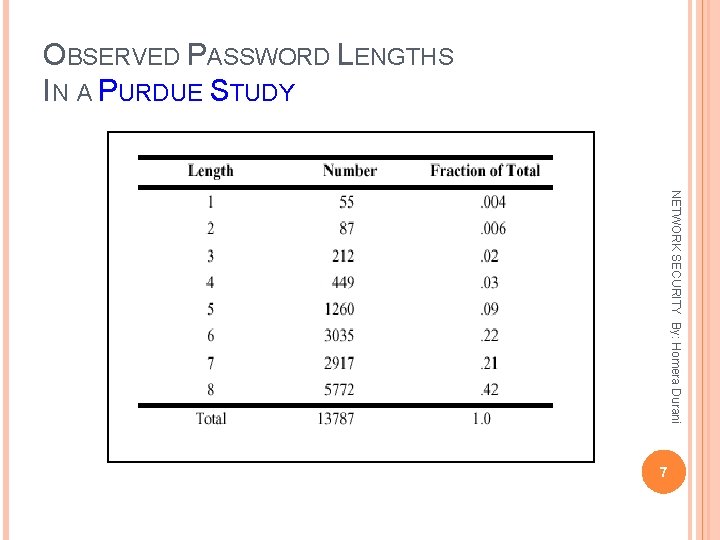
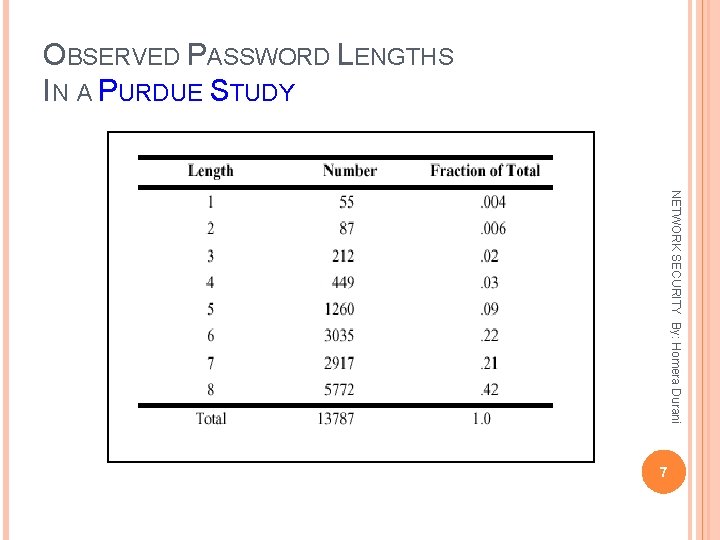
OBSERVED PASSWORD LENGTHS IN A PURDUE STUDY NETWORK SECURITY By: Homera Durani 7
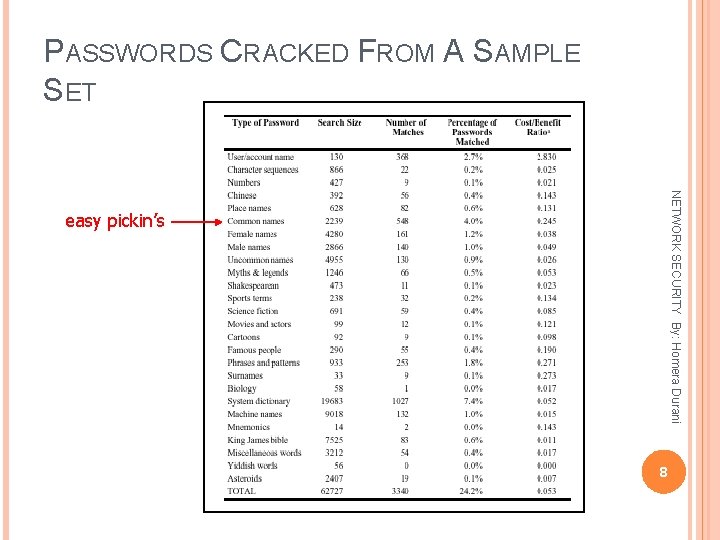
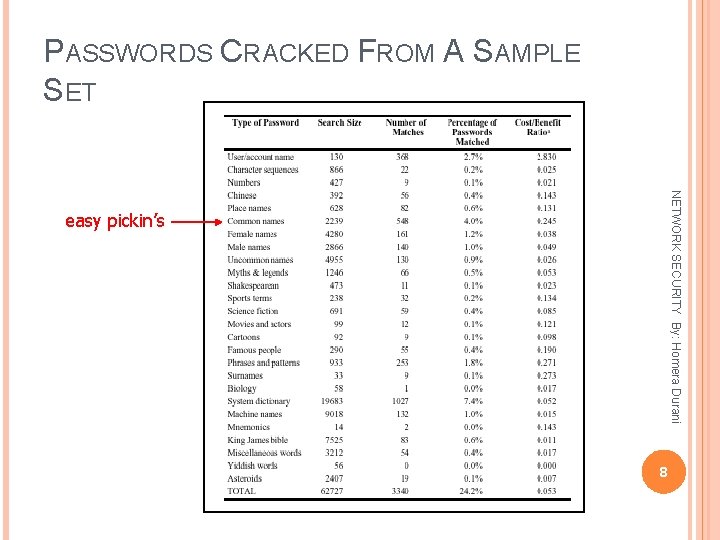
PASSWORDS CRACKED FROM A SAMPLE SET NETWORK SECURITY By: Homera Durani easy pickin’s 8
ACCESS CONTROL NETWORK SECURITY By: Homera Durani One Method: Deny access to password file Systems susceptible to unanticipated break-ins An accident in protection may render the password file readable compromising all accounts Users have accounts in other protection domains using the same passwords 9
ACCESS CONTROL Answer: Force users to select passwords that are difficult to guess Goal: Eliminate guessable passwords while allowing the user to select a password that is memorable NETWORK SECURITY By: Homera Durani 10
PASSWORD SELECTION STRATEGIES (BASIC TECHNIQUES) User education � Users may ignore the guidelines Computer-generated passwords � Poor acceptance by users � Difficult to remember passwords NETWORK SECURITY By: Homera Durani 11
PASSWORD SELECTION STRATEGIES Reactive password checking � System Proactive password checking � Password NETWORK SECURITY By: Homera Durani runs its own password cracker � Resource intensive � Existing passwords remain vulnerable until reactive checker finds them selection is guided by the system � Strike a balance between user accessibility and strength � May provide guidance to password crackers (what not to try) � Dictionary of bad passwords (space and time problem) 12
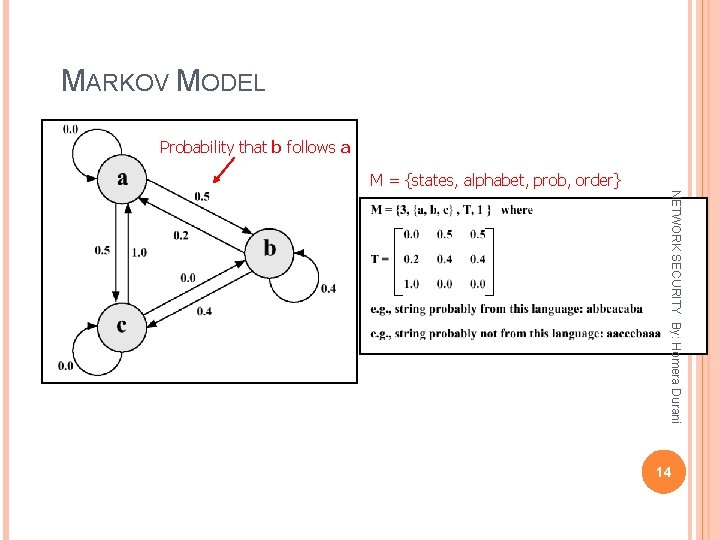
PROACTIVE PASSWORD CHECKER � � Markov Model – search for guessable password Bloom Filter – search in password dictionary NETWORK SECURITY By: Homera Durani There are two techniques currently in use: 13
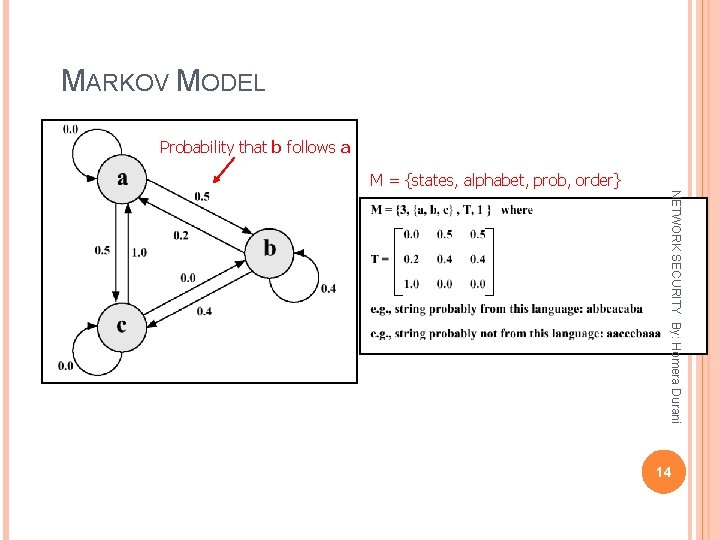
MARKOV MODEL Probability that b follows a M = {states, alphabet, prob, order} NETWORK SECURITY By: Homera Durani 14
MARKOV MODEL “Is this a bad password? ”…same as… “Was this password generated by this Markov model? ” Passwords that are likely to be generated by the model are rejected Good results for a second-order model NETWORK SECURITY By: Homera Durani 15
BLOOM FILTER NETWORK SECURITY By: Homera Durani A probabilistic algorithm to quickly test membership in a large set using multiple hash functions into a single array of bits Developed in 1970 but not used for about 25 years Used to find words in a dictionary also used for web caching Small probability of false positives which can be reduced for different values of k, # hash funcs 16
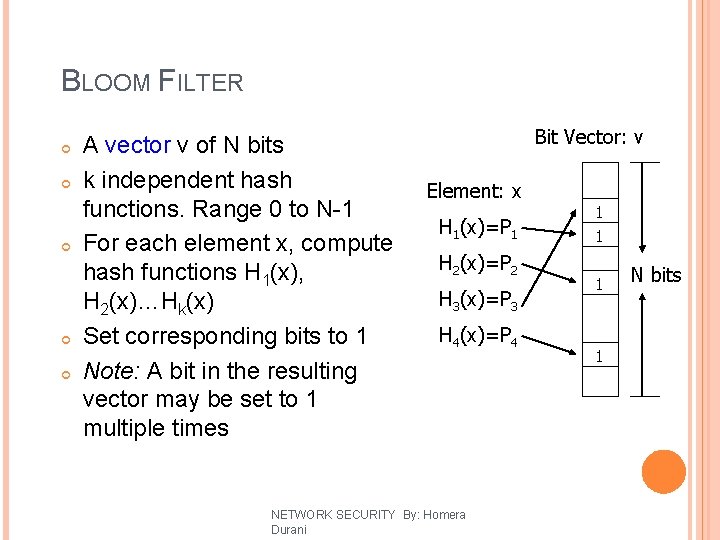
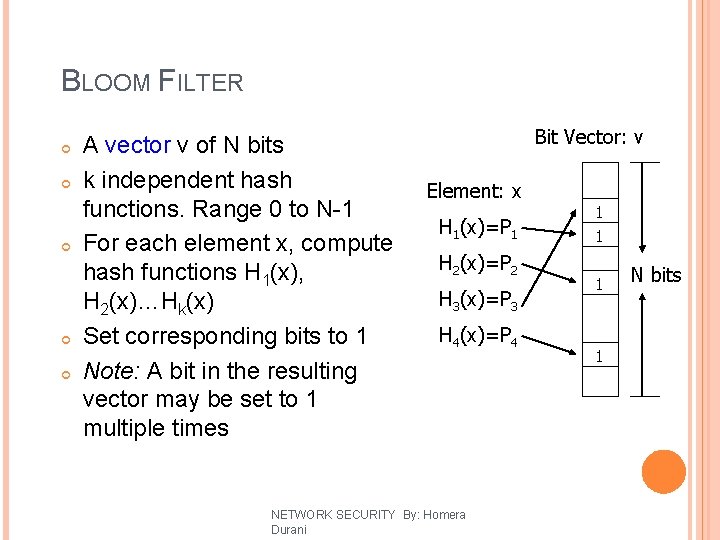
BLOOM FILTER A vector v of N bits k independent hash functions. Range 0 to N-1 For each element x, compute hash functions H 1(x), H 2(x)…Hk(x) Set corresponding bits to 1 Note: A bit in the resulting vector may be set to 1 multiple times Bit Vector: v Element: x H 1(x)=P 1 H 2(x)=P 2 H 3(x)=P 3 H 4(x)=P 4 NETWORK SECURITY By: Homera Durani 1 1 17 N bits
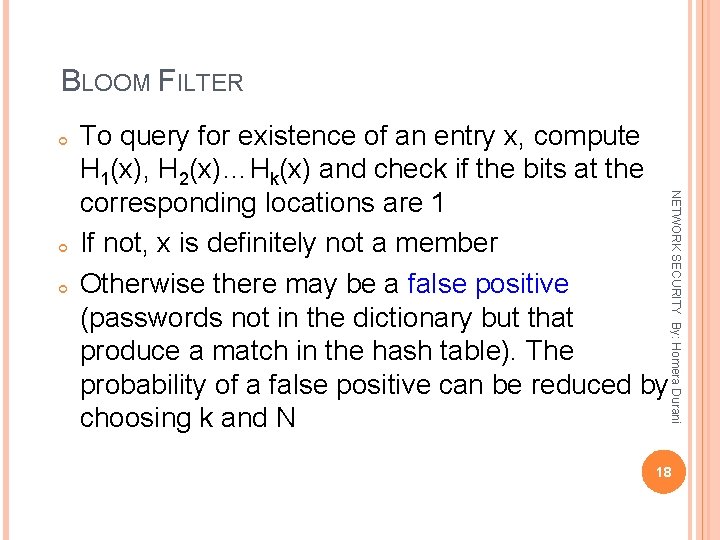
BLOOM FILTER NETWORK SECURITY By: Homera Durani To query for existence of an entry x, compute H 1(x), H 2(x)…Hk(x) and check if the bits at the corresponding locations are 1 If not, x is definitely not a member Otherwise there may be a false positive (passwords not in the dictionary but that produce a match in the hash table). The probability of a false positive can be reduced by choosing k and N 18
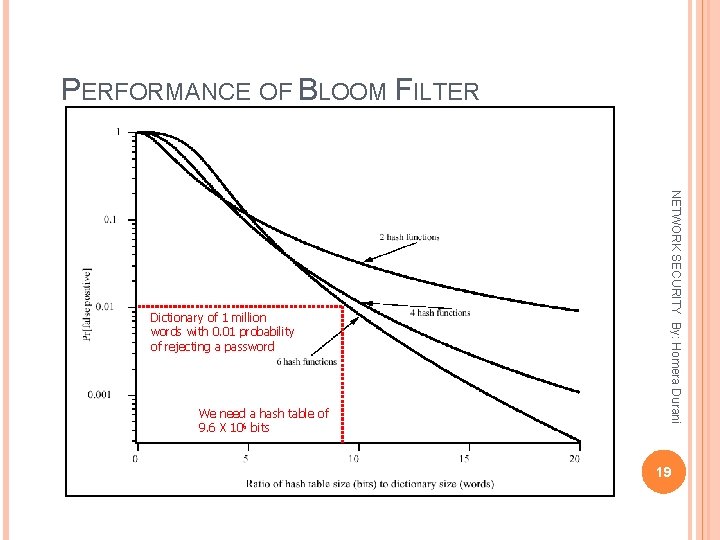
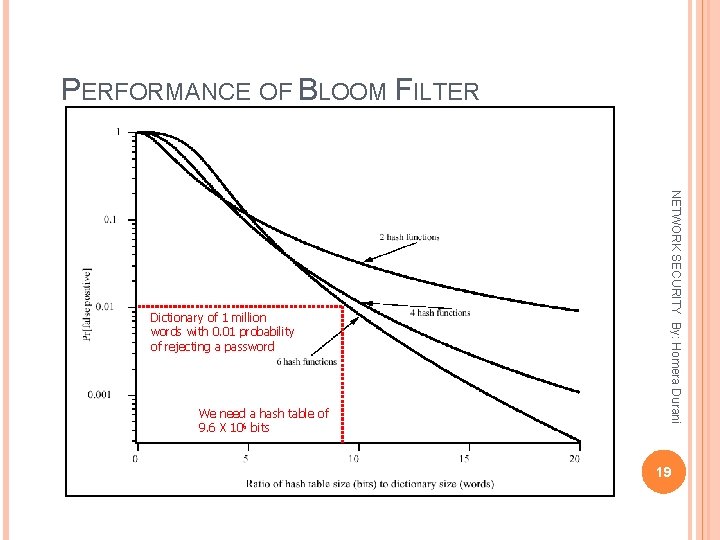
PERFORMANCE OF BLOOM FILTER We need a hash table of 9. 6 X 106 bits NETWORK SECURITY By: Homera Durani Dictionary of 1 million words with 0. 01 probability of rejecting a password 19
20 NETWORK SECURITY By: Homera Durani FIREWALL
OUTLINE Firewall Design Principles � Firewall NETWORK SECURITY By: Homera Durani Characteristics � Types of Firewalls � Firewall Configurations 21
FIREWALLS NETWORK SECURITY By: Homera Durani Effective means of protection a local system or network of systems from network-based security threats while affording access to the outside world via WAN`s or the Internet 22
FIREWALL DESIGN PRINCIPLES Information systems undergo a steady evolution (from small LAN`s to Internet connectivity) Strong security features for all workstations and servers not established NETWORK SECURITY By: Homera Durani 23
FIREWALL DESIGN PRINCIPLES The firewall is inserted between the premises network and the Internet Aims: a controlled link � Protect the premises network from Internet-based attacks � Provide a single choke point NETWORK SECURITY By: Homera Durani � Establish 24
FIREWALL CHARACTERISTICS Design goals: � All NETWORK SECURITY By: Homera Durani traffic from inside to outside must pass through the firewall (physically blocking all access to the local network except via the firewall) � Only authorized traffic (defined by the local security police) will be allowed to pass 25
FIREWALL CHARACTERISTICS Design goals: � The NETWORK SECURITY By: Homera Durani firewall itself is immune to penetration (use of trusted system with a secure operating system) 26
FIREWALL CHARACTERISTICS Four general techniques: Service control the types of Internet services that can be accessed, inbound or outbound Direction control � Determines the direction in which particular service requests are allowed to flow NETWORK SECURITY By: Homera Durani � Determines 27
FIREWALL CHARACTERISTICS User control � Controls Behavior control � Controls e-mail) how particular services are used (e. g. filter NETWORK SECURITY By: Homera Durani access to a service according to which user is attempting to access it 28
TYPES OF FIREWALLS Three common types of Firewalls: � Packet-filtering NETWORK SECURITY By: Homera Durani routers � Application-level gateways � Circuit-level gateways � (Bastion host) 29
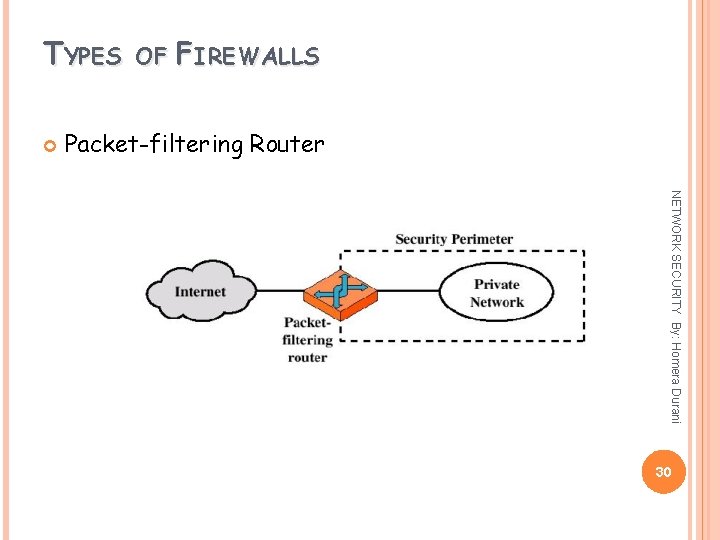
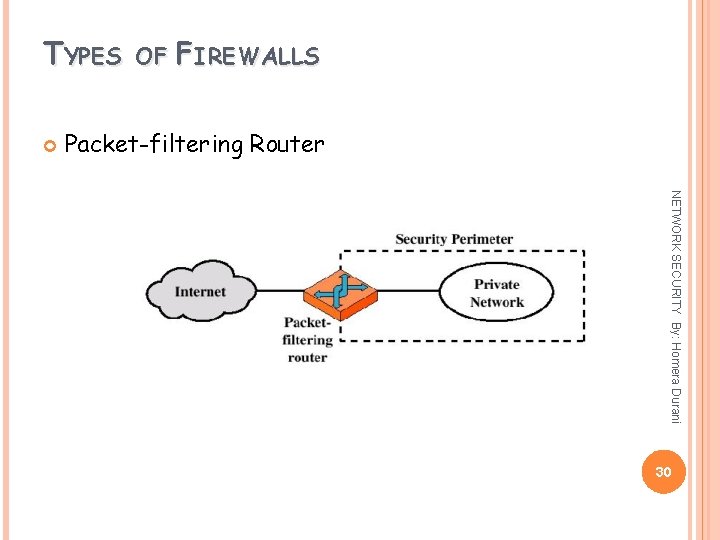
TYPES OF FIREWALLS Packet-filtering Router NETWORK SECURITY By: Homera Durani 30
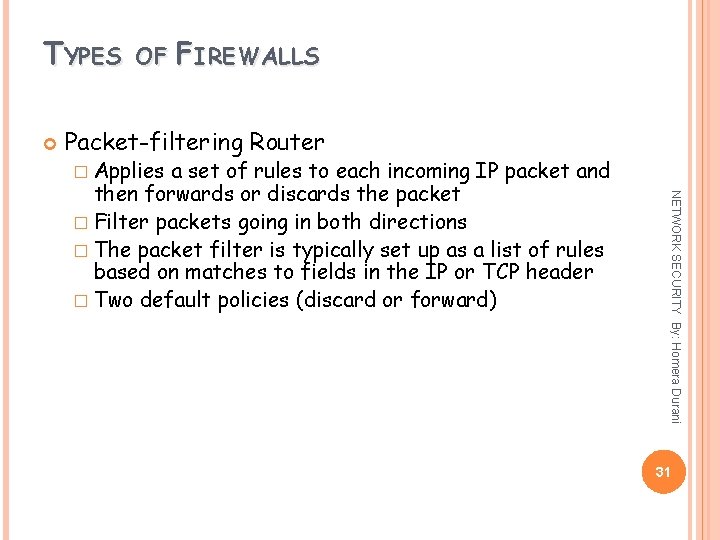
TYPES OF FIREWALLS Packet-filtering Router � Applies NETWORK SECURITY By: Homera Durani a set of rules to each incoming IP packet and then forwards or discards the packet � Filter packets going in both directions � The packet filter is typically set up as a list of rules based on matches to fields in the IP or TCP header � Two default policies (discard or forward) 31
TYPES OF FIREWALLS Advantages: � Simplicity � High speed Disadvantages: � Difficulty to users of setting up packet filter rules � Lack of Authentication NETWORK SECURITY By: Homera Durani � Transparency 32
TYPES OF FIREWALLS Possible attacks and appropriate countermeasures address spoofing � Source routing attacks � Tiny fragment attacks NETWORK SECURITY By: Homera Durani � IP 33
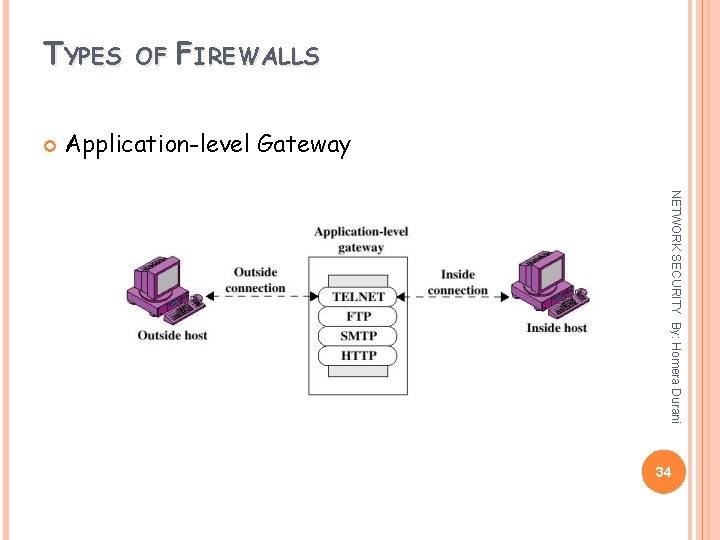
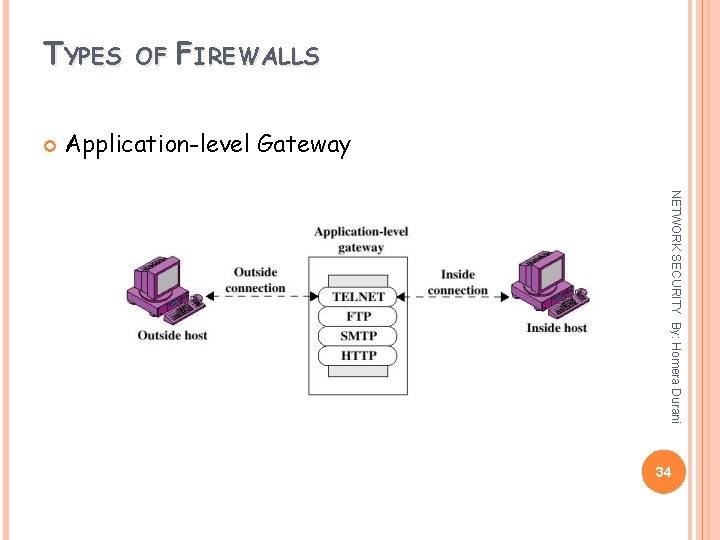
TYPES OF FIREWALLS Application-level Gateway NETWORK SECURITY By: Homera Durani 34
TYPES OF FIREWALLS Application-level Gateway � Also NETWORK SECURITY By: Homera Durani called proxy server � Acts as a relay of application-level traffic 35
TYPES OF FIREWALLS Advantages: � Higher Disadvantages: � Additional processing overhead on each connection (gateway as splice point) NETWORK SECURITY By: Homera Durani security than packet filters � Only need to scrutinize a few allowable applications � Easy to log and audit all incoming traffic 36
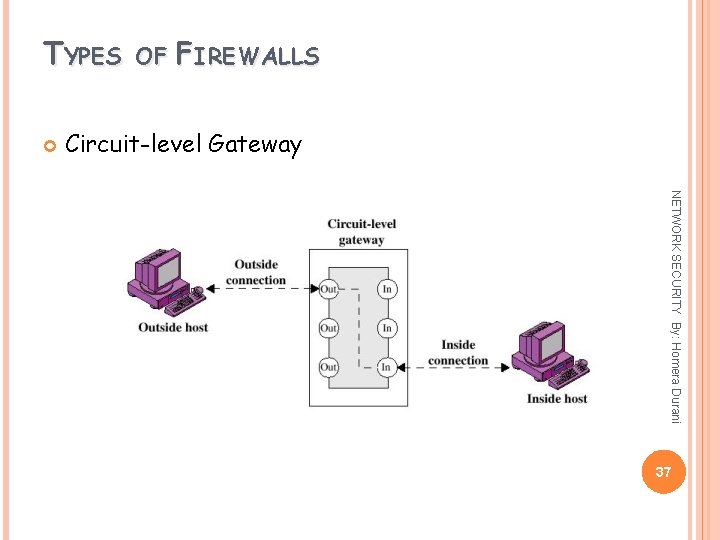
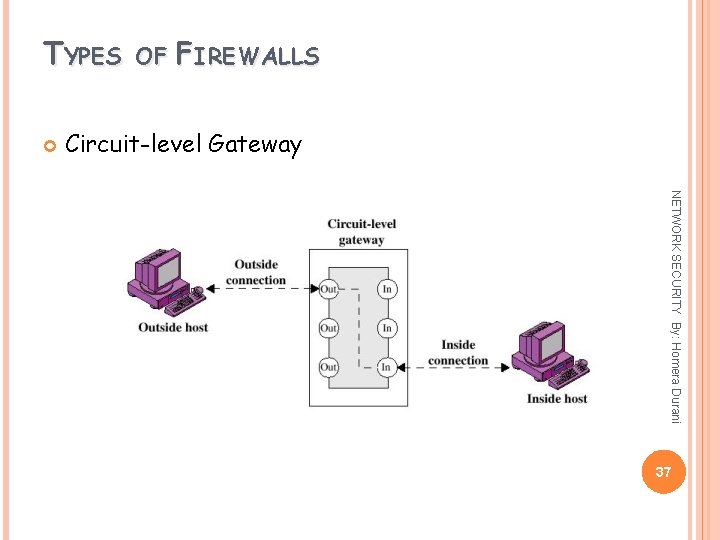
TYPES OF FIREWALLS Circuit-level Gateway NETWORK SECURITY By: Homera Durani 37
TYPES OF FIREWALLS Circuit-level Gateway � Stand-alone NETWORK SECURITY By: Homera Durani system or � Specialized function performed by an Applicationlevel Gateway � Sets up two TCP connections � The gateway typically relays TCP segments from one connection to the other without examining the contents 38
TYPES OF FIREWALLS Circuit-level Gateway � The NETWORK SECURITY By: Homera Durani security function consists of determining which connections will be allowed � Typically use is a situation in which the system administrator trusts the internal users � An example is the SOCKS package 39
TYPES OF FIREWALLS Bastion Host �A NETWORK SECURITY By: Homera Durani system identified by the firewall administrator as a critical strong point in the network´s security � The bastion host serves as a platform for an application-level or circuit-level gateway 40
FIREWALL CONFIGURATIONS In addition to the use of simple configuration of a single system (single packet filtering router or single gateway), more complex configurations are possible Three common configurations NETWORK SECURITY By: Homera Durani 41
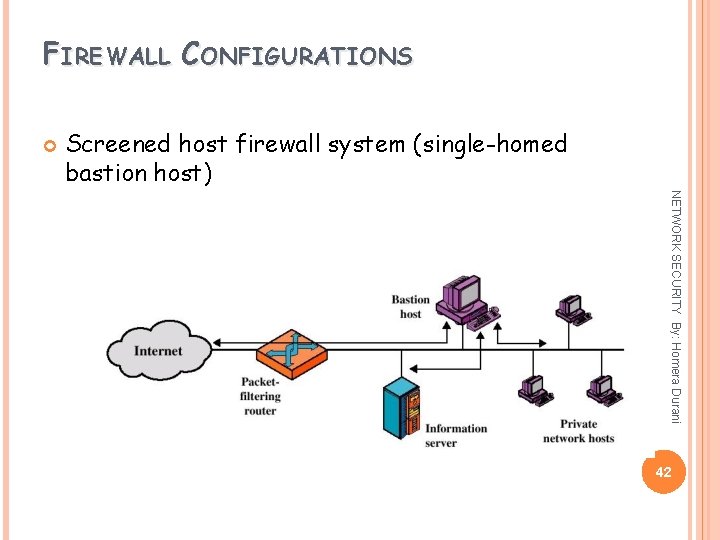
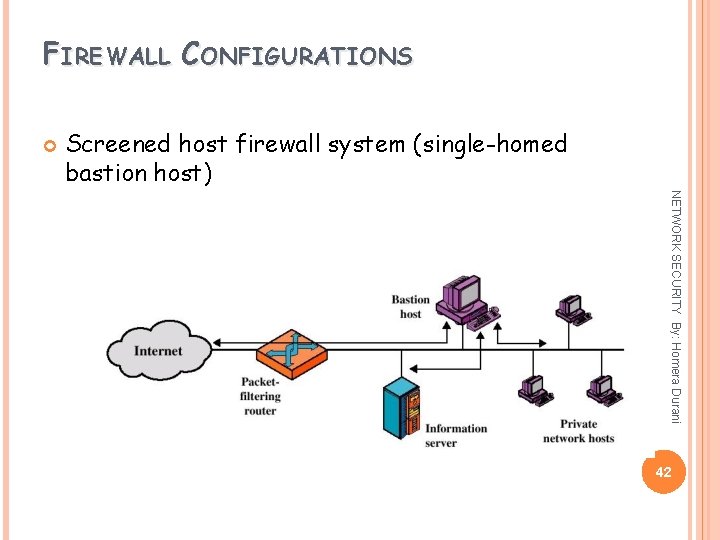
FIREWALL CONFIGURATIONS Screened host firewall system (single-homed bastion host) NETWORK SECURITY By: Homera Durani 42
FIREWALL CONFIGURATIONS Screened host firewall, single-homed bastion configuration Firewall consists of two systems: packet-filtering router � A bastion host NETWORK SECURITY By: Homera Durani �A 43
FIREWALL CONFIGURATIONS Configuration for the packet-filtering router: � Only The bastion host performs authentication and proxy functions NETWORK SECURITY By: Homera Durani packets from and to the bastion host are allowed to pass through the router 44
FIREWALL CONFIGURATIONS Greater security than single configurations because of two reasons: configuration implements both packet-level and application-level filtering (allowing for flexibility in defining security policy) � An intruder must generally penetrate two separate systems NETWORK SECURITY By: Homera Durani � This 45
FIREWALL CONFIGURATIONS NETWORK SECURITY By: Homera Durani This configuration also affords flexibility in providing direct Internet access (public information server, e. g. Web server) 46
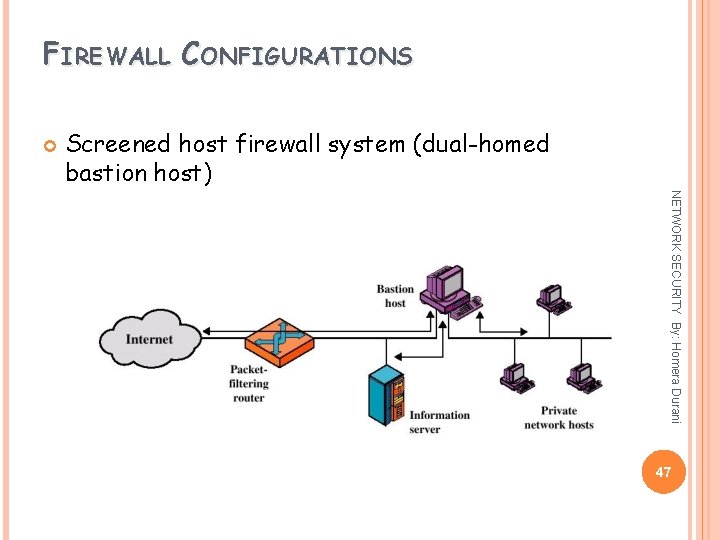
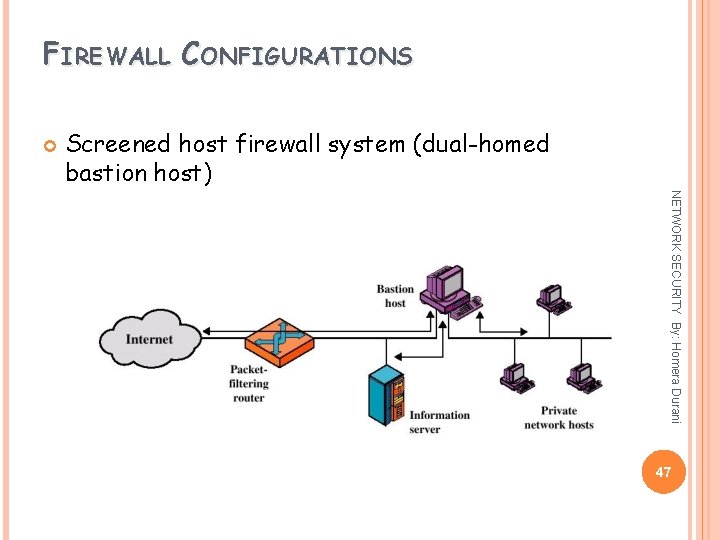
FIREWALL CONFIGURATIONS Screened host firewall system (dual-homed bastion host) NETWORK SECURITY By: Homera Durani 47
FIREWALL CONFIGURATIONS Screened host firewall, dual-homed bastion configuration packet-filtering router is not completely compromised � Traffic between the Internet and other hosts on the private network has to flow through the bastion host NETWORK SECURITY By: Homera Durani � The 48
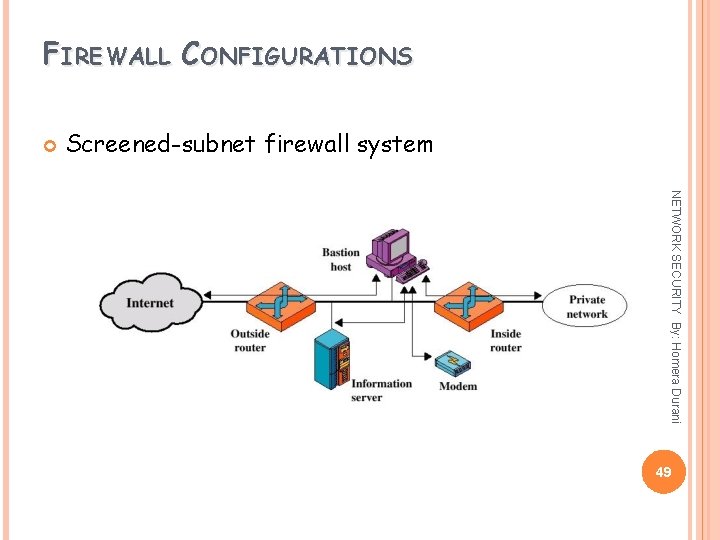
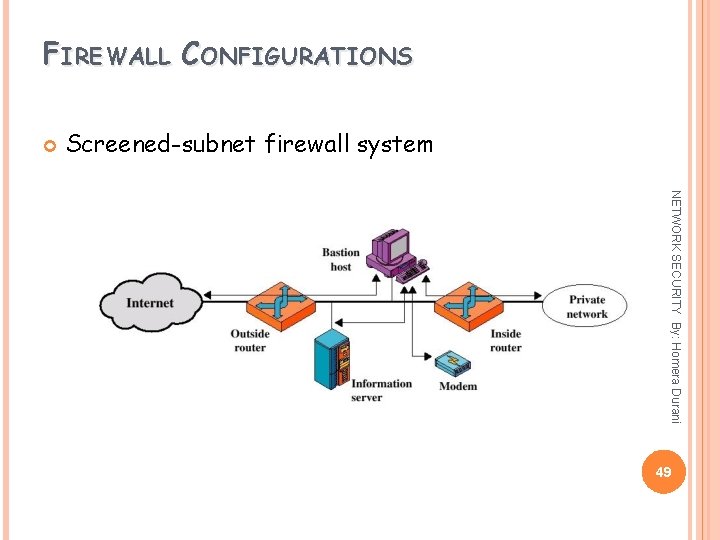
FIREWALL CONFIGURATIONS Screened-subnet firewall system NETWORK SECURITY By: Homera Durani 49
FIREWALL CONFIGURATIONS Screened subnet firewall configuration � Most NETWORK SECURITY By: Homera Durani secure configuration of the three � Two packet-filtering routers are used � Creation of an isolated sub-network 50
FIREWALL CONFIGURATIONS Advantages: � Three NETWORK SECURITY By: Homera Durani levels of defense to thwart intruders � The outside router advertises only the existence of the screened subnet to the Internet (internal network is invisible to the Internet) 51
FIREWALL CONFIGURATIONS Advantages: � The NETWORK SECURITY By: Homera Durani inside router advertises only the existence of the screened subnet to the internal network (the systems on the inside network cannot construct direct routes to the Internet) 52