Signatures Commitments and ZeroKnowledge Vadim Lyubashevsky IBM Research
Signatures, Commitments, and Zero-Knowledge Vadim Lyubashevsky IBM Research Europe, Zurich
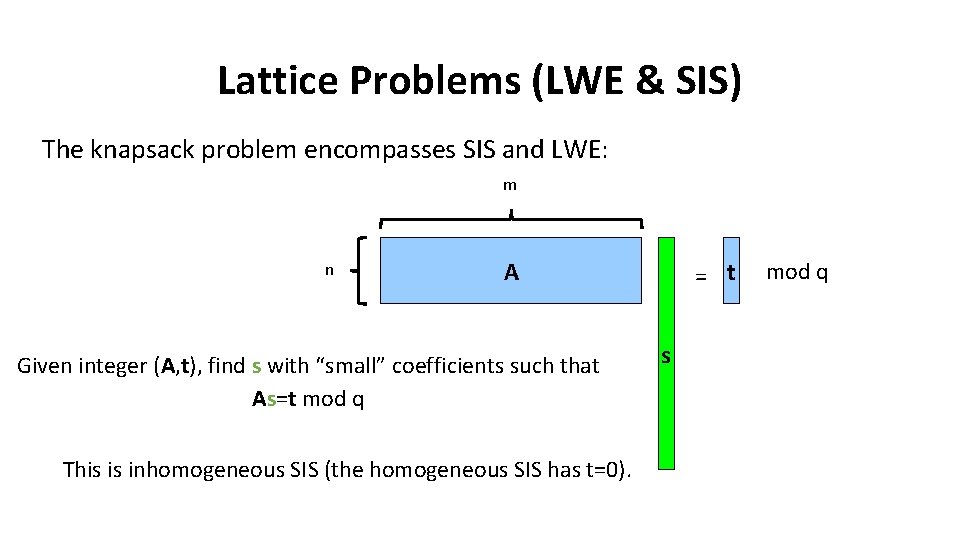
Lattice Problems (LWE & SIS) The knapsack problem encompasses SIS and LWE: m n A Given integer (A, t), find s with “small” coefficients such that As=t mod q This is inhomogeneous SIS (the homogeneous SIS has t=0). = t s mod q
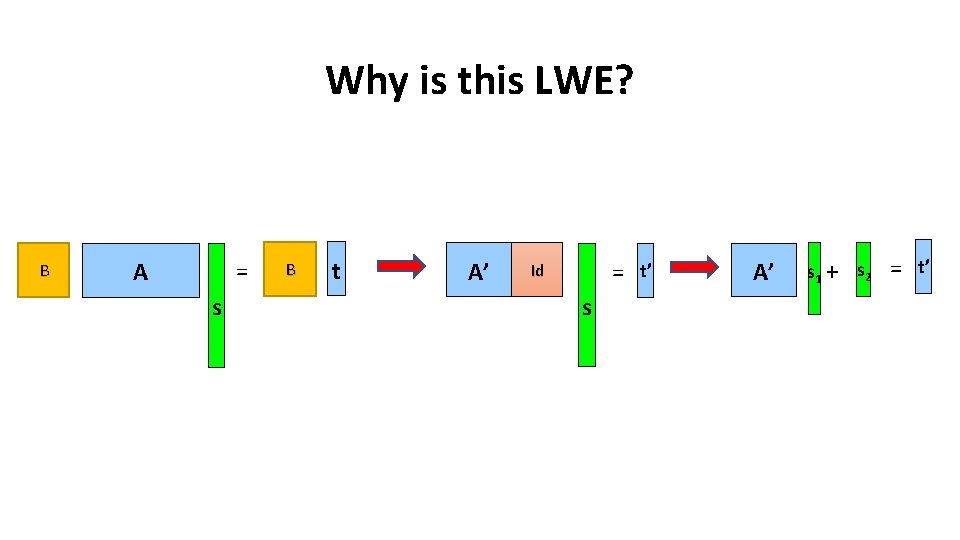
Why is this LWE? B = A s B t A’ = Id s t’ A’ s 1 + s 2 = t’
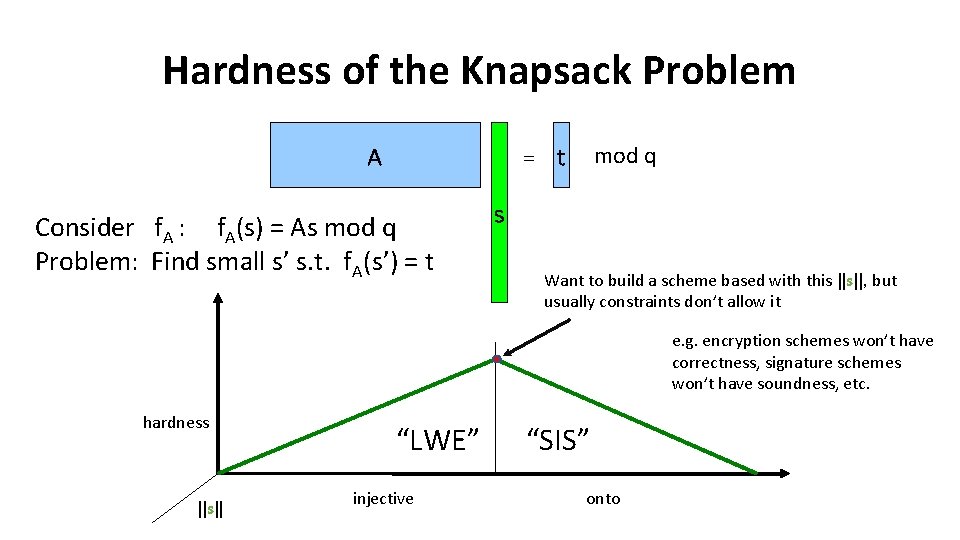
Hardness of the Knapsack Problem mod q = t A Consider f. A : f. A(s) = As mod q Problem: Find small s’ s. t. f. A(s’) = t s Want to build a scheme based with this ||s||, but usually constraints don’t allow it e. g. encryption schemes won’t have correctness, signature schemes won’t have soundness, etc. hardness ||s|| “LWE” injective “SIS” onto
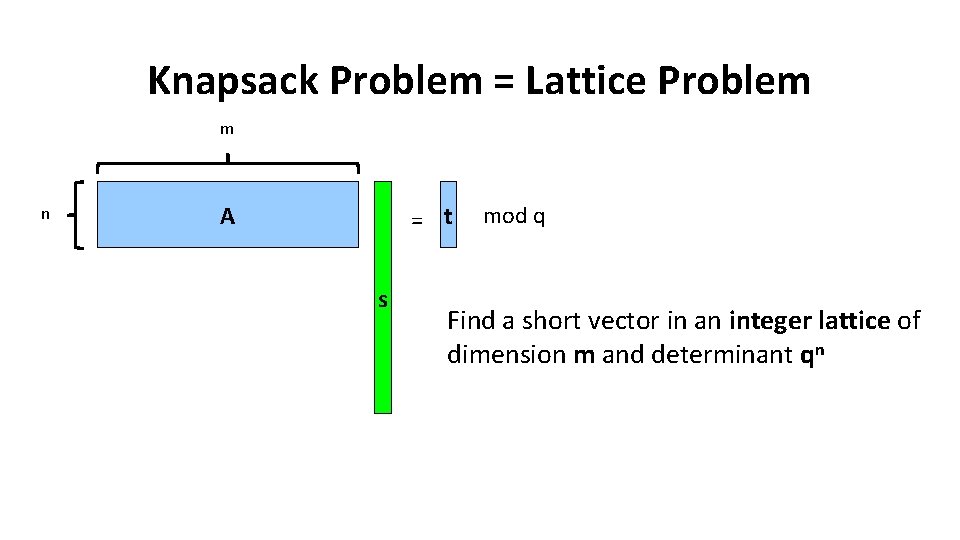
Knapsack Problem = Lattice Problem m n A = t s mod q Find a short vector in an integer lattice of dimension m and determinant qn
![Polynomial Rings R=Zq[X]/(f(x)) Example Ring Z 17[x]/(x 4+1) Elements are z(x)=z 3 x 3+z Polynomial Rings R=Zq[X]/(f(x)) Example Ring Z 17[x]/(x 4+1) Elements are z(x)=z 3 x 3+z](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-6.jpg)
Polynomial Rings R=Zq[X]/(f(x)) Example Ring Z 17[x]/(x 4+1) Elements are z(x)=z 3 x 3+z 2 x 2+z 1 x+z 0 where zi are integers mod 17 Addition is the usual coordinate-wise addition Multiplication is the usual polynomial multiplication followed by a reduction modulo x 4+1 6
![Polynomial Rings R=Zq[X]/(f(x)) (X 3 - 2 X - 1)(-3 X 2 + 6) Polynomial Rings R=Zq[X]/(f(x)) (X 3 - 2 X - 1)(-3 X 2 + 6)](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-7.jpg)
Polynomial Rings R=Zq[X]/(f(x)) (X 3 - 2 X - 1)(-3 X 2 + 6) = (-3 X 5 + 12 X 3 +3 X 2 -12 X - 6) = (3 X + 12 X 3 + 3 X 2 -12 X - 6) = (-5 X 3 +3 X 2 +8 X -6) Important: Reductions modulo X 4+1 do not increase the coefficients! (For some moduli, there could be an exponential increase – these are not useful for crypto). 7
![Lattices over R=Zq[X]/(f(x)) m n A = t s f(X)=Xd + fd-1 Xd-1 + Lattices over R=Zq[X]/(f(x)) m n A = t s f(X)=Xd + fd-1 Xd-1 +](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-8.jpg)
Lattices over R=Zq[X]/(f(x)) m n A = t s f(X)=Xd + fd-1 Xd-1 + … + f 1 X + f 0 , fi in Z A is in Rn x m s is in Rm with small coefficients Find a short vector in an integer lattice of dimension dm and determinant qdn
![Polynomial Rings Asymptotically, worst-case to average-case reduction from lattice problems over the ring Z[X]/(f(X)) Polynomial Rings Asymptotically, worst-case to average-case reduction from lattice problems over the ring Z[X]/(f(X))](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-9.jpg)
Polynomial Rings Asymptotically, worst-case to average-case reduction from lattice problems over the ring Z[X]/(f(X)) to knapsacks over Zq[X]/(f(x)) What should f(X) and q be according to the reductions? • f(X) should be irreducible and multiplication mod f(X) should not increase the coefficients too much. Otherwise, no guidance (e. g. could some f(X) make the problem to be easier? ) • reductions (mostly) work for any q
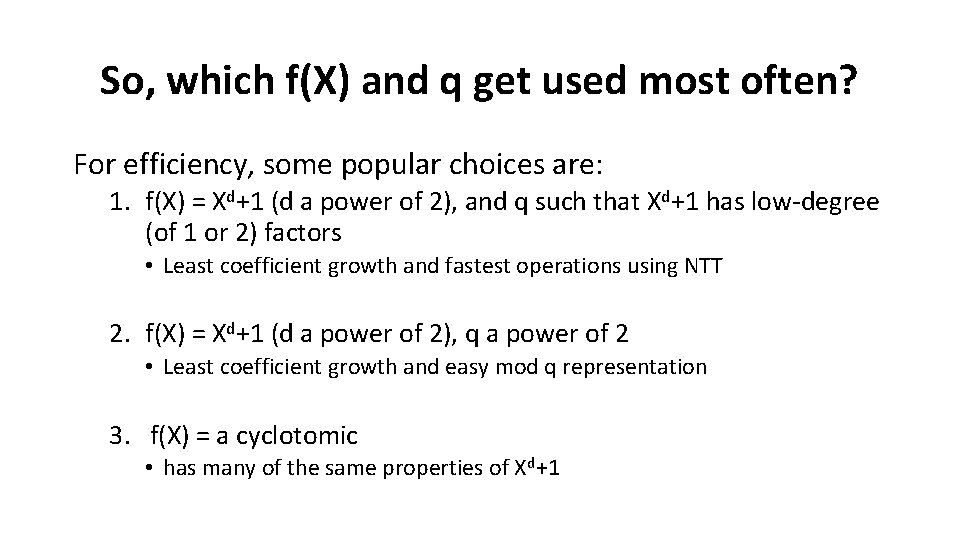
So, which f(X) and q get used most often? For efficiency, some popular choices are: 1. f(X) = Xd+1 (d a power of 2), and q such that Xd+1 has low-degree (of 1 or 2) factors • Least coefficient growth and fastest operations using NTT 2. f(X) = Xd+1 (d a power of 2), q a power of 2 • Least coefficient growth and easy mod q representation 3. f(X) = a cyclotomic • has many of the same properties of Xd+1
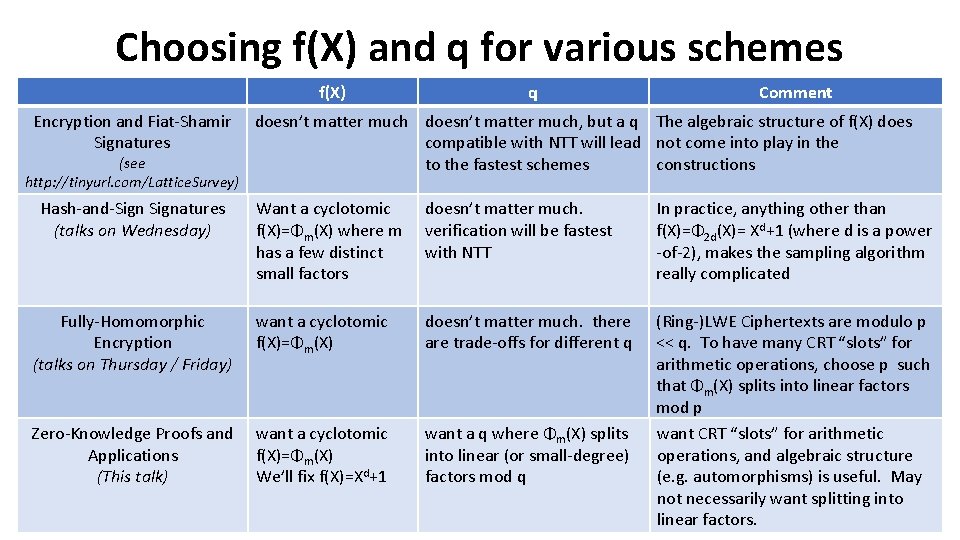
Choosing f(X) and q for various schemes f(X) Encryption and Fiat-Shamir Signatures (see http: //tinyurl. com/Lattice. Survey) Hash-and-Signatures (talks on Wednesday) q Comment doesn’t matter much, but a q The algebraic structure of f(X) does compatible with NTT will lead not come into play in the to the fastest schemes constructions Want a cyclotomic f(X)=Φm(X) where m has a few distinct small factors doesn’t matter much. verification will be fastest with NTT In practice, anything other than f(X)=Φ 2 d(X)= Xd+1 (where d is a power -of-2), makes the sampling algorithm really complicated Fully-Homomorphic Encryption (talks on Thursday / Friday) want a cyclotomic f(X)=Φm(X) doesn’t matter much. there are trade-offs for different q Zero-Knowledge Proofs and Applications (This talk) want a cyclotomic f(X)=Φm(X) We’ll fix f(X)=Xd+1 want a q where Φm(X) splits into linear (or small-degree) factors mod q (Ring-)LWE Ciphertexts are modulo p << q. To have many CRT “slots” for arithmetic operations, choose p such that Φm(X) splits into linear factors mod p want CRT “slots” for arithmetic operations, and algebraic structure (e. g. automorphisms) is useful. May not necessarily want splitting into linear factors.
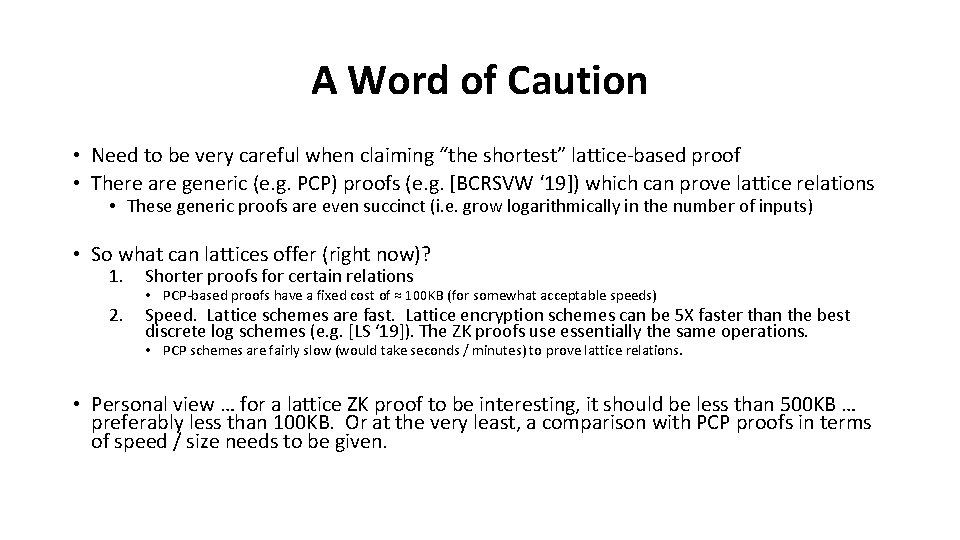
A Word of Caution • Need to be very careful when claiming “the shortest” lattice-based proof • There are generic (e. g. PCP) proofs (e. g. [BCRSVW ‘ 19]) which can prove lattice relations • These generic proofs are even succinct (i. e. grow logarithmically in the number of inputs) • So what can lattices offer (right now)? 1. Shorter proofs for certain relations 2. Speed. Lattice schemes are fast. Lattice encryption schemes can be 5 X faster than the best discrete log schemes (e. g. [LS ‘ 19]). The ZK proofs use essentially the same operations. • PCP-based proofs have a fixed cost of ≈ 100 KB (for somewhat acceptable speeds) • PCP schemes are fairly slow (would take seconds / minutes) to prove lattice relations. • Personal view … for a lattice ZK proof to be interesting, it should be less than 500 KB … preferably less than 100 KB. Or at the very least, a comparison with PCP proofs in terms of speed / size needs to be given.
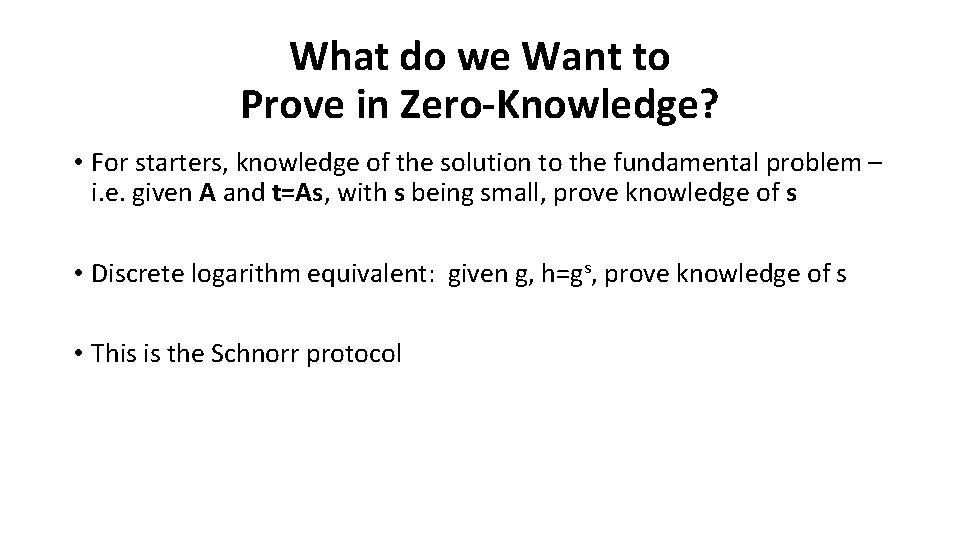
What do we Want to Prove in Zero-Knowledge? • For starters, knowledge of the solution to the fundamental problem – i. e. given A and t=As, with s being small, prove knowledge of s • Discrete logarithm equivalent: given g, h=gs, prove knowledge of s • This is the Schnorr protocol
Schnorr Protocol Prover: (g, s) Verifier: (g, h) y Zp w: =gy w c c Zp z z: =sc+y check if: g z = hcw Correctness: gsc+y = gscgy
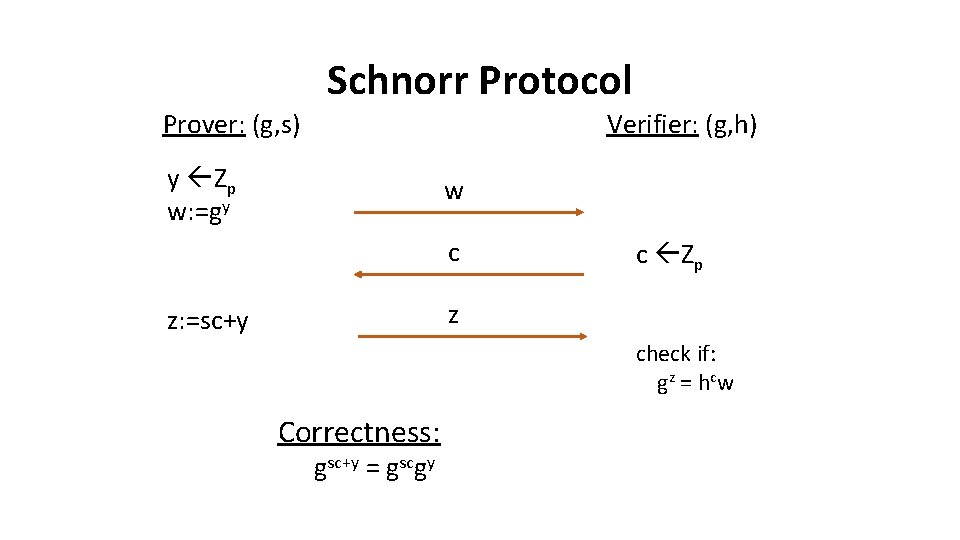
Schnorr Protocol Prover: (g, s) y Zp w: =gy Verifier: (g, h) w c z: =sc+y c Zp z check if: g z = hcw Honest-Verifier Zero Knowledge Generate random c, z Zp. Set w=gz / hc (w, c, z) has the same distribution as in the protocol
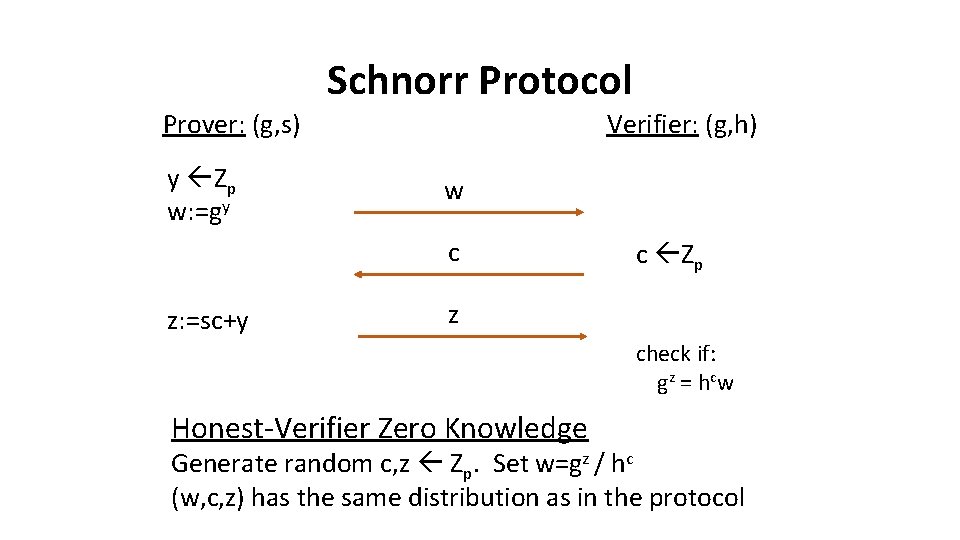
Schnorr Protocol Prover: (g, s) w Extractor: (g, h) A successful prover must be able to answer more than one distinct challenge c c Zp z c’ c’ Zp z’ gz = hcw gz’ = hc’w Proof of Knowledge: gz-z’ = hc-c’ g(z-z’)/(c-c’) = h s
![In the lattice world … n A = S m R=Zq[X]/(Xd+1) A is in In the lattice world … n A = S m R=Zq[X]/(Xd+1) A is in](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-17.jpg)
In the lattice world … n A = S m R=Zq[X]/(Xd+1) A is in Rn x m s is in Rm with small coefficients t mod q
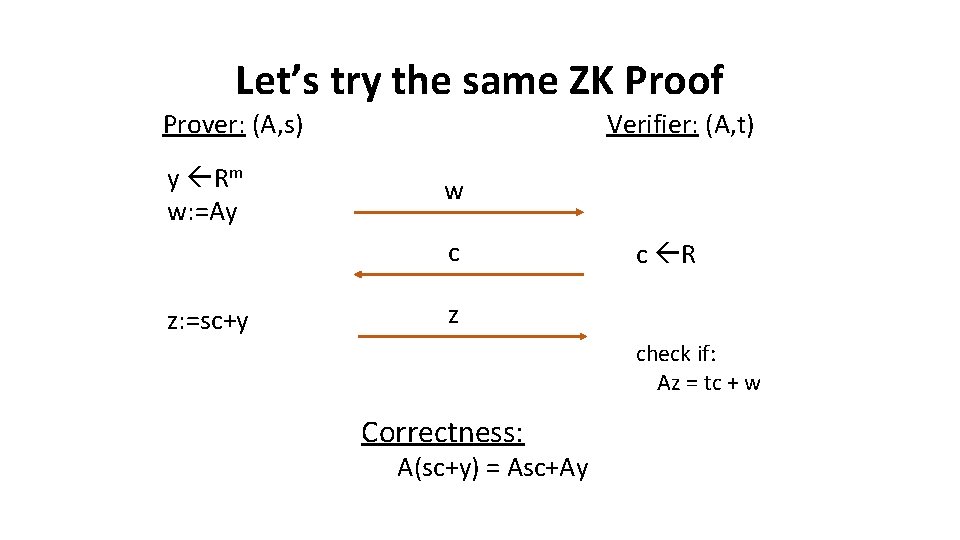
Let’s try the same ZK Proof Prover: (A, s) y Rm w: =Ay Verifier: (A, t) w c z: =sc+y c R z check if: Az = tc + w Correctness: A(sc+y) = Asc+Ay
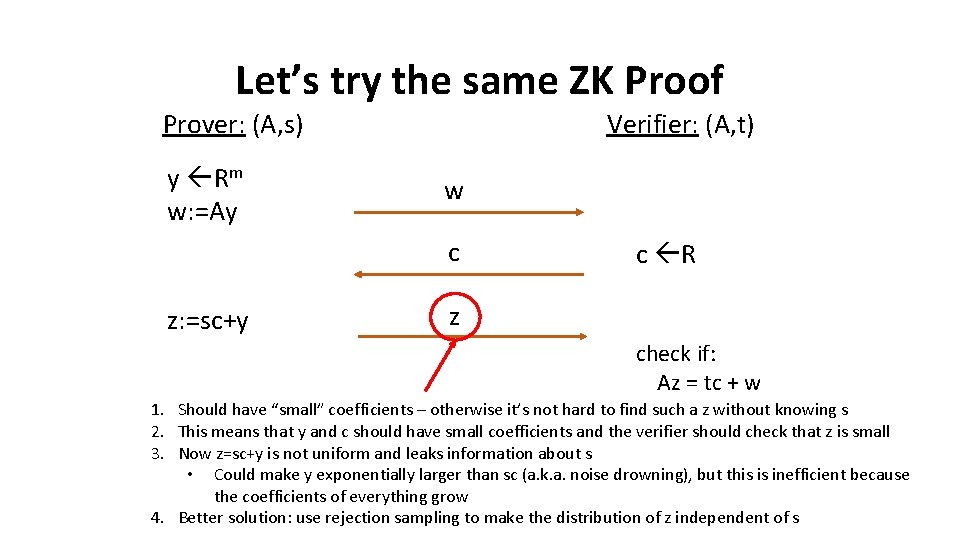
Let’s try the same ZK Proof Prover: (A, s) y Rm w: =Ay Verifier: (A, t) w c z: =sc+y c R z check if: Az = tc + w 1. Should have “small” coefficients – otherwise it’s not hard to find such a z without knowing s 2. This means that y and c should have small coefficients and the verifier should check that z is small 3. Now z=sc+y is not uniform and leaks information about s • Could make y exponentially larger than sc (a. k. a. noise drowning), but this is inefficient because the coefficients of everything grow 4. Better solution: use rejection sampling to make the distribution of z independent of s
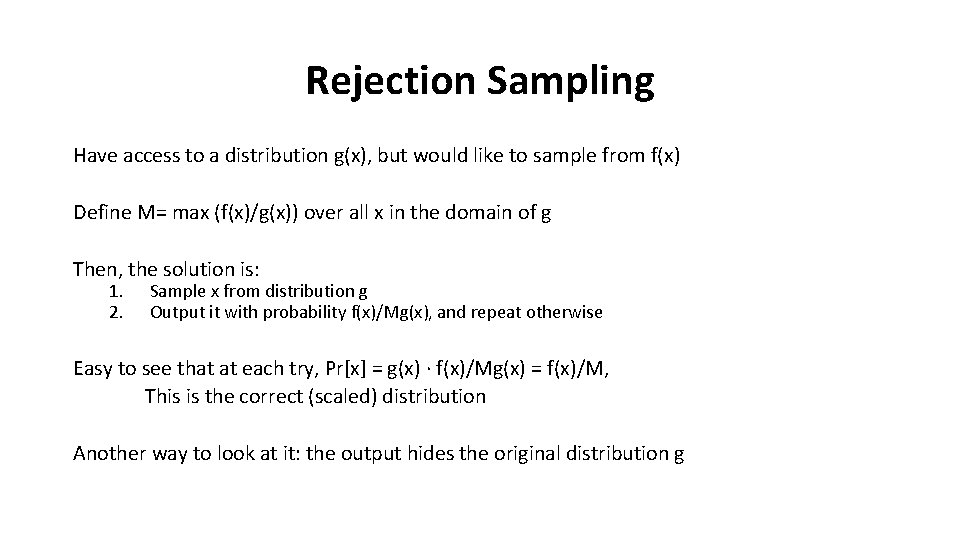
Rejection Sampling Have access to a distribution g(x), but would like to sample from f(x) Define M= max (f(x)/g(x)) over all x in the domain of g Then, the solution is: 1. 2. Sample x from distribution g Output it with probability f(x)/Mg(x), and repeat otherwise Easy to see that at each try, Pr[x] = g(x) ∙ f(x)/Mg(x) = f(x)/M, This is the correct (scaled) distribution Another way to look at it: the output hides the original distribution g
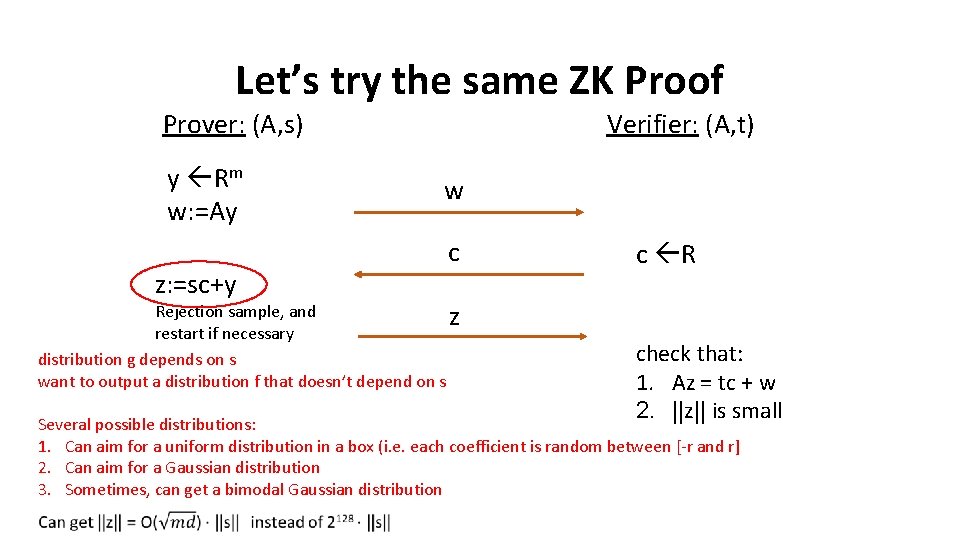
Let’s try the same ZK Proof Prover: (A, s) y Rm w: =Ay z: =sc+y Verifier: (A, t) w c Rejection sample, and z restart if necessary distribution g depends on s want to output a distribution f that doesn’t depend on s c R check that: 1. Az = tc + w 2. ||z|| is small Several possible distributions: 1. Can aim for a uniform distribution in a box (i. e. each coefficient is random between [-r and r] 2. Can aim for a Gaussian distribution 3. Sometimes, can get a bimodal Gaussian distribution
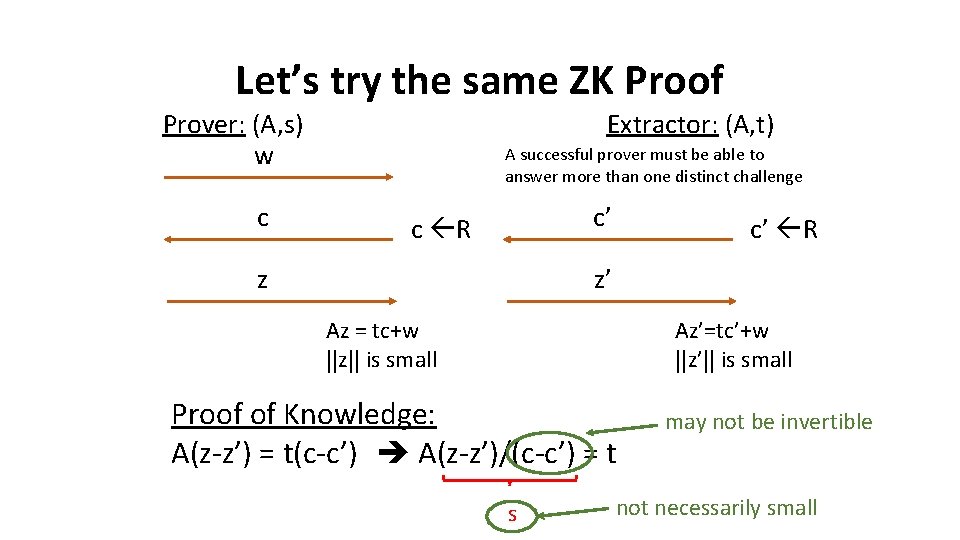
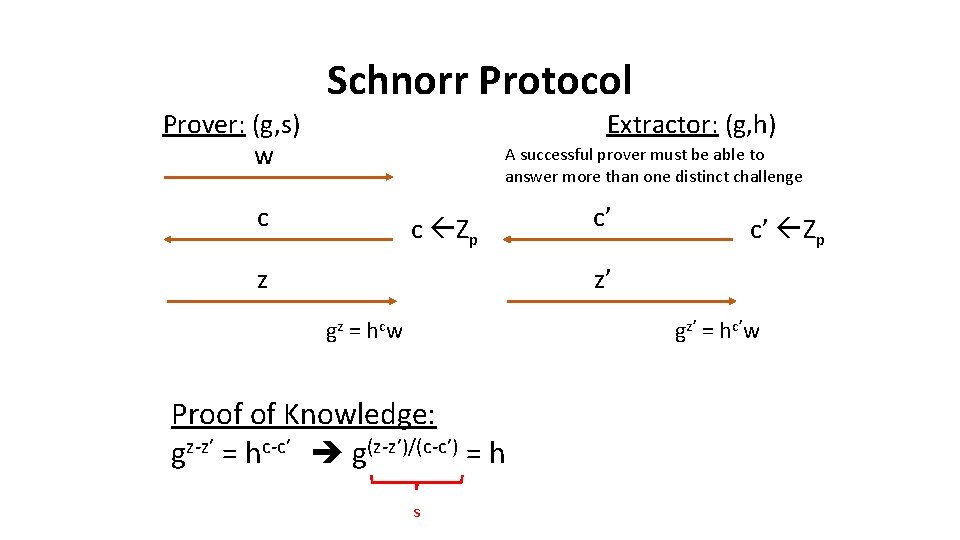
Let’s try the same ZK Proof Prover: (A, s) w c Extractor: (A, t) A successful prover must be able to answer more than one distinct challenge c’ c R z c’ R z’ Az = tc+w ||z|| is small Az’=tc’+w ||z’|| is small Proof of Knowledge: A(z-z’) = t(c-c’) A(z-z’)/(c-c’) = t s may not be invertible not necessarily small
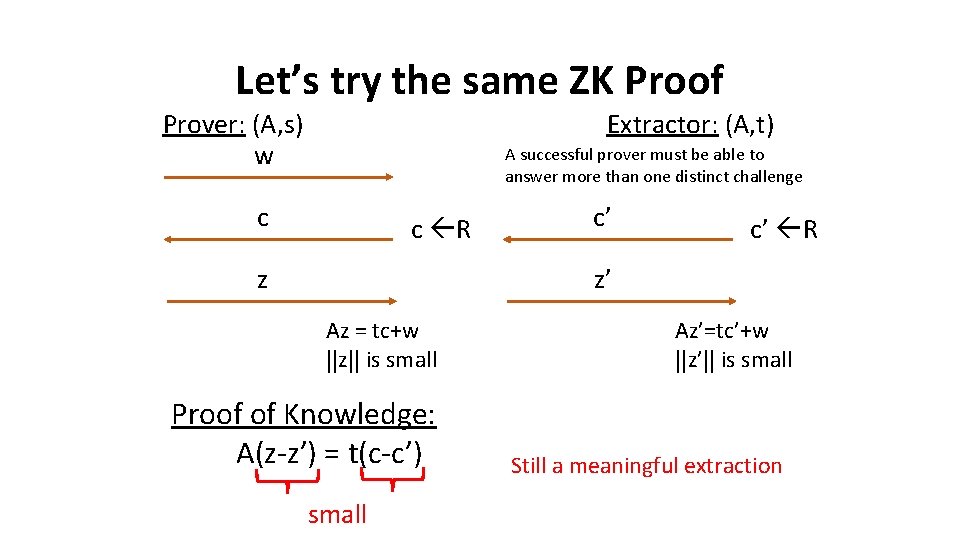
Let’s try the same ZK Proof Prover: (A, s) w Extractor: (A, t) A successful prover must be able to answer more than one distinct challenge c c R z c’ c’ R z’ Az = tc+w ||z|| is small Proof of Knowledge: A(z-z’) = t(c-c’) small Az’=tc’+w ||z’|| is small Still a meaningful extraction
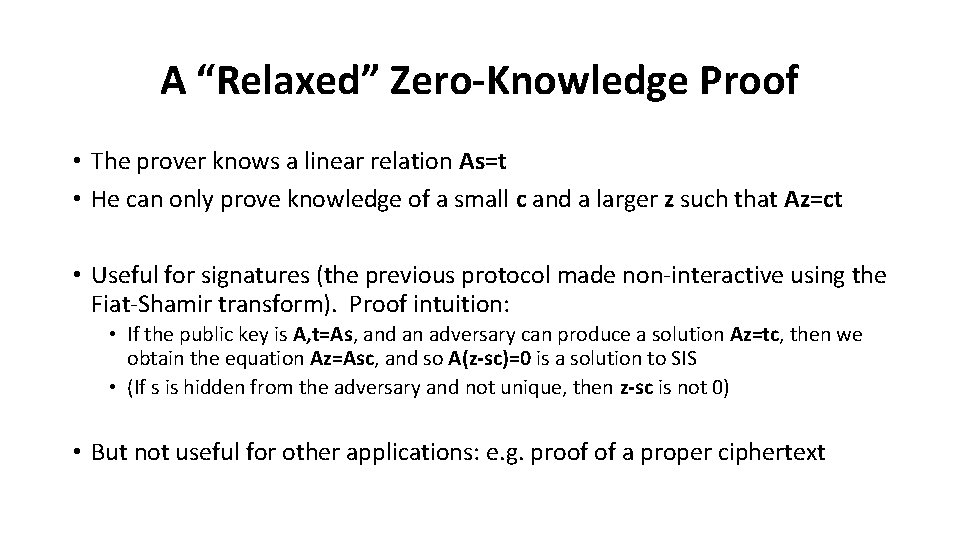
A “Relaxed” Zero-Knowledge Proof • The prover knows a linear relation As=t • He can only prove knowledge of a small c and a larger z such that Az=ct • Useful for signatures (the previous protocol made non-interactive using the Fiat-Shamir transform). Proof intuition: • If the public key is A, t=As, and an adversary can produce a solution Az=tc, then we obtain the equation Az=Asc, and so A(z-sc)=0 is a solution to SIS • (If s is hidden from the adversary and not unique, then z-sc is not 0) • But not useful for other applications: e. g. proof of a proper ciphertext
![Practical Zero-Knowledge Proofs Approximate Proofs. Commitment Scheme to Given: As=t [BDLOP ‘ 18] vectors Practical Zero-Knowledge Proofs Approximate Proofs. Commitment Scheme to Given: As=t [BDLOP ‘ 18] vectors](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-25.jpg)
Practical Zero-Knowledge Proofs Approximate Proofs. Commitment Scheme to Given: As=t [BDLOP ‘ 18] vectors of messages in R [ALS ‘ 20] Prove knowledge of: with linear (over R) small s’, c such that proofs As’=tc [BDLOP] [L ‘ 09, L ’ 12, DDLL ‘ 13, BG ’ 14, … ] (3 KB for 128 -bit security) [YAZXYW ‘ 19, BLS ‘ 19] (300 KB for some instance) Exact Proofs. Fiat-Shamir Digital Signatures. Given: A, As=t Prove knowledge of: s such that As=t Multiplicative Proofs for [BDLOP] [ENS ‘ 20] “Unstructured Proofs” (i. e. proofs over Zq) for [BDLOP] (50 KB) Proofs of Integer Relations (e. g. [LNS ‘ 20] addition, multiplication)
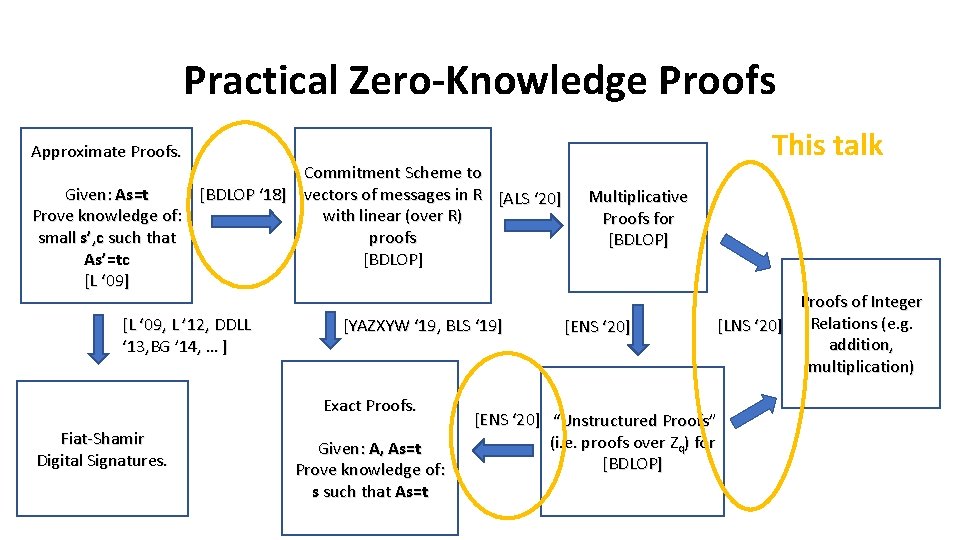
Practical Zero-Knowledge Proofs This talk Approximate Proofs. Commitment Scheme to Given: As=t [BDLOP ‘ 18] vectors of messages in R [ALS ‘ 20] Prove knowledge of: with linear (over R) small s’, c such that proofs As’=tc [BDLOP] [L ‘ 09, L ’ 12, DDLL ‘ 13, BG ’ 14, … ] [YAZXYW ‘ 19, BLS ‘ 19] Exact Proofs. Fiat-Shamir Digital Signatures. Given: A, As=t Prove knowledge of: s such that As=t Multiplicative Proofs for [BDLOP] [ENS ‘ 20] “Unstructured Proofs” (i. e. proofs over Zq) for [BDLOP] Proofs of Integer Relations (e. g. [LNS ‘ 20] addition, multiplication)
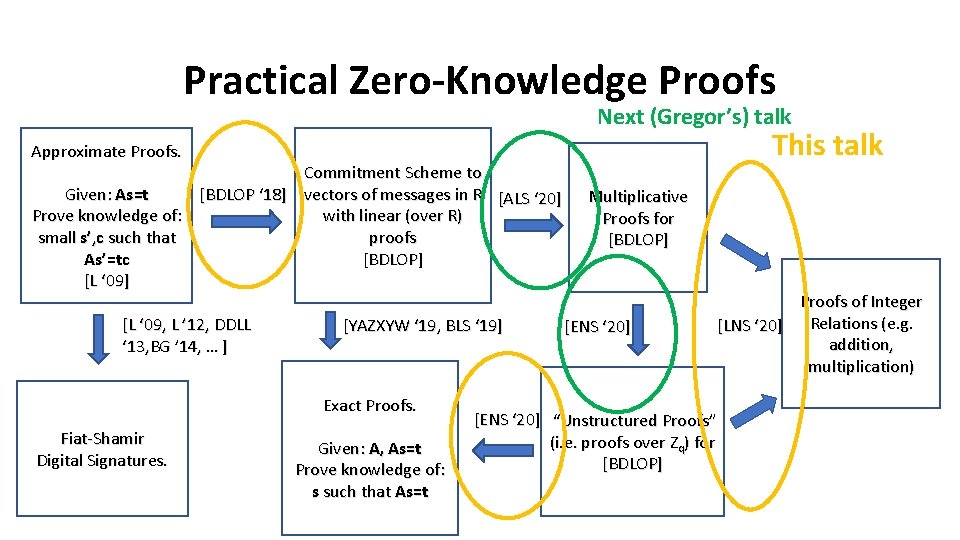
Practical Zero-Knowledge Proofs Next (Gregor’s) talk This talk Approximate Proofs. Commitment Scheme to Given: As=t [BDLOP ‘ 18] vectors of messages in R [ALS ‘ 20] Prove knowledge of: with linear (over R) small s’, c such that proofs As’=tc [BDLOP] [L ‘ 09, L ’ 12, DDLL ‘ 13, BG ’ 14, … ] [YAZXYW ‘ 19, BLS ‘ 19] Exact Proofs. Fiat-Shamir Digital Signatures. Given: A, As=t Prove knowledge of: s such that As=t Multiplicative Proofs for [BDLOP] [ENS ‘ 20] “Unstructured Proofs” (i. e. proofs over Zq) for [BDLOP] Proofs of Integer Relations (e. g. [LNS ‘ 20] addition, multiplication)
![[BDLOP ‘ 18] Commitment Scheme A + B = m r To Open: 1. [BDLOP ‘ 18] Commitment Scheme A + B = m r To Open: 1.](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-28.jpg)
[BDLOP ‘ 18] Commitment Scheme A + B = m r To Open: 1. Reveal small r 2. The m is implicitly t. B - Br 0 t. A t. B Hiding: ( , ) A B r indistinguishable from uniform Binding: Suppose r ≠ r’ are valid openings Then Ar = t. A = Ar’ A(r-r’)=0 Solution to SIS
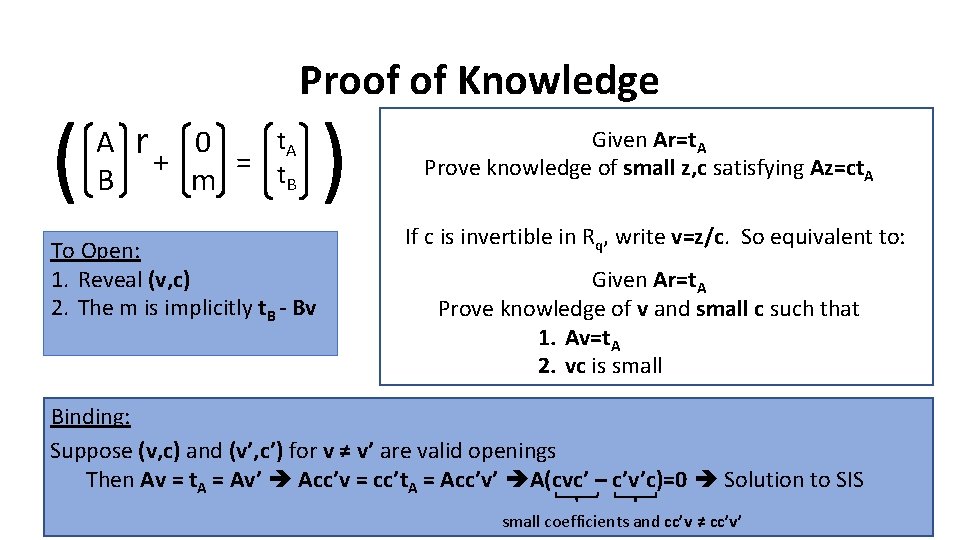
( Proof of Knowledge A B r+ t. A 0 = t B m To Open: 1. Reveal (v, c) 2. The m is implicitly t. B - Bv ) Given Ar=t. A Prove knowledge of small z, c satisfying Az=ct. A If c is invertible in Rq, write v=z/c. So equivalent to: Given Ar=t. A Prove knowledge of v and small c such that 1. Av=t. A 2. vc is small Binding: Suppose (v, c) and (v’, c’) for v ≠ v’ are valid openings Then Av = t. A = Av’ Acc’v = cc’t. A = Acc’v’ A(cvc’ – c’v’c)=0 Solution to SIS small coefficients and cc’v ≠ cc’v’
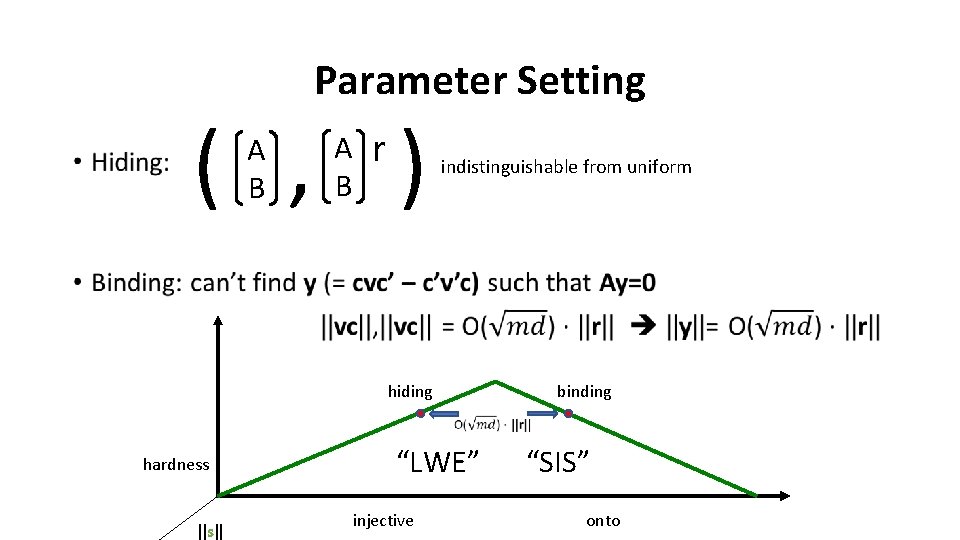
Parameter Setting • ( , ) A B r indistinguishable from uniform hiding hardness ||s|| “LWE” injective binding “SIS” onto
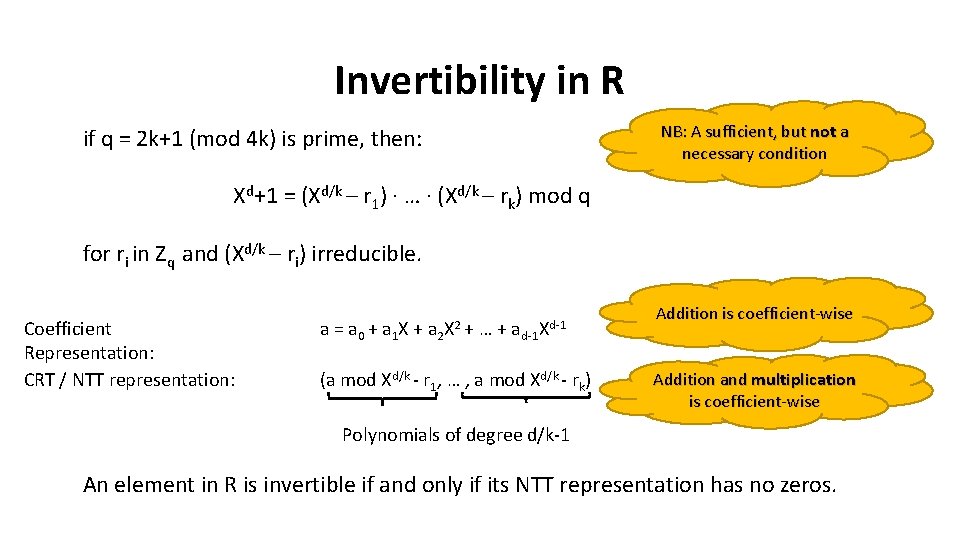
Invertibility in R NB: A sufficient, but not a necessary condition if q = 2 k+1 (mod 4 k) is prime, then: Xd+1 = (Xd/k – r 1) ∙ … ∙ (Xd/k – rk) mod q for ri in Zq and (Xd/k – ri) irreducible. Coefficient Representation: CRT / NTT representation: a = a 0 + a 1 X + a 2 X 2 + …+ ad-1 Xd-1 (a mod Xd/k - r 1, … , a mod Xd/k - rk) Addition is coefficient-wise Addition and multiplication is coefficient-wise Polynomials of degree d/k-1 An element in R is invertible if and only if its NTT representation has no zeros.
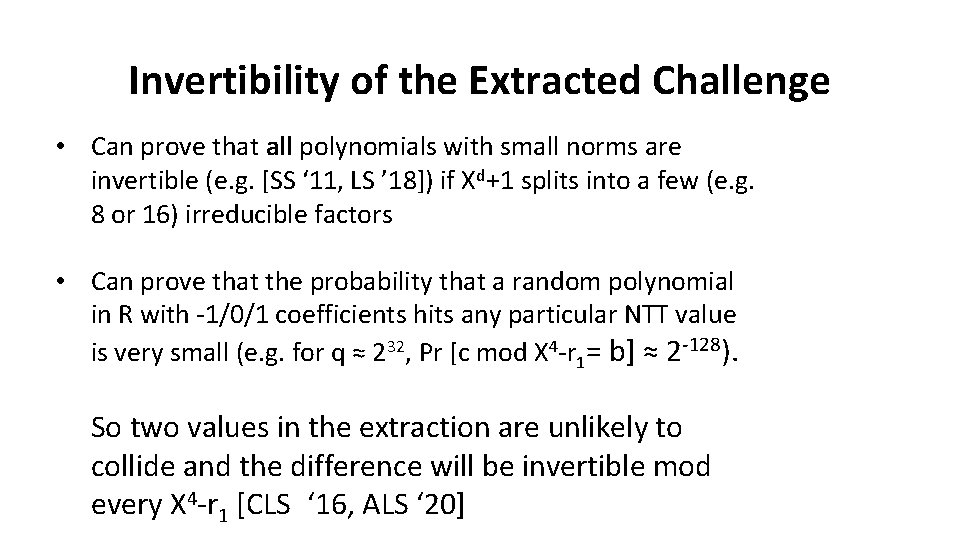
Invertibility of the Extracted Challenge • Can prove that all polynomials with small norms are invertible (e. g. [SS ‘ 11, LS ’ 18]) if Xd+1 splits into a few (e. g. 8 or 16) irreducible factors • Can prove that the probability that a random polynomial in R with -1/0/1 coefficients hits any particular NTT value is very small (e. g. for q ≈ 232, Pr [c mod X 4 -r 1= b] ≈ 2 -128). So two values in the extraction are unlikely to collide and the difference will be invertible mod every X 4 -r 1 [CLS ‘ 16, ALS ‘ 20]
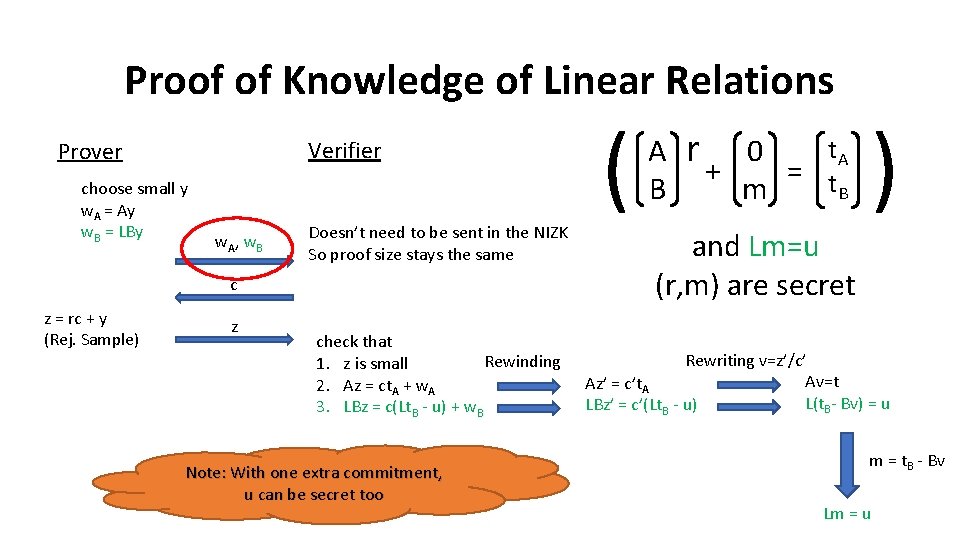
Proof of Knowledge of Linear Relations Verifier Prover choose small y w. A = Ay w. B = LBy w A, w B Doesn’t need to be sent in the NIZK So proof size stays the same c z = rc + y (Rej. Sample) z check that Rewinding 1. z is small 2. Az = ct. A + w. A 3. LBz = c(Lt. B - u) + w. B Note: With one extra commitment, u can be secret too ( A B r+ t. A 0 = t B m ) and Lm=u (r, m) are secret Rewriting v=z’/c’ Av=t Az’ = c’t. A L(t. B- Bv) = u LBz’ = c’(Lt. B - u) m = t. B - Bv Lm = u
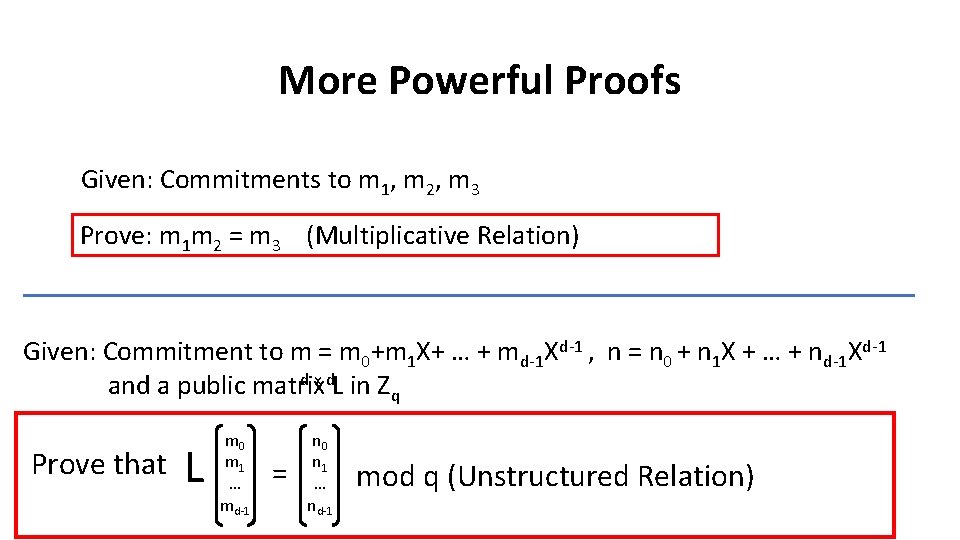
More Powerful Proofs Given: Commitments to m 1, m 2, m 3 Prove: m 1 m 2 = m 3 (Multiplicative Relation) Given: Commitment to m = m 0+m 1 X+ … + md-1 Xd-1 , n = n 0 + n 1 X + … + nd-1 Xd-1 d x d. L in Z and a public matrix q Prove that L m 0 m 1 … md-1 = n 0 n 1 … nd-1 mod q (Unstructured Relation)
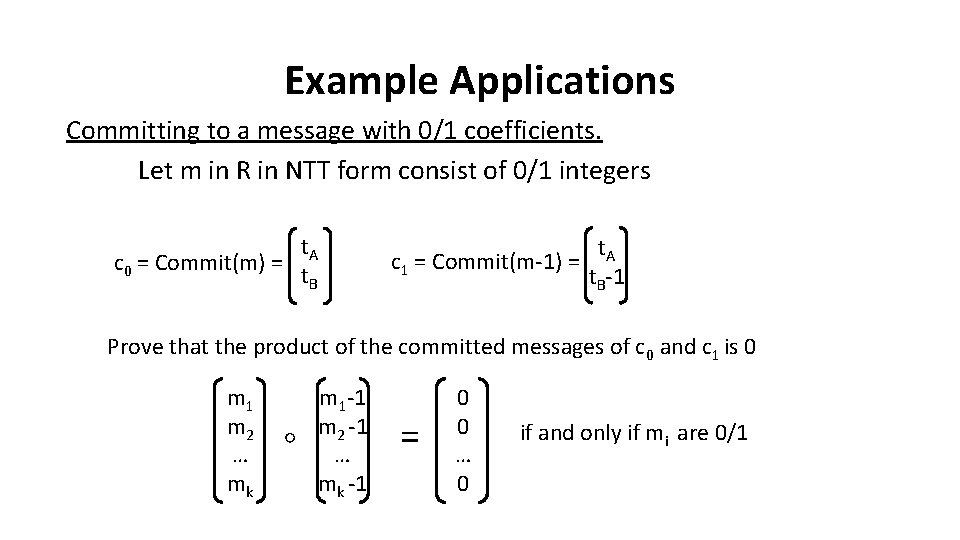
Example Applications Committing to a message with 0/1 coefficients. Let m in R in NTT form consist of 0/1 integers t. A c 0 = Commit(m) = t. B t. A c 1 = Commit(m-1) = t. B-1 Prove that the product of the committed messages of c 0 and c 1 is 0 m 1 m 2 … mk ◦ m 1 -1 m 2 -1 … mk -1 = 0 0 … 0 if and only if mi are 0/1
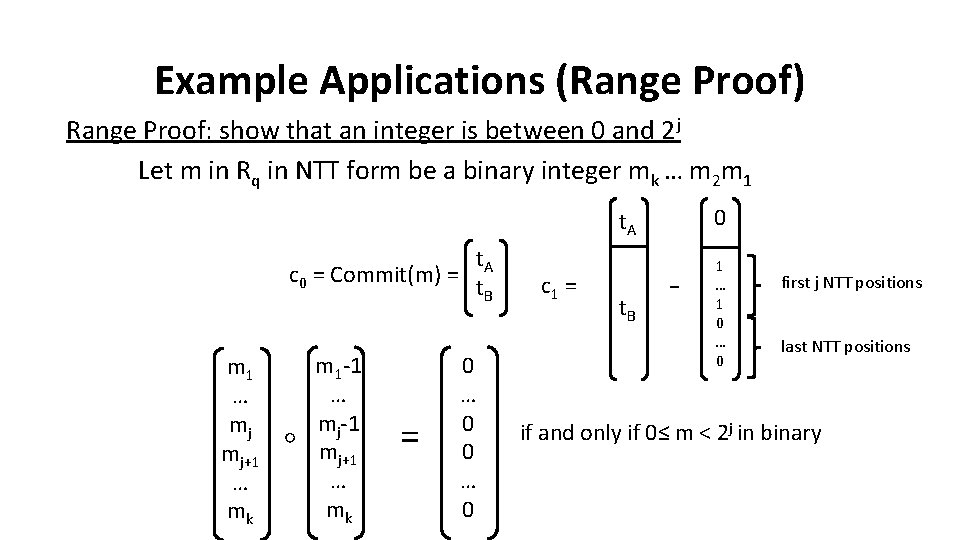
Example Applications (Range Proof) Range Proof: show that an integer is between 0 and 2 j Let m in Rq in NTT form be a binary integer mk … m 2 m 1 t. A c 0 = Commit(m) = t. B m 1 … mj mj+1 … mk ◦ m 1 -1 … mj-1 mj+1 … mk = 0 … 0 c 1 = t. A 0 t. B 1 … 1 0 … 0 - first j NTT positions last NTT positions if and only if 0≤ m < 2 j in binary
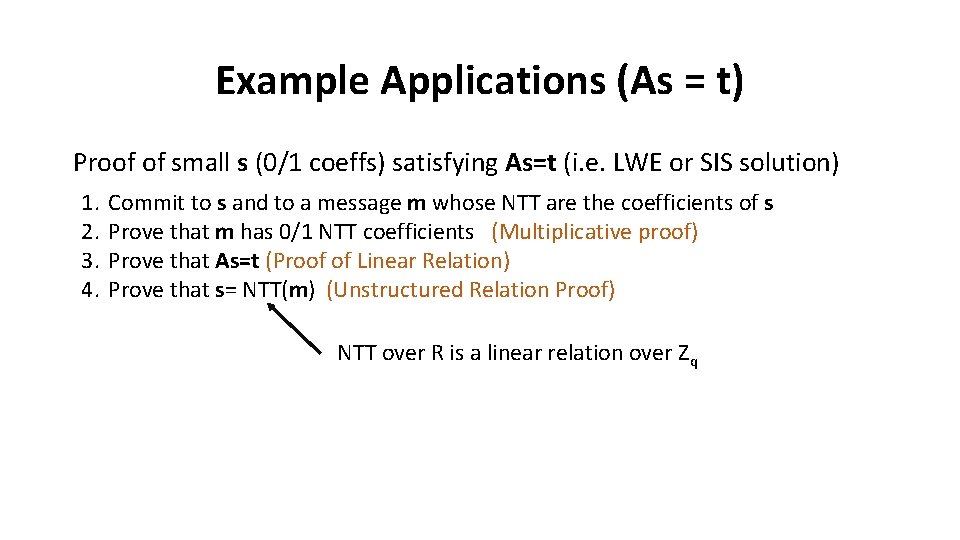
Example Applications (As = t) Proof of small s (0/1 coeffs) satisfying As=t (i. e. LWE or SIS solution) 1. 2. 3. 4. Commit to s and to a message m whose NTT are the coefficients of s Prove that m has 0/1 NTT coefficients (Multiplicative proof) Prove that As=t (Proof of Linear Relation) Prove that s= NTT(m) (Unstructured Relation Proof) NTT over R is a linear relation over Zq
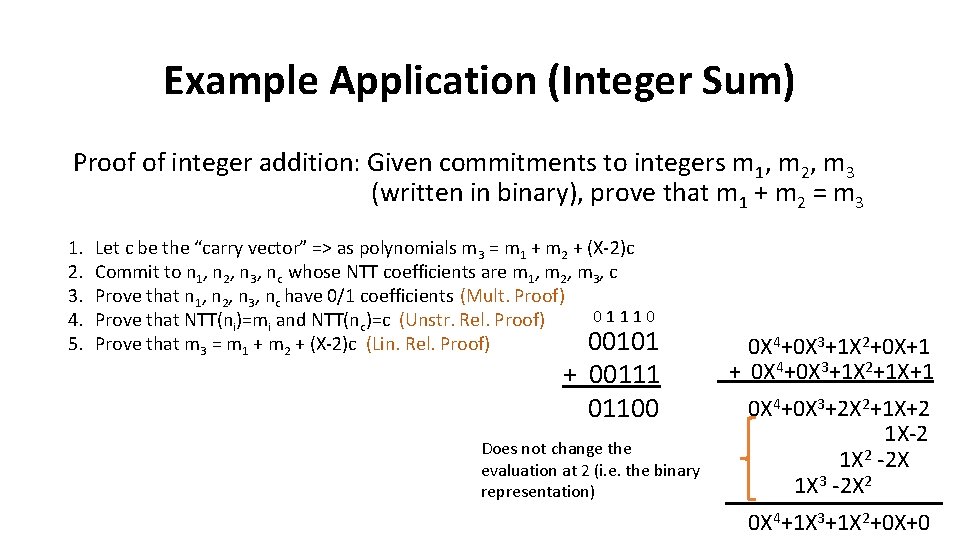
Example Application (Integer Sum) Proof of integer addition: Given commitments to integers m 1, m 2, m 3 (written in binary), prove that m 1 + m 2 = m 3 1. 2. 3. 4. 5. Let c be the “carry vector” => as polynomials m 3 = m 1 + m 2 + (X-2)c Commit to n 1, n 2, n 3, nc whose NTT coefficients are m 1, m 2, m 3, c Prove that n 1, n 2, n 3, nc have 0/1 coefficients (Mult. Proof) 01110 Prove that NTT(ni)=mi and NTT(nc)=c (Unstr. Rel. Proof) Prove that m 3 = m 1 + m 2 + (X-2)c (Lin. Rel. Proof) 00101 + 00111 01100 Does not change the evaluation at 2 (i. e. the binary representation) 0 X 4+0 X 3+1 X 2+0 X+1 + 0 X 4+0 X 3+1 X 2+1 X+1 0 X 4+0 X 3+2 X 2+1 X+2 1 X-2 1 X 2 -2 X 1 X 3 -2 X 2 0 X 4+1 X 3+1 X 2+0 X+0
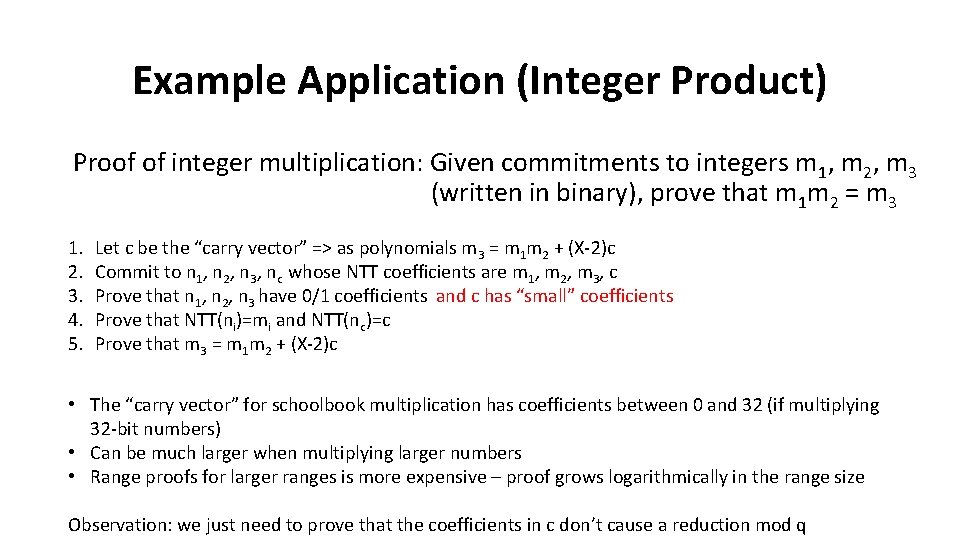
Example Application (Integer Product) Proof of integer multiplication: Given commitments to integers m 1, m 2, m 3 (written in binary), prove that m 1 m 2 = m 3 1. 2. 3. 4. 5. Let c be the “carry vector” => as polynomials m 3 = m 1 m 2 + (X-2)c Commit to n 1, n 2, n 3, nc whose NTT coefficients are m 1, m 2, m 3, c Prove that n 1, n 2, n 3 have 0/1 coefficients and c has “small” coefficients Prove that NTT(ni)=mi and NTT(nc)=c Prove that m 3 = m 1 m 2 + (X-2)c • The “carry vector” for schoolbook multiplication has coefficients between 0 and 32 (if multiplying 32 -bit numbers) • Can be much larger when multiplying larger numbers • Range proofs for larger ranges is more expensive – proof grows logarithmically in the range size Observation: we just need to prove that the coefficients in c don’t cause a reduction mod q
![“Relaxed” Range Proof Lemma [BL ‘ 18]: let c be a vector in Zk “Relaxed” Range Proof Lemma [BL ‘ 18]: let c be a vector in Zk](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-40.jpg)
“Relaxed” Range Proof Lemma [BL ‘ 18]: let c be a vector in Zk and y a vector in Zn If U is chosen at random with coefficients in 0/1, then Pr[ ||Uc+y mod q||∞ ≤. 5∙||c||∞ ] ≤ 2 -n In other words, if Uc+y mod q is small, then c must be small. U c + y = Important Notes: • If working over Z[X]/(Xd+1), the probability does not become 2 -dn, it stays as 2 -n • Taking the coefficients of U from a larger range than 0/1 also does not help So it’s important that the random matrix U be integer even if working over a larger ring z
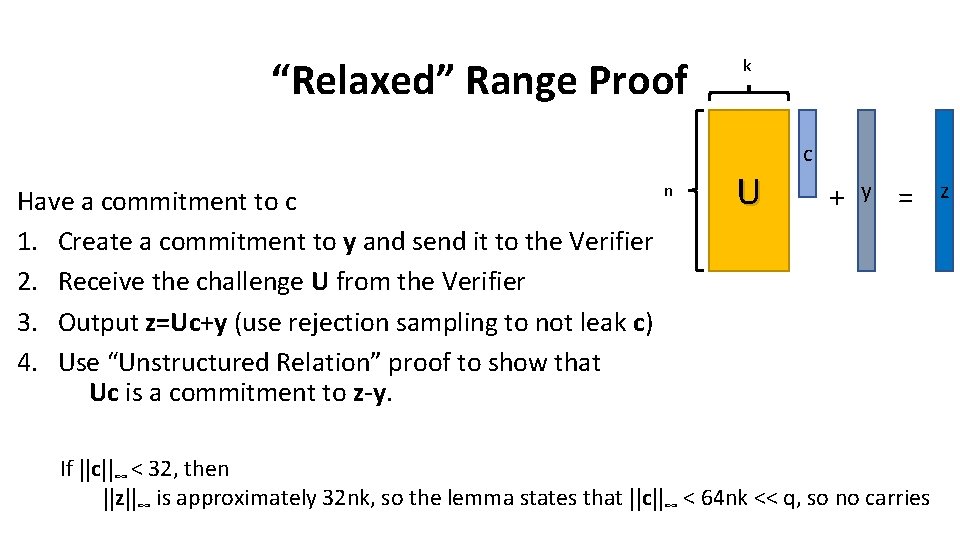
“Relaxed” Range Proof Have a commitment to c 1. Create a commitment to y and send it to the Verifier 2. Receive the challenge U from the Verifier 3. Output z=Uc+y (use rejection sampling to not leak c) 4. Use “Unstructured Relation” proof to show that Uc is a commitment to z-y. n k U c + y = If ||c||∞ < 32, then ||z||∞ is approximately 32 nk, so the lemma states that ||c||∞ < 64 nk << q, so no carries z
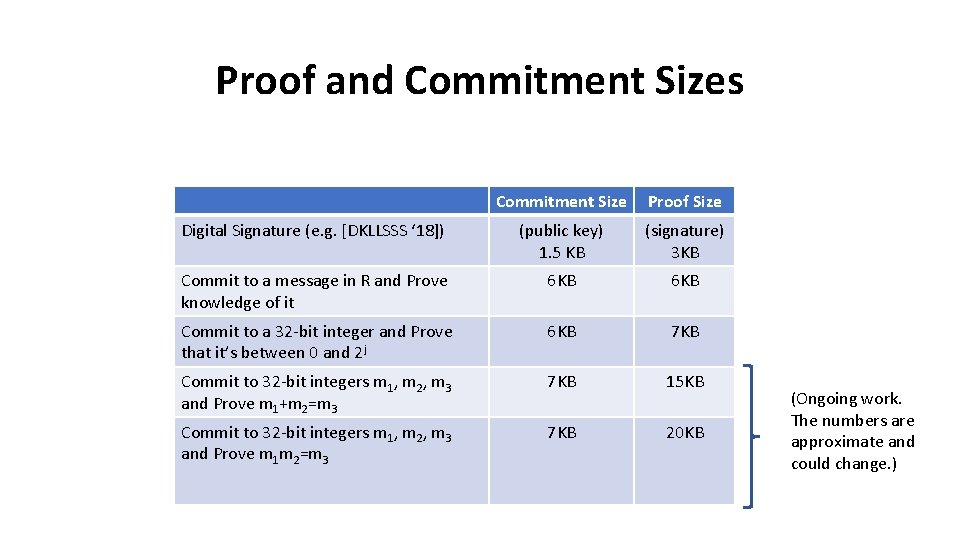
Proof and Commitment Sizes Commitment Size Proof Size Digital Signature (e. g. [DKLLSSS ‘ 18]) (public key) 1. 5 KB (signature) 3 KB Commit to a message in R and Prove knowledge of it 6 KB Commit to a 32 -bit integer and Prove that it’s between 0 and 2 j 6 KB 7 KB Commit to 32 -bit integers m 1, m 2, m 3 and Prove m 1+m 2=m 3 7 KB 15 KB Commit to 32 -bit integers m 1, m 2, m 3 and Prove m 1 m 2=m 3 7 KB 20 KB (Ongoing work. The numbers are approximate and could change. )
Lots of Open Problems • Improve BDLOP commitment Improving ZK proofs • Improve ZK proofs without improving BDLOP commitments • Apply ZK proofs to more efficient blind signatures / group signatures / etc. • Practical succinct proofs. There are some sublinear proofs, but the noise grows a lot. • ROM vs QROM the most efficient instantiations are based on the hardness of lattice problems in the ROM. • Can we prove their hardness in the QROM (see Mark’s talk Tuesday) • Does it matter? i. e. can we produce any natural example where a proof in the ROM ends up being insecure against a quantum attacker?
![Thanks! • [ALS ‘ 20] Thomas Attema, Vadim Lyubashevsky Gregor Seiler: Practical Product Proofs Thanks! • [ALS ‘ 20] Thomas Attema, Vadim Lyubashevsky Gregor Seiler: Practical Product Proofs](http://slidetodoc.com/presentation_image_h2/f7616257c12b2198b0627f9bf8ec8a18/image-44.jpg)
Thanks! • [ALS ‘ 20] Thomas Attema, Vadim Lyubashevsky Gregor Seiler: Practical Product Proofs for Lattice Commitments (In submission) • [BCRSVW ‘ 19]: Eli Ben-Sasson, Alessandro Chiesa, Michael Riabzev, Nicholas Spooner, Madars Virza, Nicholas P. Ward: Aurora: Transparent Succinct Arguments for R 1 CS. EUROCRYPT (1) 2019 • [BDLOP ‘ 18]: Carsten Baum, Ivan Damgård, Vadim Lyubashevsky, Sabine Oechsner, Chris Peikert: More Efficient Commitments from Structured Lattice Assumptions. SCN 2018 • [BG ‘ 14]: Shi Bai, Steven D. Galbraith: An Improved Compression Technique for Signatures Based on Learning with Errors. CT-RSA 2014: 28 -47 • [BL ‘ 18]: Carsten Baum, Vadim Lyubashevsky: Simple Amortized Proofs of Shortness for Linear Relations over Polynomial Rings. IACR Cryptology e. Print Archive 2017 • [BLS ‘ 19]: Jonathan Bootle, Vadim Lyubashevsky, Gregor Seiler: Algebraic Techniques for Short(er) Exact Lattice-Based Zero-Knowledge Proofs. CRYPTO (1) 2019 • [CLS ‘ 16]: Hao Chen, Kristin E. Lauter, Katherine E. Stange: Security Considerations for Galois Non-dual RLWE Families. SAC 2016 • [DDLL ‘ 13]: Léo Ducas, Alain Durmus, Tancrède Lepoint, Vadim Lyubashevsky: Lattice Signatures and Bimodal Gaussians. CRYPTO (1) 2013: • [DKLLSSS ‘ 18]: Léo Ducas, Eike Kiltz , Tancrède Lepoint, Vadim Lyubashevsky, Peter Schwabe, Gregor Seiler, Damien Stehlé: CRYSTALS-Dilithium: A Lattice-Based Digital Signature Scheme. IACR Trans. Cryptogr. Hardw. Embed. Syst. 2018(1) • [ENS ‘ 20]: Muhammed Esgin, Ngoc Khanh Nguyen, Gregor Seiler: Practical Exact Proofs from Lattices: New Techniques to Exploit Fully-Splitting Rings (In Submission) • [L ‘ 09]: Vadim Lyubashevsky: Fiat-Shamir with Aborts: Applications to Lattice and Factoring-Based Signatures. ASIACRYPT 2009 • [L ‘ 12]: Vadim Lyubashevsky: Lattice Signatures without Trapdoors. EUROCRYPT 2012 • [LS ‘ 18]: Vadim Lyubashevsky, Gregor Seiler: Short, Invertible Elements in Partially Splitting Cyclotomic Rings and Applications to Lattice-Based Zero-Knowledge Proofs. EUROCRYPT (1) 2018 • [LS ‘ 19]: Vadim Lyubashevsky, Gregor Seiler: NTTRU: Truly Fast NTRU Using NTT. IACR Trans. Cryptogr. Hardw. Embed. Syst. 2019 • [LNS ‘ 20]: Vadim Lyubashevsky, Ngoc Khanh Nguyen, Gregor Seiler: Practical Lattice-Based Zero-Knowledge Proofs for Integer Relations (In preparation) • [SS ‘ 11]: Damien Stehlé, Ron Steinfeld: Making NTRU as Secure as Worst-Case Problems over Ideal Lattices. EUROCRYPT 2011 • [YAZXYW ’ 19]: Rupeng Yang, Man Ho Au, Zhenfei Zhang, Qiuliang Xu, Zuoxia Yu, William Whyte: Efficient Lattice-Based Zero-Knowledge Arguments with Standard Soundness: Construction and Applications. CRYPTO (1) 2019
- Slides: 44