Introduction to LatticeBased Cryptography Vadim Lyubashevsky TelAviv University
Introduction to Lattice-Based Cryptography Vadim Lyubashevsky Tel-Aviv University September 9, 2009
Cryptographic Hardness Assumptions Factoring is hard Discrete Log Problem is hard Diffie-Hellman problem is hard Decisional Diffie-Hellman problem is hard Problems involving Elliptic Curves are hard Many assumptions
Why Do We Need More Assumptions? Number theoretic functions are rather slow Factoring, Discrete Log, Elliptic curves are “of the same flavor” Quantum computers break all number theoretic assumptions
Lattice-Based Cryptography Seemingly very different assumptions from factoring, discrete log, elliptic curves Simple descriptions and implementations Very parallelizable Resists quantum attacks (we think) Security based on worst-case problems
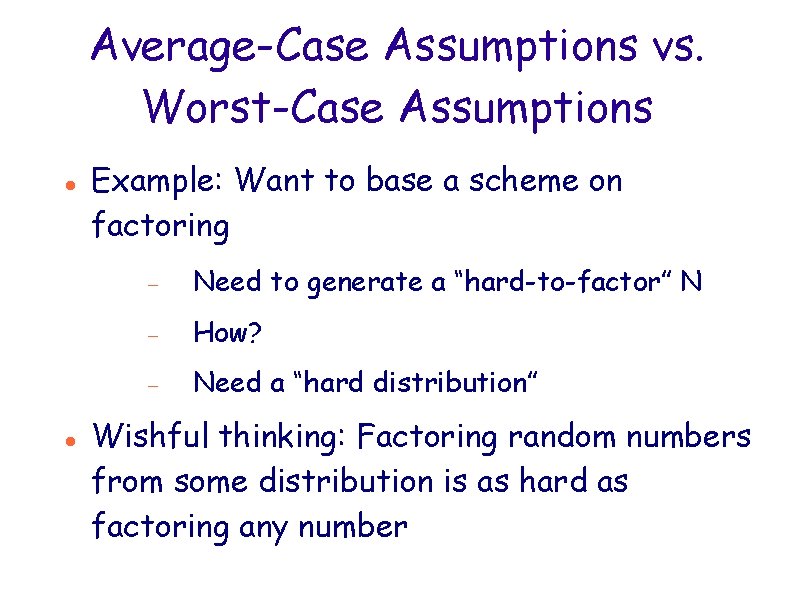
Average-Case Assumptions vs. Worst-Case Assumptions Example: Want to base a scheme on factoring Need to generate a “hard-to-factor” N How? Need a “hard distribution” Wishful thinking: Factoring random numbers from some distribution is as hard as factoring any number
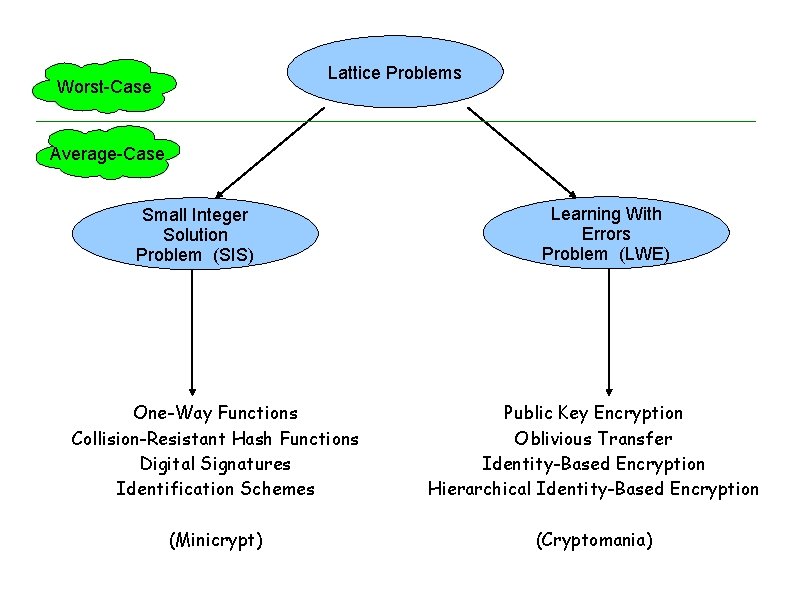
Lattice Problems Worst-Case Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)
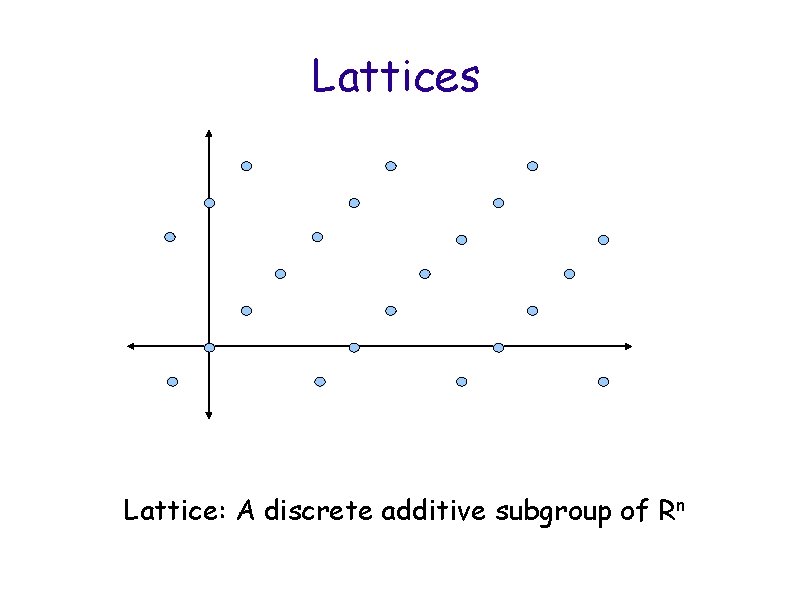
Lattices Lattice: A discrete additive subgroup of Rn
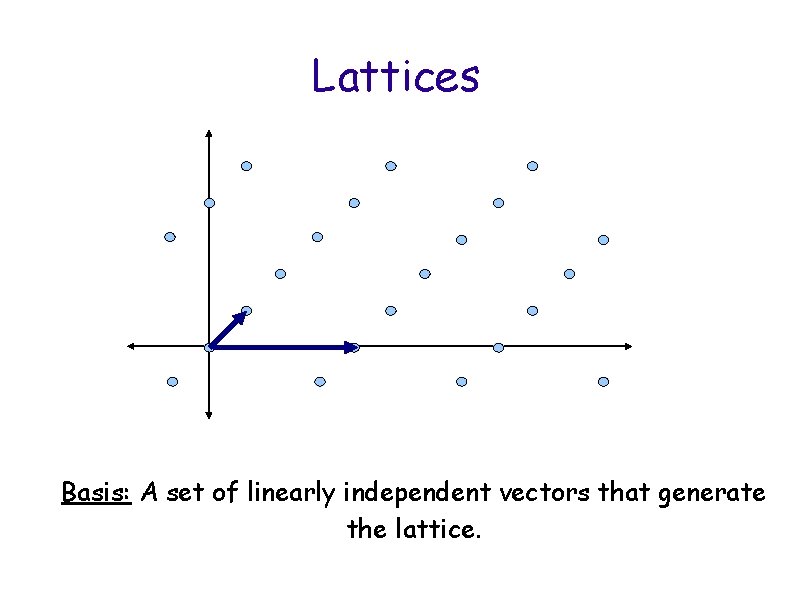
Lattices Basis: A set of linearly independent vectors that generate the lattice.
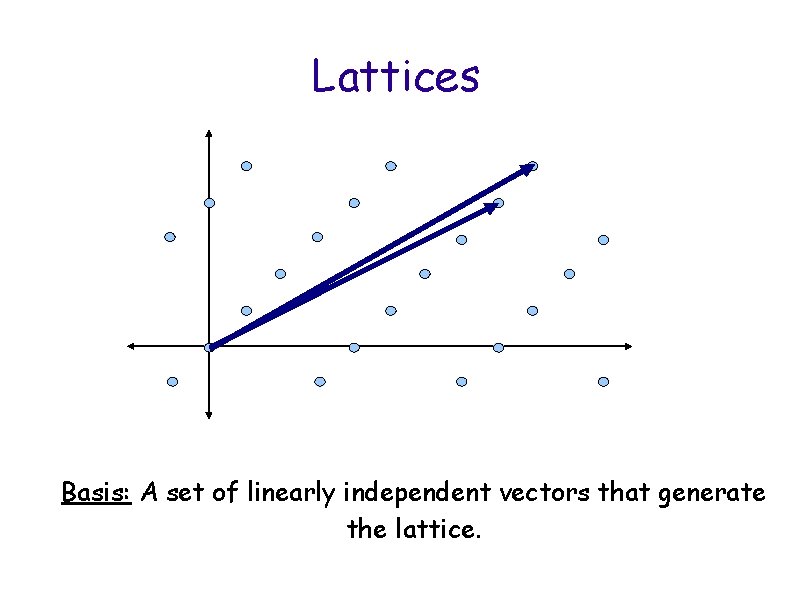
Lattices Basis: A set of linearly independent vectors that generate the lattice.
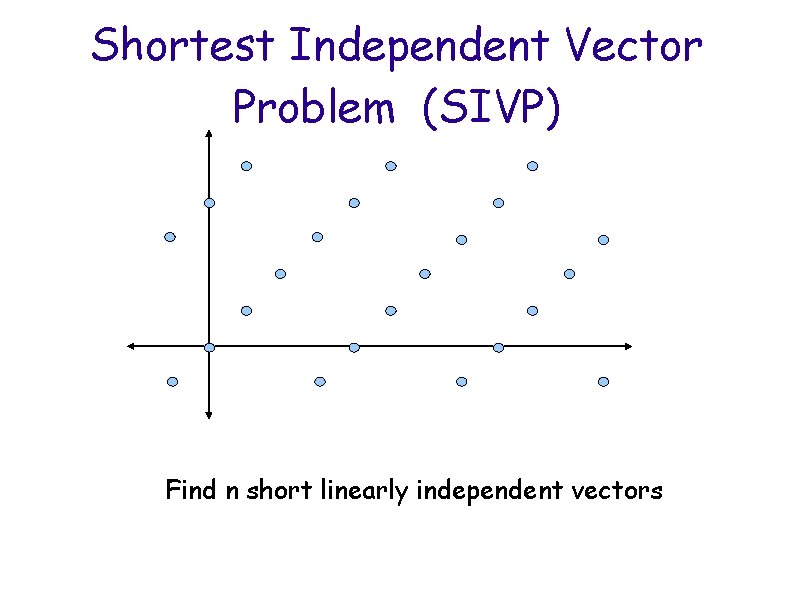
Shortest Independent Vector Problem (SIVP) Find n short linearly independent vectors
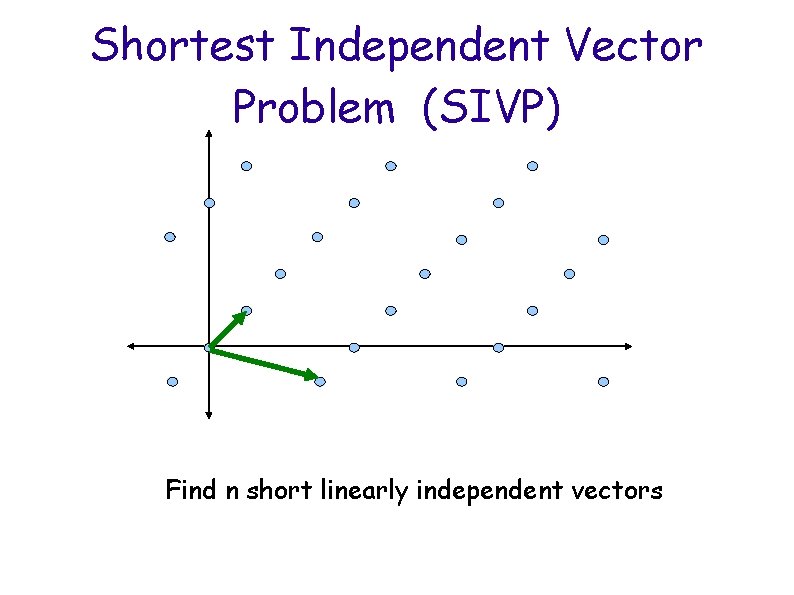
Shortest Independent Vector Problem (SIVP) Find n short linearly independent vectors
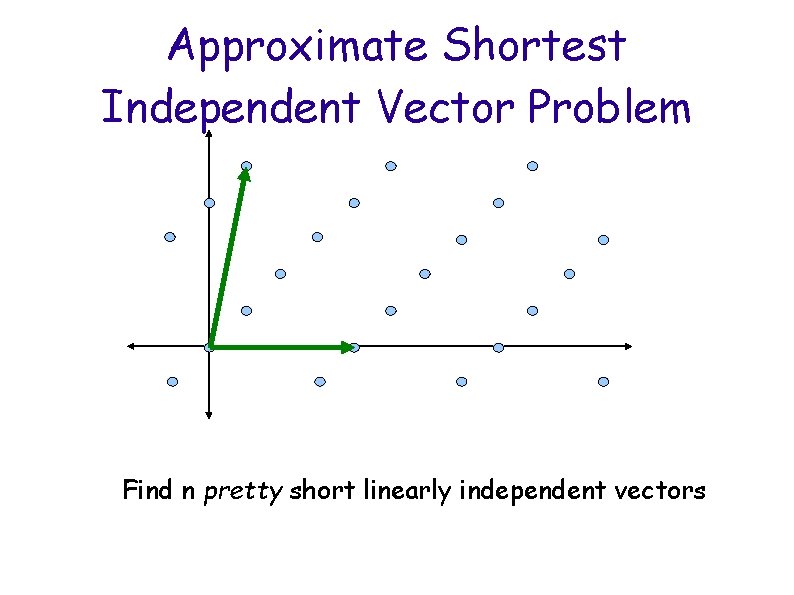
Approximate Shortest Independent Vector Problem Find n pretty short linearly independent vectors
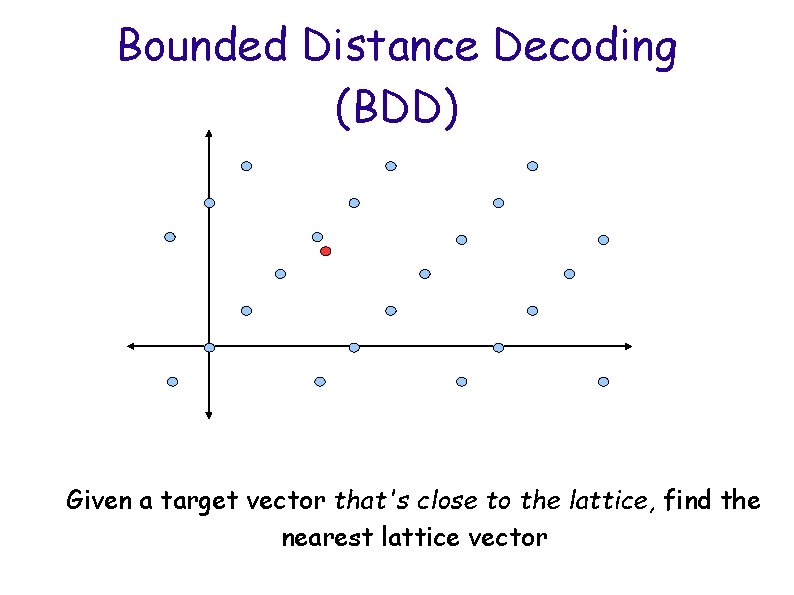
Bounded Distance Decoding (BDD) Given a target vector that's close to the lattice, find the nearest lattice vector
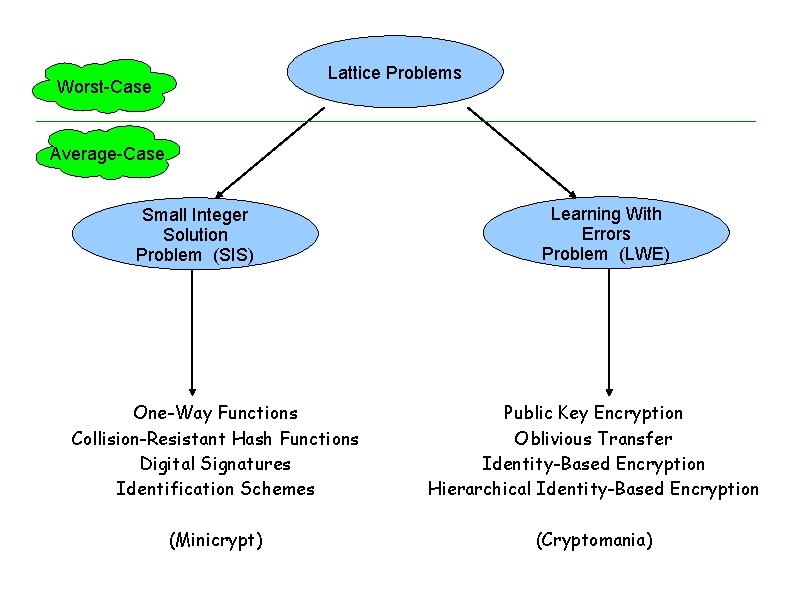
Lattice Problems Worst-Case Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)
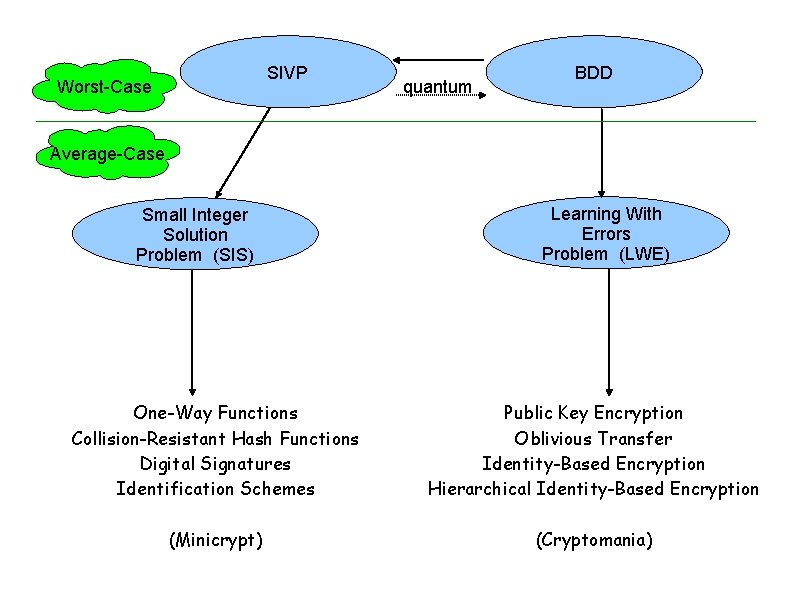
SIVP Worst-Case quantum BDD Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)
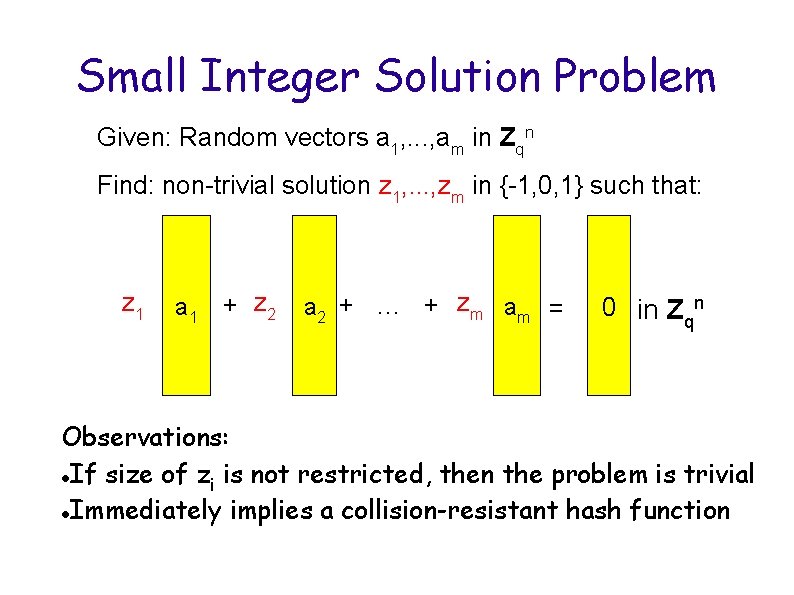
Small Integer Solution Problem Given: Random vectors a 1, . . . , am in Zqn Find: non-trivial solution z 1, . . . , zm in {-1, 0, 1} such that: z 1 a 1 + z 2 a 2 + … + zm am = 0 in Zqn Observations: If size of z is not restricted, then the problem is trivial i Immediately implies a collision-resistant hash function
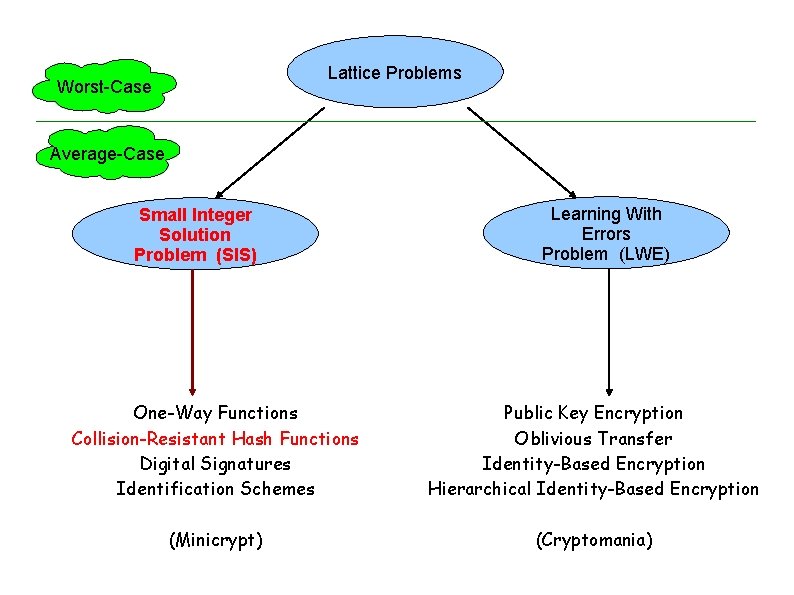
Lattice Problems Worst-Case Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)
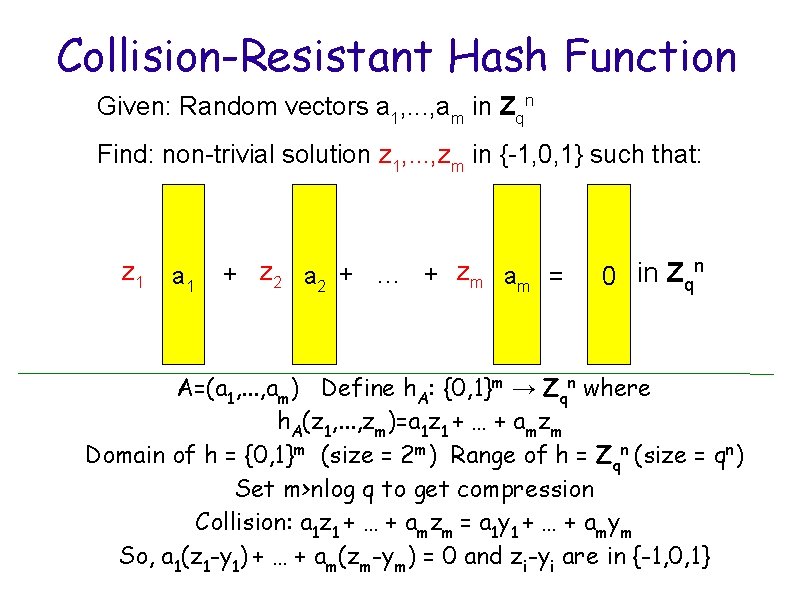
Collision-Resistant Hash Function Given: Random vectors a 1, . . . , am in Zqn Find: non-trivial solution z 1, . . . , zm in {-1, 0, 1} such that: z 1 a 1 + z 2 a 2 + … + zm am = 0 in Zqn A=(a 1, . . . , am) Define h. A: {0, 1}m → Zqn where h. A(z 1, . . . , zm)=a 1 z 1 + … + amzm Domain of h = {0, 1}m (size = 2 m) Range of h = Zqn (size = qn) Set m>nlog q to get compression Collision: a 1 z 1 + … + amzm = a 1 y 1 + … + amym So, a 1(z 1 -y 1) + … + am(zm-ym) = 0 and zi-yi are in {-1, 0, 1}
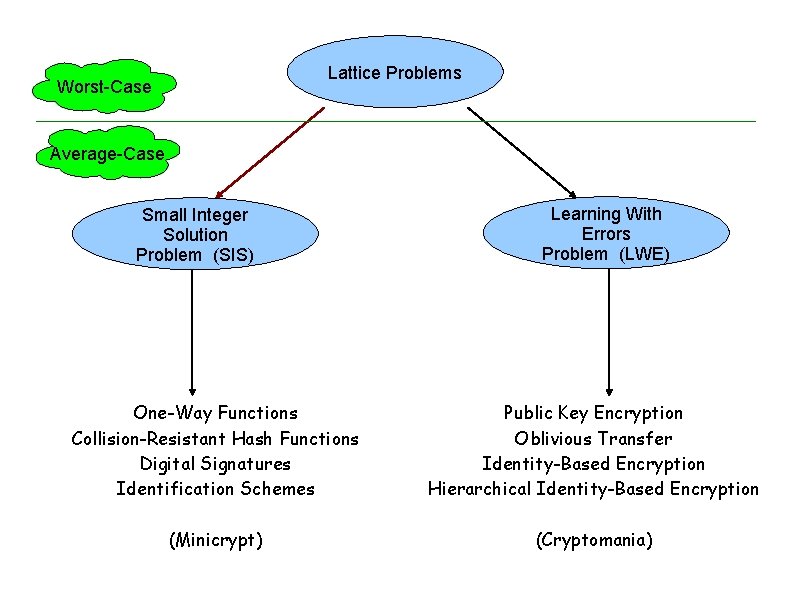
Lattice Problems Worst-Case Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)
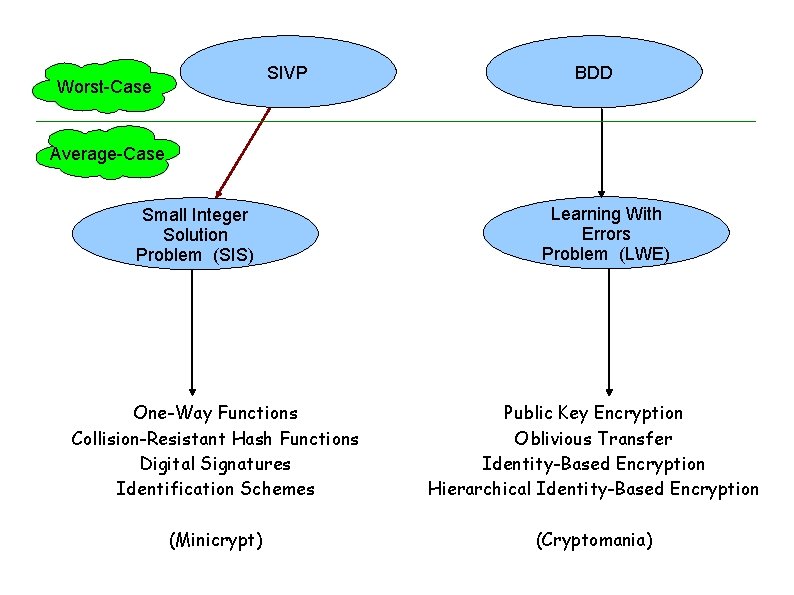
SIVP Worst-Case BDD Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)
For Any Lattice. . . Consider the distribution obtained by: 1. Pick a uniformly random lattice point 2. Sample from a Gaussian distribution centered at the lattice point
One-Dimensional Gaussian Distribution
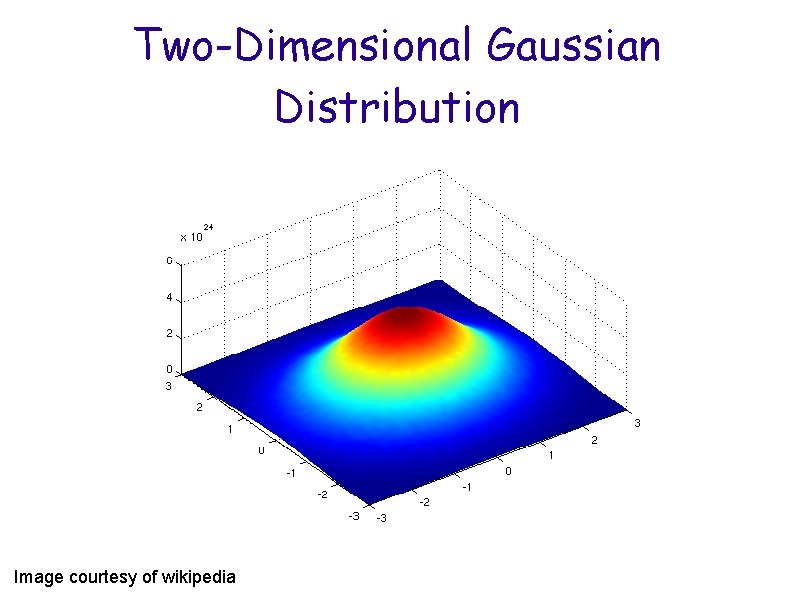
Two-Dimensional Gaussian Distribution Image courtesy of wikipedia
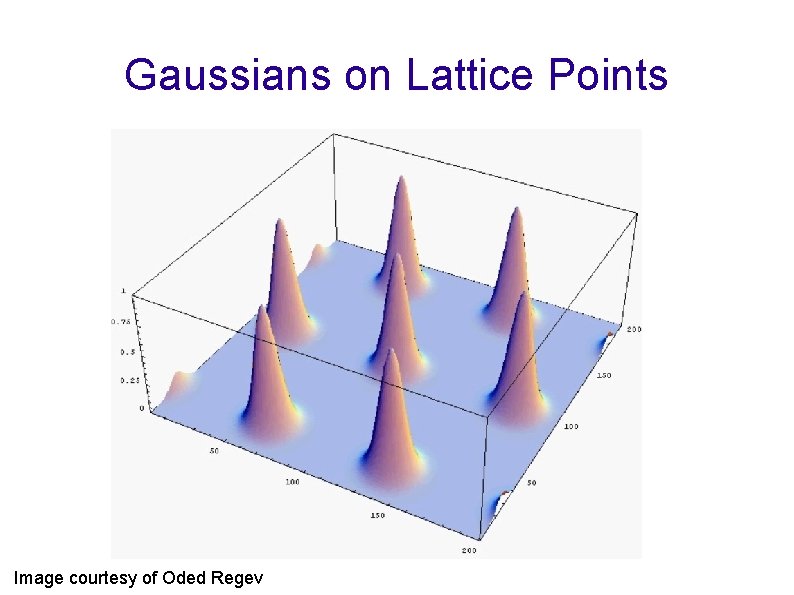
Gaussians on Lattice Points Image courtesy of Oded Regev
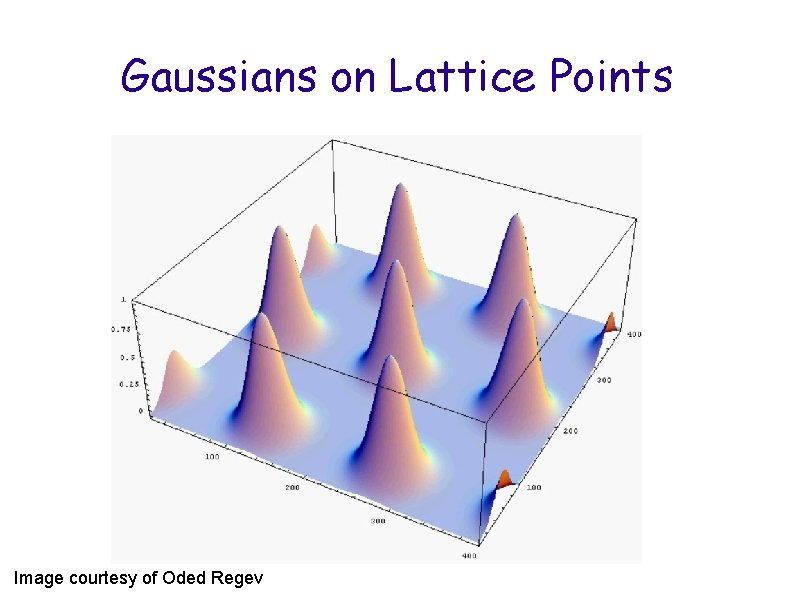
Gaussians on Lattice Points Image courtesy of Oded Regev
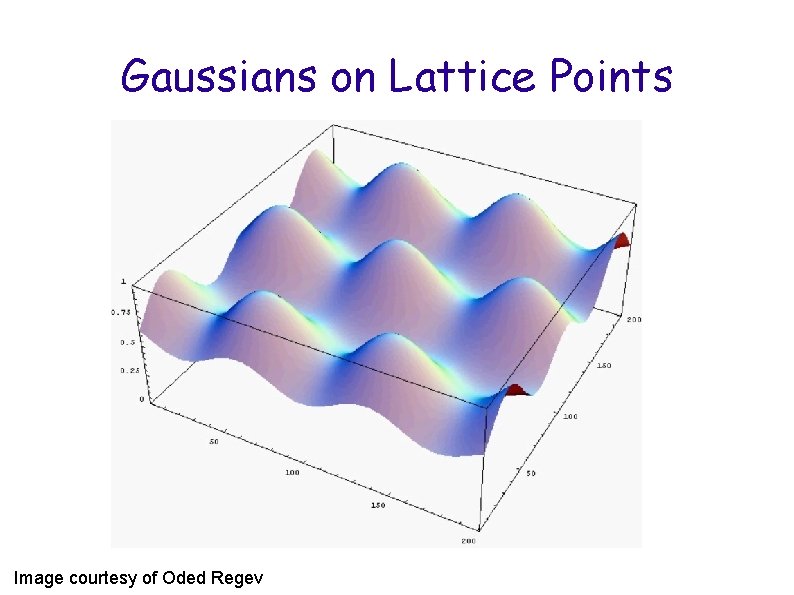
Gaussians on Lattice Points Image courtesy of Oded Regev
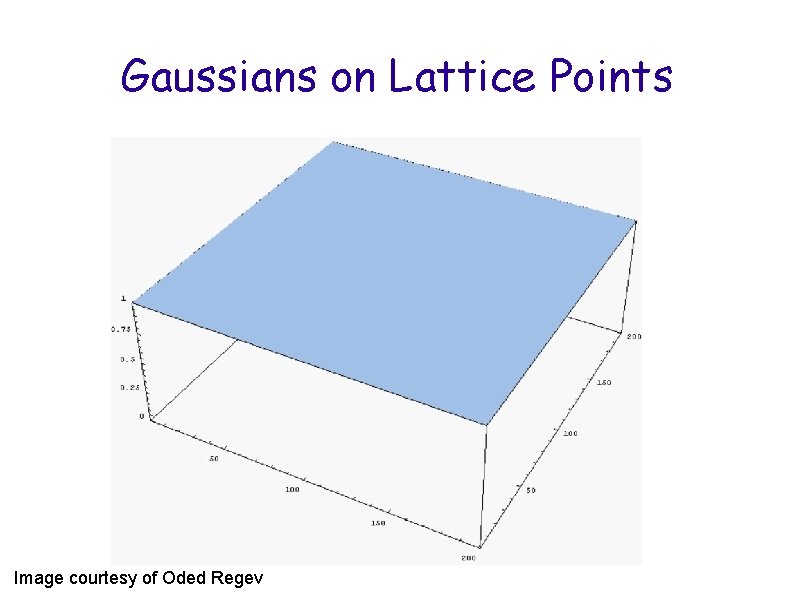
Gaussians on Lattice Points Image courtesy of Oded Regev
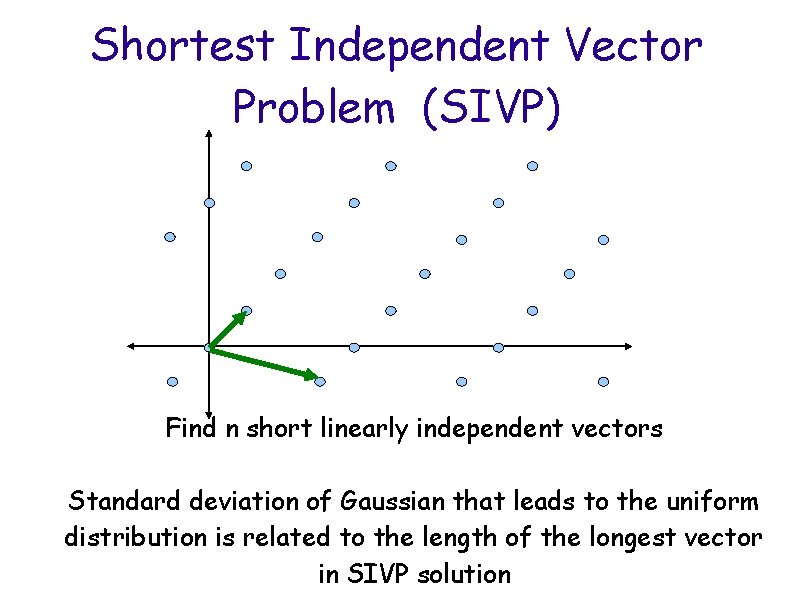
Shortest Independent Vector Problem (SIVP) Find n short linearly independent vectors Standard deviation of Gaussian that leads to the uniform distribution is related to the length of the longest vector in SIVP solution
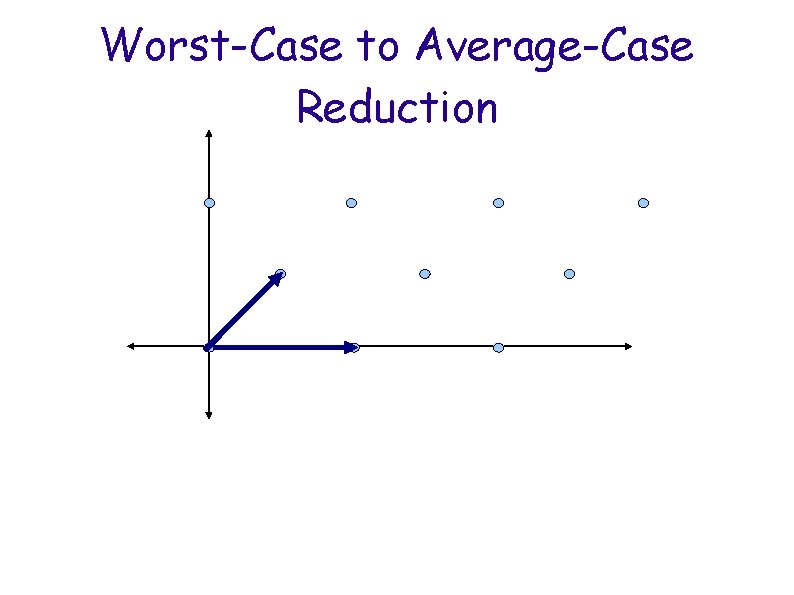
Worst-Case to Average-Case Reduction
Worst-Case to Average-Case Reduction
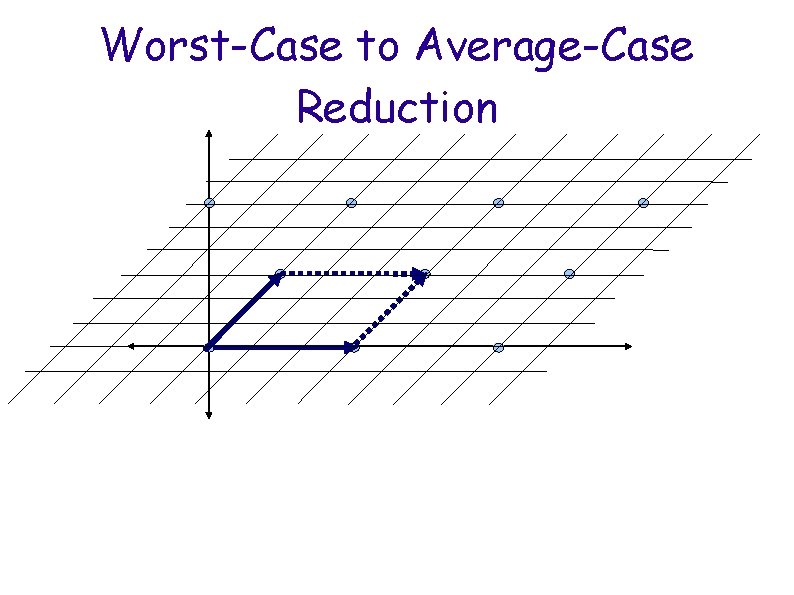
Worst-Case to Average-Case Reduction 2 1 0 1 2 0 1 Important: All lattice points have label (0, 0) and All points labeled (0, 0) are lattice points (0 n in n dimensional lattices)
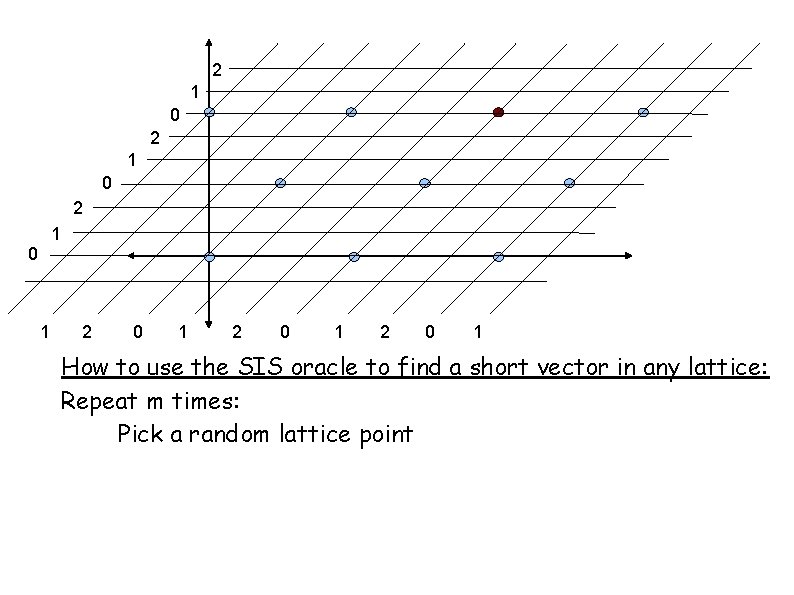
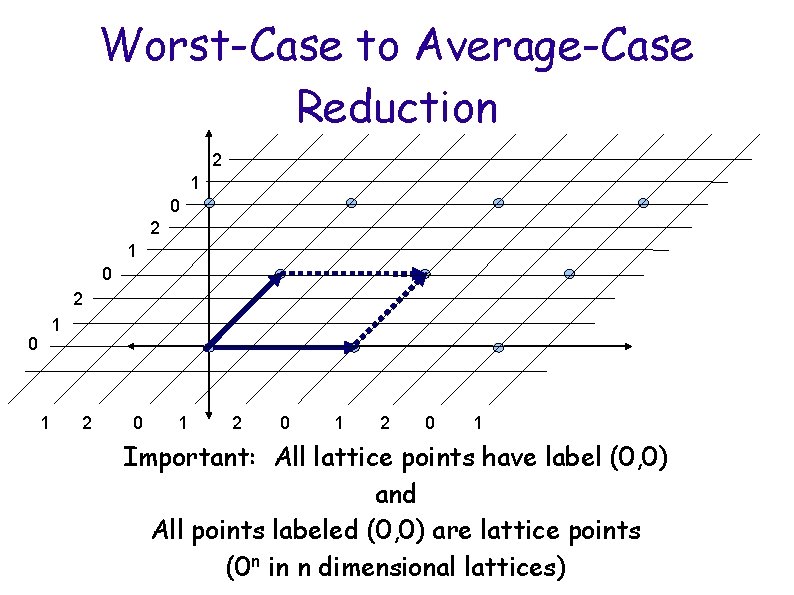
2 1 0 1 2 0 1 How to use the SIS oracle to find a short vector in any lattice: Repeat m times: Pick a random lattice point
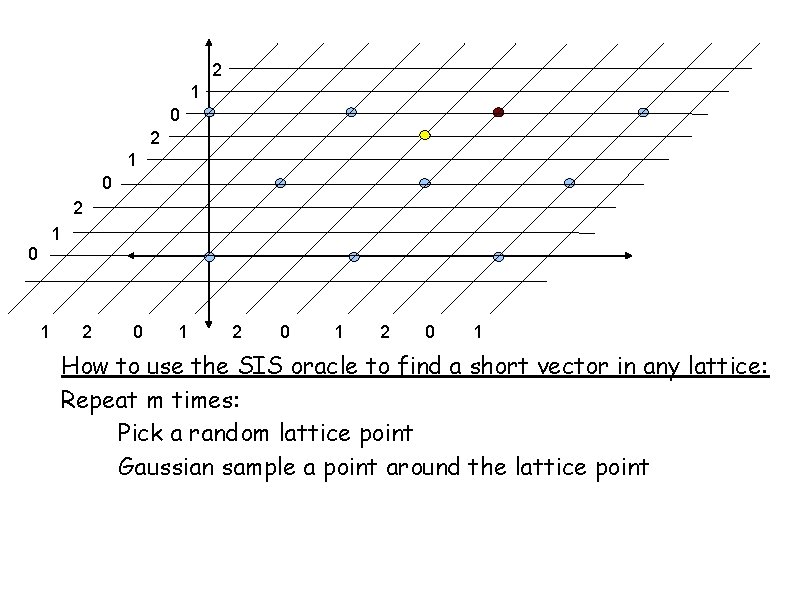
2 1 0 1 2 0 1 How to use the SIS oracle to find a short vector in any lattice: Repeat m times: Pick a random lattice point Gaussian sample a point around the lattice point

2 1 0 1 2 0 1 How to use the SIS oracle to find a short vector in any lattice: Repeat m times: Pick a random lattice point Gaussian sample a point around the lattice point All the samples are uniform in Zqn
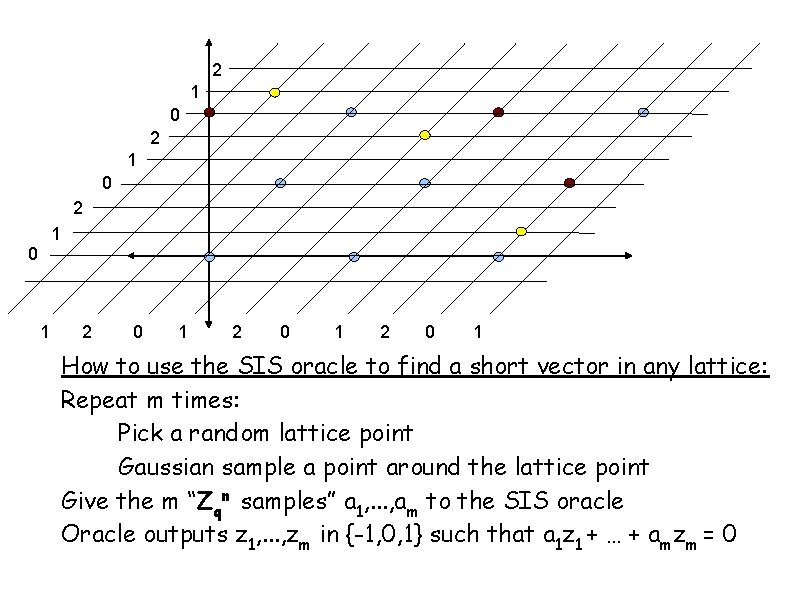
2 1 0 1 2 0 1 How to use the SIS oracle to find a short vector in any lattice: Repeat m times: Pick a random lattice point Gaussian sample a point around the lattice point Give the m “Zqn samples” a 1, . . . , am to the SIS oracle Oracle outputs z 1, . . . , zm in {-1, 0, 1} such that a 1 z 1 + … + amzm = 0
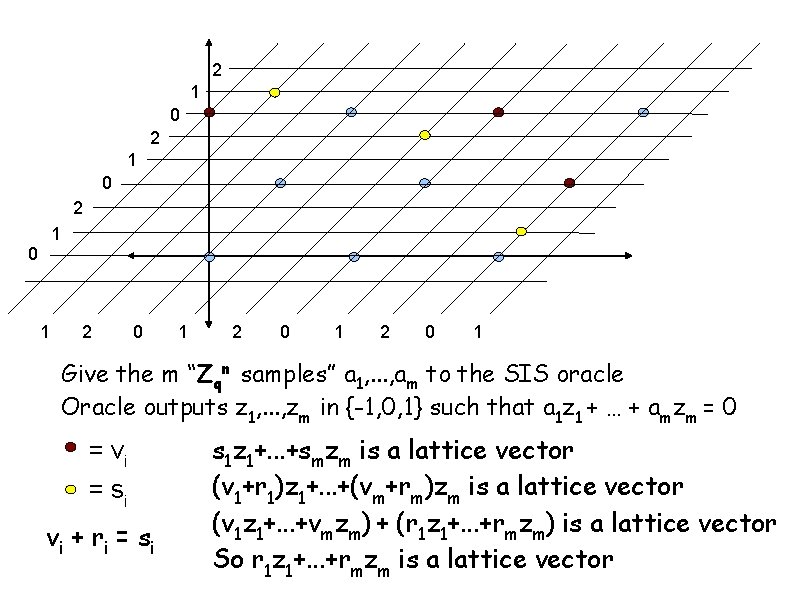
2 1 0 1 2 0 1 Give the m “Zqn samples” a 1, . . . , am to the SIS oracle Oracle outputs z 1, . . . , zm in {-1, 0, 1} such that a 1 z 1 + … + amzm = 0 = vi = si vi + r i = s i s 1 z 1+. . . +smzm is a lattice vector (v 1+r 1)z 1+. . . +(vm+rm)zm is a lattice vector (v 1 z 1+. . . +vmzm) + (r 1 z 1+. . . +rmzm) is a lattice vector So r 1 z 1+. . . +rmzm is a lattice vector
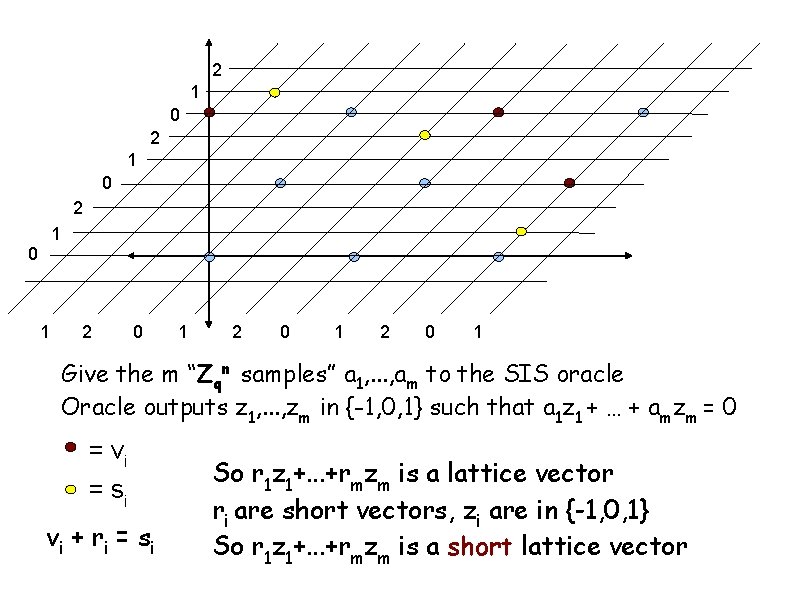
2 1 0 1 2 0 1 Give the m “Zqn samples” a 1, . . . , am to the SIS oracle Oracle outputs z 1, . . . , zm in {-1, 0, 1} such that a 1 z 1 + … + amzm = 0 = vi = si vi + r i = s i So r 1 z 1+. . . +rmzm is a lattice vector ri are short vectors, zi are in {-1, 0, 1} So r 1 z 1+. . . +rmzm is a short lattice vector
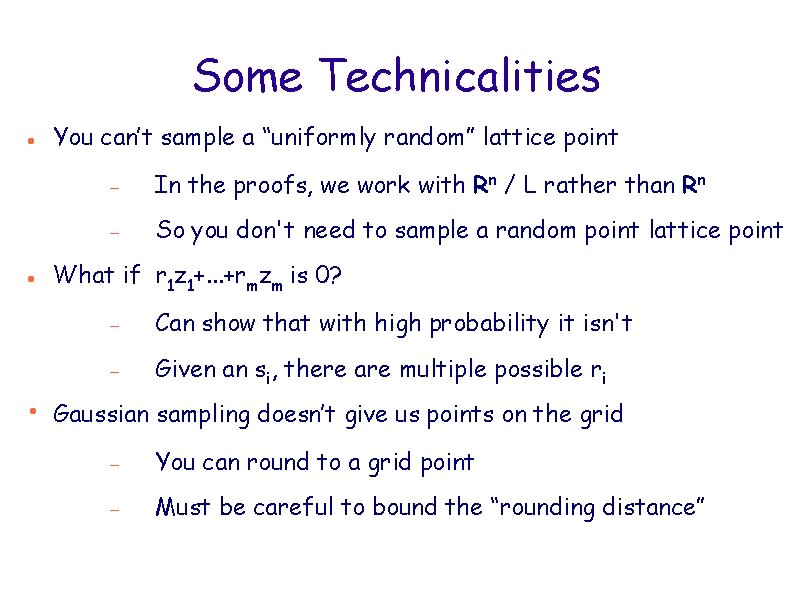
Some Technicalities You can’t sample a “uniformly random” lattice point In the proofs, we work with Rn / L rather than Rn So you don't need to sample a random point lattice point What if r 1 z 1+. . . +rmzm is 0? Can show that with high probability it isn't Given an si, there are multiple possible ri • Gaussian sampling doesn’t give us points on the grid You can round to a grid point Must be careful to bound the “rounding distance”
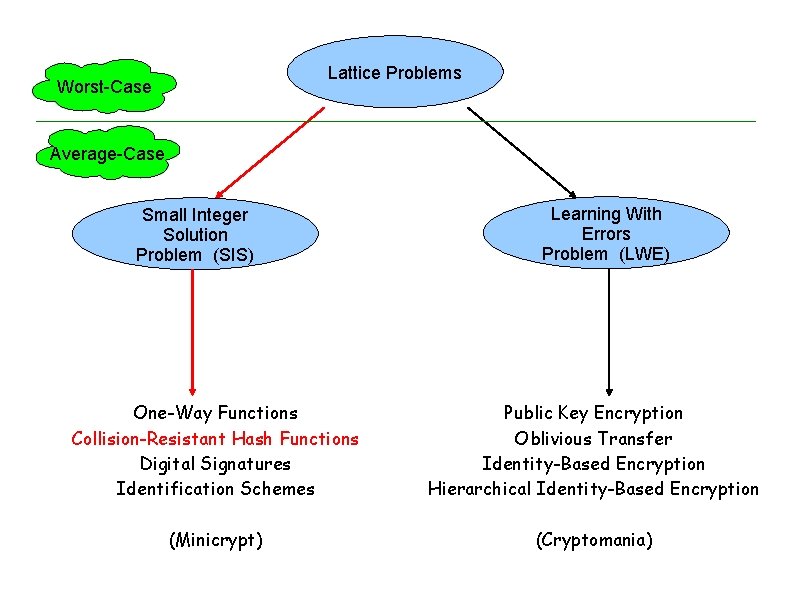
Lattice Problems Worst-Case Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)
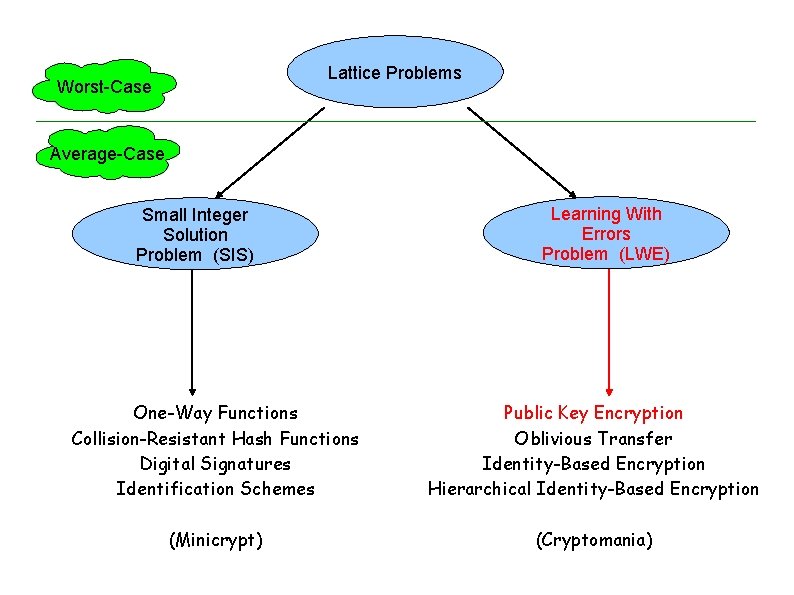
Lattice Problems Worst-Case Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)

Learning With Errors Problem Distinguish between these two distributions: Oracle 1 a 1, b 1=<a 1, s>+e 1 a 2, b 2=<a 2, s>+e 2 … s is chosen randomly in Zqn ai are chosen randomly from Zqn ei are “small” elements in Zq Oracle 2 a 1, b 1 a 2, b 2 … ai are chosen randomly from Zqn bi are chosen randomly from Zq
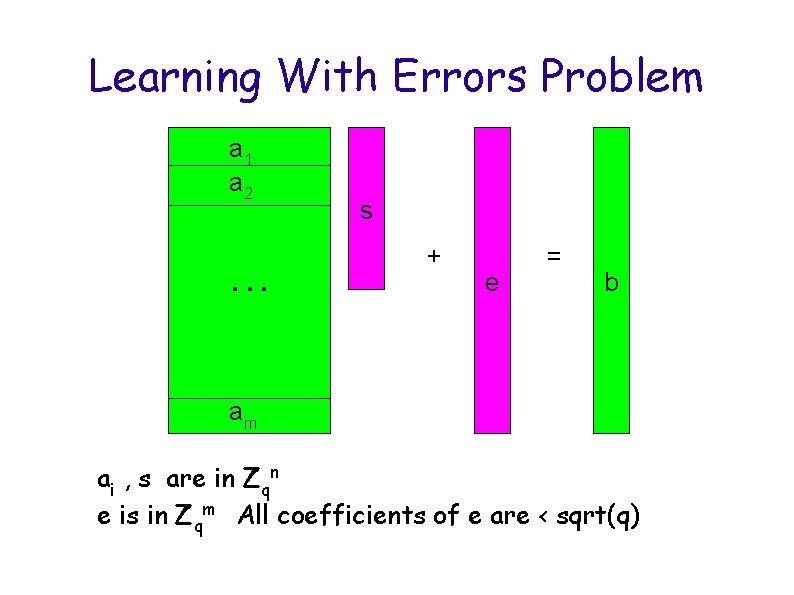
Learning With Errors Problem a 1 a 2. . . s + e = b am ai , s are in Zqn e is in Zqm All coefficients of e are < sqrt(q)
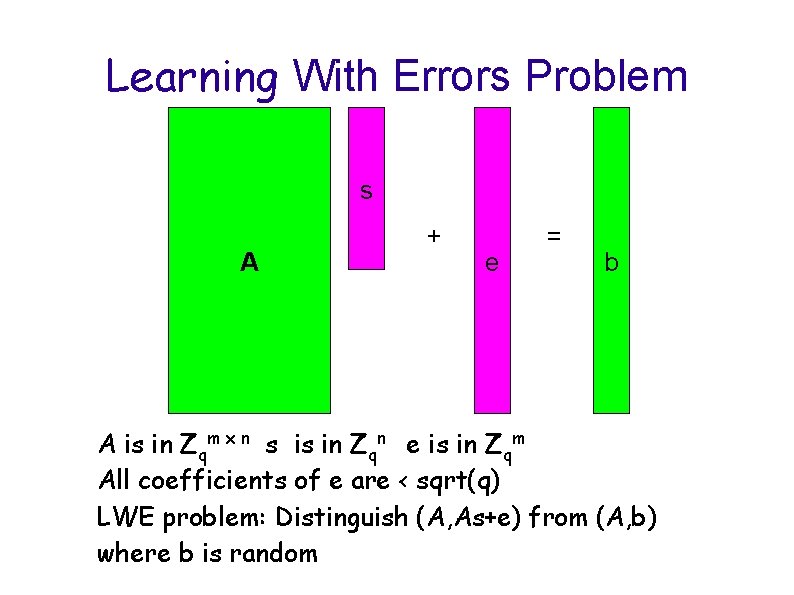
Learning With Errors Problem s A + e = b A is in Zqm x n s is in Zqn e is in Zqm All coefficients of e are < sqrt(q) LWE problem: Distinguish (A, As+e) from (A, b) where b is random
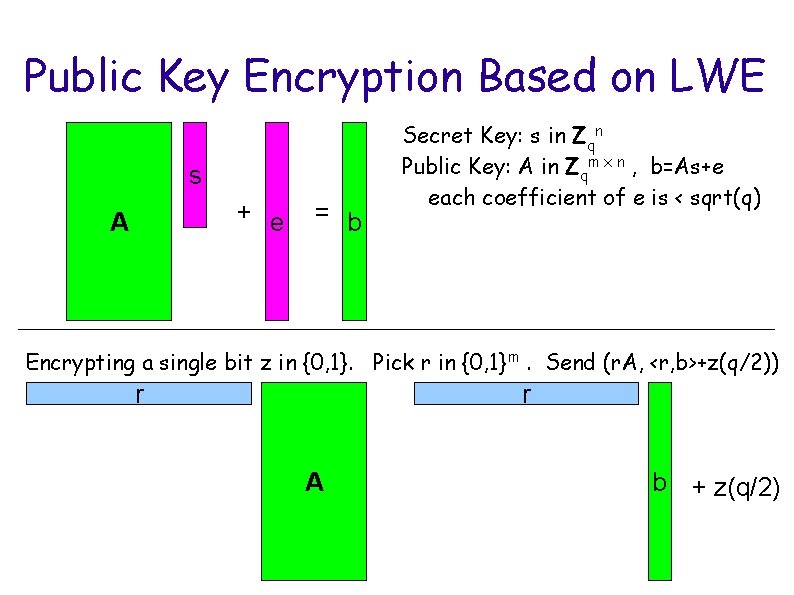
Public Key Encryption Based on LWE s + e A = b Secret Key: s in Zqn Public Key: A in Zqm x n , b=As+e each coefficient of e is < sqrt(q) Encrypting a single bit z in {0, 1}. Pick r in {0, 1}m. Send (r. A, <r, b>+z(q/2)) r r A b + z(q/2)
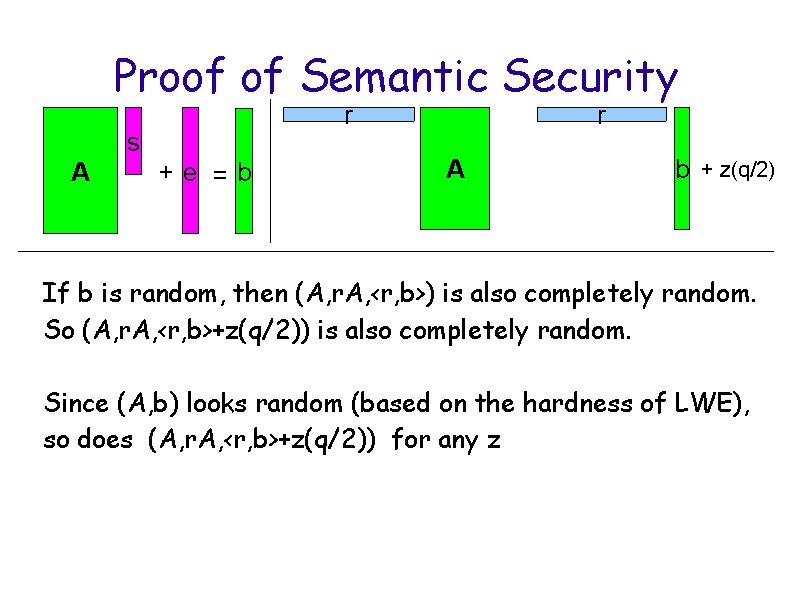
Proof of Semantic Security r s A +e =b r A b + z(q/2) If b is random, then (A, r. A, <r, b>) is also completely random. So (A, r. A, <r, b>+z(q/2)) is also completely random. Since (A, b) looks random (based on the hardness of LWE), so does (A, r. A, <r, b>+z(q/2)) for any z
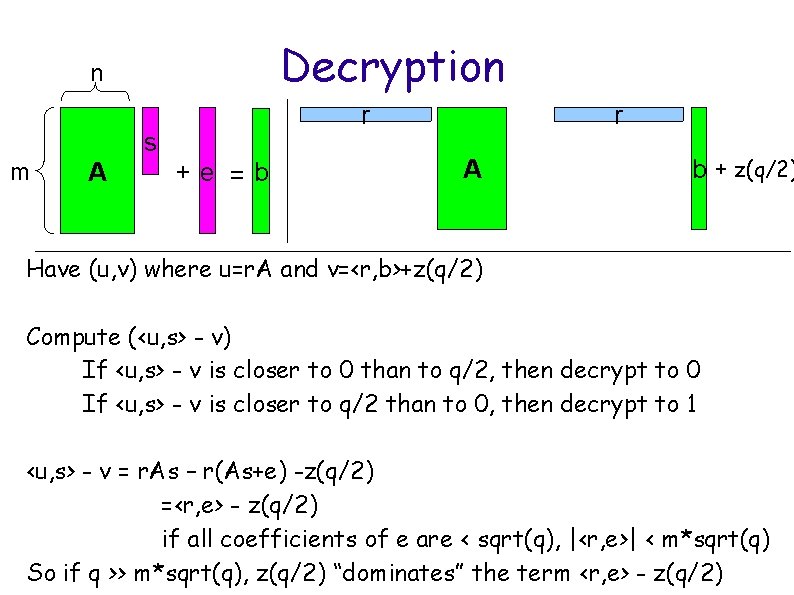
Decryption n r s m A +e =b r A b + z(q/2) Have (u, v) where u=r. A and v=<r, b>+z(q/2) Compute (<u, s> - v) If <u, s> - v is closer to 0 than to q/2, then decrypt to 0 If <u, s> - v is closer to q/2 than to 0, then decrypt to 1 <u, s> - v = r. As – r(As+e) -z(q/2) =<r, e> - z(q/2) if all coefficients of e are < sqrt(q), |<r, e>| < m*sqrt(q) So if q >> m*sqrt(q), z(q/2) “dominates” the term <r, e> - z(q/2)
Lattices in Practice Lattices have some great features Very strong security proofs The schemes are fairly simple Relatively efficient But there is a major drawback Schemes have very large keys
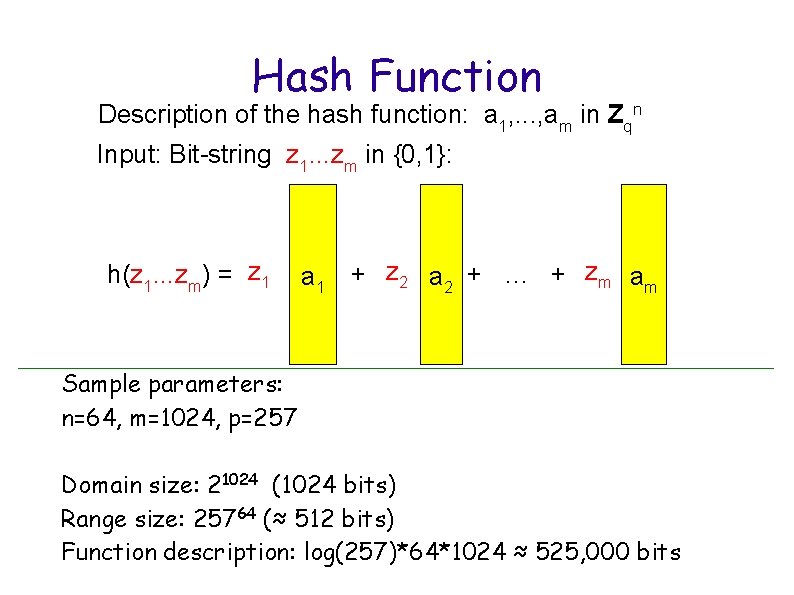
Hash Function Description of the hash function: a 1, . . . , am in Zqn Input: Bit-string z 1. . . zm in {0, 1}: h(z 1. . . zm) = z 1 a 1 + z 2 a 2 + … + zm am Sample parameters: n=64, m=1024, p=257 Domain size: 21024 (1024 bits) Range size: 25764 (≈ 512 bits) Function description: log(257)*64*1024 ≈ 525, 000 bits
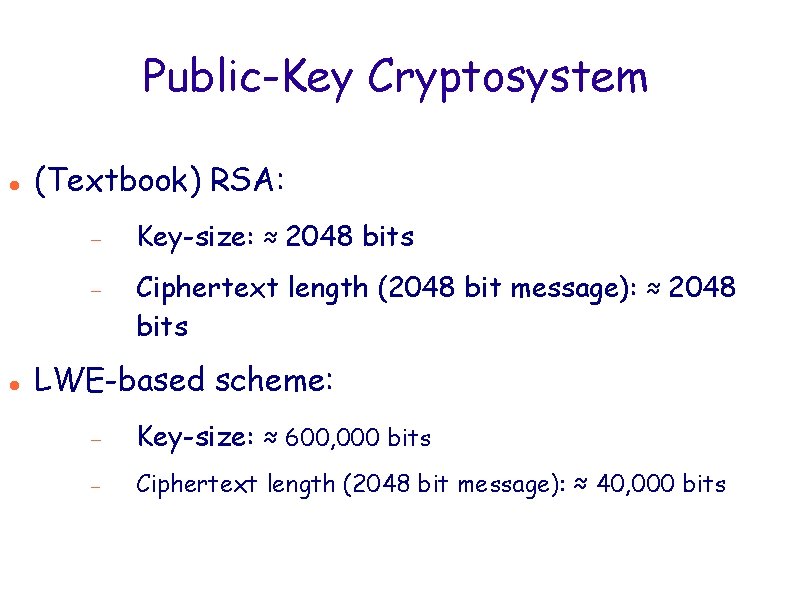
Public-Key Cryptosystem (Textbook) RSA: Key-size: ≈ 2048 bits Ciphertext length (2048 bit message): ≈ 2048 bits LWE-based scheme: Key-size: ≈ 600, 000 bits Ciphertext length (2048 bit message): ≈ 40, 000 bits
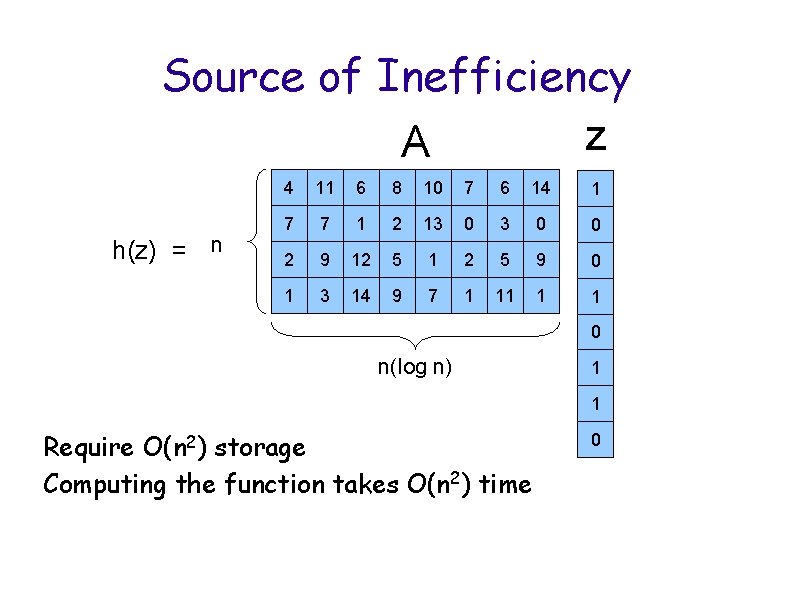
Source of Inefficiency z A h(z) = n 4 11 6 8 10 7 6 14 1 7 7 1 2 13 0 0 2 9 12 5 1 2 5 9 0 1 3 14 9 7 1 11 1 1 0 n(log n) 1 1 Require O(n 2) storage Computing the function takes O(n 2) time 0
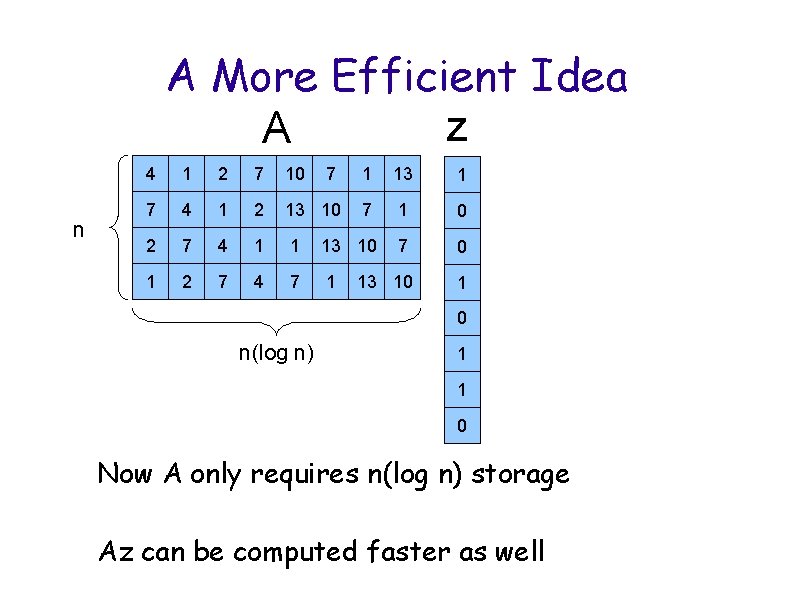
A More Efficient Idea z A n 4 1 2 7 10 7 1 13 1 7 4 1 2 13 10 7 1 0 2 7 4 1 1 13 10 7 0 1 2 7 4 7 1 13 10 1 0 n(log n) 1 1 0 Now A only requires n(log n) storage Az can be computed faster as well
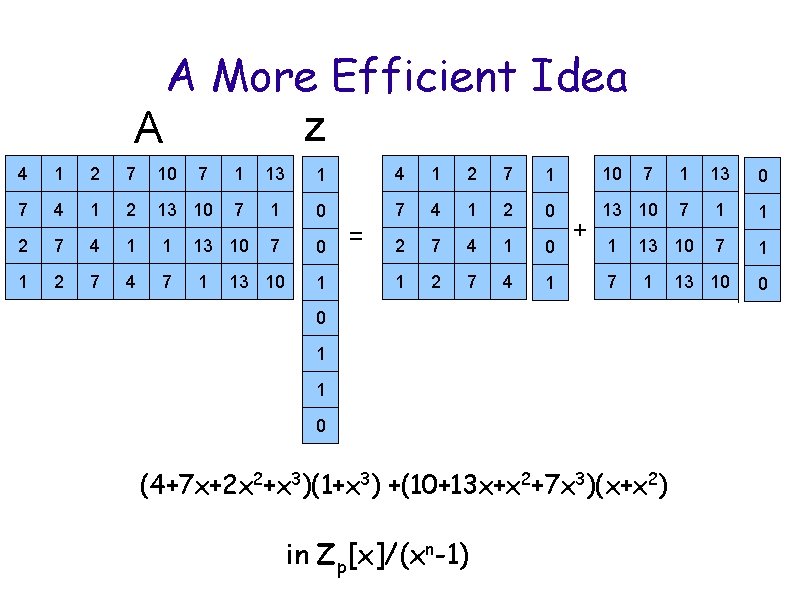
A More Efficient Idea z A 4 1 2 7 10 7 1 13 1 4 1 2 7 1 10 7 1 13 0 7 4 1 2 13 10 7 1 0 7 4 1 2 0 13 10 7 1 1 2 7 4 1 0 1 13 10 7 1 1 2 7 4 1 7 1 13 10 0 2 7 4 1 1 13 10 7 0 1 2 7 4 7 1 13 10 1 = + 0 1 1 0 (4+7 x+2 x 2+x 3)(1+x 3) +(10+13 x+x 2+7 x 3)(x+x 2) in Zp[x]/(xn-1)
![Interlude: n What is Zp[x]/(x -1)? Z = integers Zp=integers modulo p Zp[x] = Interlude: n What is Zp[x]/(x -1)? Z = integers Zp=integers modulo p Zp[x] =](http://slidetodoc.com/presentation_image_h2/c5a3e2d3f6e56821896a02d01a1c1f33/image-53.jpg)
Interlude: n What is Zp[x]/(x -1)? Z = integers Zp=integers modulo p Zp[x] = polynomials with coefficients in Zp Example if p=3: 1+x, 2+x 1001 Zp[x]/(xn-1)=polynomials of degree at most n -1, with coefficients in Zp Example if p=3 and n=4: 1+x, 2+x+x 2
![Operations in Zp[x]/(xn-1)? Addition: Addition of polynomials modulo p Example if p=3 and n=4: Operations in Zp[x]/(xn-1)? Addition: Addition of polynomials modulo p Example if p=3 and n=4:](http://slidetodoc.com/presentation_image_h2/c5a3e2d3f6e56821896a02d01a1c1f33/image-54.jpg)
Operations in Zp[x]/(xn-1)? Addition: Addition of polynomials modulo p Example if p=3 and n=4: (1+x 2) + (2+x 3)=2 x 2+x 3 Multiplication: Polynomial multiplication modulo p and xn-1 Example if p=3 and n=4: (1+x 2) * (2+x 3) = 2+3 x 2+x 3+x 4+x 5 = 2+3 x 2+x 3+1+x = x+x 3
![n [x]/(x -1) Multiplication in Zp as a Matrix/Vector Product Have polynomials f and n [x]/(x -1) Multiplication in Zp as a Matrix/Vector Product Have polynomials f and](http://slidetodoc.com/presentation_image_h2/c5a3e2d3f6e56821896a02d01a1c1f33/image-55.jpg)
n [x]/(x -1) Multiplication in Zp as a Matrix/Vector Product Have polynomials f and g=g 0+g 1 x+g 2 x 2+. . . gn-1 xn-1 g 0 f fx fx 2 fx 3 g 1 g 2 g 3 = g 0 f+g 1 fx+g 2 fx 2+g 3 fx 3 = f(g 0+g 1 x+g 2 x 2+g 3 x 3) = fg
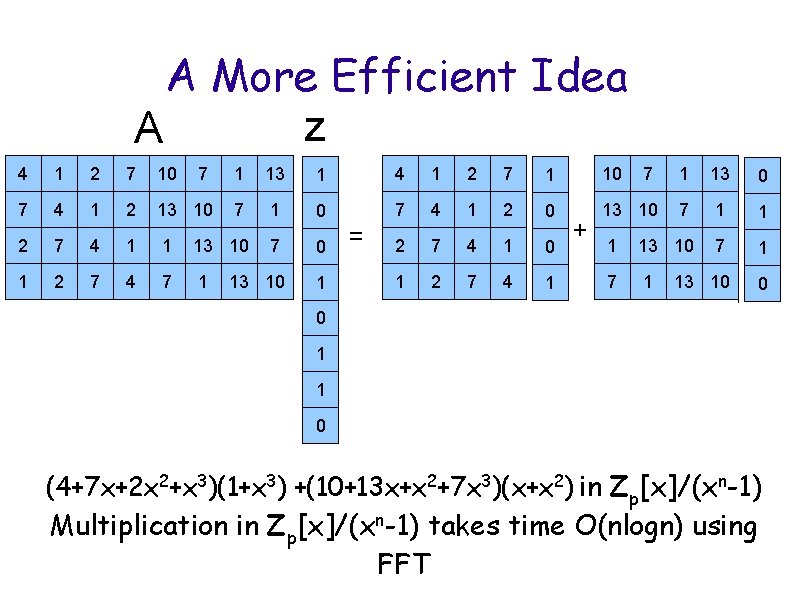
A More Efficient Idea z A 4 1 2 7 10 7 1 13 1 4 1 2 7 1 10 7 1 13 0 7 4 1 2 13 10 7 1 0 7 4 1 2 0 13 10 7 1 1 2 7 4 1 0 1 13 10 7 1 1 2 7 4 1 7 1 13 10 0 2 7 4 1 1 13 10 7 0 1 2 7 4 7 1 13 10 1 = + 0 1 1 0 (4+7 x+2 x 2+x 3)(1+x 3) +(10+13 x+x 2+7 x 3)(x+x 2) in Zp[x]/(xn-1) Multiplication in Zp[x]/(xn-1) takes time O(nlogn) using FFT
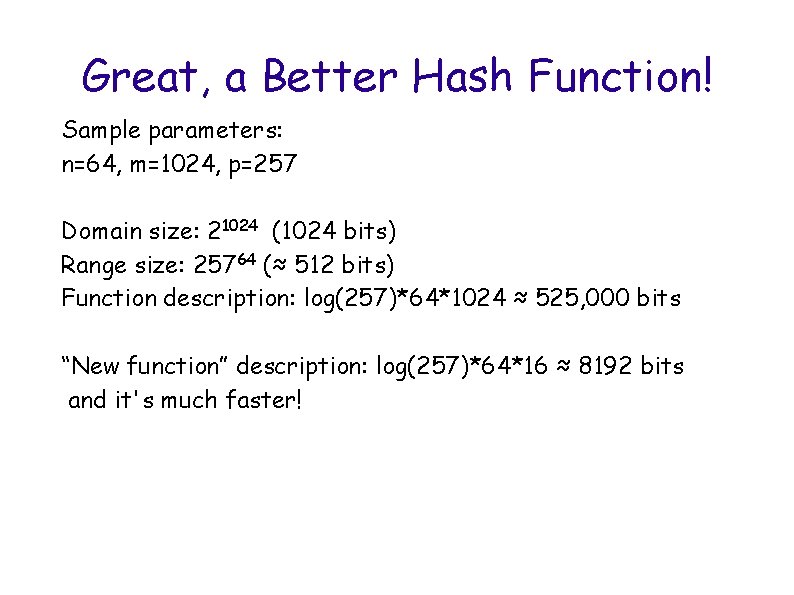
Great, a Better Hash Function! Sample parameters: n=64, m=1024, p=257 Domain size: 21024 (1024 bits) Range size: 25764 (≈ 512 bits) Function description: log(257)*64*1024 ≈ 525, 000 bits “New function” description: log(257)*64*16 ≈ 8192 bits and it's much faster!
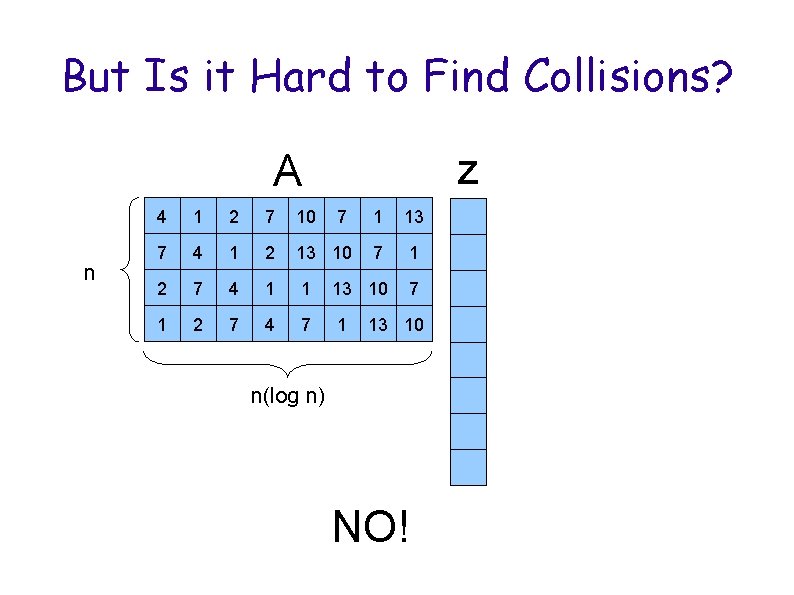
But Is it Hard to Find Collisions? z A n 4 1 2 7 10 7 1 13 7 4 1 2 13 10 7 1 2 7 4 1 1 13 10 7 1 2 7 4 7 1 13 10 n(log n) NO!
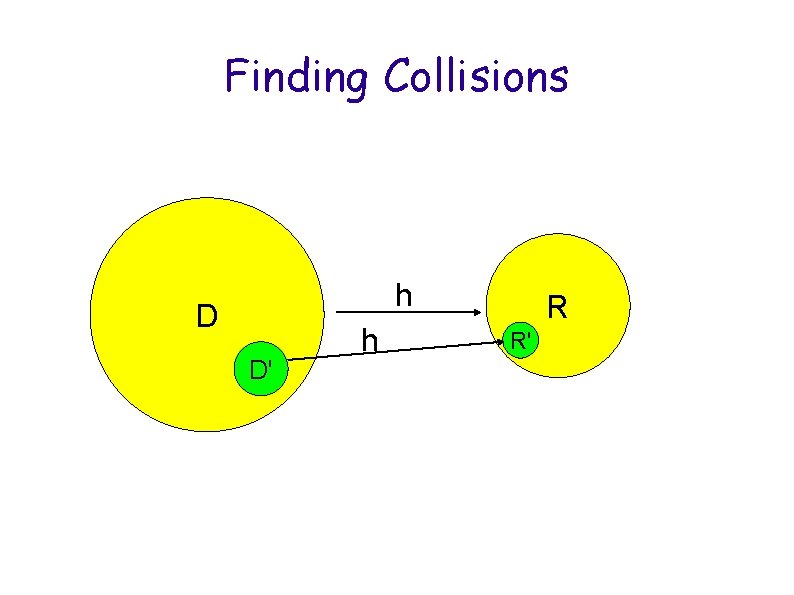
Finding Collisions h D D' h R R'
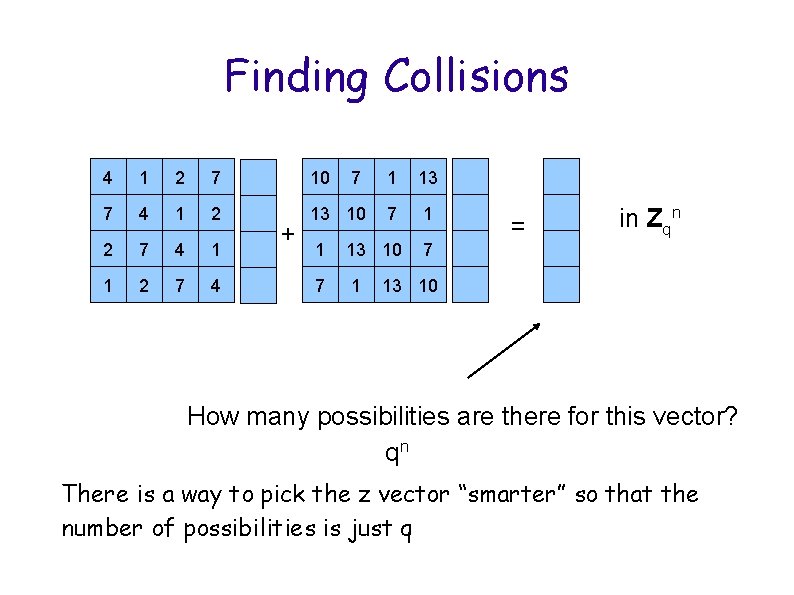
Finding Collisions 4 1 2 7 10 7 1 13 7 4 1 2 13 10 7 1 2 7 4 1 1 13 10 7 1 2 7 4 7 1 + = in Zqn 13 10 How many possibilities are there for this vector? qn There is a way to pick the z vector “smarter” so that the number of possibilities is just q
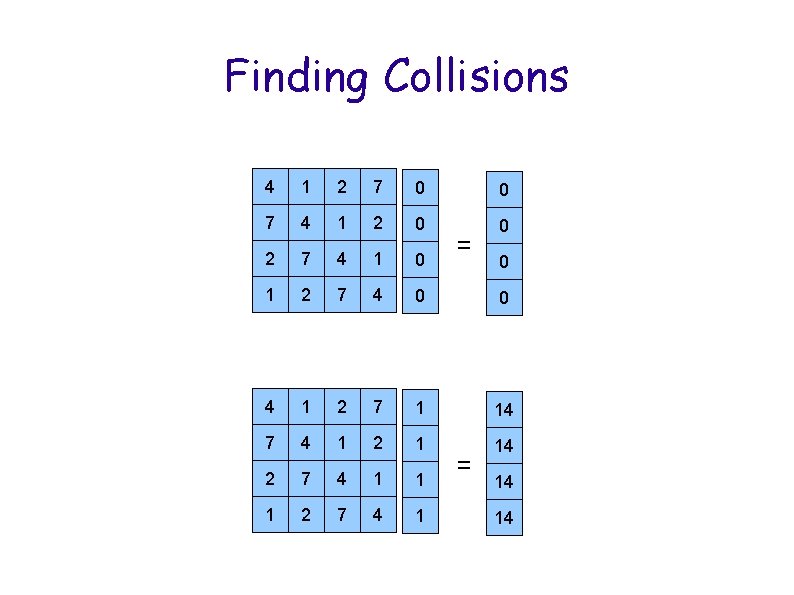
Finding Collisions 4 1 2 7 0 0 7 4 1 2 0 0 2 7 4 1 0 1 2 7 4 0 0 4 1 2 7 1 14 7 4 1 2 1 14 2 7 4 1 1 1 2 7 4 1 = = 0 14 14
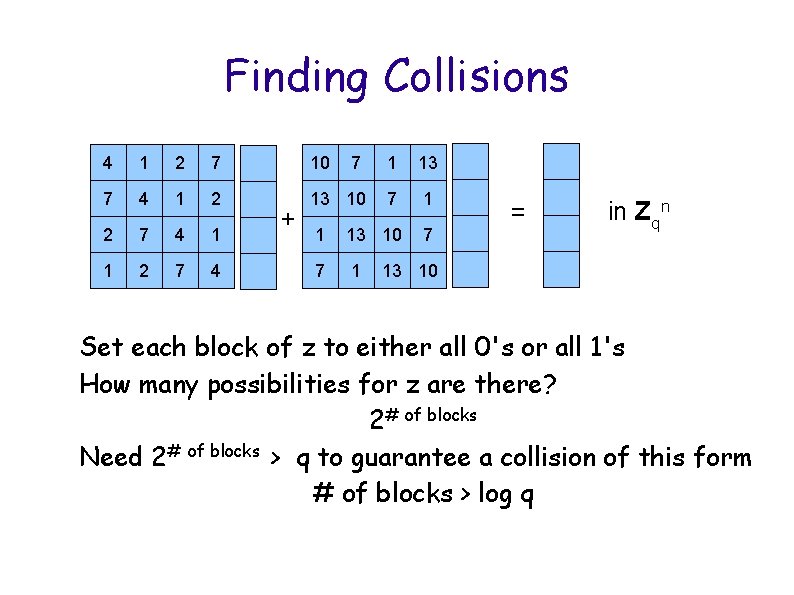
Finding Collisions 4 1 2 7 10 7 1 13 7 4 1 2 13 10 7 1 2 7 4 1 1 13 10 7 1 2 7 4 7 1 + = in Zqn 13 10 Set each block of z to either all 0's or all 1's How many possibilities for z are there? 2# of blocks Need 2# of blocks > q to guarantee a collision of this form # of blocks > log q
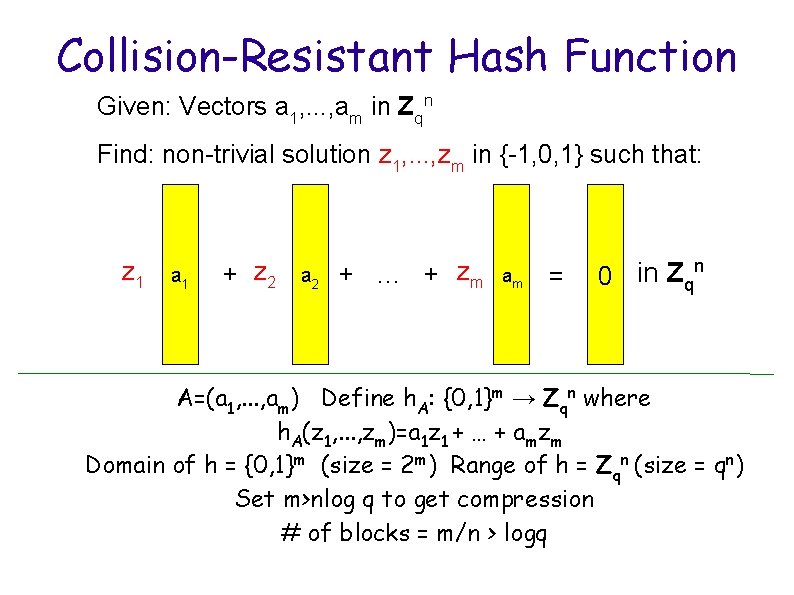
Collision-Resistant Hash Function Given: Vectors a 1, . . . , am in Zqn Find: non-trivial solution z 1, . . . , zm in {-1, 0, 1} such that: z 1 a 1 + z 2 a 2 + … + zm am = 0 in Zqn A=(a 1, . . . , am) Define h. A: {0, 1}m → Zqn where h. A(z 1, . . . , zm)=a 1 z 1 + … + amzm Domain of h = {0, 1}m (size = 2 m) Range of h = Zqn (size = qn) Set m>nlog q to get compression # of blocks = m/n > logq
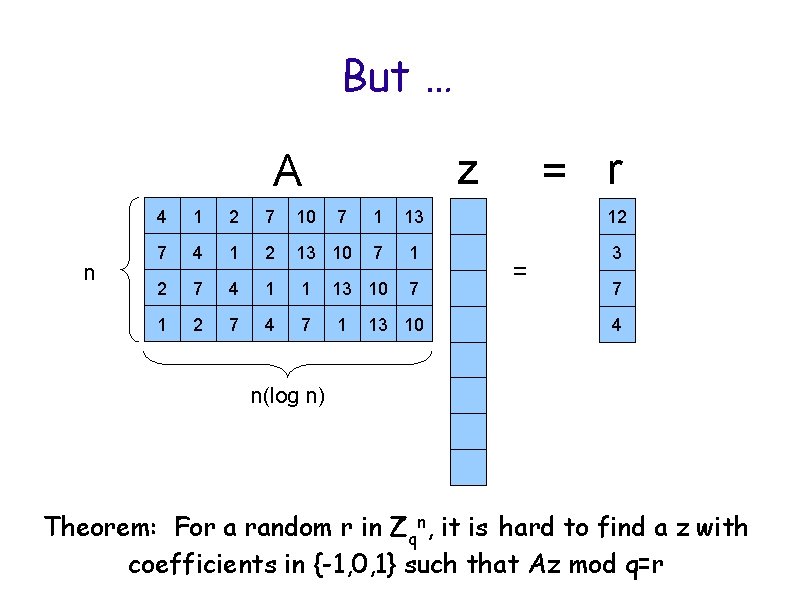
But … z A n = r 4 1 2 7 10 7 1 13 12 7 4 1 2 13 10 7 1 3 2 7 4 1 1 13 10 7 1 2 7 4 7 1 13 10 = 7 4 n(log n) Theorem: For a random r in Zqn, it is hard to find a z with coefficients in {-1, 0, 1} such that Az mod q=r
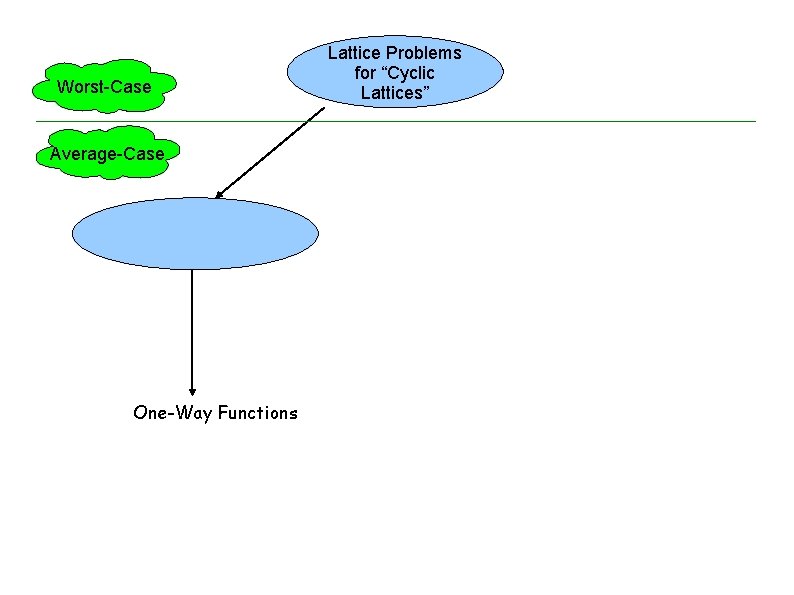
Worst-Case Average-Case One-Way Functions Lattice Problems for “Cyclic Lattices”
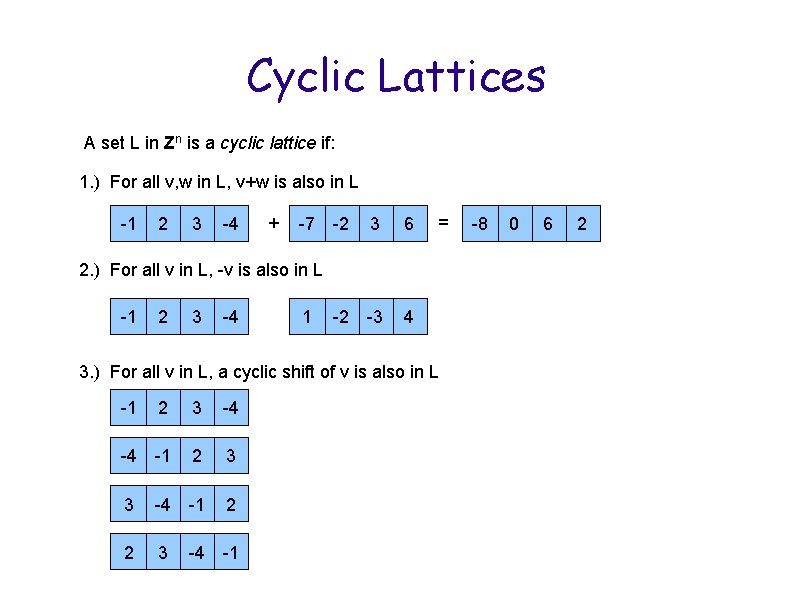
Cyclic Lattices A set L in Zn is a cyclic lattice if: 1. ) For all v, w in L, v+w is also in L -1 2 3 -4 + -7 -2 3 6 -2 -3 4 = 2. ) For all v in L, -v is also in L -1 2 3 -4 1 3. ) For all v in L, a cyclic shift of v is also in L -1 2 3 -4 -4 -1 2 3 -1 3 -4 2 -1 2 -4 3 -1 -4 2 3 -8 0 6 2
![Cyclic Lattices=Ideals in Z[x]/(xn-1) A set L in Zn is a cyclic lattice if: Cyclic Lattices=Ideals in Z[x]/(xn-1) A set L in Zn is a cyclic lattice if:](http://slidetodoc.com/presentation_image_h2/c5a3e2d3f6e56821896a02d01a1c1f33/image-67.jpg)
Cyclic Lattices=Ideals in Z[x]/(xn-1) A set L in Zn is a cyclic lattice if: 1. ) For all v, w in L, v+w is also in L -1 2 3 -4 + -7 -2 3 6 -2 -3 4 = 2. ) For all v in L, -v is also in L -1 2 3 -4 1 3. ) For all v in L, a cyclic shift of v is also in L -1 2 3 -4 -4 -1 2 3 -1 3 -4 2 -1 2 -4 3 -1 -4 2 3 -8 0 6 2
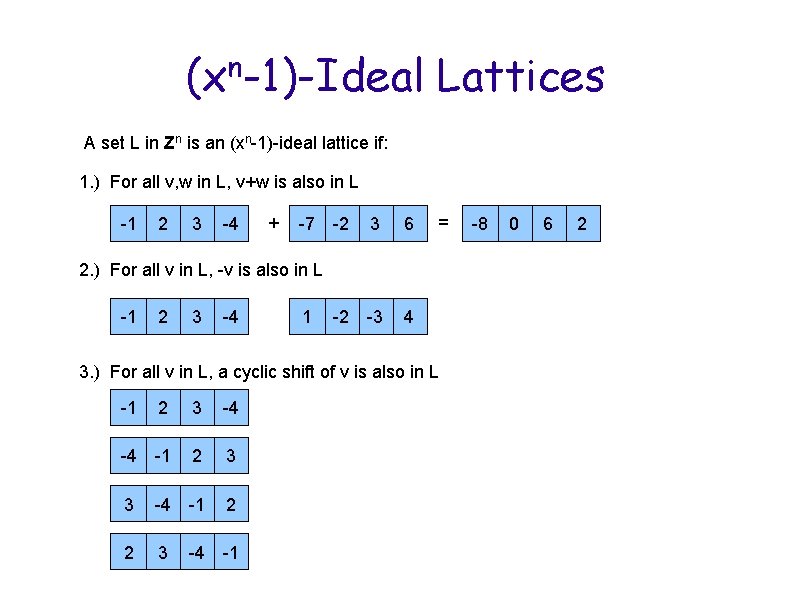
(xn-1)-Ideal Lattices A set L in Zn is an (xn-1)-ideal lattice if: 1. ) For all v, w in L, v+w is also in L -1 2 3 -4 + -7 -2 3 6 -2 -3 4 = 2. ) For all v in L, -v is also in L -1 2 3 -4 1 3. ) For all v in L, a cyclic shift of v is also in L -1 2 3 -4 -4 -1 2 3 -1 3 -4 2 -1 2 -4 3 -1 -4 2 3 -8 0 6 2
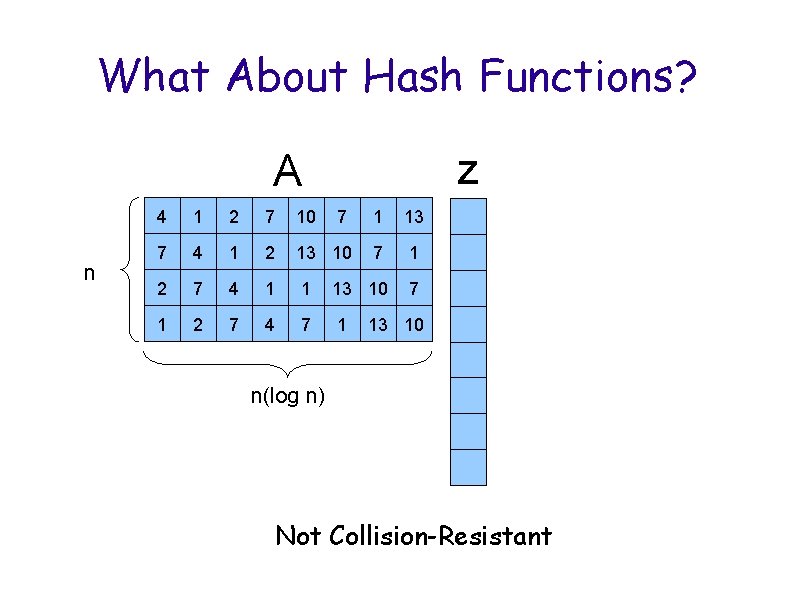
What About Hash Functions? z A n 4 1 2 7 10 7 1 13 7 4 1 2 13 10 7 1 2 7 4 1 1 13 10 7 1 2 7 4 7 1 13 10 n(log n) Not Collision-Resistant
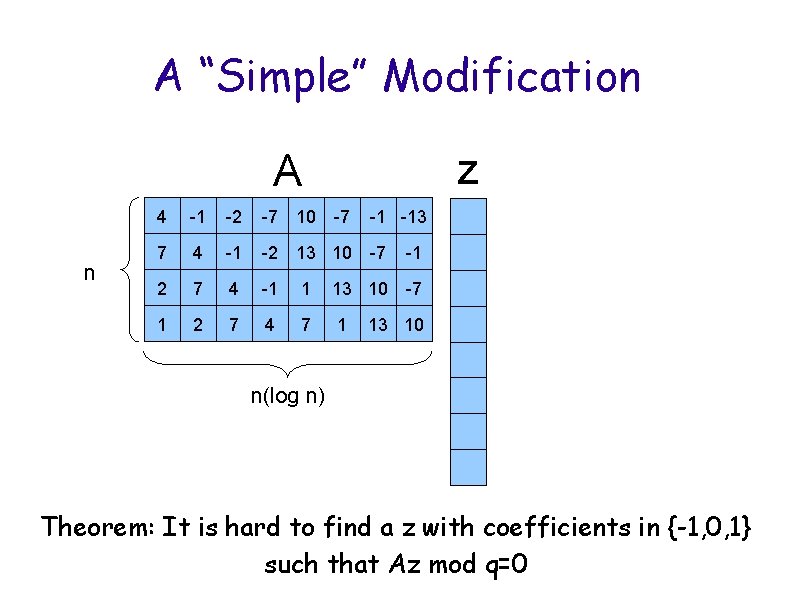
A “Simple” Modification z A n 4 -1 -2 -7 10 -7 -1 -13 7 4 -1 -2 13 10 -7 2 7 4 -1 1 13 10 -7 1 2 7 4 7 1 -1 13 10 n(log n) Theorem: It is hard to find a z with coefficients in {-1, 0, 1} such that Az mod q=0
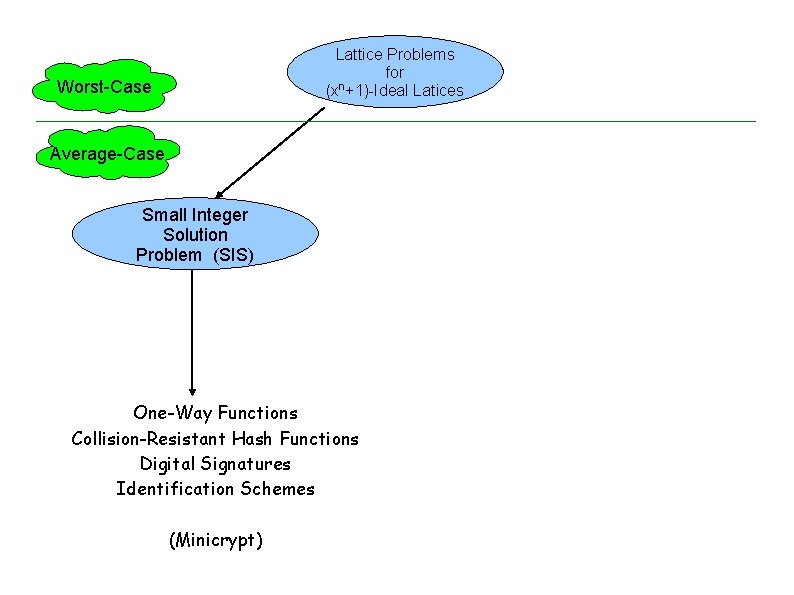
Lattice Problems for n (x +1)-Ideal Latices Worst-Case Average-Case Small Integer Solution Problem (SIS) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes (Minicrypt)
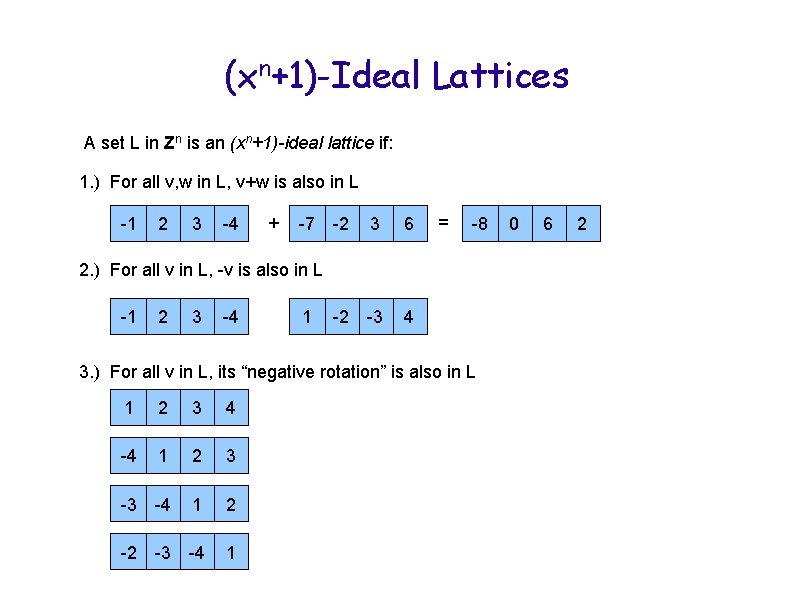
(xn+1)-Ideal Lattices A set L in Zn is an (xn+1)-ideal lattice if: 1. ) For all v, w in L, v+w is also in L -1 2 3 -4 + -7 -2 3 6 -2 -3 4 = -8 2. ) For all v in L, -v is also in L -1 2 3 -4 1 3. ) For all v in L, its “negative rotation” is also in L -1 1 2 3 -4 4 -4 1 2 3 -1 -4 -3 2 3 1 -4 2 -1 -3 -2 2 -4 3 -4 1 0 6 2
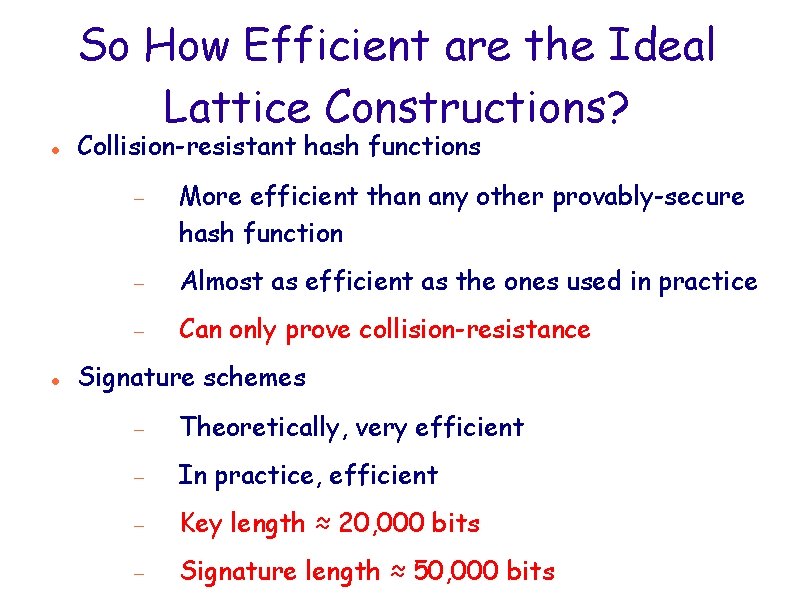
So How Efficient are the Ideal Lattice Constructions? Collision-resistant hash functions More efficient than any other provably-secure hash function Almost as efficient as the ones used in practice Can only prove collision-resistance Signature schemes Theoretically, very efficient In practice, efficient Key length ≈ 20, 000 bits Signature length ≈ 50, 000 bits
Future Directions Build more primitives (for ideas, go to http: //cseweb. ucsd. edu/users/mihir/crypto-topic-generator. html) Build “theoretically efficient” primitives based on lattices
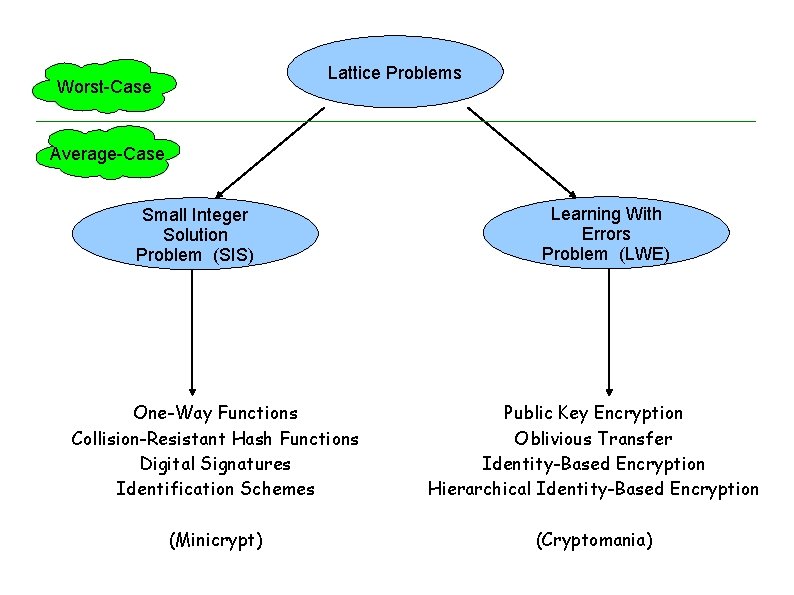
Lattice Problems Worst-Case Average-Case Small Integer Solution Problem (SIS) Learning With Errors Problem (LWE) One-Way Functions Collision-Resistant Hash Functions Digital Signatures Identification Schemes Public Key Encryption Oblivious Transfer Identity-Based Encryption Hierarchical Identity-Based Encryption (Minicrypt) (Cryptomania)
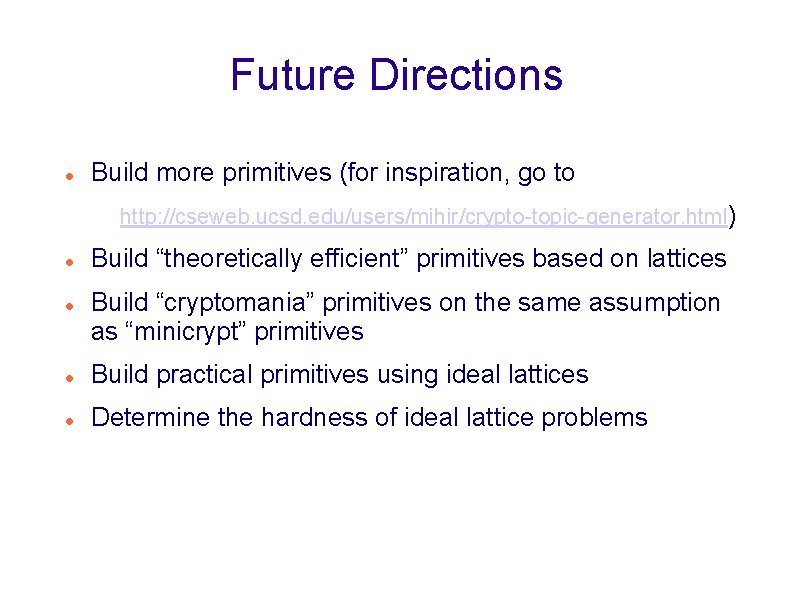
Future Directions Build more primitives (for inspiration, go to http: //cseweb. ucsd. edu/users/mihir/crypto-topic-generator. html) Build “theoretically efficient” primitives based on lattices Build “cryptomania” primitives on the same assumption as “minicrypt” primitives Build practical primitives using ideal lattices Determine the hardness of ideal lattice problems
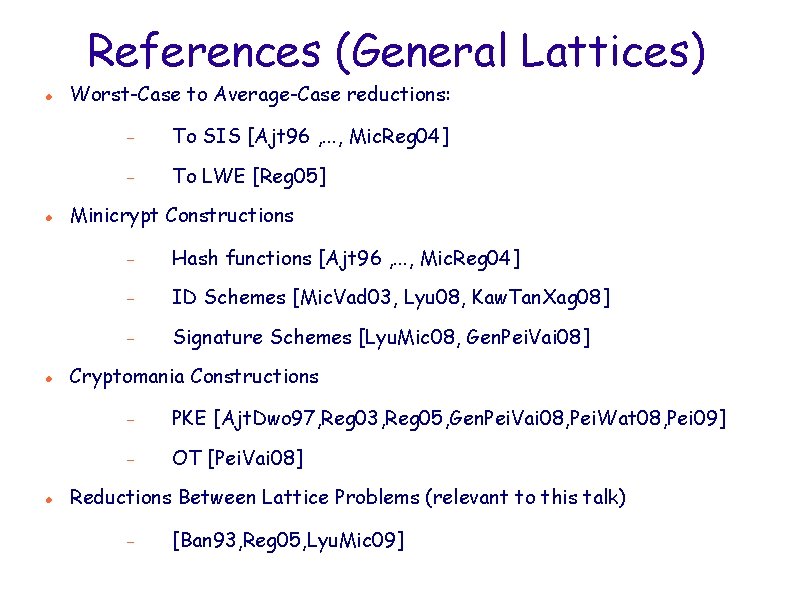
References (General Lattices) Worst-Case to Average-Case reductions: To SIS [Ajt 96 , . . . , Mic. Reg 04] To LWE [Reg 05] Minicrypt Constructions Hash functions [Ajt 96 , . . . , Mic. Reg 04] ID Schemes [Mic. Vad 03, Lyu 08, Kaw. Tan. Xag 08] Signature Schemes [Lyu. Mic 08, Gen. Pei. Vai 08] Cryptomania Constructions PKE [Ajt. Dwo 97, Reg 03, Reg 05, Gen. Pei. Vai 08, Pei. Wat 08, Pei 09] OT [Pei. Vai 08] Reductions Between Lattice Problems (relevant to this talk) [Ban 93, Reg 05, Lyu. Mic 09]
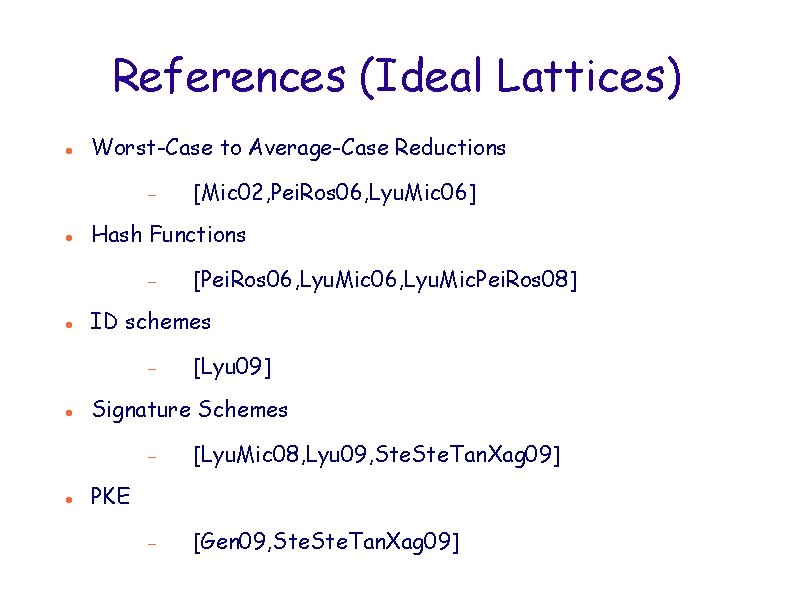
References (Ideal Lattices) Worst-Case to Average-Case Reductions Hash Functions [Pei. Ros 06, Lyu. Mic. Pei. Ros 08] ID schemes [Mic 02, Pei. Ros 06, Lyu. Mic 06] [Lyu 09] Signature Schemes [Lyu. Mic 08, Lyu 09, Ste. Tan. Xag 09] [Gen 09, Ste. Tan. Xag 09] PKE
- Slides: 78