Secure Collaborative Planning Forecasting and Replenishment Vinayak Deshpande
Secure Collaborative Planning, Forecasting, and Replenishment Vinayak Deshpande Krannert School of Management Purdue University Collaborators: Mikhail Atallah, Marina Blanton, Keith Frikken, Jiangtao Li Computer Sciences, Purdue University Leroy B. Schwarz School of Management, Purdue University Research funded by NSF ITR Grant 1
The Starting Point. . “Information Asymmetry” is one of the major sources of inefficiency in Managing Supply Chains ==> Wrong Investment in Capacity ==> Misallocation of Resources ==> “Bullwhip Effect” ==> Reduced Customer Service ==> Unnecessary Additional Costs 2
Supply Chain Management Trends • Collaboration between supply-chain partners to improve efficiencies • Information sharing for collaborative decision making • National program sponsored by VICS for establishing collaboration standards – called CPFR (Collaborative Planning, Forecasting and Replenishment) 3
. . but, there are Very Good Reasons for Keeping Asymmetric Information Asymmetric • Fear that Supply-Chain Partner will Take Advantage of Private Information • Fear that Private Information will Leak to a Competitor 4
As a result… • Reluctance to share private/proprietary info – Even when both sides would gain from sharing • Consequence: Information asymmetry – Many inefficiencies 5
Obvious Question… Is it possible to enjoy the benefits of Information-Sharing without Disclosing Private Information? 6
The Future • Online interactions that give the benefits of sharing, without its drawbacks – “As if” information sharing had taken place, yet without revealing one’s private/proprietary data • Counterpart’s information is often needed only as partial input for computing a desired output • Can two parties compute desired output without either learning the other’s input? 7
An Example: Vickrey Auction • Requires computation of the second highest bid value and identity of highest bidder from all submitted bids • Secure Multi-party Computation (SMC) protocols can – Compute the second highest bid without revealing the identity of the second highest bidder – Identify highest bidder without revealing his bid – Not reveal bids of any other bidders 8
Secure multiparty computation Alice x • • Bob y Alice has private data x, Bob has private data y, They want to jointly compute f(x, y), Only Alice (or Bob, or both) knows the result. 9
Secure multiparty computation (SMC) Literature • A decades old area – Yao, Goldreich, Micali, Wigderson, … (many others) – Elegant theory – General results • Circuit simulations, use oblivious transfer – General results typically impractical • Recently: Protocols for specific problems – More practical 10
Mechanism Design Literature • Studies how private information can be elicited from agents by providing incentives • Mechanism design problem simplified through the revelation principle (principal announces a menu constructed to induce truth telling) • No future or side consequences of participating in the mechanism and truthfully revealing private information • Assumes that the entity implementing the mechanism is trustworthy 11
Supply Chain Literature… • Has quantified the benefit of information sharing (e. g. Lee, So and Tang; Cachon and Fisher) • Has modeled Supply-Chain Collaboration, e. g. collaborative forecasting (Aviv 2001, 2003) • Key obstacles: companies unwilling to share sensitive information, fear of information leakage 12
We Propose to marry three distinct disciplines • Secure Multi-Party Computation from CS • Mechanism Design from Economics • Supply-Chain Management from OM 13
Our Goal. . . we are developing protocols to enable Supply-Chain Partners to Make Decisions that Cooperatively Achieve Desired System Goals without Revealing Private Information 14
A Supply Chain Problem. . • Collaborative Forecasting and Planning without revealing private forecast information 15
Industry Backdrop • Collaborative Planning, Forecasting, and Replenishment (CPFR), an initiative of the Voluntary Intra-Industry Collaboration Society (VICS) – buyer and supplier share inventory-status, forecast, and event-oriented information and collaboratively make replenishment decisions – pilot program between Wal-Mart and Warner-Lambert, called CFAR: (www. cpfr. org) • Challenges to CPFR – fear that competitively-sensitive “private information” will be compromised – Necessary to protect “sensitive” forecast information such as sales promotions from “leaking” 16
Business Scenario • A supply-chain with two players, a supplier selling to a retailer. • The retailer and the supplier receive independent “signals” about future market demand – e. g. , a retailer has private information about “promotions” that he may be planning to run in the future which can affect his forecast of demand; – the supplier can receive signals about overall “market trends” • Incorporating these “signals” can improve forecast accuracy • But. . “signal” information should be kept private 17
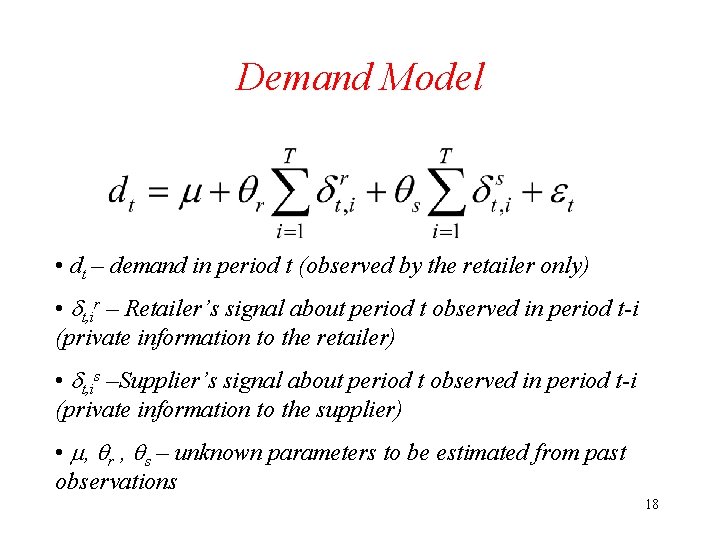
Demand Model • dt – demand in period t (observed by the retailer only) • t, ir – Retailer’s signal about period t observed in period t-i (private information to the retailer) • t, is –Supplier’s signal about period t observed in period t-i (private information to the supplier) • , r , s – unknown parameters to be estimated from past observations 18
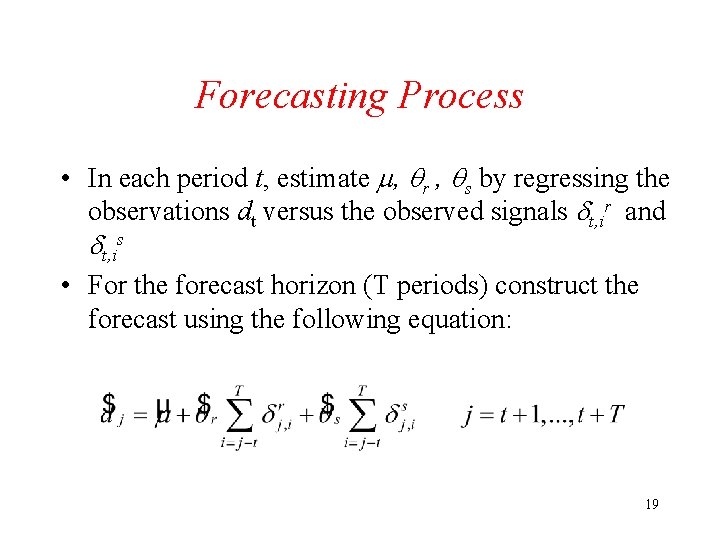
Forecasting Process • In each period t, estimate , r , s by regressing the observations dt versus the observed signals t, ir and t, is • For the forecast horizon (T periods) construct the forecast using the following equation: 19
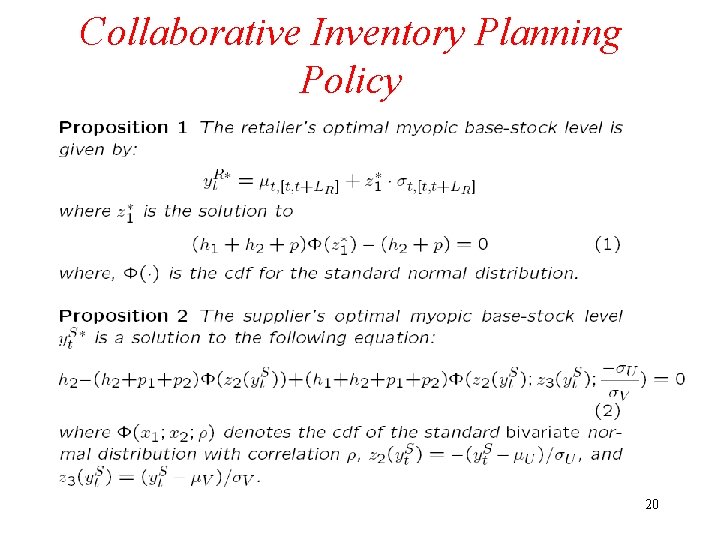
Collaborative Inventory Planning Policy 20
Secure Protocols Example: Average Salary 21
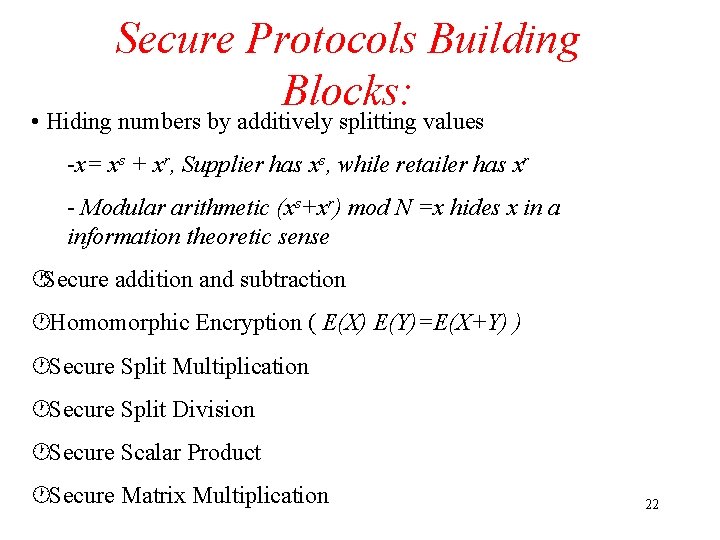
Secure Protocols Building Blocks: • Hiding numbers by additively splitting values -x= xs + xr, Supplier has xs, while retailer has xr - Modular arithmetic (xs+xr) mod N =x hides x in a information theoretic sense ·Secure addition and subtraction ·Homomorphic Encryption ( E(X) E(Y)=E(X+Y) ) ·Secure Split Multiplication ·Secure Split Division ·Secure Scalar Product ·Secure Matrix Multiplication 22
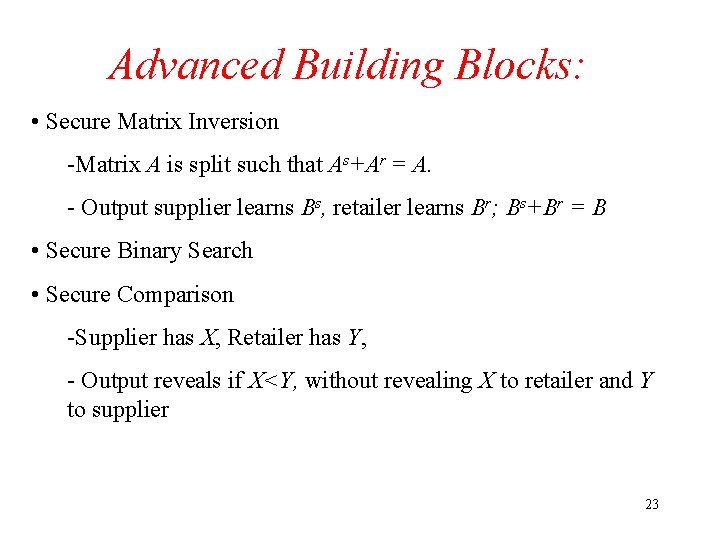
Advanced Building Blocks: • Secure Matrix Inversion -Matrix A is split such that As+Ar = A. - Output supplier learns Bs, retailer learns Br; Bs+Br = B • Secure Binary Search • Secure Comparison -Supplier has X, Retailer has Y, - Output reveals if X<Y, without revealing X to retailer and Y to supplier 23
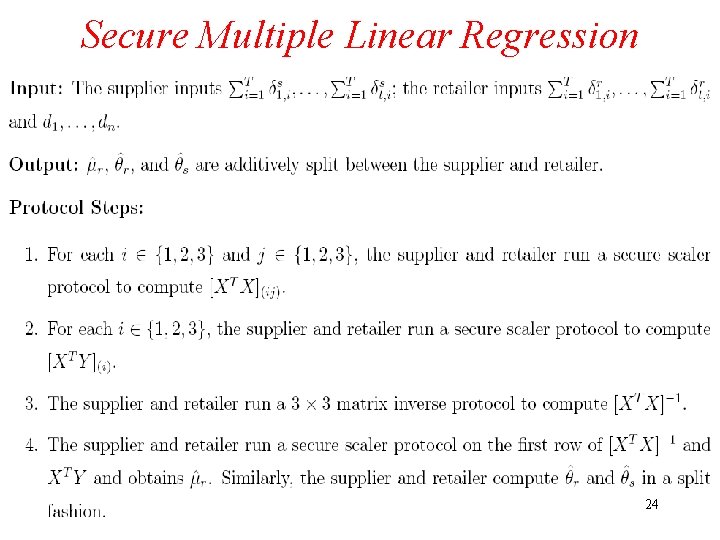
Secure Multiple Linear Regression Protocol 24
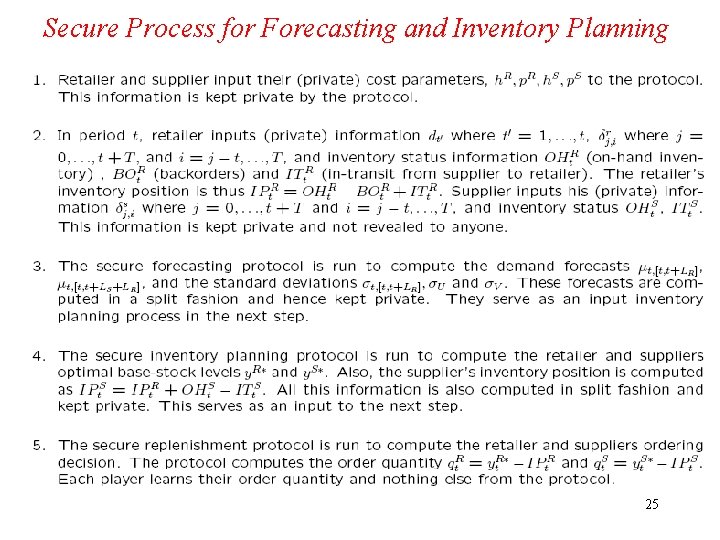
Secure Process for Forecasting and Inventory Planning 25
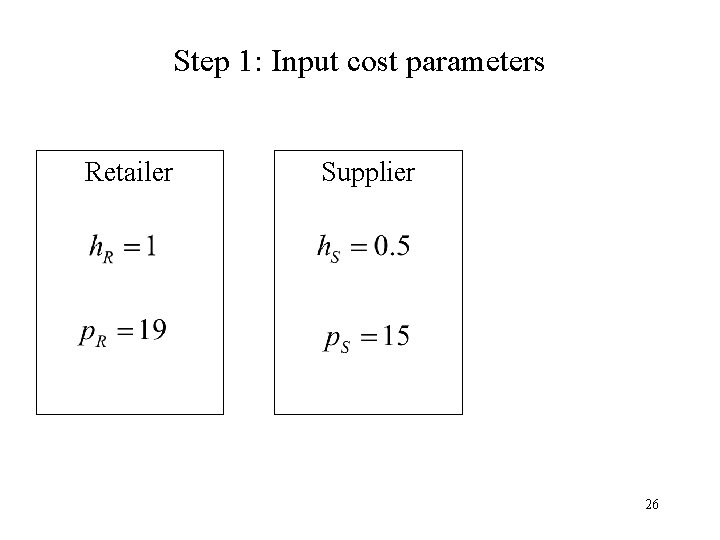
Step 1: Input cost parameters Retailer Supplier 26
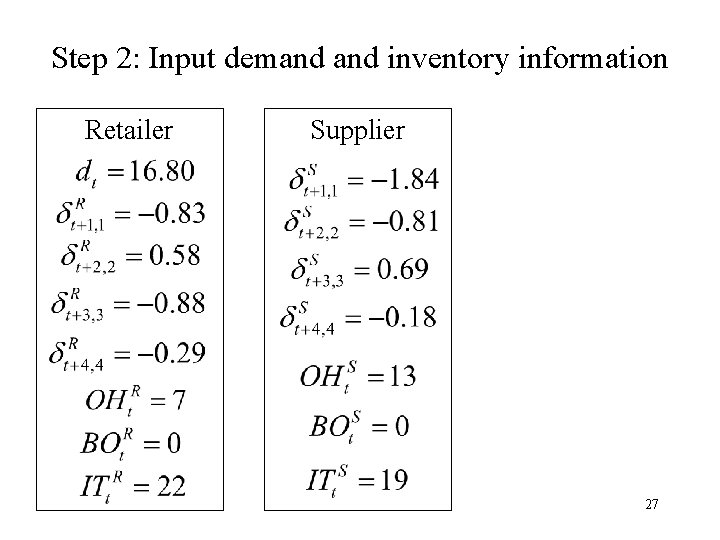
Step 2: Input demand inventory information Retailer Supplier 27
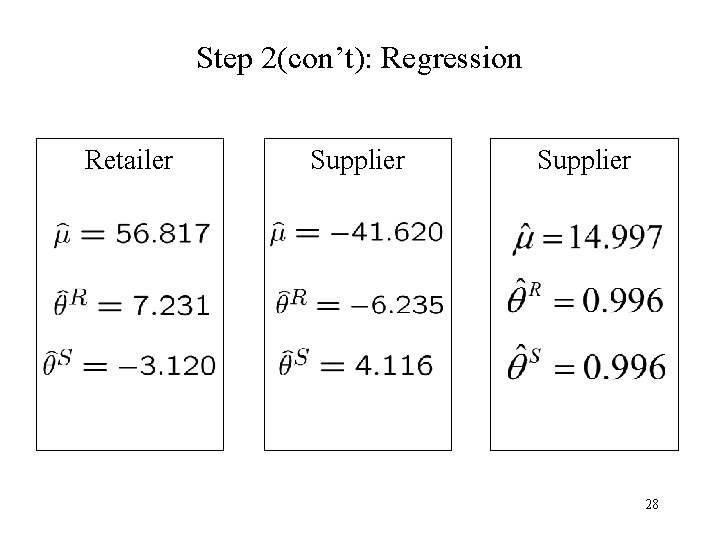
Step 2(con’t): Regression Retailer Supplier 28
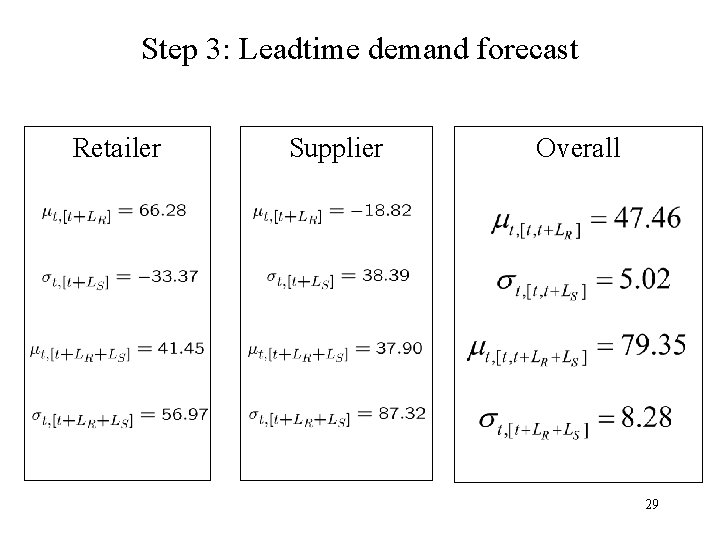
Step 3: Leadtime demand forecast Retailer Supplier Overall 29
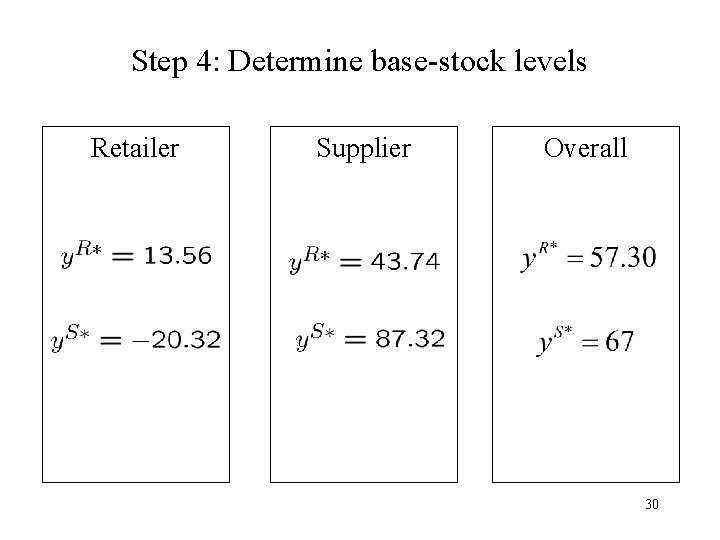
Step 4: Determine base-stock levels Retailer Supplier Overall 30
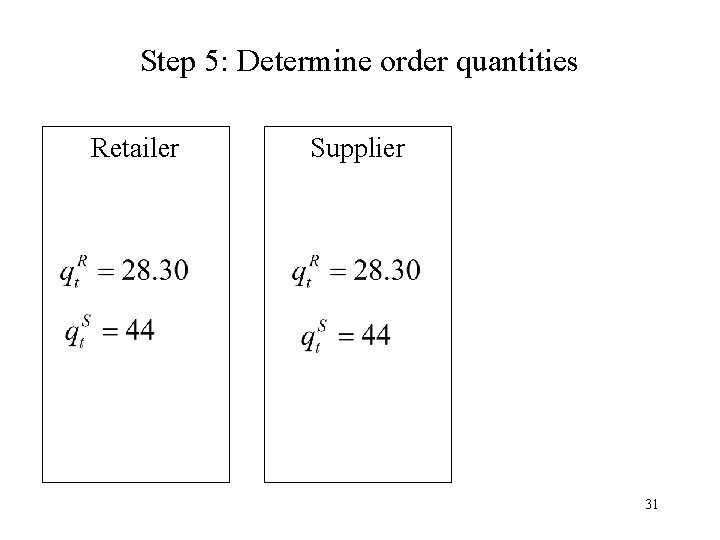
Step 5: Determine order quantities Retailer Supplier 31
Protocol Implementation Issues: Protocols are verifiable • The Logic of the Protocol is Auditable – Logic of Source Code Can be Audited • Outputs Can be Tested – Outputs Can be Verified Given Known Inputs 32
Protocol Implementation Issues: Other Advantages • Valuable even in Trusted e. g. (intracorporate) interactions – “Defense in depth” ! – Systems are hacked into, break-ins occur, viruses occur, spy-ware, bad insiders, etc – Liability Decreased • “Don’t send me your data even if you trust me” • Impact on Litigation and Insurance Rates 33
We Have Only Just Begun. . . • Tough Issues to Deal with: – SMC Complexities; e. g. , • How to Deal with Collusion • Computational Complexity (e. g. , simultaneity) – Supply-Chain Modeling Complexities; e. g. • Contracting/Incentive Issues – SSCC Complexities; e. g. , • Inverse Optimization • Bob’s Objective is f. B(x. A, x. B); Alice’s is f. A((x. A, x. B) 34
Future Work • Protocols for other supply-chain applications – Price-Masking – Bullwhip Scenarios – Capacity Allocation • Protocol implementation issues – Collusion by a subset of parties – Intrusion detection – Incentive issues and mechanism design 35
Questions? . . . 36
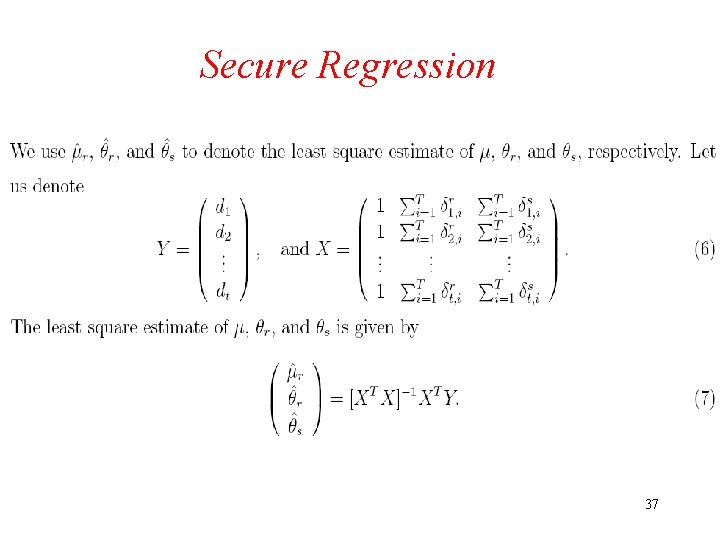
Secure Regression 37
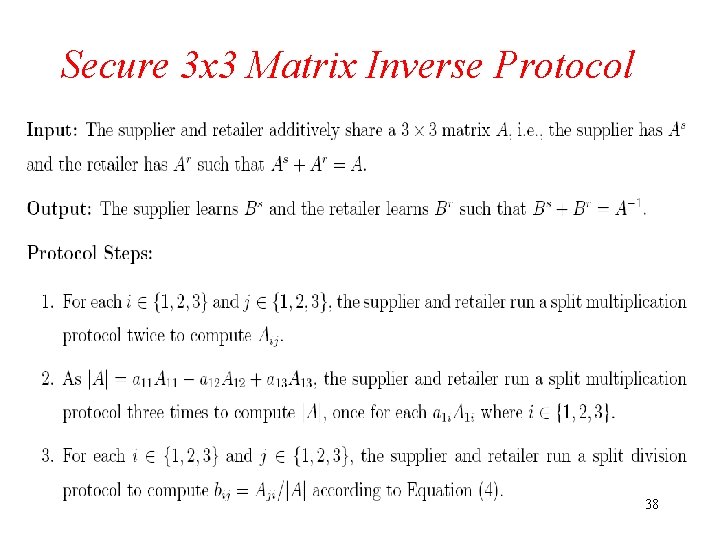
Secure 3 x 3 Matrix Inverse Protocol 38
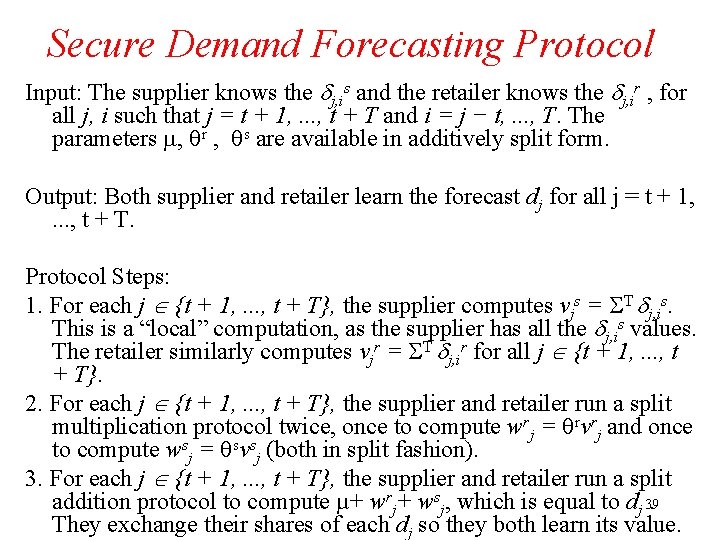
Secure Demand Forecasting Protocol Input: The supplier knows the j, is and the retailer knows the j, ir , for all j, i such that j = t + 1, . . . , t + T and i = j − t, . . . , T. The parameters , r , s are available in additively split form. Output: Both supplier and retailer learn the forecast dj for all j = t + 1, . . . , t + T. Protocol Steps: 1. For each j {t + 1, . . . , t + T}, the supplier computes vjs = T j, is. This is a “local” computation, as the supplier has all the j, is values. The retailer similarly computes vjr = T j, ir for all j {t + 1, . . . , t + T}. 2. For each j {t + 1, . . . , t + T}, the supplier and retailer run a split multiplication protocol twice, once to compute wrj = rvrj and once to compute wsj = svsj (both in split fashion). 3. For each j {t + 1, . . . , t + T}, the supplier and retailer run a split addition protocol to compute µ+ wrj+ wsj, which is equal to dj 39. They exchange their shares of each dj so they both learn its value.
- Slides: 39