SEC 555 Presentation based on SEC 555 SIEM
SEC 555 Presentation based on SEC 555: SIEM with Tactical Analytics Will that be one log or two? Logging before, during, and after an attack. Craig Bowser GSEC, GCED, GCDA @Reswob 10 cbowser@shadowtrackers. net
Who am I? • 20 years Information Security • 8+ years Sr Security Engineer w/ Arc. Sight, Splunk, ELK • Presenter • • Multiple SANS Summits from 2015 -2019 Derbycon 2016, BSides. Charm 2019, BSides. DC 2019 • Blog at www. shadowtrackers. net/blog • Mentor for SEC 555 • Christian, Father, Husband, Geek, Scout Leader who enjoys woodworking, sci-fi fantasy, home networking SEC 555 | SIEM with Tactical Analytics 2
A copy of this talk (as well as past presentations) will be available at www. shadowtrackers. net/presentations. html SEC 555 | SIEM with Tactical Analytics 3
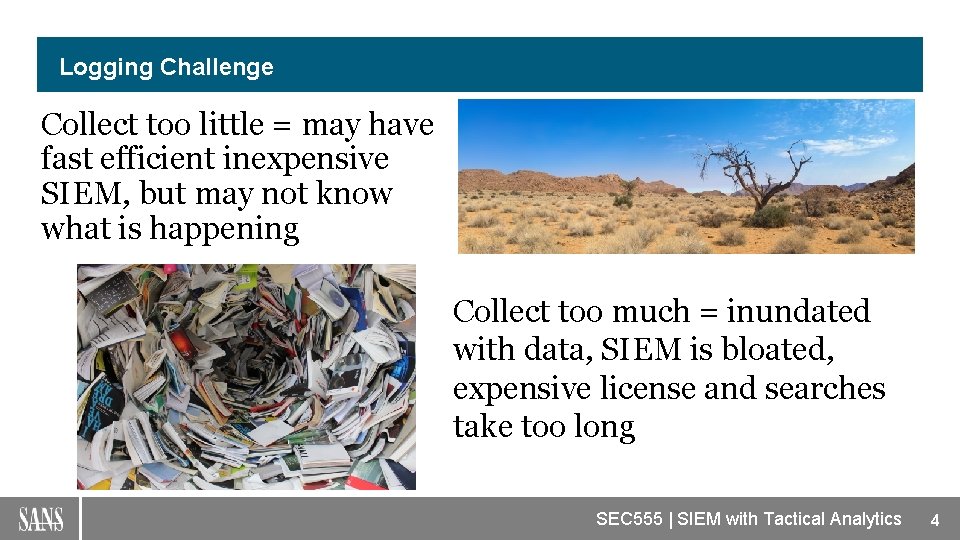
Logging Challenge Collect too little = may have fast efficient inexpensive SIEM, but may not know what is happening Collect too much = inundated with data, SIEM is bloated, expensive license and searches take too long SEC 555 | SIEM with Tactical Analytics 4
Logging Challenge Goal is to set a collection that works for your organization. This is not to say it’s perfect, just a collection where you have the most data coming in that allows you to know what is going on without overwhelming your SIEM or your license. SEC 555 | SIEM with Tactical Analytics 5
But what about when a you are under attack? What should you log? SEC 555 | SIEM with Tactical Analytics 6
Start from a Solid Baseline Well, first let’s cover some basics…. . Implement required or recommended GPO settings i. e. Microsoft, Center for Internet Security, Do. D STIG, Australian Cert, NSA Use one of those ‘as is’ or as starting point then customize to your environment. SEC 555 | SIEM with Tactical Analytics 7
Preparations Need to plan for and be aware of increased logging when under attack. • How close are you to max license/space? • How does your SIEM license handle overages? • How long will you have to maintain higher logging? • How many machines will have extra logging? • Should you increase the size of the log channel(s) on affected workstations/servers • Can you redirect all the logs of affected devices to another data lake, a second SIEM? SEC 555 | SIEM with Tactical Analytics 8
Acknowledgements NOTE: Full list and all references will be given at the end. Shout outs must go to at least: • Michael Gough (@hackerhurricaine) • https: //www. malwarearchaeology. com • Sean Metcalf (@Pyro. Tek 3) • www. adsecurity. org • Miriam Wiesner (@miriamxyra) • • https: //github. com/miriamxyra/Event. List https: //youtu. be/nk. MDsw 4 MA 48 SEC 555 | SIEM with Tactical Analytics 9

The following slides are going to cover audits settings that are not normally enabled due to log volume and/or not in normal ‘settings’ (security, system, application) Sysmon use is increasing, but still not a default installation (although it SHOULD be) Almost all the settings are tied to the MITRE ATT&CK matrix and specific techniques SEC 555 | SIEM with Tactical Analytics 10
Most logs can be enabled by GPO or use Powershell Often Analytic logs cannot be collected while Enabled unless special scripts used. MS Trace. FMT Fire. Eye Silk. ETW May require additional scripting SEC 555 | SIEM with Tactical Analytics 11
Covers many ATT&CK IDs Install Sysmon Suggested starting configurations Swift on Security: https: //github. com/Swift. On. Security/sysmon-config Olaf Hartong (logs tied to ATT&CK): https: //github. com/olafhartong/sysmon-modular Customize for your enterprise Applications and Services Logs-Microsoft-Windows-Sysmon/Operational SEC 555 | SIEM with Tactical Analytics 12

Enable Windows Defender Exploit Guard – Exploit Protection Provides same protection as EMET and more Three Steps to deploy in a Domain 1. Create a policy (can use defaults) a) https: //docs. microsoft. com/en-us/windows/security/threat-protection/microsoftdefender-atp/enable-exploit-protection 2. Export the XML configuration (save to domain wide accessible folder) a) https: //docs. microsoft. com/en-us/windows/security/threat-protection/microsoftdefender-atp/import-exploit-protection-emet-xml 3. Deploy via GPO a) https: //docs. microsoft. com/en-us/windows/security/threat-protection/microsoftdefender-atp/enable-exploit-protection#group-policy Applications and Services Logs-Microsoft-Windows-Security-Mitigations/Kernel Mode SEC 555 | SIEM with Tactical Analytics 13
Enable Powershell Logging Covers 4 ATT&CK IDs Powershell is one of the most used techniques for both attack and postexploitation i. e. Empire, Invoke-Mimikatz, Powersploit, Powercat Enable the following Powershell logging via GPO under: Administrative Templates → Windows Components → Windows Power. Shell Module Script blocking Use this to start Transaction – send these logs to a write-only share drive for collection/ searching later Applications and Services Logs-Microsoft-Windows-Power. Shell/Operational Multiple Event. IDs to monitor Applications and Services Logs-Microsoft-Windows-Win. RM/Operational SEC 555 | SIEM with Tactical Analytics 14
Covers many ATT&CK IDs Enable WMI logging Attackers can utilize WMI for multiple stages of an attack i. e. Lateral Movement, Enumeration, Establish Persistence, File Execution APT 29 used WMI to persist a backdoor and also store the Power. Shell backdoor code Monitor WMI Event. ID 5861 Applications and Services Logs-Microsoft-Windows-WMI-Activity/Operational Applications and Services Logs-Microsoft-Windows-Win. RM/Operational Applications and Services Logs-Microsoft-Windows-Distributed. COM SEC 555 | SIEM with Tactical Analytics 15

Covers many ATT&CK IDs Enable Host Firewalls Logging Watch for changes to firewall policy and/or disabling of firewall entirely – technique used by CARBANAK (aka ANUNAK) Links process to IP/port and adds redundancy to Sysmon event. ID 3 In case attackers disable/subvert sysmon Monitor Event. ID 5156 Enable firewall text log Provides more details about connections Log to write only share drive Security SEC 555 | SIEM with Tactical Analytics 16
Enable File/Folder Auditing Covers many ATT&CK IDs Attackers will enumerate files and folders looking for specific items (i. e. password. txt, intellectual property, personnel files) or general file types (i. e. ransomware looking to encrypt all pdf, docx, pptx, etc) Attackers also will use certain files/folders for persistence Monitor Event 4656, 4663, 4658 High value objects (You DO have a list right? ) Start up folders, system folders that shouldn’t change Security SEC 555 | SIEM with Tactical Analytics 17
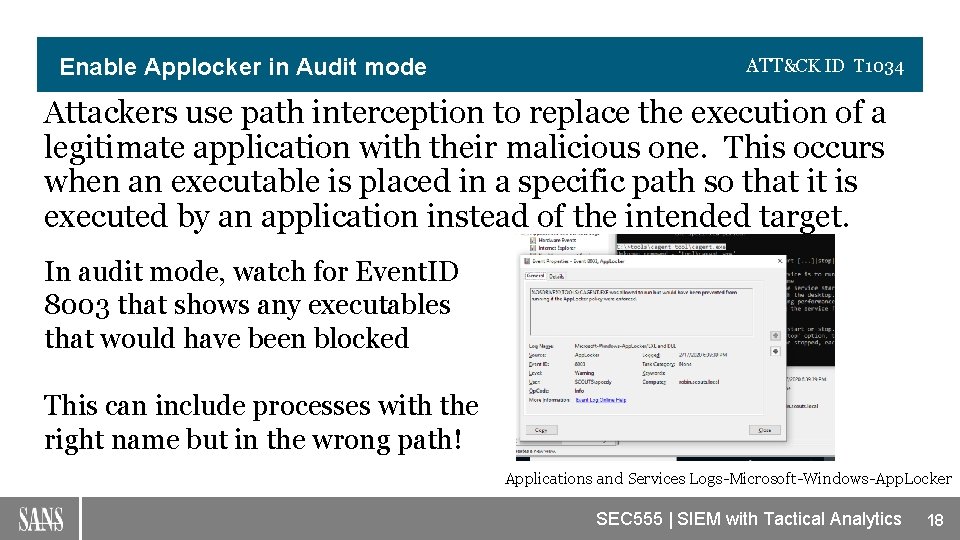
Enable Applocker in Audit mode ATT&CK ID T 1034 Attackers use path interception to replace the execution of a legitimate application with their malicious one. This occurs when an executable is placed in a specific path so that it is executed by an application instead of the intended target. In audit mode, watch for Event. ID 8003 that shows any executables that would have been blocked This can include processes with the right name but in the wrong path! Applications and Services Logs-Microsoft-Windows-App. Locker SEC 555 | SIEM with Tactical Analytics 18
Enable Auditing of Registry Keys Covers many ATT&CK IDs Attackers will use the registry for persistence and search the registry for credentials and other information regarding the environment Recent versions of Trickbot grab Pu. TTY creds from the registry for lateral movement Multiple keys to monitor for changes and unapproved programs gaining access – Event. ID 4657 https: //blog. trendmicro. com/trendlabs-security-intelligence/trickbot-adds-remote-application-credentialgrabbing-capabilities-to-its-repertoire/ Security SEC 555 | SIEM with Tactical Analytics 19
Enable Kerberos logging ATT&CK IDs T 1208, T 1110 Kerberoasting is when attackers acquire a valid Kerberos ticketgranting ticket (TGT) and request one or more Kerberos ticketgranting service (TGS) service tickets for the purpose of brute forcing the credentials Password spraying can be conducted against LDAP instead of SMB. Both of these attacks can be detected via auditing Kerberos activity Enable auditing of Audit Kerberos Service Ticket Operations (success) - Event. ID 4769 Audit Kerberos Authentication Service (success/failure) - Event. ID 4771 Security SEC 555 | SIEM with Tactical Analytics 20
Enable RDP logs ATT&CK ID T 1021 Attackers use RDP as another LOL method attackers for lateral movement Triton actors routinely used standard tools that would mimic legitimate administrator activities. This included heavy use of RDP and Ps. Exec/Win. RM Monitor Event. IDs 21, 23, 25, and 41 from Terminal. Services. Local. Session. Manager and 1149 and 261 from Terminal. Services. Remote. Connection. Manager Applications and Services Logs -Microsoft -Windows - Terminal. Services-Remote. Connection. Manager Applications and Services Logs - Microsoft - Windows - Terminal. Services-Local. Session. Manager SEC 555 | SIEM with Tactical Analytics 21
Pay attention to Windows Error Reporting events Covers 4 ATT&CK IDs Often when attackers attempt an exploit, it may not work 100% of the time. Crashes of applications can indicate potential failed exploitation attempts Especially of security tools! Watch crash reports in Application log Event. ID 1000 and 1001 Application SEC 555 | SIEM with Tactical Analytics 22

Enable detailed detection of USB Covers 3 ATT&CK IDs As the capabilities of USB devices continues to increase, a single device can perform any number of attacks within seconds of being inserted into a machine. i. e. Credential Stealing, Persistence, Exfiltration, Reconnaissance, all of the above and more Look for Event. ID 2010 in the Operational log to tell you what is being inserted or has been inserted into your environment. This can tell you if malware is being introduced or data is Microsoft-Windows-Driver. Frameworks-User. Mode/Operational Microsoft-Windows-Partition/Diagnostic being exfiltrated. SEC 555 | SIEM with Tactical Analytics 23
Enable Scheduled Tasks logging ATT&CK ID T 1209, All Persistence Attackers use Scheduled Tasks for a variety of tasks during an attack. These include: Persistence Conduct remote execution as part of Lateral Movement Gain SYSTEM privileges Run a process under the context of a specified account. Monitor for Event. IDs 4698 -4702 and 100, 102, 129. Use long tail analysis to find the tasks that are only executing on 1 or 2 devices in your environment and validate. Security Microsoft-Windows-Task. Scheduler/Operational SEC 555 | SIEM with Tactical Analytics 24
Enable Auditing of Connections to network shares Covers 5 ATT&CK IDs Attackers may use SMB to make RPCs, transfer files, conduct remote execution. Monitoring of suspicious or unusual use of network admin shares can discover this lateral movements Examples: Admin$, IPC$, PRINT$ Look for Event. ID 5140 and 5145 in the Security log. MS has excellent suggestions for filtering these events: https: //docs. microsoft. com/en-us/windows/security/threat-protection/auditing/event-5140 Security SEC 555 | SIEM with Tactical Analytics 25
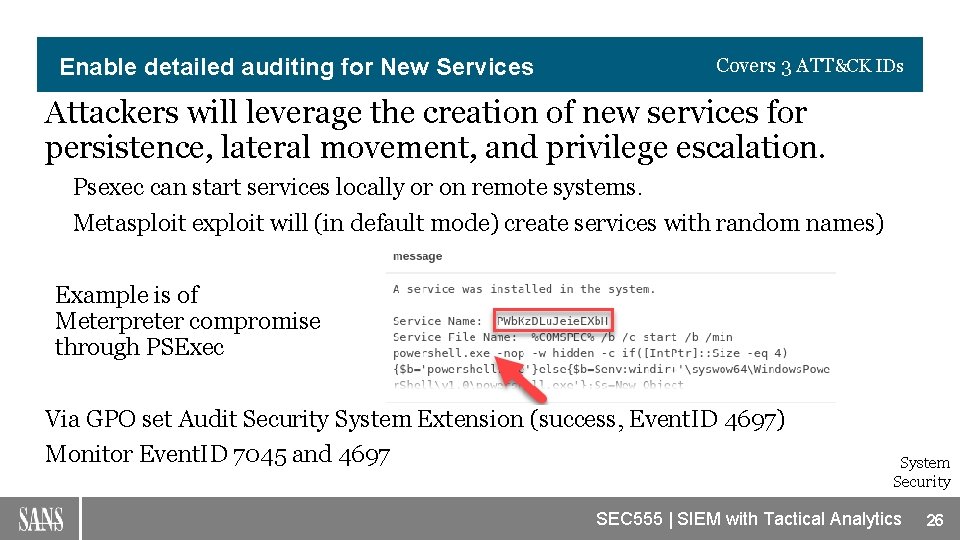
Enable detailed auditing for New Services Covers 3 ATT&CK IDs Attackers will leverage the creation of new services for persistence, lateral movement, and privilege escalation. Psexec can start services locally or on remote systems. Metasploit exploit will (in default mode) create services with random names) Example is of Meterpreter compromise through PSExec Via GPO set Audit Security System Extension (success, Event. ID 4697) Monitor Event. ID 7045 and 4697 System Security SEC 555 | SIEM with Tactical Analytics 26

Bonus 1 – Detect AD Recon Activity Attackers will often ‘rummage’ through AD to find their targets, gain understanding of the environment, etc. Audit Directory Service Access subcategory under “DS Access. ” – Event. ID 4662 Detect AD Recon Activity • Configure auditing on the Admin. SDHolder object. • This applies to all privileged accounts/groups (after about 60 mins). Security SEC 555 | SIEM with Tactical Analytics 27
Bonus 2 – Additional Actions to Consider 1. Run autoruns against machine to find suspicious stuff Save to blind drop Autorunssc –a * -chms > \sharedrivemachinefolder 2. Evaluate events you are currently filtering during log ingestion to determine if a filter should be temporarily lifted. SEC 555 | SIEM with Tactical Analytics 28
Event List Create GPO Demo SEC 555 | SIEM with Tactical Analytics 29
Concluding Thoughts Build multiple IR GPOs Only add machines/OUs to this policy as needed. Decide on criteria for adding machines/OUs to the GPO Decide on criteria to removing machines/OUs from the GPO SEC 555 | SIEM with Tactical Analytics 30

Concluding Thoughts Test IR GPO(s) BEFORE you need to use Determine if new policy breaks something Evaluate impact of increase in logs SEC 555 | SIEM with Tactical Analytics 31

References MITRE ATT&CK: https: //attack. mitre. org/techniques/enterprise/ Atomic Red Team: https: //github. com/redcanaryco/atomic-red-team Cheat Sheets: https: //www. malwarearchaeology. com/cheat-sheets https: //www. malwarearchaeology. com/s/Windows-ATTCK_Logging-Cheat. Sheet_ver_Sept_2018. pdf To Collect ETW logs: https: //docs. microsoft. com/en-us/windows-hardware/drivers/devtest/tracefmt https: //www. fireeye. com/blog/threat-research/2019/03/silketw-because-free-telemetry-isfree. html Living of the Land Binaries: https: //lolbas-project. github. io/ SEC 555 | SIEM with Tactical Analytics 32
References con’t Powershell Downgrade attacks bypass security • Except Windows Powershell log Event ID 400 gives it away • Look for Engine. Version less than 5 Windows Defender Exploit Guard https: //www. microsoft. com/security/blog/2017/10/23/windows-defender-exploit-guardreduce-the-attack-surface-against-next-generation-malware/ Bookmark this page for reference about all Advance Security Audit Policy settings: https: //docs. microsoft. com/en-us/windows/security/threat-protection/auditing/advancedsecurity-auditing-faq https: //twitter. com/mattifestation/status/1217179698008068096? s=20 <<--- if patched, the alert for CVE-2020 -0601 comes in app log SEC 555 | SIEM with Tactical Analytics 33
Notes Configure auditing on the following AD privileged groups to identify AD recon type activities: • Administrators (Admin. SDHolder) • Domain Admins (Admin. SDHolder) • Enterprise Admins (Admin. SDHolder) • Other custom privileged groups • The same auditing settings apply for auditing group access: • Principal, enter “Everyone” • Applies to “This object only” (or “This object and all descendants” for member account auditing as well) • Permissions = “Read all properties” • Properties = “Read all properties” SEC 555 | SIEM with Tactical Analytics 34
Notes Set Auditing on Custom Privileged Groups Enable File Auditing • Computer Configuration/Policies/Windows Settings/Advanced Audit Policy Configuration/Audit Policies/Object Access • Enable Audit File System for Success • Configure File Auditing On %systemroot%SYSVOL folder, open the properties of the domain folder and go to the Auditing tab • Audit Everyone & applies to This folder, subfolders and files • Successful accesses of type Create files / Write data, Create folders / append data, Delete subfolders and files, Delete, and Change permissions. SEC 555 | SIEM with Tactical Analytics 35
Notes LAPS Access Auditing (Event ID 4662) • Use the LAPS Power. Shell module to configure auditing on the LAPS PW attribute: • Set-Adm. Pwd. Auditing –Org. Unit: <name of OU on which you want to setup the auditing> -Audited. Principals: <identification of users/groups whose access to password shall be audited> • Configure auditing of DS Access: • Advanced Audit Policies > DS Access > Audit Directory Service Access Enable SMB Auditing on DCs & file servers. • Enable Power. Shell logging everywhere & send to SIEM. • Monitor scheduled tasks on sensitive systems (DCs, etc). SEC 555 | SIEM with Tactical Analytics 36
- Slides: 36