PIC Microcontroller and Embedded Systems Muhammad Ali Mazidi
PIC Microcontroller and Embedded Systems Muhammad Ali Mazidi, Rolin Mc. Kinlay and Danny Causey Eng. Husam Alzaq The Islamic Uni. Of Gaza The PIC u. Cs 5 -1
Chapter 6: Bank Switching, Table processing, Macros and Modules PIC Microcontroller and Embedded Systems Muhammad Ali Mazidi, Rolin Mc. Kinlay and Danny Causey, February 2007. The PIC u. Cs 6 -2
Objective r List all addressing modes of PIC 18 u. Cs r Contrast and compare the addressing modes r Code PIC 18 instructions to manipulate a r r r lookup table. Access fixed data residing in ROM space. Discuss how to create macros and models, and its advantages. Discuss how to access the entire 4 k. B of RAM List address for all 16 banks of the PIC 18 Discuss bank switching for the PIC 18 The PIC u. Cs 6 -3
Outlines r Immediate and Direct Addressing mode r Register indirect Addressing mode r Lookup table and table processing r Bit addressability of data RAM r Bank switching r Checksum and ASCII subroutines r Macros and models The PIC u. Cs 6 -4
Introduction r Data could be in m A register m In memory m Provided as an immediate values r PIC 18 provides 4 addressing modes m Immediate m Direct m Register indirect m Indexed-ROM The PIC u. Cs 6 -5
Section 6. 1: Immediate and Direct Addressing mode r In immediate addressing mode, the operands comes after the opcode MOVLW 0 x 25 m SUBLW D’ 34’ m ADDLW 0 x 86 m r In direct addressing mode, the operand data is in a RAM location whose address is known and given as a part of the instruction. The PIC u. Cs 6 -6
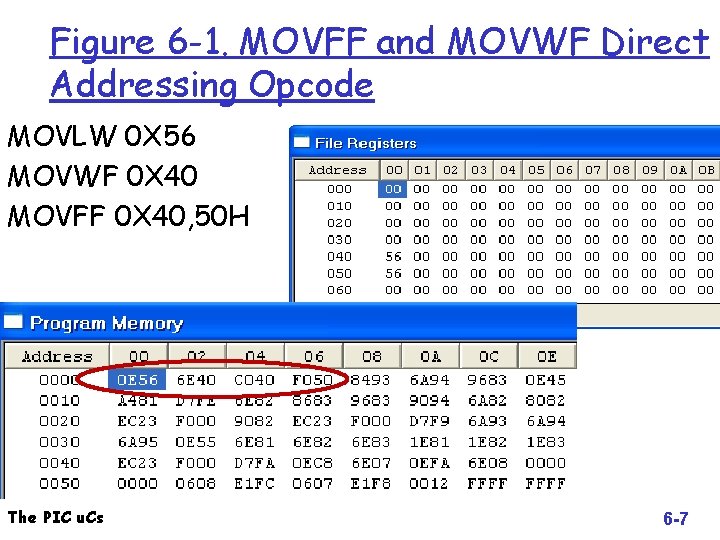
Figure 6 -1. MOVFF and MOVWF Direct Addressing Opcode MOVLW 0 X 56 MOVWF 0 X 40 MOVFF 0 X 40, 50 H The PIC u. Cs 6 -7
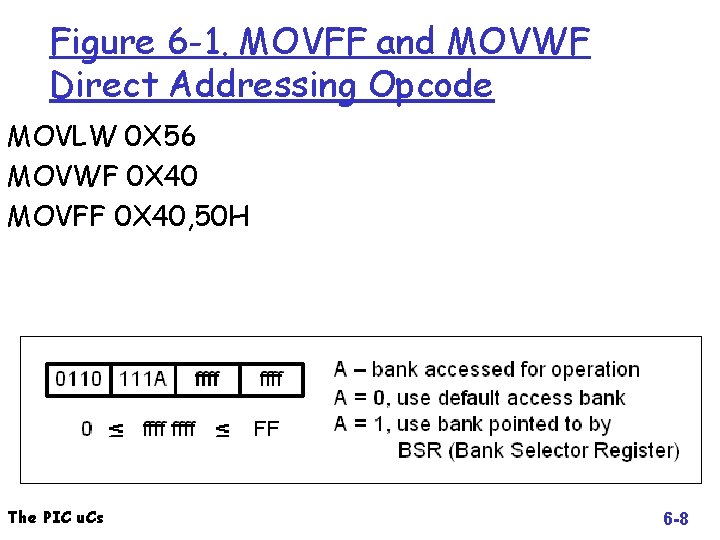
Figure 6 -1. MOVFF and MOVWF Direct Addressing Opcode MOVLW 0 X 56 MOVWF 0 X 40 MOVFF 0 X 40, 50 H The PIC u. Cs 6 -8
Immediate and Direct Addressing mode r What is the difference between m INCF file. Reg, W m INCF file. Reg, F r What is the default destination? r What is the difference between DECFSZ and DECF? Operation m Branch m The PIC u. Cs 6 -9
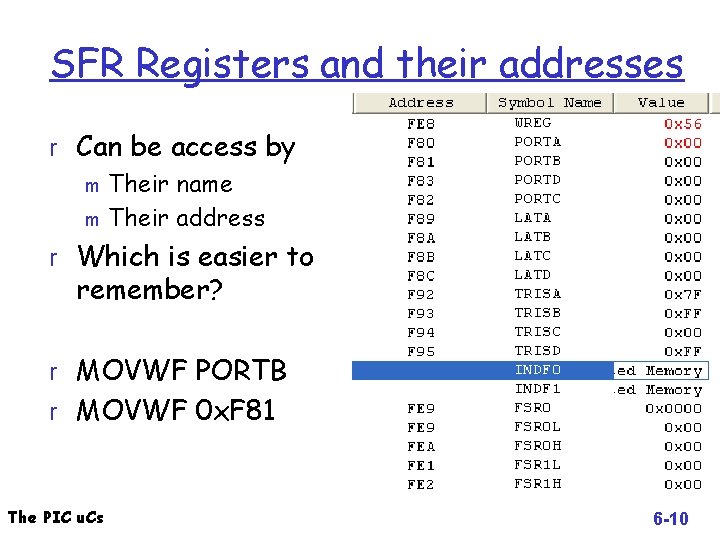
SFR Registers and their addresses r Can be access by m Their name m Their address r Which is easier to remember? r MOVWF PORTB r MOVWF 0 x. F 81 The PIC u. Cs 6 -10
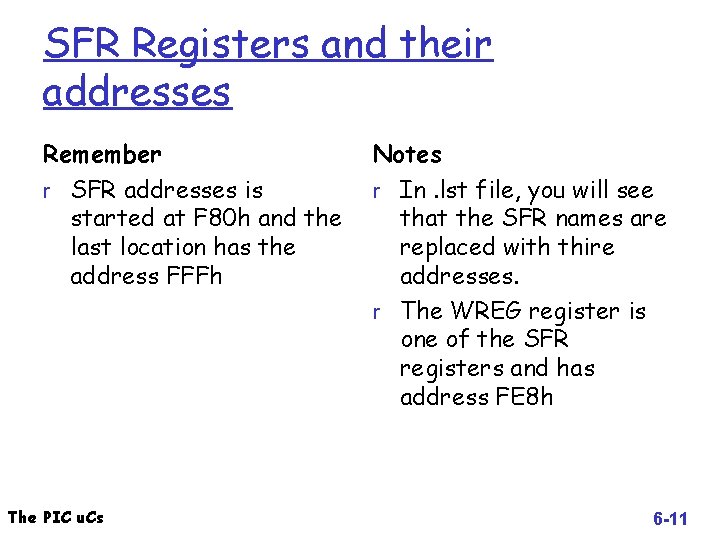
SFR Registers and their addresses Remember Notes r SFR addresses is r In. lst file, you will see started at F 80 h and the last location has the address FFFh The PIC u. Cs that the SFR names are replaced with thire addresses. r The WREG register is one of the SFR registers and has address FE 8 h 6 -11
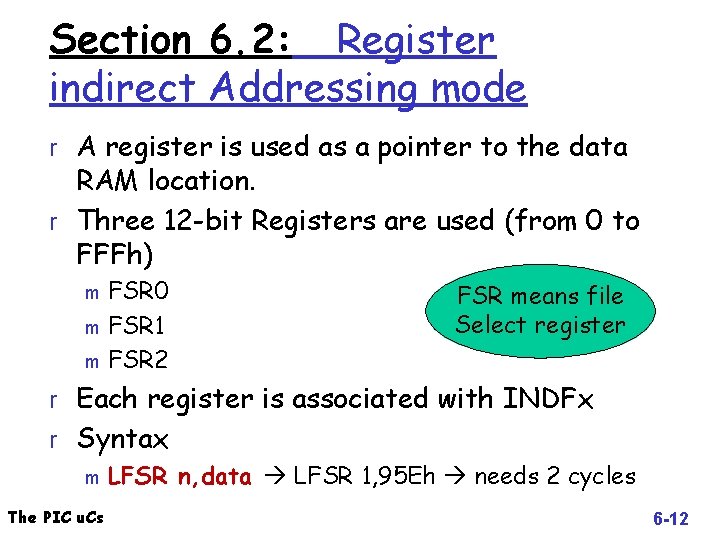
Section 6. 2: Register indirect Addressing mode r A register is used as a pointer to the data RAM location. r Three 12 -bit Registers are used (from 0 to FFFh) FSR 0 m FSR 1 m FSR 2 m FSR means file Select register r Each register is associated with INDFx r Syntax m LFSR n, data LFSR 1, 95 Eh needs 2 cycles The PIC u. Cs 6 -12
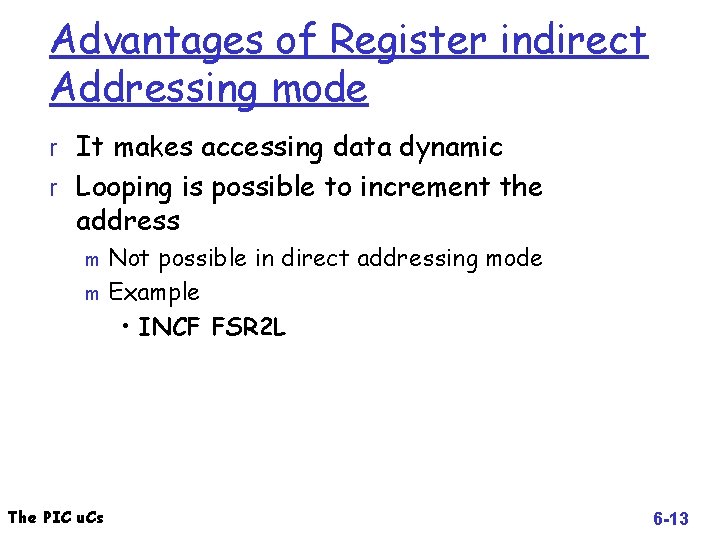
Advantages of Register indirect Addressing mode r It makes accessing data dynamic r Looping is possible to increment the address Not possible in direct addressing mode m Example • INCF FSR 2 L m The PIC u. Cs 6 -13
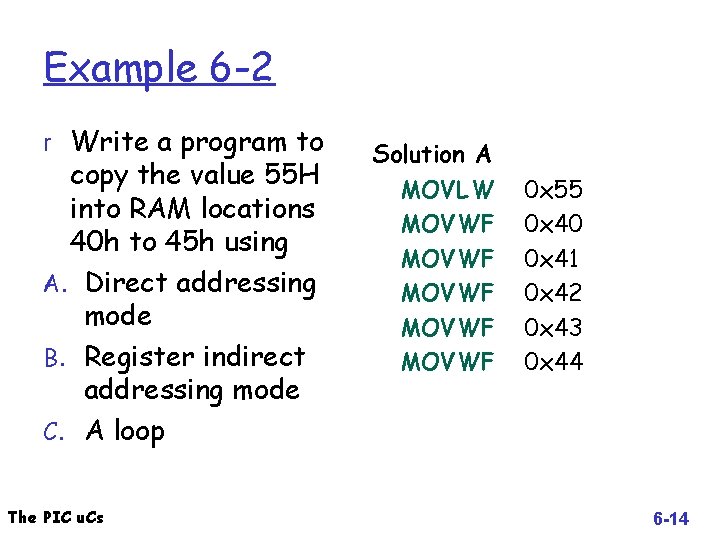
Example 6 -2 r Write a program to copy the value 55 H into RAM locations 40 h to 45 h using A. Direct addressing mode B. Register indirect addressing mode C. A loop The PIC u. Cs Solution A MOVLW MOVWF MOVWF 0 x 55 0 x 40 0 x 41 0 x 42 0 x 43 0 x 44 6 -14
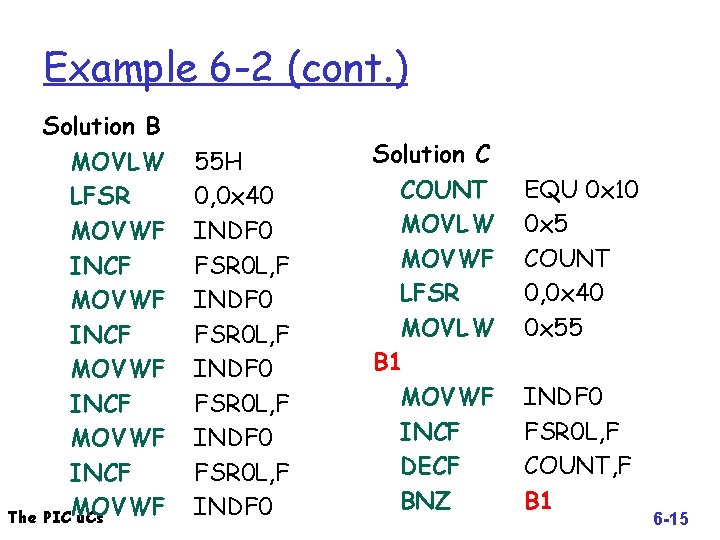
Example 6 -2 (cont. ) Solution B MOVLW LFSR MOVWF INCF The PICMOVWF u. Cs 55 H 0, 0 x 40 INDF 0 FSR 0 L, F INDF 0 Solution C COUNT MOVLW MOVWF LFSR MOVLW B 1 MOVWF INCF DECF BNZ EQU 0 x 10 0 x 5 COUNT 0, 0 x 40 0 x 55 INDF 0 FSR 0 L, F COUNT, F B 1 6 -15
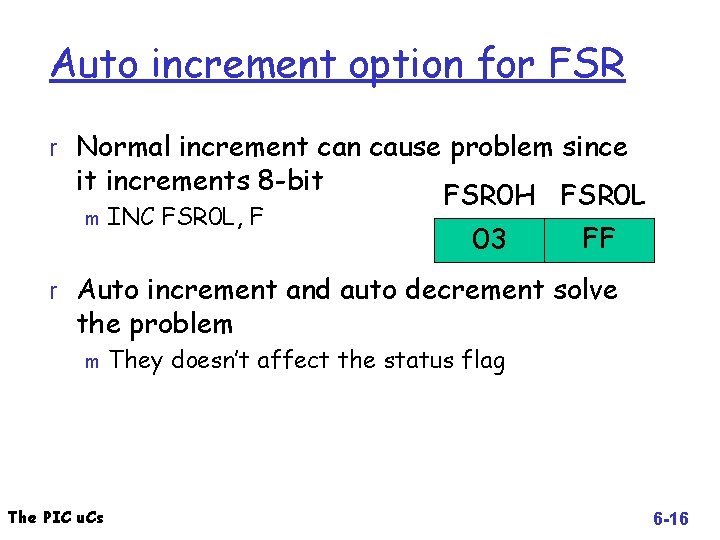
Auto increment option for FSR r Normal increment can cause problem since it increments 8 -bit m INC FSR 0 L, F FSR 0 H FSR 0 L 03 FF r Auto increment and auto decrement solve the problem m The PIC u. Cs They doesn’t affect the status flag 6 -16
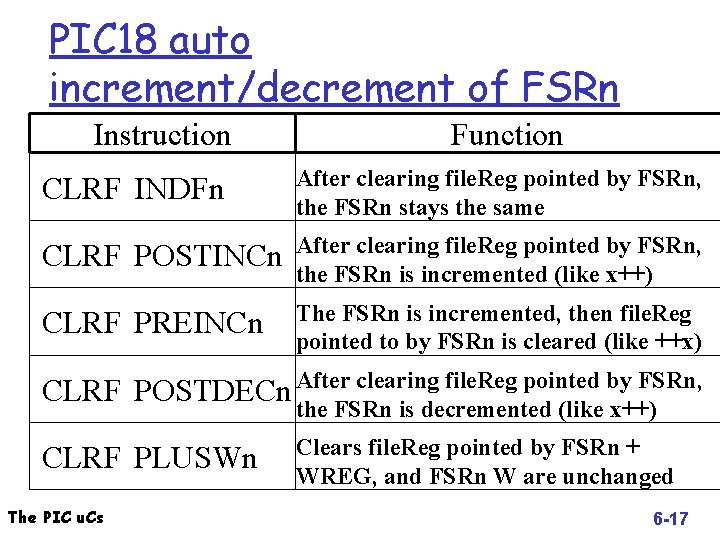
PIC 18 auto increment/decrement of FSRn Instruction Function CLRF INDFn After clearing file. Reg pointed by FSRn, the FSRn stays the same CLRF POSTINCn After clearing file. Reg pointed by FSRn, the FSRn is incremented (like x++) CLRF PREINCn The FSRn is incremented, then file. Reg pointed to by FSRn is cleared (like ++x) CLRF After clearing file. Reg pointed by FSRn, POSTDECn the FSRn is decremented (like x++) CLRF PLUSWn The PIC u. Cs Clears file. Reg pointed by FSRn + WREG, and FSRn W are unchanged 6 -17
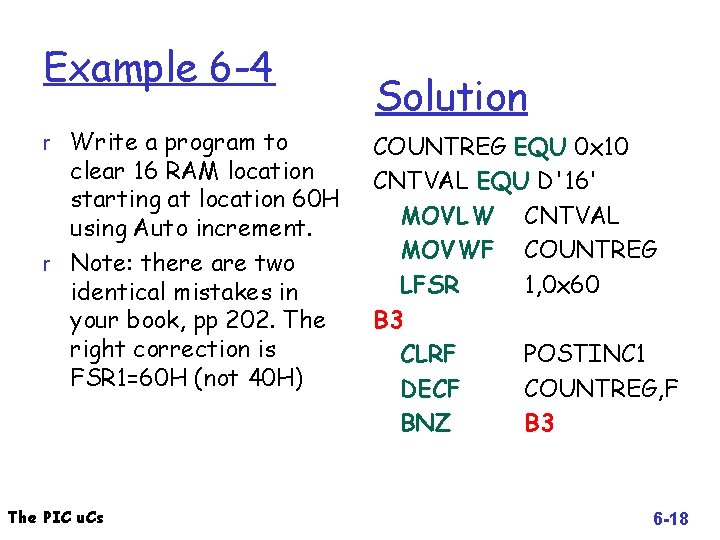
Example 6 -4 r Write a program to clear 16 RAM location starting at location 60 H using Auto increment. r Note: there are two identical mistakes in your book, pp 202. The right correction is FSR 1=60 H (not 40 H) The PIC u. Cs Solution COUNTREG EQU 0 x 10 CNTVAL EQU D'16' MOVLW CNTVAL MOVWF COUNTREG LFSR 1, 0 x 60 B 3 CLRF POSTINC 1 DECF COUNTREG, F BNZ B 3 6 -18
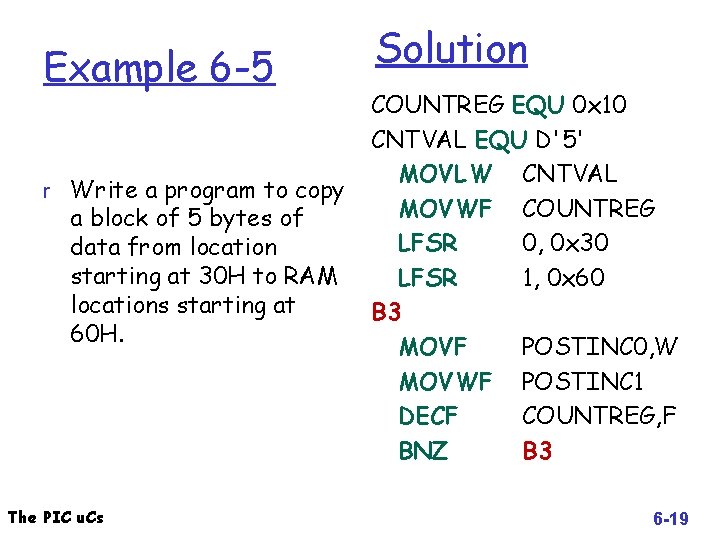
Example 6 -5 r Write a program to copy a block of 5 bytes of data from location starting at 30 H to RAM locations starting at 60 H. The PIC u. Cs Solution COUNTREG EQU 0 x 10 CNTVAL EQU D'5' MOVLW CNTVAL MOVWF COUNTREG LFSR 0, 0 x 30 LFSR 1, 0 x 60 B 3 MOVF POSTINC 0, W MOVWF POSTINC 1 DECF COUNTREG, F BNZ B 3 6 -19
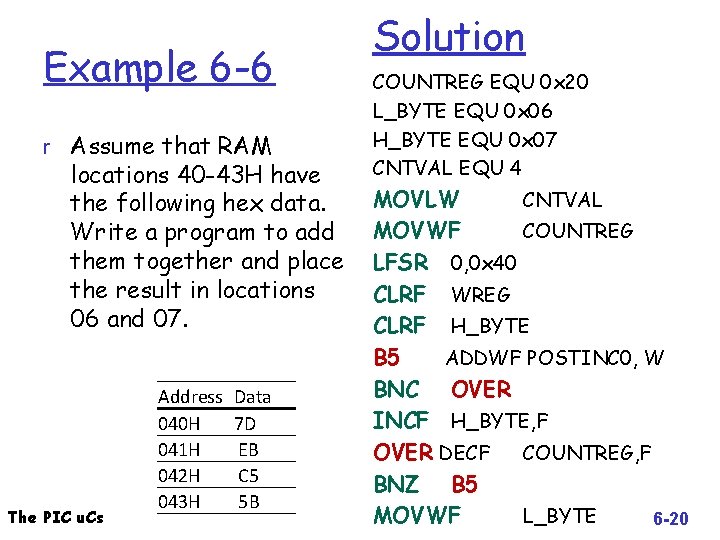
Example 6 -6 r Assume that RAM locations 40 -43 H have the following hex data. Write a program to add them together and place the result in locations 06 and 07. The PIC u. Cs Address 040 H 041 H 042 H 043 H Data 7 D EB C 5 5 B Solution COUNTREG EQU 0 x 20 L_BYTE EQU 0 x 06 H_BYTE EQU 0 x 07 CNTVAL EQU 4 MOVLW CNTVAL MOVWF COUNTREG LFSR 0, 0 x 40 CLRF WREG CLRF H_BYTE B 5 ADDWF POSTINC 0, W BNC OVER INCF H_BYTE, F OVER DECF COUNTREG, F BNZ B 5 MOVWF L_BYTE 6 -20
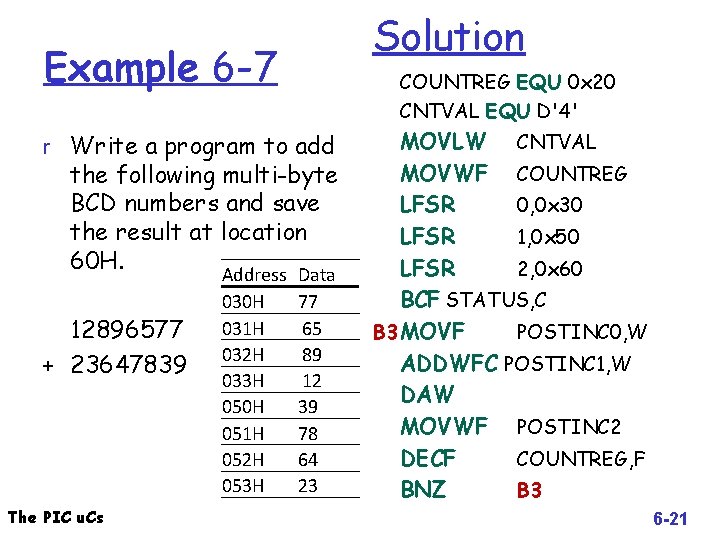
Solution Example 6 -7 COUNTREG EQU 0 x 20 CNTVAL EQU D'4' r Write a program to add the following multi-byte BCD numbers and save the result at location 60 H. 12896577 + 23647839 The PIC u. Cs Address 030 H 031 H 032 H 033 H 050 H 051 H 052 H 053 H Data 77 65 89 12 39 78 64 23 MOVLW CNTVAL MOVWF COUNTREG LFSR 0, 0 x 30 LFSR 1, 0 x 50 LFSR 2, 0 x 60 BCF STATUS, C B 3 MOVF POSTINC 0, W ADDWFC POSTINC 1, W DAW MOVWF POSTINC 2 DECF COUNTREG, F BNZ B 3 6 -21
Section 6. 3: Lookup table and table processing The PIC u. Cs 6 -22
Section 6. 4: bit addressability of data RAM r One of the basic feathers of the PIC 18 is the bit addressability of RAM. m Bit-addressable instructions • Use only direct addressing mode m The PIC u. Cs Byte-addressable instructions 6 -23
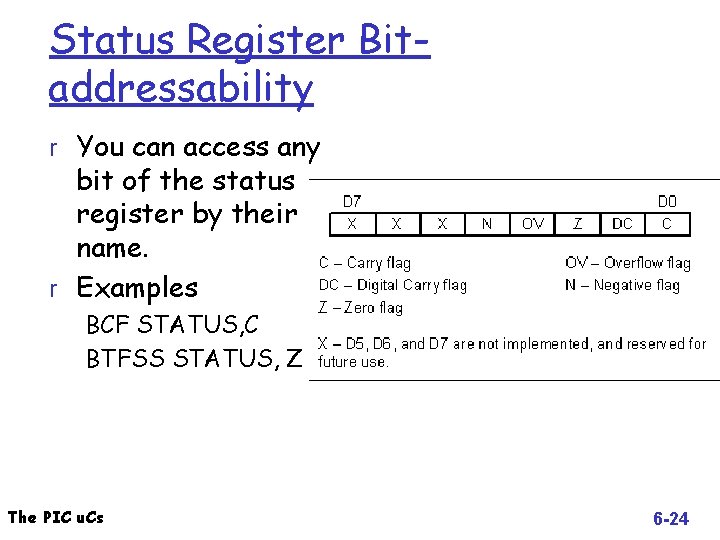
Status Register Bitaddressability r You can access any bit of the status register by their name. r Examples BCF STATUS, C BTFSS STATUS, Z The PIC u. Cs 6 -24
Section 6. 5: Bank switching in the PIC 18 r PIC 18 has maximum of 4 K of RAM m Not all the space used. m The file. Reg is divided into 16 banks of 256 B each m Every PIC 18 has the access bank (the first 128 B of RAM + SFR ) m Most PIC 18 that access the data space in RAM has the ability to access any bank through setting an optional operand, called A m Example: MOVWF my. Reg, A • If 0 it access the default bank (default) • If 1, it uses the bank selection register (BSR) to select the bank The PIC u. Cs 6 -25
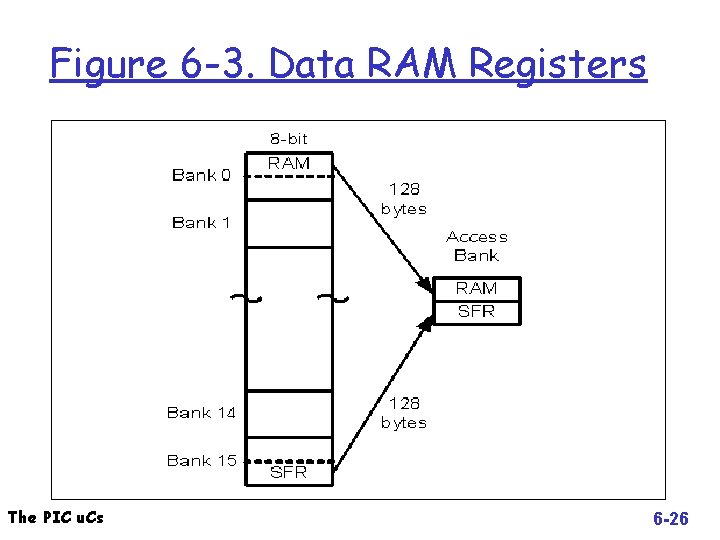
Figure 6 -3. Data RAM Registers The PIC u. Cs 6 -26
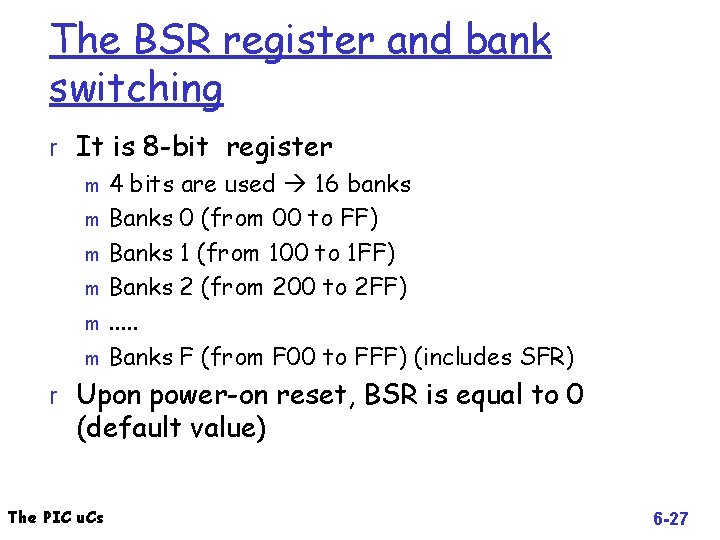
The BSR register and bank switching r It is 8 -bit register m 4 bits are used 16 banks m Banks 0 (from 00 to FF) m Banks 1 (from 100 to 1 FF) m Banks 2 (from 200 to 2 FF) m. . . m Banks F (from F 00 to FFF) (includes SFR) r Upon power-on reset, BSR is equal to 0 (default value) The PIC u. Cs 6 -27
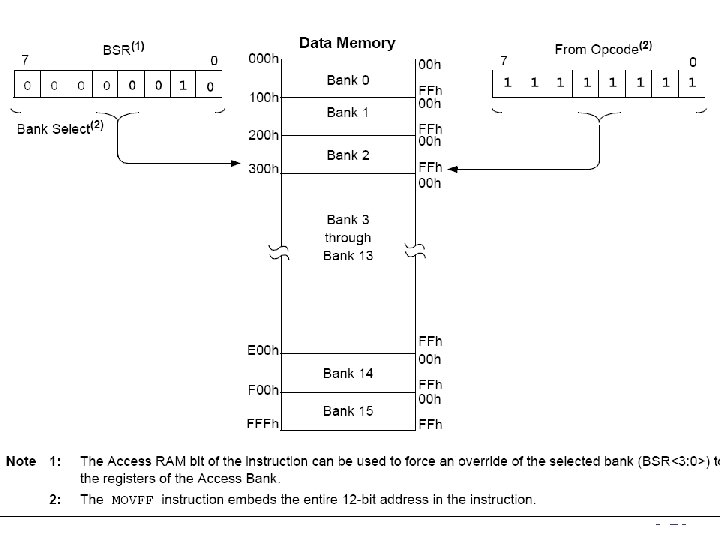
The PIC u. Cs 6 -28
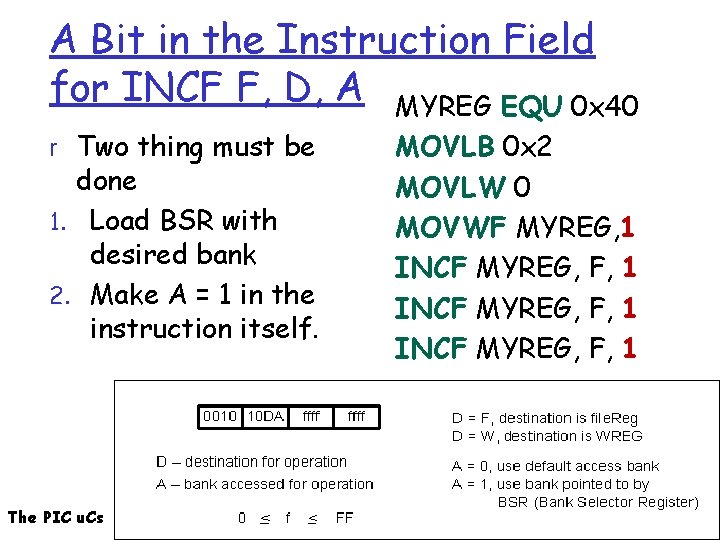
A Bit in the Instruction Field for INCF F, D, A MYREG EQU 0 x 40 r Two thing must be done 1. Load BSR with desired bank 2. Make A = 1 in the instruction itself. The PIC u. Cs MOVLB 0 x 2 MOVLW 0 MOVWF MYREG, 1 INCF MYREG, F, 1 6 -29
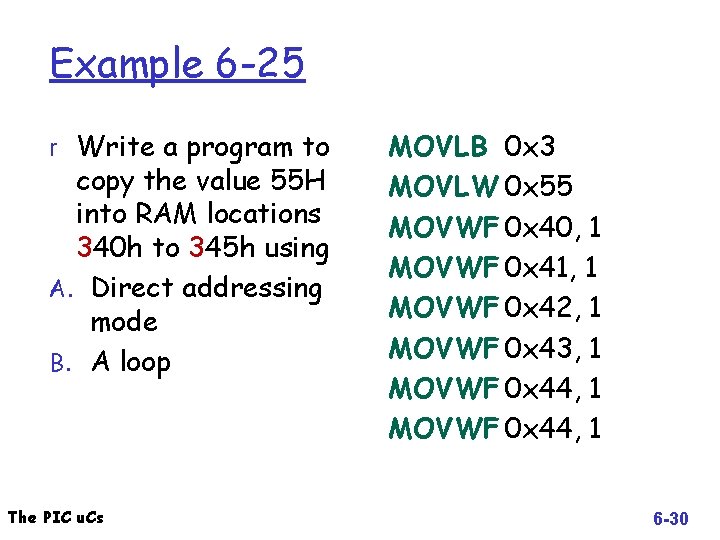
Example 6 -25 r Write a program to copy the value 55 H into RAM locations 340 h to 345 h using A. Direct addressing mode B. A loop The PIC u. Cs MOVLB 0 x 3 MOVLW 0 x 55 MOVWF 0 x 40, 1 MOVWF 0 x 41, 1 MOVWF 0 x 42, 1 MOVWF 0 x 43, 1 MOVWF 0 x 44, 1 6 -30
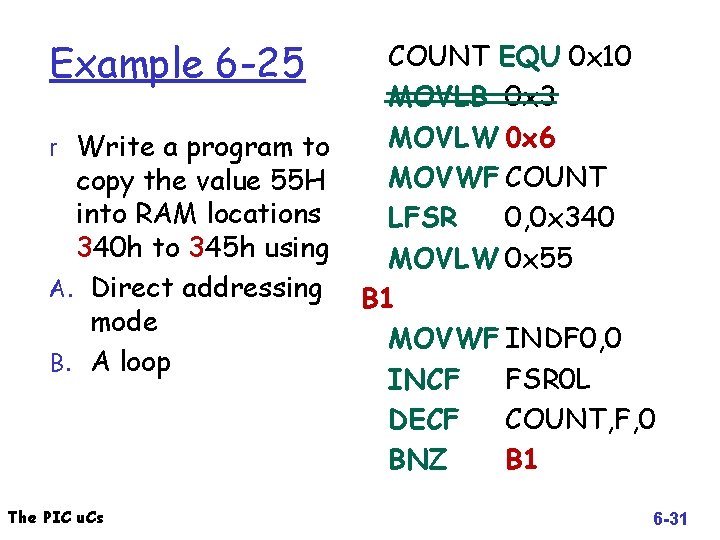
Example 6 -25 r Write a program to copy the value 55 H into RAM locations 340 h to 345 h using A. Direct addressing mode B. A loop The PIC u. Cs COUNT EQU 0 x 10 MOVLB 0 x 3 MOVLW 0 x 6 MOVWF COUNT LFSR 0, 0 x 340 MOVLW 0 x 55 B 1 MOVWF INDF 0, 0 INCF FSR 0 L DECF COUNT, F, 0 BNZ B 1 6 -31
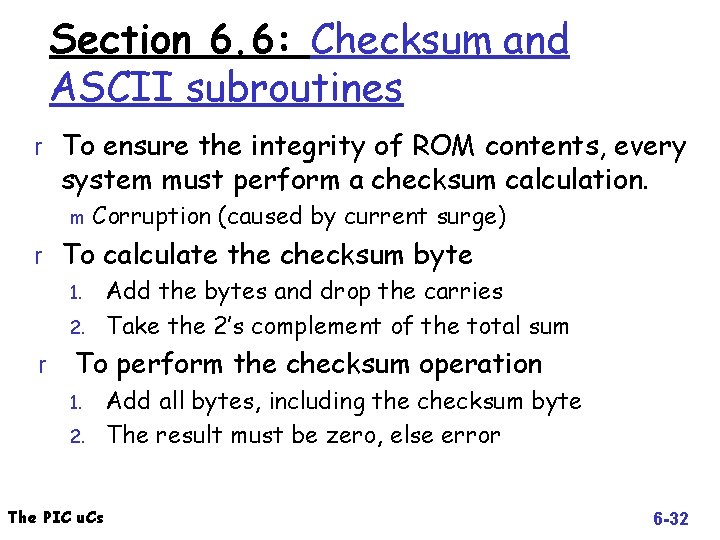
Section 6. 6: Checksum and ASCII subroutines r To ensure the integrity of ROM contents, every system must perform a checksum calculation. m Corruption (caused by current surge) r To calculate the checksum byte 1. Add the bytes and drop the carries 2. Take the 2’s complement of the total sum r To perform the checksum operation 1. 2. The PIC u. Cs Add all bytes, including the checksum byte The result must be zero, else error 6 -32
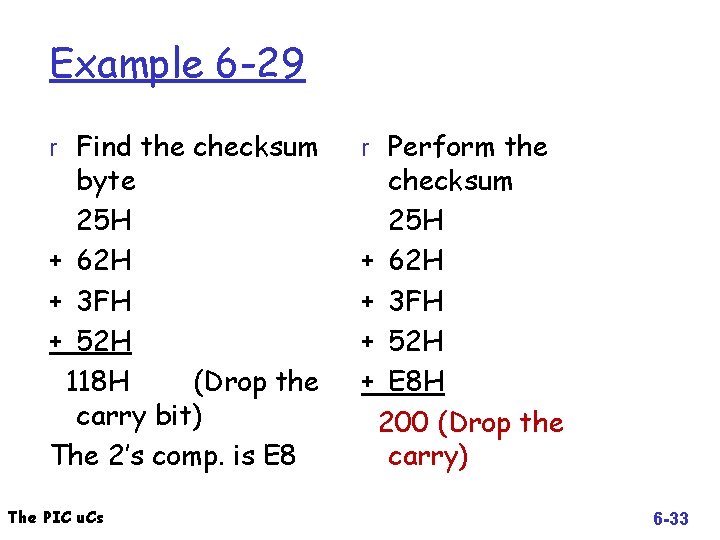
Example 6 -29 r Find the checksum byte 25 H + 62 H + 3 FH + 52 H 118 H (Drop the carry bit) The 2’s comp. is E 8 The PIC u. Cs r Perform the checksum 25 H + 62 H + 3 FH + 52 H + E 8 H 200 (Drop the carry) 6 -33
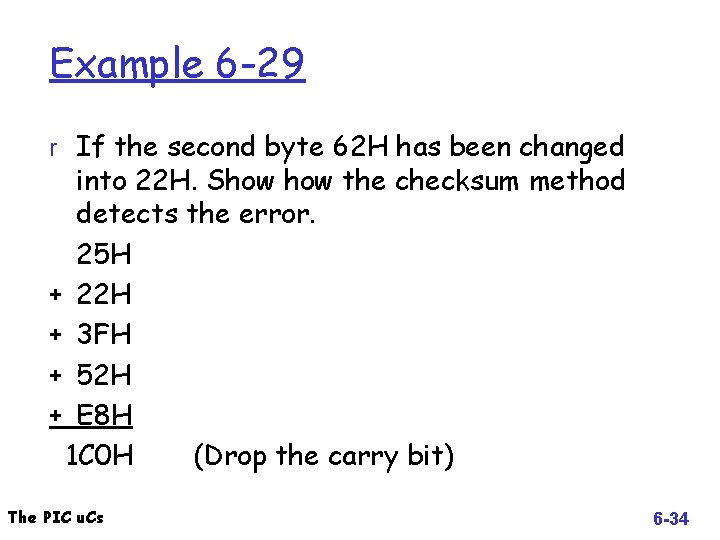
Example 6 -29 r If the second byte 62 H has been changed into 22 H. Show the checksum method detects the error. 25 H + 22 H + 3 FH + 52 H + E 8 H 1 C 0 H (Drop the carry bit) The PIC u. Cs 6 -34
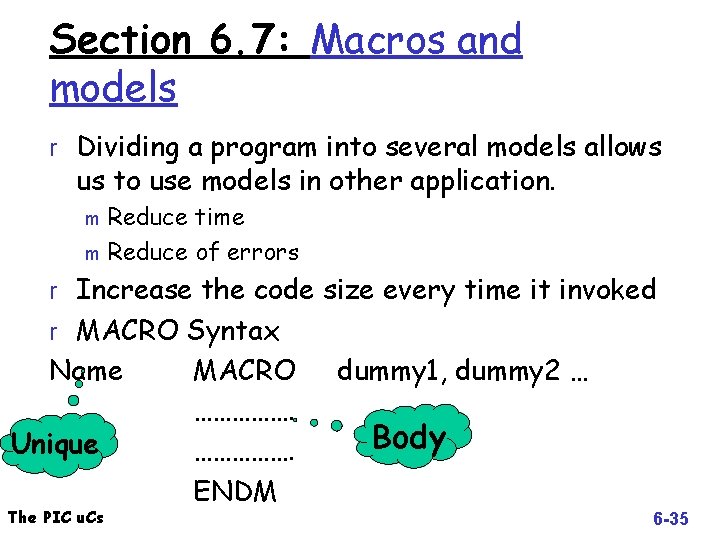
Section 6. 7: Macros and models r Dividing a program into several models allows us to use models in other application. Reduce time m Reduce of errors m r Increase the code size every time it invoked r MACRO Syntax Name Unique The PIC u. Cs MACRO ……………. ENDM dummy 1, dummy 2 … Body 6 -35
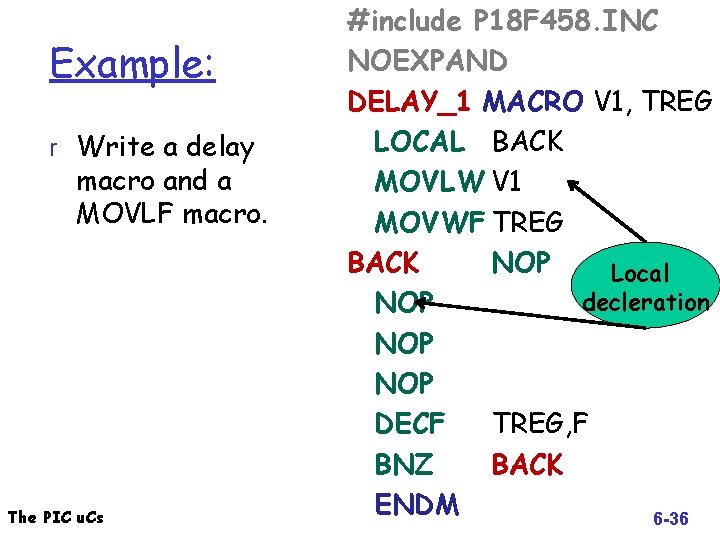
Example: r Write a delay macro and a MOVLF macro. The PIC u. Cs #include P 18 F 458. INC NOEXPAND DELAY_1 MACRO V 1, TREG LOCAL BACK MOVLW V 1 MOVWF TREG BACK NOP Local decleration NOP NOP DECF TREG, F BNZ BACK ENDM 6 -36
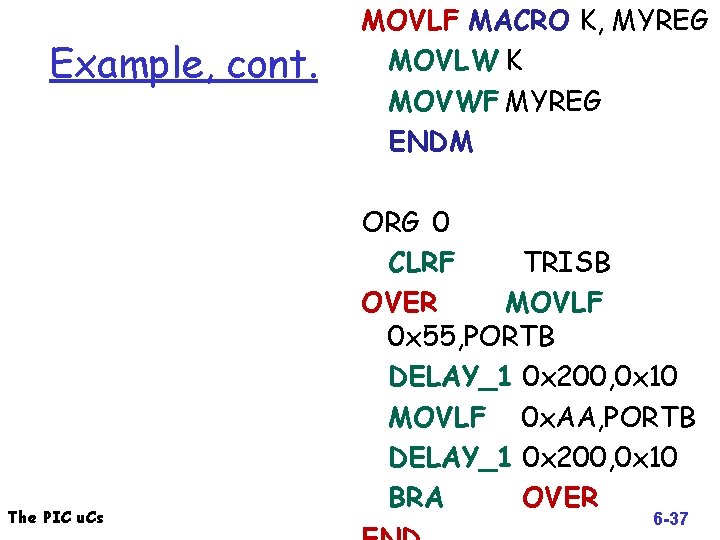
Example, cont. The PIC u. Cs MOVLF MACRO K, MYREG MOVLW K MOVWF MYREG ENDM ORG 0 CLRF TRISB OVER MOVLF 0 x 55, PORTB DELAY_1 0 x 200, 0 x 10 MOVLF 0 x. AA, PORTB DELAY_1 0 x 200, 0 x 10 BRA OVER 6 -37
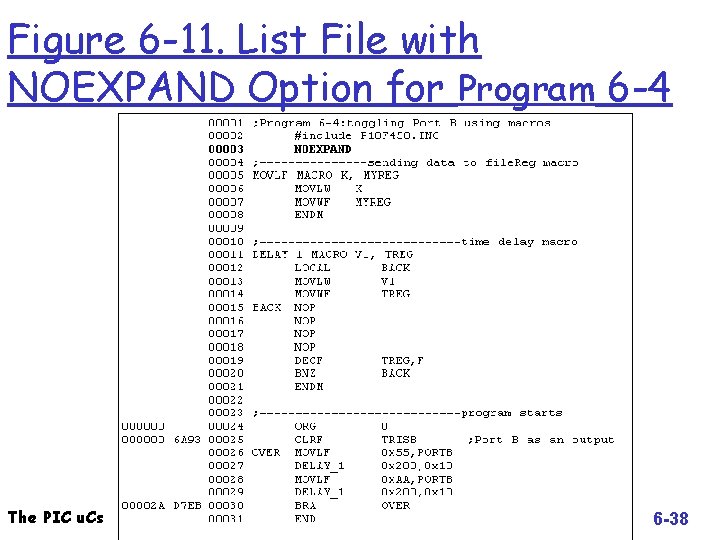
Figure 6 -11. List File with NOEXPAND Option for Program 6 -4 The PIC u. Cs 6 -38
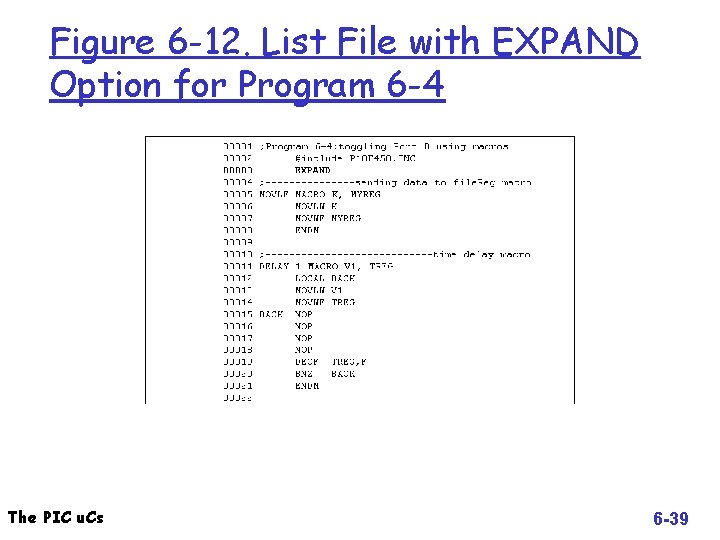
Figure 6 -12. List File with EXPAND Option for Program 6 -4 The PIC u. Cs 6 -39
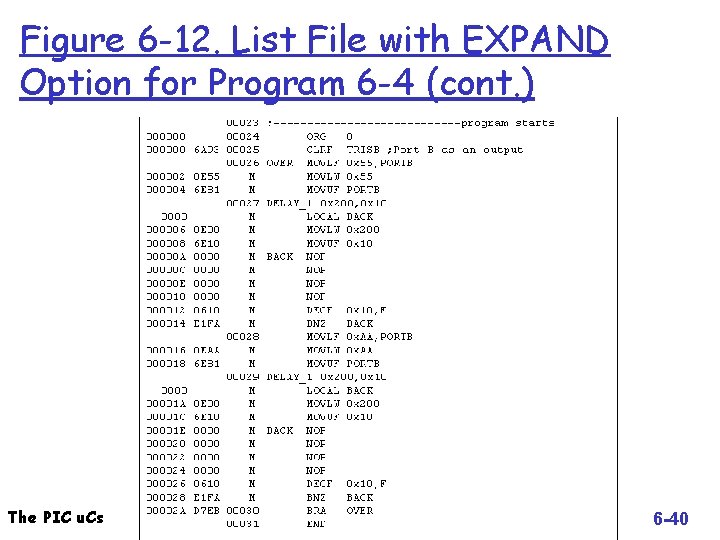
Figure 6 -12. List File with EXPAND Option for Program 6 -4 (cont. ) The PIC u. Cs 6 -40
Chapter 6: Summary Next: Chapter 9 Arithmetic, logic Instruction and programs The PIC u. Cs 6 -41
- Slides: 41