Nexus 7000 virtual PortChannel Best Practices Design Guidelines

Nexus 7000 virtual Port-Channel Best Practices & Design Guidelines Roberto Mari Technical Marketing Engineer Data Center Business Unit © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential November 2009 version 1. 1 1
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 2
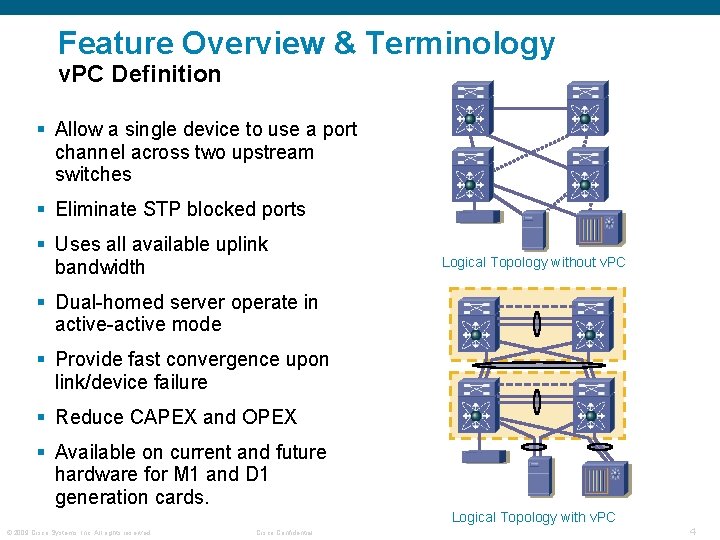
Feature Overview & Terminology v. PC Definition § Allow a single device to use a port channel across two upstream switches § Eliminate STP blocked ports § Uses all available uplink bandwidth Logical Topology without v. PC § Dual-homed server operate in active-active mode § Provide fast convergence upon link/device failure § Reduce CAPEX and OPEX § Available on current and future hardware for M 1 and D 1 generation cards. Logical Topology with v. PC © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 4
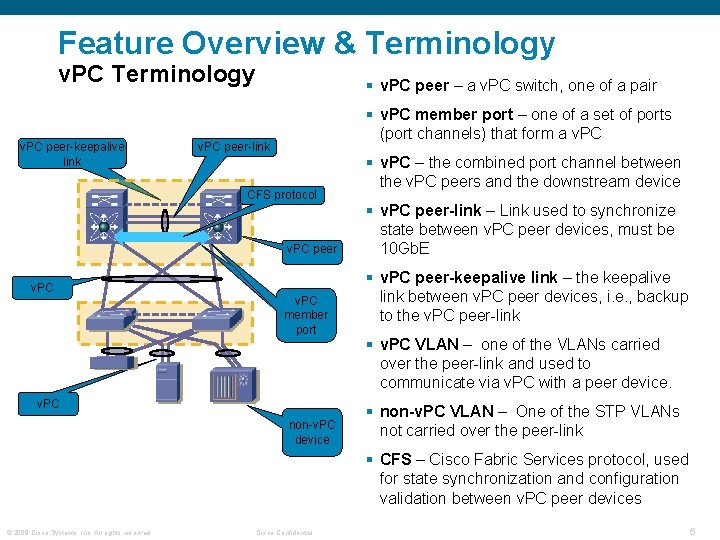
Feature Overview & Terminology v. PC peer-keepalive link § v. PC peer – a v. PC switch, one of a pair § v. PC member port – one of a set of ports (port channels) that form a v. PC peer-link CFS protocol v. PC peer v. PC member port v. PC non-v. PC device § v. PC – the combined port channel between the v. PC peers and the downstream device § v. PC peer-link – Link used to synchronize state between v. PC peer devices, must be 10 Gb. E § v. PC peer-keepalive link – the keepalive link between v. PC peer devices, i. e. , backup to the v. PC peer-link § v. PC VLAN – one of the VLANs carried over the peer-link and used to communicate via v. PC with a peer device. § non-v. PC VLAN – One of the STP VLANs not carried over the peer-link § CFS – Cisco Fabric Services protocol, used for state synchronization and configuration validation between v. PC peer devices © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 5
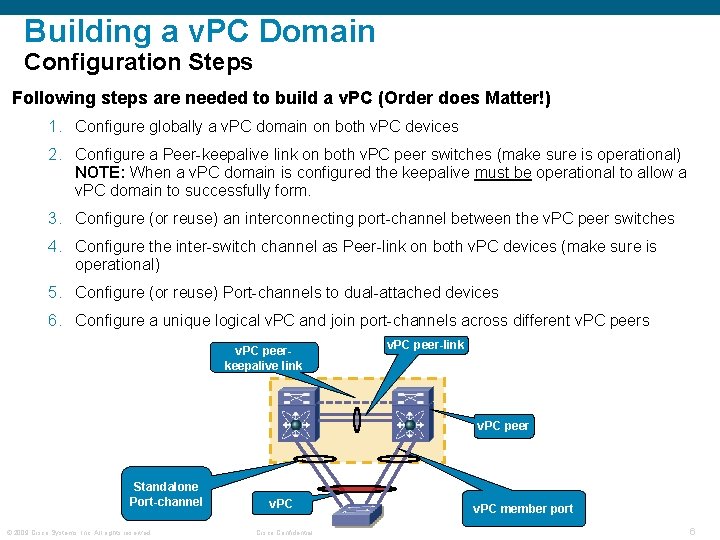
Building a v. PC Domain Configuration Steps Following steps are needed to build a v. PC (Order does Matter!) 1. Configure globally a v. PC domain on both v. PC devices 2. Configure a Peer-keepalive link on both v. PC peer switches (make sure is operational) NOTE: When a v. PC domain is configured the keepalive must be operational to allow a v. PC domain to successfully form. 3. Configure (or reuse) an interconnecting port-channel between the v. PC peer switches 4. Configure the inter-switch channel as Peer-link on both v. PC devices (make sure is operational) 5. Configure (or reuse) Port-channels to dual-attached devices 6. Configure a unique logical v. PC and join port-channels across different v. PC peers v. PC peerkeepalive link v. PC peer-link v. PC peer Standalone Port-channel © 2009 Cisco Systems, Inc. All rights reserved. v. PC Cisco Confidential v. PC member port 6
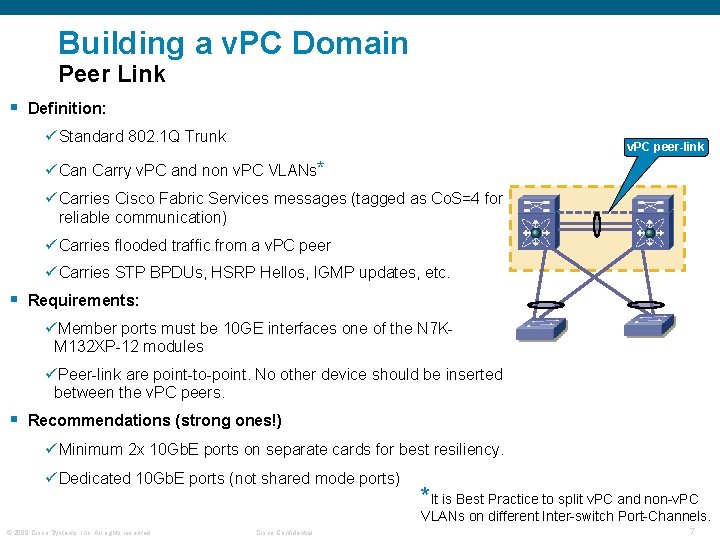
Building a v. PC Domain Peer Link § Definition: ü Standard 802. 1 Q Trunk v. PC peer-link ü Can Carry v. PC and non v. PC VLANs* ü Carries Cisco Fabric Services messages (tagged as Co. S=4 for reliable communication) ü Carries flooded traffic from a v. PC peer ü Carries STP BPDUs, HSRP Hellos, IGMP updates, etc. § Requirements: üMember ports must be 10 GE interfaces one of the N 7 KM 132 XP-12 modules üPeer-link are point-to-point. No other device should be inserted between the v. PC peers. § Recommendations (strong ones!) ü Minimum 2 x 10 Gb. E ports on separate cards for best resiliency. ü Dedicated 10 Gb. E ports (not shared mode ports) *It is Best Practice to split v. PC and non-v. PC VLANs on different Inter-switch Port-Channels. © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 7
Building a v. PC Domain Peer Link with Single 10 G Module § Common Nexus 7000 configuration: 1 x 10 G, 7 x 1 G cards § v. PC recommendation is 2 10 G cards § Potential problem occurs if Nexus 7000 is L 3 boundary with single 10 G card § Use Object Tracking Feature available in 4. 2 § More information from CCO: http: //www. cisco. com/en/US/docs/switches/datacenter/sw/4_2/nxos/interfaces/configuration/guide/if_v. PC. html#wp 1529488 © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 8
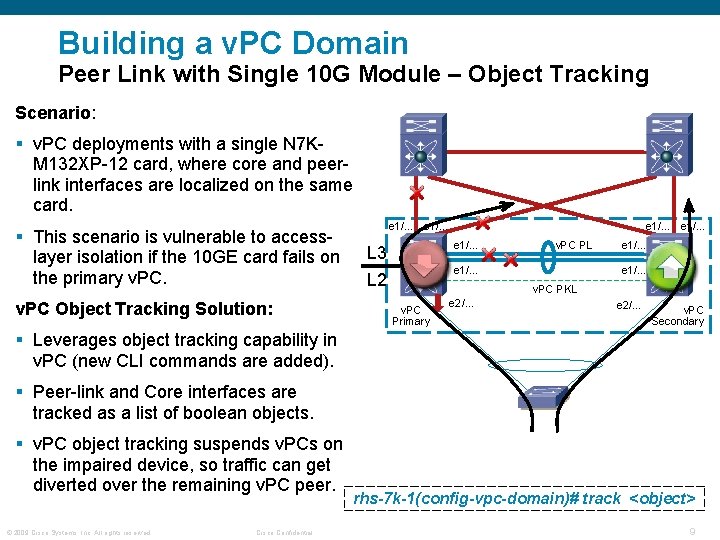
Building a v. PC Domain Peer Link with Single 10 G Module – Object Tracking Scenario: § v. PC deployments with a single N 7 KM 132 XP-12 card, where core and peerlink interfaces are localized on the same card. § This scenario is vulnerable to accesslayer isolation if the 10 GE card fails on the primary v. PC Object Tracking Solution: e 1/… e 1/… L 3 L 2 v. PC PL e 1/… v. PC PKL v. PC Primary e 2/… v. PC Secondary § Leverages object tracking capability in v. PC (new CLI commands are added). § Peer-link and Core interfaces are tracked as a list of boolean objects. § v. PC object tracking suspends v. PCs on the impaired device, so traffic can get diverted over the remaining v. PC peer. © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential rhs-7 k-1(config-vpc-domain)# track <object> 9
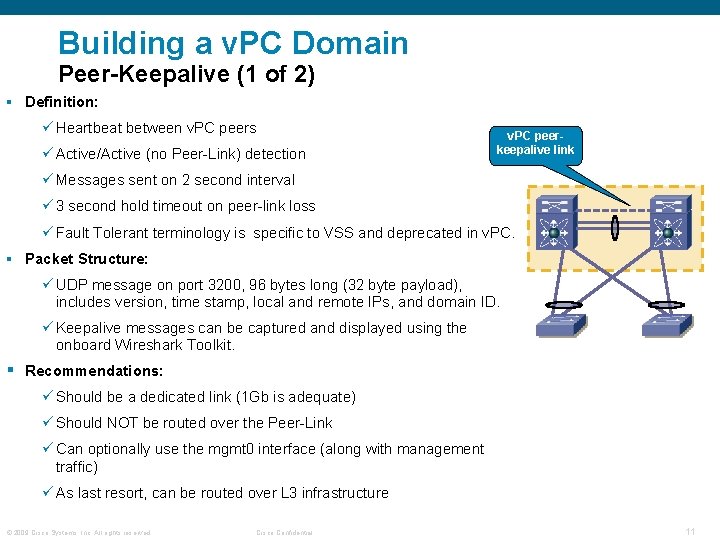
Building a v. PC Domain Peer-Keepalive (1 of 2) § Definition: ü Heartbeat between v. PC peers ü Active/Active (no Peer-Link) detection v. PC peerkeepalive link ü Messages sent on 2 second interval ü 3 second hold timeout on peer-link loss ü Fault Tolerant terminology is specific to VSS and deprecated in v. PC. § Packet Structure: ü UDP message on port 3200, 96 bytes long (32 byte payload), includes version, time stamp, local and remote IPs, and domain ID. ü Keepalive messages can be captured and displayed using the onboard Wireshark Toolkit. § Recommendations: ü Should be a dedicated link (1 Gb is adequate) ü Should NOT be routed over the Peer-Link ü Can optionally use the mgmt 0 interface (along with management traffic) ü As last resort, can be routed over L 3 infrastructure © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 11
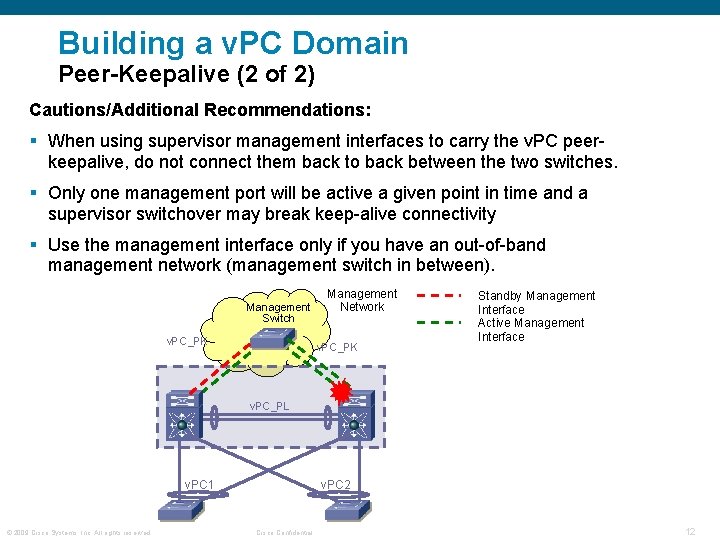
Building a v. PC Domain Peer-Keepalive (2 of 2) Cautions/Additional Recommendations: § When using supervisor management interfaces to carry the v. PC peerkeepalive, do not connect them back to back between the two switches. § Only one management port will be active a given point in time and a supervisor switchover may break keep-alive connectivity § Use the management interface only if you have an out-of-band management network (management switch in between). Management Switch v. PC_PK Management Network v. PC_PK Standby Management Interface Active Management Interface v. PC_PL v. PC 1 © 2009 Cisco Systems, Inc. All rights reserved. v. PC 2 Cisco Confidential 12
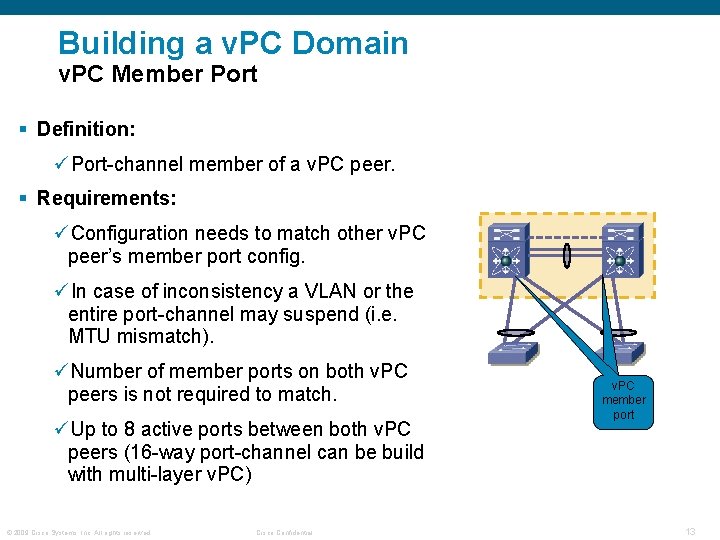
Building a v. PC Domain v. PC Member Port § Definition: üPort-channel member of a v. PC peer. § Requirements: üConfiguration needs to match other v. PC peer’s member port config. üIn case of inconsistency a VLAN or the entire port-channel may suspend (i. e. MTU mismatch). üNumber of member ports on both v. PC peers is not required to match. üUp to 8 active ports between both v. PC peers (16 -way port-channel can be build with multi-layer v. PC) © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential v. PC member port 13
Building a v. PC Domain VDC Interaction § v. PC works seamlessly in any VDC based environment. § One v. PC domain per VDC is supported, up to the maximum number of VDCs supported in the system. § It is still necessary to have a separate v. PC peer-link and v. PC Peer. Keepalive Link infrastructure for each VDC deployed. Can v. PC run between VDCs on the same switch? § This scenario should technically work, but it is NOT officially supported and has not been extensively tested by our QA team. § Could be useful for Demo or hands on, but It is NOT recommended for production environments. Will consolidate redundant points on the same box with VDCs (e. g. whole aggregation layer on a box) and introduce a single point of failure. § ISSU will NOT work in this configuration, because the v. PC devices can NOT be independently upgraded. © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 14
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 15
Attaching to a v. PC domain The One and Only Rule… ALWAYS dual attach devices to a v. PC Domain!!! © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 16
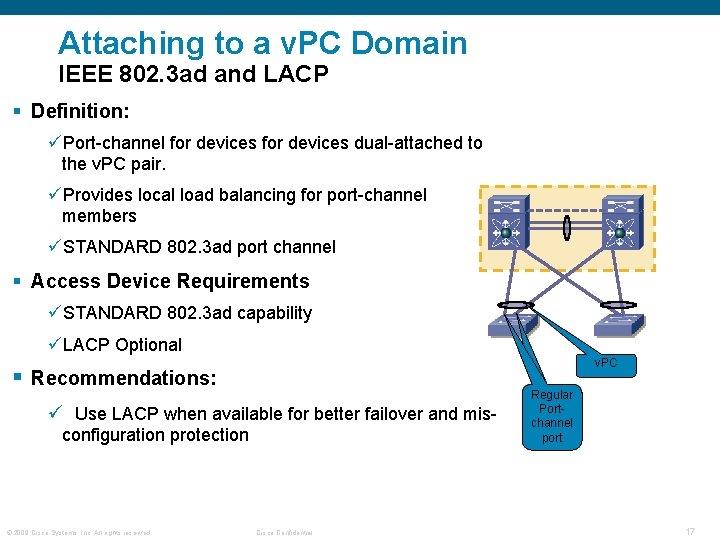
Attaching to a v. PC Domain IEEE 802. 3 ad and LACP § Definition: üPort-channel for devices dual-attached to the v. PC pair. üProvides local load balancing for port-channel members üSTANDARD 802. 3 ad port channel § Access Device Requirements üSTANDARD 802. 3 ad capability üLACP Optional v. PC § Recommendations: ü Use LACP when available for better failover and misconfiguration protection © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential v. PC Regular member Portport channel port 17
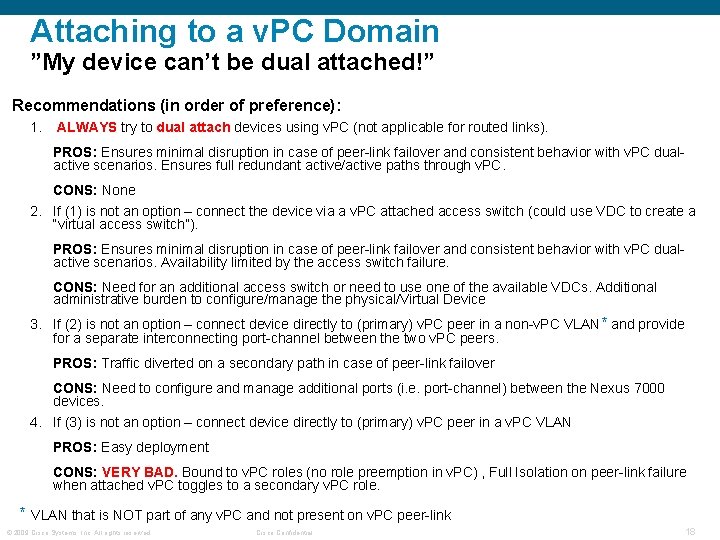
Attaching to a v. PC Domain ”My device can’t be dual attached!” Recommendations (in order of preference): 1. ALWAYS try to dual attach devices using v. PC (not applicable for routed links). PROS: Ensures minimal disruption in case of peer-link failover and consistent behavior with v. PC dualactive scenarios. Ensures full redundant active/active paths through v. PC. CONS: None 2. If (1) is not an option – connect the device via a v. PC attached access switch (could use VDC to create a “virtual access switch”). PROS: Ensures minimal disruption in case of peer-link failover and consistent behavior with v. PC dualactive scenarios. Availability limited by the access switch failure. CONS: Need for an additional access switch or need to use one of the available VDCs. Additional administrative burden to configure/manage the physical/Virtual Device 3. If (2) is not an option – connect device directly to (primary) v. PC peer in a non-v. PC VLAN* and provide for a separate interconnecting port-channel between the two v. PC peers. PROS: Traffic diverted on a secondary path in case of peer-link failover CONS: Need to configure and manage additional ports (i. e. port-channel) between the Nexus 7000 devices. 4. If (3) is not an option – connect device directly to (primary) v. PC peer in a v. PC VLAN PROS: Easy deployment CONS: VERY BAD. Bound to v. PC roles (no role preemption in v. PC) , Full Isolation on peer-link failure when attached v. PC toggles to a secondary v. PC role. * VLAN that is NOT part of any v. PC and not present on v. PC peer-link © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 18
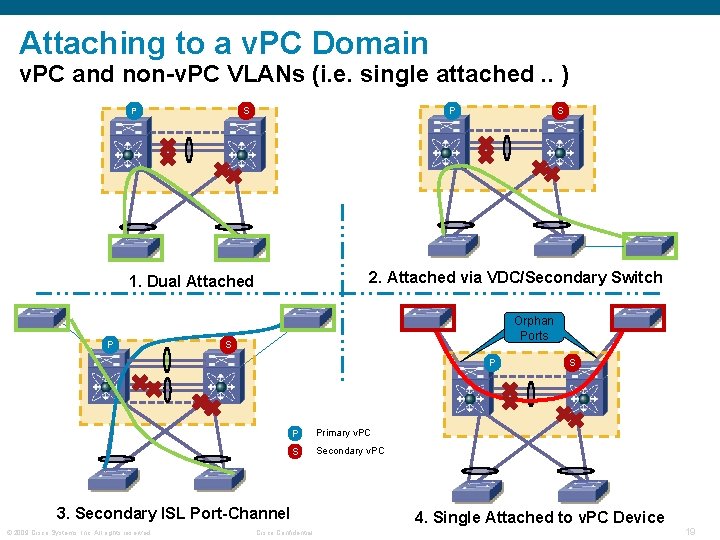
Attaching to a v. PC Domain v. PC and non-v. PC VLANs (i. e. single attached. . ) S P P 2. Attached via VDC/Secondary Switch 1. Dual Attached P S Orphan Ports S P P Primary v. PC S Secondary v. PC 3. Secondary ISL Port-Channel © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential S 4. Single Attached to v. PC Device 19
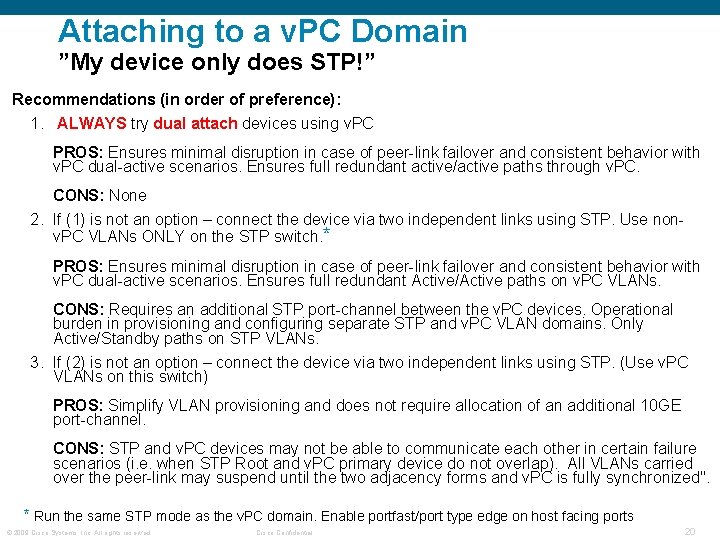
Attaching to a v. PC Domain ”My device only does STP!” Recommendations (in order of preference): 1. ALWAYS try dual attach devices using v. PC PROS: Ensures minimal disruption in case of peer-link failover and consistent behavior with v. PC dual-active scenarios. Ensures full redundant active/active paths through v. PC. CONS: None 2. If (1) is not an option – connect the device via two independent links using STP. Use nonv. PC VLANs ONLY on the STP switch. * PROS: Ensures minimal disruption in case of peer-link failover and consistent behavior with v. PC dual-active scenarios. Ensures full redundant Active/Active paths on v. PC VLANs. CONS: Requires an additional STP port-channel between the v. PC devices. Operational burden in provisioning and configuring separate STP and v. PC VLAN domains. Only Active/Standby paths on STP VLANs. 3. If (2) is not an option – connect the device via two independent links using STP. (Use v. PC VLANs on this switch) PROS: Simplify VLAN provisioning and does not require allocation of an additional 10 GE port-channel. CONS: STP and v. PC devices may not be able to communicate each other in certain failure scenarios (i. e. when STP Root and v. PC primary device do not overlap). All VLANs carried over the peer-link may suspend until the two adjacency forms and v. PC is fully synchronized". * Run the same STP mode as the v. PC domain. Enable portfast/port type edge on host facing ports © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 20
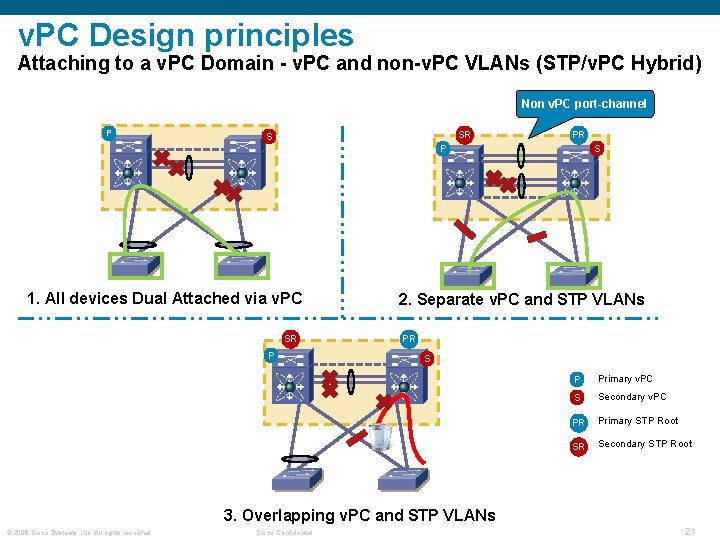
v. PC Design principles Attaching to a v. PC Domain - v. PC and non-v. PC VLANs (STP/v. PC Hybrid) Non v. PC port-channel P SR S P 1. All devices Dual Attached via v. PC SR P 2. Separate v. PC and STP VLANs PR S P Primary v. PC S Secondary v. PC PR Primary STP Root SR Secondary STP Root 3. Overlapping v. PC and STP VLANs © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 21
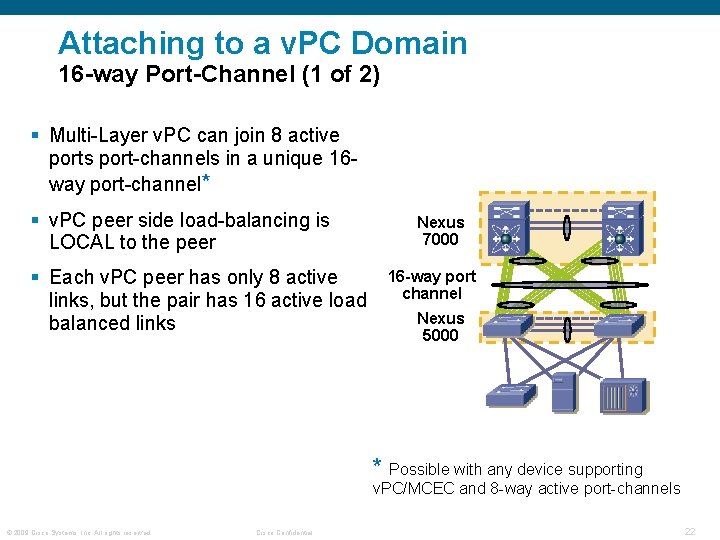
Attaching to a v. PC Domain 16 -way Port-Channel (1 of 2) § Multi-Layer v. PC can join 8 active ports port-channels in a unique 16 way port-channel* § v. PC peer side load-balancing is LOCAL to the peer § Each v. PC peer has only 8 active links, but the pair has 16 active load balanced links Nexus 7000 16 -way port channel Nexus 5000 * Possible with any device supporting v. PC/MCEC and 8 -way active port-channels © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 22
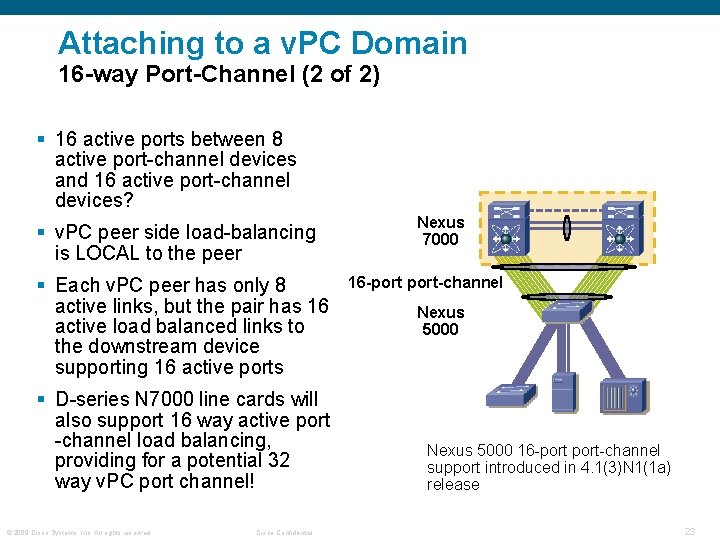
Attaching to a v. PC Domain 16 -way Port-Channel (2 of 2) § 16 active ports between 8 active port-channel devices and 16 active port-channel devices? § v. PC peer side load-balancing is LOCAL to the peer § Each v. PC peer has only 8 active links, but the pair has 16 active load balanced links to the downstream device supporting 16 active ports § D-series N 7000 line cards will also support 16 way active port -channel load balancing, providing for a potential 32 way v. PC port channel! © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential Nexus 7000 16 -port-channel Nexus 5000 16 -port-channel support introduced in 4. 1(3)N 1(1 a) release 23
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 24
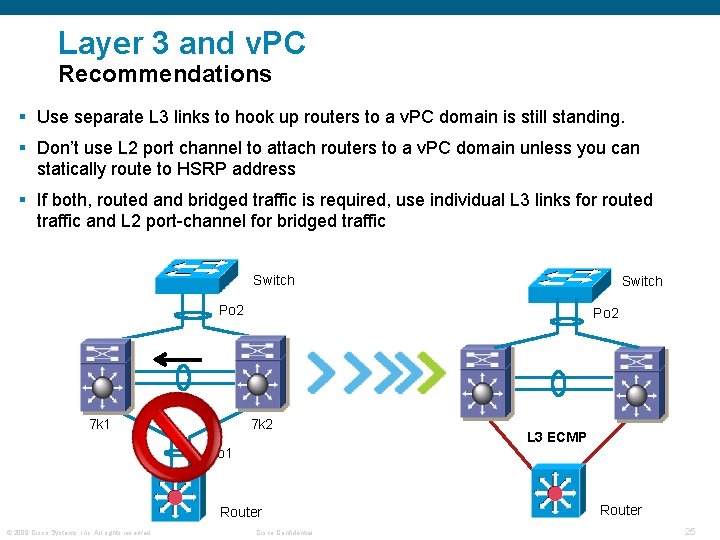
Layer 3 and v. PC Recommendations § Use separate L 3 links to hook up routers to a v. PC domain is still standing. § Don’t use L 2 port channel to attach routers to a v. PC domain unless you can statically route to HSRP address § If both, routed and bridged traffic is required, use individual L 3 links for routed traffic and L 2 port-channel for bridged traffic Switch Po 2 7 k 1 Po 2 7 k 2 L 3 ECMP Po 1 Router © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential Router 25
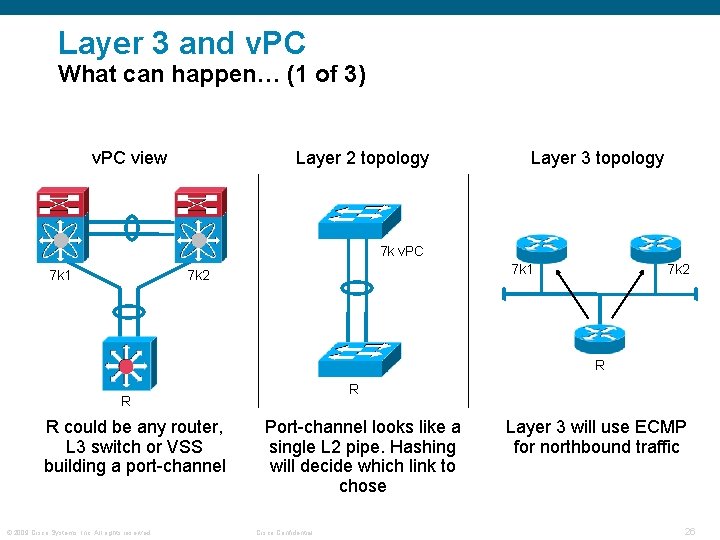
Layer 3 and v. PC What can happen… (1 of 3) v. PC view Layer 2 topology Layer 3 topology 7 k v. PC 7 k 1 7 k 2 R R could be any router, L 3 switch or VSS building a port-channel © 2009 Cisco Systems, Inc. All rights reserved. Port-channel looks like a single L 2 pipe. Hashing will decide which link to chose Cisco Confidential Layer 3 will use ECMP for northbound traffic 26
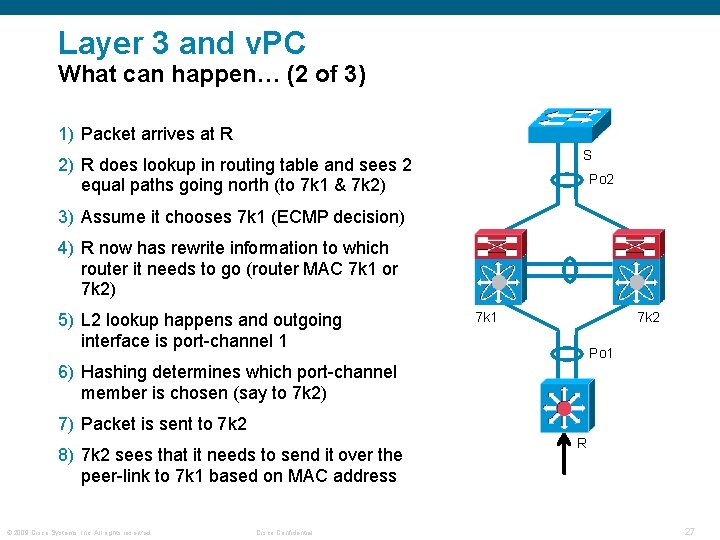
Layer 3 and v. PC What can happen… (2 of 3) 1) Packet arrives at R S 2) R does lookup in routing table and sees 2 equal paths going north (to 7 k 1 & 7 k 2) Po 2 3) Assume it chooses 7 k 1 (ECMP decision) 4) R now has rewrite information to which router it needs to go (router MAC 7 k 1 or 7 k 2) 5) L 2 lookup happens and outgoing interface is port-channel 1 7 k 2 Po 1 6) Hashing determines which port-channel member is chosen (say to 7 k 2) 7) Packet is sent to 7 k 2 8) 7 k 2 sees that it needs to send it over the peer-link to 7 k 1 based on MAC address © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential R 27
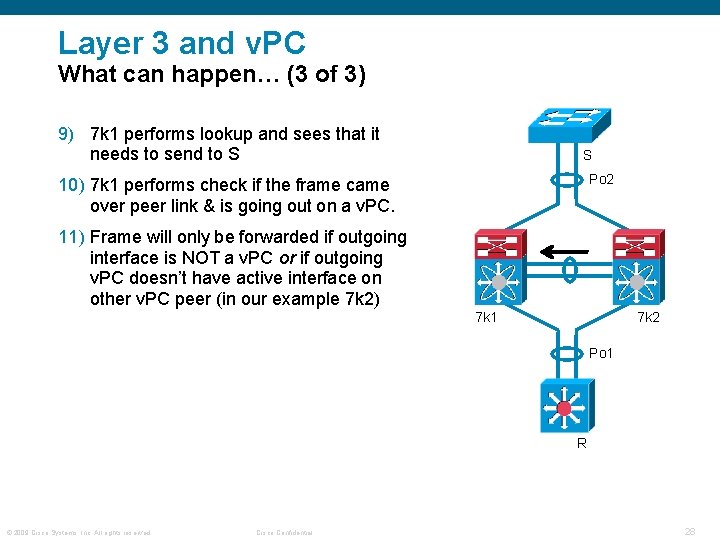
Layer 3 and v. PC What can happen… (3 of 3) 9) 7 k 1 performs lookup and sees that it needs to send to S S Po 2 10) 7 k 1 performs check if the frame came over peer link & is going out on a v. PC. 11) Frame will only be forwarded if outgoing interface is NOT a v. PC or if outgoing v. PC doesn’t have active interface on other v. PC peer (in our example 7 k 2) 7 k 1 7 k 2 Po 1 R © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 28
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 29
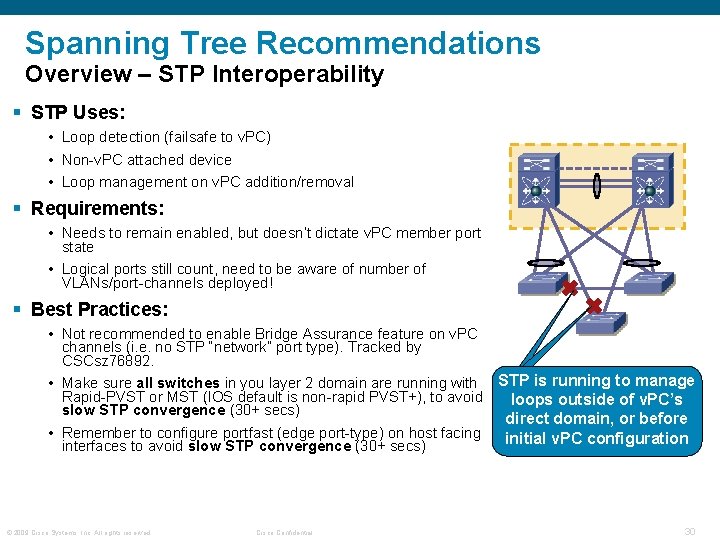
Spanning Tree Recommendations Overview – STP Interoperability § STP Uses: • Loop detection (failsafe to v. PC) • Non-v. PC attached device • Loop management on v. PC addition/removal § Requirements: • Needs to remain enabled, but doesn’t dictate v. PC member port state • Logical ports still count, need to be aware of number of VLANs/port-channels deployed! § Best Practices: • Not recommended to enable Bridge Assurance feature on v. PC channels (i. e. no STP “network” port type). Tracked by CSCsz 76892. v. PC • Make sure all switches in you layer 2 domain are running with STP is running to manage Rapid-PVST or MST (IOS default is non-rapid PVST+), to avoid loops outside of v. PC’s slow STP convergence (30+ secs) direct domain, or before • Remember to configure portfast (edge port-type) on host facing initial v. PC configuration interfaces to avoid slow STP convergence (30+ secs) © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 30
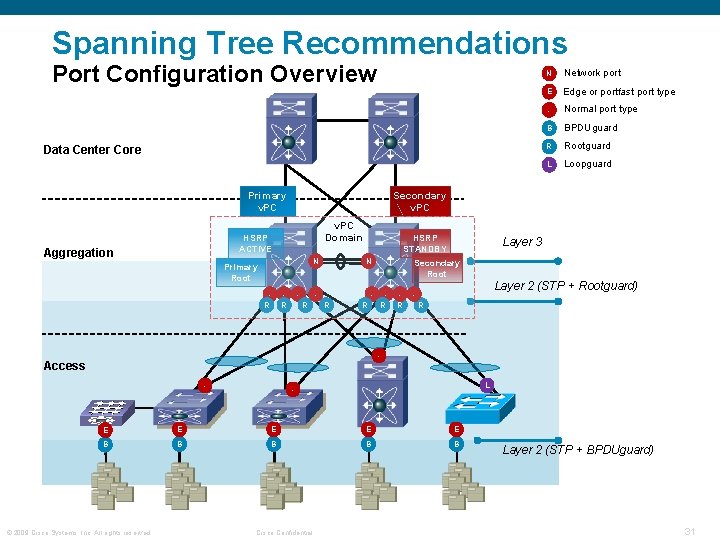
Spanning Tree Recommendations Port Configuration Overview Data Center Core Primary v. PC Domain Primary Root R Network port E Edge or portfast port type - Normal port type B BPDUguard R Rootguard L Loopguard Secondary v. PC HSRP ACTIVE Aggregation N R R HSRP STANDBY N N - R R Layer 3 Secondary Root R R Layer 2 (STP + Rootguard) R - Access - L - E E E B B B © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential Layer 2 (STP + BPDUguard) 31
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 32
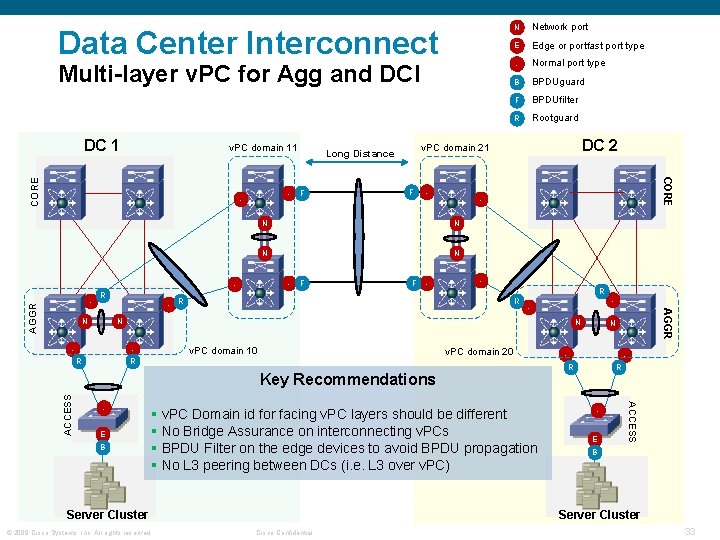
Data Center Interconnect Multi-layer v. PC for Agg and DCI DC 1 - - R - - Normal port type B BPDUguard F BPDUfilter R Rootguard DC 2 N N N F Edge or portfast port type F - R R - N N - N R R v. PC domain 10 v. PC domain 20 E B § v. PC Domain id for facing v. PC layers should be different § No Bridge Assurance on interconnecting v. PCs § BPDU Filter on the edge devices to avoid BPDU propagation § No L 3 peering between DCs (i. e. L 3 over v. PC) Server Cluster © 2009 Cisco Systems, Inc. All rights reserved. N - R R E ACCESS Key Recommendations - AGGR - F N - - E v. PC domain 21 Long Distance F Network port CORE v. PC domain 11 N B Server Cluster Cisco Confidential 33
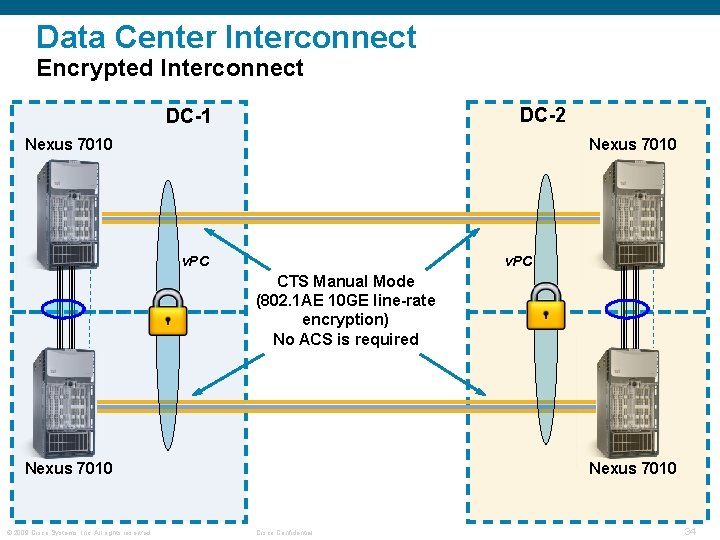
Data Center Interconnect Encrypted Interconnect DC-2 DC-1 Nexus 7010 v. PC CTS Manual Mode (802. 1 AE 10 GE line-rate encryption) No ACS is required Nexus 7010 © 2009 Cisco Systems, Inc. All rights reserved. Nexus 7010 Cisco Confidential 34
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 35
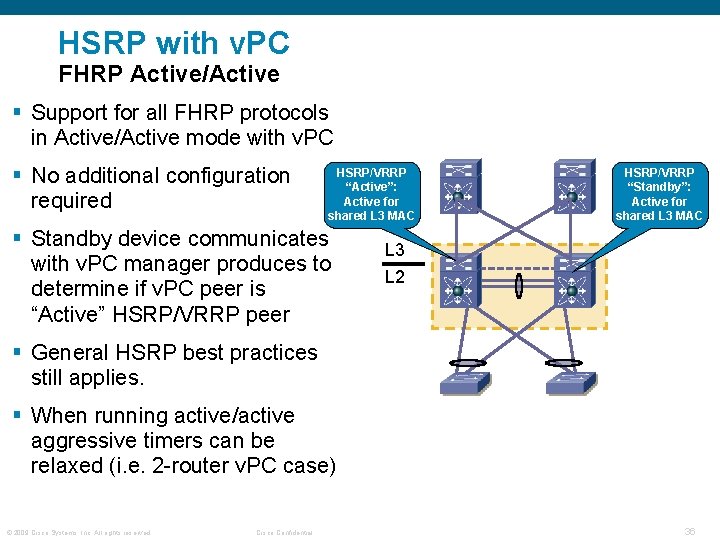
HSRP with v. PC FHRP Active/Active § Support for all FHRP protocols in Active/Active mode with v. PC § No additional configuration required HSRP/VRRP “Active”: Active for shared L 3 MAC § Standby device communicates with v. PC manager produces to determine if v. PC peer is “Active” HSRP/VRRP peer HSRP/VRRP “Standby”: Active for shared L 3 MAC L 3 L 2 § General HSRP best practices still applies. § When running active/active aggressive timers can be relaxed (i. e. 2 -router v. PC case) © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 36
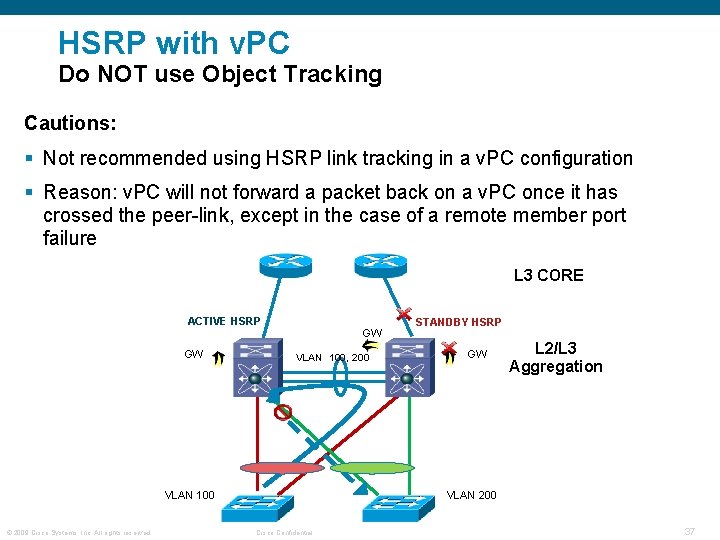
HSRP with v. PC Do NOT use Object Tracking Cautions: § Not recommended using HSRP link tracking in a v. PC configuration § Reason: v. PC will not forward a packet back on a v. PC once it has crossed the peer-link, except in the case of a remote member port failure L 3 CORE ACTIVE HSRP GW GW VLAN 100, 200 VLAN 100 © 2009 Cisco Systems, Inc. All rights reserved. STANDBY HSRP GW L 2/L 3 Aggregation VLAN 200 Cisco Confidential 37
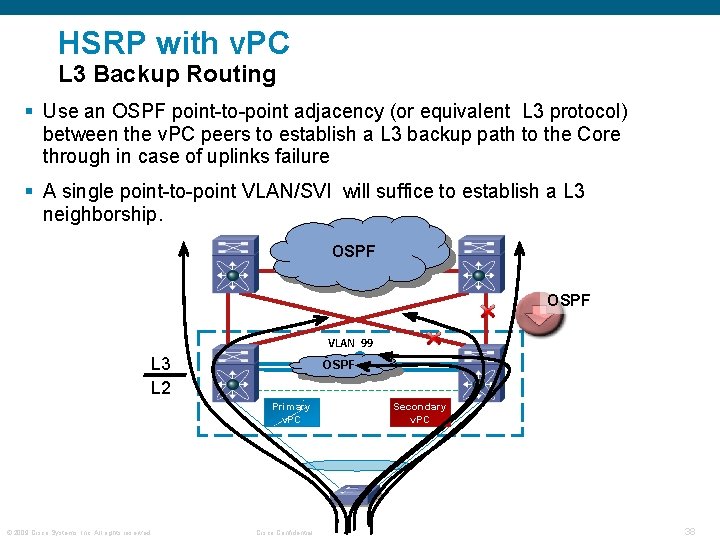
HSRP with v. PC L 3 Backup Routing § Use an OSPF point-to-point adjacency (or equivalent L 3 protocol) between the v. PC peers to establish a L 3 backup path to the Core through in case of uplinks failure § A single point-to-point VLAN/SVI will suffice to establish a L 3 neighborship. OSPF VLAN 99 L 3 L 2 OSPF Primary v. PC © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential Secondary v. PC 38
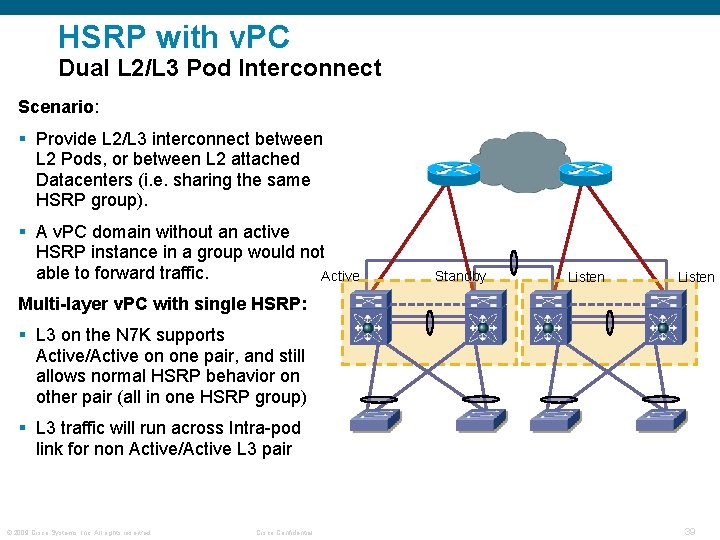
HSRP with v. PC Dual L 2/L 3 Pod Interconnect Scenario: § Provide L 2/L 3 interconnect between L 2 Pods, or between L 2 attached Datacenters (i. e. sharing the same HSRP group). § A v. PC domain without an active HSRP instance in a group would not able to forward traffic. Active Standby Listen Multi-layer v. PC with single HSRP: § L 3 on the N 7 K supports Active/Active on one pair, and still allows normal HSRP behavior on other pair (all in one HSRP group) § L 3 traffic will run across Intra-pod link for non Active/Active L 3 pair © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 39
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 40
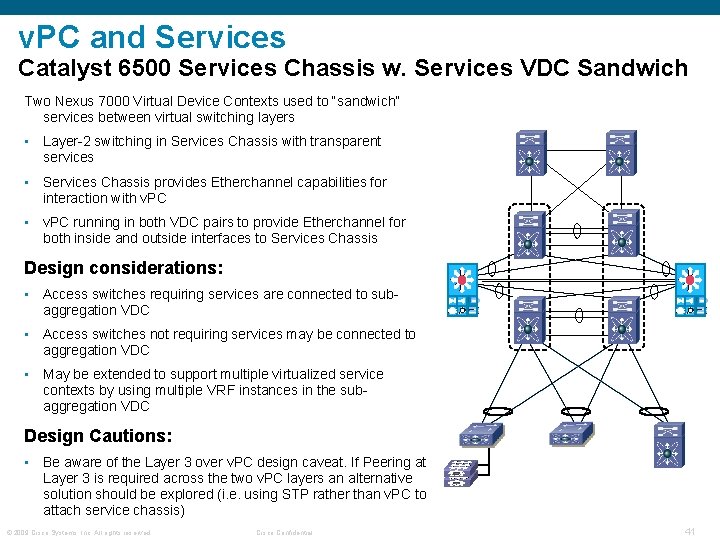
v. PC and Services Catalyst 6500 Services Chassis w. Services VDC Sandwich Two Nexus 7000 Virtual Device Contexts used to “sandwich” services between virtual switching layers • Layer-2 switching in Services Chassis with transparent services • Services Chassis provides Etherchannel capabilities for interaction with v. PC • v. PC running in both VDC pairs to provide Etherchannel for both inside and outside interfaces to Services Chassis Design considerations: • Access switches requiring services are connected to subaggregation VDC • Access switches not requiring services may be connected to aggregation VDC • May be extended to support multiple virtualized service contexts by using multiple VRF instances in the subaggregation VDC Design Cautions: • Be aware of the Layer 3 over v. PC design caveat. If Peering at Layer 3 is required across the two v. PC layers an alternative solution should be explored (i. e. using STP rather than v. PC to attach service chassis) © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 41
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 42
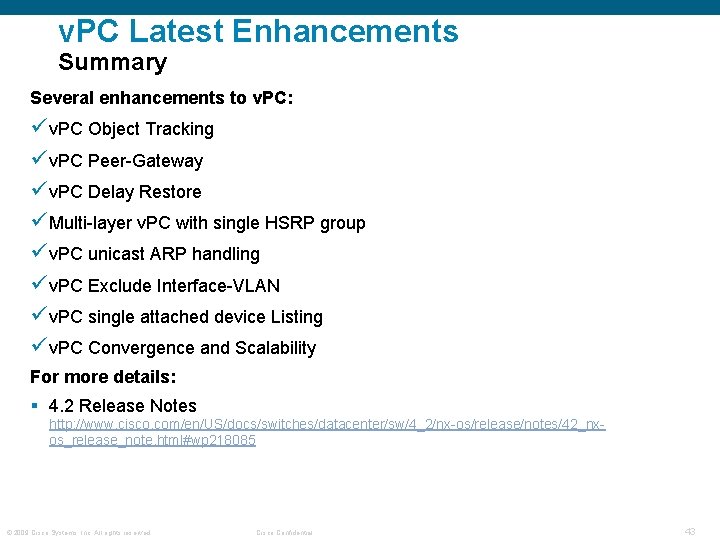
v. PC Latest Enhancements Summary Several enhancements to v. PC: ü v. PC Object Tracking ü v. PC Peer-Gateway ü v. PC Delay Restore ü Multi-layer v. PC with single HSRP group ü v. PC unicast ARP handling ü v. PC Exclude Interface-VLAN ü v. PC single attached device Listing ü v. PC Convergence and Scalability For more details: § 4. 2 Release Notes http: //www. cisco. com/en/US/docs/switches/datacenter/sw/4_2/nx-os/release/notes/42_nxos_release_note. html#wp 218085 © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 43
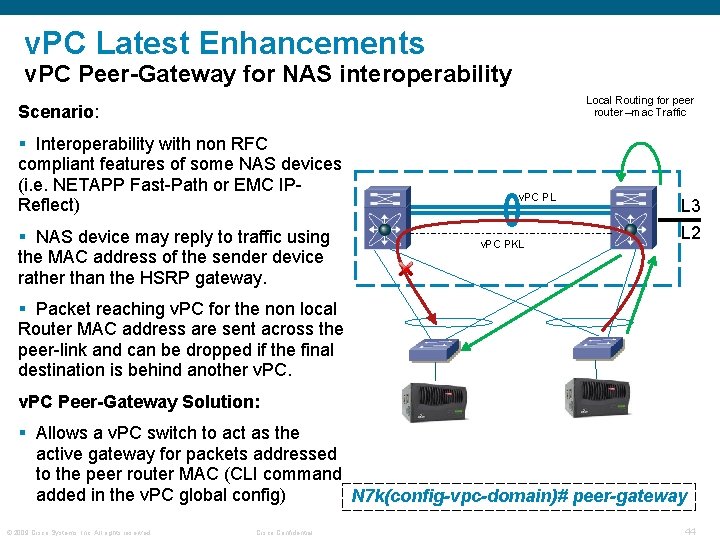
v. PC Latest Enhancements v. PC Peer-Gateway for NAS interoperability Local Routing for peer router –mac Traffic Scenario: § Interoperability with non RFC compliant features of some NAS devices (i. e. NETAPP Fast-Path or EMC IPReflect) § NAS device may reply to traffic using the MAC address of the sender device rather than the HSRP gateway. v. PC PL v. PC PKL L 3 L 2 § Packet reaching v. PC for the non local Router MAC address are sent across the peer-link and can be dropped if the final destination is behind another v. PC Peer-Gateway Solution: § Allows a v. PC switch to act as the active gateway for packets addressed to the peer router MAC (CLI command added in the v. PC global config) N 7 k(config-vpc-domain)# peer-gateway © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 44
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 45
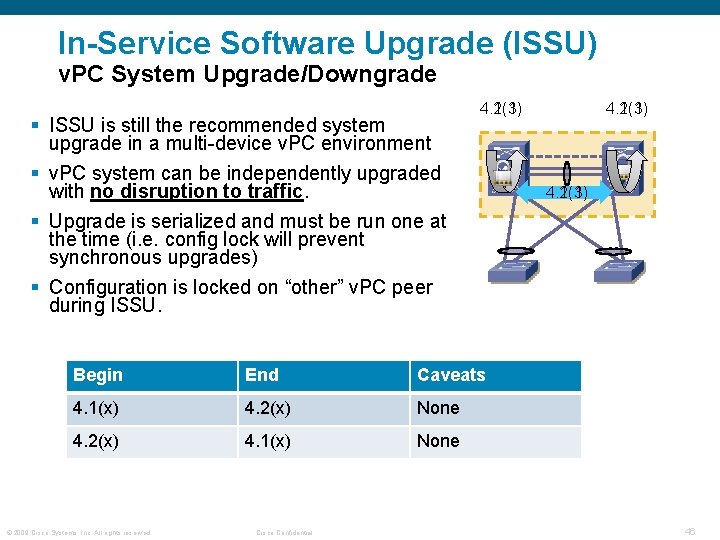
In-Service Software Upgrade (ISSU) v. PC System Upgrade/Downgrade § ISSU is still the recommended system upgrade in a multi-device v. PC environment § v. PC system can be independently upgraded with no disruption to traffic. § Upgrade is serialized and must be run one at the time (i. e. config lock will prevent synchronous upgrades) § Configuration is locked on “other” v. PC peer during ISSU. 4. 1(3) 4. 2(1) Begin End Caveats 4. 1(x) 4. 2(x) None 4. 2(x) 4. 1(x) None © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 4. 1(3) 4. 2(1) 46
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 47
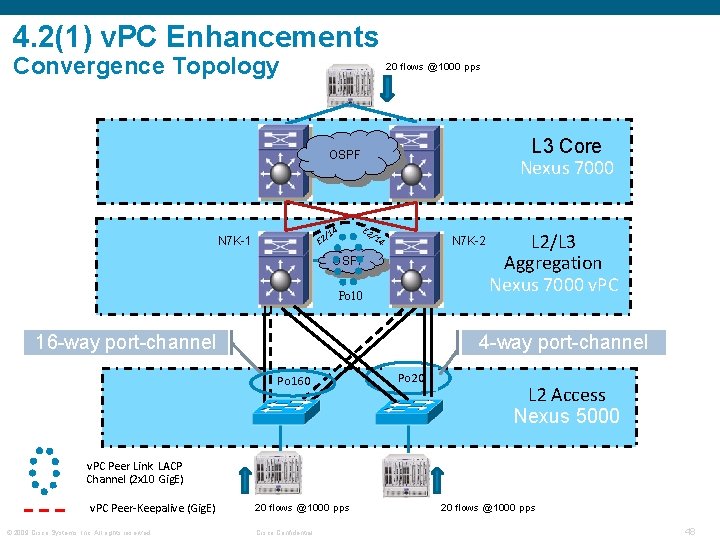
4. 2(1) v. PC Enhancements Convergence Topology 20 flows @1000 pps L 3 Core Nexus 7000 OSPF E 2 4 /1 /1 E 2 N 7 K-1 4 N 7 K-2 OSPF Po 10 16 -way port-channel L 2/L 3 Aggregation Nexus 7000 v. PC 4 -way port-channel Po 160 Po 20 L 2 Access Nexus 5000 v. PC Peer Link LACP Channel (2 x 10 Gig. E) v. PC Peer-Keepalive (Gig. E) © 2009 Cisco Systems, Inc. All rights reserved. 20 flows @1000 pps Cisco Confidential 20 flows @1000 pps 48
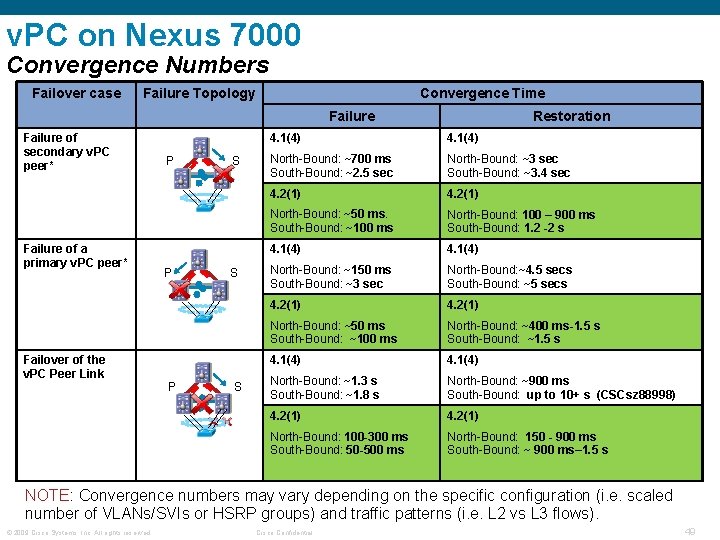
v. PC on Nexus 7000 Convergence Numbers Failover case Failure Topology Convergence Time Failure of secondary v. PC peer* Failure of a primary v. PC peer* Failover of the v. PC Peer Link P P P S S S Restoration 4. 1(4) North-Bound: ~700 ms South-Bound: ~2. 5 sec North-Bound: ~3 sec South-Bound: ~3. 4 sec 4. 2(1) North-Bound: ~50 ms. South-Bound: ~100 ms North-Bound: 100 – 900 ms South-Bound: 1. 2 -2 s 4. 1(4) North-Bound: ~150 ms South-Bound: ~3 sec North-Bound: ~4. 5 secs South-Bound: ~5 secs 4. 2(1) North-Bound: ~50 ms South-Bound: ~100 ms North-Bound: ~400 ms-1. 5 s South-Bound: ~1. 5 s 4. 1(4) North-Bound: ~1. 3 s South-Bound: ~1. 8 s North-Bound: ~900 ms South-Bound: up to 10+ s (CSCsz 88998) 4. 2(1) North-Bound: 100 -300 ms South-Bound: 50 -500 ms North-Bound: 150 - 900 ms South-Bound: ~ 900 ms– 1. 5 s NOTE: Convergence numbers may vary depending on the specific configuration (i. e. scaled number of VLANs/SVIs or HSRP groups) and traffic patterns (i. e. L 2 vs L 3 flows). © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 49
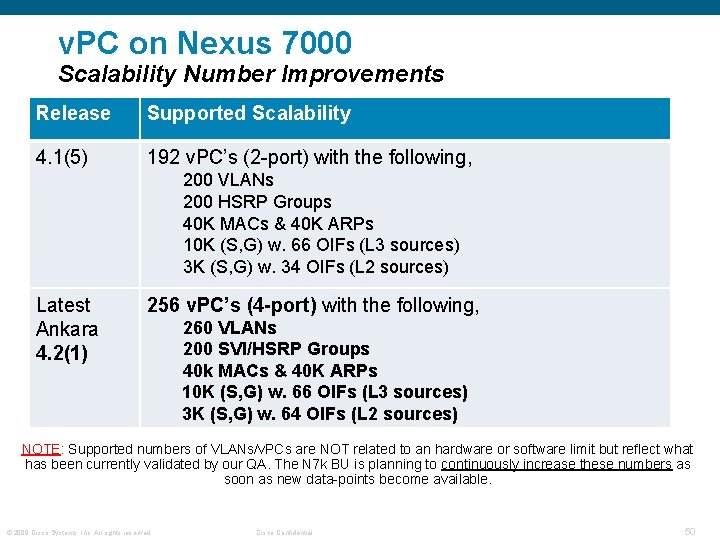
v. PC on Nexus 7000 Scalability Number Improvements Release Supported Scalability 4. 1(5) 192 v. PC’s (2 -port) with the following, 200 VLANs 200 HSRP Groups 40 K MACs & 40 K ARPs 10 K (S, G) w. 66 OIFs (L 3 sources) 3 K (S, G) w. 34 OIFs (L 2 sources) Latest Ankara 4. 2(1) 256 v. PC’s (4 -port) with the following, 260 VLANs 200 SVI/HSRP Groups 40 k MACs & 40 K ARPs 10 K (S, G) w. 66 OIFs (L 3 sources) 3 K (S, G) w. 64 OIFs (L 2 sources) NOTE: Supported numbers of VLANs/v. PCs are NOT related to an hardware or software limit but reflect what has been currently validated by our QA. The N 7 k BU is planning to continuously increase these numbers as soon as new data-points become available. © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 50
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 51
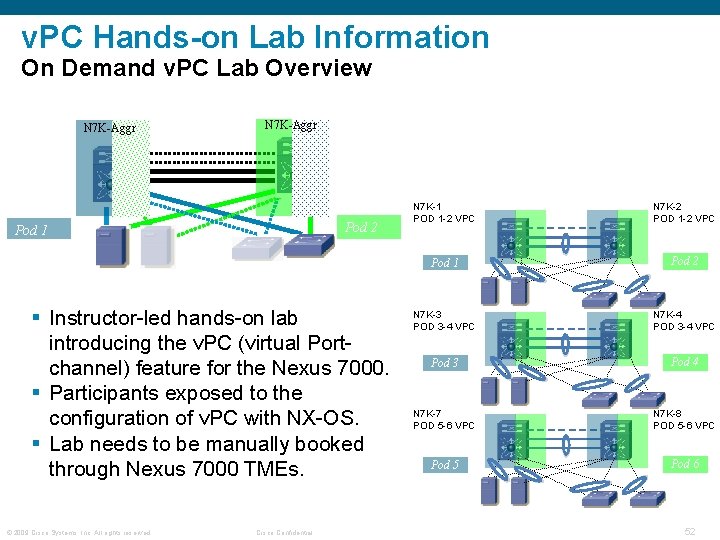
v. PC Hands-on Lab Information On Demand v. PC Lab Overview N 7 K-Aggr Pod 2 Pod 1 § Instructor-led hands-on lab introducing the v. PC (virtual Portchannel) feature for the Nexus 7000. § Participants exposed to the configuration of v. PC with NX-OS. § Lab needs to be manually booked through Nexus 7000 TMEs. © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential N 7 K-1 POD 1 -2 VPC N 7 K-2 POD 1 -2 VPC Pod 1 Pod 2 N 7 K-3 POD 3 -4 VPC N 7 K-4 POD 3 -4 VPC Pod 3 Pod 4 N 7 K-7 POD 5 -6 VPC N 7 K-8 POD 5 -6 VPC Pod 5 Pod 6 52
v. PC Hands-on Lab Information v. PC Lab Logistics and Timing § The v. PC Laboratory consists of 6 independent PODs. § A group of 2 students is assigned to each Pod. § Each student will configure a v. PC peer device. § PODs are logically independent. Two adjacent PODs are physically bound to the same Nexus. Virtual Device Contexts (VDCs) are used to define logically independent devices on the same Nexus 7010 box. § The v. PC Lab session is expected to be completed in around two hours. © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 53
Agenda § Feature Overview & Terminology § v. PC Design Guidance & Best Practices üBuilding a v. PC domain üAttaching to a v. PC domain üLayer 3 and v. PC üSpanning Tree Recommendations üData Center Interconnect (& Encryption) üHSRP with v. PC üv. PC and Services üv. PC latest enhancements üISSU § Convergence and Scalability § v. PC Hands-on Lab Information § Reference Material © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 54
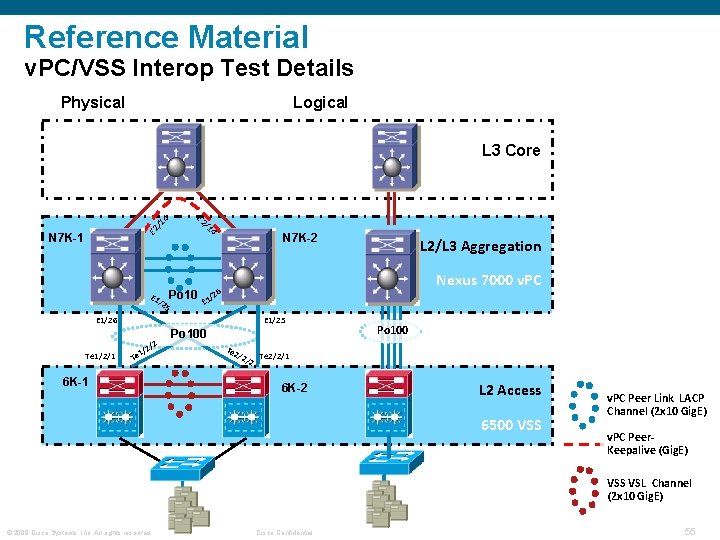
Reference Material v. PC/VSS Interop Test Details Physical Logical E 2 / 14 L 3 Core N 7 K-1 E 1 /2 5 Po 10 /1 4 N 7 K-2 Nexus 7000 v. PC 6 /2 E 1/26 Te 1/2/1 E 1/25 2 1/ Te /2 6 K-1 L 2/L 3 Aggregation Po 100 Te 2 /2/ 2 Po 100 Te 2/2/1 6 K-2 L 2 Access 6500 VSS v. PC Peer Link LACP Channel (2 x 10 Gig. E) v. PC Peer. Keepalive (Gig. E) VSS VSL Channel (2 x 10 Gig. E) © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 55
Reference Material v. PC/VSS Interop Test Details § The following scenarios were tested: • VSS and v. PC member failover and convergence • Dual active scenarios and behavior • Best practice guidelines for STP, L 3 (NSF), Multicast § Catalyst 6500/Nexus 7000 interoperability: • Multiple ports per chassis act as one larger ether-channel © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 56
Reference Material Other Solution Tests and Recent v. PC Documentation § Enterprise Solutions Engineering: http: //www. cisco. com/en/US/docs/solutions/Enterprise/Data_Center/DC_3_0/DC-3_0_IPInfra. html § Implementing Nexus 7000 in the Data Center Aggregation Layer with Services: https: //www. cisco. com/en/US/docs/solutions/Enterprise/Data_Center/nx_7000_dc. html § Configuration Guide for Object Tracking Feature: http: //www. cisco. com/en/US/partner/docs/switches/datacenter/sw/4_2/nxos/interfaces/configuration/guide/if_v. PC. html#wp 1530133 § v. PC white Paper: http: //www. cisco. com/en/US/prod/collateral/switches/ps 9441/ps 9402/white_paper_c 11516396. html © 2009 Cisco Systems, Inc. All rights reserved. Cisco Confidential 57

- Slides: 56