QRadar Tuning Overview and Best Practices Sterling Jones
QRadar Tuning Overview and Best Practices Sterling Jones North America Security Intelligence Tech Lead

Contents • Data Sources • Prime Data Sources • Terminology • Events, Alerts & Offenses • What to Tune • Tuning Report • How to Tune 1. Environment 2. Rules 3. False Positive • Maintenance Best Practices
Data Sources Data Overload – here’s why

Data Sources Where to start • • • • Antimalware Antispam/Email Gateway Security Antivirus Application & Network Acceleration, Packet Shaping Encryption Management (At rest, in Motion, WDE, Removable & Mobile Device) Forward Proxy / Egress Filtering / Web Security Host Intrusion Prevention Identity Management / Two-Factor Authentication Information Leak Protection Inventory & Configuration Management Solution IP Address Management Load Balancing / Network Performance Monitoring Network Access Control Network Anomaly Detection/IDS • • • • Network Firewall Network Intrusion Prevention System Networking Infrastructure / Switches, Routers, APs PKI, Public Key Infrastructure and Cross Platform Certificate Management Privileged Identity Management Secure DNS/SHCP Secure File Transfer System Secure Instant Messaging, Collaboration Software Distribution / Patch Management Virtualization & Cloud Management VPN Access System Vulnerability Management Web Application Firewall Web Application Scanner Wireless Controllers Wireless Intrusion Prevention
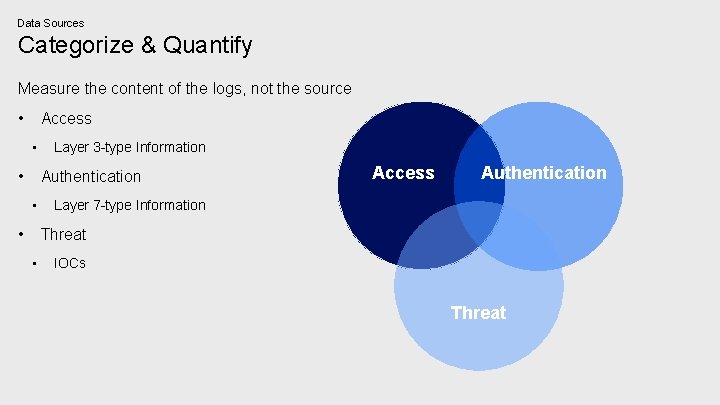
Data Sources Categorize & Quantify Measure the content of the logs, not the source • Access • • Layer 3 -type Information Authentication • • Access Authentication Layer 7 -type Information Threat • IOCs Threat
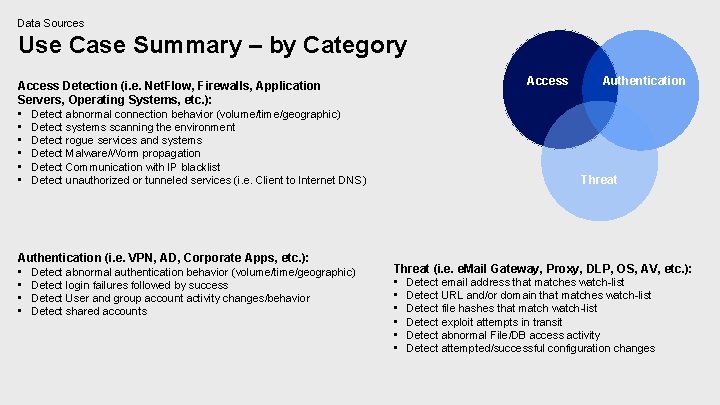
Data Sources Use Case Summary – by Category Access Detection (i. e. Net. Flow, Firewalls, Application Servers, Operating Systems, etc. ): • Detect abnormal connection behavior (volume/time/geographic) • Detect systems scanning the environment • Detect rogue services and systems • Detect Malware/Worm propagation • Detect Communication with IP blacklist • Detect unauthorized or tunneled services (i. e. Client to Internet DNS) Access Authentication Threat Authentication (i. e. VPN, AD, Corporate Apps, etc. ): • Detect abnormal authentication behavior (volume/time/geographic) • Detect login failures followed by success • Detect User and group account activity changes/behavior • Detect shared accounts Threat (i. e. e. Mail Gateway, Proxy, DLP, OS, AV, etc. ): • Detect email address that matches watch-list • Detect URL and/or domain that matches watch-list • Detect file hashes that match watch-list • Detect exploit attempts in transit • Detect abnormal File/DB access activity • Detect attempted/successful configuration changes
Terminology Logical Data Flow
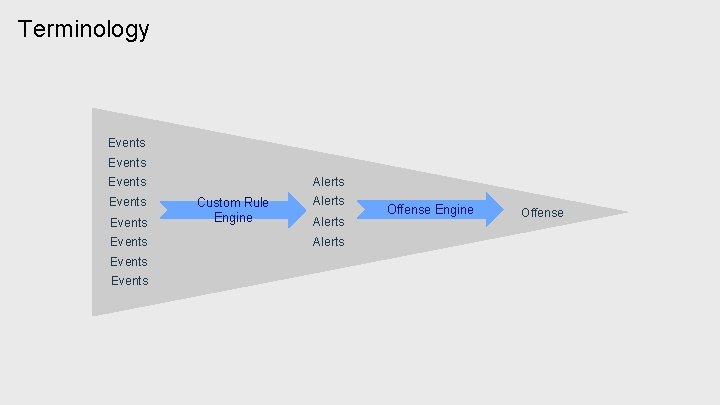
Terminology Events Alerts Events Events Custom Rule Engine Alerts Offense Engine Offense
Where to Start What to Tune
Where to Start Not Here
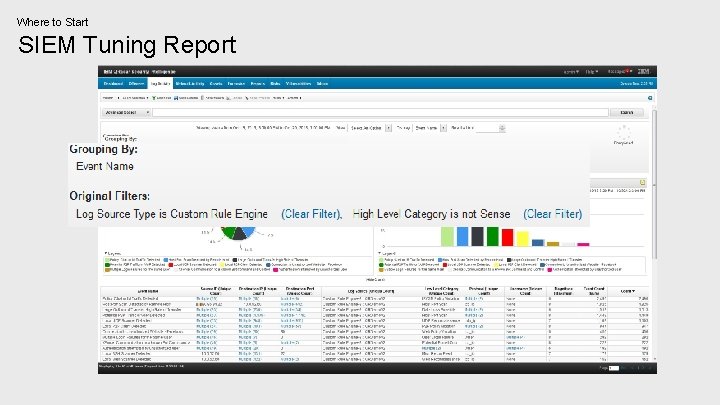
Where to Start SIEM Tuning Report
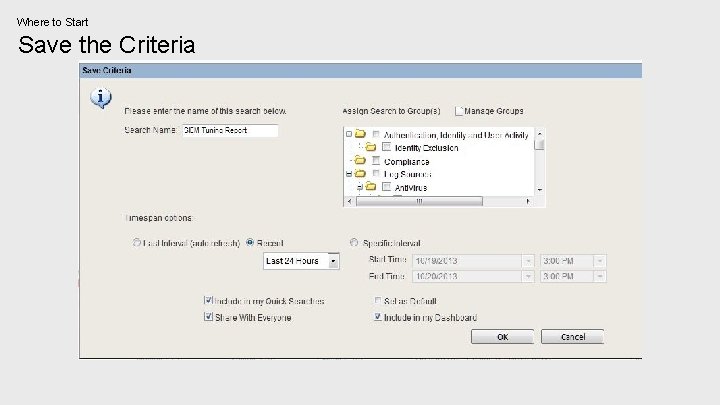
Where to Start Save the Criteria
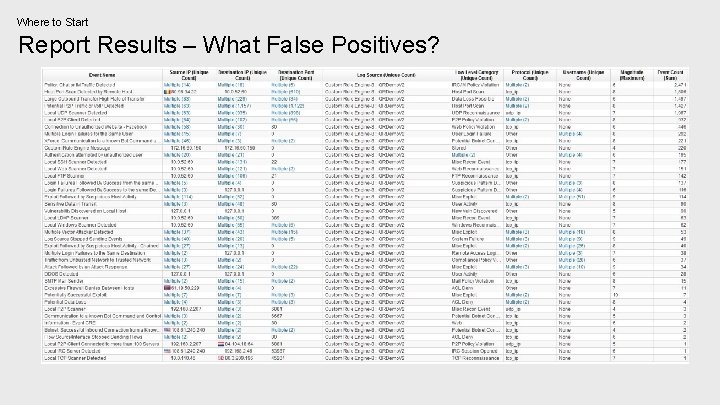
Where to Start Report Results – What False Positives?

Tuning How to Tune
Tuning Three Step Process 1. 2. 3. Define Your Environment Modify the Rules False Positive
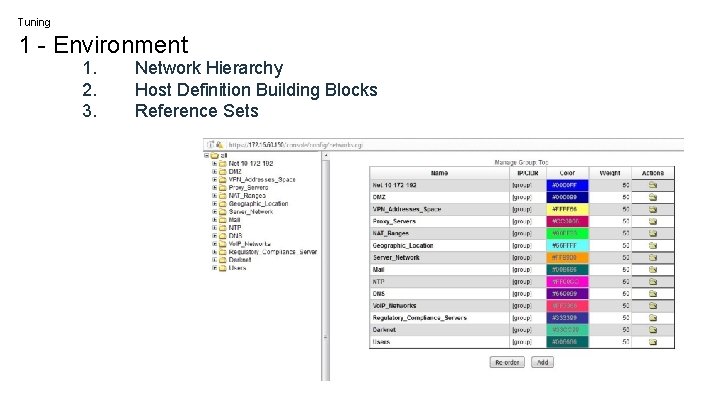
Tuning 1 - Environment 1. 2. 3. Network Hierarchy Host Definition Building Blocks Reference Sets
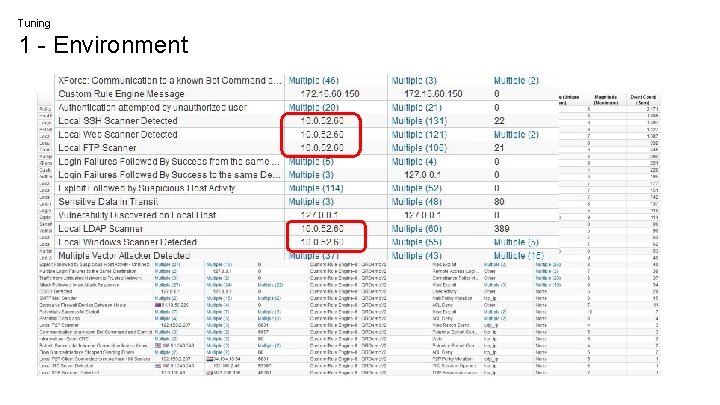
Tuning 1 - Environment
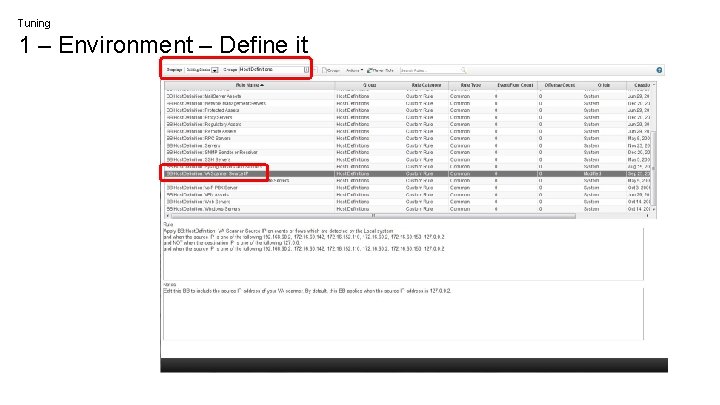
Tuning 1 – Environment – Define it
Tuning 2 - Rules 1. 2. 3. Add/Remove Tests Modify Tests/Thresholds Change the Response
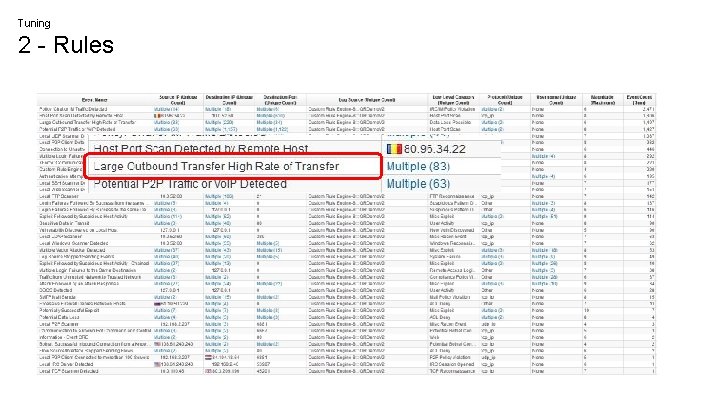
Tuning 2 - Rules
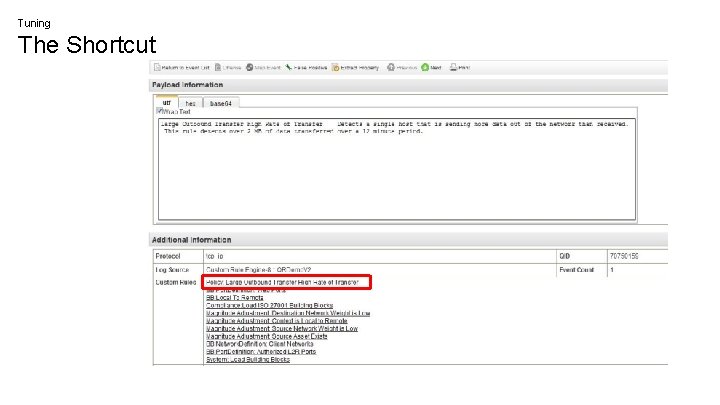
Tuning The Shortcut
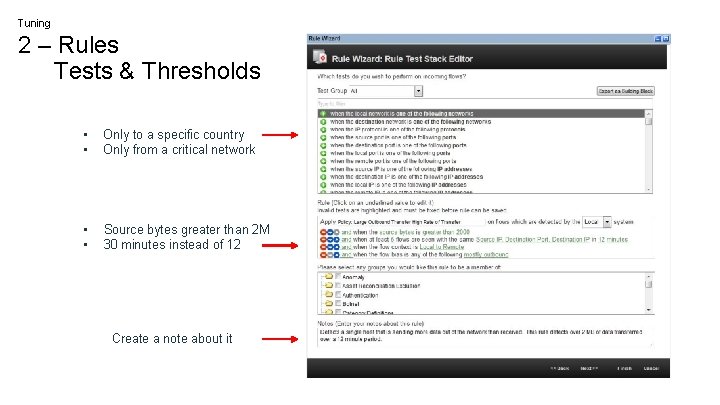
Tuning 2 – Rules Tests & Thresholds • • Only to a specific country Only from a critical network • • Source bytes greater than 2 M 30 minutes instead of 12 Create a note about it
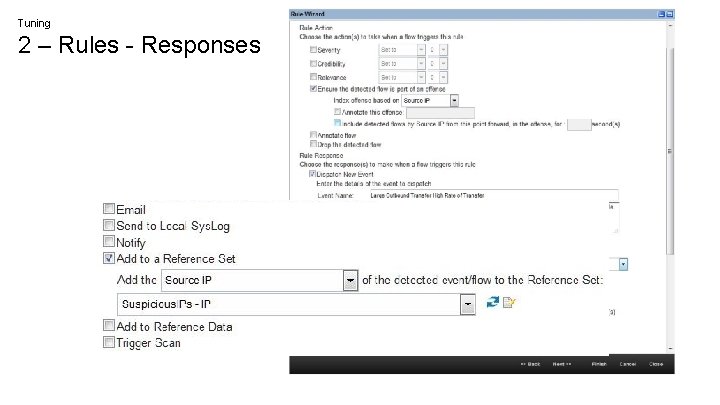
Tuning 2 – Rules - Responses
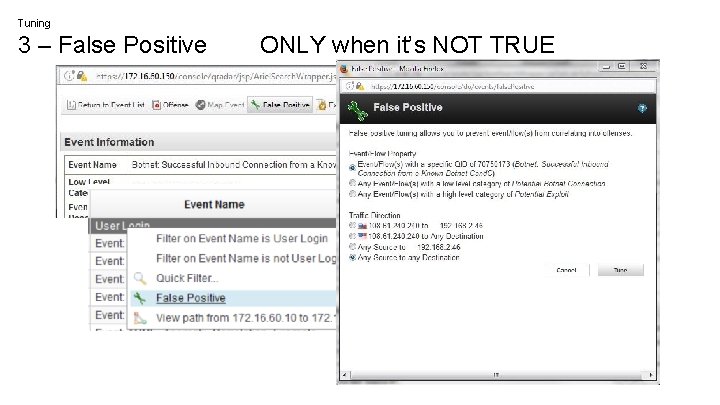
Tuning 3 – False Positive ONLY when it’s NOT TRUE
Maintenance Not a one-time event
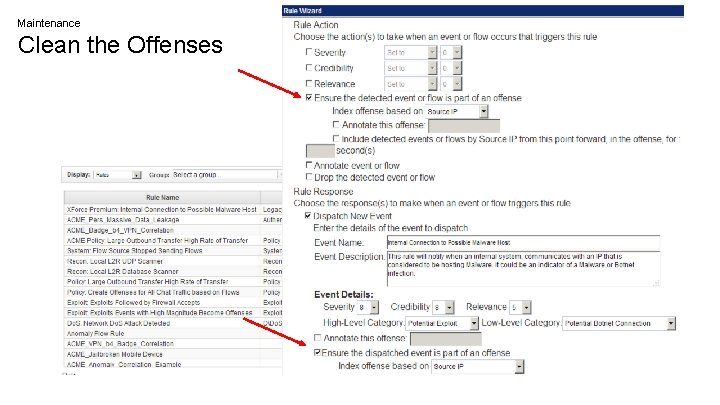
Maintenance Clean the Offenses
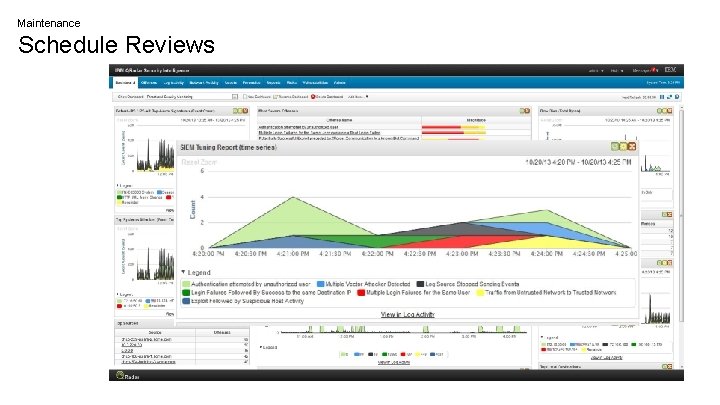
Maintenance Schedule Reviews
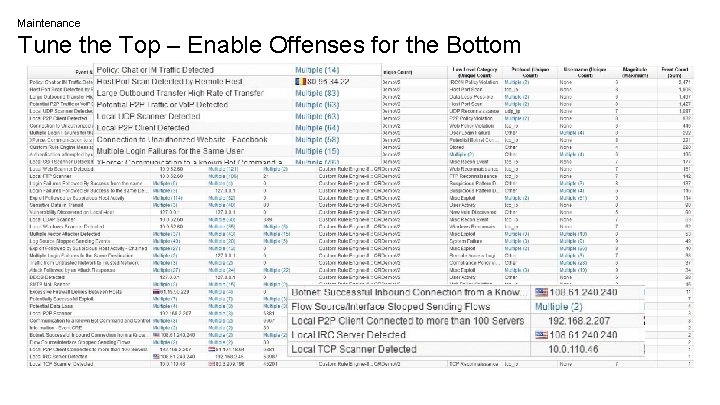
Maintenance Tune the Top – Enable Offenses for the Bottom
In Summary 1. Create Tuning Report 2. Tune busy rules I. Define Your Environment a. b. II. Building Blocks/Reference Sets Define Network Hierarchy Modify Busy Rules 1. 2. 3. Add/Remove Tests Modify Variables & Thresholds Change Reponses III. False Positive 1. ONLY for False Positives 3. Maintenance Best Practices I. II. Clean the Offenses Daily, Weekly, Monthly Monitoring 1. Tune Noisy Rules, Enable Offenses
Thank you Sterling Jones North America Security Intelligence Tech Lead — sterlingj@us. ibm. com +1 -303 -656 -9122
- Slides: 30