How to Register and Login Marjan Kindalov Basics
How to: Register and Login Marjan Kindalov
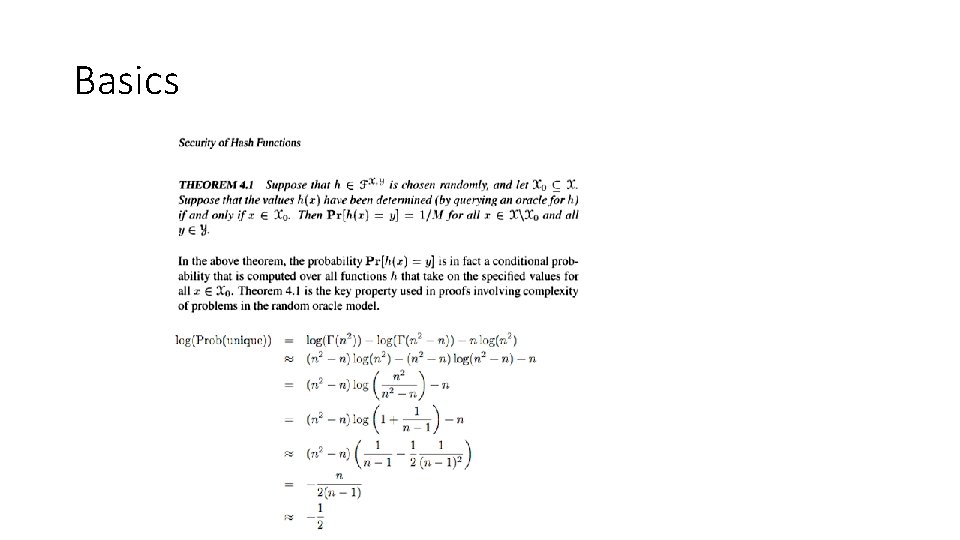
Basics

Registration
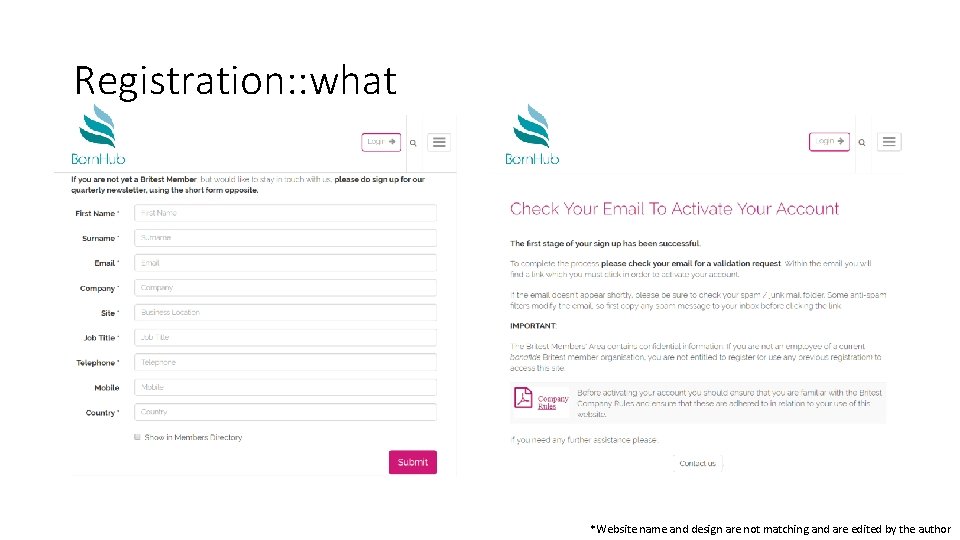
Registration: : what *Website name and design are not matching and are edited by the author
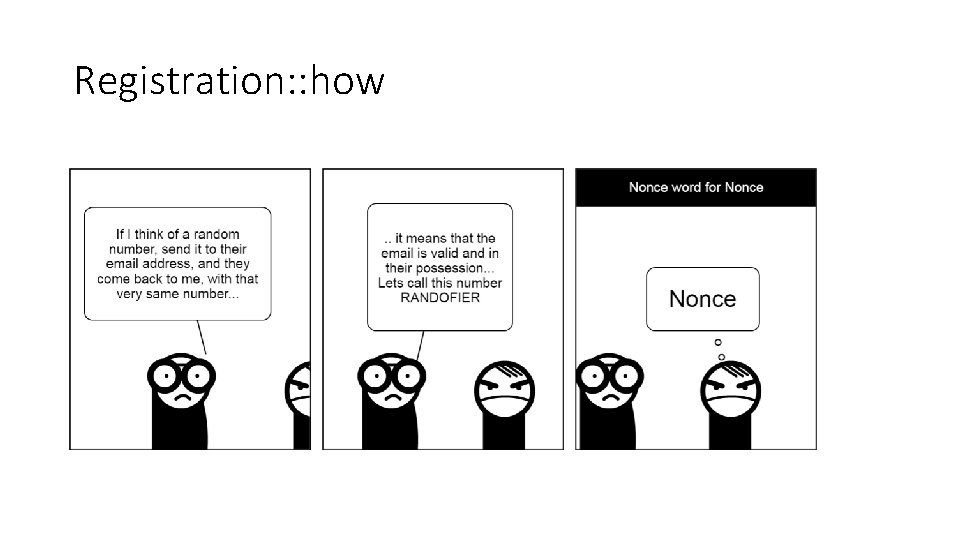
Registration: : how
Registration: : why Forgot password
Enlarge your @#$%!#$#^%#$ in only 7 days By Qwertyxp 2000 - Own work, CC BY-SA 4. 0, https: //commons. wikimedia. org/w/index. php? curid=37340578
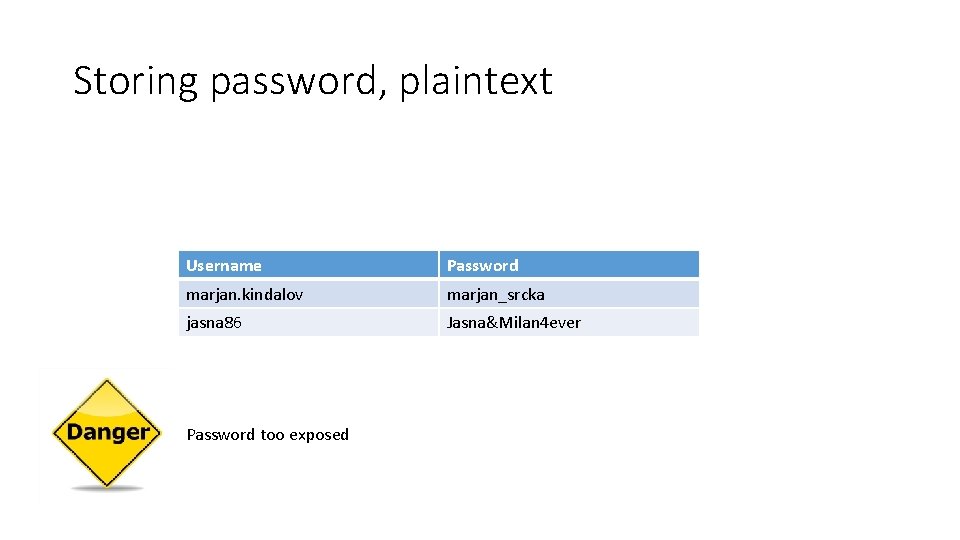
Storing password, plaintext Username Password marjan. kindalov marjan_srcka jasna 86 Jasna&Milan 4 ever Password too exposed
Hash? https: //mulpix. com/post/1021395473011807709. html
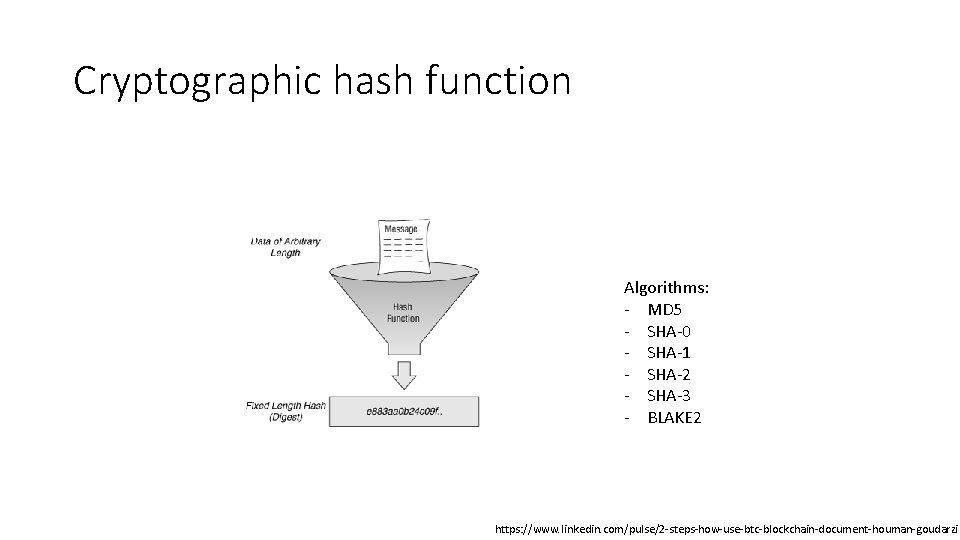
Cryptographic hash function Algorithms: - MD 5 - SHA-0 - SHA-1 - SHA-2 - SHA-3 - BLAKE 2 https: //www. linkedin. com/pulse/2 -steps-how-use-btc-blockchain-document-houman-goudarzi
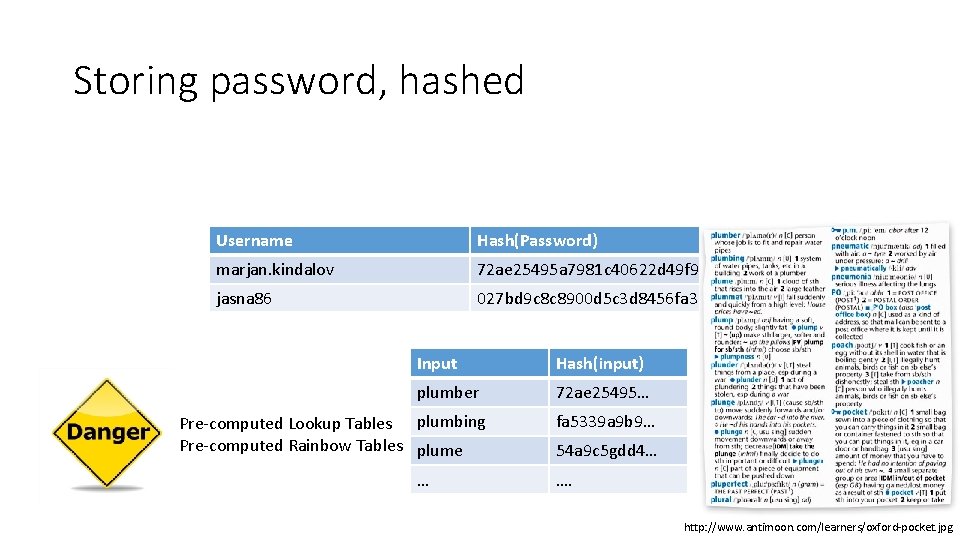
Storing password, hashed Username Hash(Password) marjan. kindalov 72 ae 25495 a 7981 c 40622 d 49 f 9 a jasna 86 027 bd 9 c 8 c 8900 d 5 c 3 d 8456 fa 33 Input Hash(input) plumber 72 ae 25495… Pre-computed Lookup Tables plumbing Pre-computed Rainbow Tables plume … fa 5339 a 9 b 9… 54 a 9 c 5 gdd 4… …. http: //www. antimoon. com/learners/oxford-pocket. jpg

Salt - Salted. Password = Password + Salt - Calculate hash function on Salted. Password - Efectivly longer password -> out of reach of precomputed lookup tables and similar
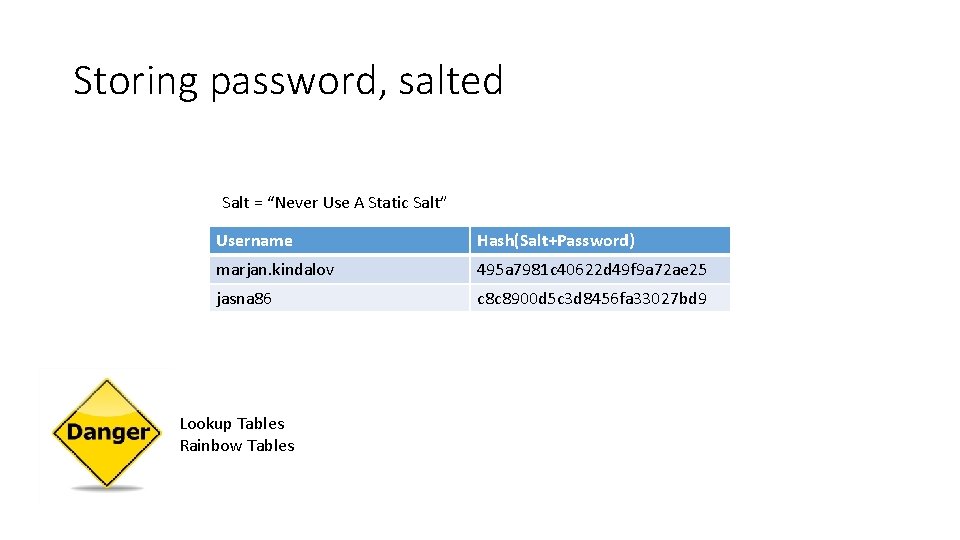
Storing password, salted Salt = “Never Use A Static Salt” Username Hash(Salt+Password) marjan. kindalov 495 a 7981 c 40622 d 49 f 9 a 72 ae 25 jasna 86 c 8 c 8900 d 5 c 3 d 8456 fa 33027 bd 9 Lookup Tables Rainbow Tables
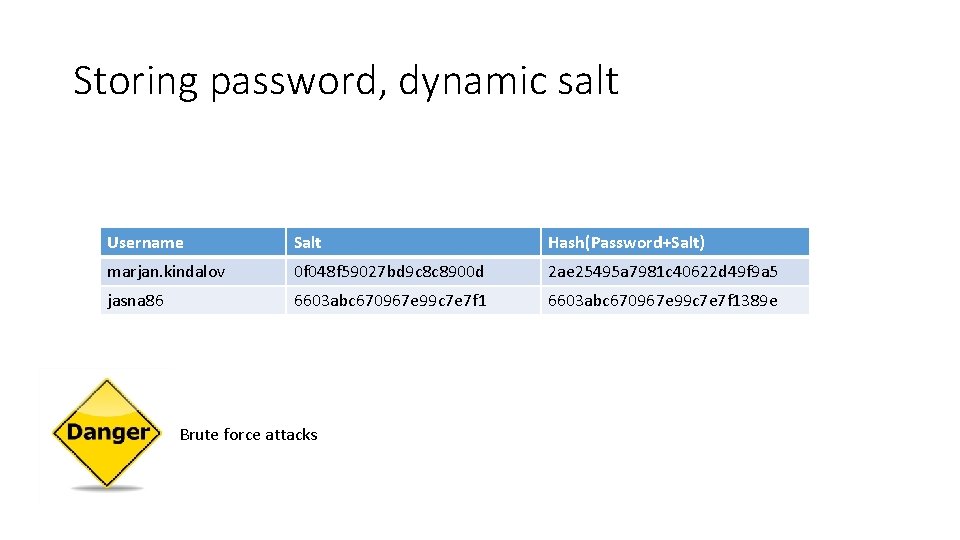
Storing password, dynamic salt Username Salt Hash(Password+Salt) marjan. kindalov 0 f 048 f 59027 bd 9 c 8 c 8900 d 2 ae 25495 a 7981 c 40622 d 49 f 9 a 5 jasna 86 6603 abc 670967 e 99 c 7 e 7 f 1389 e Brute force attacks
Key stretching 100 000 hash/sec 10 000 iterations 10 password/sec
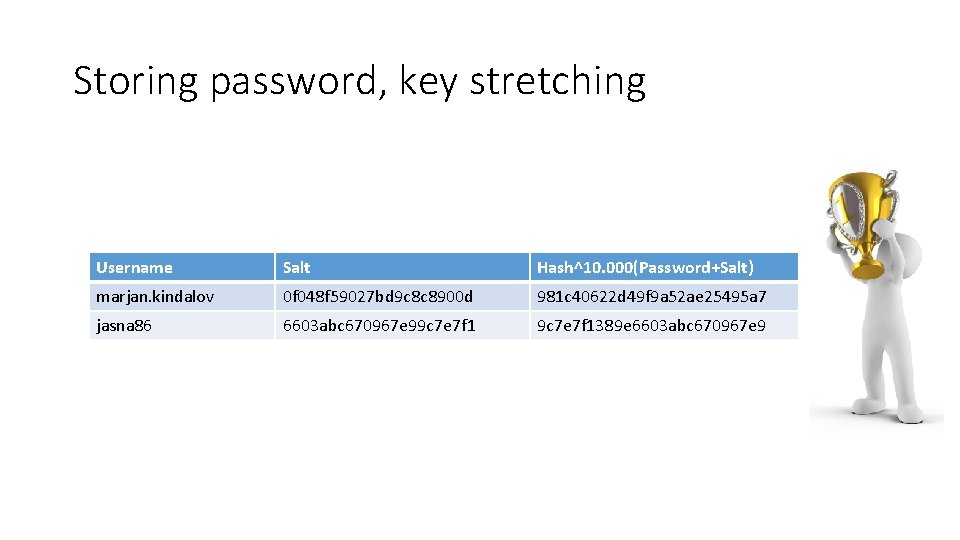
Storing password, key stretching Username Salt Hash^10. 000(Password+Salt) marjan. kindalov 0 f 048 f 59027 bd 9 c 8 c 8900 d 981 c 40622 d 49 f 9 a 52 ae 25495 a 7 jasna 86 6603 abc 670967 e 99 c 7 e 7 f 1389 e 6603 abc 670967 e 9
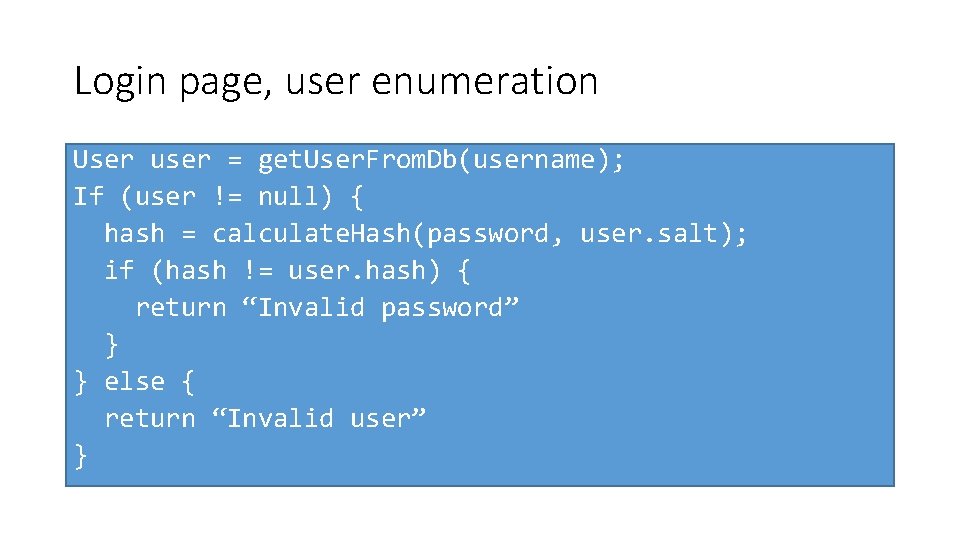
Login page, user enumeration User user = get. User. From. Db(username); If (user != null) { hash = calculate. Hash(password, user. salt); if (hash != user. hash) { return “Invalid password” } } else { return “Invalid user” }
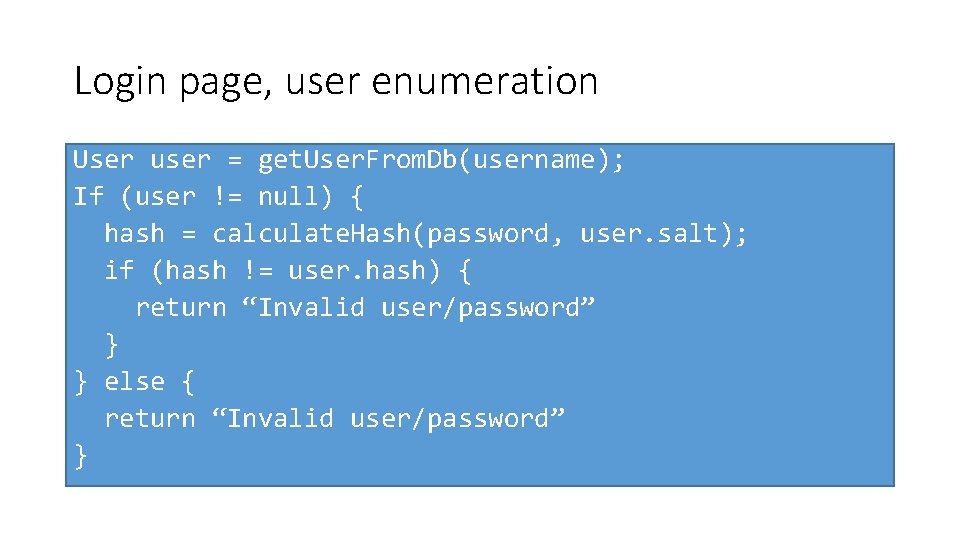
Login page, user enumeration User user = get. User. From. Db(username); If (user != null) { hash = calculate. Hash(password, user. salt); if (hash != user. hash) { return “Invalid user/password” } } else { return “Invalid user/password” }
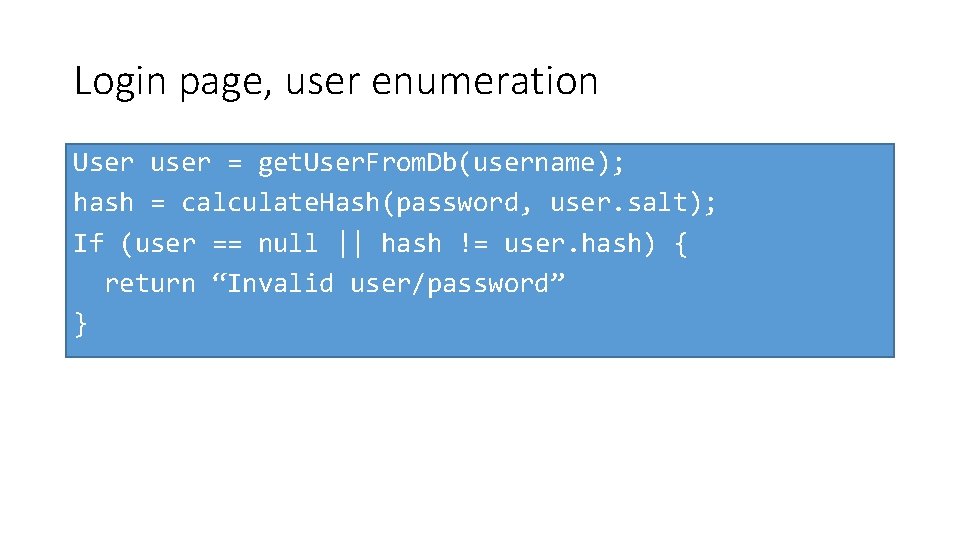
Login page, user enumeration User user = get. User. From. Db(username); hash = calculate. Hash(password, user. salt); If (user == null || hash != user. hash) { return “Invalid user/password” }
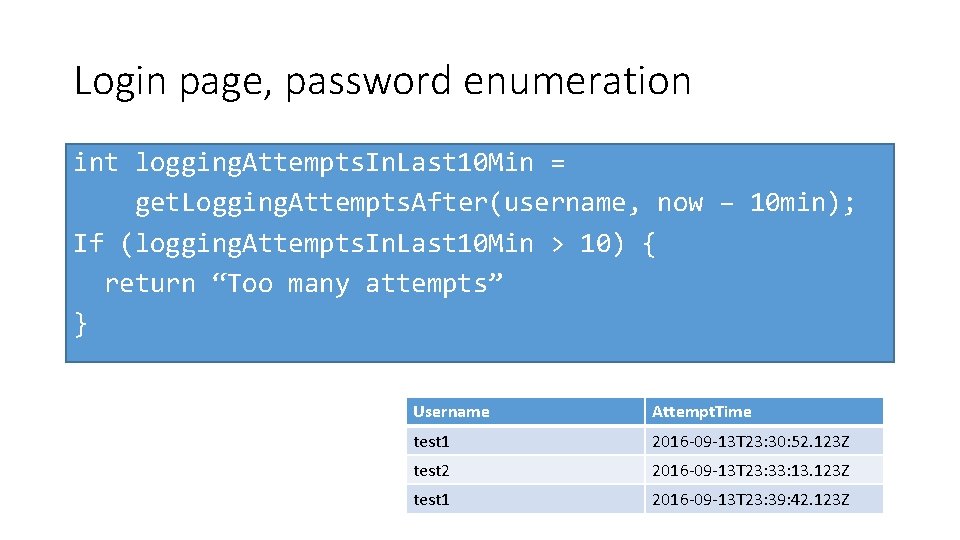
Login page, password enumeration int logging. Attempts. In. Last 10 Min = get. Logging. Attempts. After(username, now – 10 min); If (logging. Attempts. In. Last 10 Min > 10) { return “Too many attempts” } Username Attempt. Time test 1 2016 -09 -13 T 23: 30: 52. 123 Z test 2 2016 -09 -13 T 23: 33: 13. 123 Z test 1 2016 -09 -13 T 23: 39: 42. 123 Z

Java
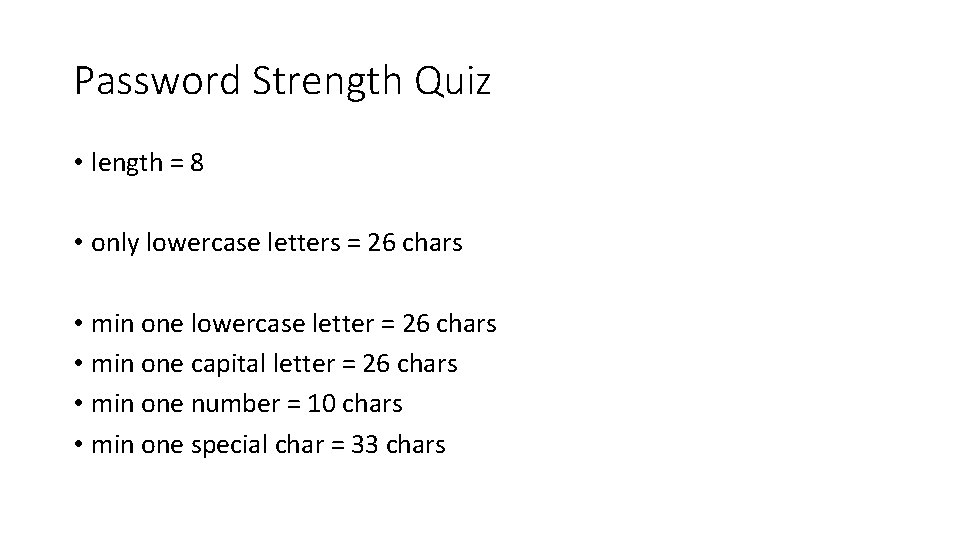
Password Strength Quiz • length = 8 • only lowercase letters = 26 chars • min one lowercase letter = 26 chars • min one capital letter = 26 chars • min one number = 10 chars • min one special char = 33 chars
Contact Marjan Kindalov Netcetera mail: marjan. kindalov@gmail. com
Resources • https: //en. wikipedia. org/wiki/Cryptographic_nonce • https: //en. wikipedia. org/wiki/Cryptographic_hash_function • https: //en. wikipedia. org/wiki/Rainbow_table • https: //en. wikipedia. org/wiki/Salt_(cryptography) • https: //en. wikipedia. org/wiki/Key_stretching • https: //en. wikipedia. org/wiki/Bcrypt • https: //www. owasp. org/index. php/Authentication_Cheat_Sheet
- Slides: 25