Fault Detection and Diagnosis Outline l Fault management
- Slides: 59
Fault Detection and Diagnosis
Outline l Fault management functionality l Event correlations concept l Techniques
Definitions l l A fault may cause hundreds of alarms. We need to be able to do the following: u u l An alarm u l l Detect the existence of faults Locate faults External manifestations of faults n Generated by components n Observable, e. g. via messages An alarm represents a symptom of a fault. An event u An occurrence of interest, e. g. an alarm message
Fault Management Functionalities l Fault detection Should be real-time u Techniques can be based on active schemes (e. g. , polling) or event-based schemes (where a system component says that it has detected a failure). u l Fault location u Is it a link or system component or application component? Determine corrective actions l Carry out corrective actions and determine effectiveness l
Alarm (Event) Correlation l Alarm explosion u l A single problem might trigger multiple symptoms (e. g. , router is down) There could be too many alarms for an administrator to handle; Techniques used to help: Compression: reduction of multiple occurrences of an alarm into a single alarm u Count: replacement of a number of occurrences of alarms with a new alarm u Suppression: inhibiting a low-priority alarm in the presence of a higher priority alarm u Boolean: substitution of a set of alarms satisfying a condition with a new alarm u
Fault Diagnosis Major application of alarm correlation is fault diagnosis l Useful in fault location l
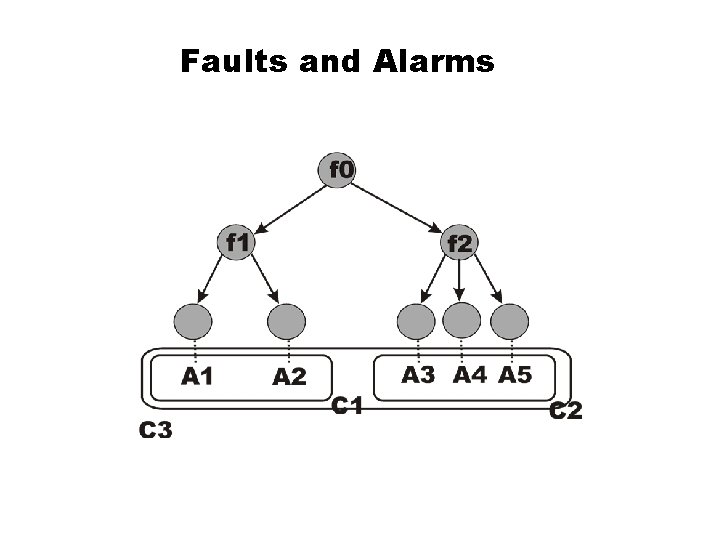
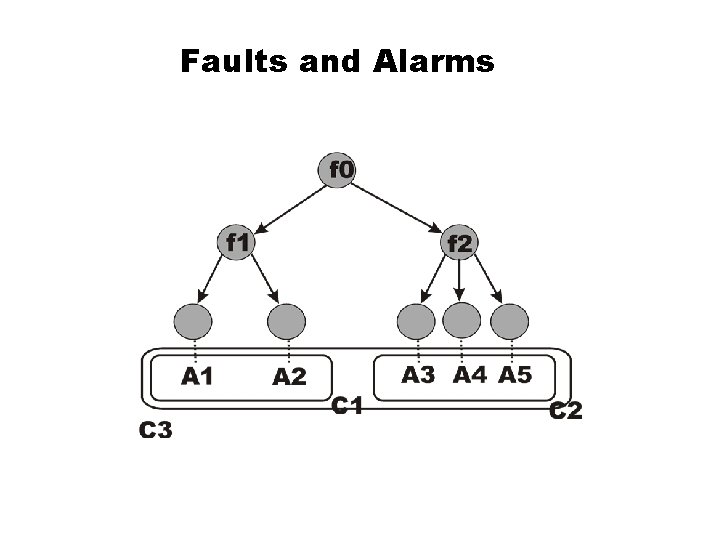
Faults and Alarms
Faults and Alarms l The previous figure shows that correlation c 1 detects the fault f 1 and that correlation c 2 detects the fault f 2. l Correlating c 1 and c 2 into the correlation c 0 allows the diagnosis of the fault f 0.
Example l Let a 1, a 2, a 3, a 4, a 5 be alarms generated by client processes indicating that a client process is not getting a response from a server. l Correlation techniques can be used to show that since a 1, a 2, a 3 were generated by client processes by trying to contact the same server then the server may be the problem. Similar comments apply to a 4 and a 5.
Example l From the perspective of client processes, the servers (at the second level of the previous figure) are at fault. l However, it may be observed that alarms were generated by these two servers. Both alarms indicate that each of the two servers are not getting a response and that both were trying to contact the same server. This is another correlation.
Rule-Based Reasoning l Based on expert systems l Intended to represent heuristic knowledge as rules. l Components Knowledge Base (KB): Contains the expert rules that describe the action to be taken when a specific condition occurs e. g. , if-then-else u Working Memory(WM): Stores information such as the system/network topology and data collected through the monitoring of application and network components. u
Rule-Based Reasoning l Components (continued) u Inference engine: matches the current state (as represented by the monitored data) of the system against the left-side of a rule in the knowledge base in order to trigger the action. The rules are meant to encapsulate expert knowledge l Why rule-based reasoning? l Rules are interpreted which means that rules can be changed without recompiling. u Since expert knowledge can be wrong and/or complete, this feature is very useful. u
Approaches l Model-based l Fault propagation l Model traversing l Case-based reasoning
Model-Based Reasoning l Use structural knowledge, e. g. , via objectoriented models l To illustrate model-based reasoning, we will look at network equipment. l A network equipment class is used to describe a network equipment type. l Network equipment classes are organized into a hierarchy using class/subclass relations.
Model-Based Reasoning l l The root class is a generic class that represents the most general information common to all network equipment e. g. , vendor name The next level of the hierarchy describes the basic network equipment classes such as physical-trunk class and switch class. Example: The trunk class refers to T 1 trunk class and T 3 trunk class. An association class represents a relationship between two object classes that represents connectivity.
Model-Based Reasoning l The network configuration model is constructed from the instances of individual network equipment. l The network configuration model is a graph consisting of objects instantiated from the network equipment classes. If there is an edge between two objects then this implies that the two objects are connected.
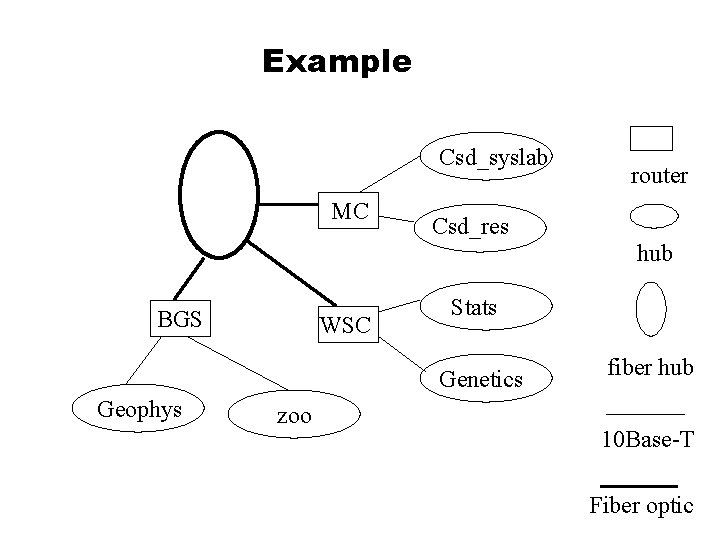
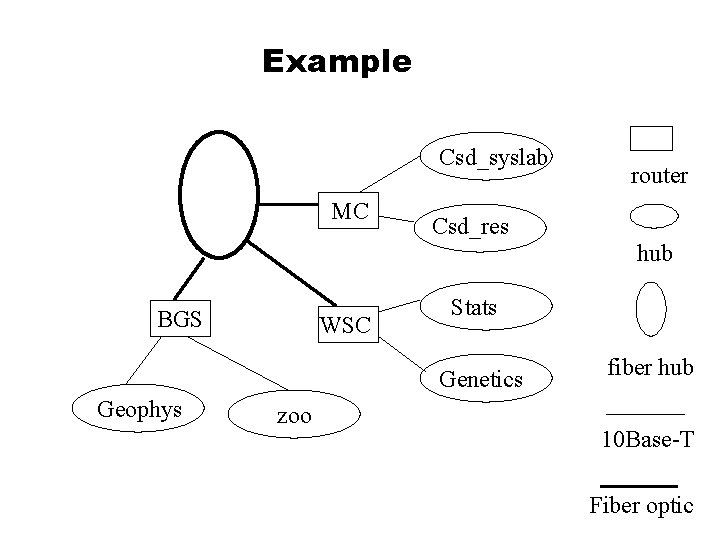
Example Csd_syslab MC router Csd_res hub BGS WSC Stats Genetics Geophys zoo fiber hub 10 Base-T Fiber optic
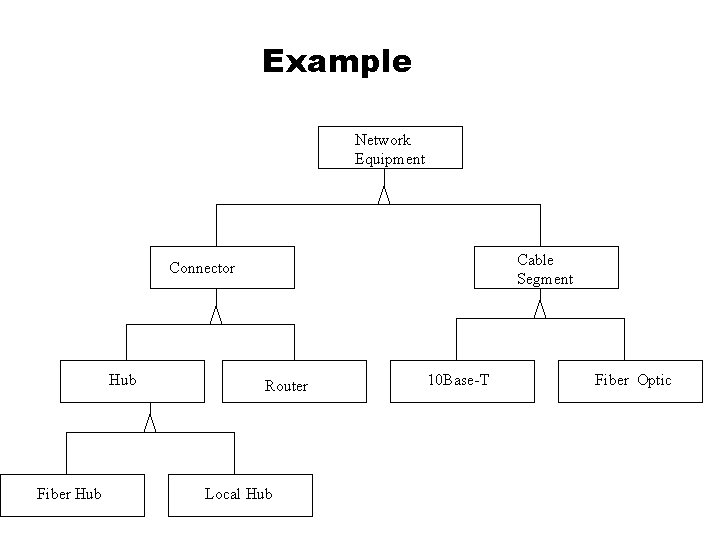
Example l There is a Network Equipment class that has attributes used to describe a network equipment. At a minimum assume that there is an attribute representing the name of the vendor. l You can subclass the following from the Network Equipment class: Connector u Cable Segment u
Example l The Connector class has two subclasses: Hub u Router u l The Cable Segment class also has two subclasses: 10 Base-T u Fiber Optic u l The Hub class has two subclasses: Fiber Hub u Local Hub u
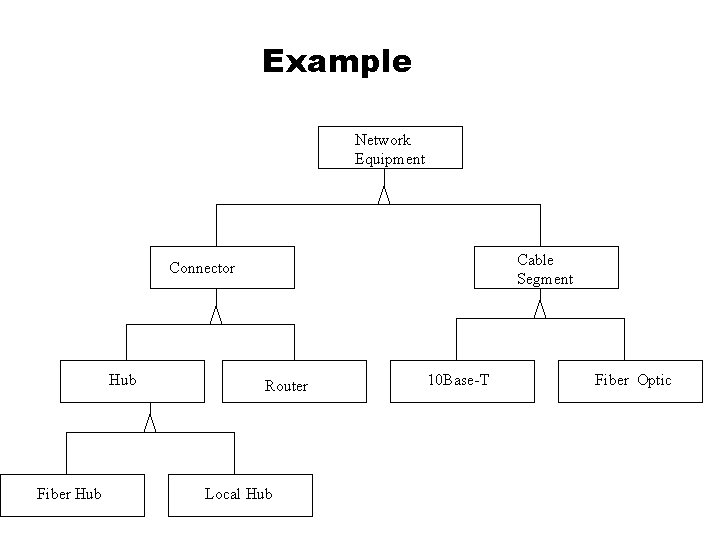
Example Network Equipment Cable Segment Connector Hub Fiber Hub Router Local Hub 10 Base-T Fiber Optic
Model-Based Reasoning l Message Class Hierarchy Describes messages created by elements of a network configuration model. u These messages report symptoms. They are essentially alarms. u
Example l A hub can generate a message stating that one of its ports is “bad”. In fact, there is a message associated with each port. l A hub can generate a message stating that the cable segment on a particular port does not seem to be functioning. This can be encapsulated in a message class called Hub_Report_Port_Bad. This can be subclassed into messages generated by each type of hub.
Model-Based Reasoning l Correlations Conditions under which the correlations are asserted u Correlations are stated in terms of message classes. u At run-time there is match between an instantiation and a message class. u Example: If a local hub is connected to more than one router and there are two messages from the routers indicating that there are problems connecting to the local hub then this is a good indication that the hub is a problem. u
Fault Propagation l Based on models that describe which symptoms will be observed if a specific fault occurs. l Monitors typically collect managed data at network elements and detect out of tolerance conditions, generating appropriate alarms. l An event model is used by a management application to analyze these alarms. l The event model represents knowledge of events and their causal relationships.
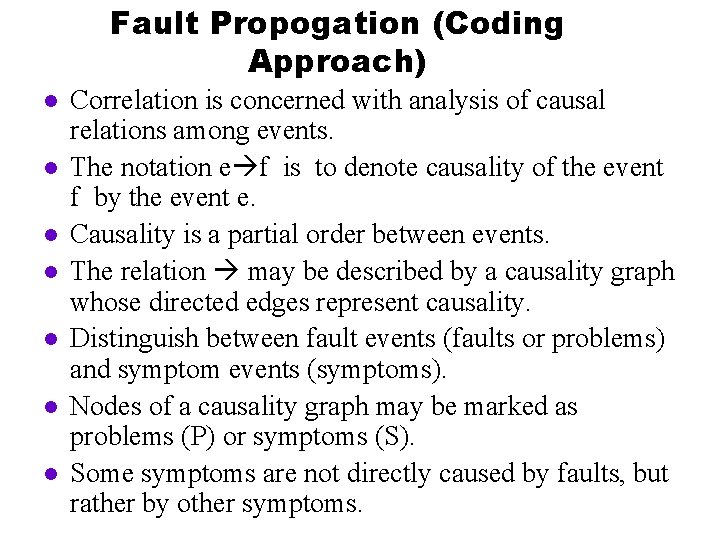
Fault Propogation (Coding Approach) l l l l Correlation is concerned with analysis of causal relations among events. The notation e f is to denote causality of the event f by the event e. Causality is a partial order between events. The relation may be described by a causality graph whose directed edges represent causality. Distinguish between fault events (faults or problems) and symptom events (symptoms). Nodes of a causality graph may be marked as problems (P) or symptoms (S). Some symptoms are not directly caused by faults, but rather by other symptoms.
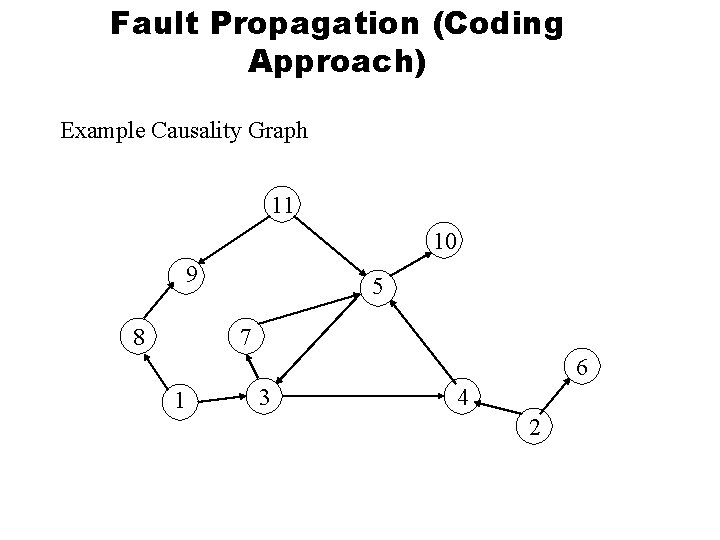
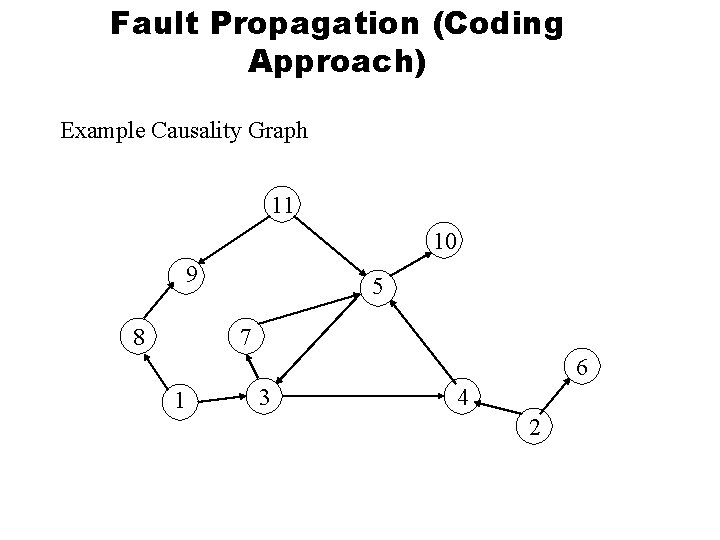
Fault Propagation (Coding Approach) Example Causality Graph 11 10 9 5 7 8 6 1 3 4 2
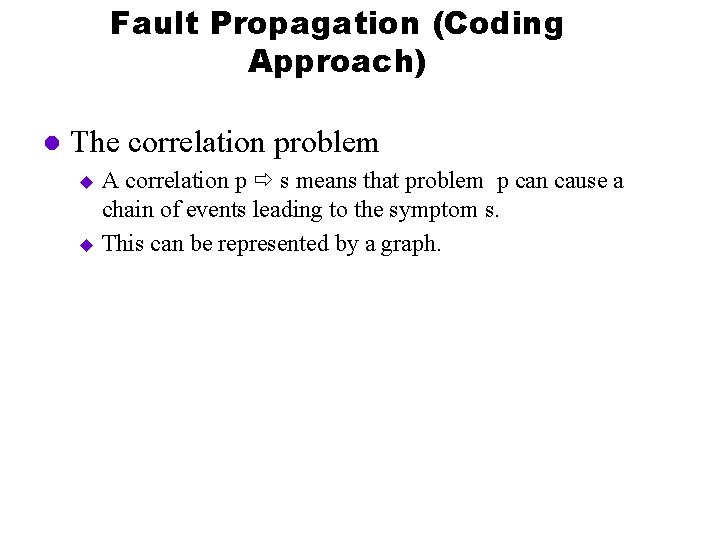
Fault Propagation (Coding Approach) l The correlation problem A correlation p s means that problem p can cause a chain of events leading to the symptom s. u This can be represented by a graph. u
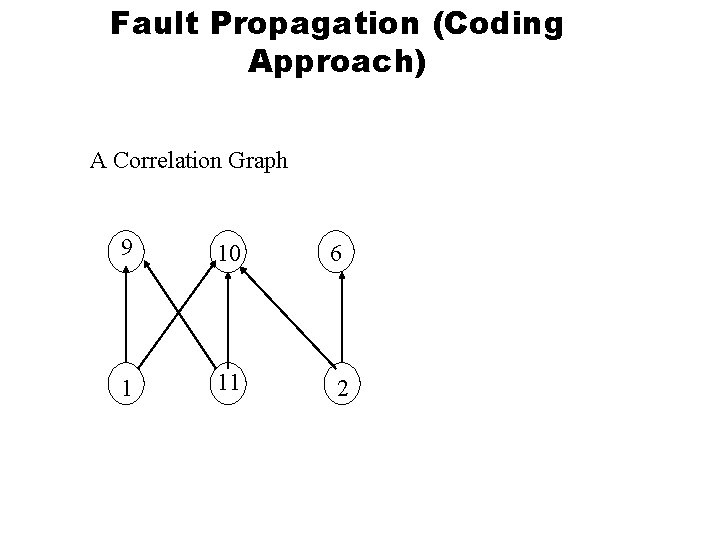
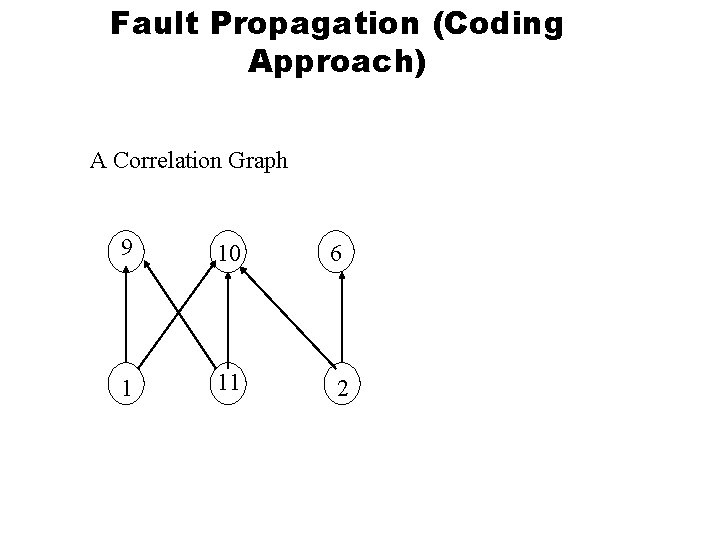
Fault Propagation (Coding Approach) A Correlation Graph 9 10 1 11 6 2
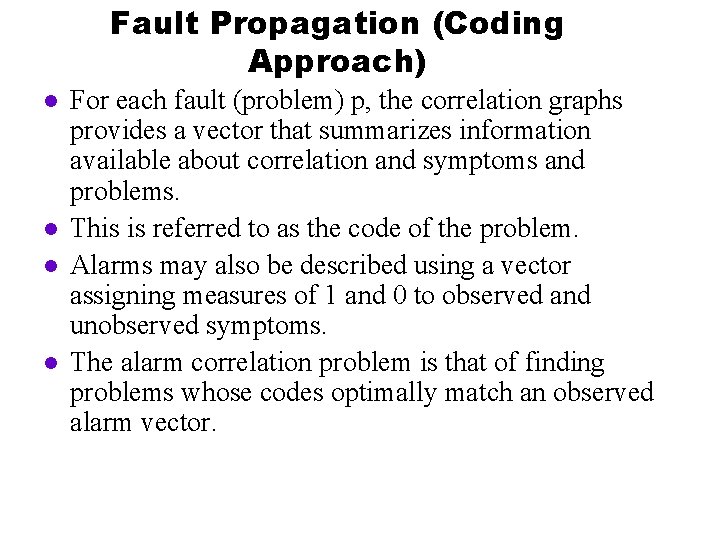
Fault Propagation (Coding Approach) l l For each fault (problem) p, the correlation graphs provides a vector that summarizes information available about correlation and symptoms and problems. This is referred to as the code of the problem. Alarms may also be described using a vector assigning measures of 1 and 0 to observed and unobserved symptoms. The alarm correlation problem is that of finding problems whose codes optimally match an observed alarm vector.
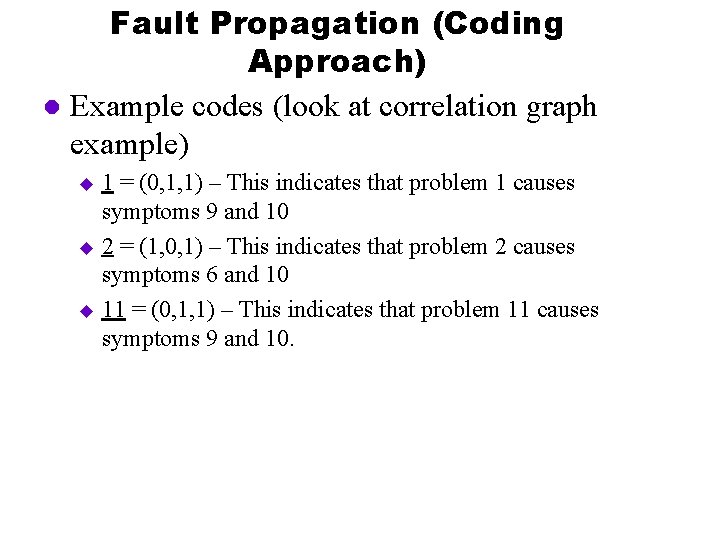
Fault Propagation (Coding Approach) l Example codes (look at correlation graph example) 1 = (0, 1, 1) – This indicates that problem 1 causes symptoms 9 and 10 u 2 = (1, 0, 1) – This indicates that problem 2 causes symptoms 6 and 10 u 11 = (0, 1, 1) – This indicates that problem 11 causes symptoms 9 and 10. u
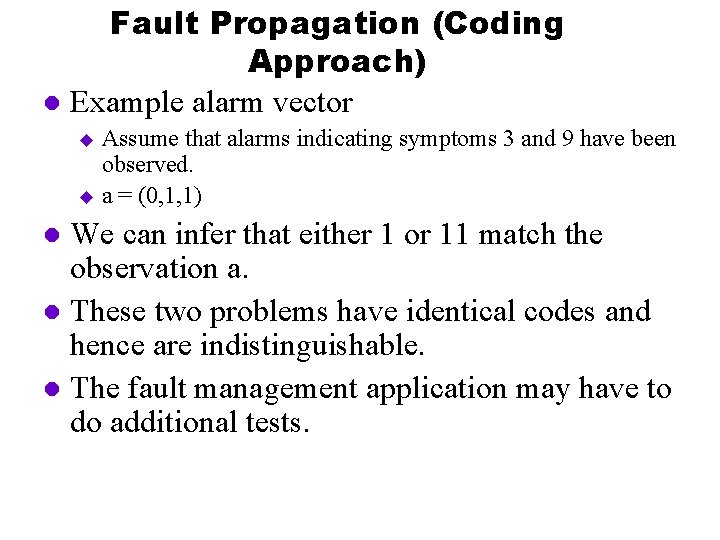
Fault Propagation (Coding Approach) l Example alarm vector Assume that alarms indicating symptoms 3 and 9 have been observed. u a = (0, 1, 1) u We can infer that either 1 or 11 match the observation a. l These two problems have identical codes and hence are indistinguishable. l The fault management application may have to do additional tests. l
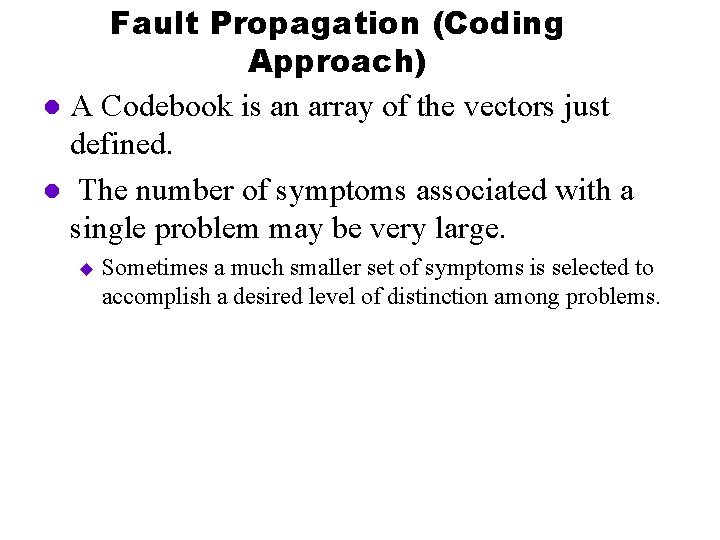
Fault Propagation (Coding Approach) l A Codebook is an array of the vectors just defined. l The number of symptoms associated with a single problem may be very large. u Sometimes a much smaller set of symptoms is selected to accomplish a desired level of distinction among problems.
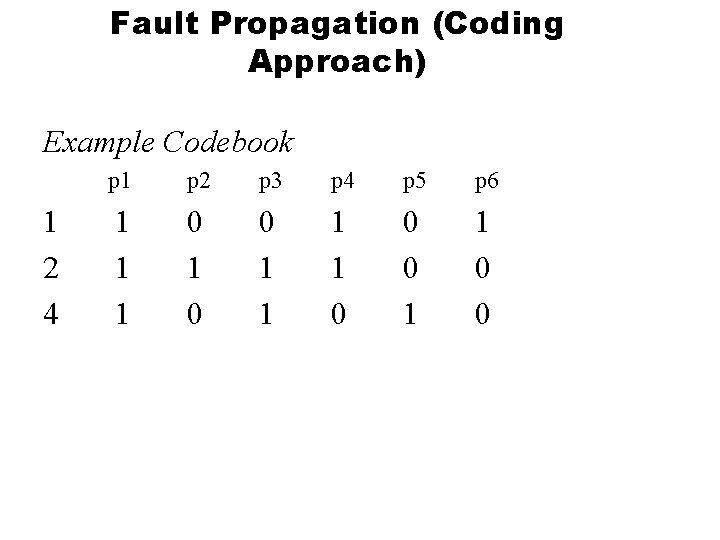
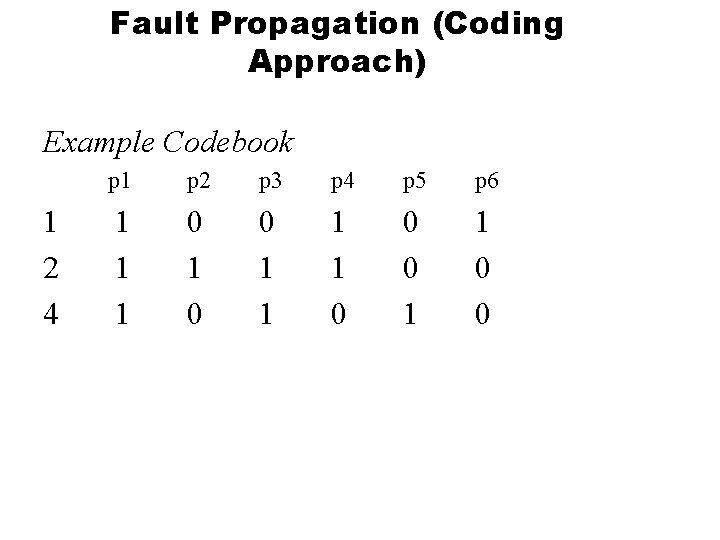
Fault Propagation (Coding Approach) Example Codebook 1 2 4 p 1 p 2 p 3 p 4 p 5 p 6 1 1 1 0 0 0 1 1 0 0
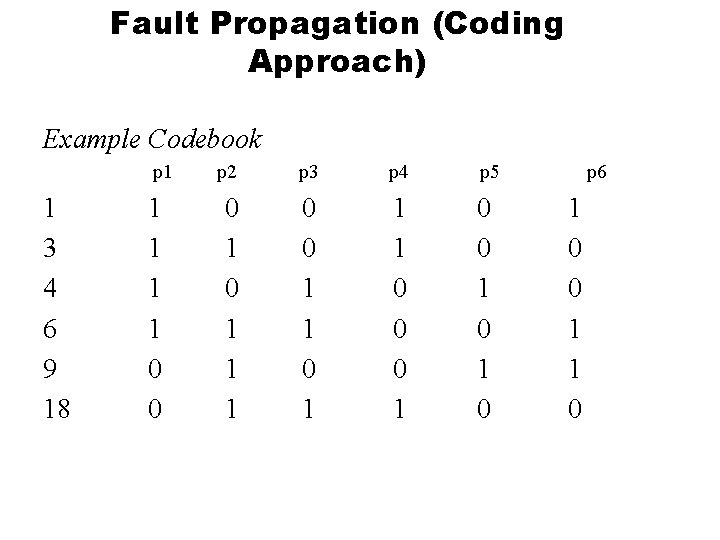
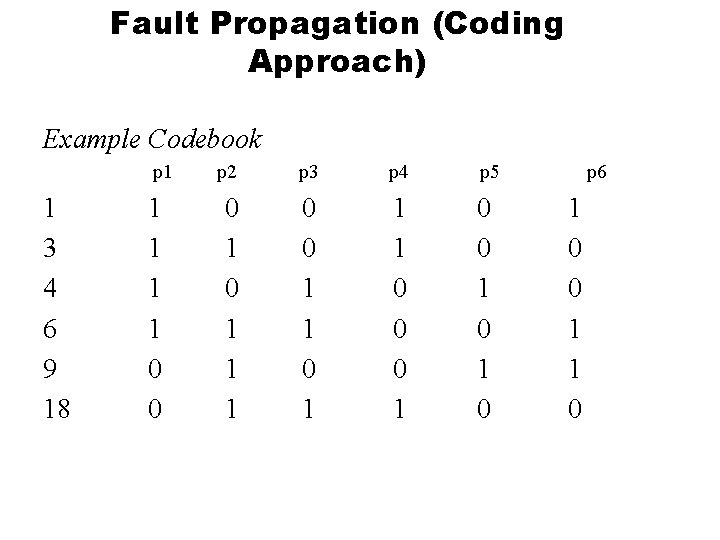
Fault Propagation (Coding Approach) Example Codebook p 1 1 3 4 6 9 18 1 1 0 0 p 2 p 3 p 4 p 5 0 1 1 1 0 0 0 1 0 1 0 p 6 1 0 0 1 1 0
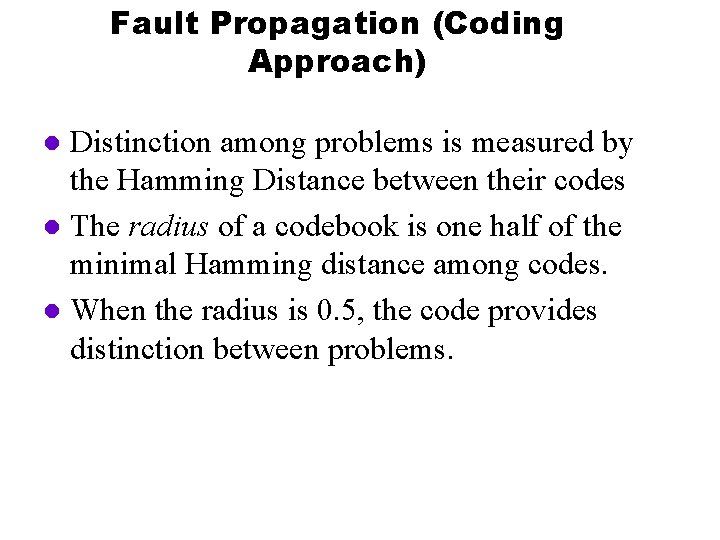
Fault Propagation (Coding Approach) Distinction among problems is measured by the Hamming Distance between their codes l The radius of a codebook is one half of the minimal Hamming distance among codes. l When the radius is 0. 5, the code provides distinction between problems. l
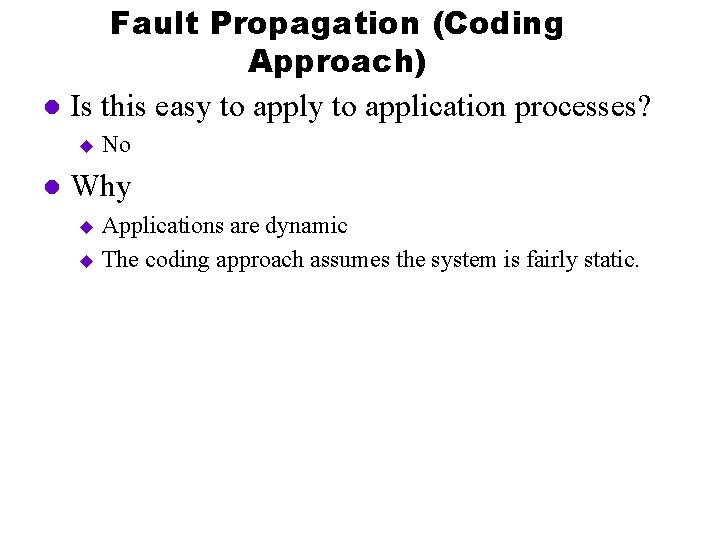
Fault Propagation (Coding Approach) l Is this easy to application processes? u l No Why Applications are dynamic u The coding approach assumes the system is fairly static. u
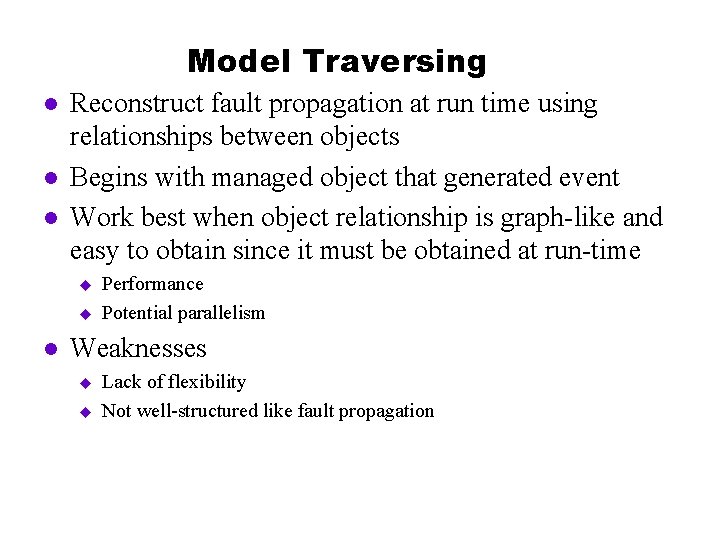
Model Traversing l l l Reconstruct fault propagation at run time using relationships between objects Begins with managed object that generated event Work best when object relationship is graph-like and easy to obtain since it must be obtained at run-time u u l Performance Potential parallelism Weaknesses u u Lack of flexibility Not well-structured like fault propagation
Model Traversing l Characteristics Event-Driven: Fault management application is passive until an event arrives. This event is the reporting of a symptom. u Correlation : Decides whether two events result from the same primary fault. u Relationship Exploration: The fault management application correlates events by detecting special relationships between the source objects of those events. u
Model Traversing l Event reports should have the following information: Symptom type u Source u Target u etc u l If symptom si’s target is the same as sj’s source then this is an indication that si is a secondary symptom. This allows us to ignore certain alarms.
Model Traversing l l l For each event, construct a graph of objects (models) related to the source object of that event. When two such graphs touch each other, i. e. contain at least one common object, the events which initiated their construction are regarded to be correlated. Possibly these two events are the result of the same fault. If si is correlated with sj and sj is correlated with sk then through transitivity we can conclude that si is a secondary symptom.
Model Traversing l The process of eliminating symptom reports may result in reports that have the same target. l Example: s 1 and t u s 2 and t u It might be necessary to construct possible paths of objects between s 1 and t as well as s 2 and t l Nodes in common are good candidates for the faults. l
Model Traversing l l We will now discuss the building of graphs The algorithm for building graphs uses relationships between network hardware and software components to search for the root cause of a problem. Assumes that information about the relationships between the components are available (e. g. , through a database). Assumes that there are functions including these: u get. Next. Hop(source, target, B): Get the node representing the next entity (that comes after B) in the path between source and target. Note that this may return more than one entity.
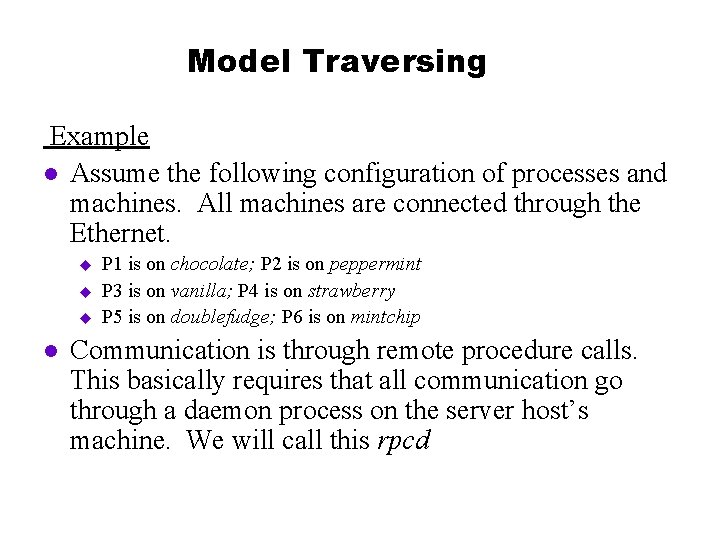
Model Traversing Example l Assume the following configuration of processes and machines. All machines are connected through the Ethernet. u u u l P 1 is on chocolate; P 2 is on peppermint P 3 is on vanilla; P 4 is on strawberry P 5 is on doublefudge; P 6 is on mintchip Communication is through remote procedure calls. This basically requires that all communication go through a daemon process on the server host’s machine. We will call this rpcd
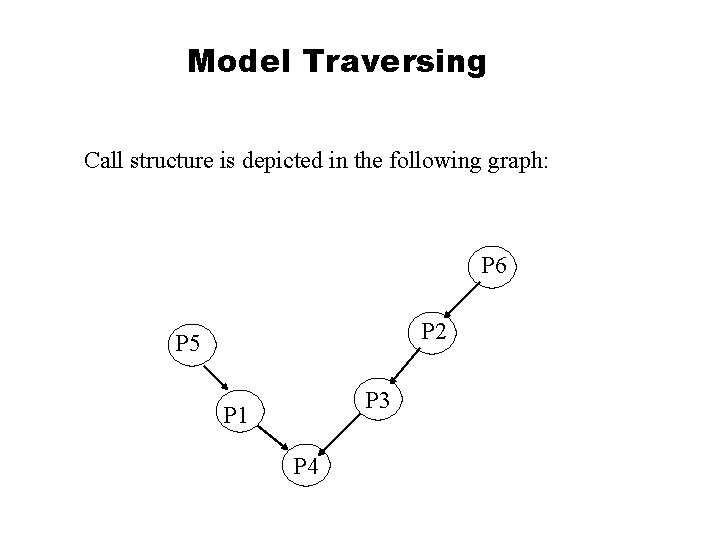
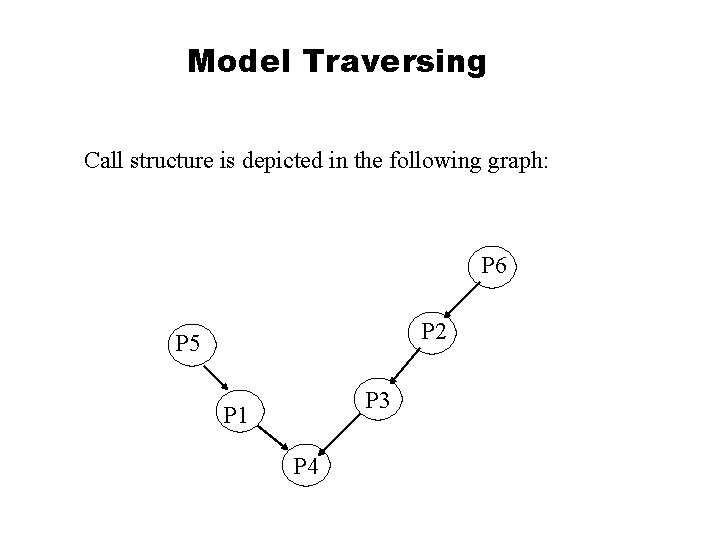
Model Traversing Call structure is depicted in the following graph: P 6 P 2 P 5 P 3 P 1 P 4
Model Traversing Example l Assume that P 4 terminates abnormally causing a cascade of timeouts l Correlation will result on focusing on these event reports: u u l (P 1, P 4) (P 3, P 4) Not enough to diagnose the fault. u u It’s all at the process level. There are still many entities or objects to examine since you do not want everything generating a message.
Model Traversing Example l Starting with P 1 the next component (node) along the path of the connection between P 1 and P 4 is identified. l Between P 1 and P 4 are many entities. We will start out with a vertical search which basically results in the fact that P 1 is running on a host machine called chocolate l
Model Traversing l chocolate is connected to the hub through an ethernet cable. l The hub is connected to strawberry through an ethernet connection cable where P 2 is running. Thus we can say that the path is the following: u l P 1, chocolate, ethernet connection cable, hub, strawberry, ethernet connection cable, rpcd. strawberry, P 4 The path between P 3 and P 4 is the following: u P 3, vanilla, ethernet connection cable, hub, ethernet connection cable, strawberry, rpcd. strawberry, P 4
Model Traversing Example l This suggests that we can narrow down the problem to hub, ethernet connection cable, strawberry. rpcd, strawberry, P 4. l At this point, the fault management application may want to poll for additional information. The polling may check to see if something is up or not. An example is applying the ping operation to the host machine called strawberry. l What if every entity is up? This may indicate that strawberry is overloaded. An indication of an overload can be found by measuring the CPU load.
Model Traversing l Building the graphs requires structural information and the use of rules.
Model Traversing Implementation l What management services are needed? To detect and report symptoms, one could use application instrumentation. u The instrumentation library should most likely talk with a management process (or agent). u The agent sends an event report to the event server. u The event server may have a set of rules for symptom correlation. u After correlation, a task may be invoked that does relationship exploration and the final diagnosis. u
Model Traversing Implementation l Information Needed Information representing the relationships between hardware components and software components is needed. u This needs to be stored in a database or a directory service (e. g. , X 500) u An API needs to be defined to retrieve this information. u Rules can be used to help construct the graph. u
Model Traversing Implementation l Information Needed How is the information collected? u Many different techniques. Examples include: n Processes (using instrumentation) may have to register and have their information put into the database. n Network information may have to be entered manually. u
Model Traversing l Summary l Performs very quickly once model is built u Model can be constructed incrementally during normal processing; do not have to wait until failure Can operate in parallel l Can accommodate multiple events; different starting points can result in same problem element l Does require model reflective of run-time l u One that changes too fast is a problem
Case-based Reasoning (CBR) l Objective Learn from experience u Solutions to novel problems u Avoid extensive maintenance u l Basic idea: recall, adapt and execute episodes of former problem-solving in an attempt to deal with a current problem
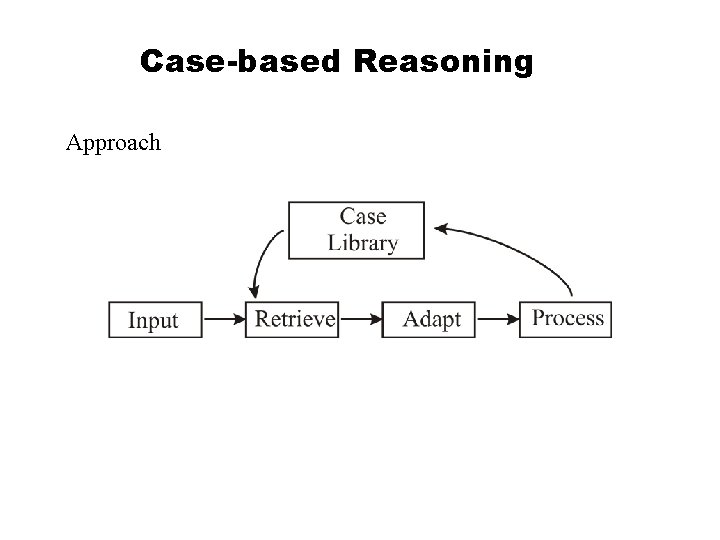
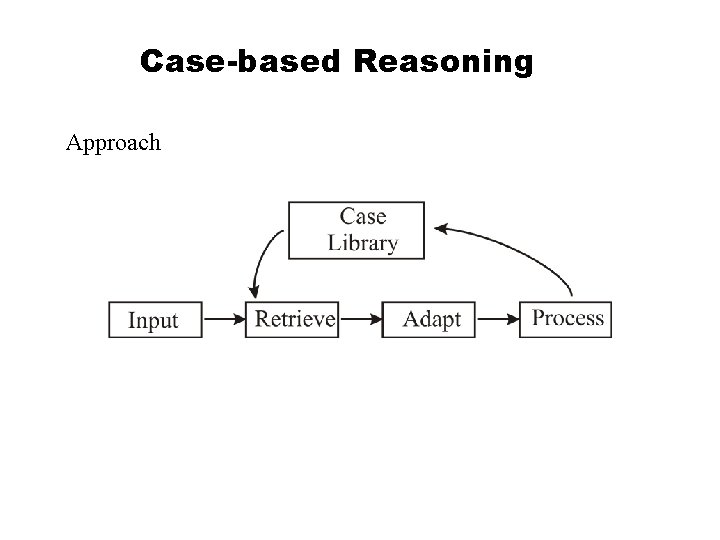
Case-based Reasoning Approach
Case-Based Reasoning l Strategy l Useful for domains in which a body of knowledge with a case structure exists or is easily obtainable l Case structure: Set of fields or “slots” u Capture “essential” information u l Yield discriminators u l Set of fields highly correlated with problems or solutions Need to find “closest” match
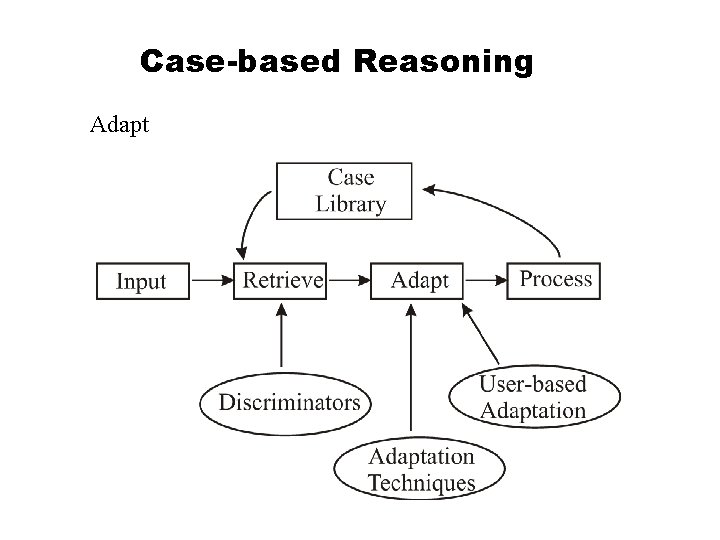
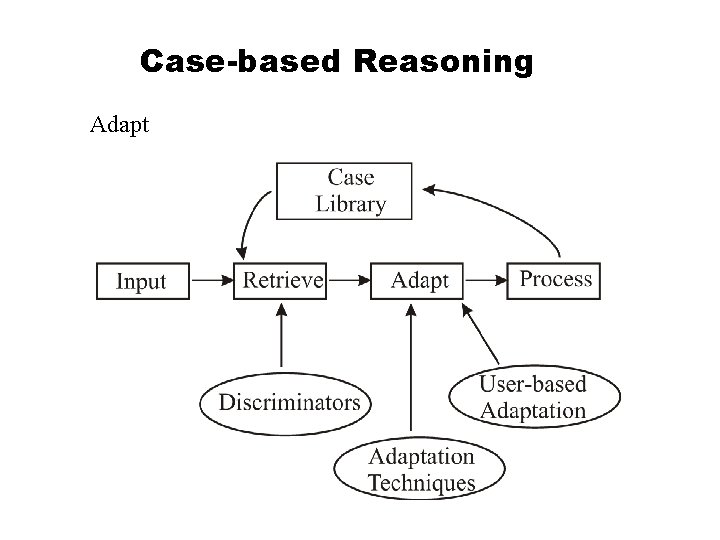
Case-based Reasoning Adapt
Case-based Reasoning l Summary l Needs well-defined cases l Likely to work well when problems are “close” to existing solutions l Problem selecting solutions when “not so close” Dangerous in following actions? u How to adapt? u
Summary Variety of approaches l Mostly applied in network management scenarios l More controlled? u Better understanding of problems? u l Limited experience in application management