Byzantine Generals Problem Overview A The Problem B
Byzantine Generals Problem
Overview A. The Problem B. Two Solutions 1. Oral Messages 2. Signed Messages Application 1. Reliable Systems 2. Bitcoin
The Problem
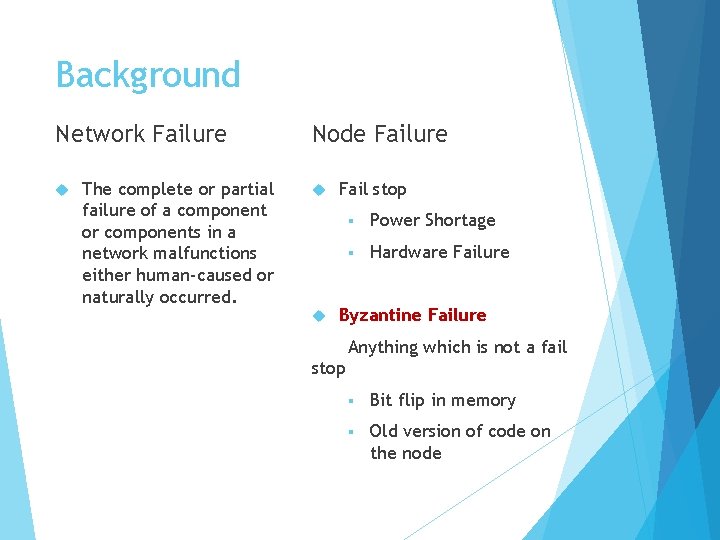
Background Network Failure The complete or partial failure of a component or components in a network malfunctions either human-caused or naturally occurred. Node Failure Fail stop § Power Shortage § Hardware Failure Byzantine Failure Anything which is not a fail stop § Bit flip in memory § Old version of code on the node
Problem Byzantine army divisions camped outside the walls of an enemy city. Each division is led by a general. Generals decide on a common plan of action.
Problem – Types of Generals There are two types of generals Loyal or Traitor
Problem – Conditions needed to be met: 1. Loyal generals decide upon the same plan of action. 2. Small number of traitors should not be able to lead the loyal generals make a bad decision.
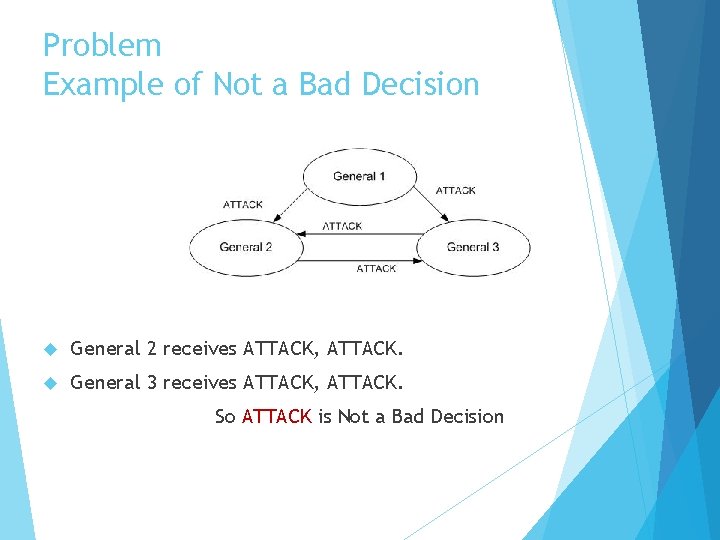
Problem Example of Not a Bad Decision General 2 receives ATTACK, ATTACK. General 3 receives ATTACK, ATTACK. So ATTACK is Not a Bad Decision
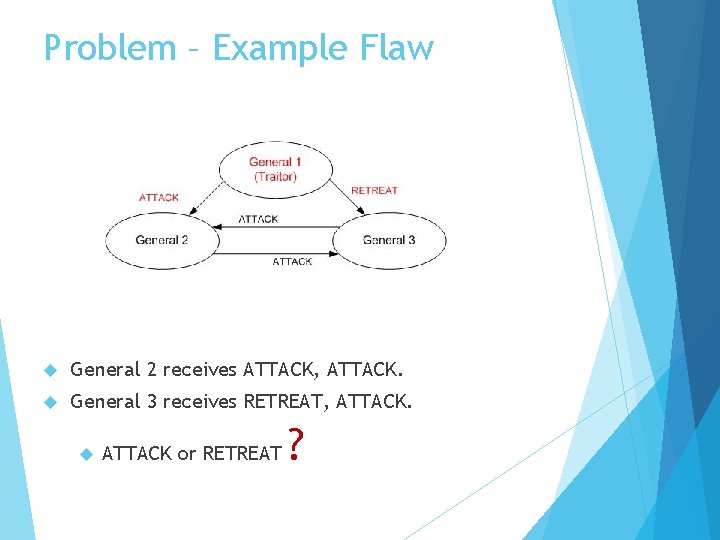
Problem – Example Flaw General 2 receives ATTACK, ATTACK. General 3 receives RETREAT, ATTACK or RETREAT ?
Interactive Consistency A commanding general must send an order to his n-1 lieutenant generals such that: IC 1. All loyal lieutenants obey the same order. IC 2. If the commanding general is loyal, then every loyal lieutenant obeys the order he sends. These are called the interactive consistency conditions.
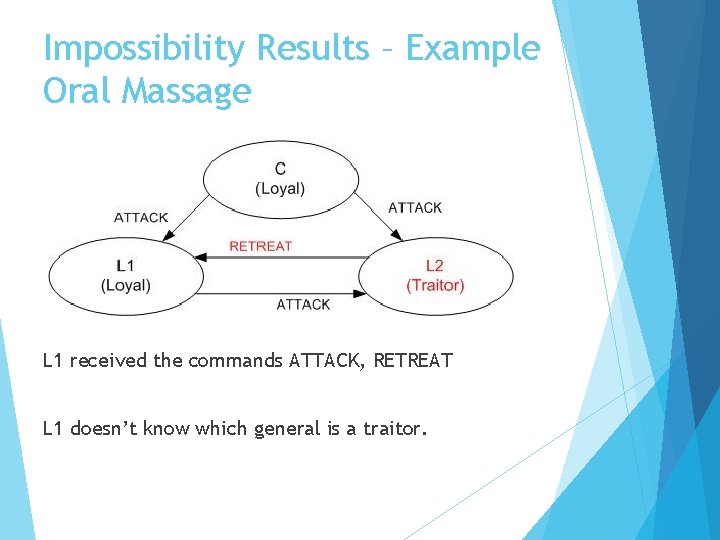
Impossibility Results – Example Oral Massage L 1 received the commands ATTACK, RETREAT L 1 doesn’t know which general is a traitor.
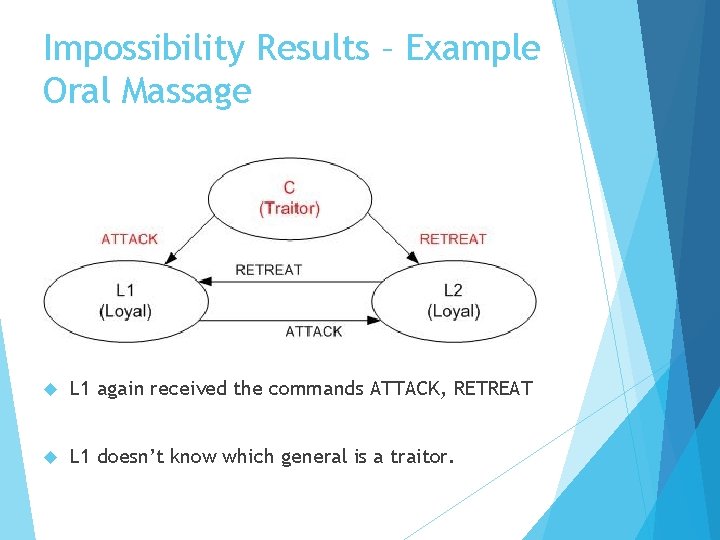
Impossibility Results – Example Oral Massage L 1 again received the commands ATTACK, RETREAT L 1 doesn’t know which general is a traitor.
Impossibility Results The Byzantine Generals Problem will fail If: 1/3 or more of the generals are traitors.
Impossibility Results Generalization No solution for: Fewer than 3 m + 1 generals; m = number of traitor generals
![Impossibility Results Application Utilized in clock synchronization as described in Dolev et al. [1986] Impossibility Results Application Utilized in clock synchronization as described in Dolev et al. [1986]](http://slidetodoc.com/presentation_image_h2/9636cb87b0e5cc76bdda2b90888d970e/image-15.jpg)
Impossibility Results Application Utilized in clock synchronization as described in Dolev et al. [1986] N > 3 f N = number of clocks f = number of clocks that are faulty Same as the Byzantine Problem!

A Solution with Oral Messages
Solution with Oral Messages Assumptions: A 1: Every message that is sent is delivered correctly. A 2: The receiver of a message knows who sent it. A 3: The absence of a message can be detected.
Solution with OM – Definition Function majority(v 1, …, vn-1) If the majority of the values vi equal v, then majority(v 1, …, vn-1) is v. If no majority exists, then the function evaluates as RETREAT.
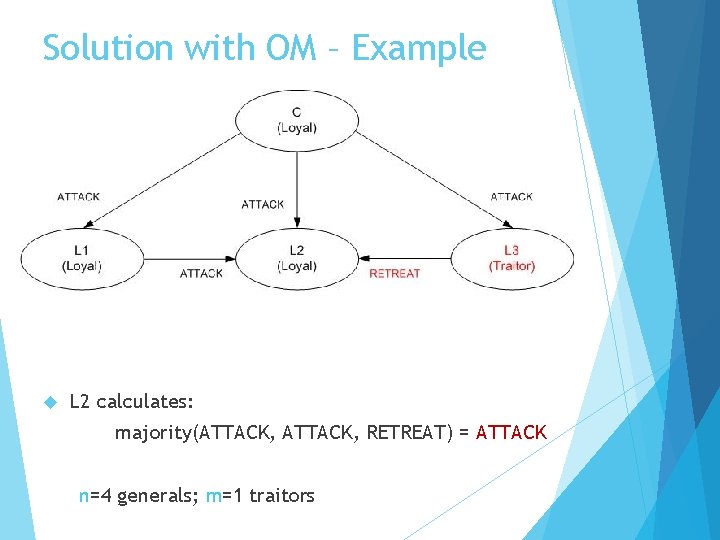
Solution with OM – Example L 2 calculates: majority(ATTACK, RETREAT) = ATTACK n=4 generals; m=1 traitors
A Solution with Signed Messages
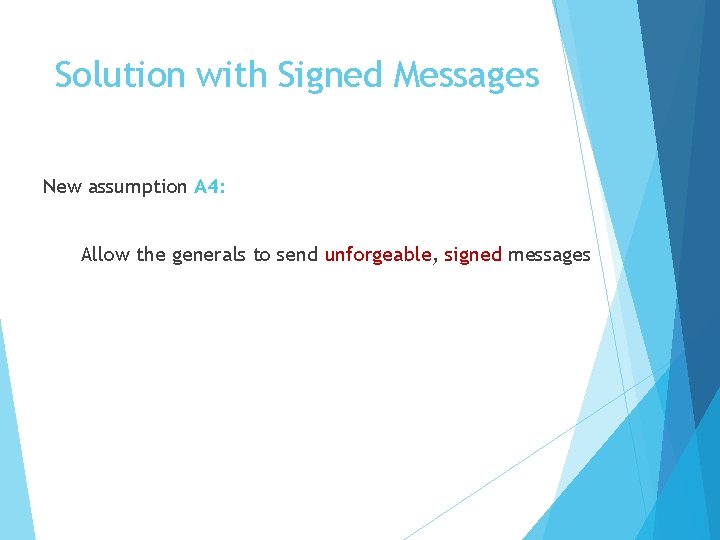
Solution with Signed Messages New assumption A 4: Allow the generals to send unforgeable, signed messages
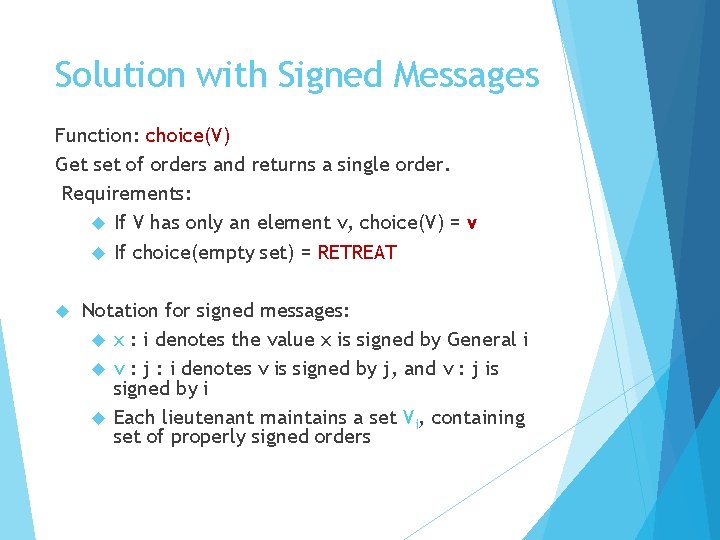
Solution with Signed Messages Function: choice(V) Get set of orders and returns a single order. Requirements: If V has only an element v, choice(V) = v If choice(empty set) = RETREAT Notation for signed messages: x : i denotes the value x is signed by General i v : j : i denotes v is signed by j, and v : j is signed by i Each lieutenant maintains a set Vi, containing set of properly signed orders
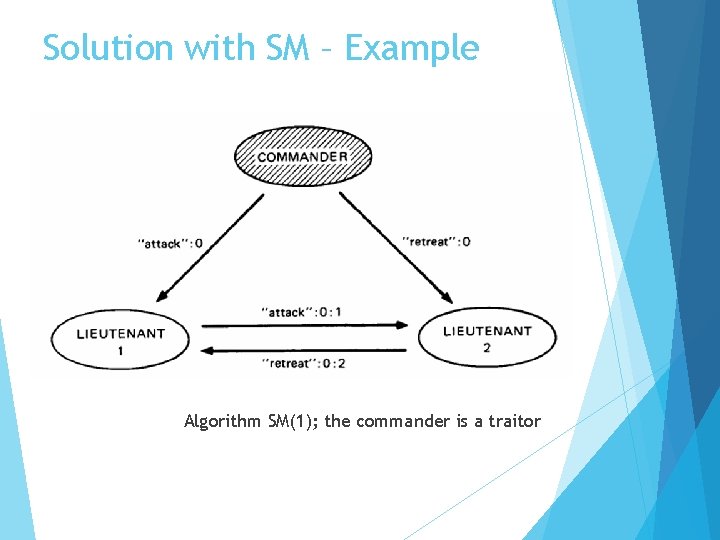
Solution with SM – Example Algorithm SM(1); the commander is a traitor
Impossibility Results Generalization No solution for: Fewer than N>= m + 2 generals; m = number of traitor generals
Reliable Systems
Implementation of Reliable Systems How to implement? Redundancy – use multiple processors Each processor computes same result Majority vote to obtain one result Examples Protect Missile Boing against failure of a single chip defense system 777
Majority Voting in Boing 777 • Primary Flight Computer (PFC) Triple-Mode Redundancy TMR configuration Receive data on all 3 ARINC 629 buses Transmit on only one ARINC 629 bus Each PFC contains 3 internal computation lanes Each lane accesses all 3 buses Each lane has dissimilar processors Different Ada compilers
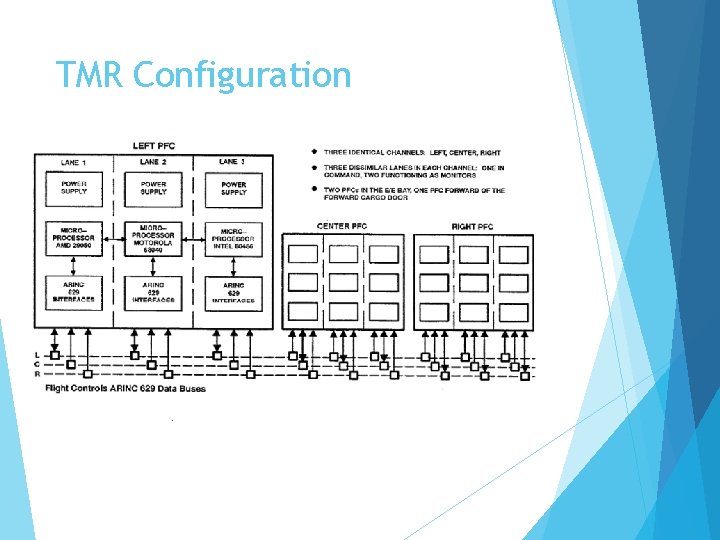
TMR Configuration
Bitcoin is a decentralized digital currency without any central bank. The heart of the protocols is the "Block chain" that acts as a shared public ledger. what's a "block"? A block holds data of a group of transactions and additional data that include also the previous block ID (hence creating a chain).
Mining To verify the "blocks" in Bitcoin environment the network nodes also referred as "miners“ should verify each one Mining process § Keep the Bitcoin network Secure § Create New Bitcoin In Bitcoin network the miners use the Proof-of-Work (Po. W) mechanism for consensus
Proof of work This mechanism requires the miners to solve a riddle in order to complete the verification process. The computations will take a long time for a mine. However, conforming the correctness will be done with minimal effort.
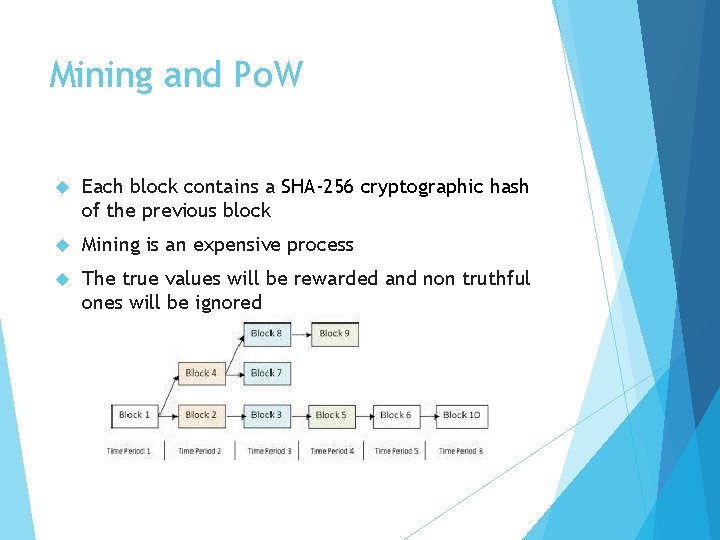
Mining and Po. W Each block contains a SHA-256 cryptographic hash of the previous block Mining is an expensive process The true values will be rewarded and non truthful ones will be ignored
- Slides: 32