An Introduction to Binary Finite Fields GF2 m
An Introduction to Binary Finite Fields GF(2 m) By Francisco Rodríguez Henríquez. Códigos y Criptografía Francisco Rodríguez Henríquez
What is a Group? An Abelian group <G, +> is an abstract mathematical object consisting of a set G together with an operation * defined on pairs of elements of G, here denoted by +: In order to qualify as an Abelian group, the operation has to fulfill the following conditions: i. Closed: ii. Associative: iii. Commutative: iv. Neutral element: v. Inverse elements: Códigos y Criptografía Francisco Rodríguez Henríquez
What is a Group? • Example: The best-known example of an Abelian Group is <Z, +> • Example: The additive group Z 15 uses the integers from 0 to 14. Some examples of additions in Z 15 are: (10 + 12) mod 15 = 22 mod 15 = 7 • In Z 15, 10 + 12 = 7 and 4 + 11 = 0. Notice that both calculations have answers between 0 and 14. • Additive Inverses – Each number x in an additive group has an additive inverse element in the group; that is an integer -x such that x + (-x) = 0 in the group. In Z 15, -4 =11 since (4 + 11) mod 15 = 15 mod 15 = 0. Códigos y Criptografía Francisco Rodríguez Henríquez
Rings (1/2) 1. 2. 3. 4. A ring <R, +, *> consists of a set R with 2 operations defined on its elements, here denoted by + and *. In order to qualify as a ring, the operations have to fulfill the following conditions: The structure <R, +> is an Abelian group. The operations * is closed, and associative over R. There is a neutral element for * in R. The two operations + and * are related by the law of distributivity: A ring <R, +. *> is called a commutative ring if the operation * is commutative. Códigos y Criptografía Francisco Rodríguez Henríquez
Rings (2/2) • The integer numbers, the rational numbers, the real numbers and the complex numbers are all rings. • An element x of a ring is said to be invertible if x has a multiplicative inverse in R, that is, if there is a unique such that: • 1 is called the unit element of the ring. Códigos y Criptografía Francisco Rodríguez Henríquez
What is a Field? • A structure <F, +, *> is called a field if F is a ring in which the multiplication is commutative and every element except 0 has a multiplicative inverse. We can define the field F with respect to the addition and the multiplication if: · F is a commutative group with respect to the addition. • is a commutative group with respect to the multiplication. · The distributive laws mentioned for rings, hold. Códigos y Criptografía Francisco Rodríguez Henríquez
What is a Field? • A field is a set of elements with two custom-defined arithmetic operations: most commonly, addition and multiplication. The elements of the field are an additive abelian group, and the non-zero elements of the field are a multiplicative abelian group. This means that all elements of the field have an additive inverse, and all non-zero elements have a multiplicative inverse. • A field is called finite if it has a finite number of elements. The most commonly used finite fields in cryptography are the field Fp (where p is a prime number) and the field F 2 m. Códigos y Criptografía Francisco Rodríguez Henríquez
Finite Fields • A finite field or Galois field denoted by GF(q=pn), is a field with characteristic p, and a number q of elements. As we have seen, such a finite field exists for every prime p and positive integer n, and contains a subfield having p elements. This subfield is called ground field of the original field. • For the rest of this class, we will consider only the two most used cases in cryptography: q=p, with p a prime and q=2 m. The former case, GF(p), is denoted as the prime field, whereas the latter, GF(2 m), is known as the finite field of characteristic two or simply binary field. Códigos y Criptografía Francisco Rodríguez Henríquez
Finite Fields • A finite field is a field with a finite number of elements. The number of elements in a finite field is called the order of the field. Fields of the same order are isomorphic: they display exactly the same algebraic structure differing only in the representation of the elements. Códigos y Criptografía Francisco Rodríguez Henríquez
The field Fp • The finite field Fp (p a prime number) consists of the numbers from 0 to p 1. Its operations are addition and multiplication. All calculations must be reduced modulo p. • It is mandatory to select p as a prime number in order to guarantee that all the non-zero elements of the field have a multiplicative inverse. • Other operations in Fp (such as division, subtraction and exponentiation) can be derived from the definitions of addition and multiplication. Códigos y Criptografía Francisco Rodríguez Henríquez
The field F 2 m ‘Plegaria del Codificador teórico: Juro por Galois que seré leal a las nobles tradiciones de la teoría de códigos; que hablaré de ella en el secreto lenguaje sólo conocido por los contados iniciados; y que celosamente vigilaré la sagrada teoría de aquellos que quisieran profanarla para usarla en aplicaciones mundanas”. J. L. Massey Although the description of the field F 2 m is complicated, this field is extremely beautiful and also quite useful, because its computations can be done efficiently when implemented in hardware. There are several ways to describe arithmetic in F 2 m; the most common one is the so-called polynomial representation. Códigos y Criptografía Francisco Rodríguez Henríquez
Some definitions Here, we restrict our discussion to the numbers that belongs to the finite field F=GF(2 m) over K=GF(2). K is also known as the characteristic field. The elements of F are polynomials of degree less than m, with coefficients in K; that is, {am-1 xm-1+am-2 xm-2+. . . +a 2 x 2+a 1 x+a 0|ai= 0 or 1}. These elements are frequently written in vector form as (am-1. . . a 1 a 0). F has exactly 2 m-1 nonzero elements plus the zero element. Códigos y Criptografía Francisco Rodríguez Henríquez
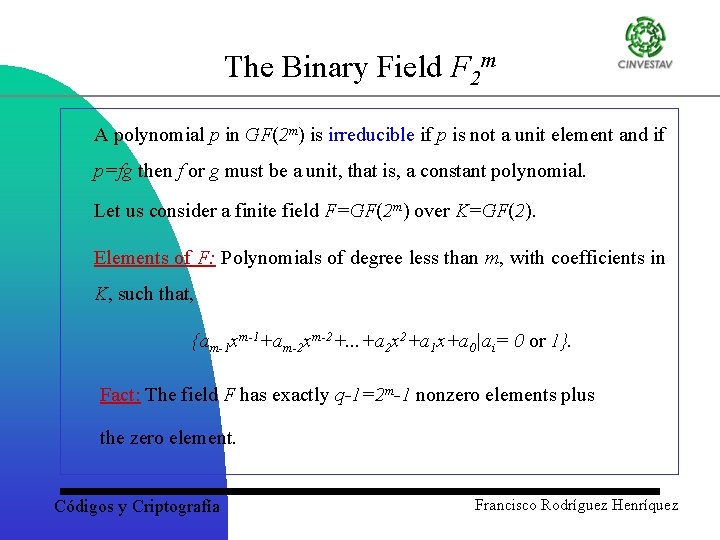
The Binary Field F 2 m A polynomial p in GF(2 m) is irreducible if p is not a unit element and if p=fg then f or g must be a unit, that is, a constant polynomial. Let us consider a finite field F=GF(2 m) over K=GF(2). Elements of F: Polynomials of degree less than m, with coefficients in K, such that, {am-1 xm-1+am-2 xm-2+. . . +a 2 x 2+a 1 x+a 0|ai= 0 or 1}. Fact: The field F has exactly q-1=2 m-1 nonzero elements plus the zero element. Códigos y Criptografía Francisco Rodríguez Henríquez
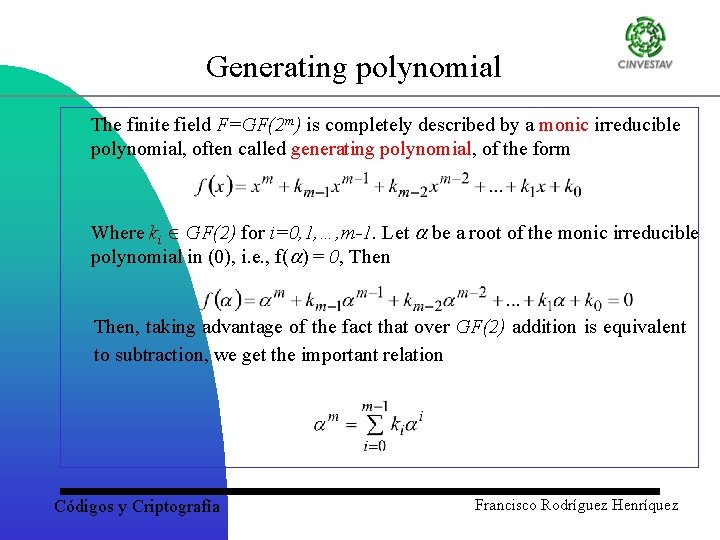
Generating polynomial The finite field F=GF(2 m) is completely described by a monic irreducible polynomial, often called generating polynomial, of the form Where ki GF(2) for i=0, 1, …, m-1. Let be a root of the monic irreducible polynomial in (0), i. e. , f( ) = 0, Then, taking advantage of the fact that over GF(2) addition is equivalent to subtraction, we get the important relation Códigos y Criptografía Francisco Rodríguez Henríquez
Generating polynomial and polynomial basis Then, we define the polynomial or canonical basis of GF(2 m) over GF(2) using the primitive element and its m first powers {1, , 2, …, m-1}, which happen to be linearly independent over GF(2). Códigos y Criptografía Francisco Rodríguez Henríquez
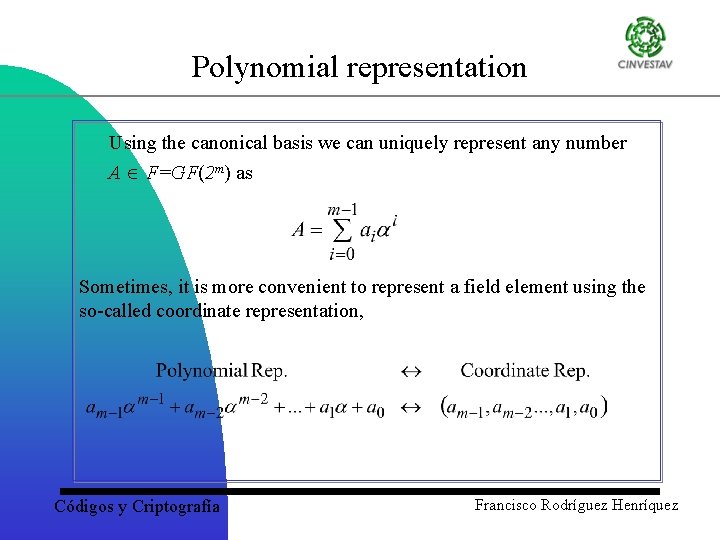
Polynomial representation Using the canonical basis we can uniquely represent any number A F=GF(2 m) as Sometimes, it is more convenient to represent a field element using the so-called coordinate representation, Códigos y Criptografía Francisco Rodríguez Henríquez
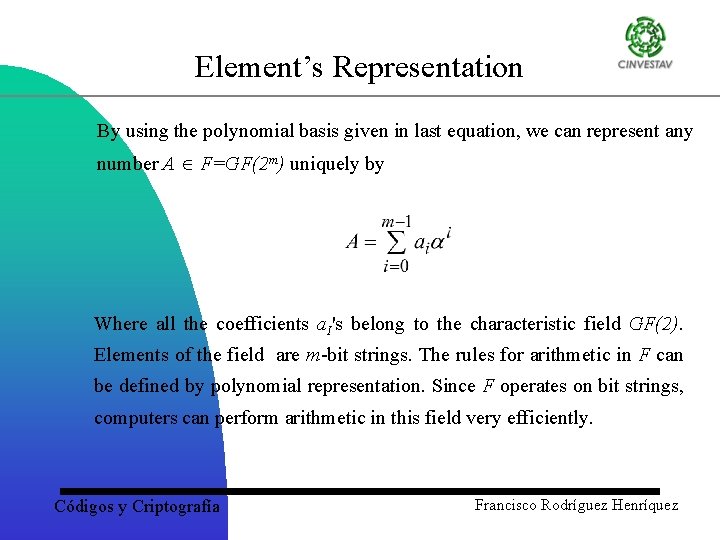
Element’s Representation By using the polynomial basis given in last equation, we can represent any number A F=GF(2 m) uniquely by Where all the coefficients a. I's belong to the characteristic field GF(2). Elements of the field are m-bit strings. The rules for arithmetic in F can be defined by polynomial representation. Since F operates on bit strings, computers can perform arithmetic in this field very efficiently. Códigos y Criptografía Francisco Rodríguez Henríquez
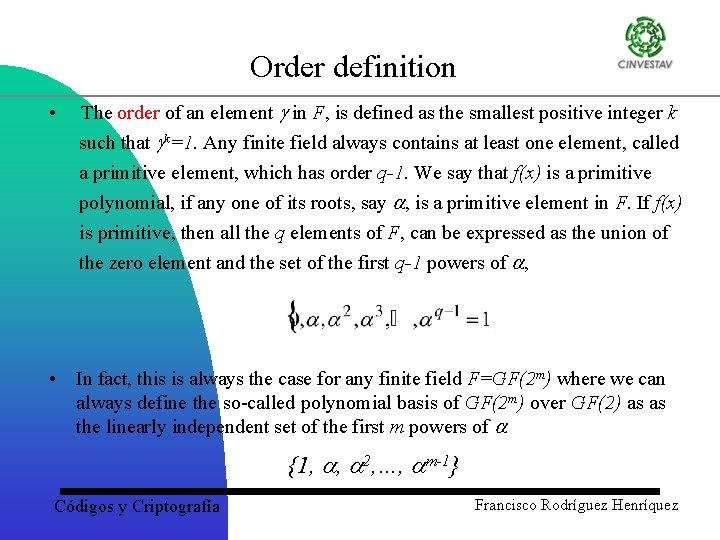
Order definition • The order of an element in F, is defined as the smallest positive integer k such that k=1. Any finite field always contains at least one element, called a primitive element, which has order q-1. We say that f(x) is a primitive polynomial, if any one of its roots, say , is a primitive element in F. If f(x) is primitive, then all the q elements of F, can be expressed as the union of the zero element and the set of the first q-1 powers of , • In fact, this is always the case for any finite field F=GF(2 m) where we can always define the so-called polynomial basis of GF(2 m) over GF(2) as as the linearly independent set of the first m powers of {1, , 2, …, m-1} Códigos y Criptografía Francisco Rodríguez Henríquez
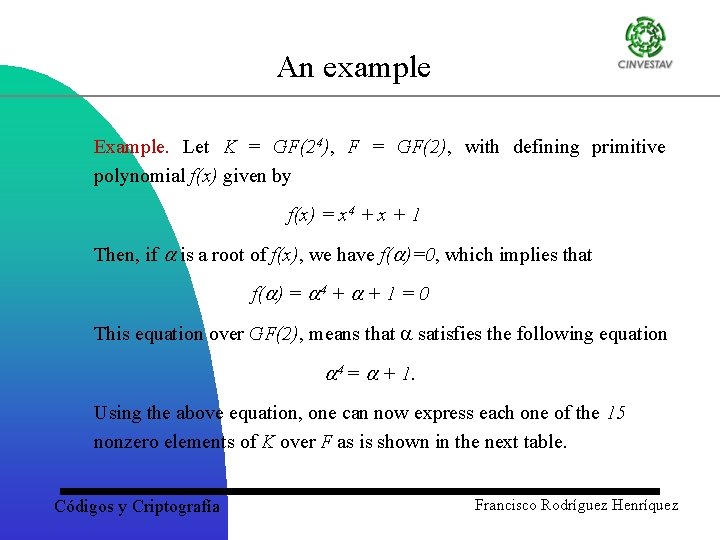
An example Example. Let K = GF(24), F = GF(2), with defining primitive polynomial f(x) given by f(x) = x 4 + x + 1 Then, if is a root of f(x), we have f( )=0, which implies that f( ) = 4 + + 1 = 0 This equation over GF(2), means that satisfies the following equation 4 = + 1. Using the above equation, one can now express each one of the 15 nonzero elements of K over F as is shown in the next table. Códigos y Criptografía Francisco Rodríguez Henríquez
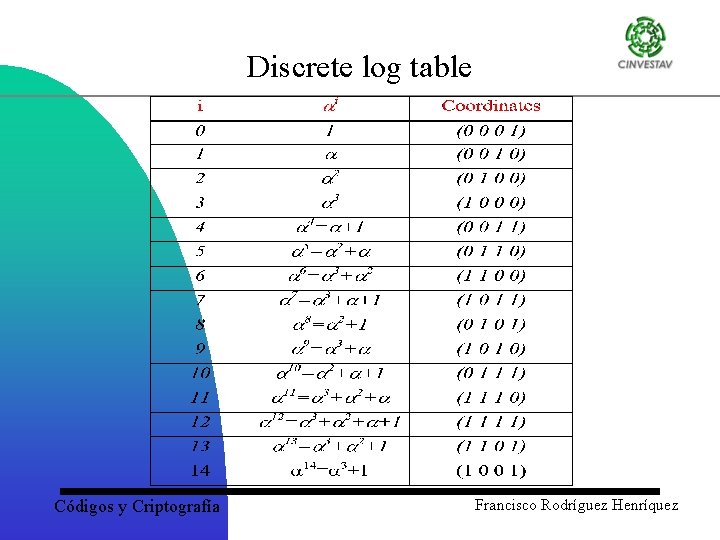
Discrete log table Códigos y Criptografía Francisco Rodríguez Henríquez
Finite fields: definitions and operations F 2 m finite field operations : Addition, Squaring, multiplication and inversion Códigos y Criptografía Francisco Rodríguez Henríquez
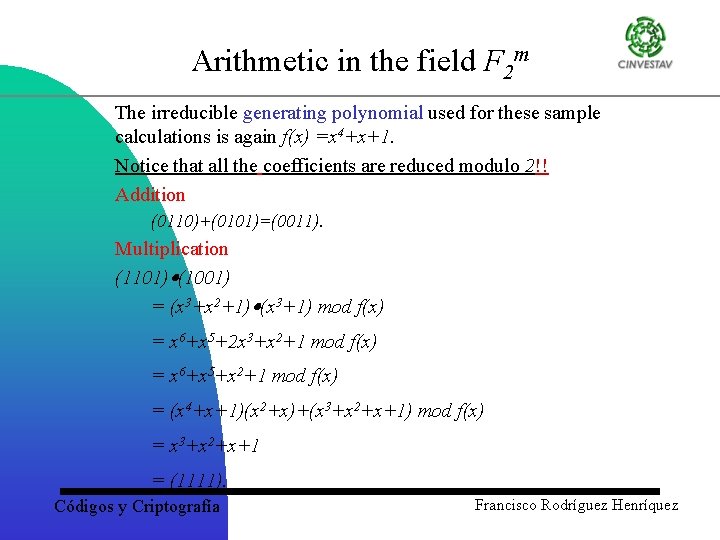
Arithmetic in the field F 2 m The irreducible generating polynomial used for these sample calculations is again f(x) =x 4+x+1. Notice that all the coefficients are reduced modulo 2!! Addition (0110)+(0101)=(0011). Multiplication (1101) (1001) = (x 3+x 2+1) (x 3+1) mod f(x) = x 6+x 5+2 x 3+x 2+1 mod f(x) = x 6+x 5+x 2+1 mod f(x) = (x 4+x+1)(x 2+x)+(x 3+x 2+x+1) mod f(x) = x 3+x 2+x+1 = (1111). Códigos y Criptografía Francisco Rodríguez Henríquez
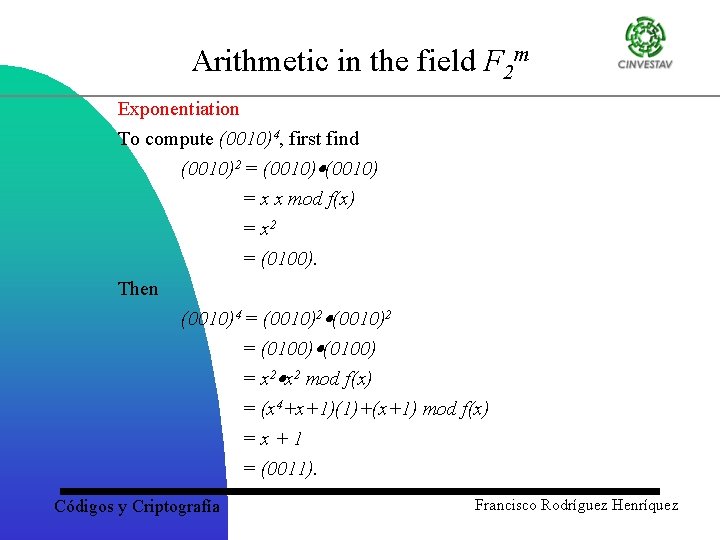
Arithmetic in the field F 2 m Exponentiation To compute (0010)4, first find (0010)2 = (0010) = x x mod f(x) = x 2 = (0100). Then (0010)4 = (0010)2 = (0100) = x 2 mod f(x) = (x 4+x+1)(1)+(x+1) mod f(x) =x+1 = (0011). Códigos y Criptografía Francisco Rodríguez Henríquez
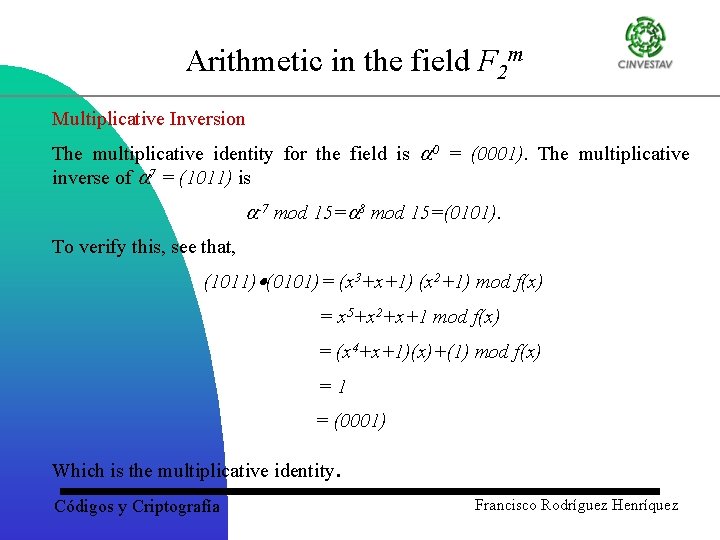
Arithmetic in the field F 2 m Multiplicative Inversion The multiplicative identity for the field is 0 = (0001). The multiplicative inverse of 7 = (1011) is -7 mod 15= 8 mod 15=(0101). To verify this, see that, (1011) (0101)= (x 3+x+1) (x 2+1) mod f(x) = x 5+x 2+x+1 mod f(x) = (x 4+x+1)(x)+(1) mod f(x) =1 = (0001) Which is the multiplicative identity Códigos y Criptografía . Francisco Rodríguez Henríquez
Field multipliers for software applications Códigos y Criptografía Francisco Rodríguez Henríquez
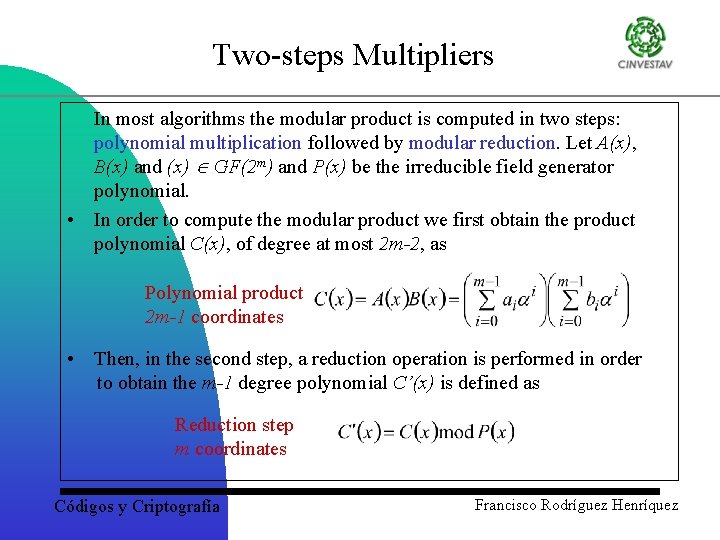
Two-steps Multipliers In most algorithms the modular product is computed in two steps: polynomial multiplication followed by modular reduction. Let A(x), B(x) and (x) GF(2 m) and P(x) be the irreducible field generator polynomial. • In order to compute the modular product we first obtain the product polynomial C(x), of degree at most 2 m-2, as Polynomial product 2 m-1 coordinates • Then, in the second step, a reduction operation is performed in order to obtain the m-1 degree polynomial C’(x) is defined as Reduction step m coordinates Códigos y Criptografía Francisco Rodríguez Henríquez
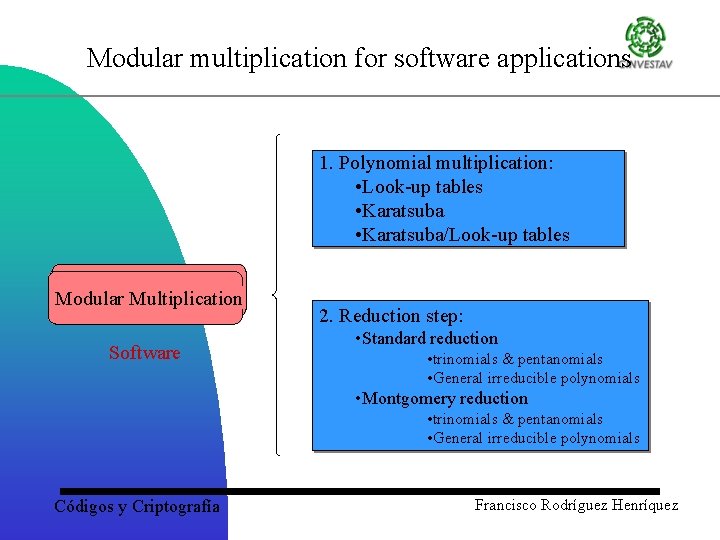
Modular multiplication for software applications 1. Polynomial multiplication: • Look-up tables • Karatsuba/Look-up tables Modular Multiplication Software 2. Reduction step: • Standard reduction • trinomials & pentanomials • General irreducible polynomials • Montgomery reduction • trinomials & pentanomials • General irreducible polynomials Códigos y Criptografía Francisco Rodríguez Henríquez
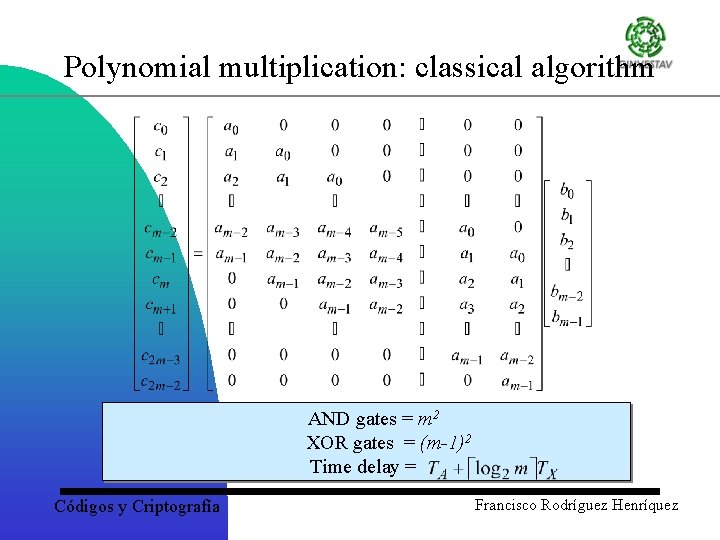
Polynomial multiplication: classical algorithm AND gates = m 2 XOR gates = (m-1)2 Time delay = Códigos y Criptografía Francisco Rodríguez Henríquez
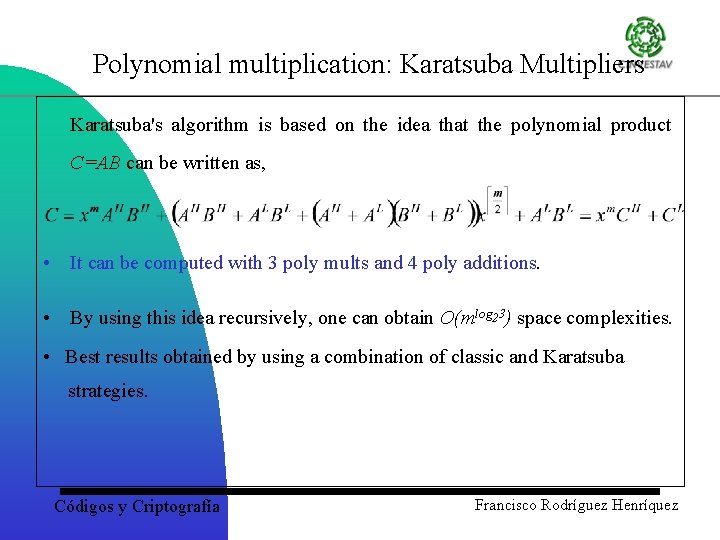
Polynomial multiplication: Karatsuba Multipliers Karatsuba's algorithm is based on the idea that the polynomial product C=AB can be written as, • It can be computed with 3 poly mults and 4 poly additions. • By using this idea recursively, one can obtain O(mlog 23) space complexities. • Best results obtained by using a combination of classic and Karatsuba strategies. Códigos y Criptografía Francisco Rodríguez Henríquez
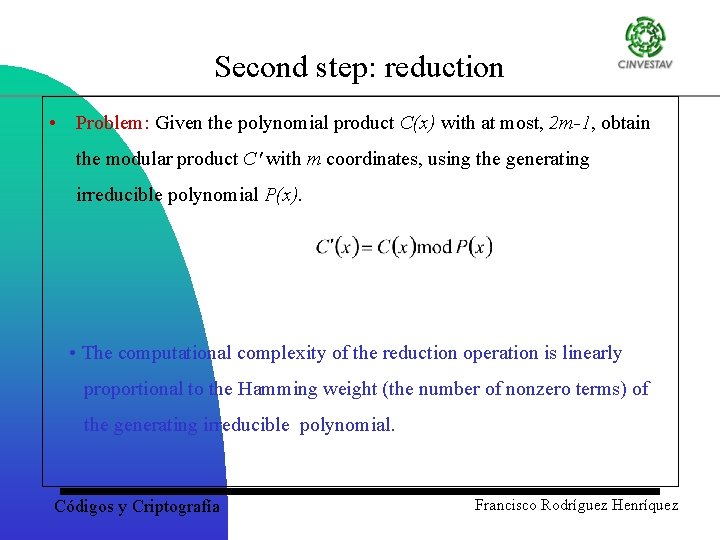
Second step: reduction • Problem: Given the polynomial product C(x) with at most, 2 m-1, obtain the modular product C' with m coordinates, using the generating irreducible polynomial P(x). • The computational complexity of the reduction operation is linearly proportional to the Hamming weight (the number of nonzero terms) of the generating irreducible polynomial. Códigos y Criptografía Francisco Rodríguez Henríquez
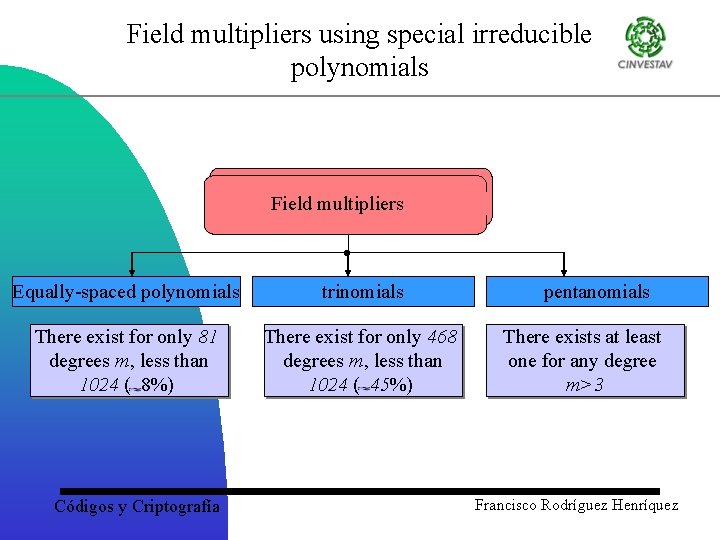
Field multipliers using special irreducible polynomials Field multipliers • Equally-spaced polynomials trinomials There exist for only 81 degrees m, less than 1024 ( 8%) There exist for only 468 degrees m, less than 1024 ( 45%) Códigos y Criptografía pentanomials There exists at least one for any degree m>3 Francisco Rodríguez Henríquez
Performance criteria and element representation • The most important measures of the performance for software implementations of the arithmetic operations in the Galois • field GF(2 m) are, • the total time required for execution (speed) and; • the amount of memory required for the algorithm (memory requirements) Códigos y Criptografía Francisco Rodríguez Henríquez
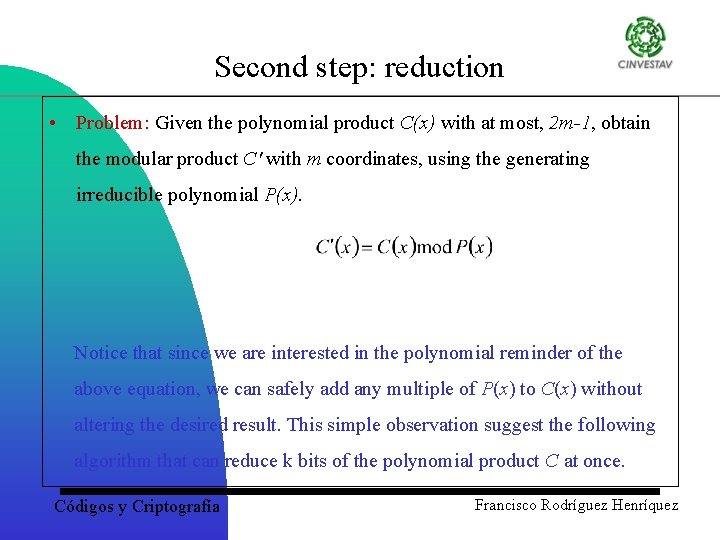
Second step: reduction • Problem: Given the polynomial product C(x) with at most, 2 m-1, obtain the modular product C' with m coordinates, using the generating irreducible polynomial P(x). Notice that since we are interested in the polynomial reminder of the above equation, we can safely add any multiple of P(x) to C(x) without altering the desired result. This simple observation suggest the following algorithm that can reduce k bits of the polynomial product C at once. Códigos y Criptografía Francisco Rodríguez Henríquez
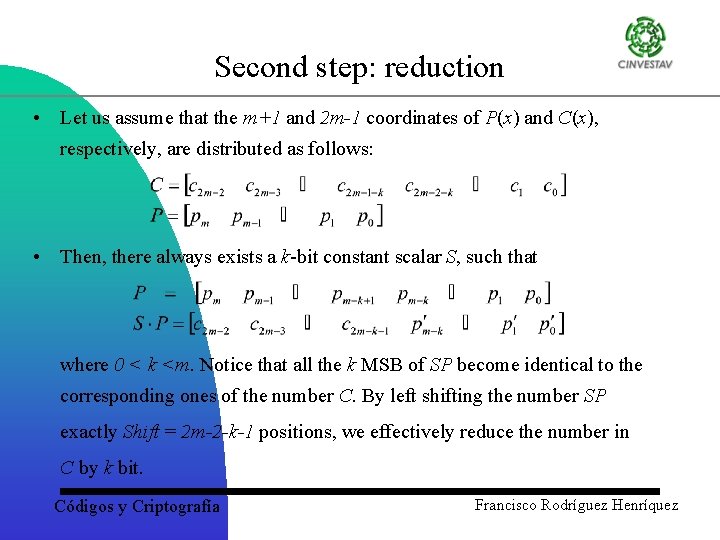
Second step: reduction • Let us assume that the m+1 and 2 m-1 coordinates of P(x) and C(x), respectively, are distributed as follows: • Then, there always exists a k-bit constant scalar S, such that where 0 < k <m. Notice that all the k MSB of SP become identical to the corresponding ones of the number C. By left shifting the number SP exactly Shift = 2 m-2 -k-1 positions, we effectively reduce the number in C by k bit. Códigos y Criptografía Francisco Rodríguez Henríquez
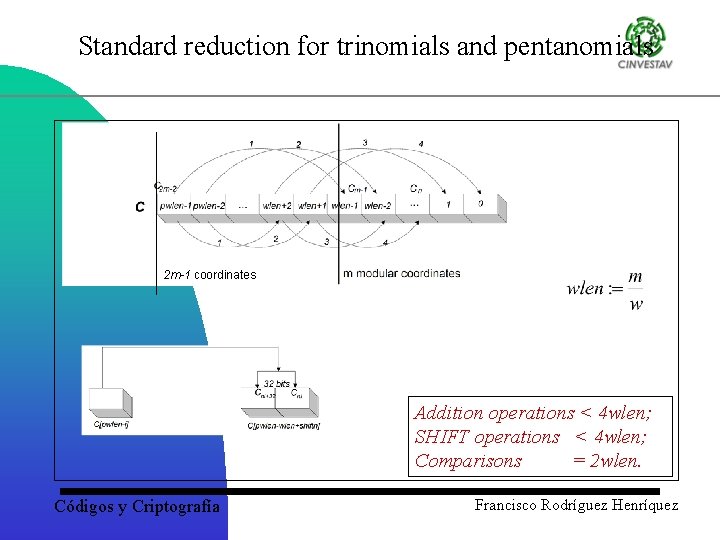
Standard reduction for trinomials and pentanomials 2 m-1 coordinates Addition operations < 4 wlen; SHIFT operations < 4 wlen; Comparisons = 2 wlen. Códigos y Criptografía Francisco Rodríguez Henríquez
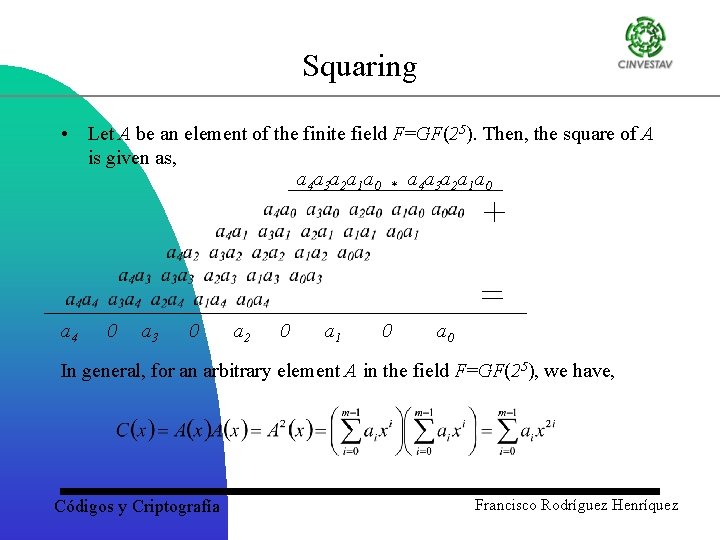
Squaring • Let A be an element of the finite field F=GF(25). Then, the square of A is given as, a 4 a 3 a 2 a 1 a 0 * a 4 a 3 a 2 a 1 a 0 a 4 0 a 3 0 a 2 0 a 1 0 a 0 In general, for an arbitrary element A in the field F=GF(25), we have, Códigos y Criptografía Francisco Rodríguez Henríquez
![Squaring rct_word sqr_table_low[256] = { 0, 1, 4, 5, 16, 17, 20, 21, 64 Squaring rct_word sqr_table_low[256] = { 0, 1, 4, 5, 16, 17, 20, 21, 64](http://slidetodoc.com/presentation_image_h/126f467f9b5b7d530561673b34028ba7/image-37.jpg)
Squaring rct_word sqr_table_low[256] = { 0, 1, 4, 5, 16, 17, 20, 21, 64 65, 68, 69, 80, 81, 84, 85, 256, 257, 260, 261, 272, 273, 276, 277, 320, 321, 324, 325, 336, 337, 340, 341, 1024, 1025, 1028, 1029, 1040, 1041, 1044, 1045, 1088, 1089, 1092, 1093, 1104, 1105, 1108, 1109, 1280, 1281, 1284, 1285, 1296, 1297, 1300, 1301, 1344, 1345, 1348, 1349, 1360, 1361, 1364, 1365, 4096, 4097, 4100, 4101, 4112, 4113, 4116, 4117, 4160, 4161, 4164, 4165, 4176, 4177, 4180, 4181, 4352, 4353, 4356, 4357, 4368, 4369, 4372, 4373, 4416, 4417, 4420, 4421, 4432, 4433, 4436, 4437, 5120, 5121, 5124, 5125, 5136, 5137, 5140, 5141, 5184, 5185, 5188, 5189, 5200, 5201, 5204, 5205, 5376, 5377, 5380, 5381, 5392, 5393, 5396, 5397, 5440, 5441, 5444, 5445, 5456, 5457, 5460, 5461, 16384, 16385, 16388, 16389, 16400, 16401, 16404, 16405, 16448, 16449, 16452, 16453, 16464, 16465, 16468, 16469, 16640, 16641, 16644, 16645, 16656, 16657, 16660, 16661, 16704, 16705, 16708, 16709, 16720, 16721, 16724, 16725, 17408, 17409, 17412, 17413, 17424, 17425, 17428, 17429, 17472, 17473, 17476, 17477, 17488, 17489, 17492, 17493, 17664, 17665, 17668, 17669, 17680, 17681, 17684, 17685, 17728, 17729, 17732, 17733, 17744, 17745, 17748, 17749, 20480, 20481, 20484, 20485, 20496, 20497, 20500, 20501, 20544, 20545, 20548, 20549, 20560, 20561, 20564, 20565, 20736, 20737, 20740, 20741, 20752, 20753, 20756, 20757, 20800, 20801, 20804, 20805, 20816, 20817, 20820, 20821, 21504, 21505, 21508, 21509, 21520, 21521, 21524, 21525, 21568, 21569, 21572, 21573, 21584, 21585, 21588, 21589, 21760, 21761, 21764, 21765, 21776, 21777, 21780, 21781, 21824, 21825, 21828, 21829, 21840, 21841, 21844, 21845 }; Códigos y Criptografía Francisco Rodríguez Henríquez
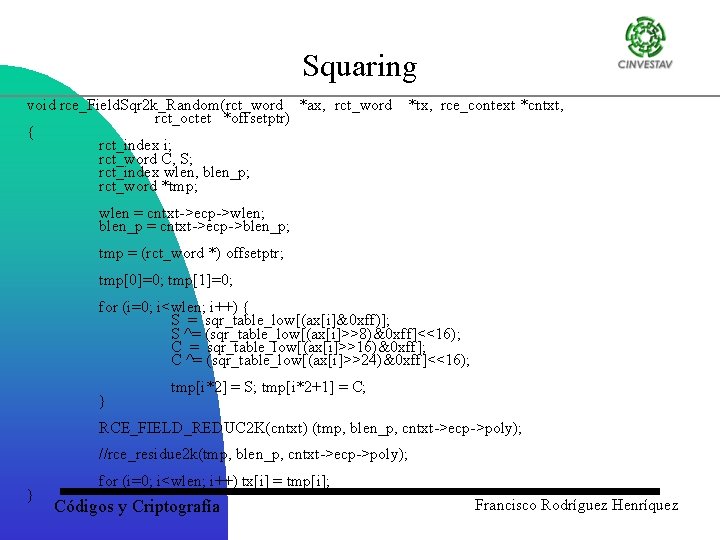
Squaring void rce_Field. Sqr 2 k_Random(rct_word *ax, rct_word rct_octet *offsetptr) { rct_index i; rct_word C, S; rct_index wlen, blen_p; rct_word *tmp; *tx, rce_context *cntxt, wlen = cntxt->ecp->wlen; blen_p = cntxt->ecp->blen_p; tmp = (rct_word *) offsetptr; tmp[0]=0; tmp[1]=0; for (i=0; i<wlen; i++) { S = sqr_table_low[(ax[i]&0 xff)]; S ^= (sqr_table_low[(ax[i]>>8)&0 xff]<<16); C = sqr_table_low[(ax[i]>>16)&0 xff]; C ^= (sqr_table_low[(ax[i]>>24)&0 xff]<<16); } tmp[i*2] = S; tmp[i*2+1] = C; RCE_FIELD_REDUC 2 K(cntxt) (tmp, blen_p, cntxt->ecp->poly); //rce_residue 2 k(tmp, blen_p, cntxt->ecp->poly); } for (i=0; i<wlen; i++) tx[i] = tmp[i]; Códigos y Criptografía Francisco Rodríguez Henríquez
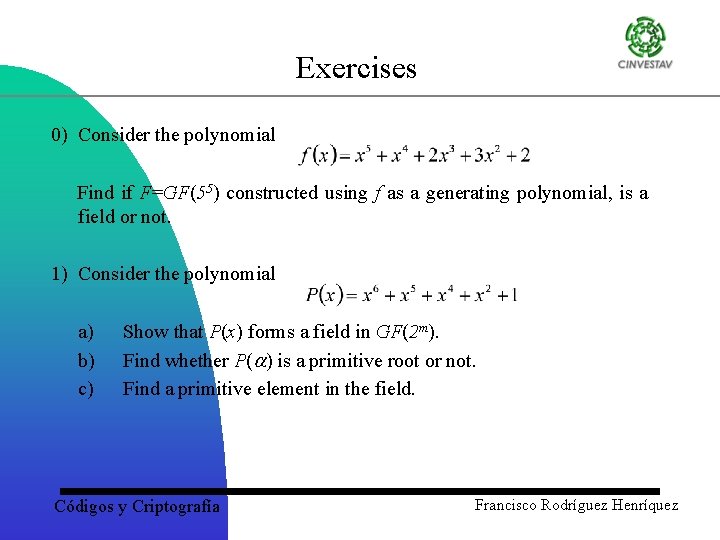
Exercises 0) Consider the polynomial Find if F=GF(55) constructed using f as a generating polynomial, is a field or not. 1) Consider the polynomial a) b) c) Show that P(x) forms a field in GF(2 m). Find whether P( ) is a primitive root or not. Find a primitive element in the field. Códigos y Criptografía Francisco Rodríguez Henríquez
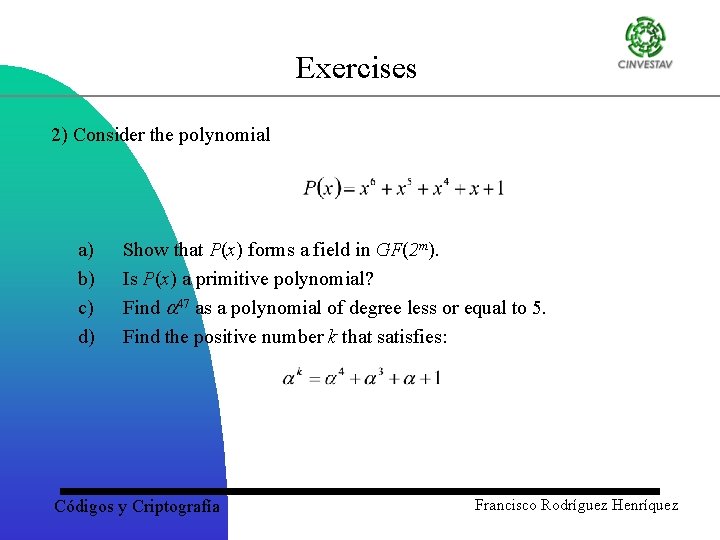
Exercises 2) Consider the polynomial a) b) c) d) Show that P(x) forms a field in GF(2 m). Is P(x) a primitive polynomial? Find 47 as a polynomial of degree less or equal to 5. Find the positive number k that satisfies: Códigos y Criptografía Francisco Rodríguez Henríquez
Elliptic curve primitives: Key-pair generation, Signing and Verification Códigos y Criptografía Francisco Rodríguez Henríquez
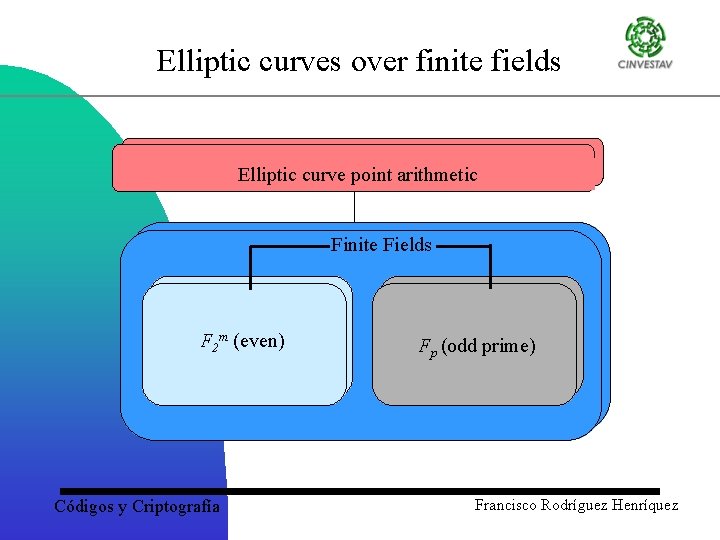
Elliptic curves over finite fields Elliptic curve point arithmetic Finite Fields F 2 m (even) Códigos y Criptografía Fp (odd prime) Francisco Rodríguez Henríquez
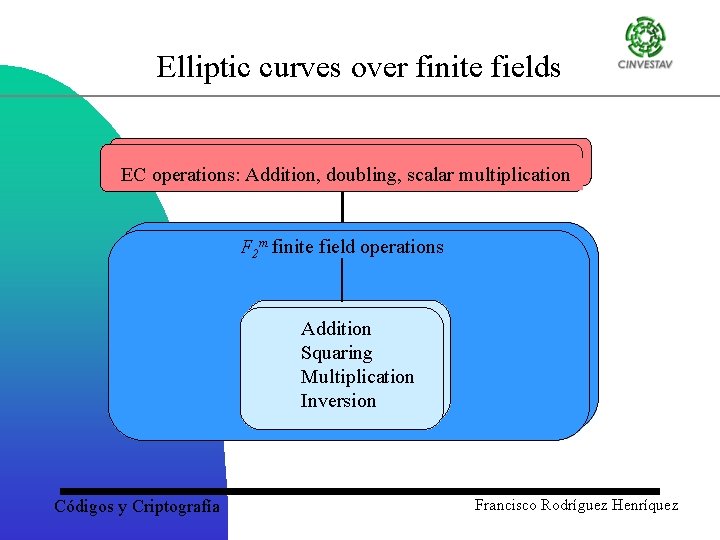
Elliptic curves over finite fields EC operations: Addition, doubling, scalar multiplication F 2 m finite field operations Addition Squaring Multiplication Inversion Códigos y Criptografía Francisco Rodríguez Henríquez
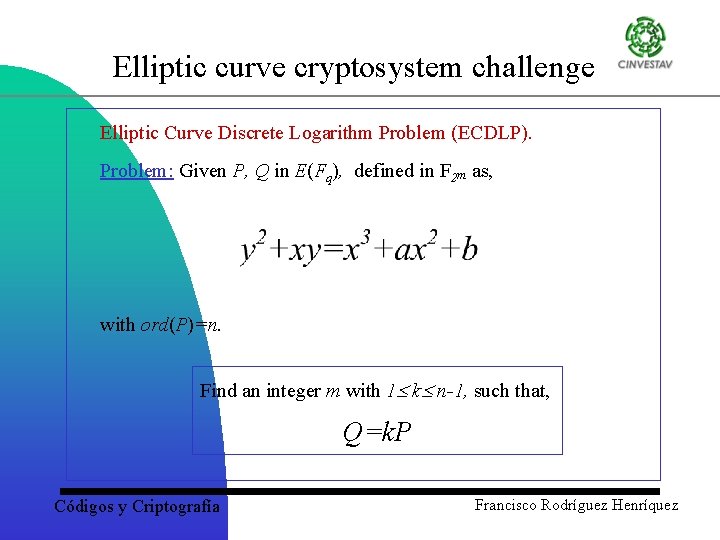
Elliptic curve cryptosystem challenge Elliptic Curve Discrete Logarithm Problem (ECDLP). Problem: Given P, Q in E(Fq), defined in F 2 m as, with ord(P)=n. Find an integer m with 1 k n-1, such that, Q=k. P Códigos y Criptografía Francisco Rodríguez Henríquez
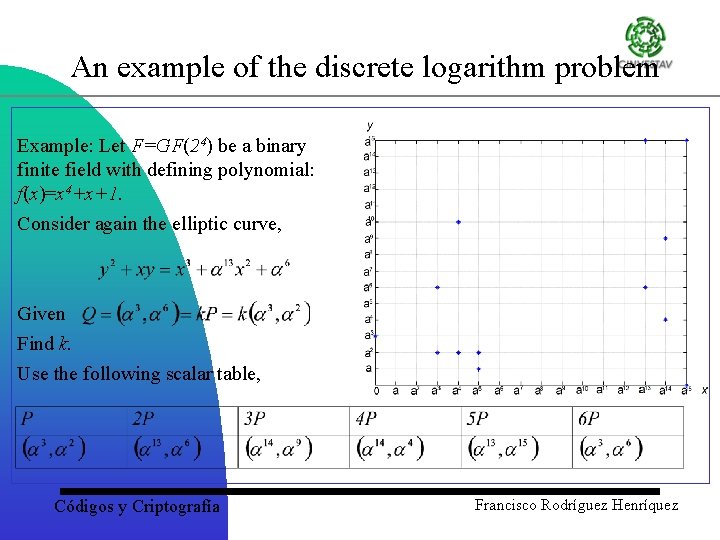
An example of the discrete logarithm problem Example: Let F=GF(24) be a binary finite field with defining polynomial: f(x)=x 4+x+1. Consider again the elliptic curve, Given Find k. Use the following scalar table, Códigos y Criptografía Francisco Rodríguez Henríquez
Order notions in elliptic curves A Point of Prime Order Given the elliptic curve, E, defined over the finite field, Fq , we want to fix a special point that will be used to mask the private key in a public/private key pair. The properties of P are important to the security of our system. Not just any point will do: we need a point P, whose order n is prime; the larger the prime is , the more secure the cryptosystem is. Remember that P is of the form P=(x, y) where x and y satisfy the elliptic curve equation. Usually, we write x and y as x. P and y. P. Therefore, the special point P gives us two parameters: • A point P=(x. P, y. P) of prime order • The order n of P P is sometimes called the base point. Códigos y Criptografía Francisco Rodríguez Henríquez
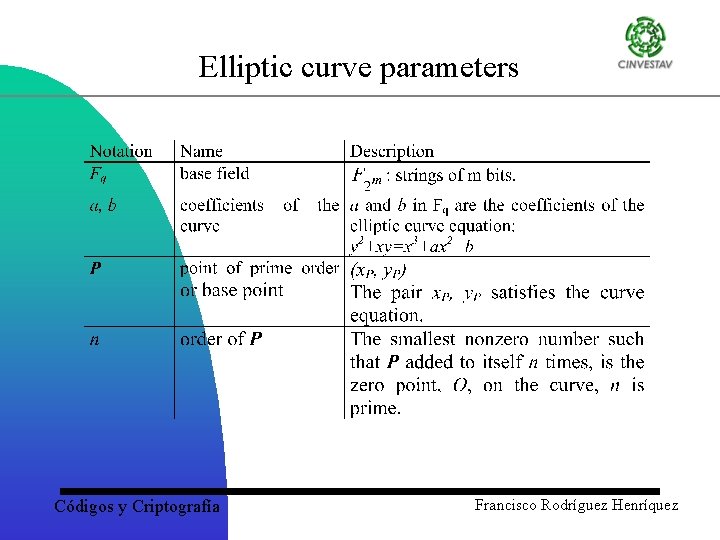
Elliptic curve parameters Códigos y Criptografía Francisco Rodríguez Henríquez
Elliptic Curve Key Pair Generation Elliptic curve parameters can be used to generate a public/private key pair. Creating a key pair To compute a public/private key pair: 1. Choose a random value, d, between 1 and n– 1. 2. Compute the elliptic curve point Q=d. P. The key pair is (Q, d): Q is the public key, d is the private key. Códigos y Criptografía Francisco Rodríguez Henríquez
Elliptic curves and Finite fields The fields GF(p) and GF(2 m) can be used: • GF(p) – Montgomery – Special primes : 2 k-c, 2 k-1 etc. • GF(2 m) – Polynomial Basis, Normal Basis – Trinomials, all-one-polynomials – Composite Fields, Montgomery GF (2 m) offers higher performance and less area consumption. Códigos y Criptografía Francisco Rodríguez Henríquez
- Slides: 49