AES Advanced Encryption Standard Advanced Encryption Standard Adopted

![AES Algorithm Key Expansion w[0] w[1] w[2] w[3] 11 55 99 CC 22 66 AES Algorithm Key Expansion w[0] w[1] w[2] w[3] 11 55 99 CC 22 66](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-13.jpg)
![AES Algorithm Key Expansion w[0] w[1] w[2] w[3] w[4] 11 55 99 CC D AES Algorithm Key Expansion w[0] w[1] w[2] w[3] w[4] 11 55 99 CC D](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-17.jpg)
![AES Algorithm Key Expansion w[0] w[1] w[2] w[3] w[4] 11 55 99 CC D AES Algorithm Key Expansion w[0] w[1] w[2] w[3] w[4] 11 55 99 CC D](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-19.jpg)
![AES Algorithm Add. Round. Key State Expanded Key w[0] w[4] After Add. Round. Key AES Algorithm Add. Round. Key State Expanded Key w[0] w[4] After Add. Round. Key](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-23.jpg)
![AES Algorithm Key. Expansion(byte key[4*Nk], word w[Nb*(Nr+1)], Nk) Cipher(byte in[4*Nb], byte out[4*Nb], word w[Nb*(Nr+1)]) AES Algorithm Key. Expansion(byte key[4*Nk], word w[Nb*(Nr+1)], Nk) Cipher(byte in[4*Nb], byte out[4*Nb], word w[Nb*(Nr+1)])](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-33.jpg)
- Slides: 48

AES Advanced Encryption Standard
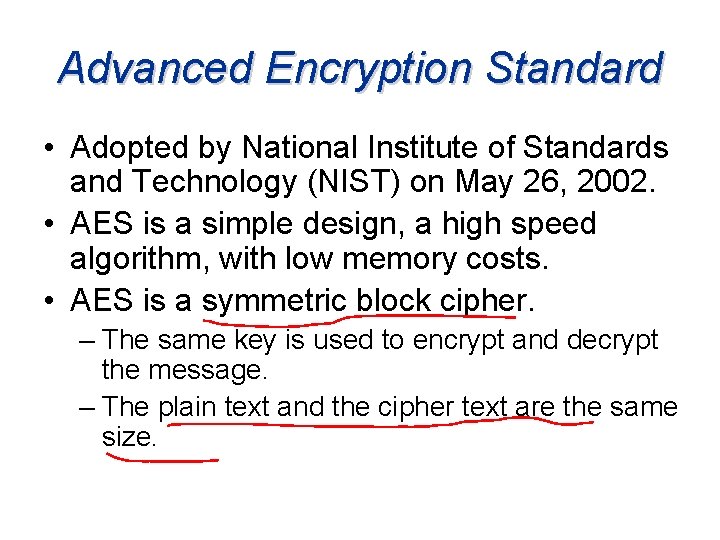
Advanced Encryption Standard • Adopted by National Institute of Standards and Technology (NIST) on May 26, 2002. • AES is a simple design, a high speed algorithm, with low memory costs. • AES is a symmetric block cipher. – The same key is used to encrypt and decrypt the message. – The plain text and the cipher text are the same size.
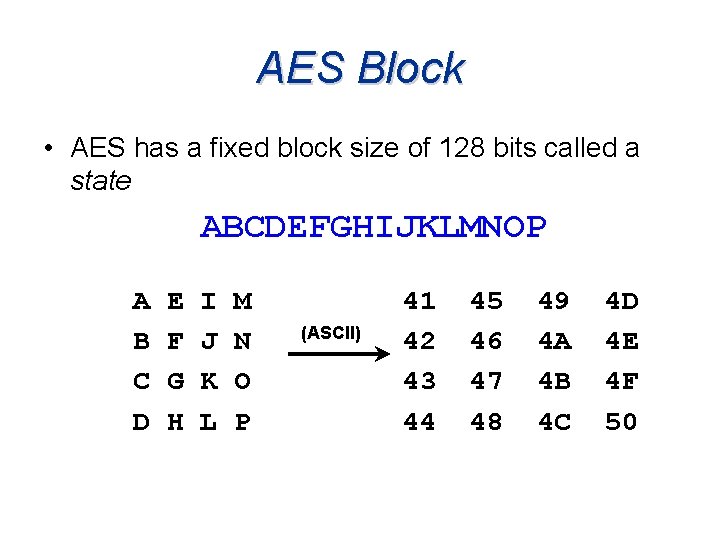
AES Block • AES has a fixed block size of 128 bits called a state ABCDEFGHIJKLMNOP A B C D E F G H I J K L M N O P (ASCII) 41 42 43 44 45 46 47 48 49 4 A 4 B 4 C 4 D 4 E 4 F 50
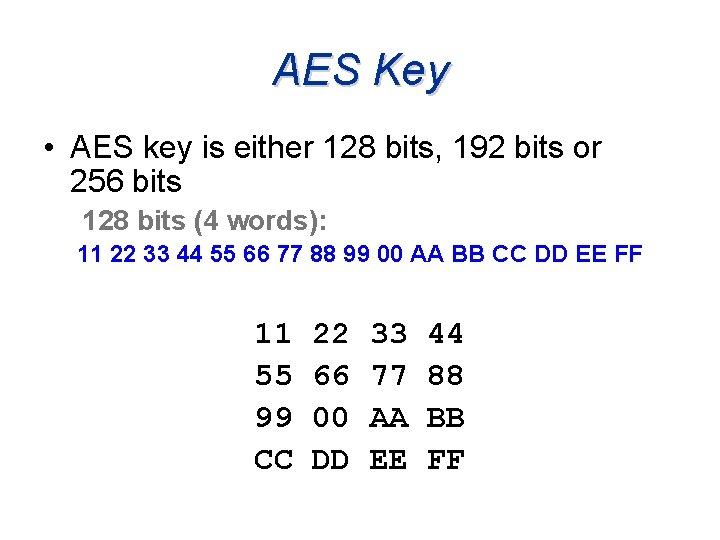
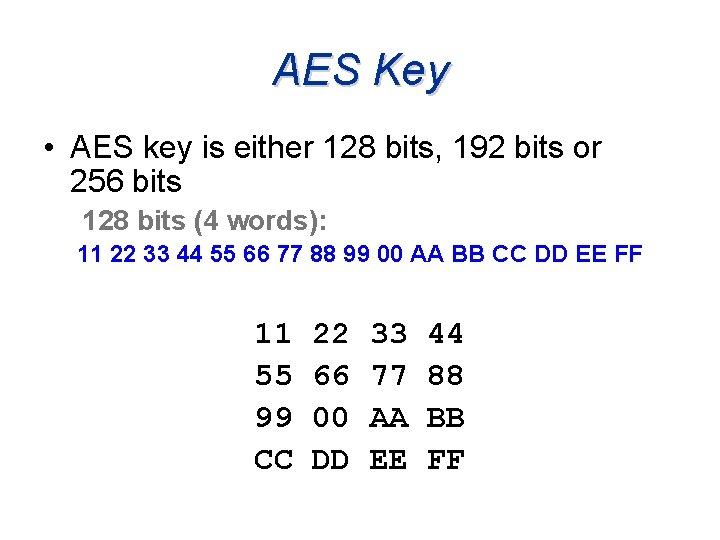
AES Key • AES key is either 128 bits, 192 bits or 256 bits 128 bits (4 words): 11 22 33 44 55 66 77 88 99 00 AA BB CC DD EE FF 11 55 99 CC 22 66 00 DD 33 77 AA EE 44 88 BB FF
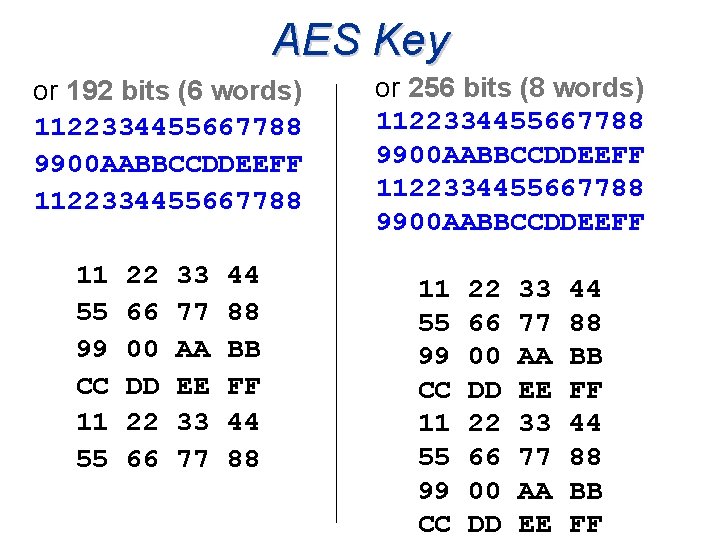
AES Key or 192 bits (6 words) 1122334455667788 9900 AABBCCDDEEFF 1122334455667788 11 55 99 CC 11 55 22 66 00 DD 22 66 33 77 AA EE 33 77 44 88 BB FF 44 88 or 256 bits (8 words) 1122334455667788 9900 AABBCCDDEEFF 11 55 99 CC 22 66 00 DD 33 77 AA EE 44 88 BB FF
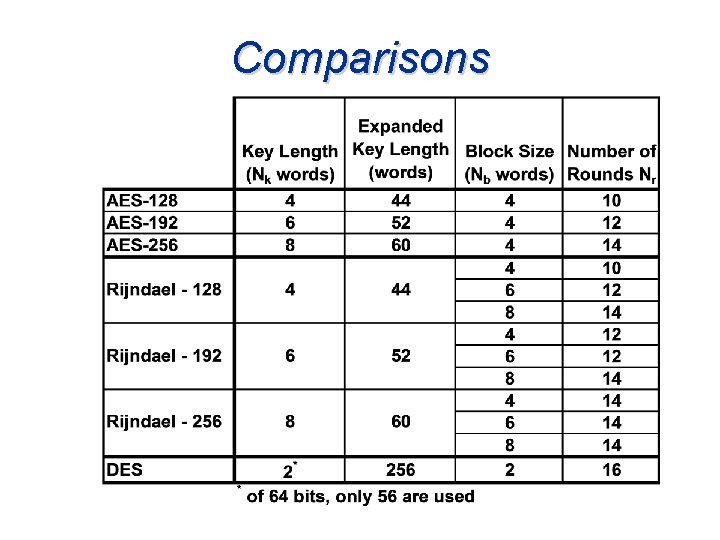
Comparisons
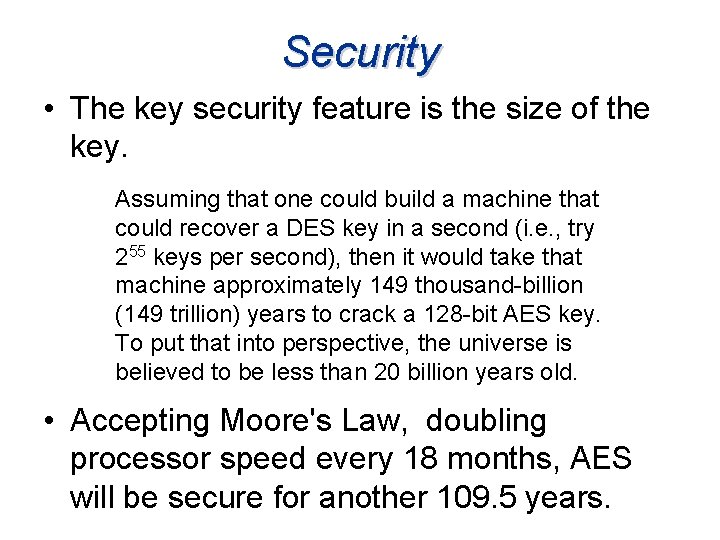
Security • The key security feature is the size of the key. Assuming that one could build a machine that could recover a DES key in a second (i. e. , try 255 keys per second), then it would take that machine approximately 149 thousand-billion (149 trillion) years to crack a 128 -bit AES key. To put that into perspective, the universe is believed to be less than 20 billion years old. • Accepting Moore's Law, doubling processor speed every 18 months, AES will be secure for another 109. 5 years.
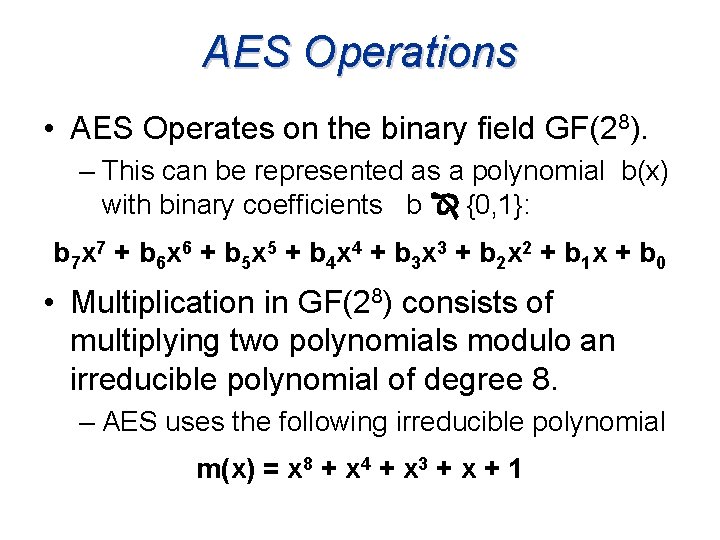
AES Operations • AES Operates on the binary field GF(28). – This can be represented as a polynomial b(x) with binary coefficients b {0, 1}: b 7 x 7 + b 6 x 6 + b 5 x 5 + b 4 x 4 + b 3 x 3 + b 2 x 2 + b 1 x + b 0 • Multiplication in GF(28) consists of multiplying two polynomials modulo an irreducible polynomial of degree 8. – AES uses the following irreducible polynomial m(x) = x 8 + x 4 + x 3 + x + 1
AES Algorithm
AES Algorithm
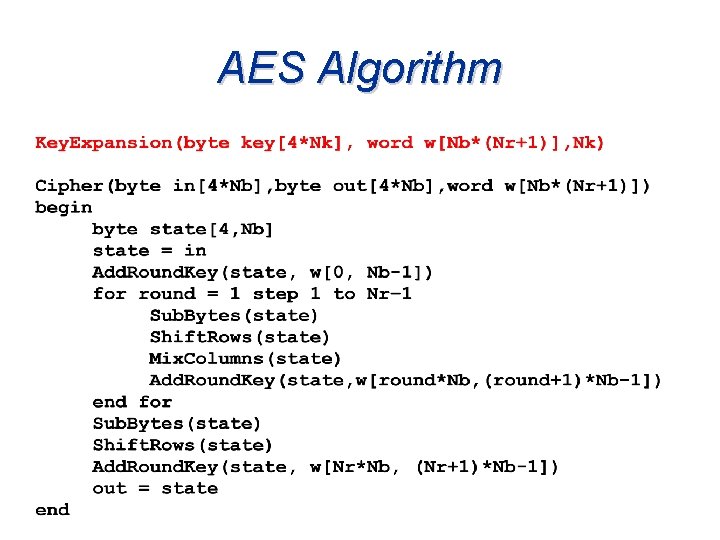
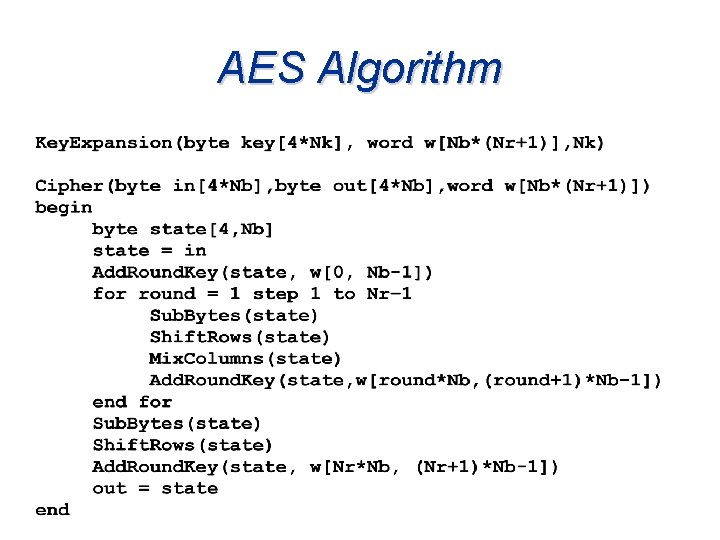
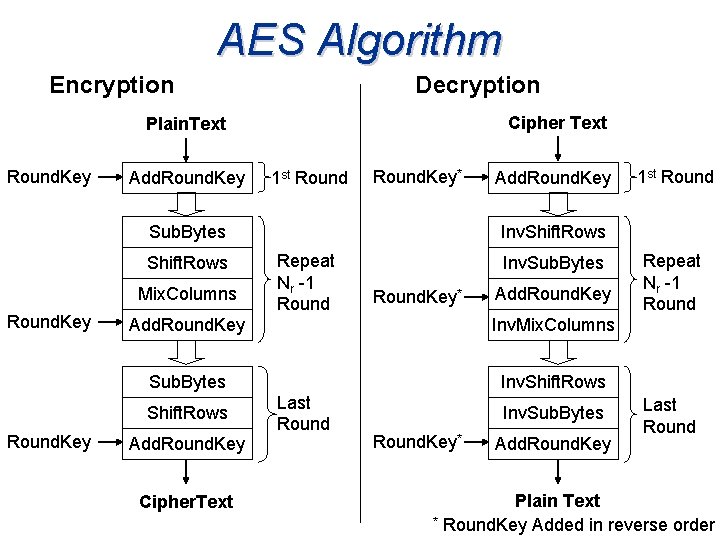
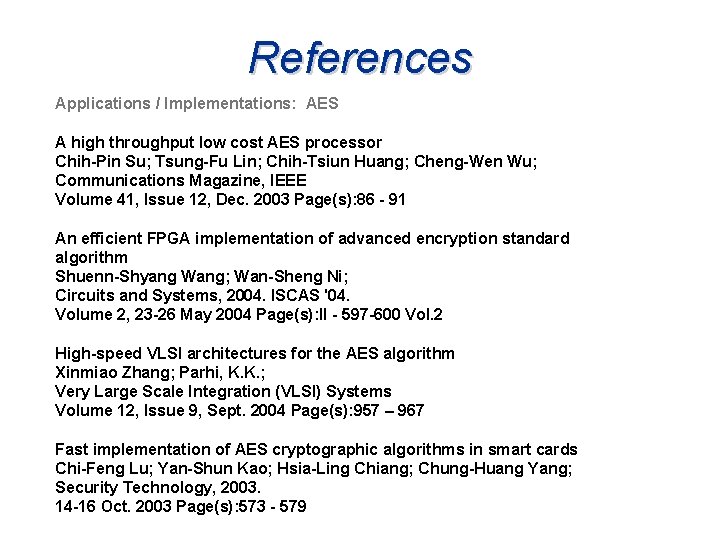
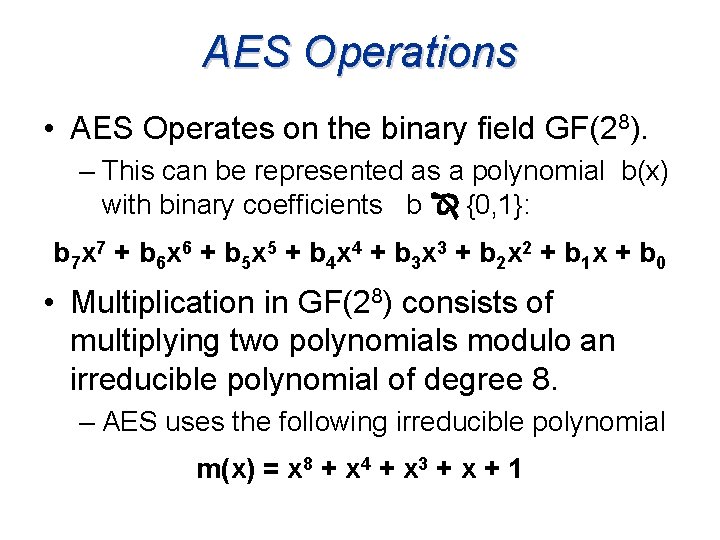
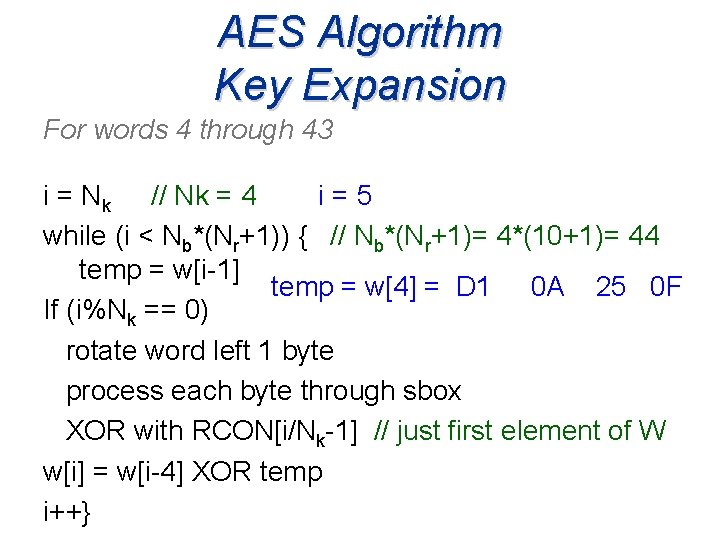
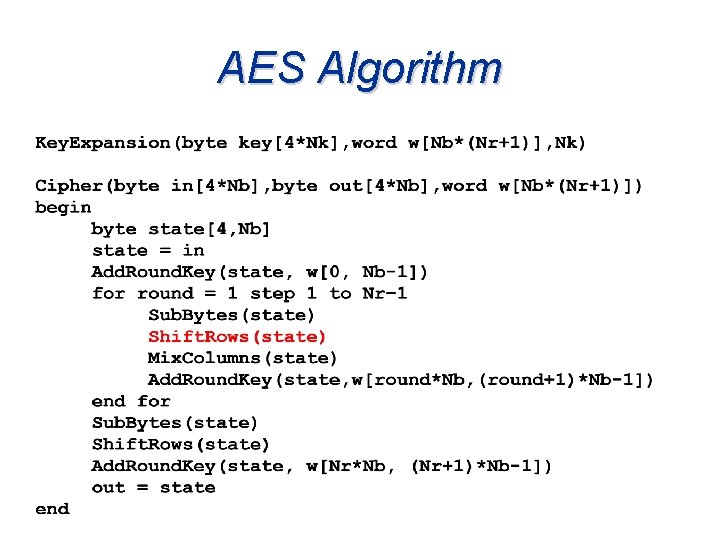
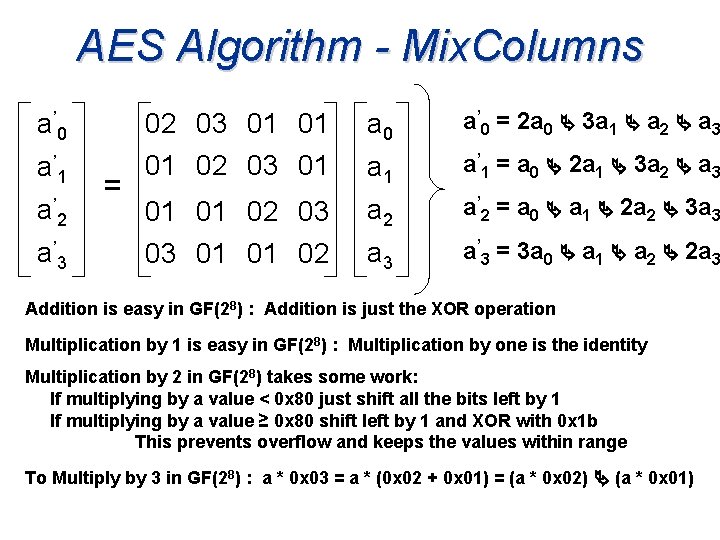
AES Algorithm Key Expansion – Sample Key: 11223344556677889900 AABBCCDDEEFF • The first 4 (Nk) words are set equal to the key w[0] w[1] w[2] w[3] 11 55 99 CC 22 66 00 DD 33 77 AA EE 44 88 BB FF
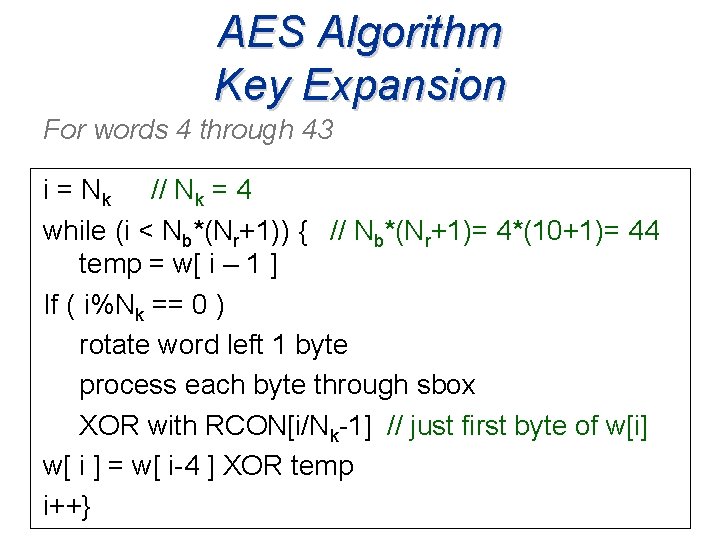
AES Algorithm Key Expansion For words 4 through 43 i = Nk // Nk = 4 while (i < Nb*(Nr+1)) { // Nb*(Nr+1)= 4*(10+1)= 44 temp = w[ i – 1 ] If ( i%Nk == 0 ) rotate word left 1 byte process each byte through sbox XOR with RCON[i/Nk-1] // just first byte of w[i] w[ i ] = w[ i-4 ] XOR temp i++}
![AES Algorithm Key Expansion w0 w1 w2 w3 11 55 99 CC 22 66 AES Algorithm Key Expansion w[0] w[1] w[2] w[3] 11 55 99 CC 22 66](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-13.jpg)
AES Algorithm Key Expansion w[0] w[1] w[2] w[3] 11 55 99 CC 22 66 00 DD 33 77 AA EE 44 88 BB FF i=4 i = Nk // Nk = 4 while (i < Nb*(Nr+1)) { // Nb*(Nr+1)= 4*(10+1)= 44 temp = w[ i - 1 ] temp = w[3] = CC DD EE FF
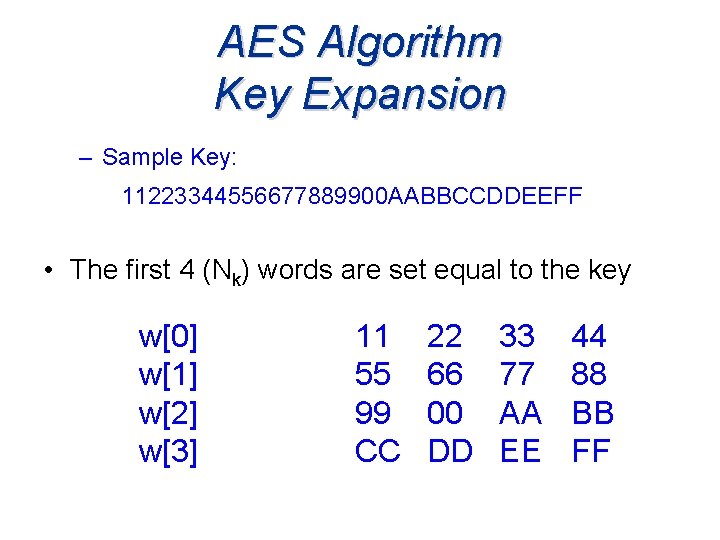
AES Algorithm Key Expansion If ( i%Nk == 0 ) temp = CC DD EE FF temp = DD EE FF CC rotate word left 1 byte process each byte through sbox temp = sbox[DD] sbox[EE] sbox[FF] sbox[CC] = C 1 28 16 4 B XOR with RCON[i/Nk-1] RCON[0] = 01 temp = (C 1 01) 28 16 4 B temp = C 0 28 16 4 B
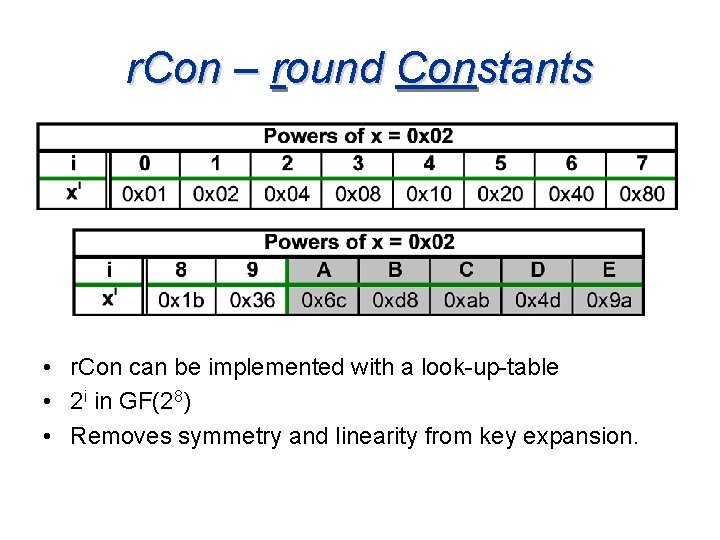
r. Con – round Constants • r. Con can be implemented with a look-up-table • 2 i in GF(28) • Removes symmetry and linearity from key expansion.
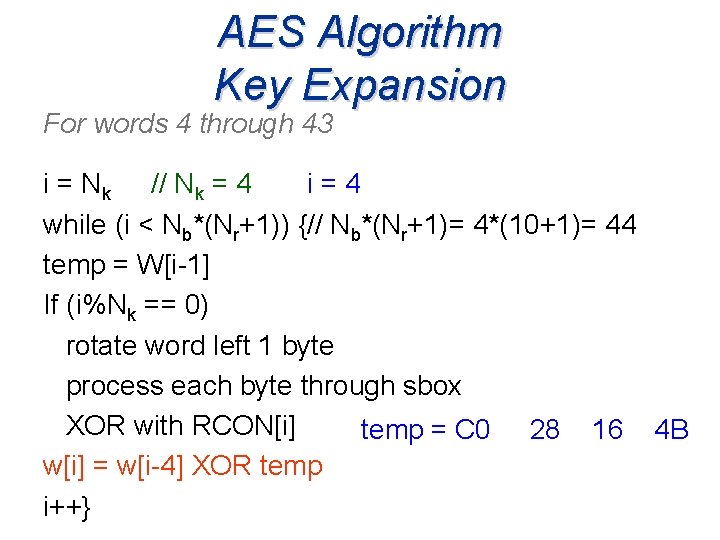
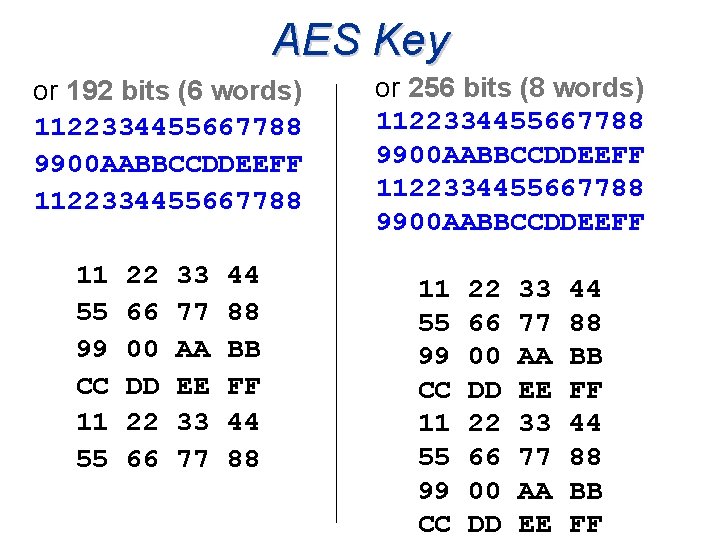
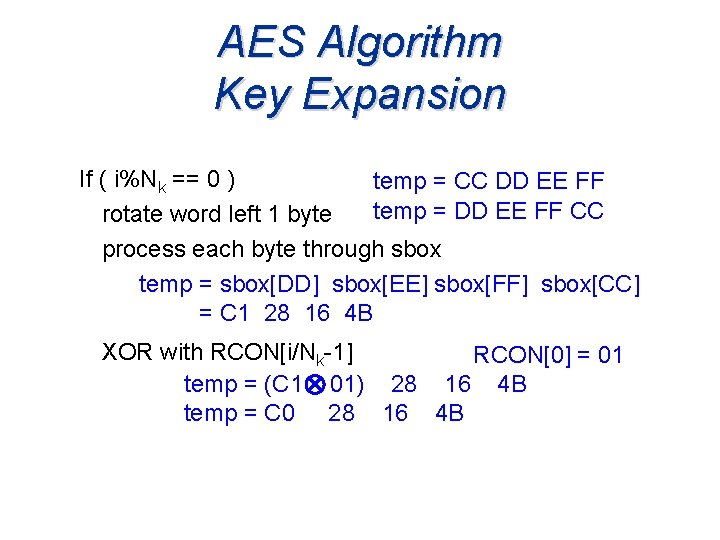
AES Algorithm Key Expansion For words 4 through 43 i=4 i = Nk // Nk = 4 while (i < Nb*(Nr+1)) {// Nb*(Nr+1)= 4*(10+1)= 44 temp = W[i-1] If (i%Nk == 0) rotate word left 1 byte process each byte through sbox XOR with RCON[i] // just=first of w 4 B temp C 0 element 28 16 w[i] = w[i-4] XOR temp i++}
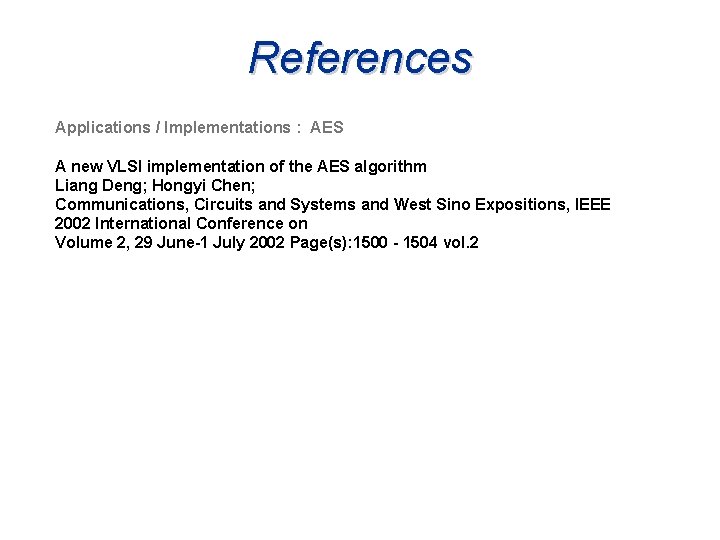
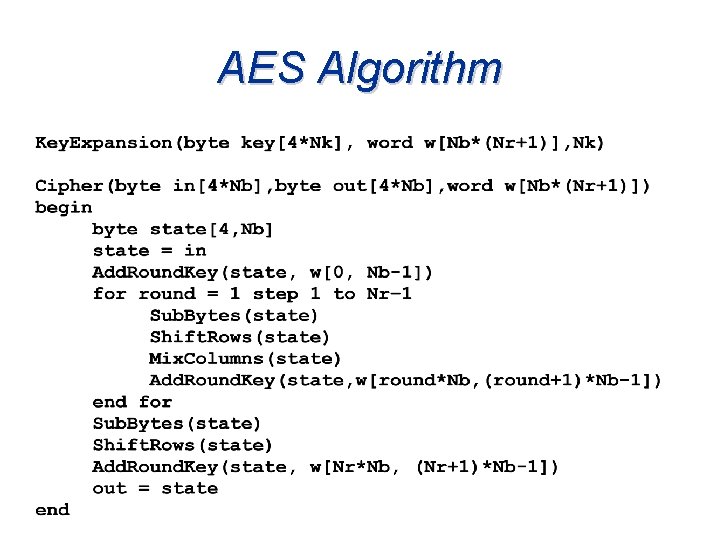
![AES Algorithm Key Expansion w0 w1 w2 w3 w4 11 55 99 CC D AES Algorithm Key Expansion w[0] w[1] w[2] w[3] w[4] 11 55 99 CC D](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-17.jpg)
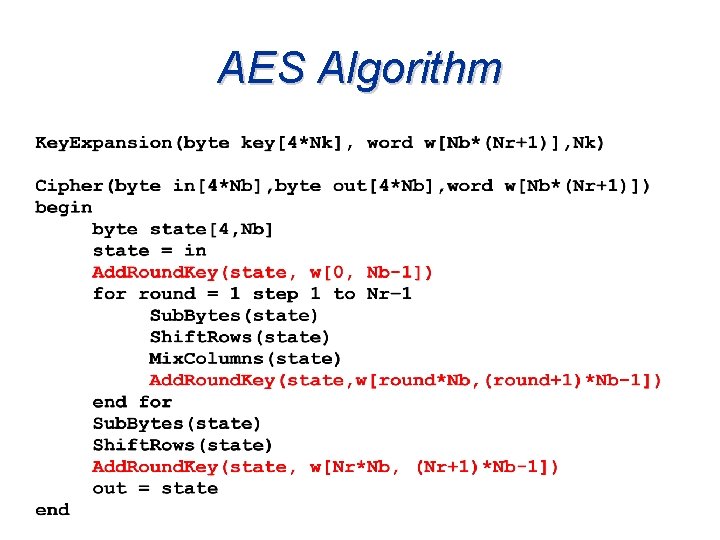
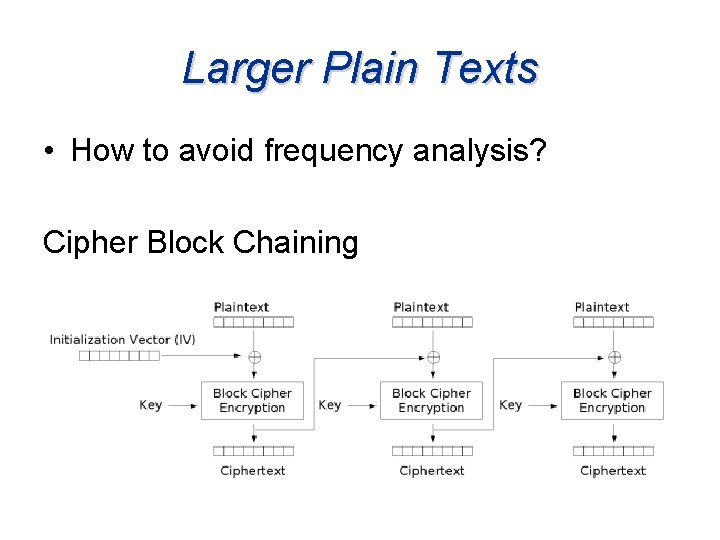
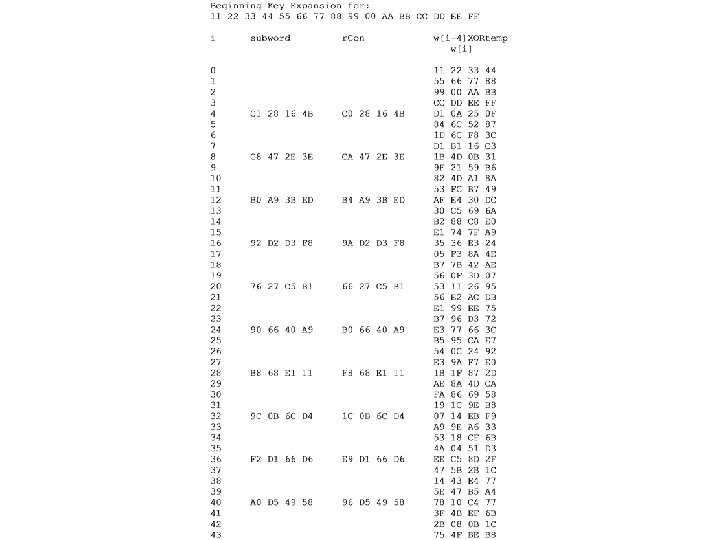
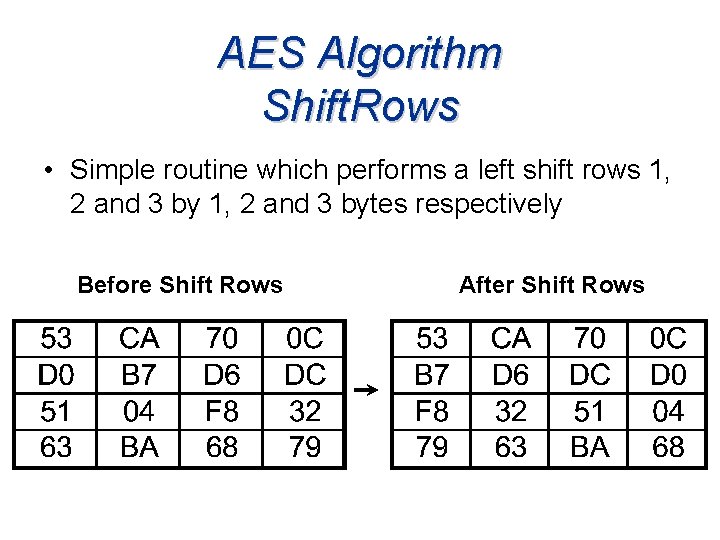
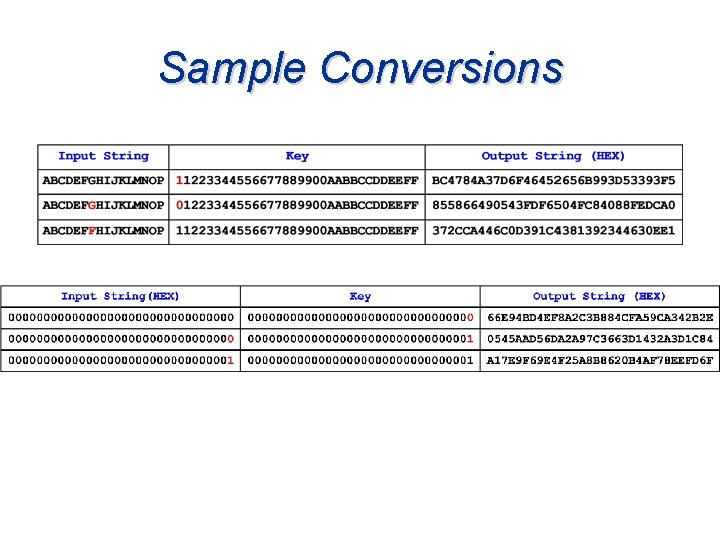
AES Algorithm Key Expansion w[0] w[1] w[2] w[3] w[4] 11 55 99 CC D 1 i=4 temp = C 0 28 16 4 B w[i] = w[i-4] XOR temp 22 66 00 DD 0 A 33 77 AA EE 25 w[4] = (11 C 0) (22 28) (33 16) w[4] = D 1 0 A 25 0 F 44 88 BB FF 0 F (44 4 B)
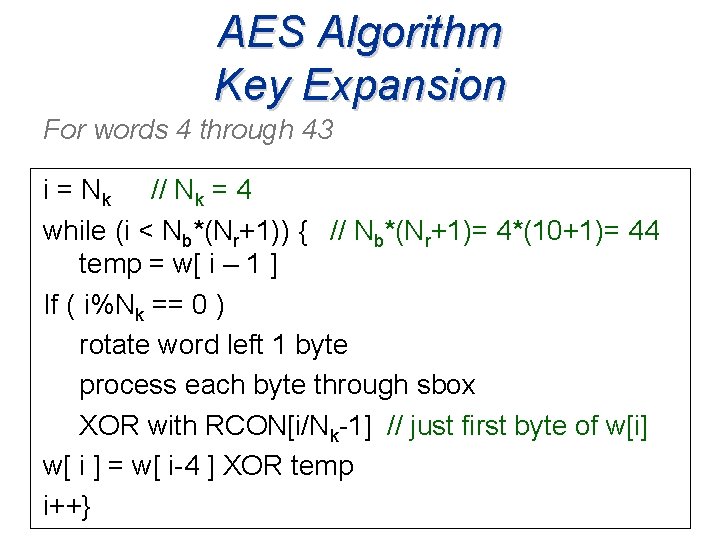
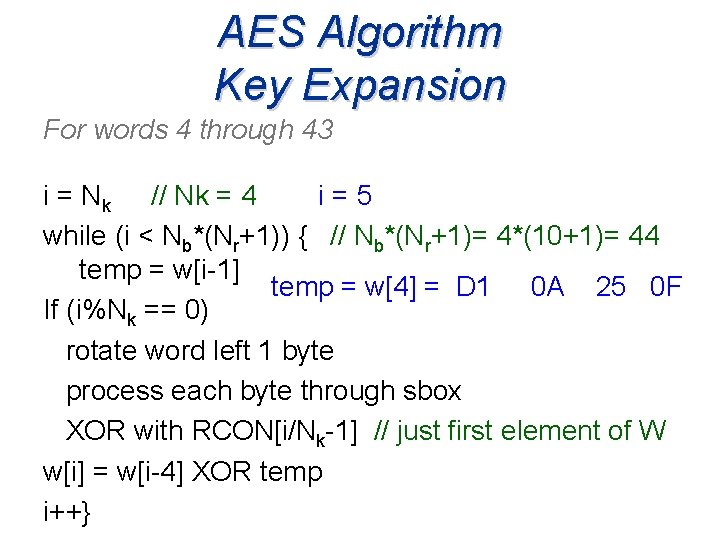
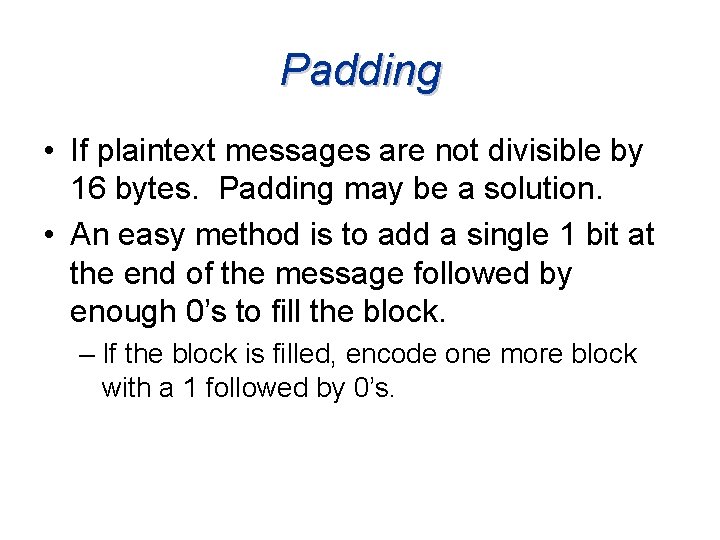
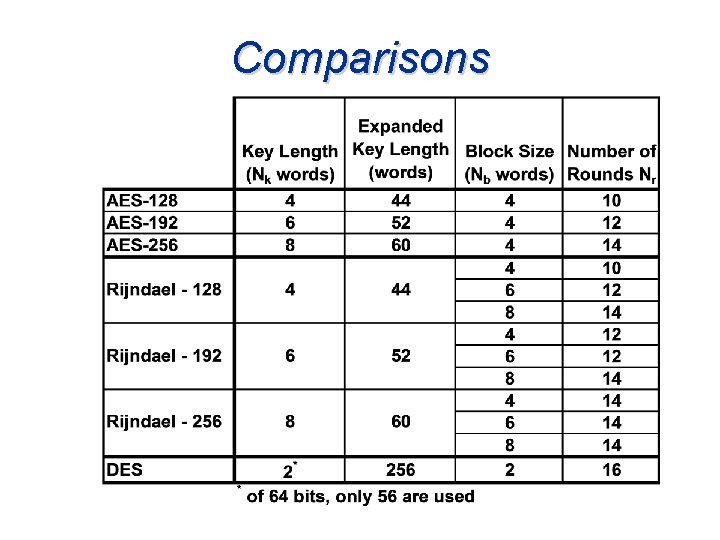
AES Algorithm Key Expansion For words 4 through 43 i = Nk // Nk = 4 i=5 while (i < Nb*(Nr+1)) { // Nb*(Nr+1)= 4*(10+1)= 44 temp = w[i-1] temp = w[4] = D 1 0 A 25 0 F If (i%Nk == 0) rotate word left 1 byte process each byte through sbox XOR with RCON[i/Nk-1] // just first element of W w[i] = w[i-4] XOR temp i++}
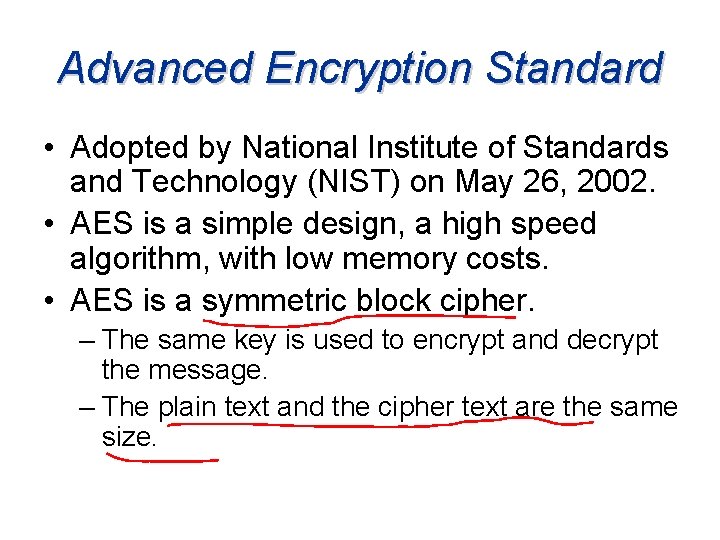
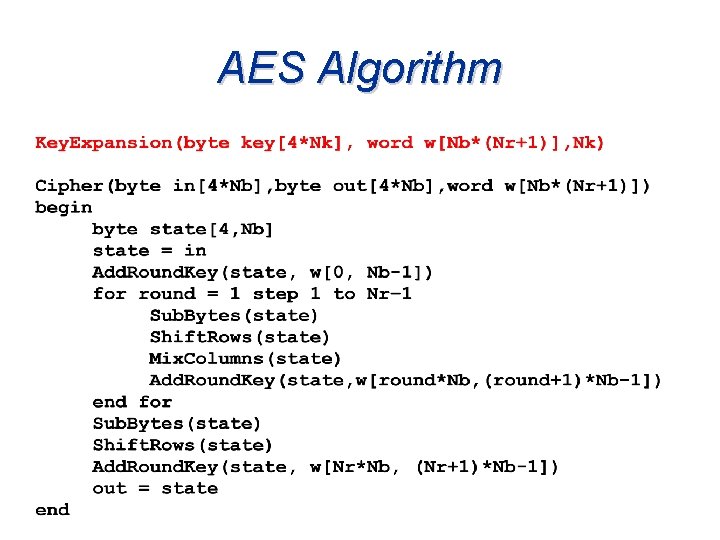
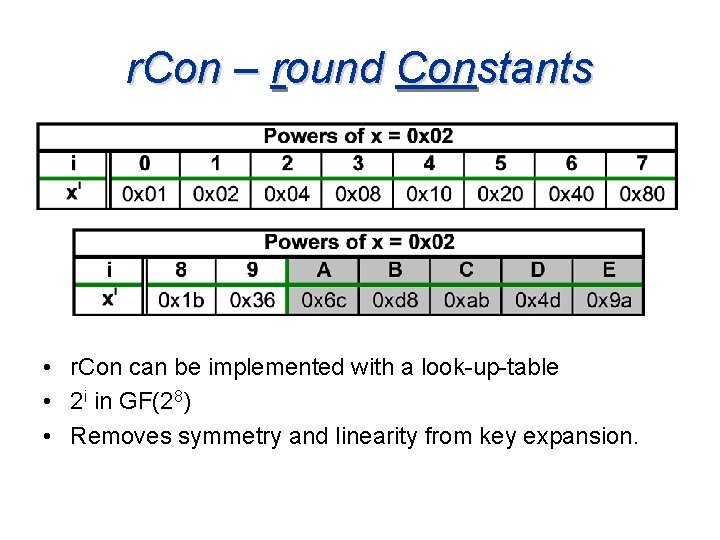
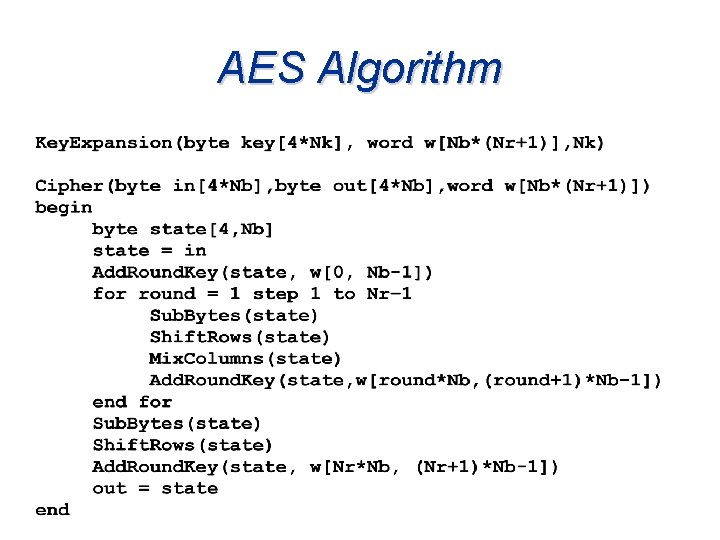
![AES Algorithm Key Expansion w0 w1 w2 w3 w4 11 55 99 CC D AES Algorithm Key Expansion w[0] w[1] w[2] w[3] w[4] 11 55 99 CC D](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-19.jpg)
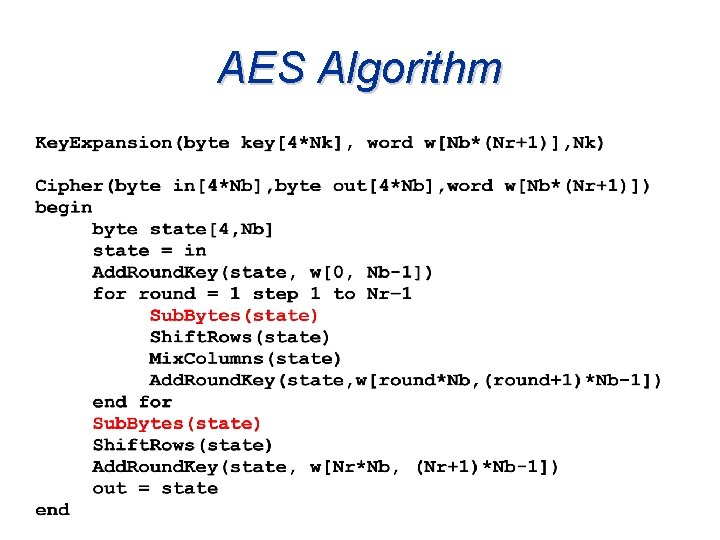
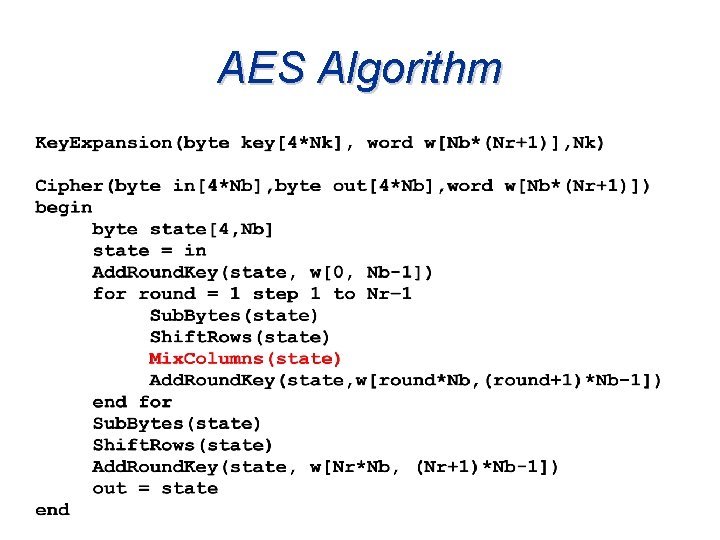
AES Algorithm Key Expansion w[0] w[1] w[2] w[3] w[4] 11 55 99 CC D 1 22 66 00 DD 0 A 33 77 AA EE 25 44 88 BB FF 0 F i=5 temp = D 1 0 A 25 0 F w[i] = w[i-4] XOR temp w[5] = (55 D 1) (66 0 A) (77 25) w[5] = 84 C 6 52 87 (88 0 F)
AES Algorithm
AES Algorithm
![AES Algorithm Add Round Key State Expanded Key w0 w4 After Add Round Key AES Algorithm Add. Round. Key State Expanded Key w[0] w[4] After Add. Round. Key](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-23.jpg)
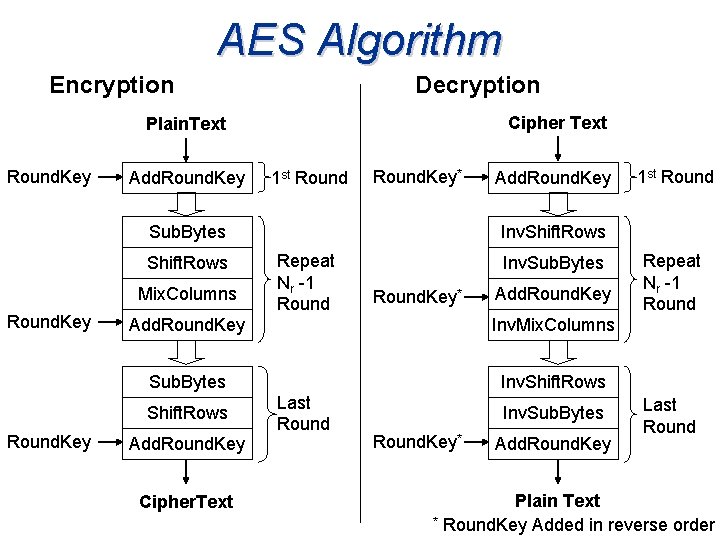
AES Algorithm Add. Round. Key State Expanded Key w[0] w[4] After Add. Round. Key
AES Algorithm
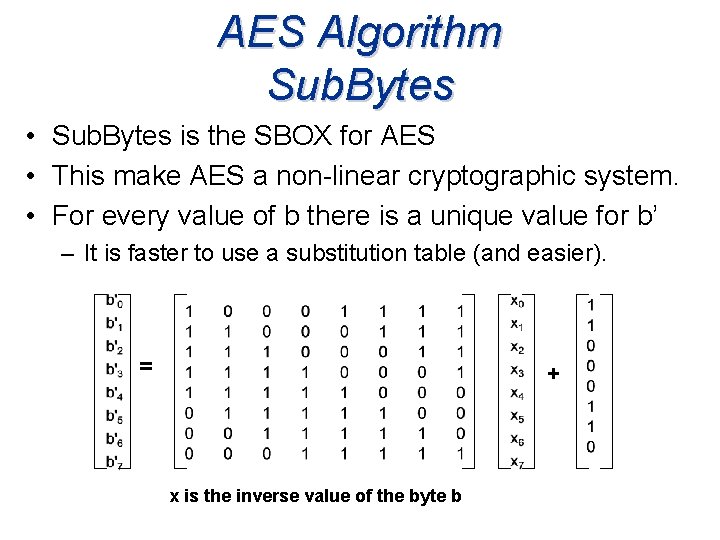
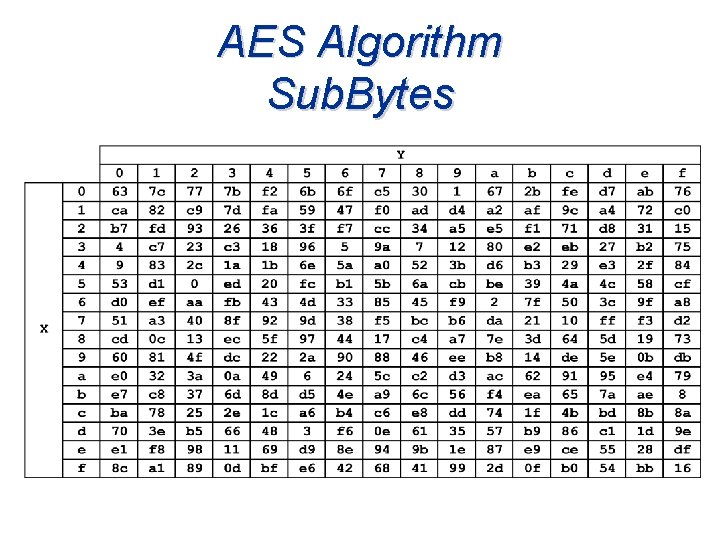
AES Algorithm Sub. Bytes • Sub. Bytes is the SBOX for AES • This make AES a non-linear cryptographic system. • For every value of b there is a unique value for b’ – It is faster to use a substitution table (and easier). = + x is the inverse value of the byte b
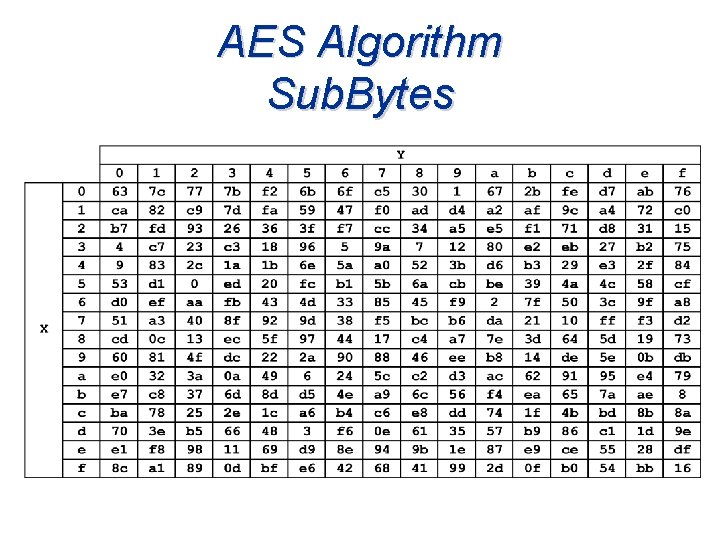
AES Algorithm Sub. Bytes
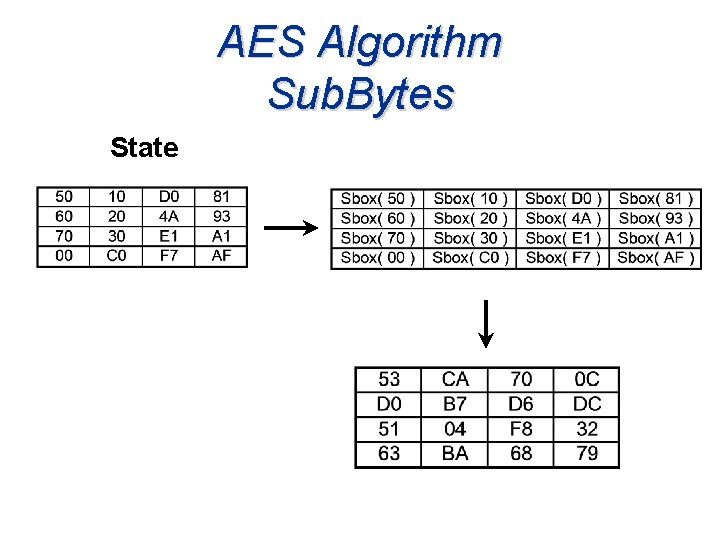
AES Algorithm Sub. Bytes State
AES Algorithm
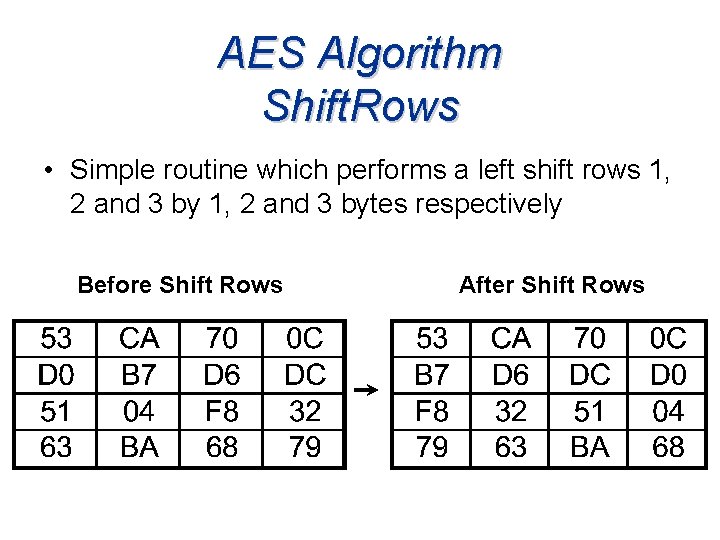
AES Algorithm Shift. Rows • Simple routine which performs a left shift rows 1, 2 and 3 bytes respectively Before Shift Rows After Shift Rows
AES Algorithm
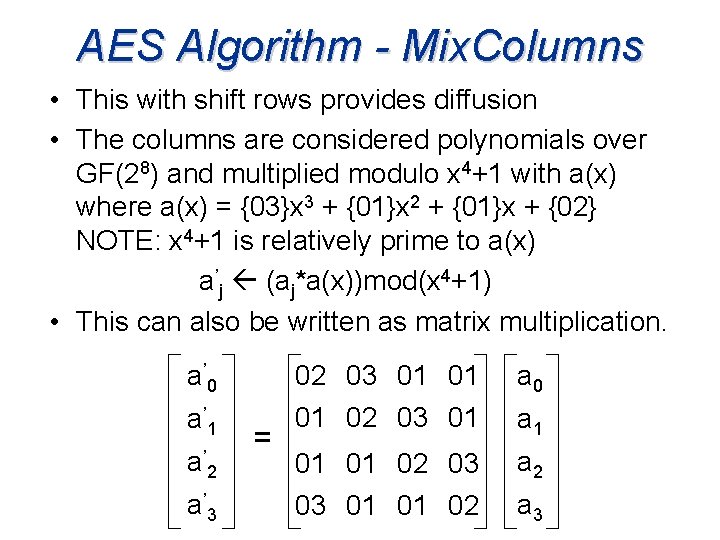
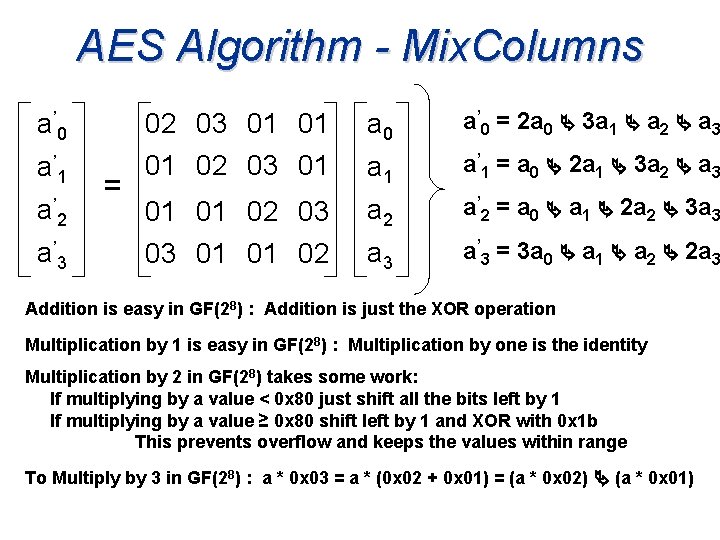
AES Algorithm - Mix. Columns • This with shift rows provides diffusion • The columns are considered polynomials over GF(28) and multiplied modulo x 4+1 with a(x) where a(x) = {03}x 3 + {01}x 2 + {01}x + {02} NOTE: x 4+1 is relatively prime to a(x) a’j (aj*a(x))mod(x 4+1) • This can also be written as matrix multiplication. a ’ 0 02 03 01 01 01 02 03 01 a 0 2 01 01 02 03 a 2 a ’ 3 03 01 01 02 a 3 a ’ 1 a’ = a 1
AES Algorithm - Mix. Columns 02 03 01 01 01 02 03 01 a 0 a’ 0 a’=0 =2 a 2 a 3 a 3 a a 2 +aa 3 0 0 + 1 1 +a 2 a 1 a’ 1 a’=1 =a 0 a 2 a 2 a 3 a 0 + 1 1 +3 a 2 2 +aa 3 2 01 01 02 03 a 2 a’ 2 a’=2 =a 0 a a 1 a 2 a 3 a 3 0 + 1 +2 a 2 2 +3 a a ’ 3 03 01 01 02 a 3 a’ 3 a’=3 =3 a 3 a a 1 a a 2 +2 a 2 a 3 0 0 + 1 +a 2 a ’ 0 a ’ 1 a’ = Addition is easy in GF(28) : Addition is just the XOR operation Multiplication by 1 is easy in GF(28) : Multiplication by one is the identity Multiplication by 2 in GF(28) takes some work: . If multiplying by a value < 0 x 80 just shift all the bits left by 1. If multiplying by a value ≥ 0 x 80 shift left by 1 and XOR with 0 x 1 b. This prevents overflow and keeps the values within range To Multiply by 3 in GF(28) : a * 0 x 03 = a * (0 x 02 + 0 x 01) = (a * 0 x 02) (a * 0 x 01)
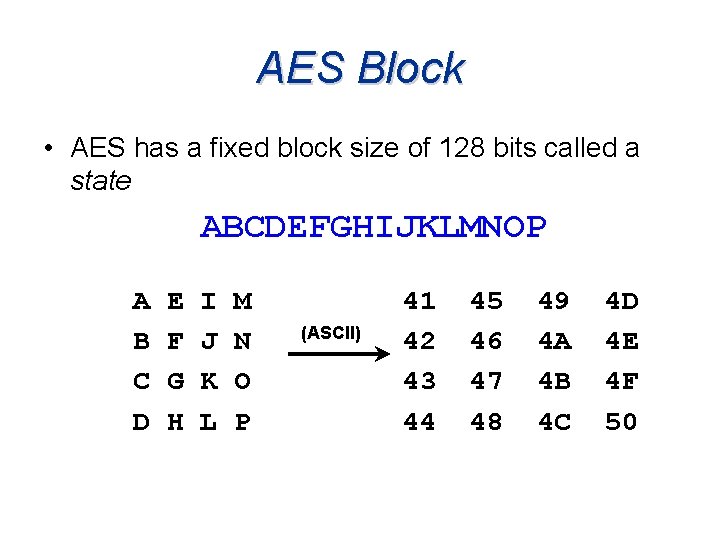
![AES Algorithm Key Expansionbyte key4Nk word wNbNr1 Nk Cipherbyte in4Nb byte out4Nb word wNbNr1 AES Algorithm Key. Expansion(byte key[4*Nk], word w[Nb*(Nr+1)], Nk) Cipher(byte in[4*Nb], byte out[4*Nb], word w[Nb*(Nr+1)])](https://slidetodoc.com/presentation_image_h2/a23528f4735c22d9151e696bcfd21dae/image-33.jpg)
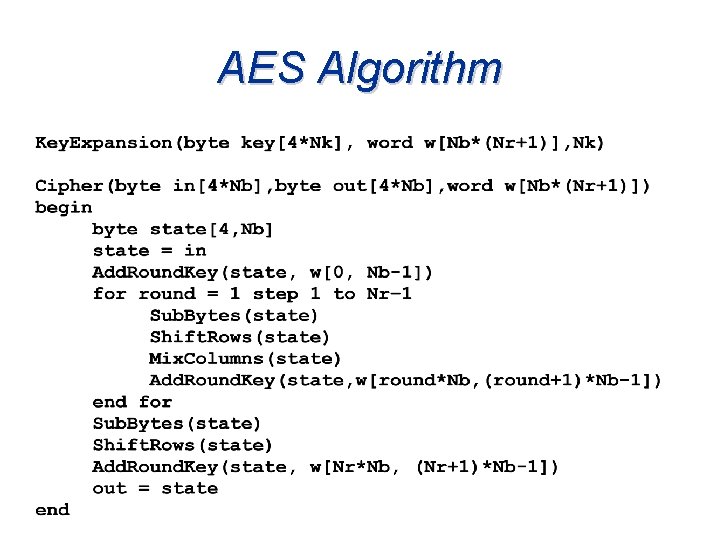
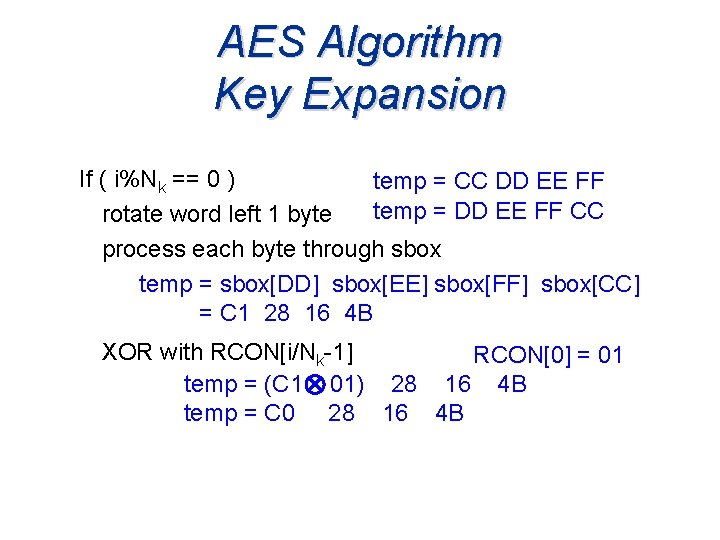
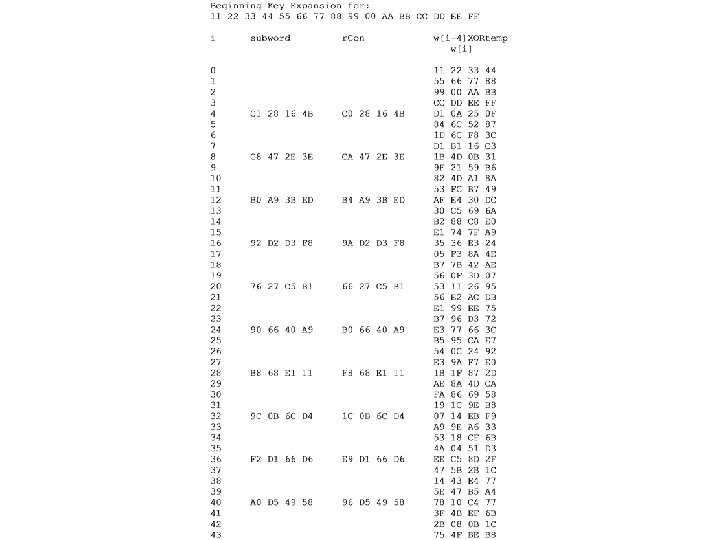
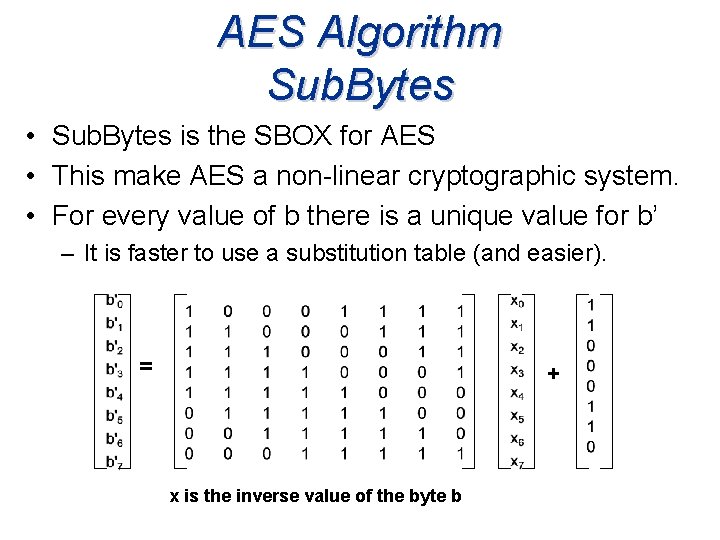
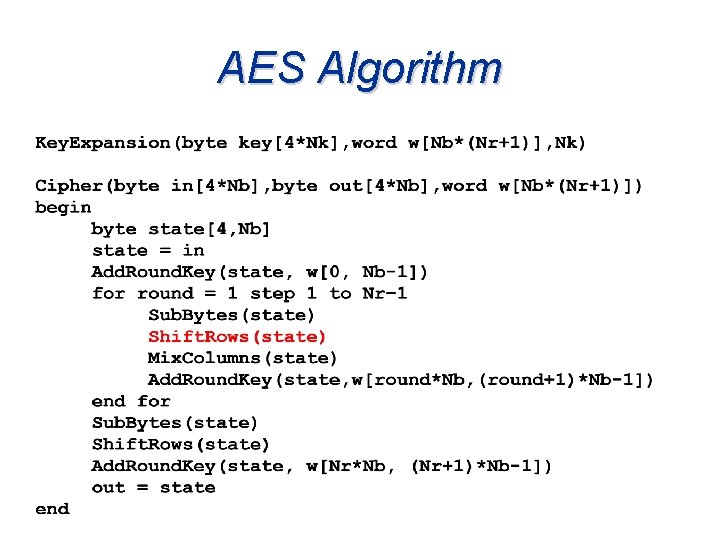
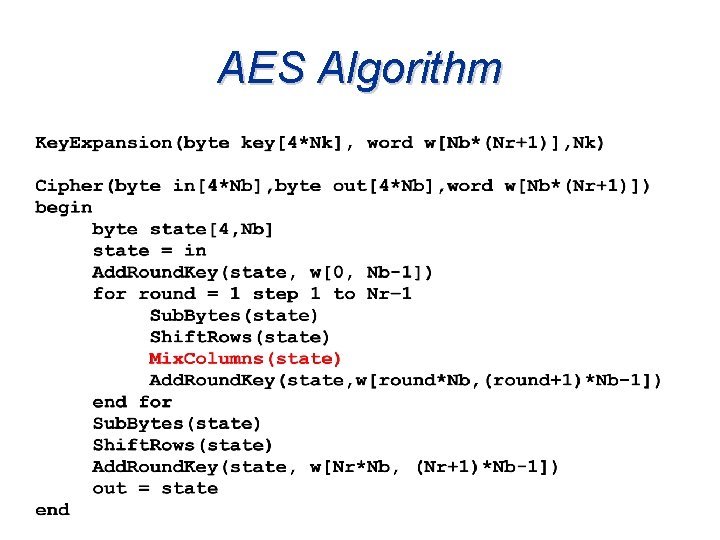
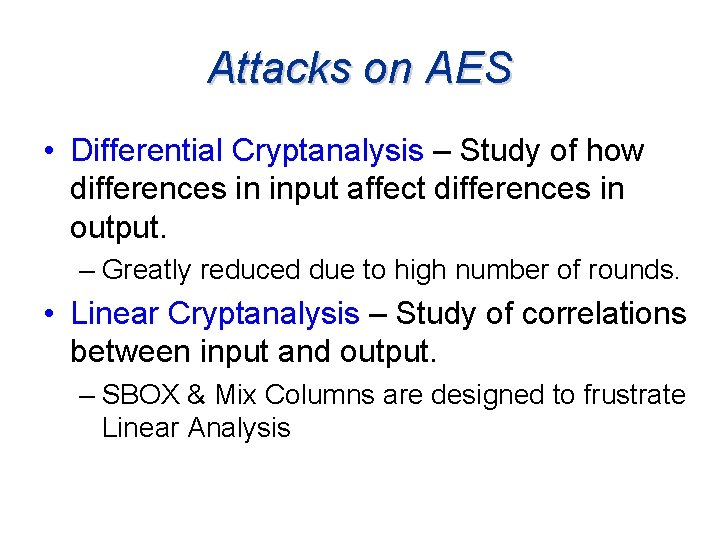
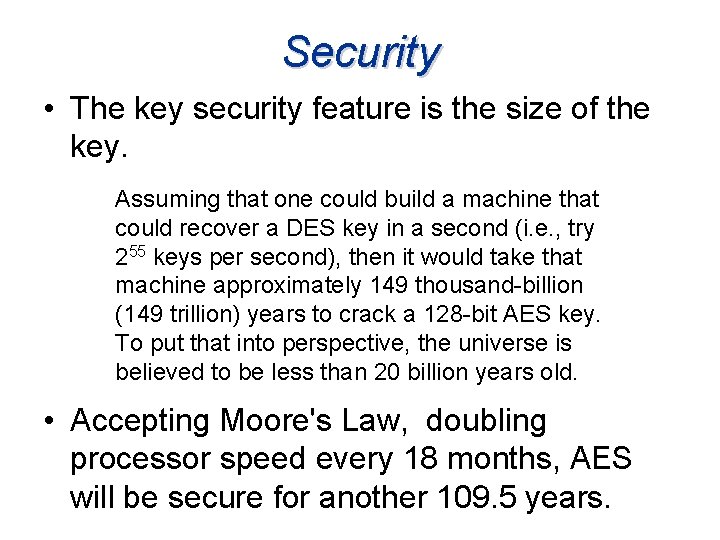
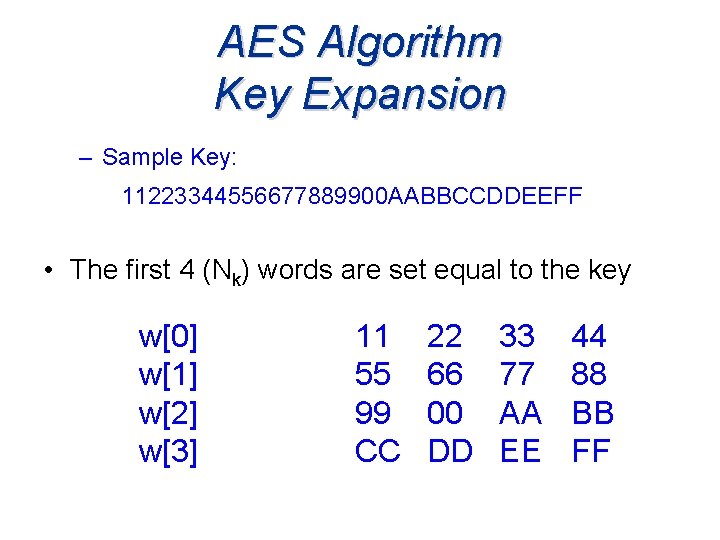
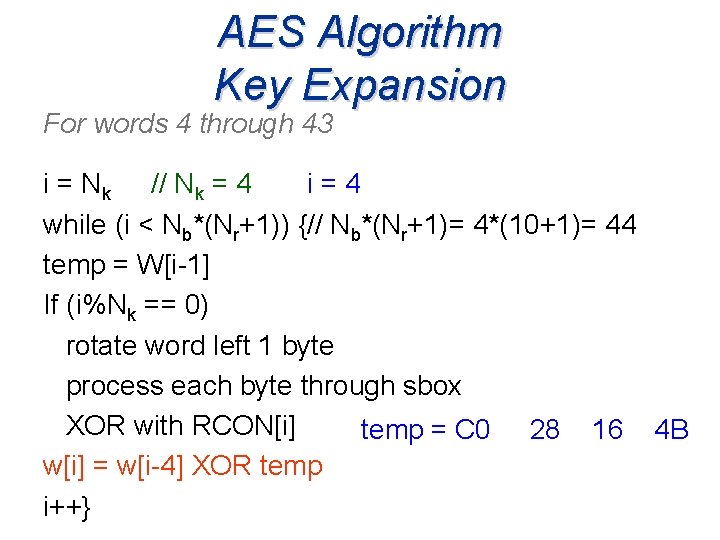
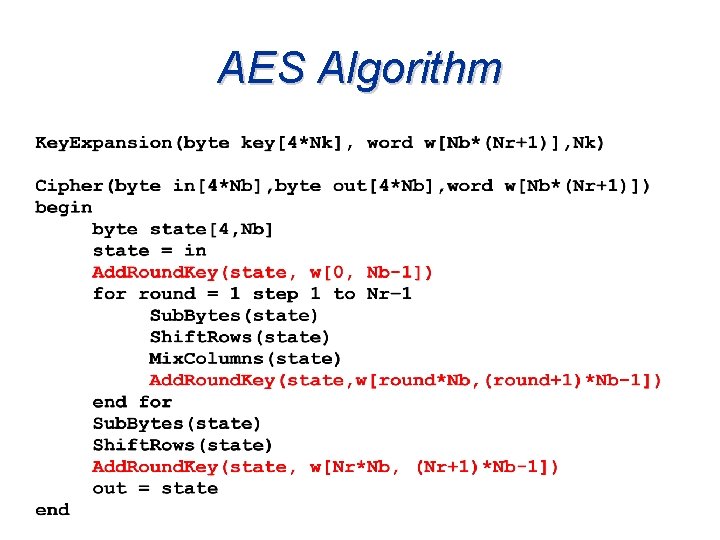
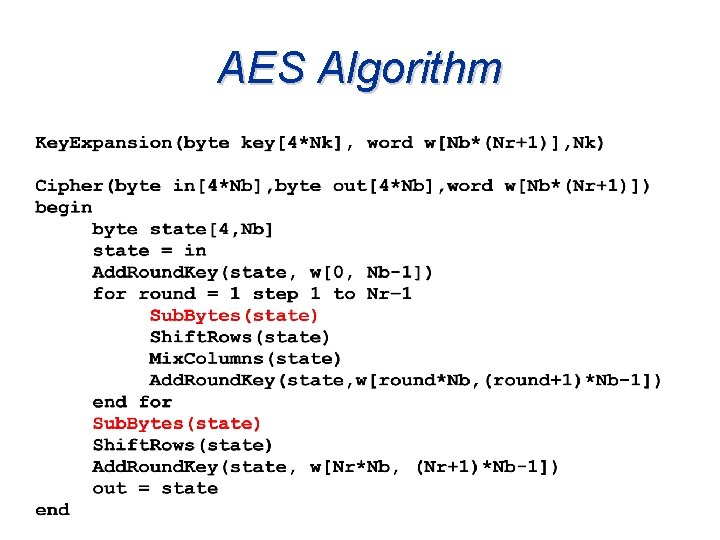
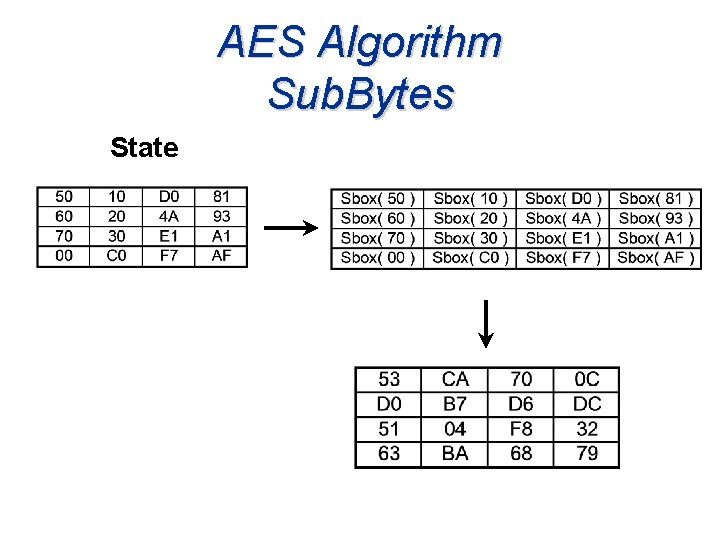
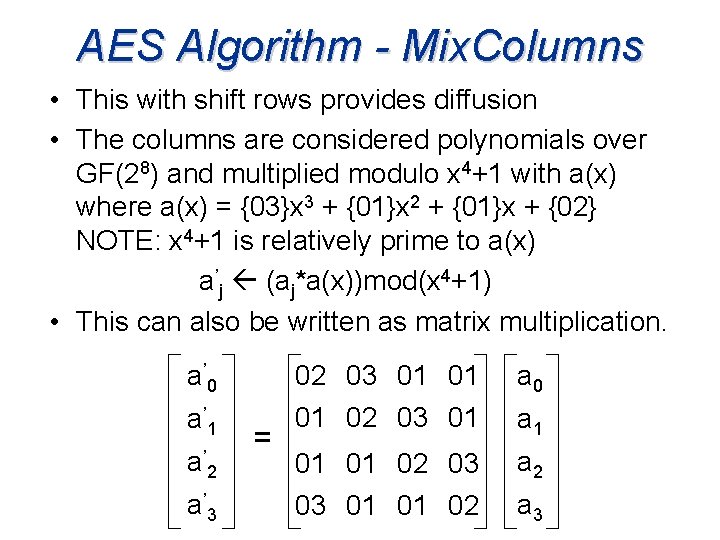
AES Algorithm Key. Expansion(byte key[4*Nk], word w[Nb*(Nr+1)], Nk) Cipher(byte in[4*Nb], byte out[4*Nb], word w[Nb*(Nr+1)]) begin byte state[4, Nb] state = in Add. Round. Key(state, w[0, Nb-1]) for round = 1 step 1 to Nr– 1 Sub. Bytes(state) Shift. Rows(state) Mix. Columns(state) Add. Round. Key(state, w[round*Nb, (round+1)*Nb-1]) end for Sub. Bytes(state) Shift. Rows(state) Add. Round. Key(state, w[Nr*Nb, (Nr+1)*Nb-1]) out = state end
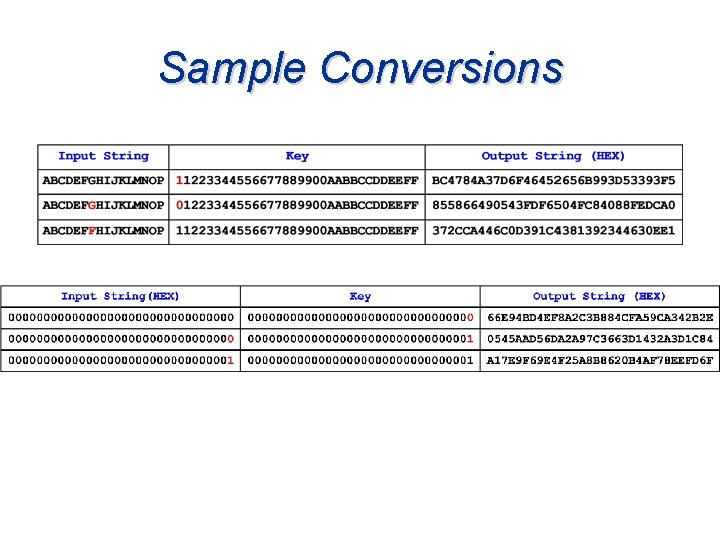
Sample Conversions
AES Algorithm Encryption Decryption Cipher Text Plain. Text Round. Key Add. Round. Key 1 st Round. Key* Sub. Bytes Shift. Rows Mix. Columns Round. Key Repeat Nr -1 Round Inv. Sub. Bytes Round. Key* Add. Round. Key Inv. Mix. Columns Sub. Bytes Inv. Shift. Rows Add. Round. Key Cipher. Text 1 st Round Inv. Shift. Rows Add. Round. Key Shift. Rows Round. Key Add. Round. Key Last Round Inv. Sub. Bytes Round. Key* Add. Round. Key Repeat Nr -1 Round Last Round Plain Text * Round. Key Added in reverse order
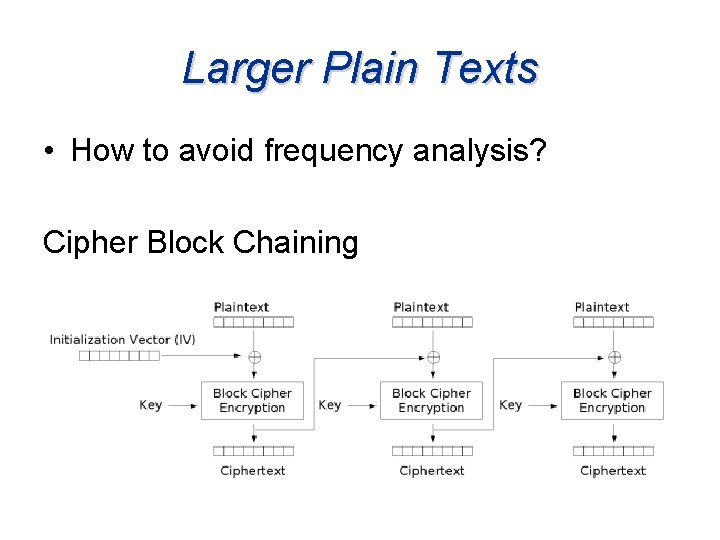
Larger Plain Texts • How to avoid frequency analysis? Cipher Block Chaining
Padding • If plaintext messages are not divisible by 16 bytes. Padding may be a solution. • An easy method is to add a single 1 bit at the end of the message followed by enough 0’s to fill the block. – If the block is filled, encode one more block with a 1 followed by 0’s.
Attacks on AES • Differential Cryptanalysis – Study of how differences in input affect differences in output. – Greatly reduced due to high number of rounds. • Linear Cryptanalysis – Study of correlations between input and output. – SBOX & Mix Columns are designed to frustrate Linear Analysis
Attacks on AES • Side Channel Attacks – Attacks based on studying and measuring the actual implementation of the code. – For some implementations of AES the key has been obtained in under 100 minutes. • Computer running AES was 850 MHz, Pentium III running Free. BSD 4. 8
Types of Side Channel Attacks • Timing Attacks – Watches movement of data in and out of the CPU or memory. – It is difficult to retrieve an array element in a time that is not dependent on the index value. • Power Attacks – Watches power consumption by CPU or memory. – Changing one bit requires considerably less power than changing all bits in a byte.
Attack Precautions • Avoid use of arrays. Compute values in SBOX and r. Con. • Design algorithms and devices to work with constant time intervals. (independent of key and plaintext. ) – Hidden CPU timing data is a threat. • Use same memory throughout, Cache is faster than DRAM • Compute Key Expansion on the fly. • Utilize pipelining to stabilize CPU power consumption.
Joan Daemen & Vincent Rijmen’s AES Selling Points • Extremely fast compared to other block ciphers. (tradeoff between size and speed) • The round transformation is parallel by design. Important in dedicated hardware. • Amenable to pipelining • The cipher does not use arithmetic operations so has no bias towards big or little endian architectures.
Joan Daemen & Vincent Rijmen’s AES Selling Points • Fully Self-supporting. Does not use Sboxes of other ciphers, bits from Rand tables, digits of or any other such jokes. • Is not based on obscure or not well understood processes • The tight cipher design does not leave enough room to hide a trap door.
Joan Daemen & Vincent Rijmen’s AES Limitations • The inverse cipher is less suited to smart cards, as it takes more codes and cycles. • The cipher and inverse cipher make use of different codes and/or tables. • In hardware, The inverse cipher can only partially re-use circuitry which implements the cipher.
References About AES Proposal : Rijndael Joan Daemen, Vincent Rijmen, 2 nd version of document to NIST Polynomials in the Nations Service: Using Algebra to Design the Advanced Encryption Standard Susan Landau The Mathmatical Association of America, Monthly 111 Feb 2004 Page(s): 89 -117 Selecting the Advanced Encryption Standard Security & Privacy Magazine, IEEE Volume 1, Issue 2, Mar-Apr 2003 Page(s): 43 - 52 Title: Introduction to Cryptography Author: Johannes A Buchman Publisher: Springer; 2 edition (July 13, 2004) Burr, W. E. ;
References Security and Attacking AES Power-analysis attack on an ASIC AES implementation Ors, S. B. ; Gurkaynak, F. ; Oswald, E. ; Preneel, B. ; Information Technology: Coding and Computing, 2004. Proceedings. ITCC 2004. International Conference on. Volume 2, 2004 Page(s): 546 - 552 Vol. 2 Algebraic attacks on cipher systems Penzhorn, W. T. ; AFRICON, 2004. 7 th AFRICON Conference in Africa Volume 2, 2004 Page(s): 969 - 974 Vol. 2 Cache-Timing attacks on AES Daniel J Bernstein Preliminary version of report to National Science Foundation, grant CCR 9983950
References Applications / Implementations: AES A high throughput low cost AES processor Chih-Pin Su; Tsung-Fu Lin; Chih-Tsiun Huang; Cheng-Wen Wu; Communications Magazine, IEEE Volume 41, Issue 12, Dec. 2003 Page(s): 86 - 91 An efficient FPGA implementation of advanced encryption standard algorithm Shuenn-Shyang Wang; Wan-Sheng Ni; Circuits and Systems, 2004. ISCAS '04. Volume 2, 23 -26 May 2004 Page(s): II - 597 -600 Vol. 2 High-speed VLSI architectures for the AES algorithm Xinmiao Zhang; Parhi, K. K. ; Very Large Scale Integration (VLSI) Systems Volume 12, Issue 9, Sept. 2004 Page(s): 957 – 967 Fast implementation of AES cryptographic algorithms in smart cards Chi-Feng Lu; Yan-Shun Kao; Hsia-Ling Chiang; Chung-Huang Yang; Security Technology, 2003. 14 -16 Oct. 2003 Page(s): 573 - 579
References Applications / Implementations : AES A new VLSI implementation of the AES algorithm Liang Deng; Hongyi Chen; Communications, Circuits and Systems and West Sino Expositions, IEEE 2002 International Conference on Volume 2, 29 June-1 July 2002 Page(s): 1500 - 1504 vol. 2