Applied Cryptography Example AES Advanced Encryption Standard It
- Slides: 43
Applied Cryptography Example: AES
Advanced Encryption Standard "It seems very simple. " "It is very simple. But if you don't know what the key is it's virtually indecipherable. " —Talking to Strange Men, Ruth Rendell
Origins Ø clear a replacement for DES was needed l l have theoretical attacks that can break it have demonstrated exhaustive key search attacks can use Triple-DES – but slow, has small blocks Ø US NIST issued call for ciphers in 1997 Ø 15 candidates accepted in Jun 98 Ø 5 were shortlisted in Aug-99 Ø Rijndael was selected as the AES in Oct-2000 Ø issued as FIPS PUB 197 standard in Nov-2001 Ø
AES Requirements Ø private key symmetric block cipher Ø 128 -bit data, 128/192/256 -bit keys Ø stronger & faster than Triple-DES Ø active life of 20 -30 years (+ archival use) Ø provide full specification & design details Ø both C & Java implementations Ø NIST have released all submissions & unclassified analyses
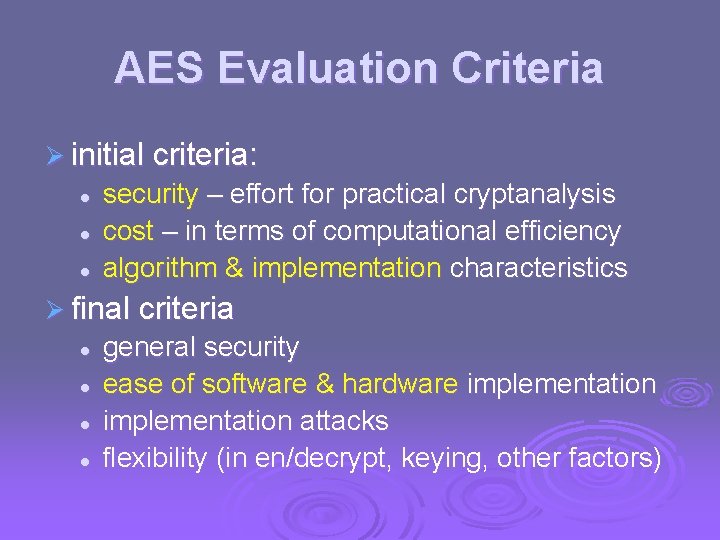
AES Evaluation Criteria Ø initial criteria: l l l security – effort for practical cryptanalysis cost – in terms of computational efficiency algorithm & implementation characteristics Ø final criteria l l general security ease of software & hardware implementation attacks flexibility (in en/decrypt, keying, other factors)
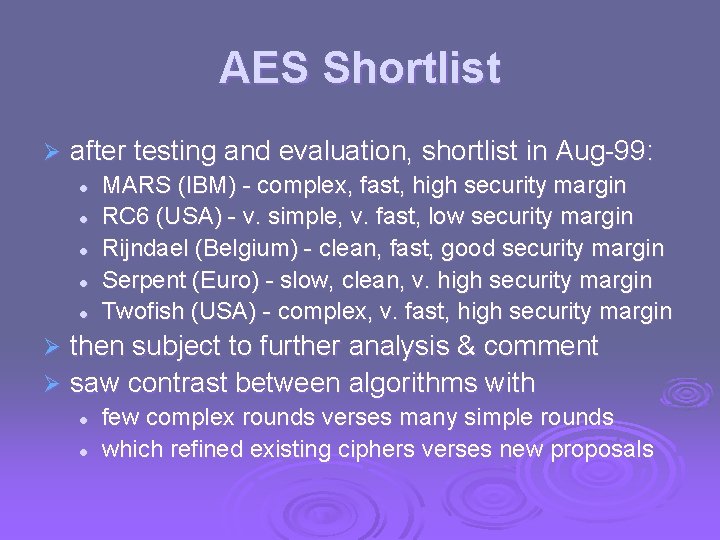
AES Shortlist Ø after testing and evaluation, shortlist in Aug-99: l l l MARS (IBM) - complex, fast, high security margin RC 6 (USA) - v. simple, v. fast, low security margin Rijndael (Belgium) - clean, fast, good security margin Serpent (Euro) - slow, clean, v. high security margin Twofish (USA) - complex, v. fast, high security margin then subject to further analysis & comment Ø saw contrast between algorithms with Ø l l few complex rounds verses many simple rounds which refined existing ciphers verses new proposals
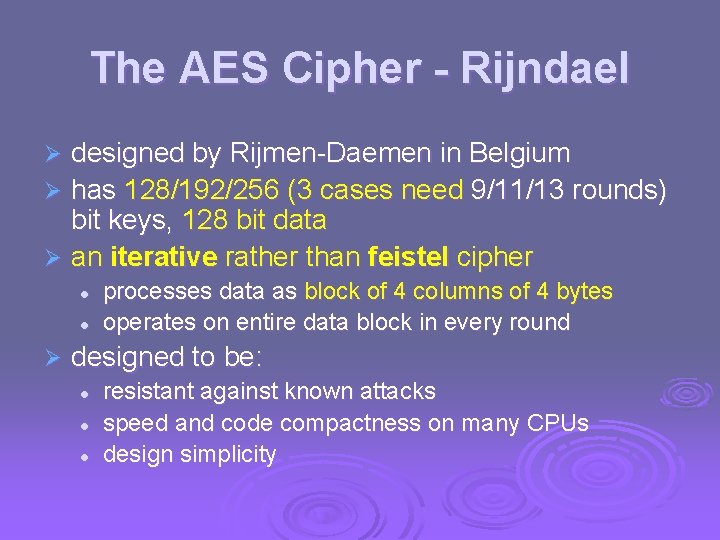
The AES Cipher - Rijndael designed by Rijmen-Daemen in Belgium Ø has 128/192/256 (3 cases need 9/11/13 rounds) bit keys, 128 bit data Ø an iterative rather than feistel cipher Ø l l Ø processes data as block of 4 columns of 4 bytes operates on entire data block in every round designed to be: l l l resistant against known attacks speed and code compactness on many CPUs design simplicity
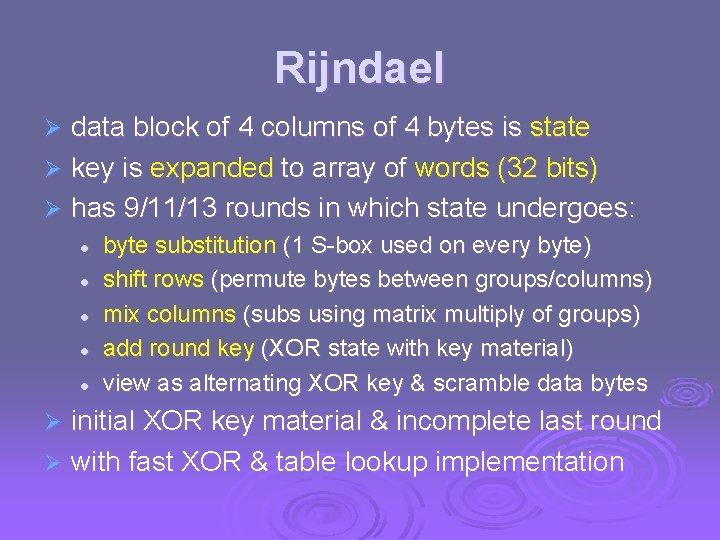
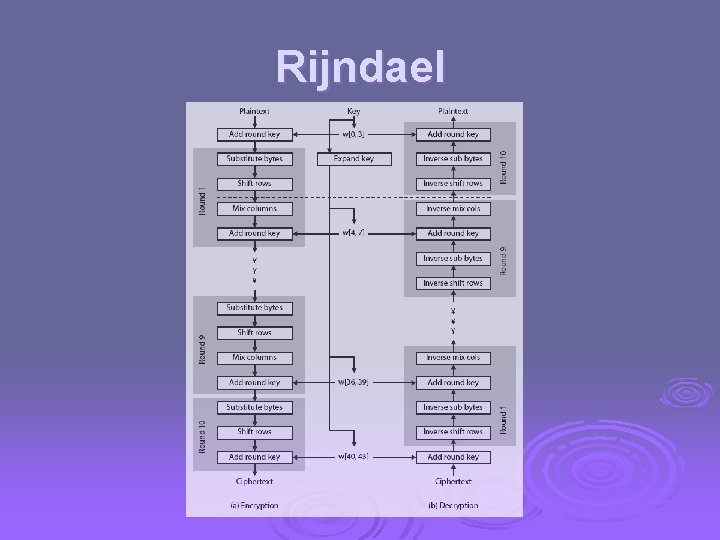
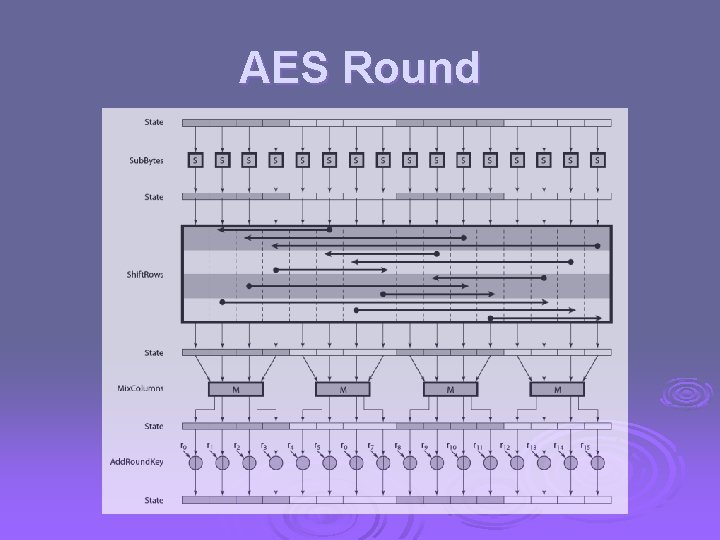
Rijndael data block of 4 columns of 4 bytes is state Ø key is expanded to array of words (32 bits) Ø has 9/11/13 rounds in which state undergoes: Ø l l l byte substitution (1 S-box used on every byte) shift rows (permute bytes between groups/columns) mix columns (subs using matrix multiply of groups) add round key (XOR state with key material) view as alternating XOR key & scramble data bytes initial XOR key material & incomplete last round Ø with fast XOR & table lookup implementation Ø
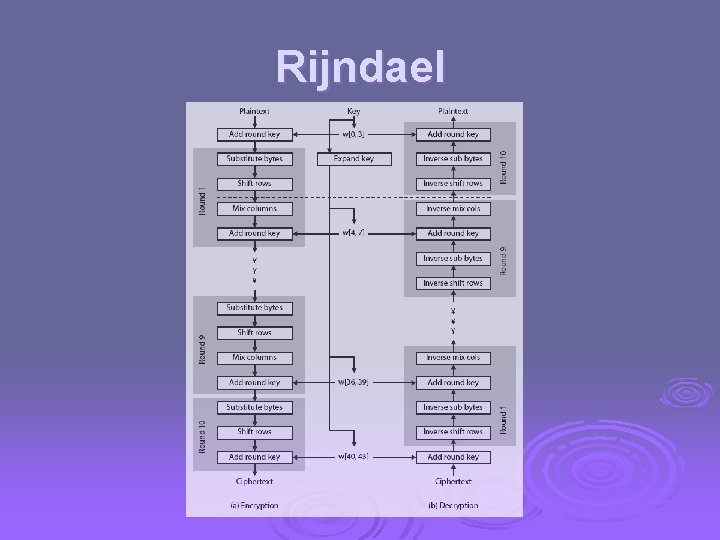
Rijndael
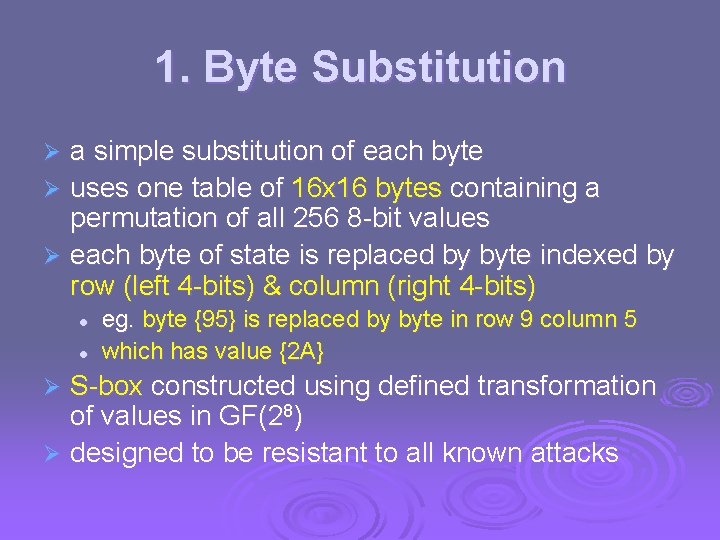
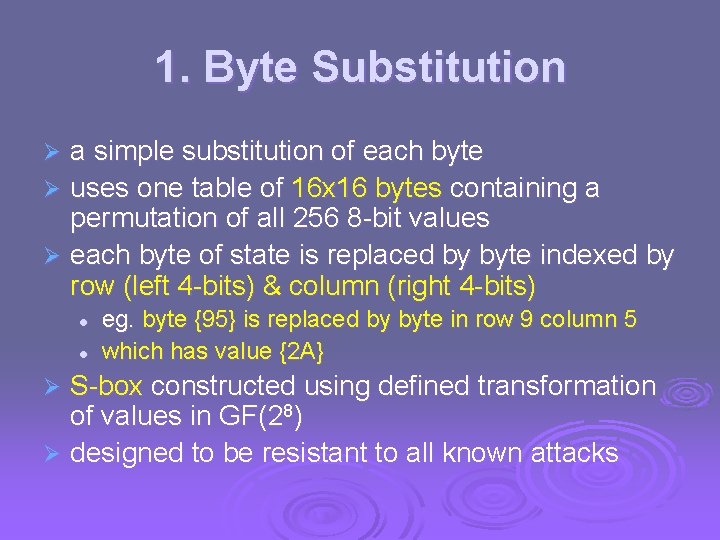
1. Byte Substitution a simple substitution of each byte Ø uses one table of 16 x 16 bytes containing a permutation of all 256 8 -bit values Ø each byte of state is replaced by byte indexed by row (left 4 -bits) & column (right 4 -bits) Ø l l eg. byte {95} is replaced by byte in row 9 column 5 which has value {2 A} S-box constructed using defined transformation of values in GF(28) Ø designed to be resistant to all known attacks Ø
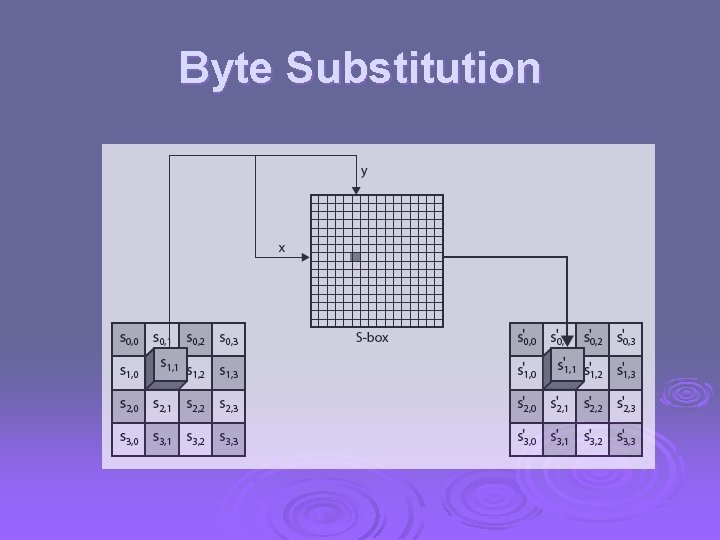
Byte Substitution
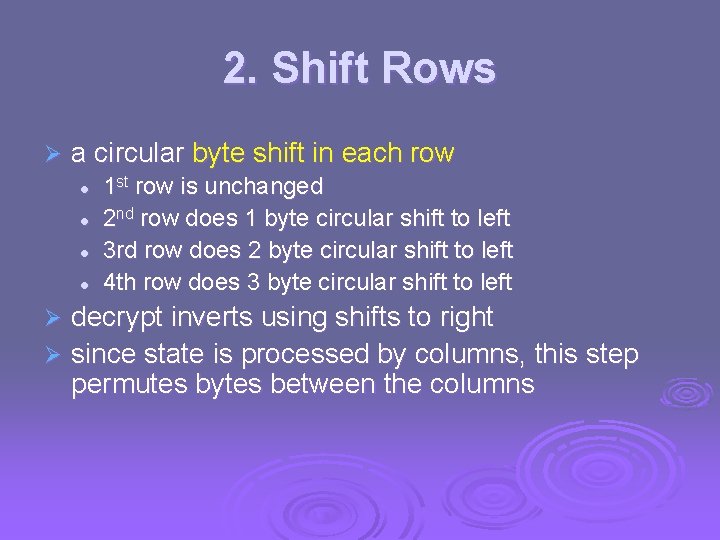
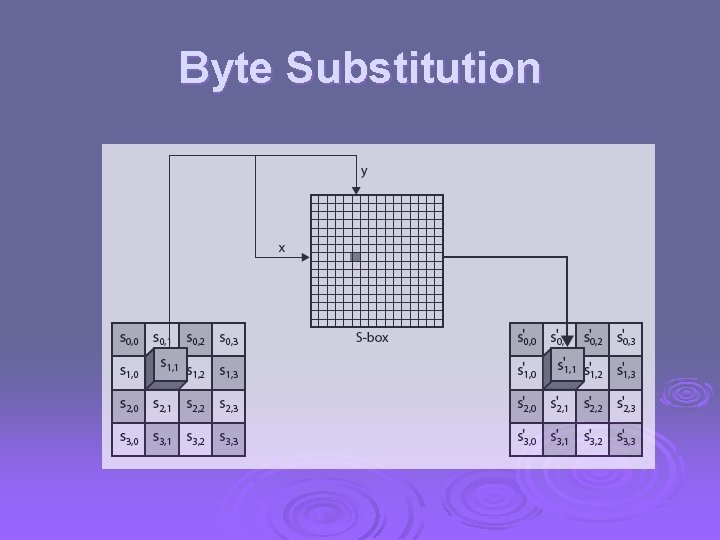
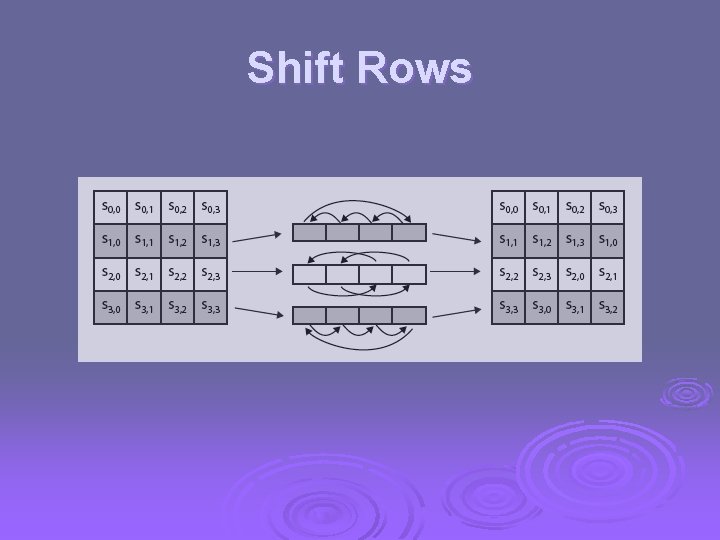
2. Shift Rows Ø a circular byte shift in each row l l 1 st row is unchanged 2 nd row does 1 byte circular shift to left 3 rd row does 2 byte circular shift to left 4 th row does 3 byte circular shift to left decrypt inverts using shifts to right Ø since state is processed by columns, this step permutes bytes between the columns Ø
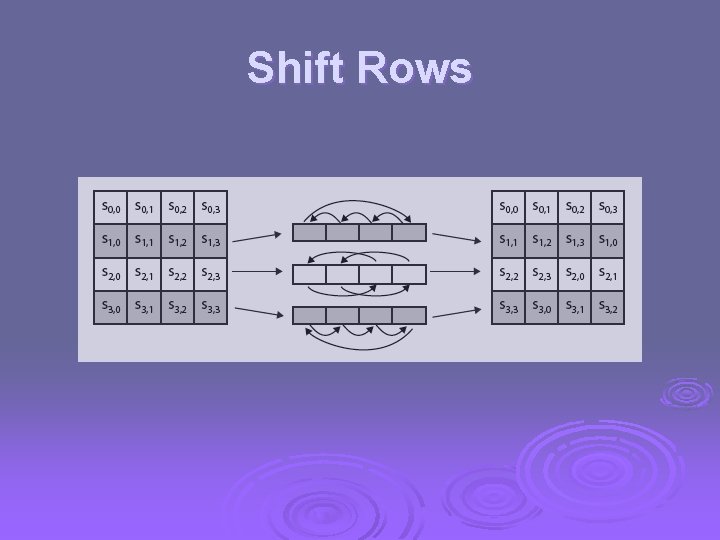
Shift Rows
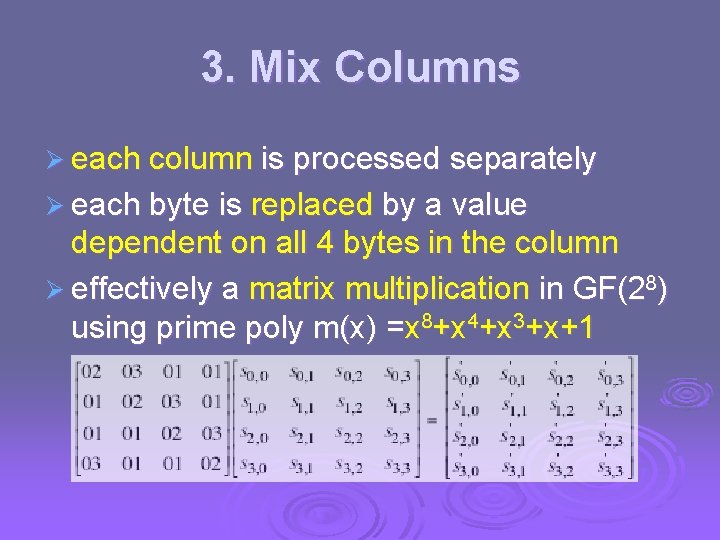
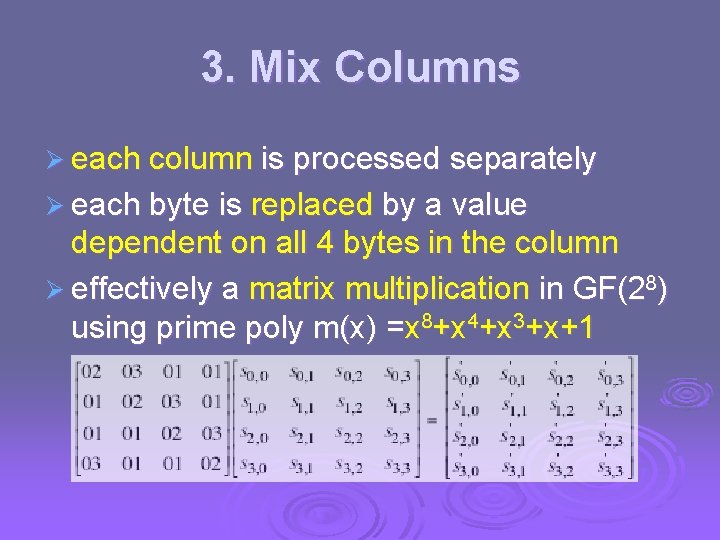
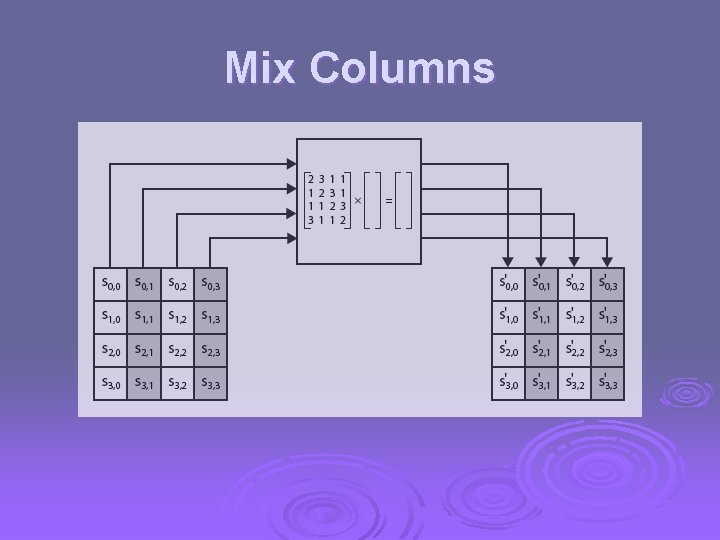
3. Mix Columns Ø each column is processed separately Ø each byte is replaced by a value dependent on all 4 bytes in the column Ø effectively a matrix multiplication in GF(28) using prime poly m(x) =x 8+x 4+x 3+x+1
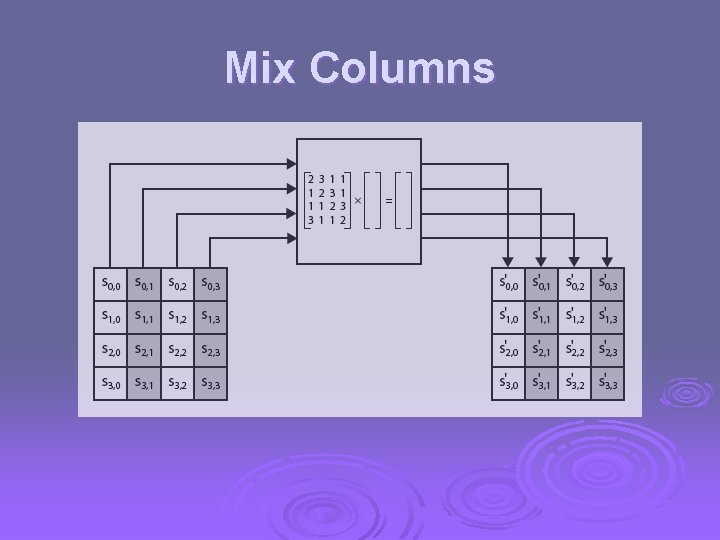
Mix Columns
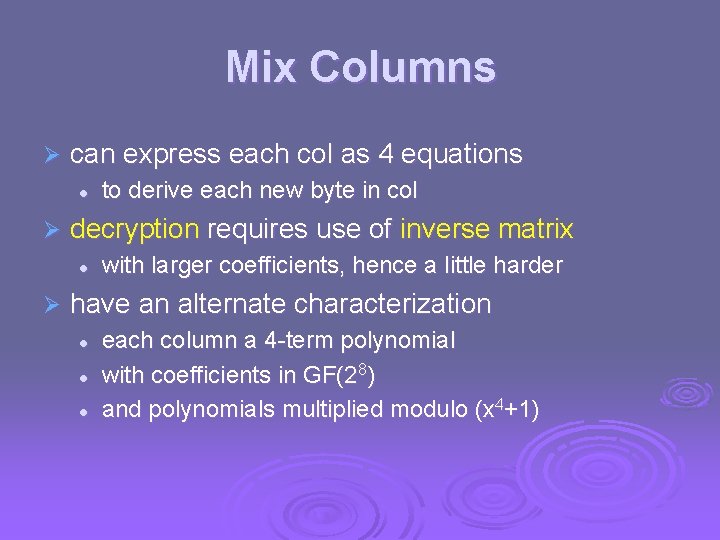
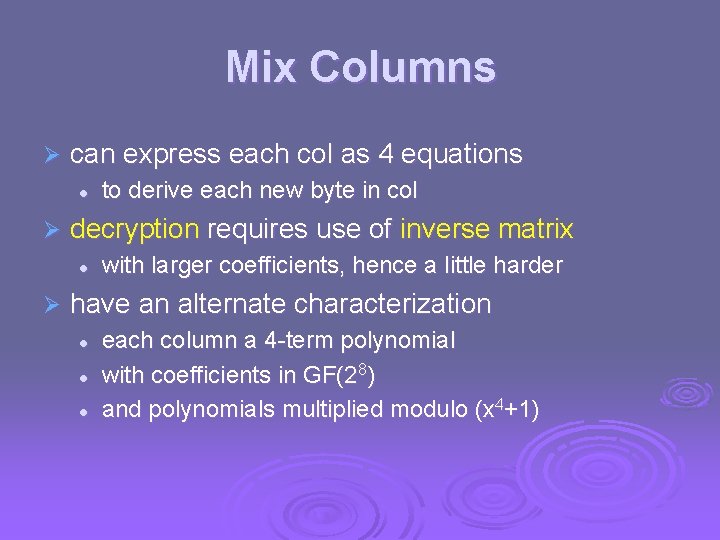
Mix Columns Ø can express each col as 4 equations l Ø decryption requires use of inverse matrix l Ø to derive each new byte in col with larger coefficients, hence a little harder have an alternate characterization l l l each column a 4 -term polynomial with coefficients in GF(28) and polynomials multiplied modulo (x 4+1)
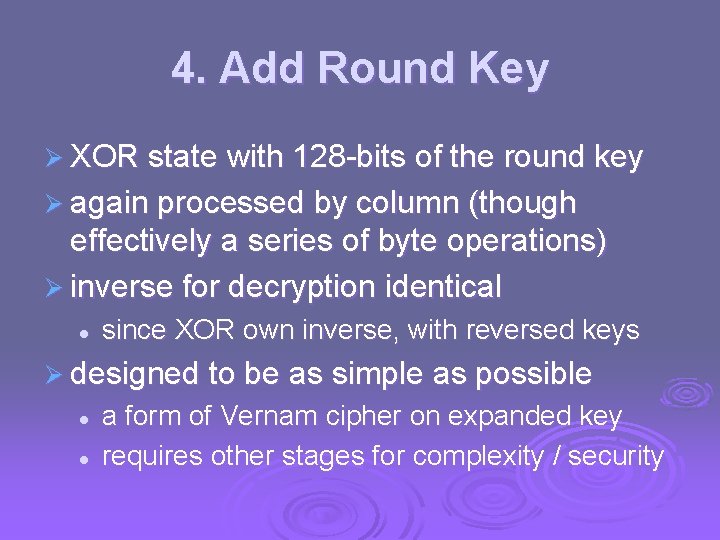
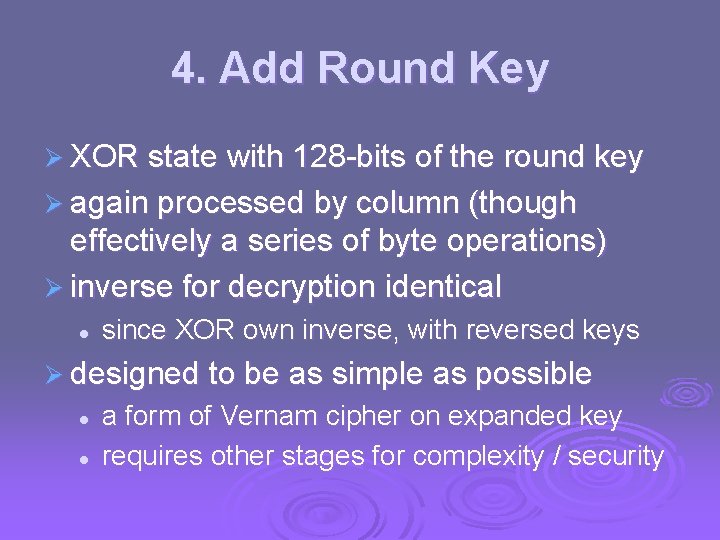
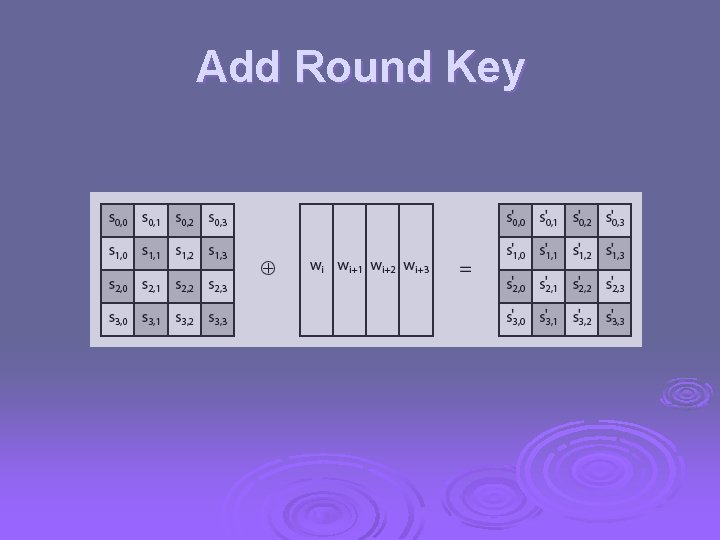
4. Add Round Key Ø XOR state with 128 -bits of the round key Ø again processed by column (though effectively a series of byte operations) Ø inverse for decryption identical l since XOR own inverse, with reversed keys Ø designed to be as simple as possible l l a form of Vernam cipher on expanded key requires other stages for complexity / security
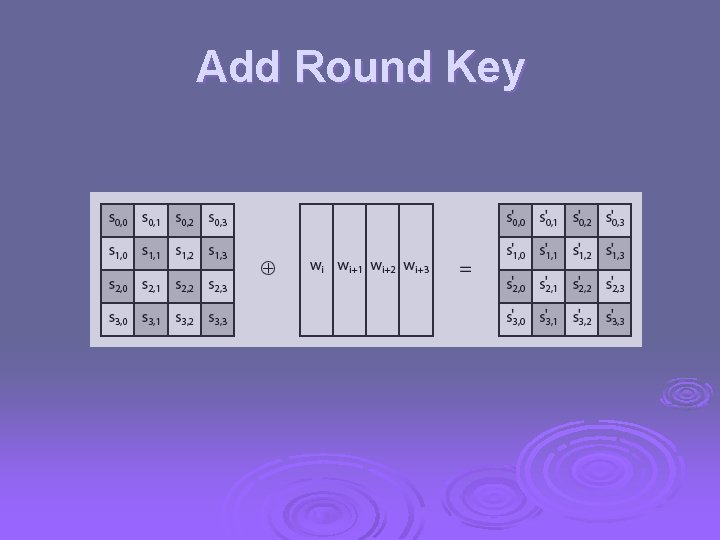
Add Round Key
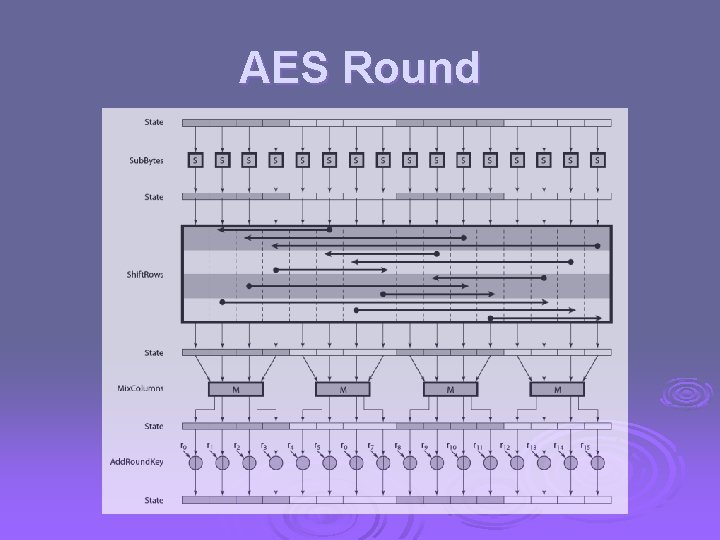
AES Round
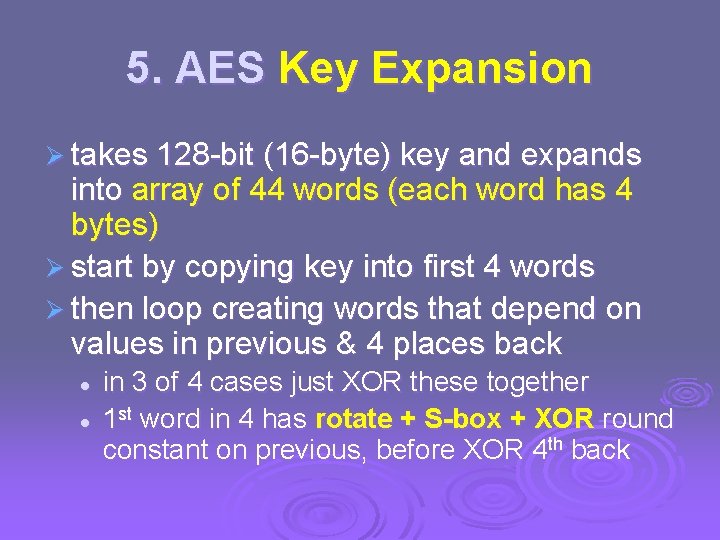
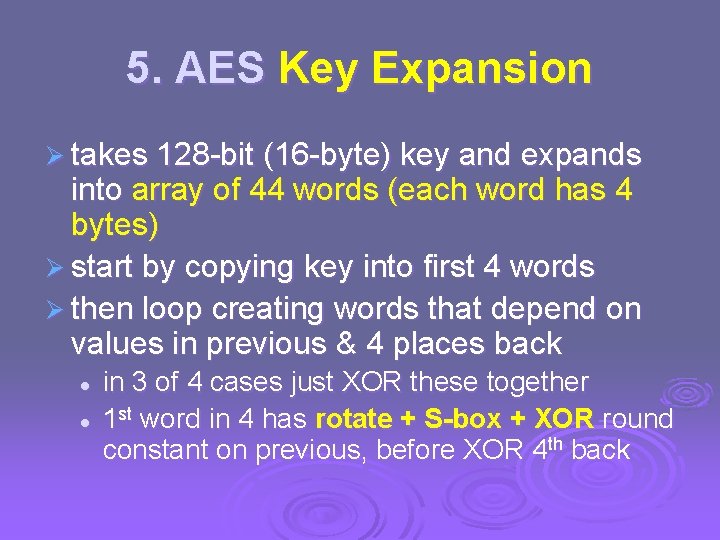
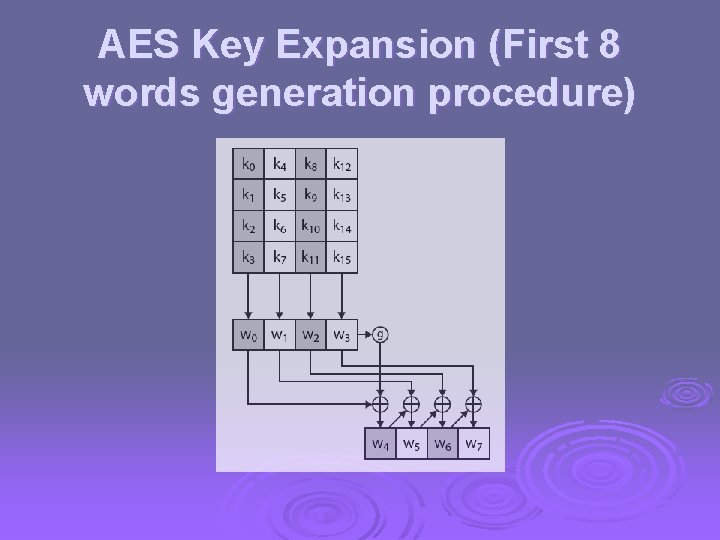
5. AES Key Expansion Ø takes 128 -bit (16 -byte) key and expands into array of 44 words (each word has 4 bytes) Ø start by copying key into first 4 words Ø then loop creating words that depend on values in previous & 4 places back l l in 3 of 4 cases just XOR these together 1 st word in 4 has rotate + S-box + XOR round constant on previous, before XOR 4 th back
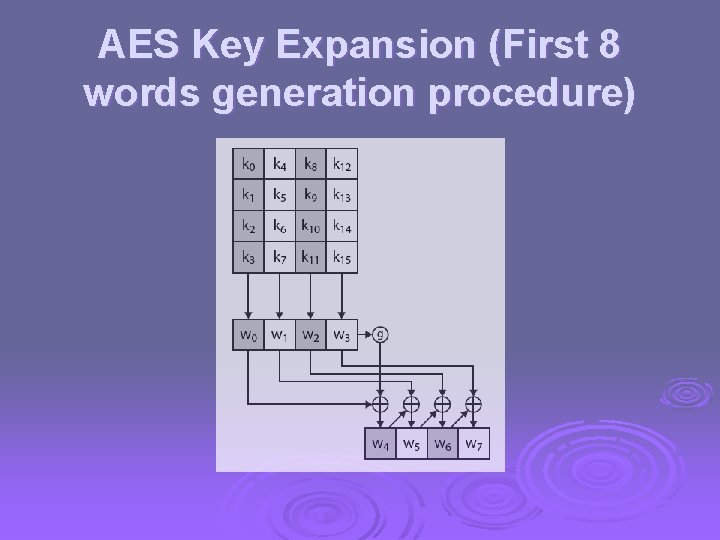
AES Key Expansion (First 8 words generation procedure)
Key Expansion Rationale Ø designed to resist known attacks Ø design criteria included l l l l knowing part key insufficient to find many more invertible transformation fast on wide range of CPU’s use round constants to break symmetry diffuse key bits into round keys enough non-linearity to hinder analysis simplicity of description
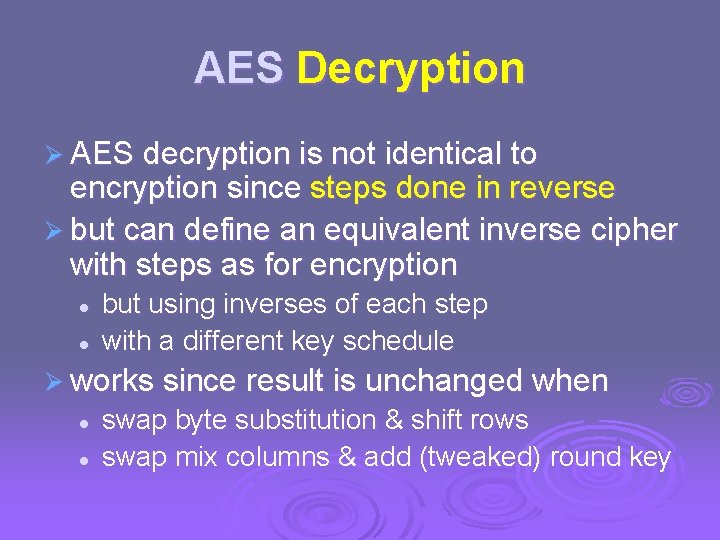
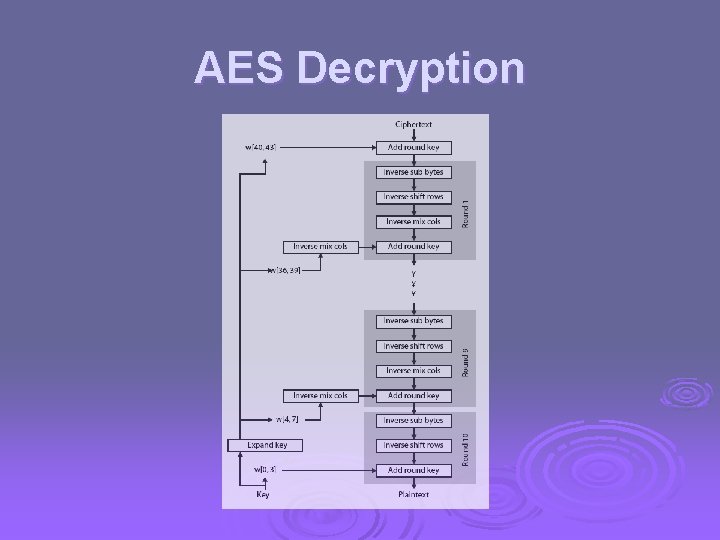
AES Decryption Ø AES decryption is not identical to encryption since steps done in reverse Ø but can define an equivalent inverse cipher with steps as for encryption l l but using inverses of each step with a different key schedule Ø works since result is unchanged when l l swap byte substitution & shift rows swap mix columns & add (tweaked) round key
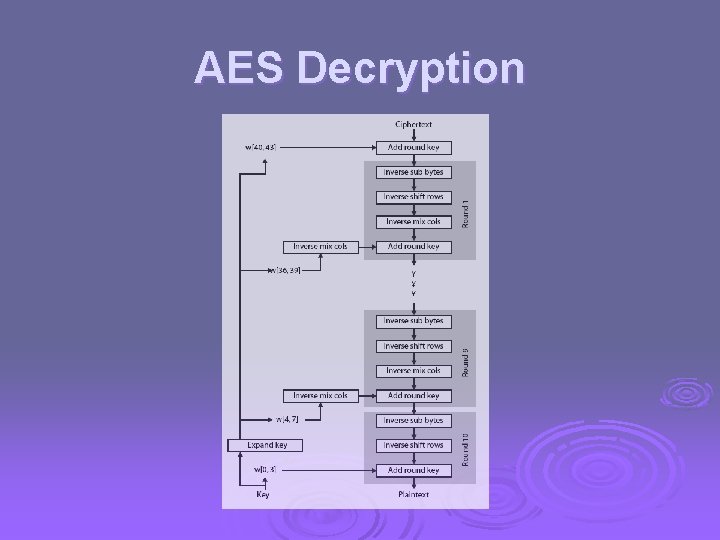
AES Decryption
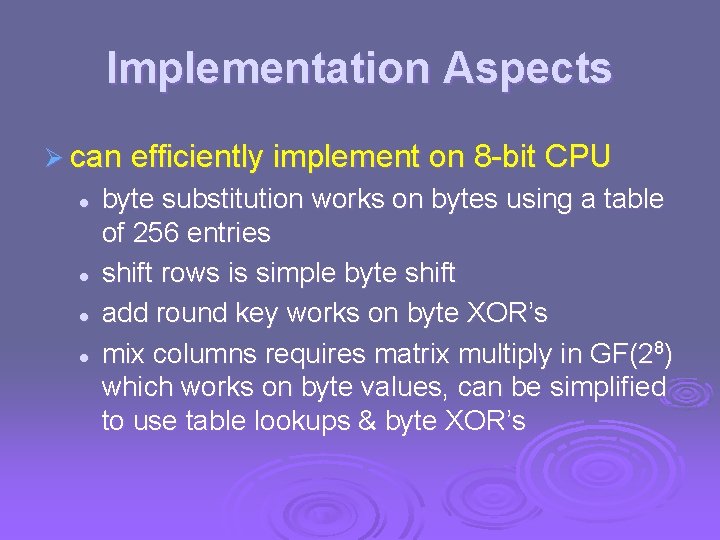
Implementation Aspects Ø can efficiently implement on 8 -bit CPU l l byte substitution works on bytes using a table of 256 entries shift rows is simple byte shift add round key works on byte XOR’s mix columns requires matrix multiply in GF(28) which works on byte values, can be simplified to use table lookups & byte XOR’s
Implementation Aspects Ø can more efficiently implement on 32 -bit CPU l l Ø redefine steps to use 32 -bit words can precompute 4 tables of 256 -words then each column in each round can be computed using 4 table lookups + 4 XORs at a cost of 4 Kb to store tables designers believe this very efficient implementation was a key factor in its selection as the AES cipher
Triple-DES with Three-Keys Ø although are no practical attacks on two- key Triple-DES have some indications Ø can use Triple-DES with Three-Keys to avoid even these l C = EK 3(DK 2(EK 1(P))) Ø has been adopted by some Internet applications, eg PGP, S/MIME
Modes of Operation Ø block ciphers encrypt fixed size blocks l eg. DES encrypts 64 -bit blocks with 56 -bit key Ø need some way to en/decrypt arbitrary amounts of data in practise Ø ANSI X 3. 106 -1983 Modes of Use (now FIPS 81) defines 4 possible modes Ø subsequently 5 defined for AES & DES Ø have block and stream modes
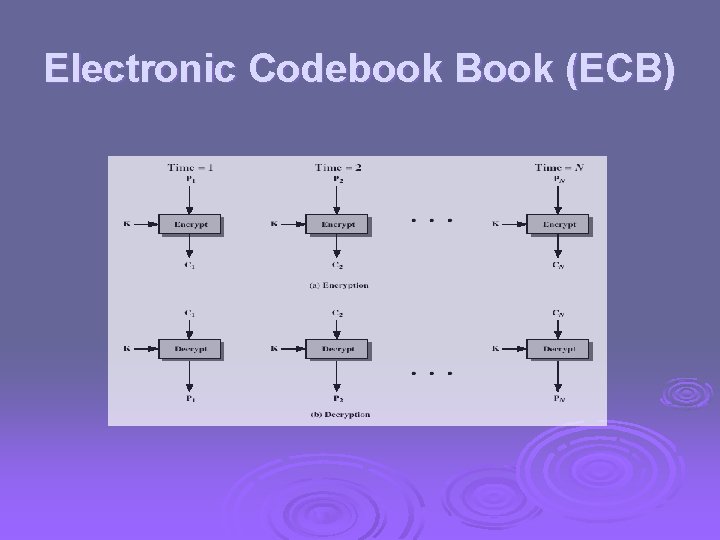
Electronic Codebook Book (ECB) Ø message is broken into independent blocks which are encrypted Ø each block is a value which is substituted, like a codebook, hence name Ø each block is encoded independently of the other blocks Ci = DESK 1(Pi) Ø uses: secure transmission of single values
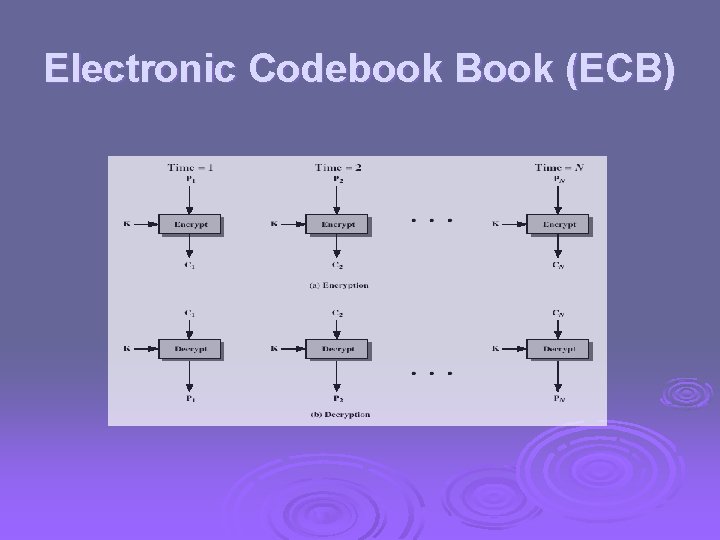
Electronic Codebook Book (ECB)
Advantages and Limitations of ECB Ø message repetitions may show in ciphertext l l l if aligned with message block particularly with data such graphics or with messages that change very little, which become a code-book analysis problem Ø weakness is due to the encrypted message blocks being independent Ø main use is sending only a few blocks of data
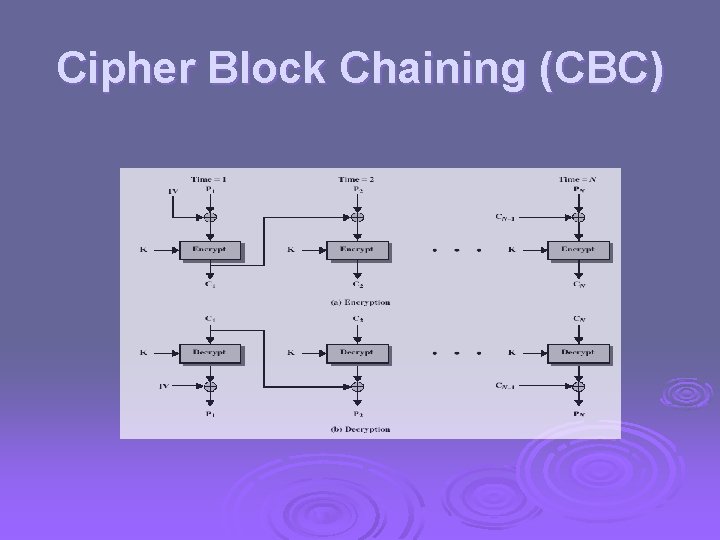
Cipher Block Chaining (CBC) Ø message is broken into blocks Ø linked together in encryption operation Ø each previous cipher blocks is chained with current plaintext block, hence name Ø use Initial Vector (IV) to start process Ci = DESK 1(Pi XOR Ci-1) C-1 = IV Ø uses: bulk data encryption, authentication
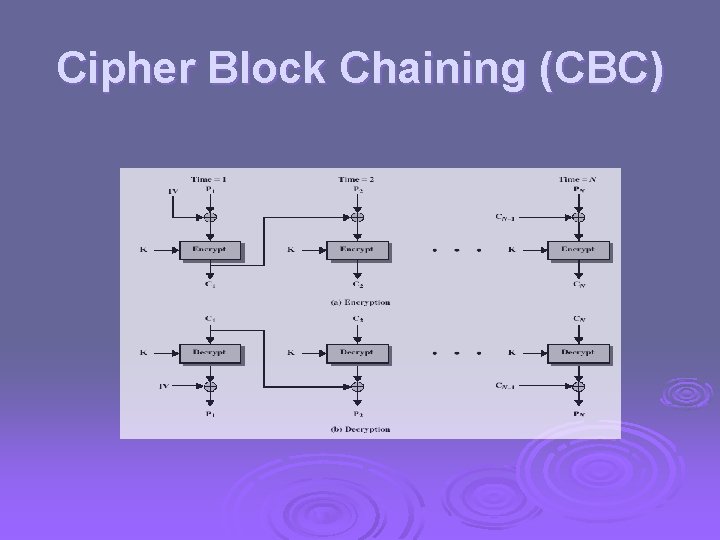
Cipher Block Chaining (CBC)
Message Padding Ø at end of message must handle a possible last short block l l l which is not as large as blocksize of cipher pad either with known non-data value (eg nulls) or pad last block along with count of pad size • eg. [ b 1 b 2 b 3 0 0 5] • means have 3 data bytes, then 5 bytes pad+count l this may require an extra entire block over those in message Ø there are other, more esoteric modes, which avoid the need for an extra block
Advantages and Limitations of CBC Ø a ciphertext block depends on all blocks before it Ø any change to a block affects all following ciphertext blocks Ø need Initialization Vector (IV) l l which must be known to sender & receiver if sent in clear, attacker can change bits of first block, and change IV to compensate hence IV must either be a fixed value (as in EFTPOS) or must be sent encrypted in ECB mode before rest of message
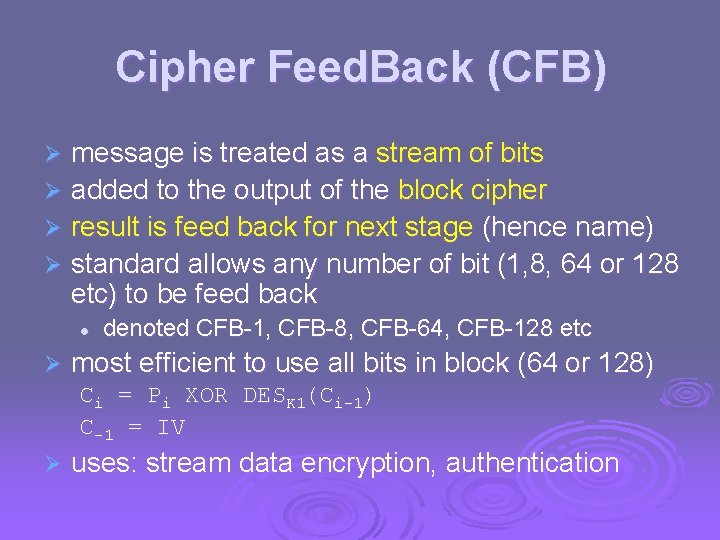
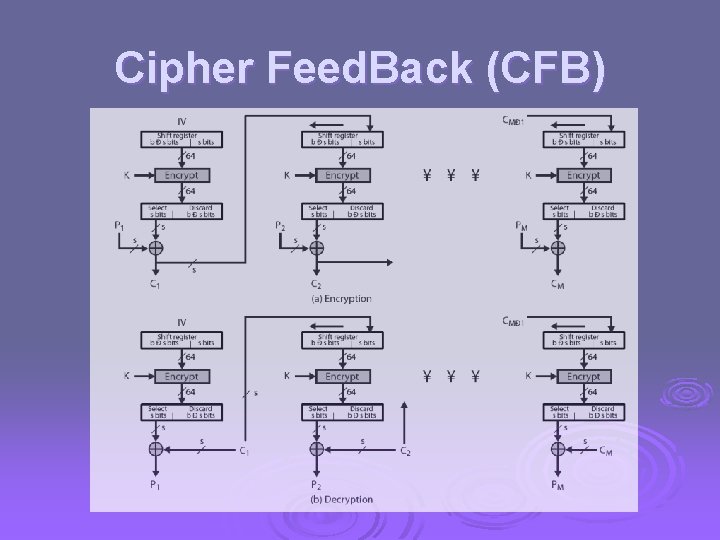
Cipher Feed. Back (CFB) message is treated as a stream of bits Ø added to the output of the block cipher Ø result is feed back for next stage (hence name) Ø standard allows any number of bit (1, 8, 64 or 128 etc) to be feed back Ø l Ø denoted CFB-1, CFB-8, CFB-64, CFB-128 etc most efficient to use all bits in block (64 or 128) Ci = Pi XOR DESK 1(Ci-1) C-1 = IV Ø uses: stream data encryption, authentication
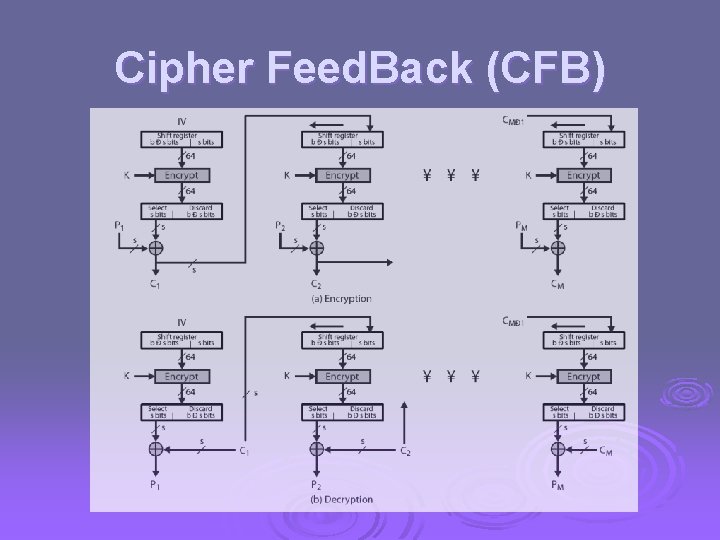
Cipher Feed. Back (CFB)
Advantages and Limitations of CFB Ø appropriate when data arrives in bits/bytes Ø most common stream mode Ø limitation is need to stall while do block encryption after every n-bits Ø note that the block cipher is used in encryption mode at both ends Ø errors propagate for several blocks after the error
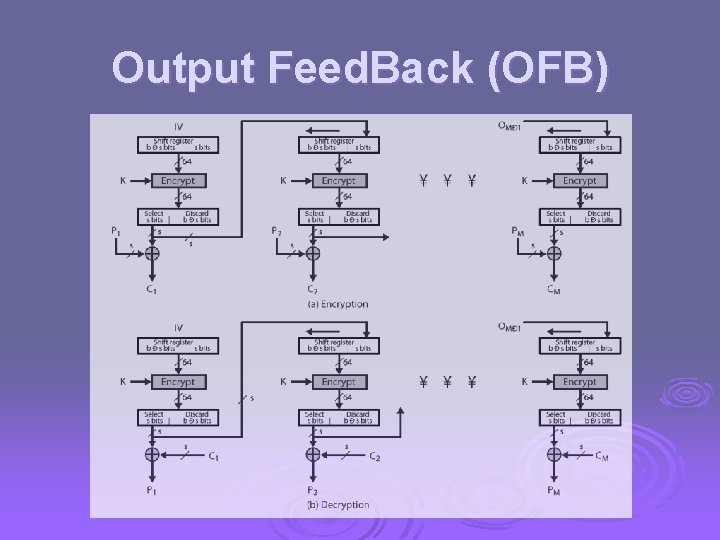
Output Feed. Back (OFB) Ø message is treated as a stream of bits Ø output of cipher is added to message Ø output is then feed back (hence name) Ø feedback is independent of message Ø can be computed in advance Ci = Pi XOR Oi Oi = DESK 1(Oi-1) O-1 = IV Ø uses: stream encryption on noisy channels
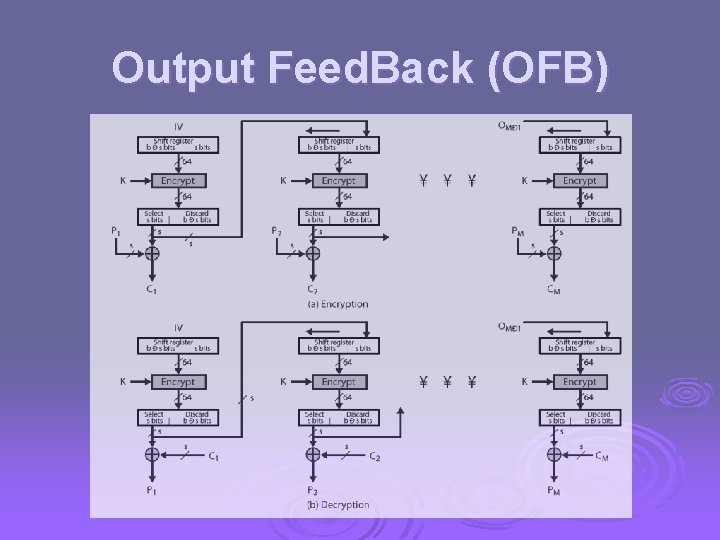
Output Feed. Back (OFB)
Advantages and Limitations of OFB bit errors do not propagate Ø more vulnerable to message stream modification Ø a variation of a Vernam cipher l hence must never reuse the same sequence (key+IV) Ø sender & receiver must remain in sync Ø originally specified with m-bit feedback Ø subsequent research has shown that only full block feedback (ie CFB-64 or CFB-128) should ever be used Ø
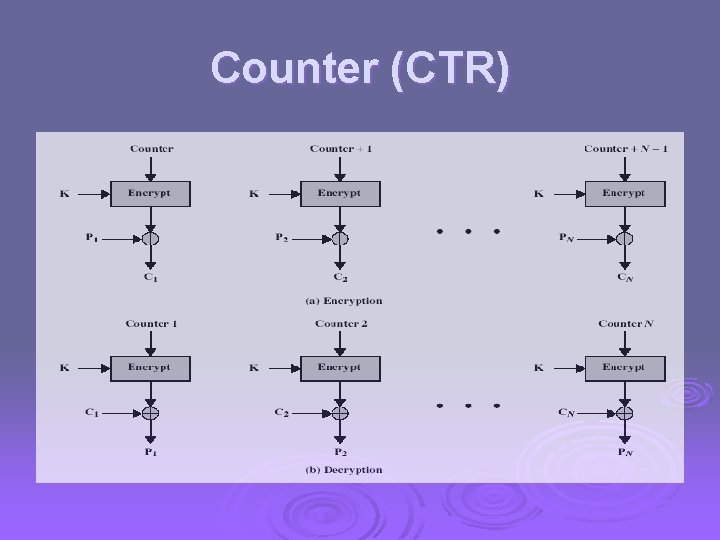
Counter (CTR) Ø a “new” mode, though proposed early on Ø similar to OFB but encrypts counter value rather than any feedback value Ø must have a different key & counter value for every plaintext block (never reused) Ci = Pi XOR Oi Oi = DESK 1(i) Ø uses: high-speed network encryptions
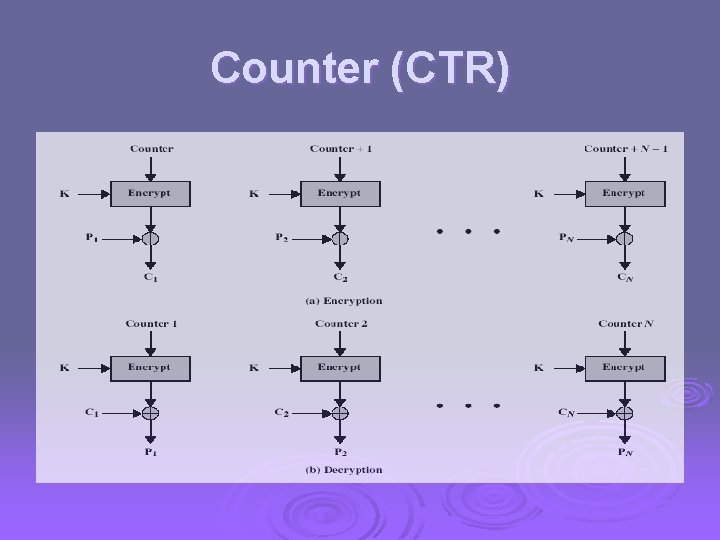
Counter (CTR)