Network Security contd Bijendra Jain bnjcse iitd ernet
Network Security (contd. ) Bijendra Jain (bnj@cse. iitd. ernet. in) 12/13/2021 Tutorial on Network Security: Sep 2003 1
Lecture 3: Public-key cryptography 12/13/2021 Tutorial on Network Security: Sep 2003 2
Public-key cryptography is not necessarily more secure than private-key cryptography l Private-key cryptography is not obsolete—it still is exceptionally useful l Distribution of keys in public-key cryptography is not trivial-- Public-key cryptography has attempted to address this issue head-on l 12/13/2021 Tutorial on Network Security: Sep 2003 3
Public-key cryptography l Public-key cryptography requires the use of two keys: – One for encryption – A related one for decryption One key is kept private, while the other is made public l Can either key be used for encryption, and the other for decryption: l – YES, for RSA 12/13/2021 Tutorial on Network Security: Sep 2003 4
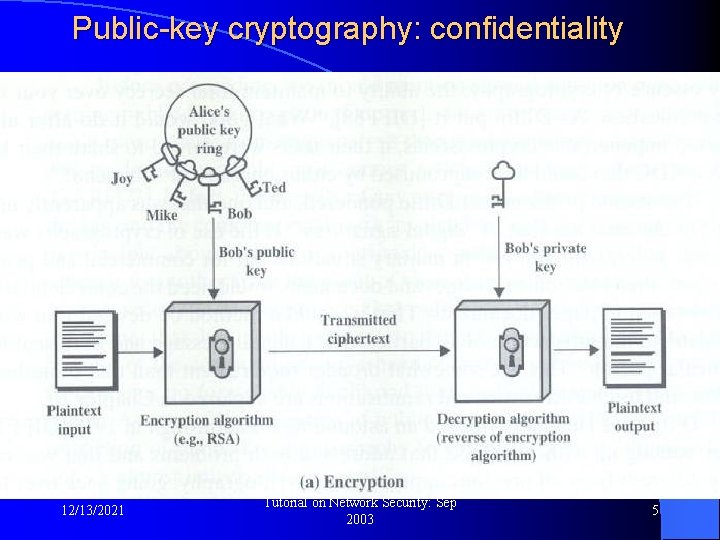
Public-key cryptography: confidentiality l Used for Confidentiality: 12/13/2021 Tutorial on Network Security: Sep 2003 5
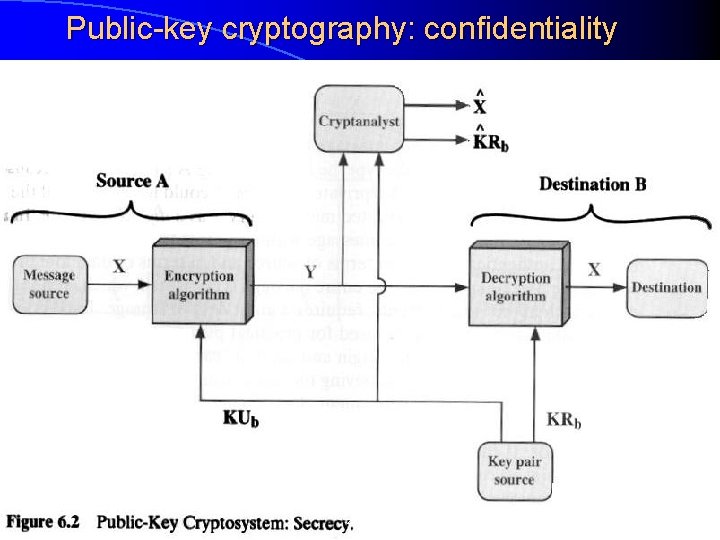
Public-key cryptography: confidentiality l Used for confidentiality: 12/13/2021 Tutorial on Network Security: Sep 2003 6
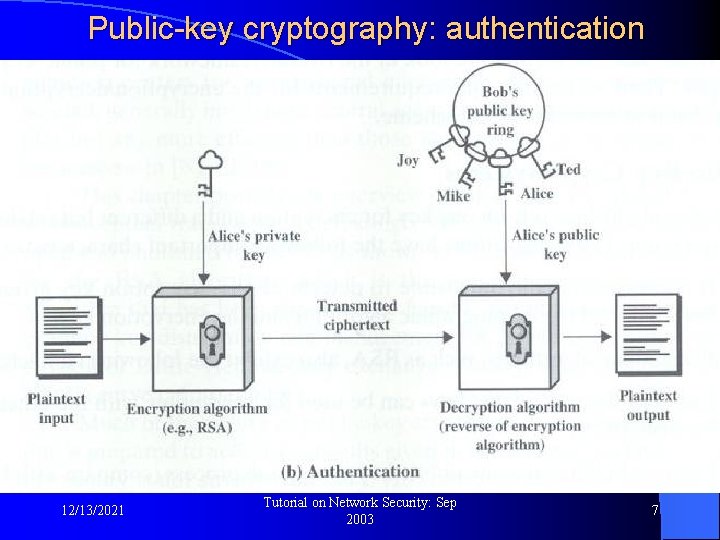
Public-key cryptography: authentication l Used for authentication: 12/13/2021 Tutorial on Network Security: Sep 2003 7
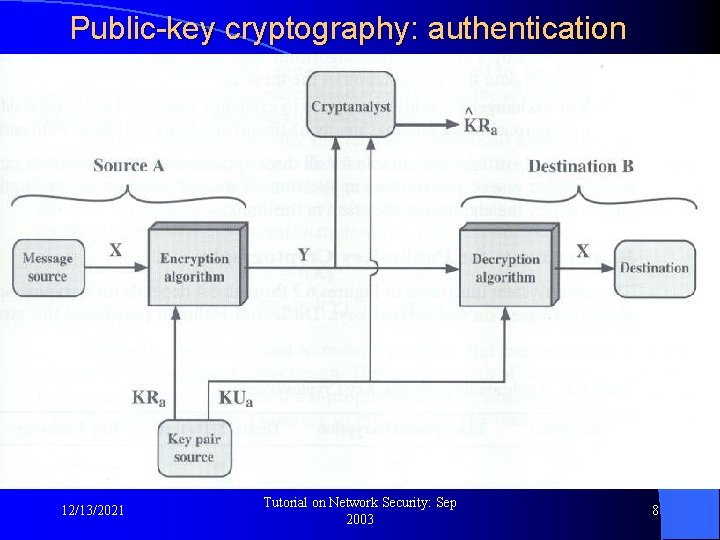
Public-key cryptography: authentication l Used for authentication: 12/13/2021 Tutorial on Network Security: Sep 2003 8
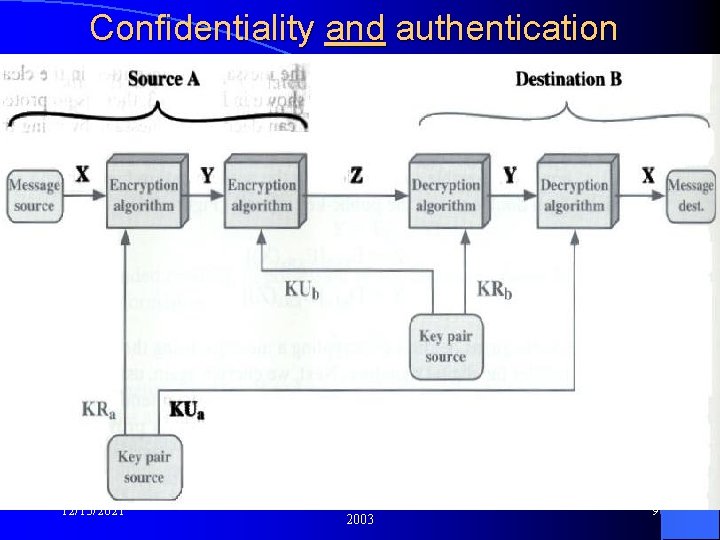
Confidentiality and authentication l Used for : 12/13/2021 Tutorial on Network Security: Sep 2003 9
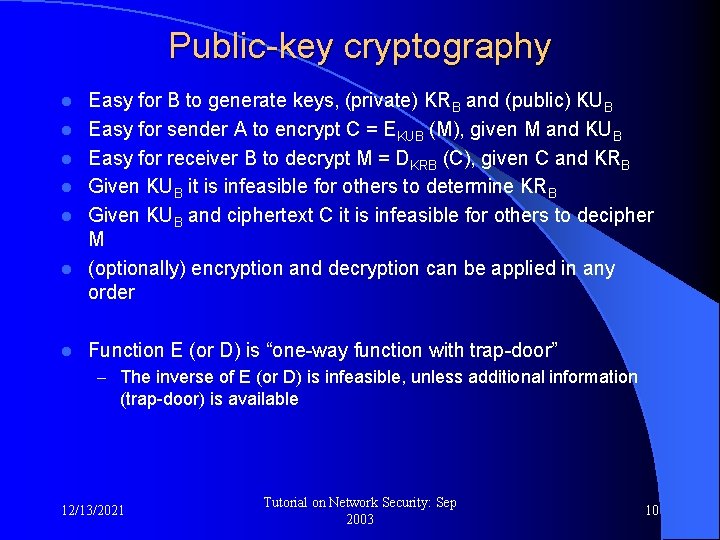
Public-key cryptography l l l l Easy for B to generate keys, (private) KRB and (public) KUB Easy for sender A to encrypt C = EKUB (M), given M and KUB Easy for receiver B to decrypt M = DKRB (C), given C and KRB Given KUB it is infeasible for others to determine KRB Given KUB and ciphertext C it is infeasible for others to decipher M (optionally) encryption and decryption can be applied in any order Function E (or D) is “one-way function with trap-door” – The inverse of E (or D) is infeasible, unless additional information (trap-door) is available 12/13/2021 Tutorial on Network Security: Sep 2003 10
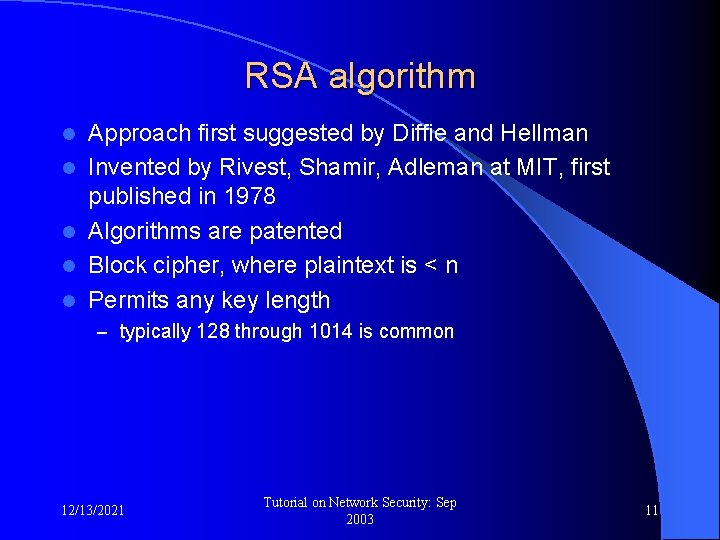
RSA algorithm l l l Approach first suggested by Diffie and Hellman Invented by Rivest, Shamir, Adleman at MIT, first published in 1978 Algorithms are patented Block cipher, where plaintext is < n Permits any key length – typically 128 through 1014 is common 12/13/2021 Tutorial on Network Security: Sep 2003 11
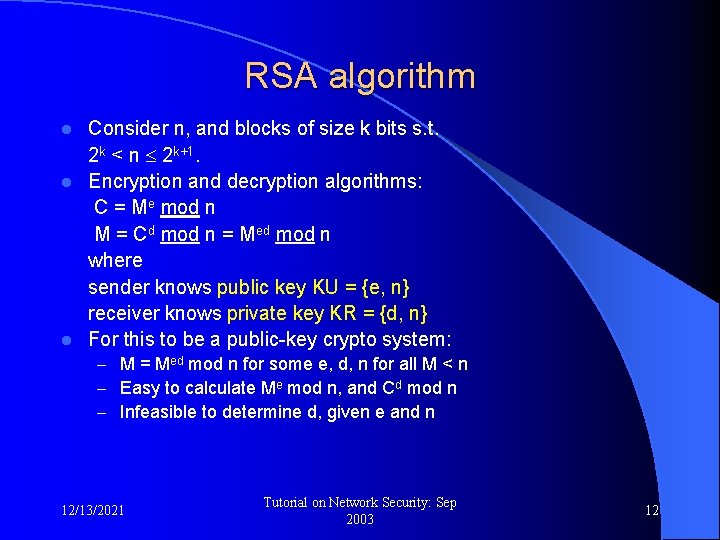
RSA algorithm Consider n, and blocks of size k bits s. t. 2 k < n 2 k+1. l Encryption and decryption algorithms: C = Me mod n M = Cd mod n = Med mod n where sender knows public key KU = {e, n} receiver knows private key KR = {d, n} l For this to be a public-key crypto system: l – M = Med mod n for some e, d, n for all M < n – Easy to calculate Me mod n, and Cd mod n – Infeasible to determine d, given e and n 12/13/2021 Tutorial on Network Security: Sep 2003 12
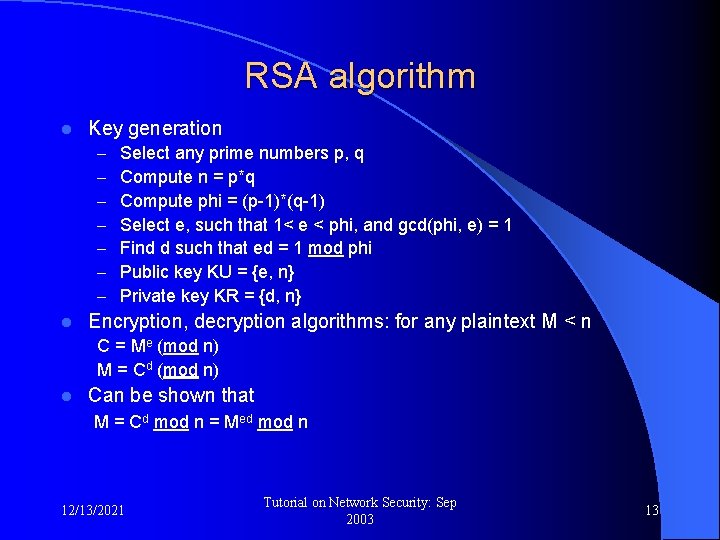
RSA algorithm l Key generation – – – – l Select any prime numbers p, q Compute n = p*q Compute phi = (p-1)*(q-1) Select e, such that 1< e < phi, and gcd(phi, e) = 1 Find d such that ed = 1 mod phi Public key KU = {e, n} Private key KR = {d, n} Encryption, decryption algorithms: for any plaintext M < n C = Me (mod n) M = Cd (mod n) l Can be shown that M = Cd mod n = Med mod n 12/13/2021 Tutorial on Network Security: Sep 2003 13
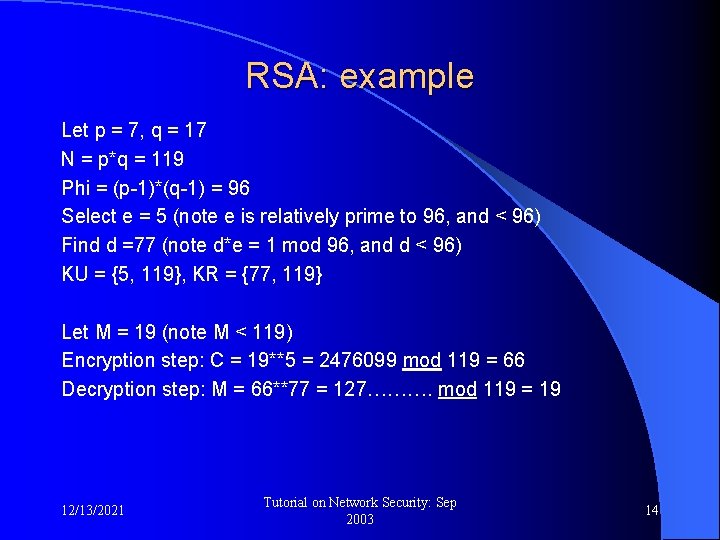
RSA: example Let p = 7, q = 17 N = p*q = 119 Phi = (p-1)*(q-1) = 96 Select e = 5 (note e is relatively prime to 96, and < 96) Find d =77 (note d*e = 1 mod 96, and d < 96) KU = {5, 119}, KR = {77, 119} Let M = 19 (note M < 119) Encryption step: C = 19**5 = 2476099 mod 119 = 66 Decryption step: M = 66**77 = 127………. mod 119 = 19 12/13/2021 Tutorial on Network Security: Sep 2003 14
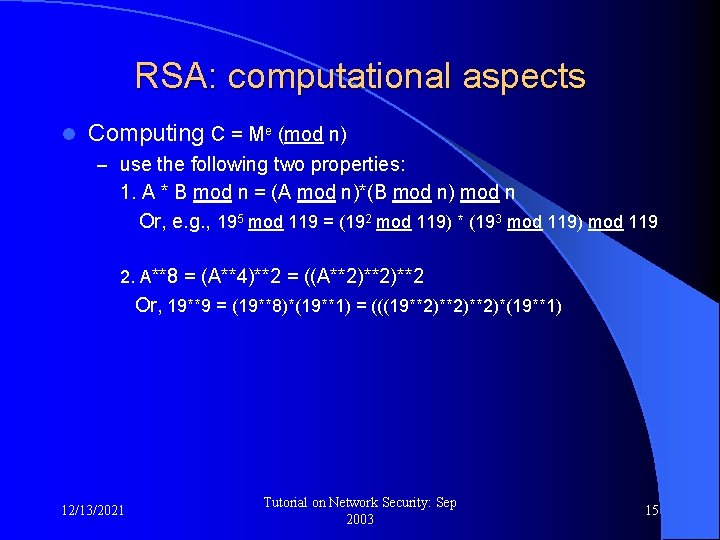
RSA: computational aspects l Computing C = Me (mod n) – use the following two properties: 1. A * B mod n = (A mod n)*(B mod n) mod n Or, e. g. , 195 mod 119 = (192 mod 119) * (193 mod 119) mod 119 2. A**8 = (A**4)**2 = ((A**2)**2 Or, 19**9 = (19**8)*(19**1) = (((19**2)**2)*(19**1) 12/13/2021 Tutorial on Network Security: Sep 2003 15
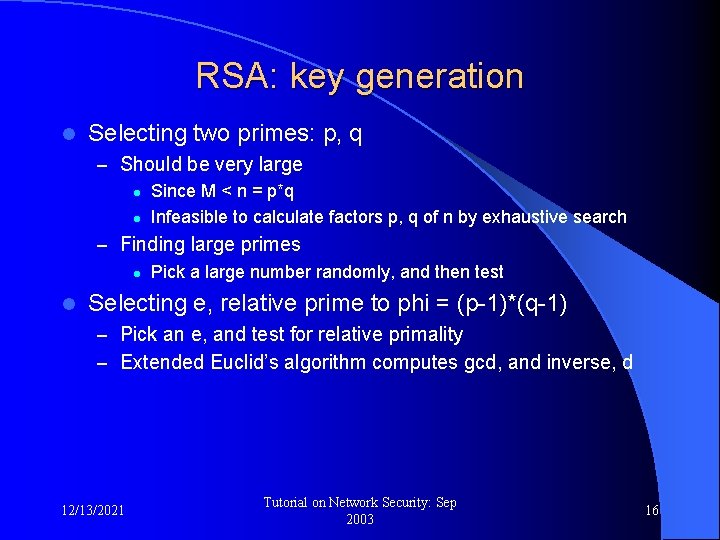
RSA: key generation l Selecting two primes: p, q – Should be very large l Since M < n = p*q l Infeasible to calculate factors p, q of n by exhaustive search – Finding large primes l Pick a large number randomly, and then test l Selecting e, relative prime to phi = (p-1)*(q-1) – Pick an e, and test for relative primality – Extended Euclid’s algorithm computes gcd, and inverse, d 12/13/2021 Tutorial on Network Security: Sep 2003 16
RSA: its strength Brute force l Factor n to obtain p and q l – Then calculate phi = (p-1)*(q-1), and then invert e to obtain d l “Factor” n to obtain phi – Then invert e to obtain d l Progress towards meeting challenges – Ciphers using RSA with keys of size up to 431 bits have been deciphered l Effort involved was only 500 MIPS-years (1 MIPS machine working for 1 year – a 200 MHz Pentium is 50 MIPS) A 2048 bit RSA is expected to require 1014 MIPS-years l Today, and for the near future, consider RSA key size of 1024 to 2048 l Additionally consider selecting p and q appropriately, such as p and q are of approx. same length, etc. l 12/13/2021 Tutorial on Network Security: Sep 2003 17
RSA: distribution of public keys Public announcements l Directory on the web, where data is secured l Public-key authority l Certificates l 12/13/2021 Tutorial on Network Security: Sep 2003 18
RSA: distribution of public keys l Public announcements – Public key is “public” – User can share his/her public with others – Popular with PGP – However, one may even send “false” keys 12/13/2021 Tutorial on Network Security: Sep 2003 19
RSA: distribution of public keys l Publicly accessible directory – By a trusted and well known “authority” – Individual users “register” their public key using some other – – means Public keys are secure For instance on the web, or printed directory Individual users control, update their public keys, and do so in a secure manner Weaknesses: l l 12/13/2021 Break into the authority’s database Alter the key during communication Tutorial on Network Security: Sep 2003 20
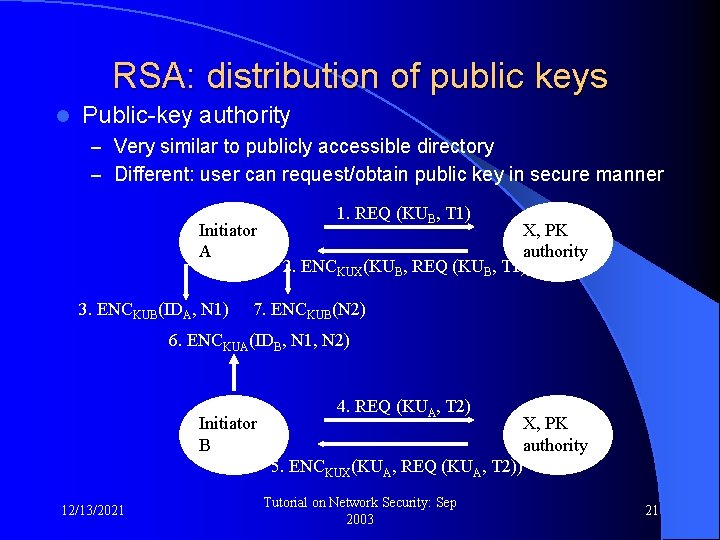
RSA: distribution of public keys l Public-key authority – Very similar to publicly accessible directory – Different: user can request/obtain public key in secure manner Initiator A 3. ENCKUB(IDA, N 1) 1. REQ (KUB, T 1) X, PK authority 2. ENCKUX(KUB, REQ (KUB, T 1)) 7. ENCKUB(N 2) 6. ENCKUA(IDB, N 1, N 2) Initiator B 4. REQ (KUA, T 2) X, PK authority 5. ENCKUX(KUA, REQ (KUA, T 2)) 12/13/2021 Tutorial on Network Security: Sep 2003 21
RSA: distribution of public keys l Public-key certificates – Certificates need not be issued each time – Sender provides public key with a certificate – Receiver checks the certificate, thereby confirms public key – A certificate: l Anyone can read, determine the owner’s public key l Anyone can verify that certificate is signed by authority l Only certificate can create certificate l Anyone can check “currency” of certificate 12/13/2021 Tutorial on Network Security: Sep 2003 22
RSA: Certificates CERTA = ENCPUX (IDA, KUA, TA, DURA) where l PUX is public key of certification authority l IDA is user ID l KUA is public key of A l TA is time of issuance of certificate l DURA is the duration for which the certificate is valid 12/13/2021 Tutorial on Network Security: Sep 2003 23
Lecture 4: Message Authentication 12/13/2021 Tutorial on Network Security: Sep 2003 24
Message authentication l Source of Message – Protection against masquerading l Integrity of message – Protection against modification l Integrity of sequence of messages – Protection against deletion, addition and re-ordering l Integrity of timing – Protection against delay and replay 12/13/2021 Tutorial on Network Security: Sep 2003 25
Using private-key encryption l Encrypt message using private-key encryption system – Basically provides confidentiality – Authentication and Integrity check are difficult, but possible l Particularly if it is some bit sequence l Use an FCS (frame check sequence), as in TCP Integrity of a sequence of TCP messages can also be ensured l Does not provide for non-repudiation l 12/13/2021 Tutorial on Network Security: Sep 2003 26
Using public-key encryption Similar, except that it only provides for authentication l Again, the transmitted message must have some structure (FCS, for example) l 12/13/2021 Tutorial on Network Security: Sep 2003 27
Message Authentication Codes Integrity check is not difficult any more l Based on private-key encryption l Transmitted message in (M, MAC) MAC = CK(M) where: l – C is MAC algorithm, – K is the shared key l Provides for message integrity, user authentication, but non-repudiation 12/13/2021 Tutorial on Network Security: Sep 2003 28
Message Authentication Codes l Algorithm C differs: – from encryption in that it is NOT reversible – From FCS, etc. in that it is not easy to design a new message with same FCS – From use of hash functions, in that encryption and “hashing” is simultaneous l Algorithm C is more difficult to crack 12/13/2021 Tutorial on Network Security: Sep 2003 29
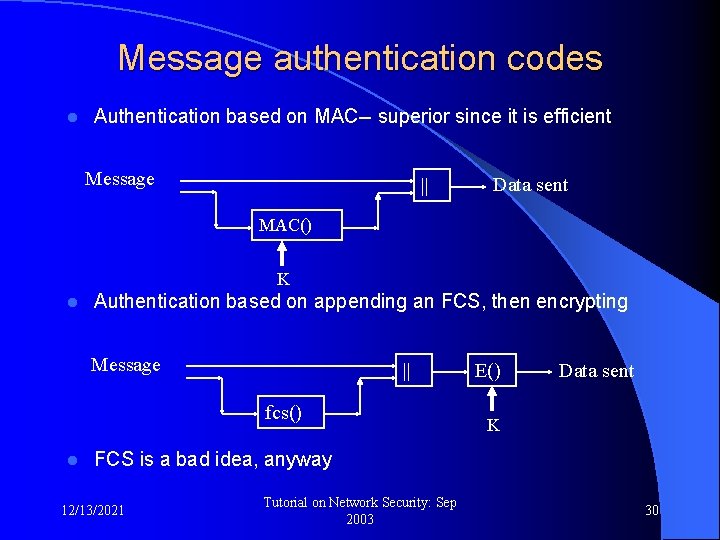
Message authentication codes l Authentication based on MAC-- superior since it is efficient Message || Data sent MAC() K l Authentication based on appending an FCS, then encrypting Message || fcs() l E() Data sent K FCS is a bad idea, anyway 12/13/2021 Tutorial on Network Security: Sep 2003 30
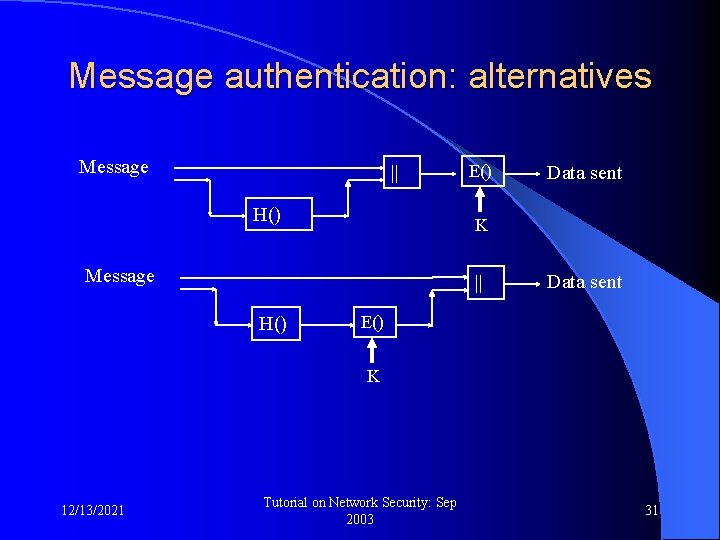
Message authentication: alternatives Message || H() E() K Message || H() Data sent E() K 12/13/2021 Tutorial on Network Security: Sep 2003 31
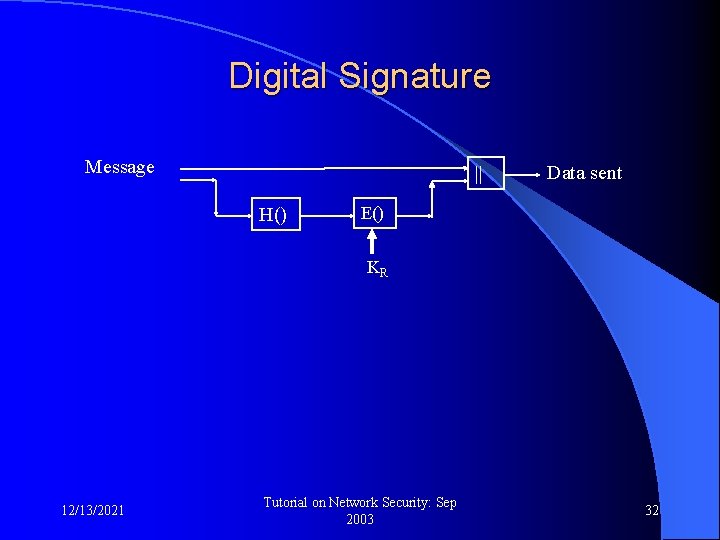
Digital Signature Message || H() Data sent E() KR 12/13/2021 Tutorial on Network Security: Sep 2003 32
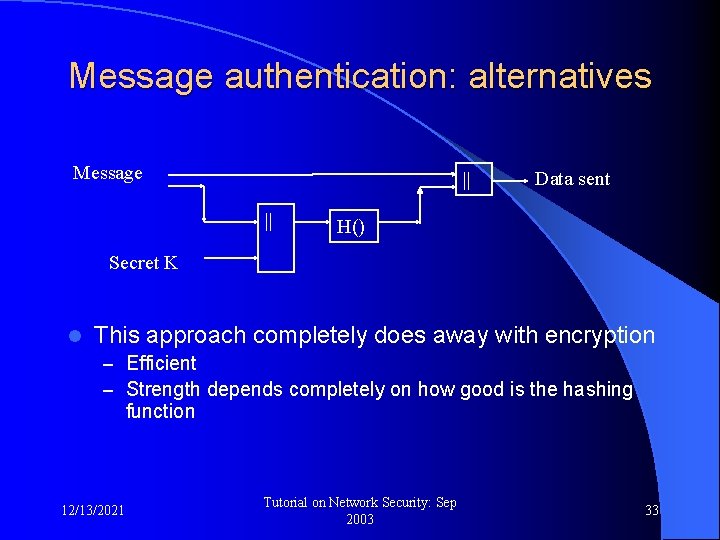
Message authentication: alternatives Message || || Data sent H() Secret K l This approach completely does away with encryption – Efficient – Strength depends completely on how good is the hashing function 12/13/2021 Tutorial on Network Security: Sep 2003 33
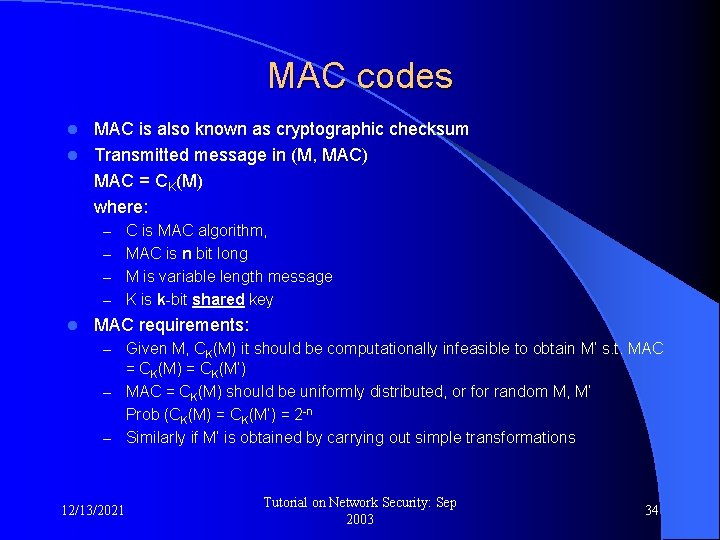
MAC codes MAC is also known as cryptographic checksum l Transmitted message in (M, MAC) MAC = CK(M) where: l – C is MAC algorithm, – MAC is n bit long – M is variable length message – K is k-bit shared key l MAC requirements: – Given M, CK(M) it should be computationally infeasible to obtain M’ s. t. MAC = CK(M) = CK(M’) – MAC = CK(M) should be uniformly distributed, or for random M, M’ Prob (CK(M) = CK(M’) = 2 -n – Similarly if M’ is obtained by carrying out simple transformations 12/13/2021 Tutorial on Network Security: Sep 2003 34
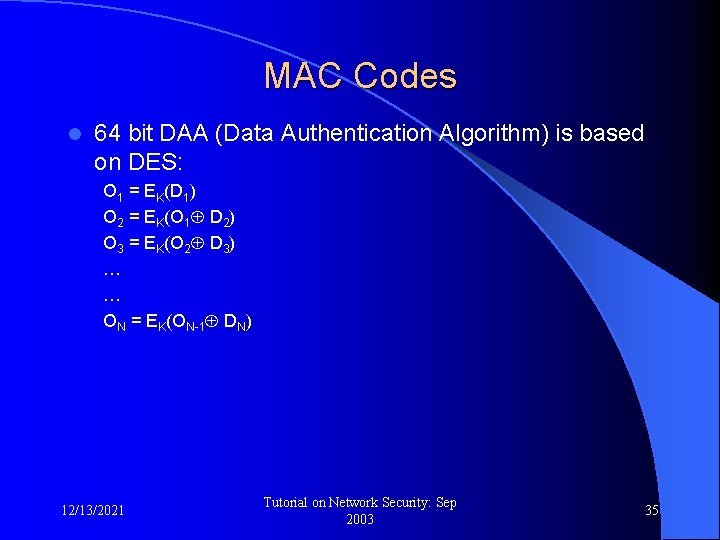
MAC Codes l 64 bit DAA (Data Authentication Algorithm) is based on DES: O 1 = EK(D 1) O 2 = EK(O 1 D 2) O 3 = EK(O 2 D 3) … … ON = EK(ON-1 DN) 12/13/2021 Tutorial on Network Security: Sep 2003 35
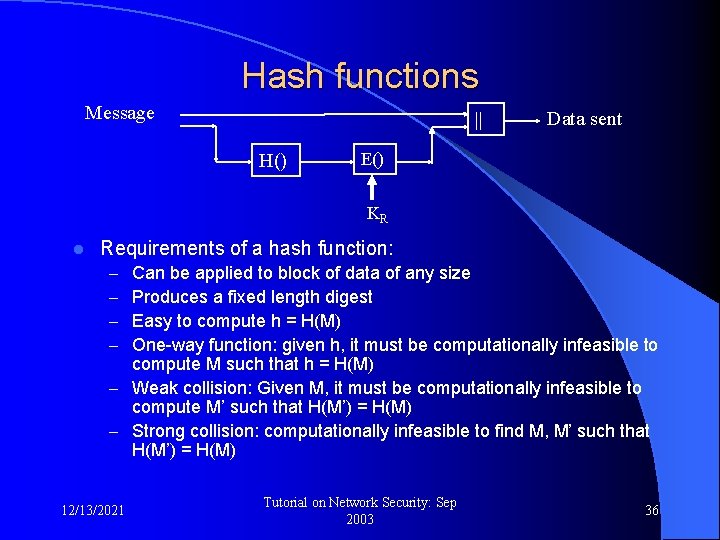
Hash functions Message || H() Data sent E() KR l Requirements of a hash function: Can be applied to block of data of any size Produces a fixed length digest Easy to compute h = H(M) One-way function: given h, it must be computationally infeasible to compute M such that h = H(M) – Weak collision: Given M, it must be computationally infeasible to compute M’ such that H(M’) = H(M) – Strong collision: computationally infeasible to find M, M’ such that H(M’) = H(M) – – 12/13/2021 Tutorial on Network Security: Sep 2003 36
Hash functions l Simple hash function: O 1 = D 1 O 2 = O 1 D 2 O 3 = O 2 D 3 … … ON = ON-1 DN l MD 4, MD 5 12/13/2021 Tutorial on Network Security: Sep 2003 37
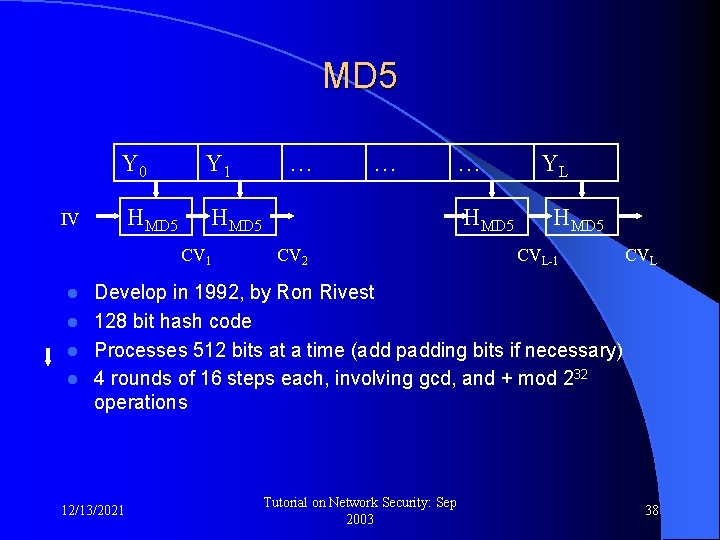
MD 5 Y 0 Y 1 HMD 5 IV CV 1 … … … HMD 5 CV 2 YL HMD 5 CVL-1 CVL Develop in 1992, by Ron Rivest l 128 bit hash code l Processes 512 bits at a time (add padding bits if necessary) l 4 rounds of 16 steps each, involving gcd, and + mod 232 operations l 12/13/2021 Tutorial on Network Security: Sep 2003 38
MD 4 Similar to MD 5, developed earlier in 1990 by Ron Rivest l 128 bit hash code, processes 512 bits at a time l 3 rounds of 16 steps each, involving gcd, and + mod 232 operations l faster l 12/13/2021 Tutorial on Network Security: Sep 2003 39
SHA-1 hash function l l l l Developed by NIST in 1995 Based on MD 4 160 bit hash Operates on blocks of length 512 bit More secure against brute force attacks Appears to be secure against cryptanalysis MD 5 and SHA-1 are equally fast, simple 12/13/2021 Tutorial on Network Security: Sep 2003 40
HMAC l l l Truly a MAC Required for IPSec Based on hash functions Any “good” hash function can be used The “IV” can be kept secret (becomes the key) MD 5 or SHA-1 can be used 12/13/2021 Tutorial on Network Security: Sep 2003 41
Thanks 12/13/2021 Tutorial on Network Security: Sep 2003 42
- Slides: 42