Network Security contd Bijendra Jain bnjcse iitd ernet
Network Security (contd. ) Bijendra Jain (bnj@cse. iitd. ernet. in) 9/14/2021 Tutorial on Network Security: Sep 2003 1
Lecture 5: IPSec 9/14/2021 Tutorial on Network Security: Sep 2003 2
IPSec: IP Security l An IETF standard – IPSec architecture and related standards published as refer RFC 1825 thru RFC 1829 l Adrresses security issues arising from – authentication and confidentiality – connecting a remote host to a server – Interconnecting two LANs using a public network l Applications: – wide-area networking of branch offices using Internet – Interconnecting supplier/distributor extranets to enterprise network – Telecommuting – E-commerce l Implemented in clients, servers or in routers 9/14/2021 Tutorial on Network Security: Sep 2003 3
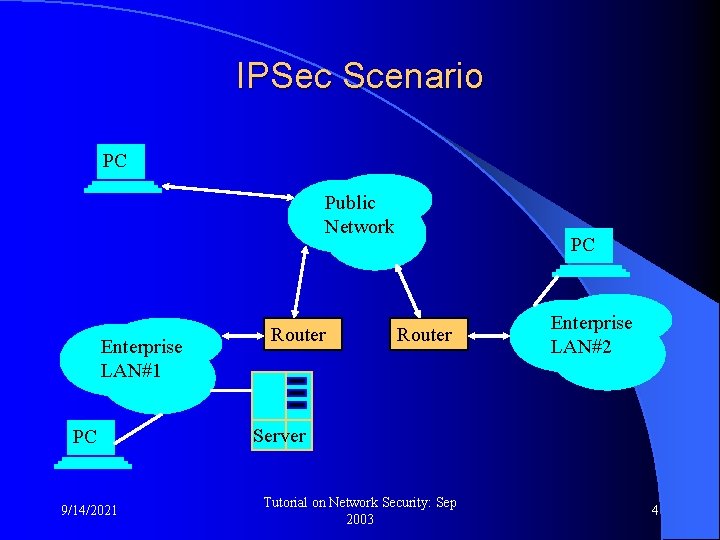
IPSec Scenario PC Public Network Enterprise LAN#1 PC 9/14/2021 Router PC Router Enterprise LAN#2 Server Tutorial on Network Security: Sep 2003 4
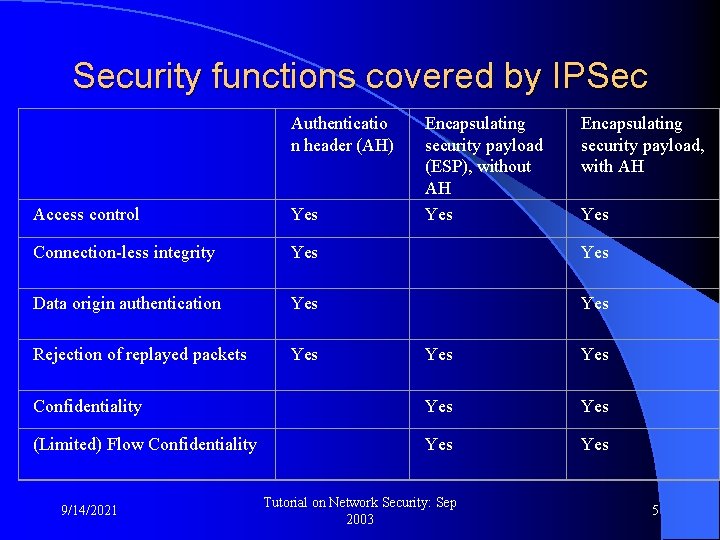
Security functions covered by IPSec Authenticatio n header (AH) Encapsulating security payload (ESP), without AH Yes Encapsulating security payload, with AH Access control Yes Connection-less integrity Yes Data origin authentication Yes Rejection of replayed packets Yes Yes Confidentiality Yes (Limited) Flow Confidentiality Yes 9/14/2021 Tutorial on Network Security: Sep 2003 5
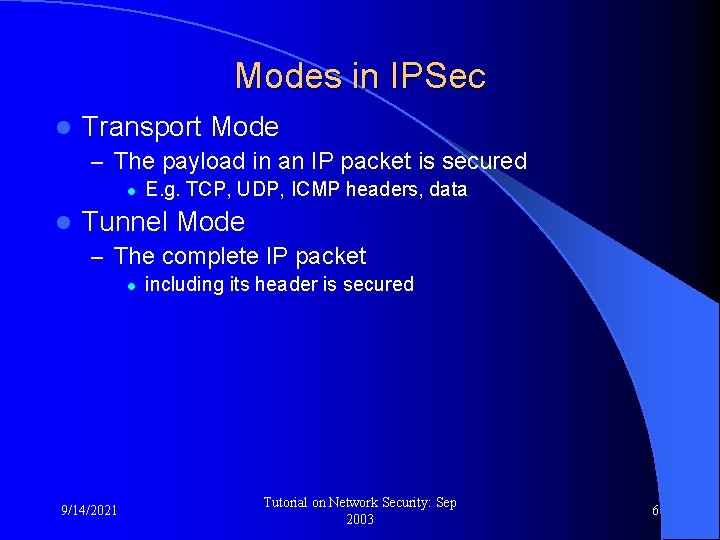
Modes in IPSec l Transport Mode – The payload in an IP packet is secured l l E. g. TCP, UDP, ICMP headers, data Tunnel Mode – The complete IP packet l 9/14/2021 including its header is secured Tutorial on Network Security: Sep 2003 6
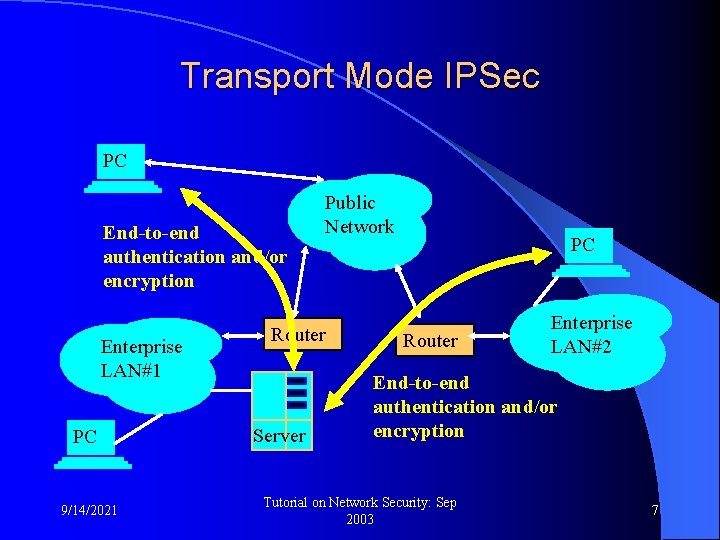
Transport Mode IPSec PC End-to-end authentication and/or encryption Enterprise LAN#1 PC 9/14/2021 Public Network Router Server PC Router Enterprise LAN#2 End-to-end authentication and/or encryption Tutorial on Network Security: Sep 2003 7
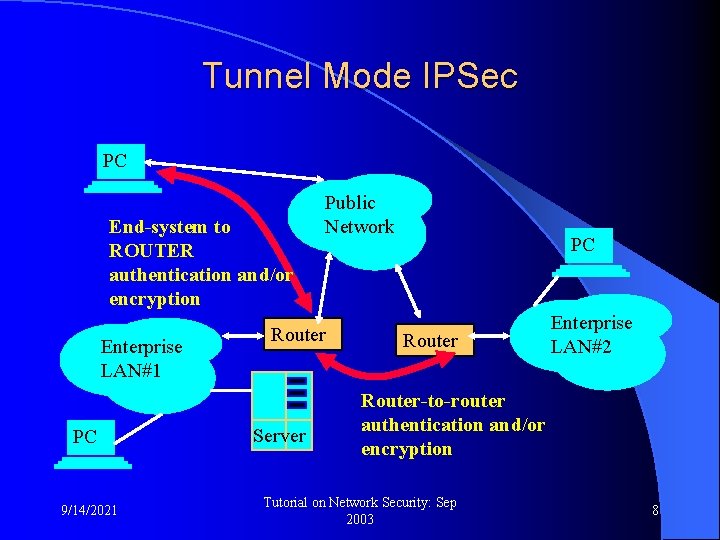
Tunnel Mode IPSec PC End-system to ROUTER authentication and/or encryption Enterprise LAN#1 PC 9/14/2021 Public Network Router Server PC Router Enterprise LAN#2 Router-to-router authentication and/or encryption Tutorial on Network Security: Sep 2003 8
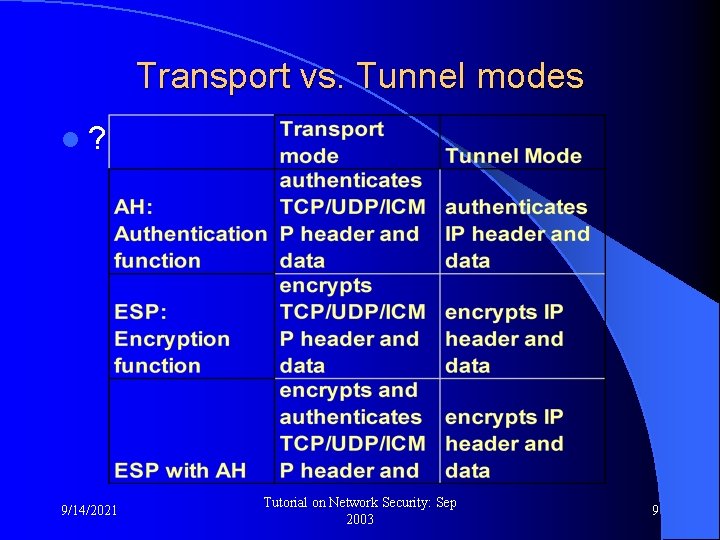
Transport vs. Tunnel modes l? 9/14/2021 Tutorial on Network Security: Sep 2003 9
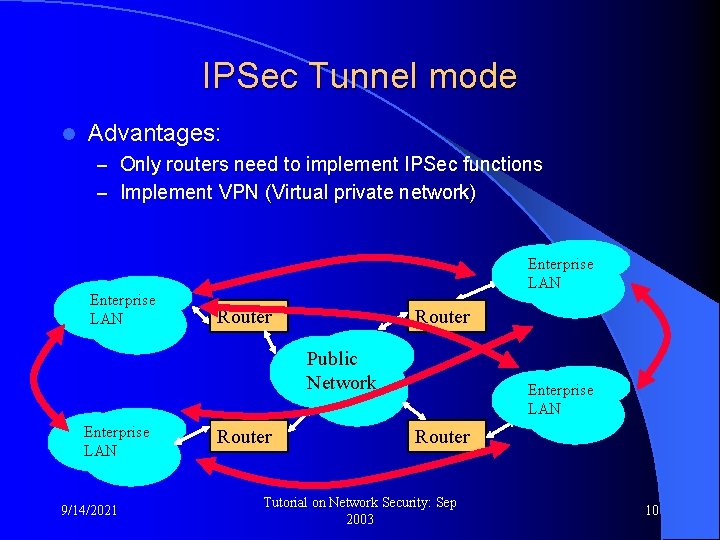
IPSec Tunnel mode l Advantages: – Only routers need to implement IPSec functions – Implement VPN (Virtual private network) Enterprise LAN Router Public Network Enterprise LAN 9/14/2021 Router Enterprise LAN Router Tutorial on Network Security: Sep 2003 10
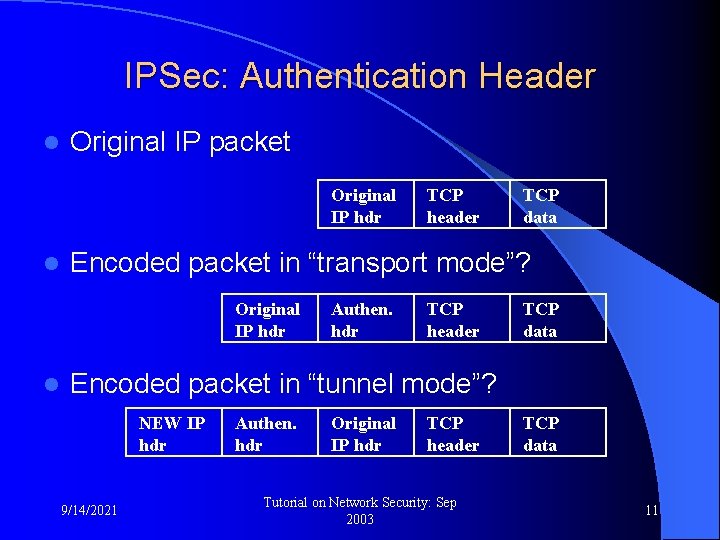
IPSec: Authentication Header l Original IP packet Original IP hdr l TCP data Encoded packet in “transport mode”? Original IP hdr l TCP header Authen. hdr TCP header TCP data Encoded packet in “tunnel mode”? NEW IP hdr 9/14/2021 Authen. hdr Original IP hdr TCP header Tutorial on Network Security: Sep 2003 TCP data 11
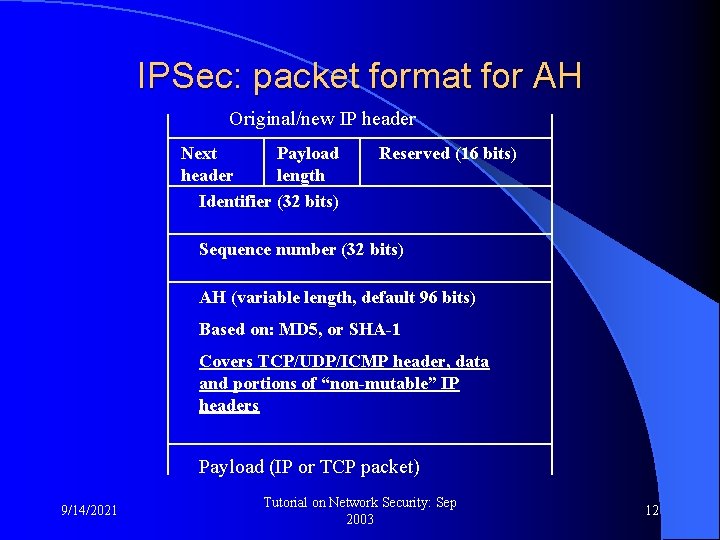
IPSec: packet format for AH Original/new IP header Next Payload header length Identifier (32 bits) Reserved (16 bits) Sequence number (32 bits) AH (variable length, default 96 bits) Based on: MD 5, or SHA-1 Covers TCP/UDP/ICMP header, data and portions of “non-mutable” IP headers Payload (IP or TCP packet) 9/14/2021 Tutorial on Network Security: Sep 2003 12
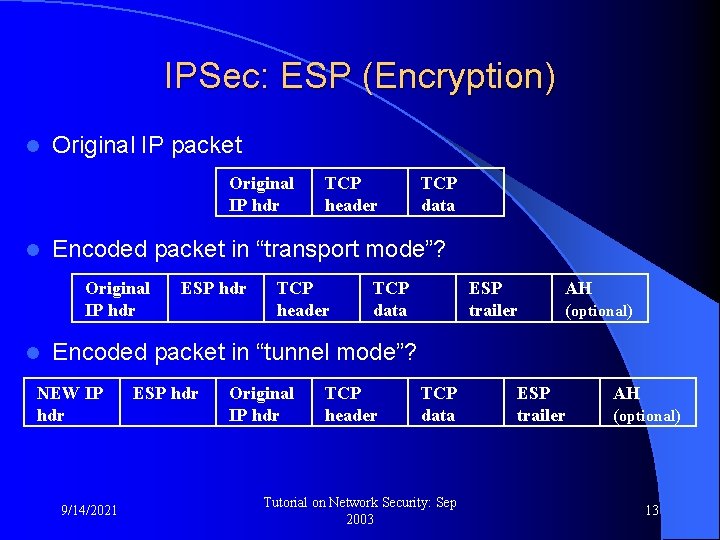
IPSec: ESP (Encryption) l Original IP packet Original IP hdr l TCP data Encoded packet in “transport mode”? Original IP hdr l TCP header ESP hdr TCP header TCP data ESP trailer AH (optional) Encoded packet in “tunnel mode”? NEW IP hdr 9/14/2021 ESP hdr Original IP hdr TCP header TCP data Tutorial on Network Security: Sep 2003 ESP trailer AH (optional) 13
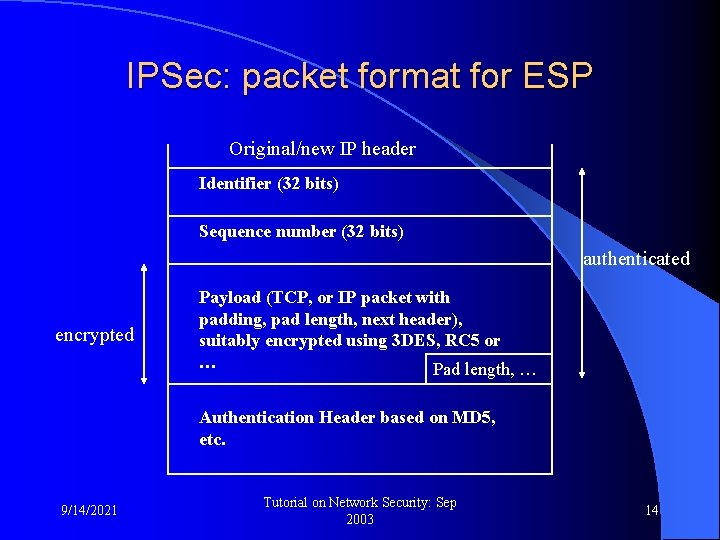
IPSec: packet format for ESP Original/new IP header Identifier (32 bits) Sequence number (32 bits) authenticated encrypted Payload (TCP, or IP packet with padding, pad length, next header), suitably encrypted using 3 DES, RC 5 or … Pad length, … Authentication Header based on MD 5, etc. 9/14/2021 Tutorial on Network Security: Sep 2003 14
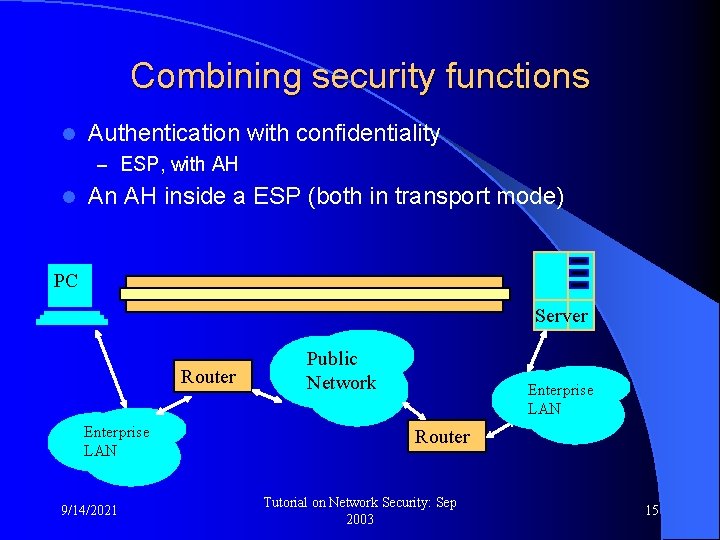
Combining security functions l Authentication with confidentiality – ESP, with AH l An AH inside a ESP (both in transport mode) PC Server Router Enterprise LAN 9/14/2021 Public Network Enterprise LAN Router Tutorial on Network Security: Sep 2003 15
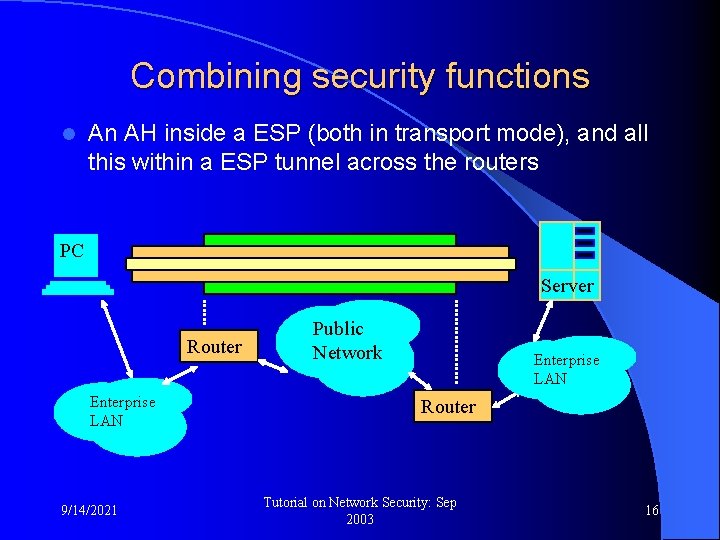
Combining security functions l An AH inside a ESP (both in transport mode), and all this within a ESP tunnel across the routers PC Server Router Enterprise LAN 9/14/2021 Public Network Enterprise LAN Router Tutorial on Network Security: Sep 2003 16
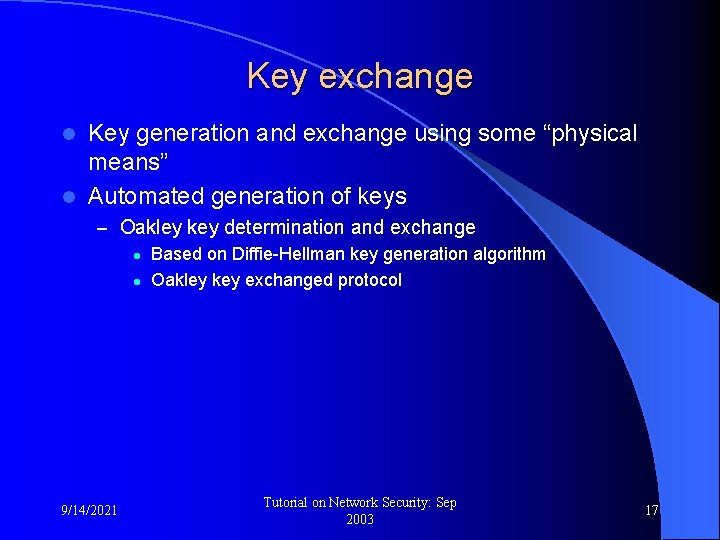
Key exchange Key generation and exchange using some “physical means” l Automated generation of keys l – Oakley key determination and exchange l Based on Diffie-Hellman key generation algorithm l Oakley key exchanged protocol 9/14/2021 Tutorial on Network Security: Sep 2003 17
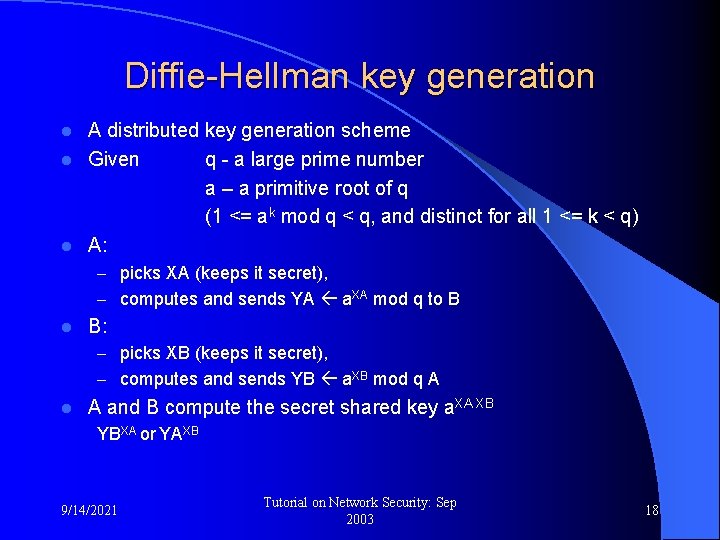
Diffie-Hellman key generation A distributed key generation scheme l Given q - a large prime number a – a primitive root of q (1 <= ak mod q < q, and distinct for all 1 <= k < q) l A: l – picks XA (keeps it secret), – computes and sends YA a. XA mod q to B l B: – picks XB (keeps it secret), – computes and sends YB a. XB mod q A l A and B compute the secret shared key a. XA XB YBXA or YAXB 9/14/2021 Tutorial on Network Security: Sep 2003 18
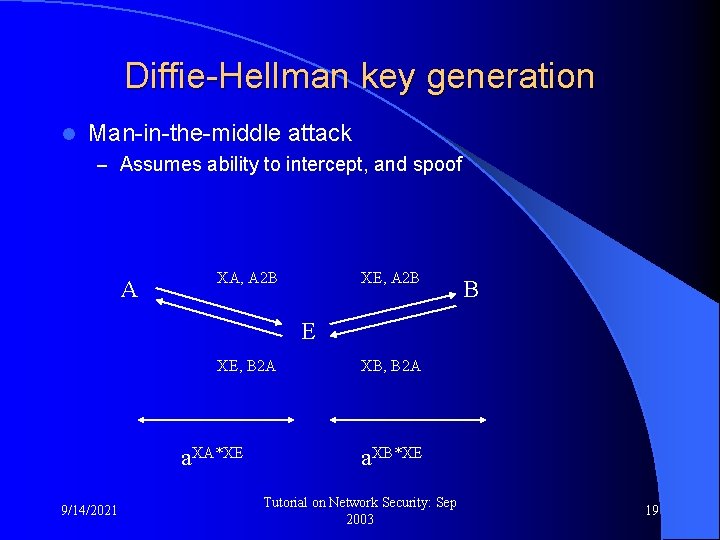
Diffie-Hellman key generation l Man-in-the-middle attack – Assumes ability to intercept, and spoof A XA, A 2 B XE, A 2 B B E XE, B 2 A a. XA*XE 9/14/2021 XB, B 2 A a. XB*XE Tutorial on Network Security: Sep 2003 19
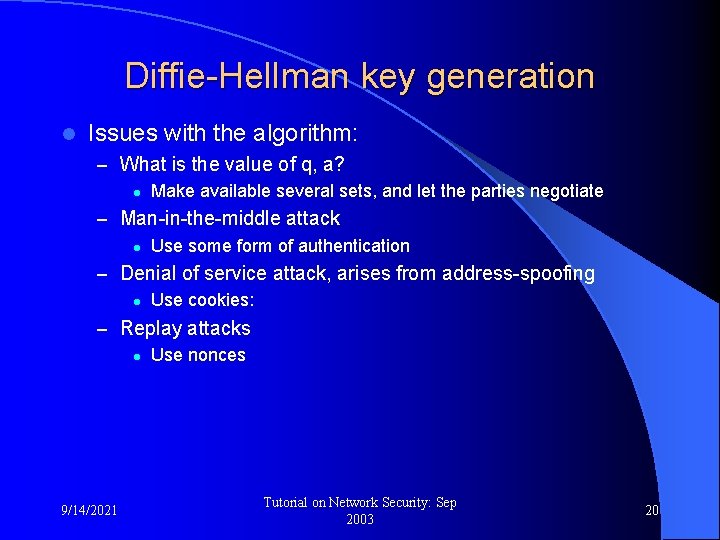
Diffie-Hellman key generation l Issues with the algorithm: – What is the value of q, a? l Make available several sets, and let the parties negotiate – Man-in-the-middle attack l Use some form of authentication – Denial of service attack, arises from address-spoofing l Use cookies: – Replay attacks l Use nonces 9/14/2021 Tutorial on Network Security: Sep 2003 20
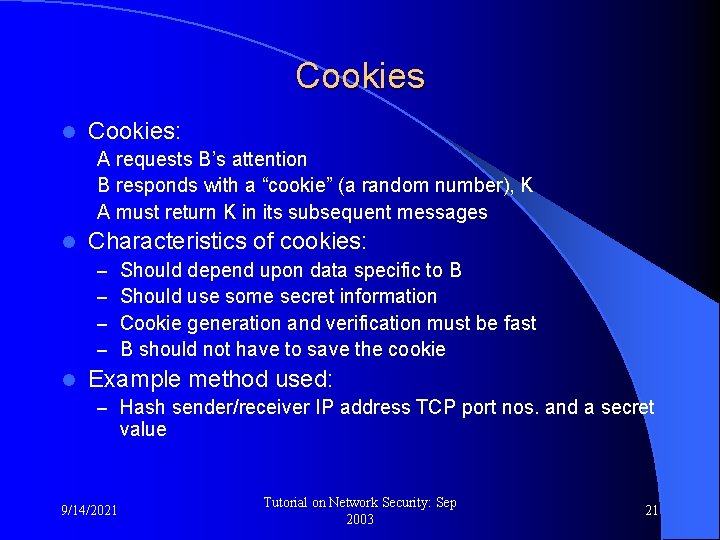
Cookies l Cookies: A requests B’s attention B responds with a “cookie” (a random number), K A must return K in its subsequent messages l Characteristics of cookies: – – l Should depend upon data specific to B Should use some secret information Cookie generation and verification must be fast B should not have to save the cookie Example method used: – Hash sender/receiver IP address TCP port nos. and a secret value 9/14/2021 Tutorial on Network Security: Sep 2003 21
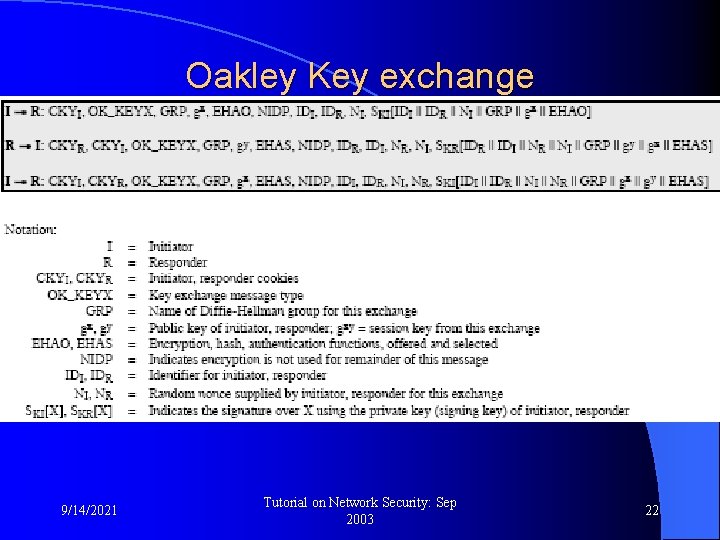
Oakley Key exchange 9/14/2021 Tutorial on Network Security: Sep 2003 22
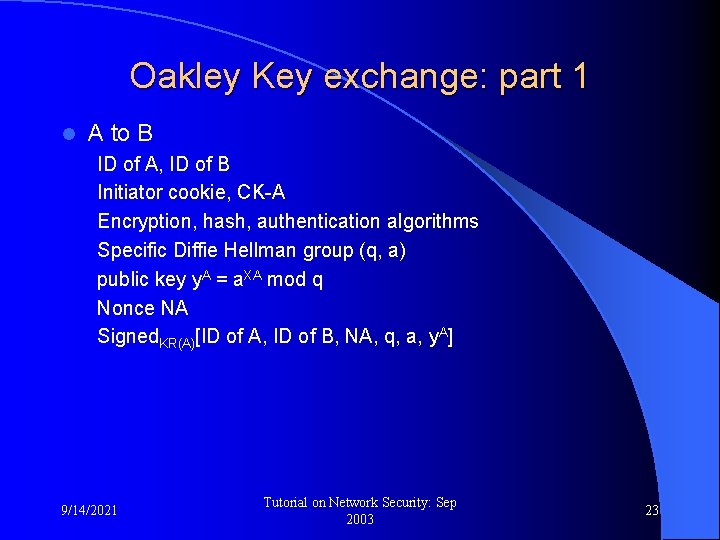
Oakley Key exchange: part 1 l A to B ID of A, ID of B Initiator cookie, CK-A Encryption, hash, authentication algorithms Specific Diffie Hellman group (q, a) public key y. A = a. XA mod q Nonce NA Signed. KR(A)[ID of A, ID of B, NA, q, a, y. A] 9/14/2021 Tutorial on Network Security: Sep 2003 23
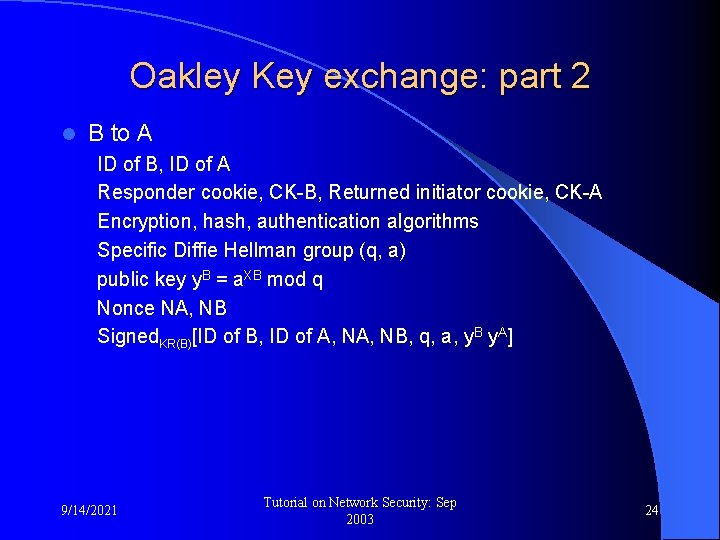
Oakley Key exchange: part 2 l B to A ID of B, ID of A Responder cookie, CK-B, Returned initiator cookie, CK-A Encryption, hash, authentication algorithms Specific Diffie Hellman group (q, a) public key y. B = a. XB mod q Nonce NA, NB Signed. KR(B)[ID of B, ID of A, NB, q, a, y. B y. A] 9/14/2021 Tutorial on Network Security: Sep 2003 24
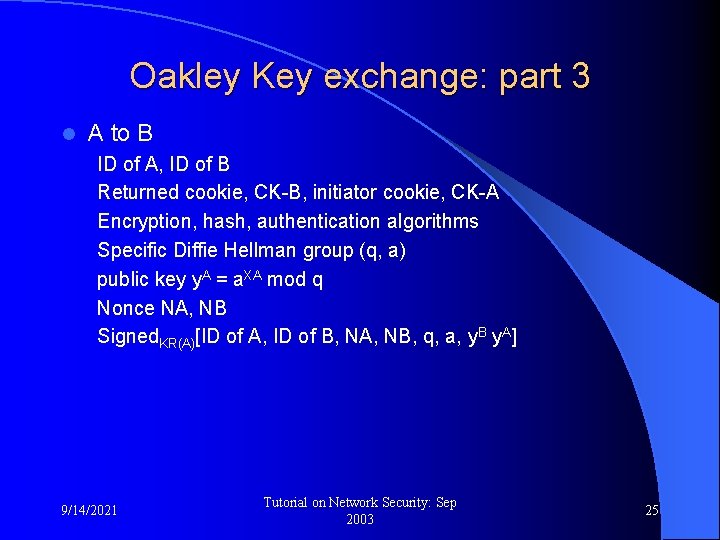
Oakley Key exchange: part 3 l A to B ID of A, ID of B Returned cookie, CK-B, initiator cookie, CK-A Encryption, hash, authentication algorithms Specific Diffie Hellman group (q, a) public key y. A = a. XA mod q Nonce NA, NB Signed. KR(A)[ID of A, ID of B, NA, NB, q, a, y. B y. A] 9/14/2021 Tutorial on Network Security: Sep 2003 25
Thanks 9/14/2021 Tutorial on Network Security: Sep 2003 26
- Slides: 26