Verifiable Functional Encryption Saikrishna Badrinarayanan UCLA Joint work
Verifiable Functional Encryption Saikrishna Badrinarayanan UCLA, Joint work with Vipul Goyal, Aayush Jain and Amit Sahai
Classical Encryption “All or nothing”
![Functional Encryption (FE) [SW’ 05] f(x) MSK f f x x SKf should not Functional Encryption (FE) [SW’ 05] f(x) MSK f f x x SKf should not](http://slidetodoc.com/presentation_image_h/2e05b9d62645adcd219d3cb86d8df57a/image-3.jpg)
Functional Encryption (FE) [SW’ 05] f(x) MSK f f x x SKf should not allow adversary to compute Fine Grained Access to Private Data anything other than f(x) !
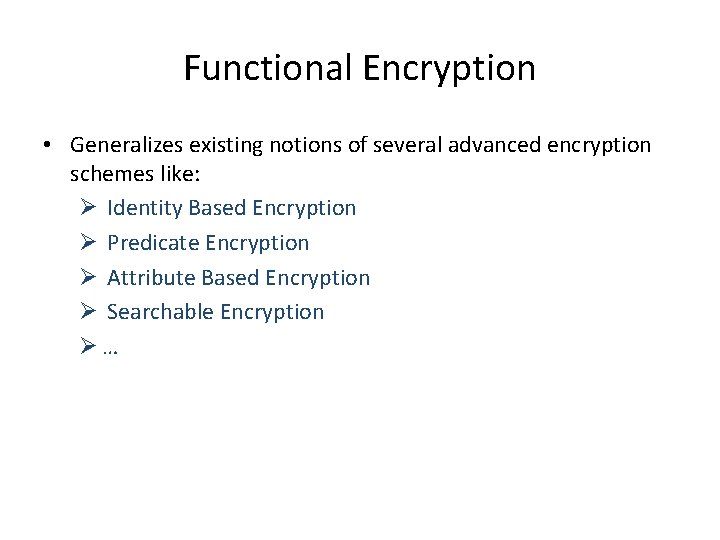
Functional Encryption • Generalizes existing notions of several advanced encryption schemes like: Ø Identity Based Encryption Ø Predicate Encryption Ø Attribute Based Encryption Ø Searchable Encryption Ø…
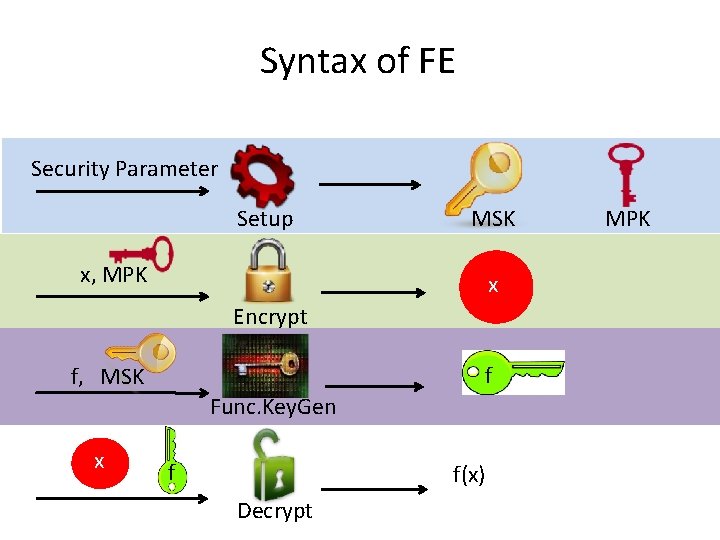
Syntax of FE Security Parameter Setup MSK x, MPK x Encrypt f f, MSK Func. Key. Gen x x, n f f(x) Decrypt MPK
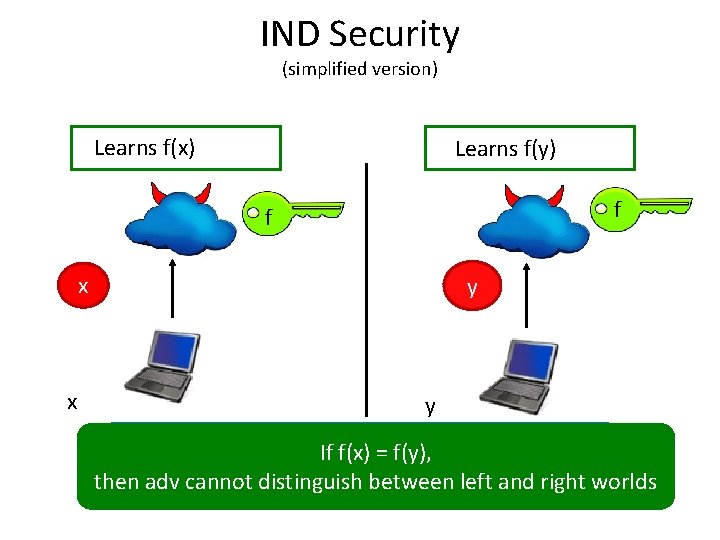
IND Security (simplified version) Learns f(x) Learns f(y) f f x x y y Adv cannot distinguish between the If f(x) = f(y), left and right worlds then adv cannot distinguish between left and right worlds
![Example: Audits [GPSW’ 06] f(x) f MSK f Auditor should not learn anything other Example: Audits [GPSW’ 06] f(x) f MSK f Auditor should not learn anything other](http://slidetodoc.com/presentation_image_h/2e05b9d62645adcd219d3cb86d8df57a/image-7.jpg)
Example: Audits [GPSW’ 06] f(x) f MSK f Auditor should not learn anything other than f(x). x x
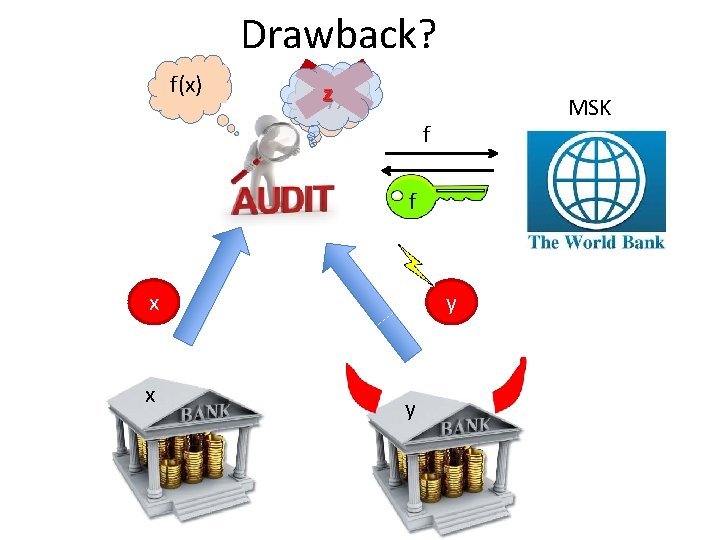
Drawback? f(x) Z f(y) MSK f f x x y y
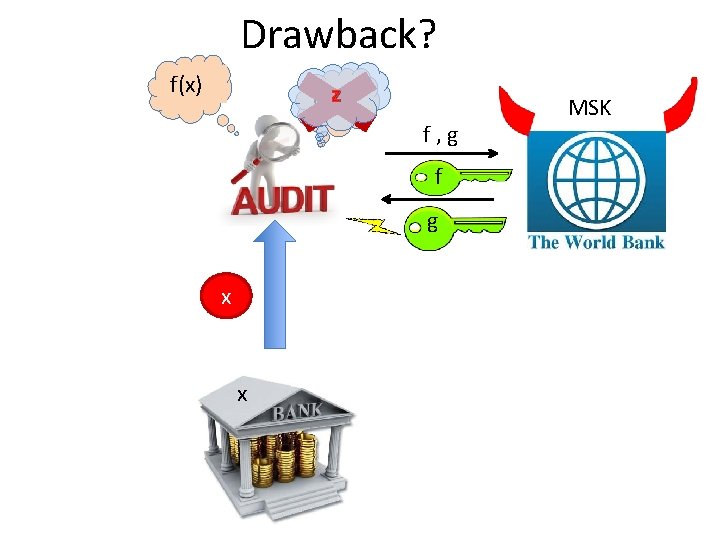
Drawback? f(x) Z g(x) f , g f g x x MSK
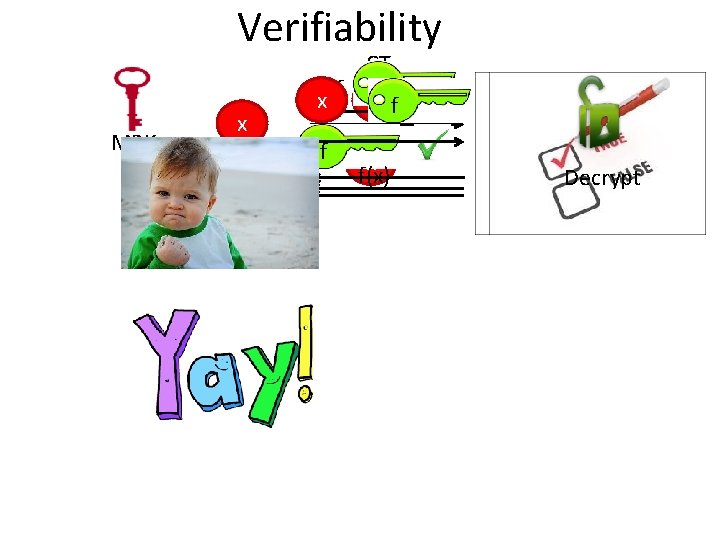
Verifiability MPK x f f CT f x f(x) Decrypt
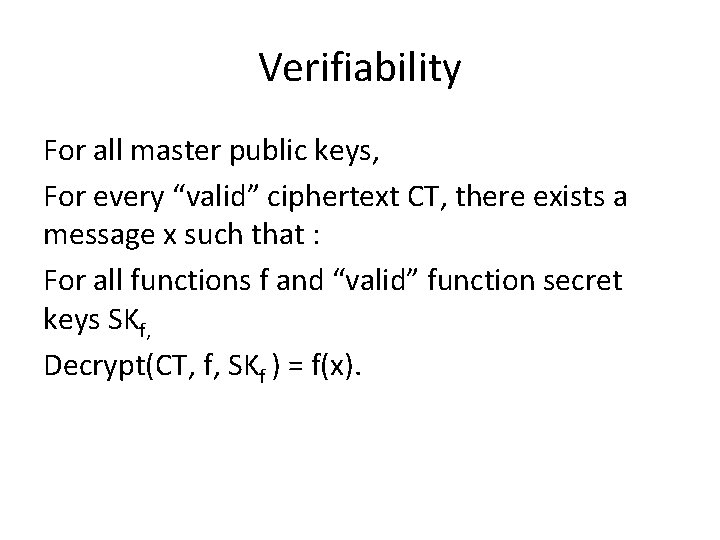
Verifiability For all master public keys, For every “valid” ciphertext CT, there exists a message x such that : For all functions f and “valid” function secret keys SKf, Decrypt(CT, f, SKf ) = f(x).
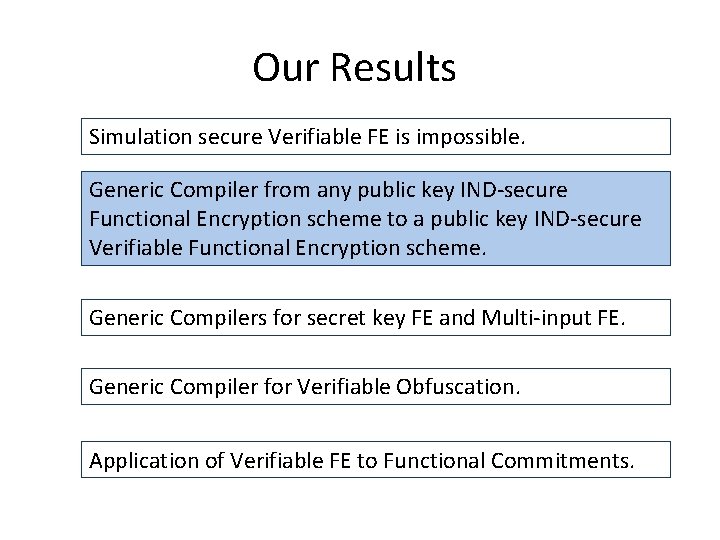
Our Results Simulation secure Verifiable FE is impossible. Generic Compiler from any public key IND-secure Functional Encryption scheme to a public key IND-secure Verifiable Functional Encryption scheme. Generic Compilers for secret key FE and Multi-input FE. Generic Compiler for Verifiable Obfuscation. Application of Verifiable FE to Functional Commitments.
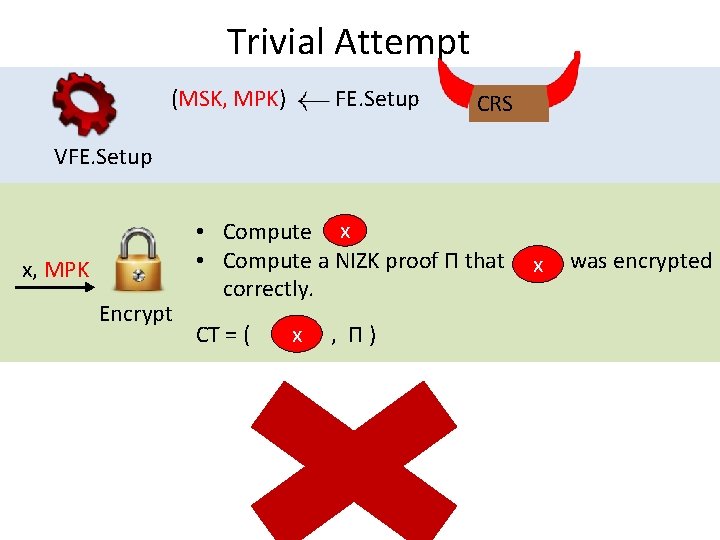
Trivial Attempt (MSK, MPK) FE. Setup CRS VFE. Setup x, MPK Encrypt • Compute x • Compute a NIZK proof Π that was encrypted x correctly. x CT = ( , Π )
![Non-Interactive Witness Indistinguishable Proofs (NIWI) [GOS’ 06, GS’ 08] Prover Pick b randomly Statement Non-Interactive Witness Indistinguishable Proofs (NIWI) [GOS’ 06, GS’ 08] Prover Pick b randomly Statement](http://slidetodoc.com/presentation_image_h/2e05b9d62645adcd219d3cb86d8df57a/image-15.jpg)
Non-Interactive Witness Indistinguishable Proofs (NIWI) [GOS’ 06, GS’ 08] Prover Pick b randomly Statement x (x, w 0 , w 1) Verifier Can’t guess b Π = Prove( x , wb ) In NIZK, verifier learns nothing at all about the witness, whereas in NIWI, verifier doesn’t learn which witness was used to construct the proof.
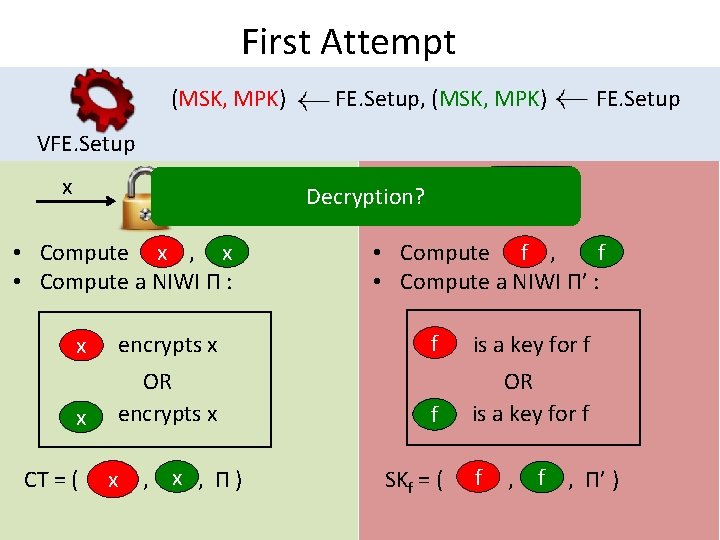
First Attempt (MSK, MPK) FE. Setup, (MSK, MPK) FE. Setup VFE. Setup x f Decryption? x x • Compute , • Compute a NIWI Π : x encrypts x x OR encrypts x f f • Compute , • Compute a NIWI Π’ : x x CT = ( , Π ) f is a key for f f OR is a key for f f f SKf = ( , , Π’ )
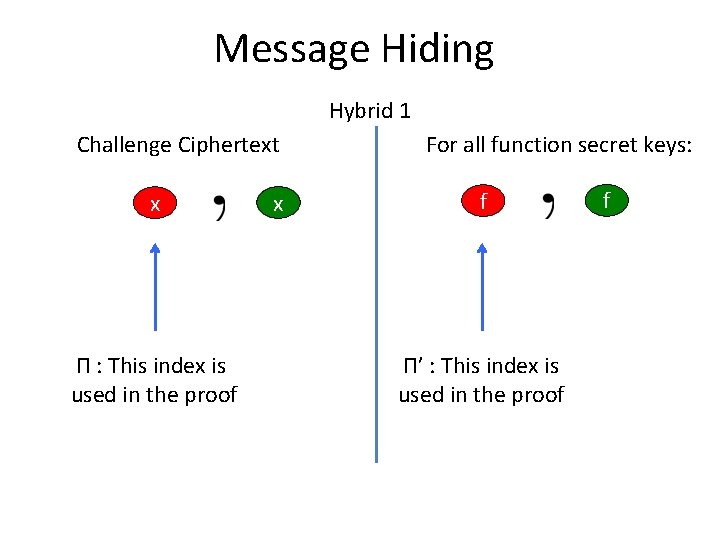
Message Hiding Hybrid 1 Challenge Ciphertext x Π : This index is used in the proof x For all function secret keys: f Π’ : This index is used in the proof f
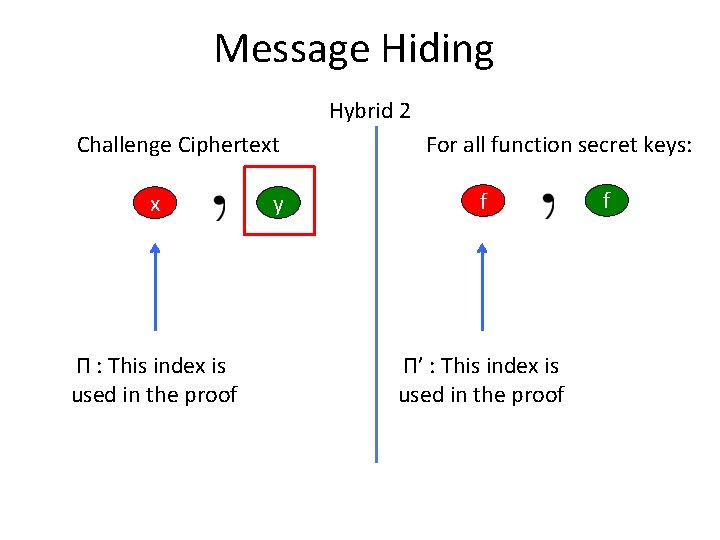
Message Hiding Hybrid 2 Challenge Ciphertext x Π : This index is used in the proof y For all function secret keys: f Π’ : This index is used in the proof f
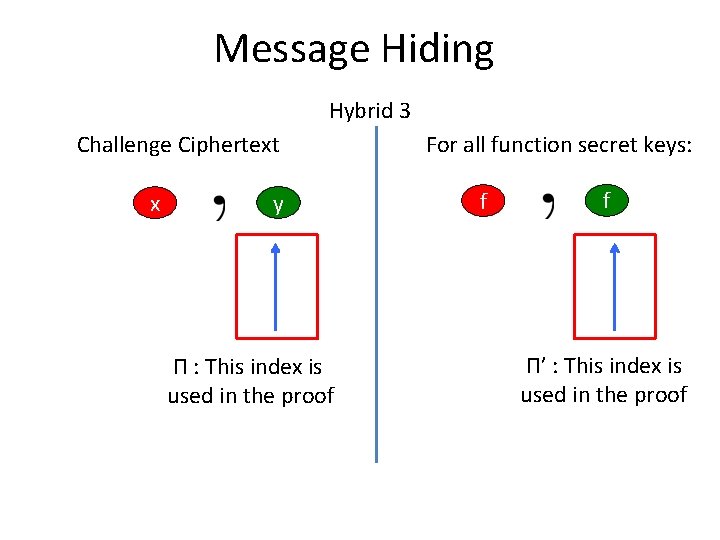
Message Hiding Hybrid 3 Challenge Ciphertext x y Π : This index is used in the proof For all function secret keys: f f Π’ : This index is used in the proof
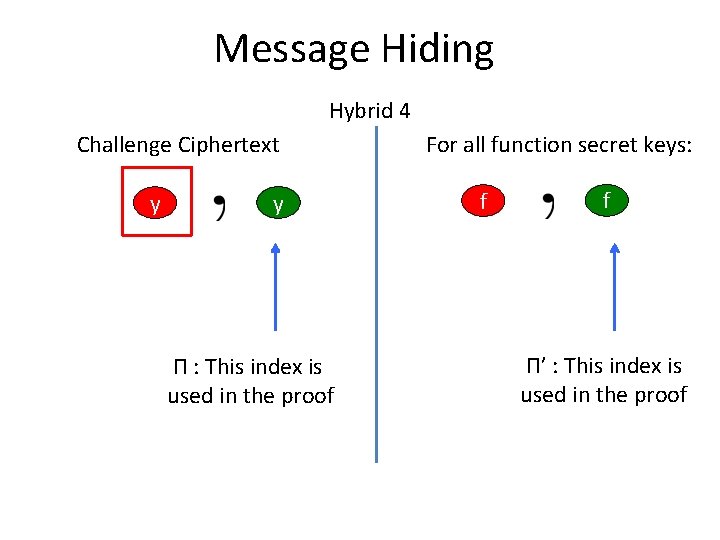
Message Hiding Hybrid 4 Challenge Ciphertext y y Π : This index is used in the proof For all function secret keys: f f Π’ : This index is used in the proof
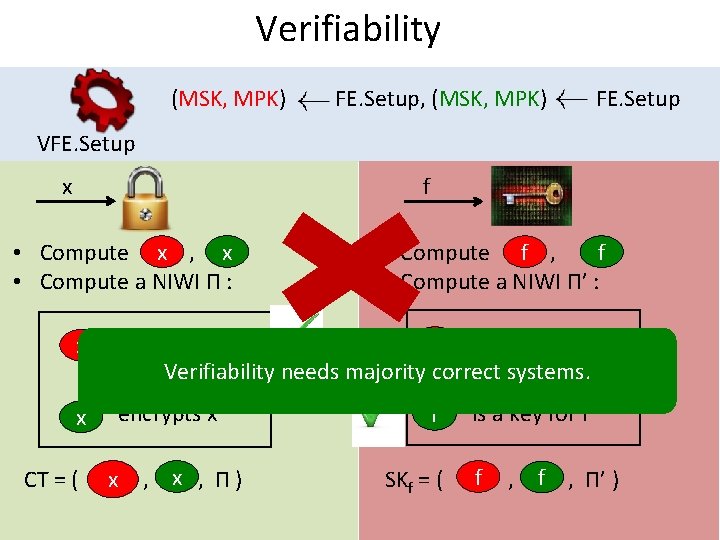
Verifiability (MSK, MPK) FE. Setup, (MSK, MPK) FE. Setup VFE. Setup x f x x • Compute , • Compute a NIWI Π : x x f f • Compute , • Compute a NIWI Π’ : f is a key for f encrypts x ORVerifiability needs majority correct systems. OR encrypts x f is a key for f x x CT = ( , Π ) f f SKf = ( , , Π’ )
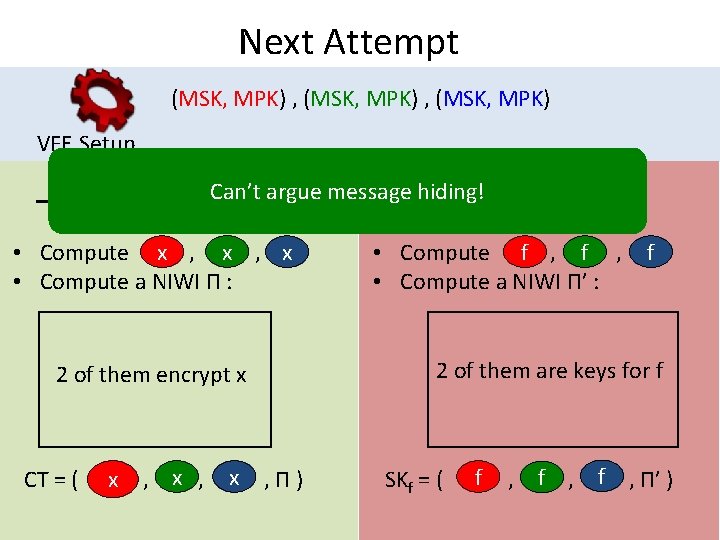
Next Attempt (MSK, MPK) , (MSK, MPK) VFE. Setup x f Can’t argue message hiding! x x x • Compute , , • Compute a NIWI Π : 2 of them encrypt x f f • Compute , , • Compute a NIWI Π’ : f 2 of them are keys for f x x x CT = ( , , Π ) f f f SKf = ( , , , Π’ )
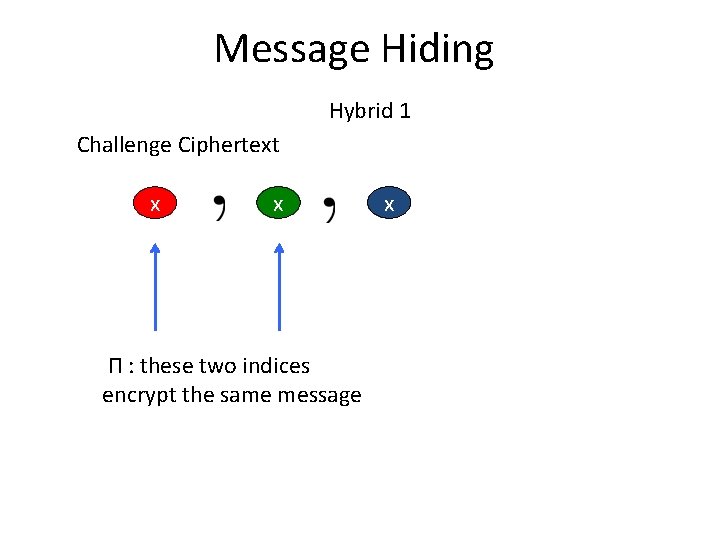
Message Hiding Hybrid 1 Challenge Ciphertext x x Π : these two indices encrypt the same message x
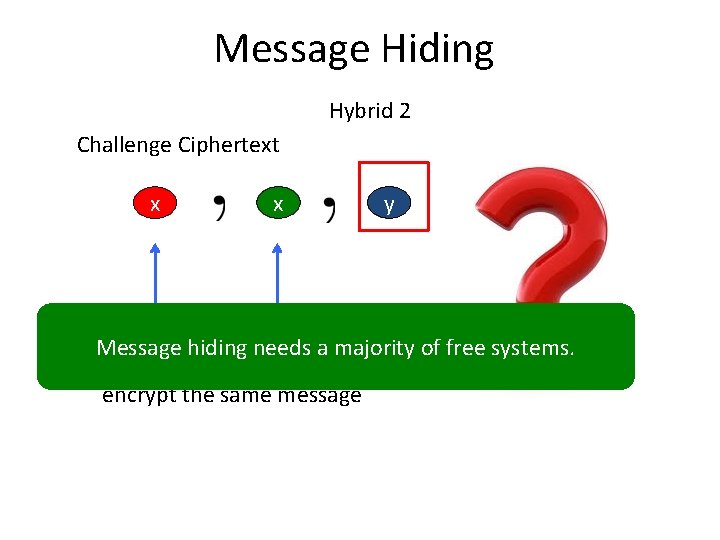
Message Hiding Hybrid 2 Challenge Ciphertext x x y Message hiding needs a majority of free systems. Π : these two indices encrypt the same message
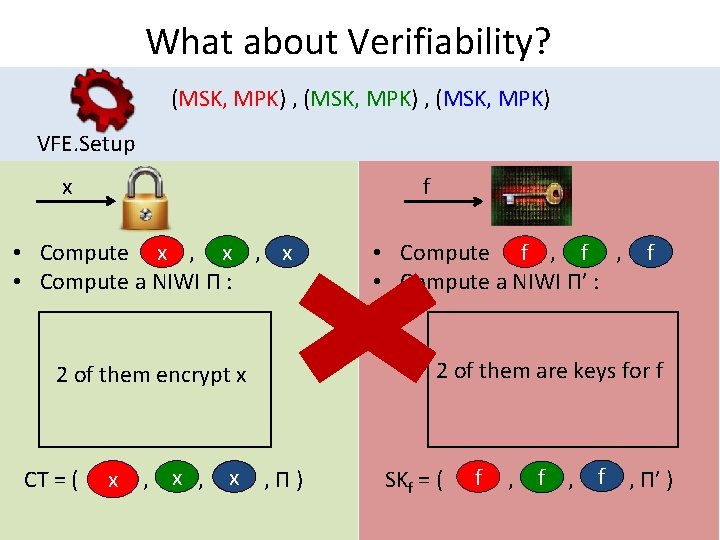
What about Verifiability? (MSK, MPK) , (MSK, MPK) VFE. Setup x f x x x • Compute , , • Compute a NIWI Π : 2 of them encrypt x f f • Compute , , • Compute a NIWI Π’ : f 2 of them are keys for f x x x CT = ( , , Π ) f f f SKf = ( , , , Π’ )
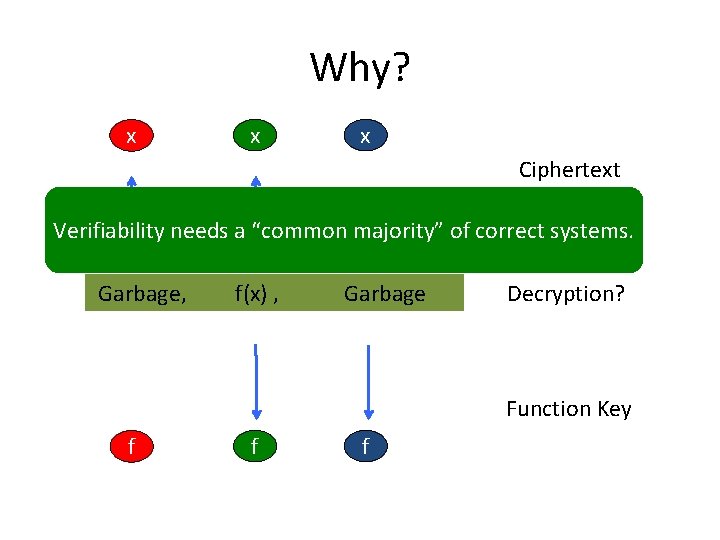
Why? x x x Ciphertext Verifiability needs a “common majority” of correct systems. Garbage, f(x) , Garbage Decryption? Function Key f f f
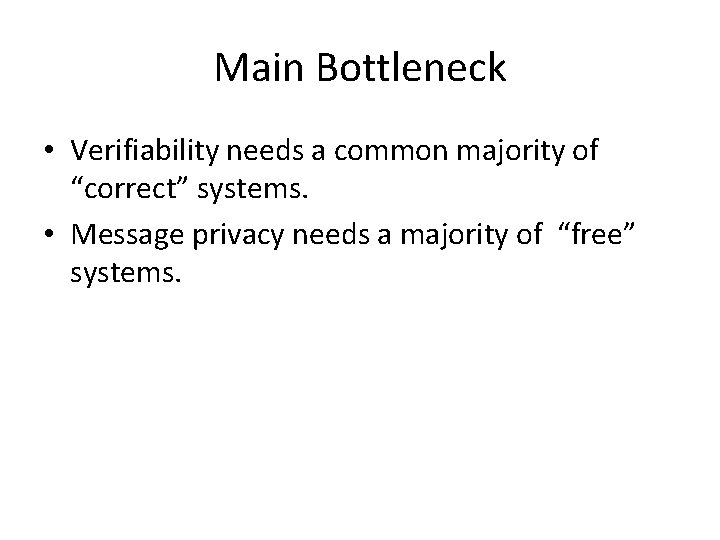
Main Bottleneck • Verifiability needs a common majority of “correct” systems. • Message privacy needs a majority of “free” systems.
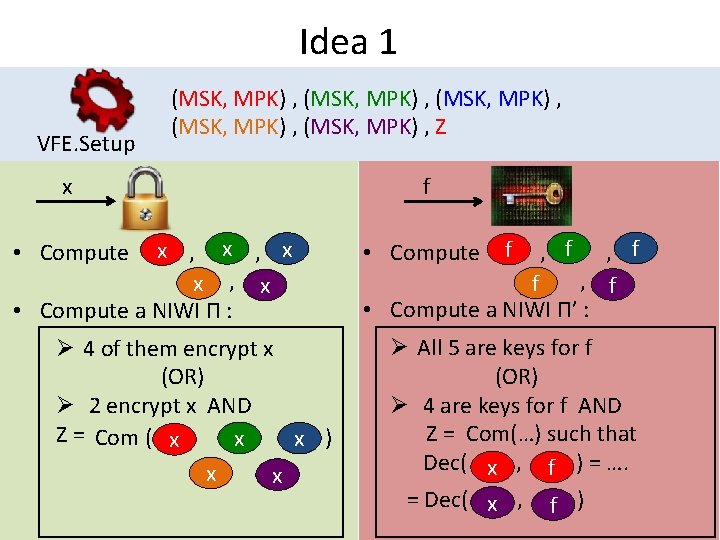
Idea 1 VFE. Setup (MSK, MPK) , (MSK, MPK) , Z x f f f x x x • Compute f , , • Compute , , , , f x • Compute a NIWI Π’ : • Compute a NIWI Π : Ø 4 of them encrypt x (OR) Ø 2 encrypt x AND Z = Com ( ) x x x Ø All 5 are keys for f (OR) Ø 4 are keys for f AND Z = Com(…) such that Dec( , ) = …. x f = Dec( , ) x f
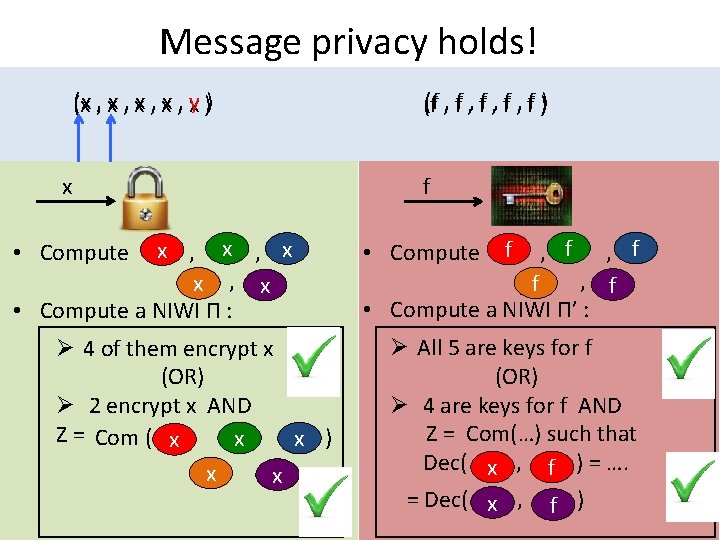
Message privacy holds! (x , x , y ) (f , f , f ) (x , x , x ) (f , f , f ) x f f f x x x • Compute f , , • Compute , , , , f x • Compute a NIWI Π’ : • Compute a NIWI Π : Ø 4 of them encrypt x (OR) Ø 2 encrypt x AND Z = Com ( ) x x x Ø All 5 are keys for f (OR) Ø 4 are keys for f AND Z = Com(…) such that Dec( , ) = …. x f = Dec( , ) x f
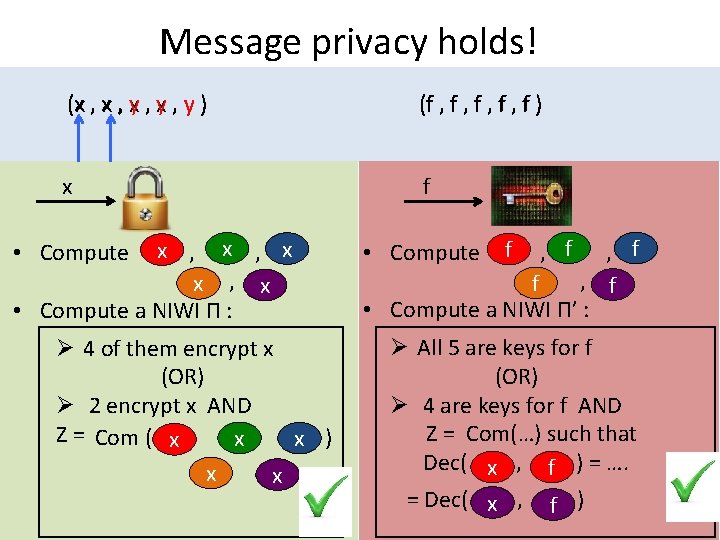
Message privacy holds! (x , y , y ) (f , f , f ) (x , x , y ) (f , f , f ) x f f f x x x • Compute f , , • Compute , , , , f x • Compute a NIWI Π’ : • Compute a NIWI Π : Ø 4 of them encrypt x (OR) Ø 2 encrypt x AND Z = Com ( ) x x x Ø All 5 are keys for f (OR) Ø 4 are keys for f AND Z = Com(…) such that Dec( , ) = …. x f = Dec( , ) x f
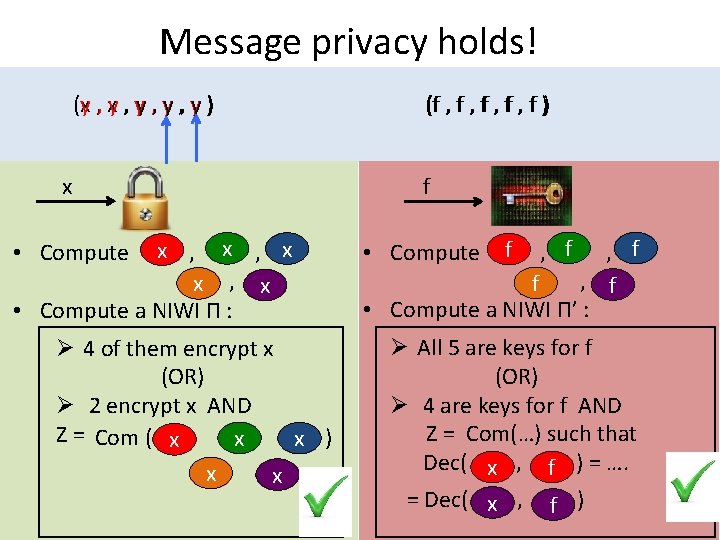
Message privacy holds! (x , y , y ) (f , f , f ) (y , y , y ) (f , f , f ) x f f f x x x • Compute f , , • Compute , , , , f x • Compute a NIWI Π’ : • Compute a NIWI Π : Ø 4 of them encrypt x (OR) Ø 2 encrypt x AND Z = Com ( ) x x x Ø All 5 are keys for f (OR) Ø 4 are keys for f AND Z = Com(…) such that Dec( , ) = …. x f = Dec( , ) x f
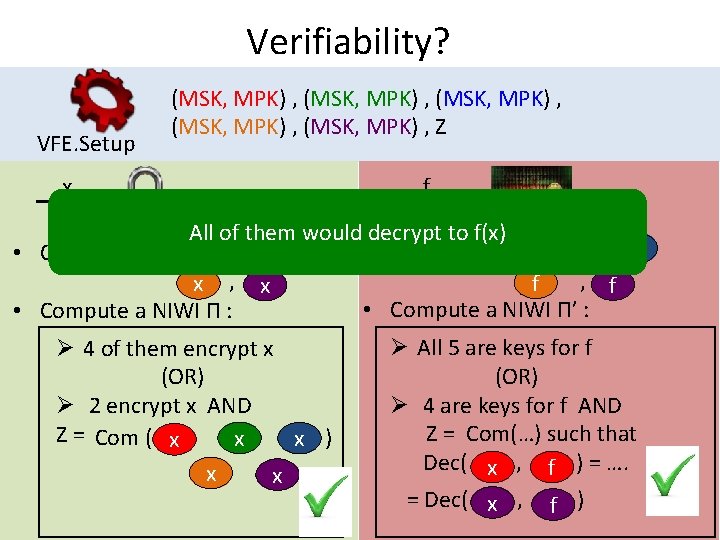
Verifiability? VFE. Setup (MSK, MPK) , (MSK, MPK) , Z x f All of them would decrypt to f(x) f f x x x • Compute f , , • Compute , , , , f x • Compute a NIWI Π’ : • Compute a NIWI Π : Ø 4 of them encrypt x (OR) Ø 2 encrypt x AND Z = Com ( ) x x x Ø All 5 are keys for f (OR) Ø 4 are keys for f AND Z = Com(…) such that Dec( , ) = …. x f = Dec( , ) x f
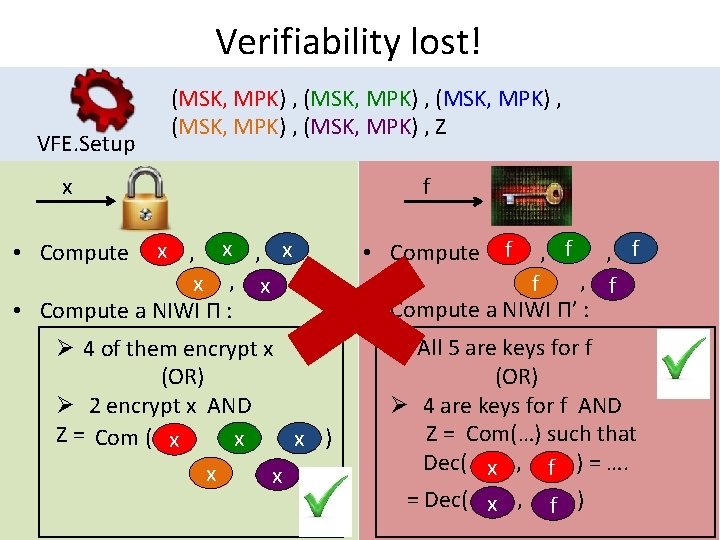
Verifiability lost! VFE. Setup (MSK, MPK) , (MSK, MPK) , Z x f f f x x x • Compute f , , • Compute , , , , f x • Compute a NIWI Π’ : • Compute a NIWI Π : Ø 4 of them encrypt x (OR) Ø 2 encrypt x AND Z = Com ( ) x x x Ø All 5 are keys for f (OR) Ø 4 are keys for f AND Z = Com(…) such that Dec( , ) = …. x f = Dec( , ) x f
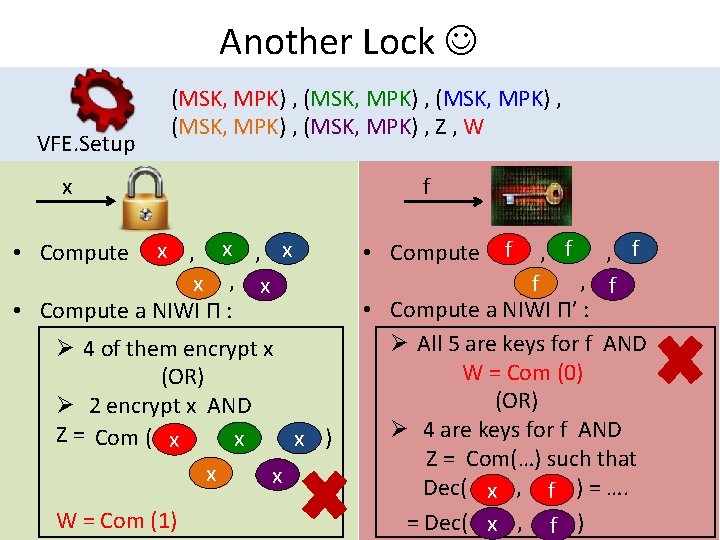
Another Lock VFE. Setup x (MSK, MPK) , (MSK, MPK) , Z , W f f f x x x • Compute f , , • Compute , , , , f x • Compute a NIWI Π’ : • Compute a NIWI Π : Ø All 5 are keys for f AND Ø 4 of them encrypt x W = Com (0) (OR) Ø 2 encrypt x AND Ø 4 are keys for f AND Z = Com ( ) x x x Z = Com(…) such that x x Dec( , ) = …. x f W = Com (1) = Dec( , ) x f
Thank you! Questions?
- Slides: 35