Functional Encryption Origins and Recent Developments Brent Waters
Functional Encryption: Origins and Recent Developments Brent Waters
Part I: Origins of Functional Encryption Part II: ABE for Circuits
Nine years ago in 2004 Me Excited younger researcher Bilinear Maps in Cryptography Powerful and exciting Identity-Based Encryption: Lots of movement Boneh-Franklin 01, Cannetti-Halevi-Katz 03, Boneh-Boyen 04 3
![Identity-Based Encryption Public Parameters [S 84, BF 01] MSK Theme: Collusion resistance central! Authority Identity-Based Encryption Public Parameters [S 84, BF 01] MSK Theme: Collusion resistance central! Authority](http://slidetodoc.com/presentation_image_h/747e2171652ba5c2bbf548e5f256ba26/image-4.jpg)
Identity-Based Encryption Public Parameters [S 84, BF 01] MSK Theme: Collusion resistance central! Authority Functionality: Decrypt if strings match CT: “sarah@gmail. com” Key: “sarah@gmail. com” SK 4
What if we had biometric identities? (1) Biometrics are noisy (2) Standard IBE will not work (3) Want threshold k-of-n IBE 5
![Fuzzy Identity-Based Encryption Public Parameters [SW 05] MSK Mentioned more general concept of Attribute-Based Fuzzy Identity-Based Encryption Public Parameters [SW 05] MSK Mentioned more general concept of Attribute-Based](http://slidetodoc.com/presentation_image_h/747e2171652ba5c2bbf548e5f256ba26/image-6.jpg)
Fuzzy Identity-Based Encryption Public Parameters [SW 05] MSK Mentioned more general concept of Attribute-Based Encryption Authority Functionality: Decrypt if k of n features match CT: Key: SK 6
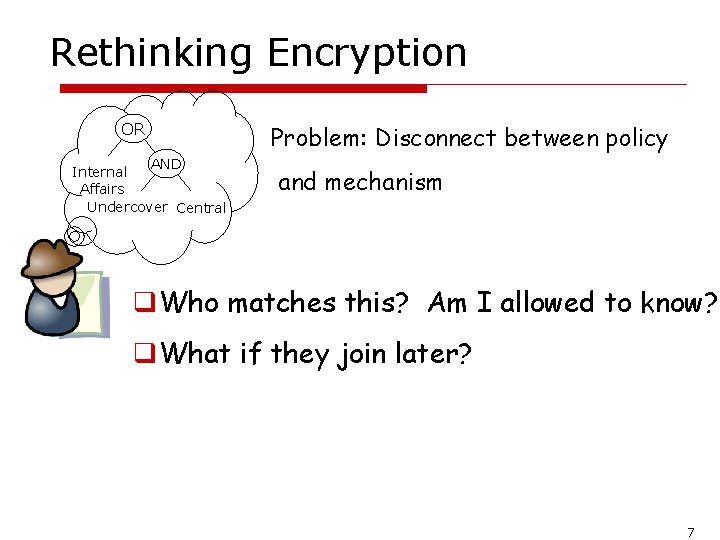
Rethinking Encryption OR AND Internal Affairs Undercover Central Problem: Disconnect between policy and mechanism q. Who matches this? Am I allowed to know? q. What if they join later? 7
![Attribute-Based Encryption Public Parameters [SW 05, GPSW 06, …] MSK Authority Functionality: output message Attribute-Based Encryption Public Parameters [SW 05, GPSW 06, …] MSK Authority Functionality: output message](http://slidetodoc.com/presentation_image_h/747e2171652ba5c2bbf548e5f256ba26/image-8.jpg)
Attribute-Based Encryption Public Parameters [SW 05, GPSW 06, …] MSK Authority Functionality: output message if Á(x) = true x is not hidden CT: x Key: Á SK 8
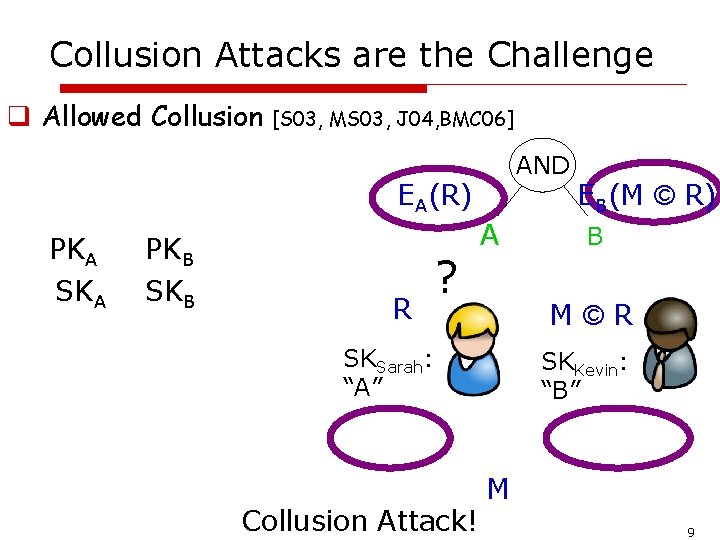
Collusion Attacks are the Challenge q Allowed Collusion [S 03, MS 03, J 04, BMC 06] AND EA(R) PKA SKA PKB SKB R ? A B M©R SKSarah: “A” Collusion Attack! EB(M © R) SKKevin: “B” M 9
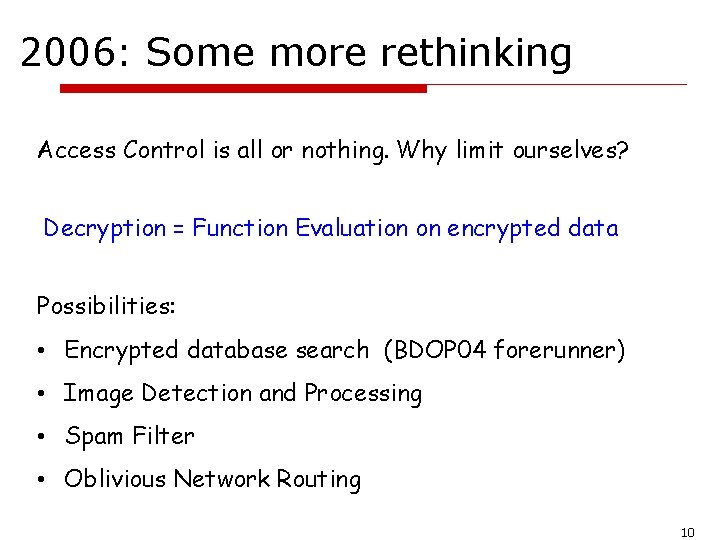
2006: Some more rethinking Access Control is all or nothing. Why limit ourselves? Decryption = Function Evaluation on encrypted data Possibilities: • Encrypted database search (BDOP 04 forerunner) • Image Detection and Processing • Spam Filter • Oblivious Network Routing 10
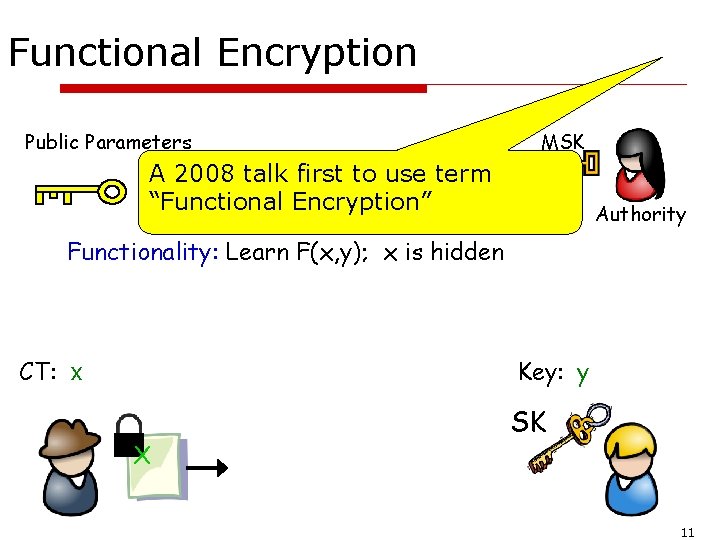
Functional Encryption Public Parameters MSK A 2008 talk first to use term “Functional Encryption” Authority Functionality: Learn F(x, y); x is hidden CT: x Key: y X SK 11
![Activity in Functional Encryption • Adaptive Security [LOSTW 10, OT 10, LW 12] • Activity in Functional Encryption • Adaptive Security [LOSTW 10, OT 10, LW 12] •](http://slidetodoc.com/presentation_image_h/747e2171652ba5c2bbf548e5f256ba26/image-12.jpg)
Activity in Functional Encryption • Adaptive Security [LOSTW 10, OT 10, LW 12] • Multi-Authority [C 07, CC 09, LW 11] • Lattice Realizations [GPV 08, CHKP 10, ABB 10, AFV 11, ABVVW 12, Boy 13] • Collusion Bounded FE [SS 10, GVW 12, GKPVZ 13] • Definitions [BSW 11, GVW 12, BO 12] • Other: Universe Size, Faster Decryption, Outsourcing, … What about core functionality? 12
Recent State of Art in Functionality Collusion Resistant Schemes Access Control/ABE: Boolean Formulas/Monotone Span Programs [GPSW 06, BSW 07] General FE: Dot product of KSW 08 Why? Limitation seems to be bilinear map. 13
Part II: ABE for Circuits
The rest of the talk (1) ABE for boolean formulas (2) Backtracking Attacks: Why circuits are hard (3) Circuit ABE from Multilinear Maps (4) Open Directions 15
Bilinear maps High Level: single multiplication Key for collusion resistance 16
ABE formulas sketch Show four algorithms “Key-Policy”, “Small Universe”, “Monotonic Formulas” 17
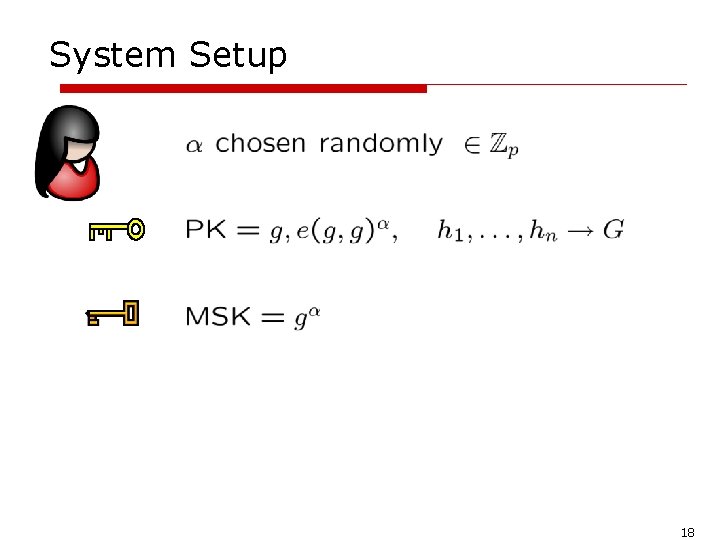
System Setup 18
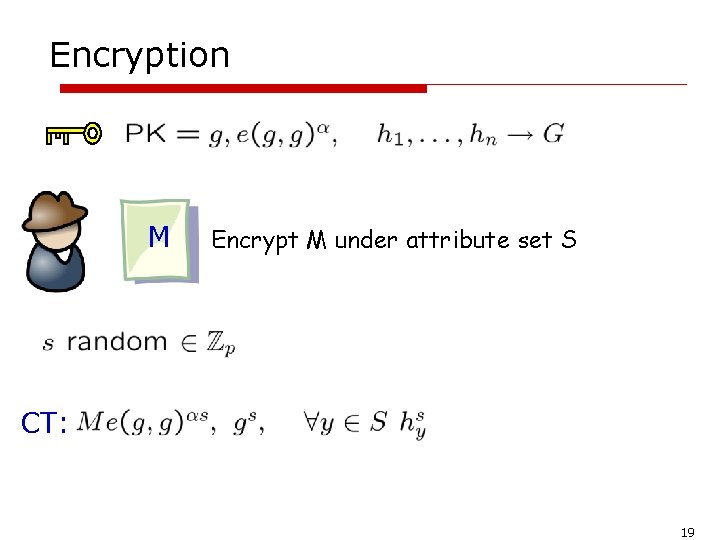
Encryption M Encrypt M under attribute set S CT: 19
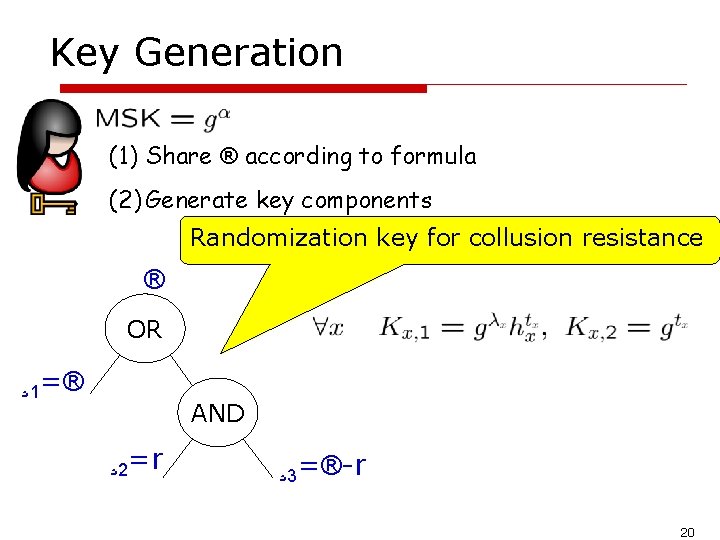
Key Generation (1) Share ® according to formula (2) Generate key components Randomization key for collusion resistance ® OR ¸ 1=® AND ¸ 2=r ¸ 3=®-r 20
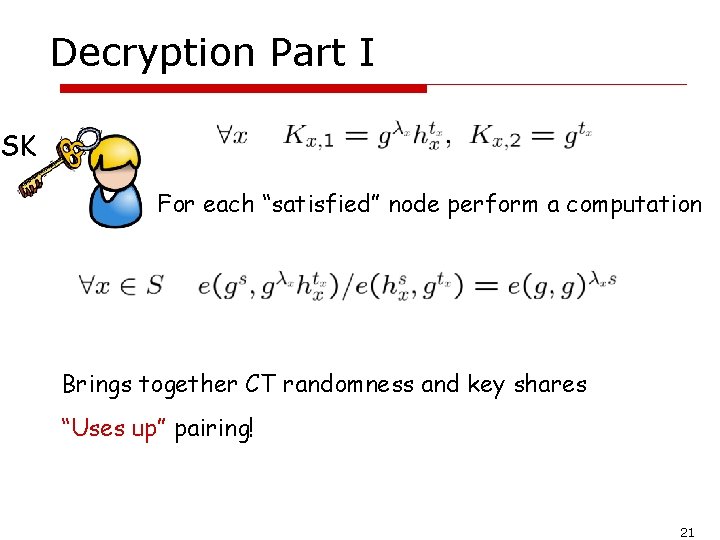
Decryption Part I SK For each “satisfied” node perform a computation Brings together CT randomness and key shares “Uses up” pairing! 21
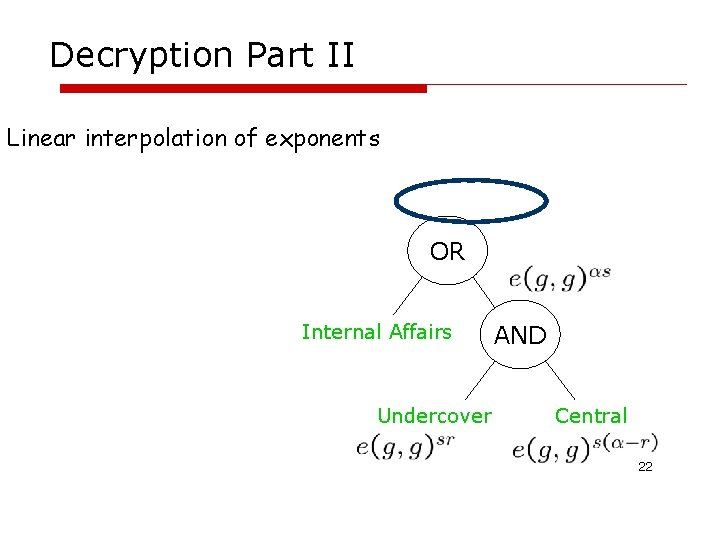
Decryption Part II Linear interpolation of exponents OR Internal Affairs Undercover AND Central 22
Circuits (1) TM computation of fixed time efficiently (2) Formulas: Circuits limited to fanout of 1 (3) Circuit to formula gives exponential blowup 23
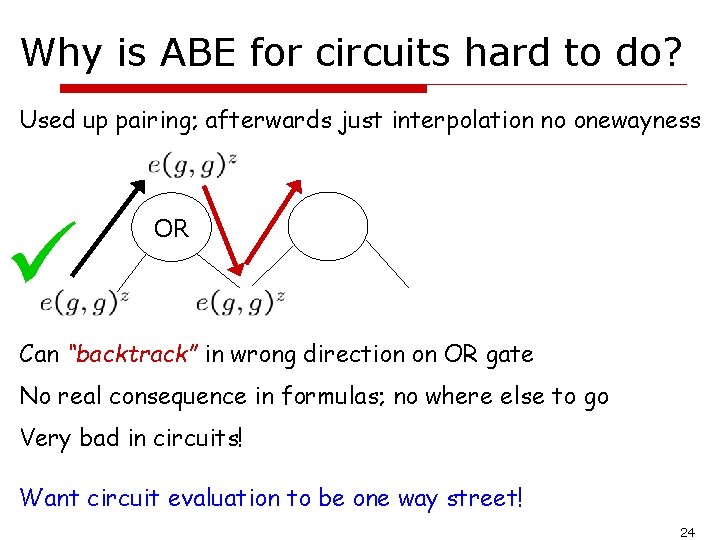
Why is ABE for circuits hard to do? Used up pairing; afterwards just interpolation no onewayness OR Can “backtrack” in wrong direction on OR gate No real consequence in formulas; no where else to go Very bad in circuits! Want circuit evaluation to be one way street! 24
![Leveled Multilinear maps [GGH 13] Actually graded encodings 25 Leveled Multilinear maps [GGH 13] Actually graded encodings 25](http://slidetodoc.com/presentation_image_h/747e2171652ba5c2bbf548e5f256ba26/image-25.jpg)
Leveled Multilinear maps [GGH 13] Actually graded encodings 25
![ABE for Circuits [SW 12] Idea: Use pairing to evaluate through circuit; no backtracking ABE for Circuits [SW 12] Idea: Use pairing to evaluate through circuit; no backtracking](http://slidetodoc.com/presentation_image_h/747e2171652ba5c2bbf548e5f256ba26/image-26.jpg)
ABE for Circuits [SW 12] Idea: Use pairing to evaluate through circuit; no backtracking Decrypt: Circuit wire at level i, use group at level i+1 Technique: “Move forward & shift” replaces interpolation Note: Montonic circuits => General circuits 26
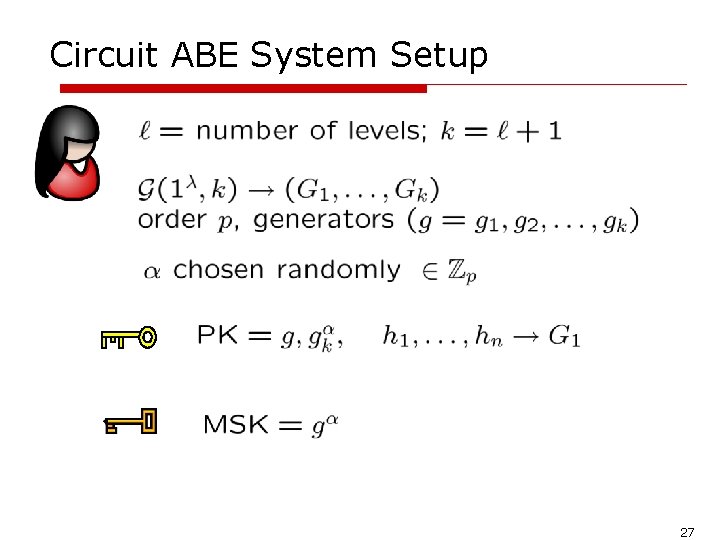
Circuit ABE System Setup 27
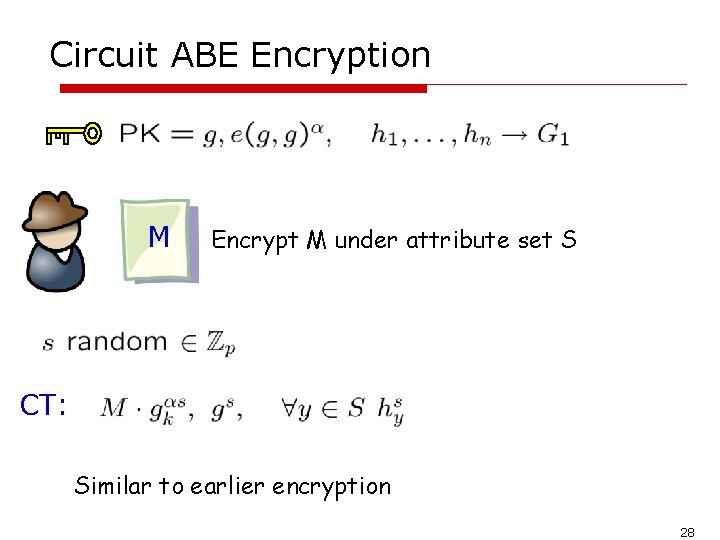
Circuit ABE Encryption M Encrypt M under attribute set S CT: Similar to earlier encryption 28
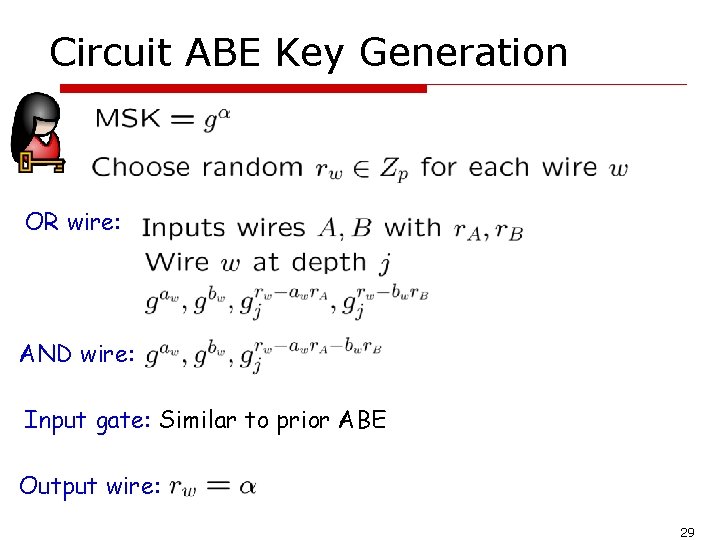
Circuit ABE Key Generation OR wire: AND wire: Input gate: Similar to prior ABE Output wire: 29
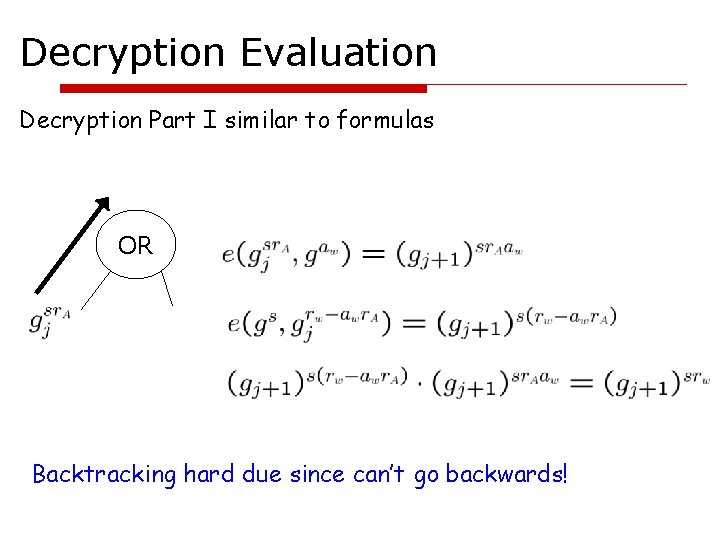
Decryption Evaluation Decryption Part I similar to formulas OR Backtracking hard due since can’t go backwards!
Summarizing the results ABE for any circuit Circuit depth fixed on setup; ciphertexts grow with maximum depth Proof: Decision k-multilinear assumption (d-BDH analog) Exciting concurrent work: GVW 13 Circuit ABE from LWE 31
Big Problem: Functional Encryption Key: y CT: x X SK Functionality: Learn F(x, y); x is hidden Some negative results [BSW 11, GVW 12] for simulation def. Indistinguishability & other simulation defs. very open; need to be better understood 32
Thank you 33
- Slides: 33