AttributeBased Encryption Brent Waters SRI International Joint work
Attribute-Based Encryption Brent Waters SRI International Joint work with Vipul Goyal, Omkant Pandey, and Amit Sahai http: //www. csl. sri. com/users/bwaters/ 1
![IBE [BF 01] IBE: [BF 01] Public key encryption scheme where public key is IBE [BF 01] IBE: [BF 01] Public key encryption scheme where public key is](http://slidetodoc.com/presentation_image/30d1ebada54647952dc5377f96148dab/image-2.jpg)
IBE [BF 01] IBE: [BF 01] Public key encryption scheme where public key is an arbitrary string (ID). - Examples: user’s e-mail address Is regular PKI good enough? “bo b@ I am stan ford email encrypted using public key: . ed “bob@stanford. edu” Pr iv Alice does not access a PKI at e u” ke y CA/PKG Authority is offline master-key 2
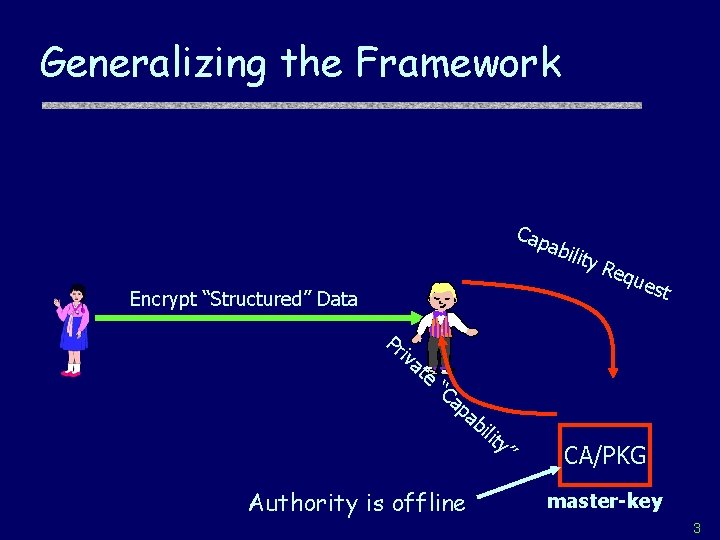
Generalizing the Framework Cap abil Encrypt “Structured” Data Pr iv at e “C ity Req ues t ap ab ilit y” Authority is offline CA/PKG master-key 3
![Attributed-Based Encryption(ABE) [SW 05] Ø Encrypt Data with descriptive “Attributes” Ø Users Private Keys Attributed-Based Encryption(ABE) [SW 05] Ø Encrypt Data with descriptive “Attributes” Ø Users Private Keys](http://slidetodoc.com/presentation_image/30d1ebada54647952dc5377f96148dab/image-4.jpg)
Attributed-Based Encryption(ABE) [SW 05] Ø Encrypt Data with descriptive “Attributes” Ø Users Private Keys reflect Decryption Policies Encrypt w/attributes CA/PKG Authority is offline master-key 4
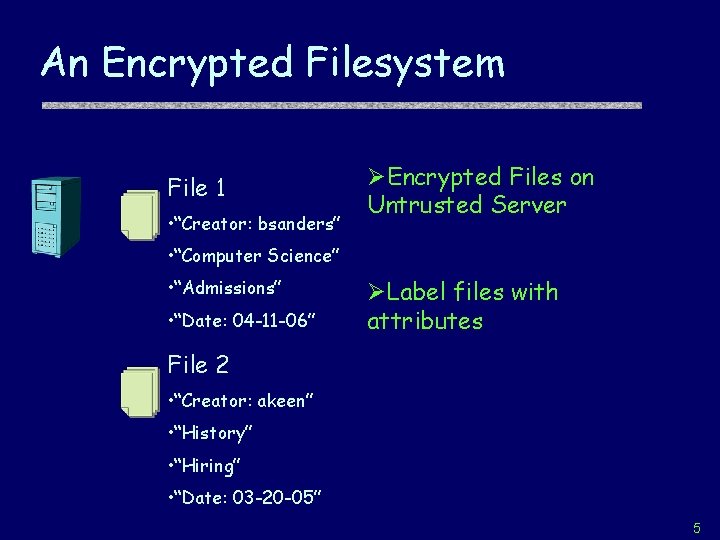
An Encrypted Filesystem File 1 • “Creator: bsanders” ØEncrypted Files on Untrusted Server • “Computer Science” • “Admissions” • “Date: 04 -11 -06” ØLabel files with attributes File 2 • “Creator: akeen” • “History” • “Hiring” • “Date: 03 -20 -05” 5
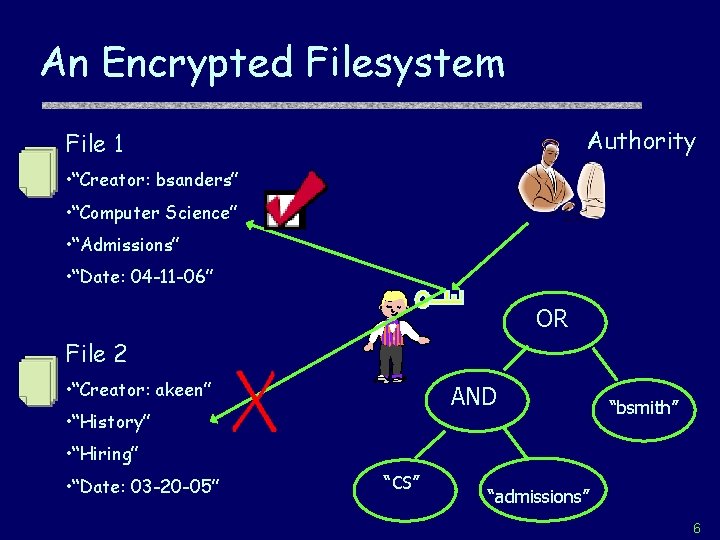
An Encrypted Filesystem Authority File 1 • “Creator: bsanders” • “Computer Science” • “Admissions” • “Date: 04 -11 -06” OR File 2 • “Creator: akeen” AND • “History” “bsmith” • “Hiring” • “Date: 03 -20 -05” “CS” “admissions” 6
This Talk Ø Threshold ABE & Biometrics Ø More “Advanced” ABE Ø Other Systems 7
![A Warmup: Threshold ABE[SW 05] Ø Data labeled with attributes Ø Keys of form A Warmup: Threshold ABE[SW 05] Ø Data labeled with attributes Ø Keys of form](http://slidetodoc.com/presentation_image/30d1ebada54647952dc5377f96148dab/image-8.jpg)
A Warmup: Threshold ABE[SW 05] Ø Data labeled with attributes Ø Keys of form “At least k” attributes Ø Application: IBE with Biometric Identities 8
Biometric Identities Iris Scan Voiceprint Fingerprint 9
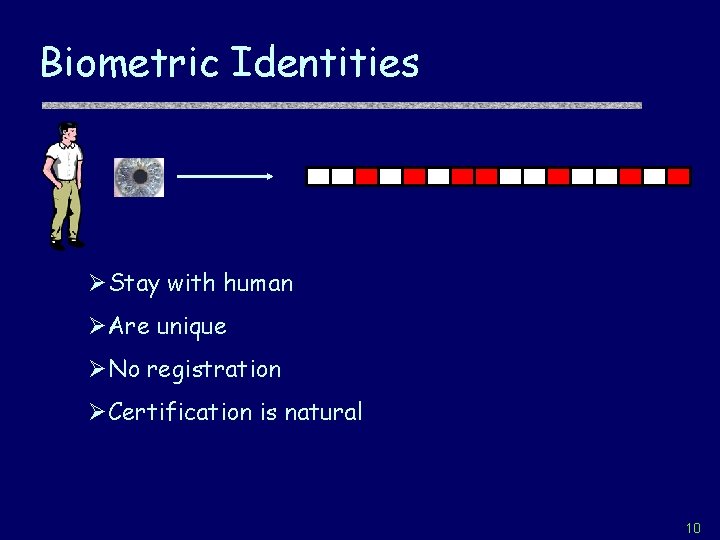
Biometric Identities ØStay with human ØAre unique ØNo registration ØCertification is natural 10
Biometric Identities Deviations Environment Difference in sensors Small change in trait Can’t use previous IBE solutions! 11
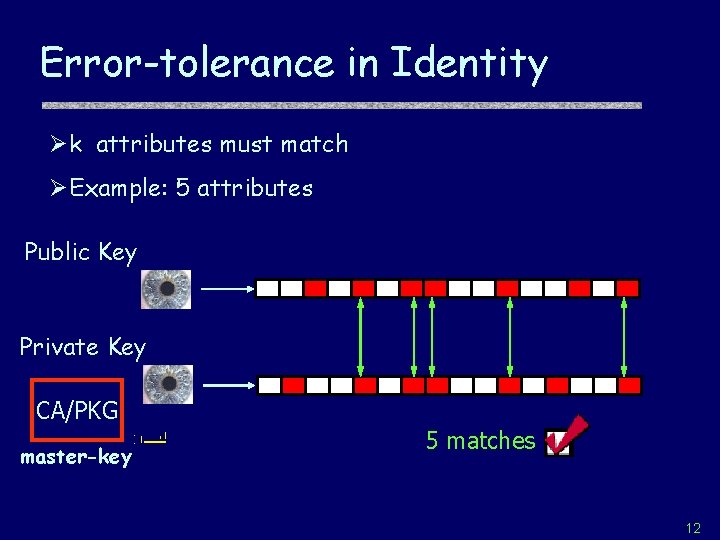
Error-tolerance in Identity Øk attributes must match ØExample: 5 attributes Public Key Private Key CA/PKG master-key 5 matches 12
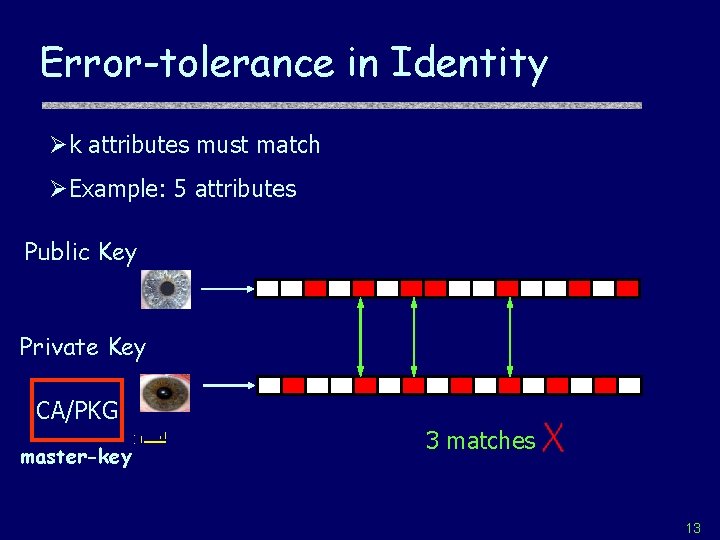
Error-tolerance in Identity Øk attributes must match ØExample: 5 attributes Public Key Private Key CA/PKG master-key 3 matches 13
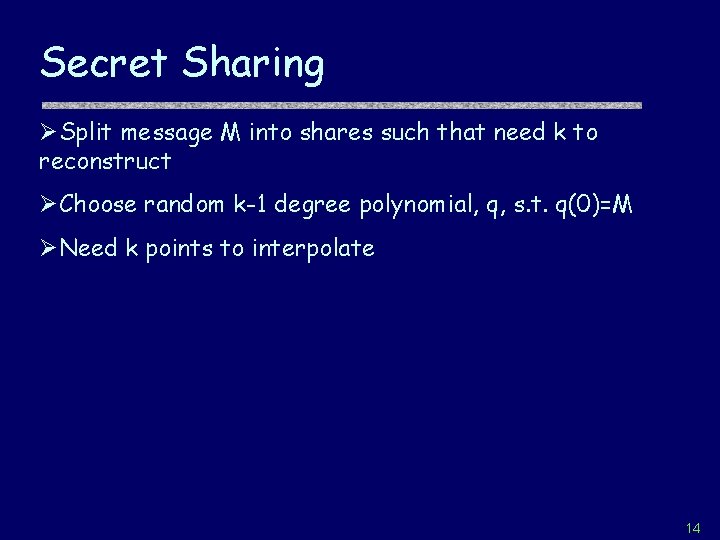
Secret Sharing ØSplit message M into shares such that need k to reconstruct ØChoose random k-1 degree polynomial, q, s. t. q(0)=M ØNeed k points to interpolate 14
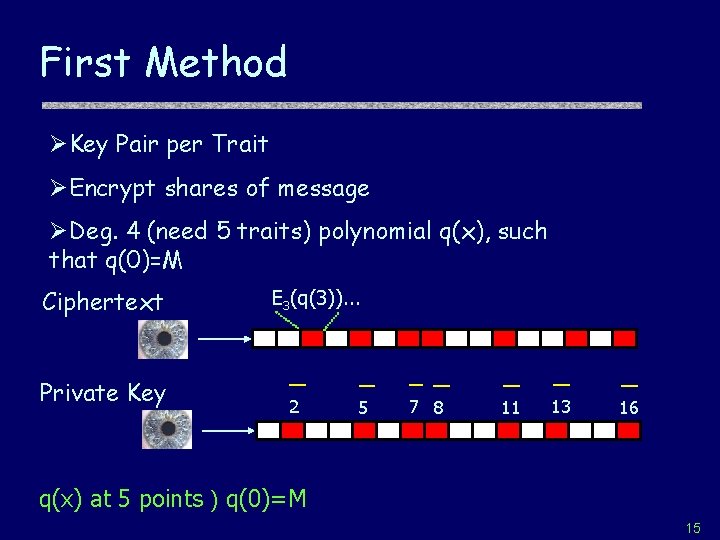
First Method ØKey Pair per Trait ØEncrypt shares of message ØDeg. 4 (need 5 traits) polynomial q(x), such that q(0)=M Ciphertext Private Key E 3(q(3)). . . 2 5 7 8 11 13 16 q(x) at 5 points ) q(0)=M 15
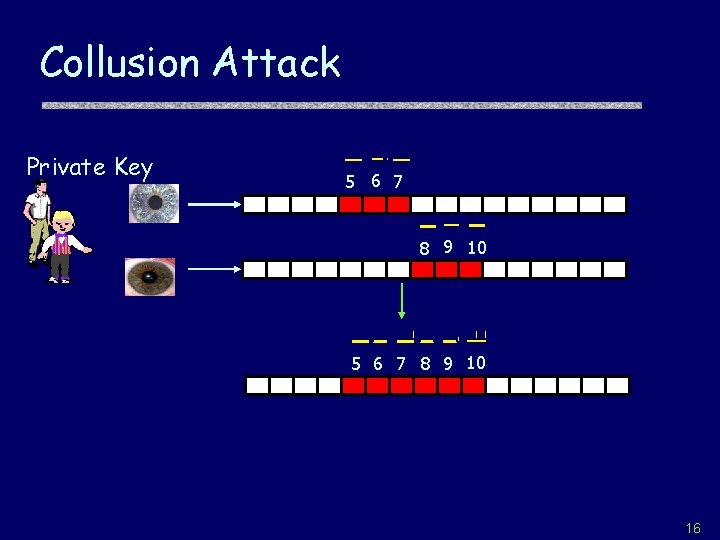
Collusion Attack Private Key 5 6 7 8 9 10 16
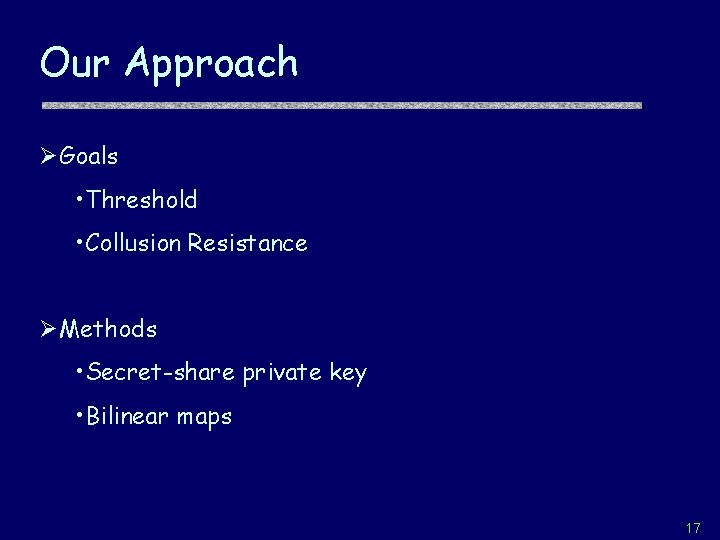
Our Approach ØGoals • Threshold • Collusion Resistance ØMethods • Secret-share private key • Bilinear maps 17
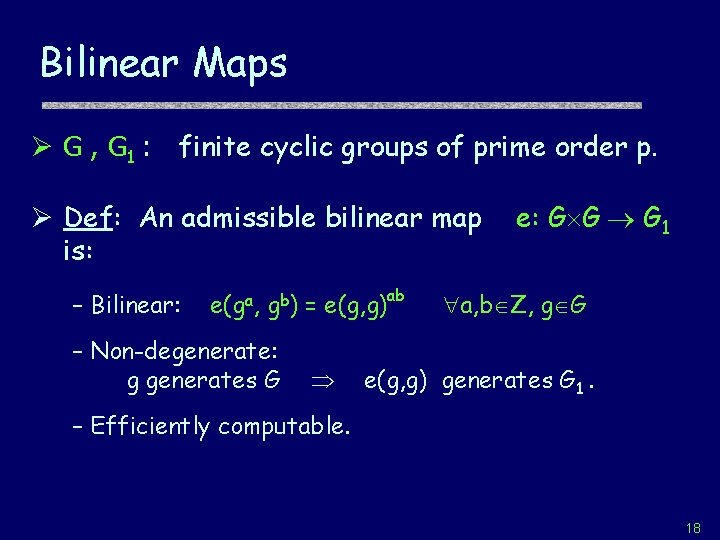
Bilinear Maps Ø G , G 1 : finite cyclic groups of prime order p. Ø Def: An admissible bilinear map is: – Bilinear: e(ga, gb) = e(g, g)ab – Non-degenerate: g generates G e: G G G 1 a, b Z, g G e(g, g) generates G 1. – Efficiently computable. 18
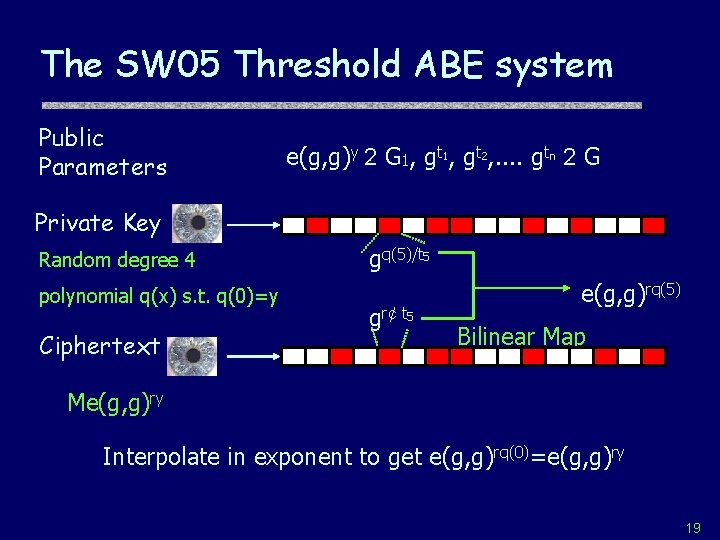
The SW 05 Threshold ABE system Public Parameters e(g, g)y 2 G 1, gt 2, . . gtn 2 G Private Key Random degree 4 polynomial q(x) s. t. q(0)=y Ciphertext gq(5)/t 5 gr¢ t 5 e(g, g)rq(5) Bilinear Map Me(g, g)ry Interpolate in exponent to get e(g, g)rq(0)=e(g, g)ry 19
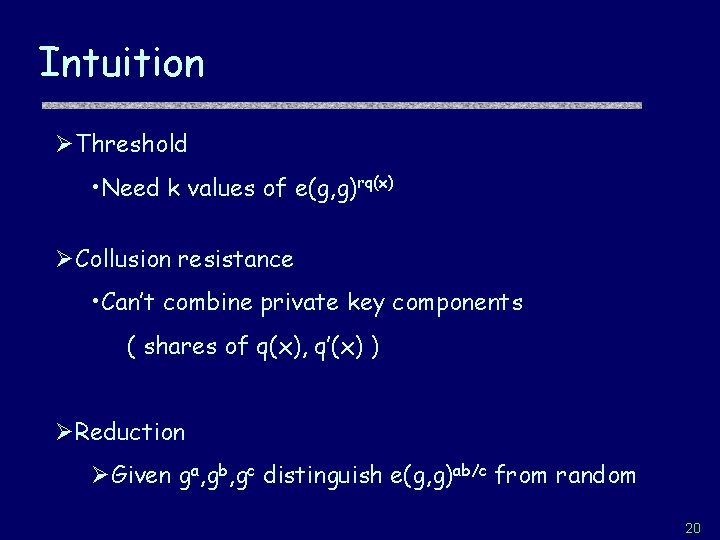
Intuition ØThreshold • Need k values of e(g, g)rq(x) ØCollusion resistance • Can’t combine private key components ( shares of q(x), q’(x) ) ØReduction ØGiven ga, gb, gc distinguish e(g, g)ab/c from random 20
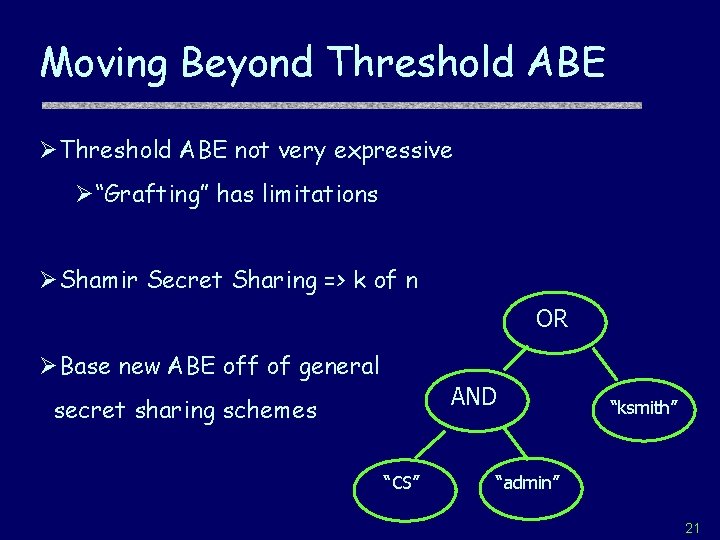
Moving Beyond Threshold ABE ØThreshold ABE not very expressive Ø“Grafting” has limitations ØShamir Secret Sharing => k of n OR ØBase new ABE off of general AND secret sharing schemes “CS” “ksmith” “admin” 21
![Access Trees [Ben 86] Ø Secret Sharing for tree-structure of AND + OR Ø Access Trees [Ben 86] Ø Secret Sharing for tree-structure of AND + OR Ø](http://slidetodoc.com/presentation_image/30d1ebada54647952dc5377f96148dab/image-22.jpg)
Access Trees [Ben 86] Ø Secret Sharing for tree-structure of AND + OR Ø Replicate ORs Split ANDs OR s Alice s-s’ s AND Bob s’ AND OR Charlie s-s’’ s s’’ Doug s’’ Edith 22
![Key-Policy Attribute-Based Encryption [GPSW 06] ØEncryption similar to Threshold ABE ØKeys reflect a tree Key-Policy Attribute-Based Encryption [GPSW 06] ØEncryption similar to Threshold ABE ØKeys reflect a tree](http://slidetodoc.com/presentation_image/30d1ebada54647952dc5377f96148dab/image-23.jpg)
Key-Policy Attribute-Based Encryption [GPSW 06] ØEncryption similar to Threshold ABE ØKeys reflect a tree access structure ØRandomness to prevent collusion! OR ØUse Threshold Gates ØDecrypt iff attributes from CT AND “ksmith” satisfy key’s policy “CS” “admin” 23
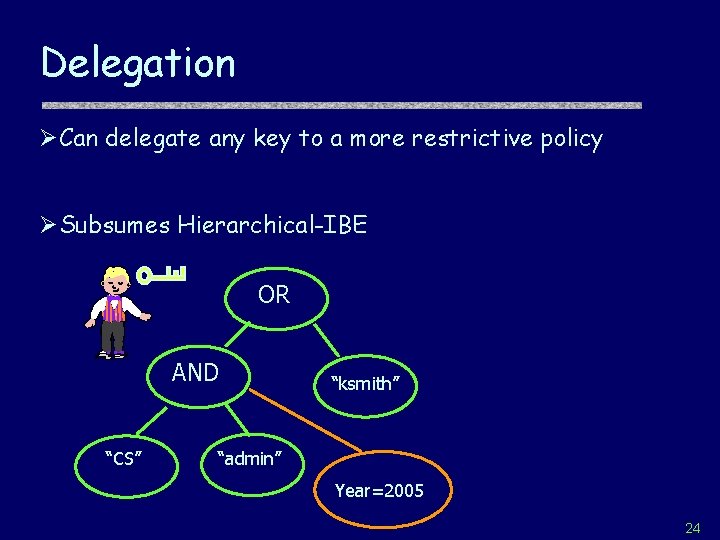
Delegation ØCan delegate any key to a more restrictive policy ØSubsumes Hierarchical-IBE OR AND “CS” “ksmith” “admin” Year=2005 24
![A comparison ABE [GPSW 06] Hidden Vector Enc. [BW 06] • Arbitrary Attributes • A comparison ABE [GPSW 06] Hidden Vector Enc. [BW 06] • Arbitrary Attributes •](http://slidetodoc.com/presentation_image/30d1ebada54647952dc5377f96148dab/image-25.jpg)
A comparison ABE [GPSW 06] Hidden Vector Enc. [BW 06] • Arbitrary Attributes • Fields Fixed at Setup • Expressive Policy • Conjunctions & don’t care • Attributes in Clear • Hidden Attributes 25
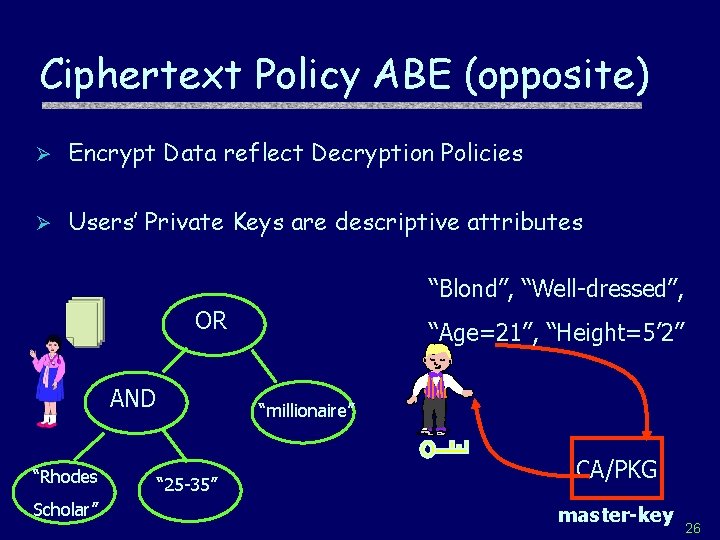
Ciphertext Policy ABE (opposite) Ø Encrypt Data reflect Decryption Policies Ø Users’ Private Keys are descriptive attributes “Blond”, “Well-dressed”, OR AND “Rhodes Scholar” “Age=21”, “Height=5’ 2” “millionaire” “ 25 -35” CA/PKG master-key 26
![Multi-Authority ABE [Chase 07] Ø Authorities over different domains • E. g. DMV and Multi-Authority ABE [Chase 07] Ø Authorities over different domains • E. g. DMV and](http://slidetodoc.com/presentation_image/30d1ebada54647952dc5377f96148dab/image-27.jpg)
Multi-Authority ABE [Chase 07] Ø Authorities over different domains • E. g. DMV and IRS Ø Challenge: Prevent Collusion Across Domains Ø Insight: Use “globally verifiable ID/attribute” to link 27
Open Problems Ø Ciphertext Policy ABE Ø ABE with “hidden attributes” Ø Policies from Circuits instead of Trees 28
Generalizing the Framework Cap abil Encrypt “Structured” Data Pr iv at e “C ity Req ues t ap ab ilit y” Authority is offline CA/PKG master-key 29
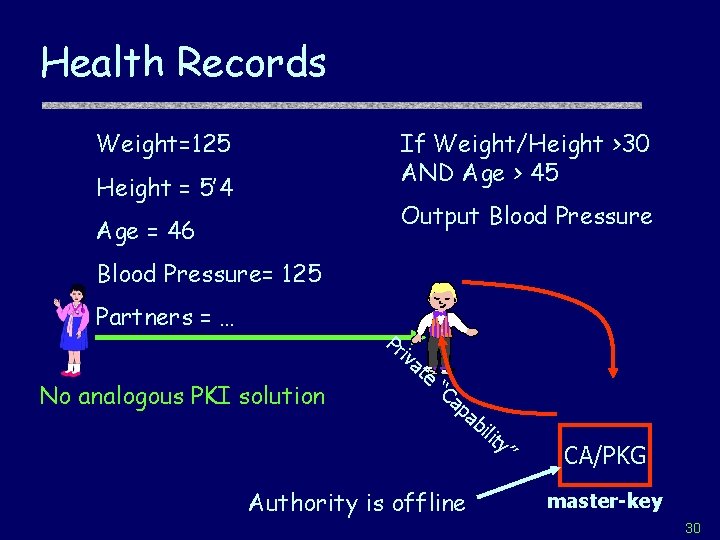
Health Records Weight=125 If Weight/Height >30 AND Age > 45 Height = 5’ 4 Output Blood Pressure Age = 46 Blood Pressure= 125 Partners = … Pr iv No analogous PKI solution at e “C ap ab ilit y” Authority is offline CA/PKG master-key 30
THE END 31
![Related Work Ø Secret Sharing Schemes [Shamir 79, Benaloh 86…] • Allow Collusion Ø Related Work Ø Secret Sharing Schemes [Shamir 79, Benaloh 86…] • Allow Collusion Ø](http://slidetodoc.com/presentation_image/30d1ebada54647952dc5377f96148dab/image-32.jpg)
Related Work Ø Secret Sharing Schemes [Shamir 79, Benaloh 86…] • Allow Collusion Ø Building from IBE + Secret Sharing [Smart 03, Juels] • IBE gives key Compression • Not Collusion Resistant 32
- Slides: 32