AttributeBased Encryption with NonMonotonic Access Structures Rafail Ostrovsky
Attribute-Based Encryption with Non-Monotonic Access Structures Rafail Ostrovsky Amit Sahai Brent Waters UCLA SRI International 1
Server Mediated Access Control File 1 Access list: John, Beth, Sue, Bob Attributes: “Computer Science” , “Admissions” • Server stores data in clear • Expressive access controls 2
Distributed Storage • Scalability • Reliability Downside: Increased vulnerability 3
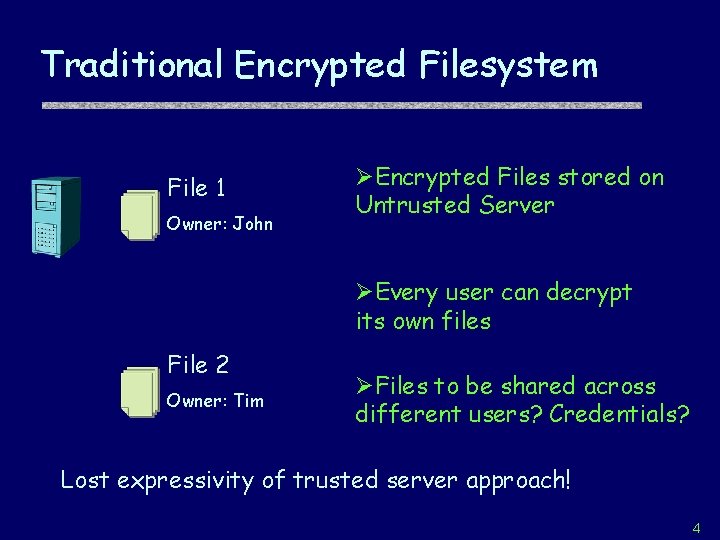
Traditional Encrypted Filesystem File 1 Owner: John ØEncrypted Files stored on Untrusted Server ØEvery user can decrypt its own files File 2 Owner: Tim ØFiles to be shared across different users? Credentials? Lost expressivity of trusted server approach! 4
![Attribute-Based Encryption [SW 05] Goal: Encryption with Expressive Access Control File 1 • “Creator: Attribute-Based Encryption [SW 05] Goal: Encryption with Expressive Access Control File 1 • “Creator:](http://slidetodoc.com/presentation_image_h2/aa8eb9acb84f25248af5ebea5d01d666/image-5.jpg)
Attribute-Based Encryption [SW 05] Goal: Encryption with Expressive Access Control File 1 • “Creator: John” ØLabel files with attributes • “Computer Science” • “Admissions” • “Date: 04 -11 -06” File 2 • “Creator: Tim” • “History” • “Admissions” • “Date: 03 -20 -05” 5
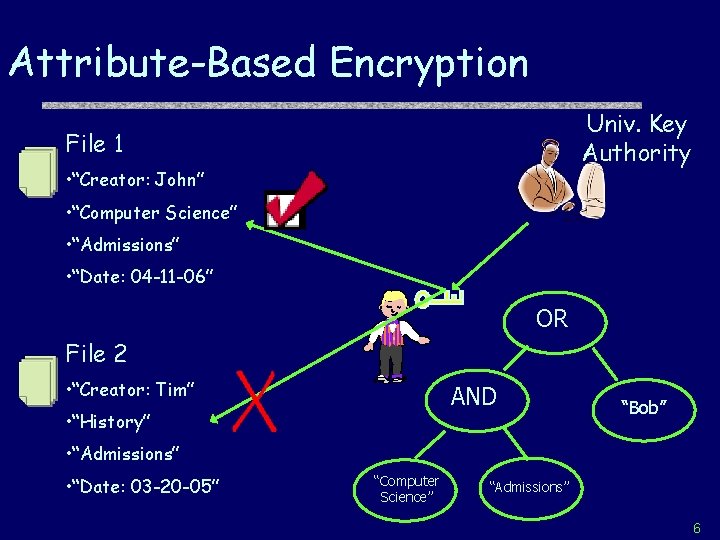
Attribute-Based Encryption Univ. Key Authority File 1 • “Creator: John” • “Computer Science” • “Admissions” • “Date: 04 -11 -06” OR File 2 • “Creator: Tim” AND • “History” “Bob” • “Admissions” • “Date: 03 -20 -05” “Computer Science” “Admissions” 6
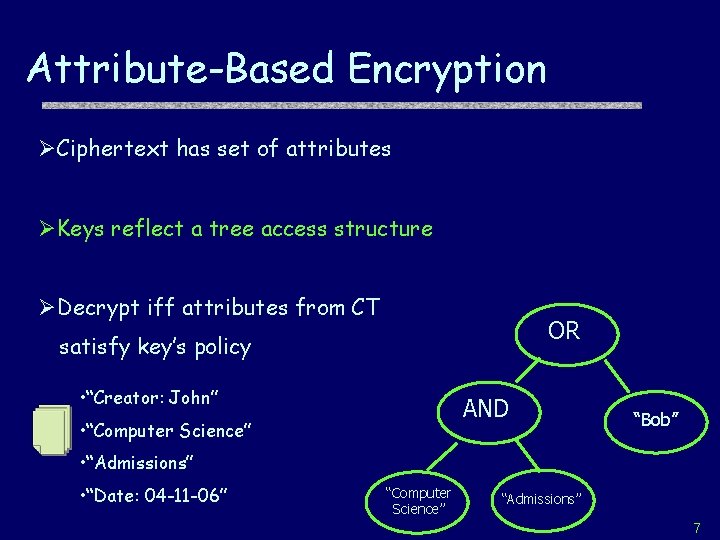
Attribute-Based Encryption ØCiphertext has set of attributes ØKeys reflect a tree access structure ØDecrypt iff attributes from CT OR satisfy key’s policy • “Creator: John” AND • “Computer Science” “Bob” • “Admissions” • “Date: 04 -11 -06” “Computer Science” “Admissions” 7
Central goal: Prevent Collusions ØIf neither user can decrypt a CT, then they can’t together AND “Computer Science” “Admissions” AND “History” “Hiring” Ciphertext = M, {“Computer Science”, “Hiring”} 8
![Current ABE Systems [GPWS 06] Monotonic Access Formulas • Tree of ANDs, ORs, threshold Current ABE Systems [GPWS 06] Monotonic Access Formulas • Tree of ANDs, ORs, threshold](http://slidetodoc.com/presentation_image_h2/aa8eb9acb84f25248af5ebea5d01d666/image-9.jpg)
Current ABE Systems [GPWS 06] Monotonic Access Formulas • Tree of ANDs, ORs, threshold (k of N) … • Attributes at leaves • NOT is unsupported! OR AND “Computer Science” “Bob” “Admissions” 9
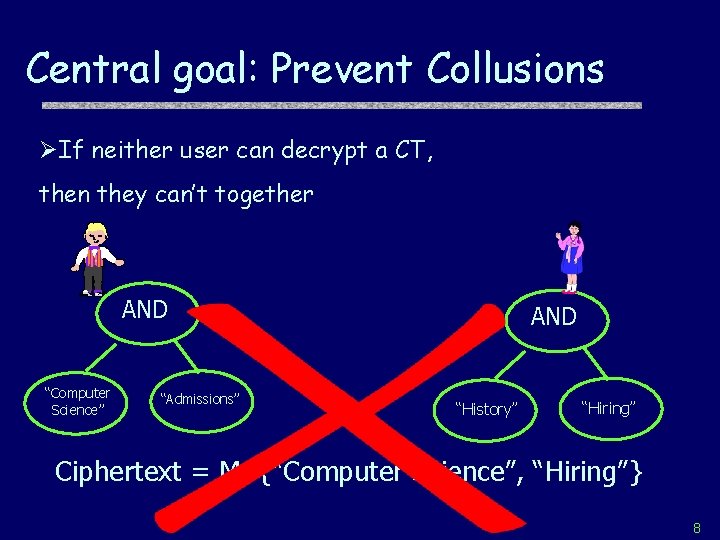
Key Generation t 1, geach t 2, . . key y Publicrandomness usedgfor Fresh gtn, e(g, g) generated! Parameters y OR y “Compute r Science” y 3= (y-r) Private Key AND “Bob” “Greedy” Decryption y 1=y “Admissions” yn=r gy 1/t 1 , gy 3/t 3 , gyn/tn 10
![Supporting “NOTs” [OSW 07] Example Peer Review of Other Depts. Bob is in C. Supporting “NOTs” [OSW 07] Example Peer Review of Other Depts. Bob is in C.](http://slidetodoc.com/presentation_image_h2/aa8eb9acb84f25248af5ebea5d01d666/image-11.jpg)
Supporting “NOTs” [OSW 07] Example Peer Review of Other Depts. Bob is in C. S. dept => Avoid Conflict of Interest AND NOT “Dept. Review” “Year: 2007” “Computer Science” Challenge: Can’t attacker just ignore CT components? 11
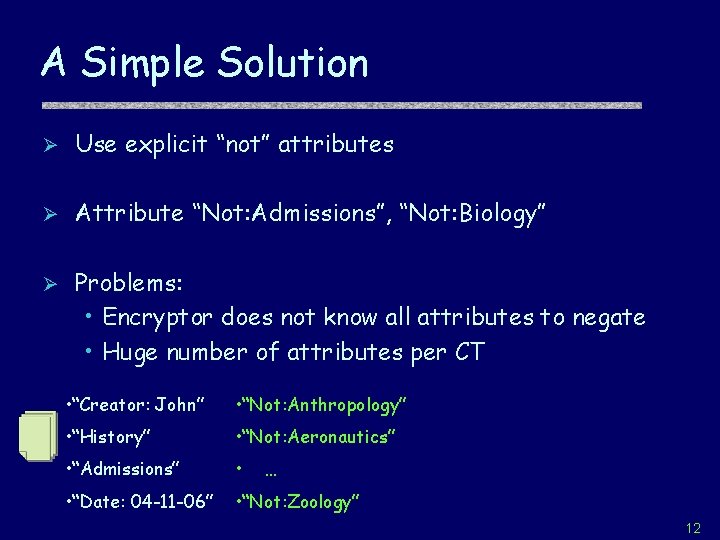
A Simple Solution Ø Use explicit “not” attributes Ø Attribute “Not: Admissions”, “Not: Biology” Ø Problems: • Encryptor does not know all attributes to negate • Huge number of attributes per CT • “Creator: John” • “Not: Anthropology” • “History” • “Not: Aeronautics” • “Admissions” • • “Date: 04 -11 -06” • “Not: Zoology” … 12
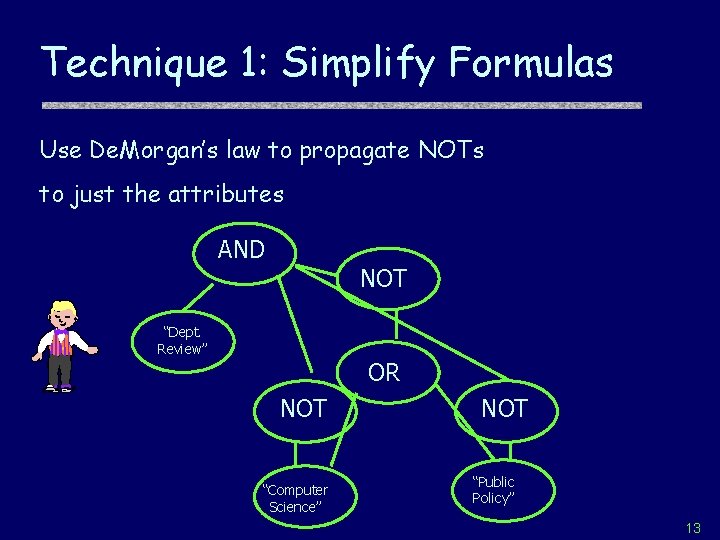
Technique 1: Simplify Formulas Use De. Morgan’s law to propagate NOTs to just the attributes AND NOT “Dept. Review” OR NOT “Computer Science” NOT “Public Policy” 13
![Revocation Systems [NNL 01, NP 01…] Ø Broadcast to all but a certain set Revocation Systems [NNL 01, NP 01…] Ø Broadcast to all but a certain set](http://slidetodoc.com/presentation_image_h2/aa8eb9acb84f25248af5ebea5d01d666/image-14.jpg)
Revocation Systems [NNL 01, NP 01…] Ø Broadcast to all but a certain set of users Ø Application: Digital content protection P 1 P 2 P 3 14
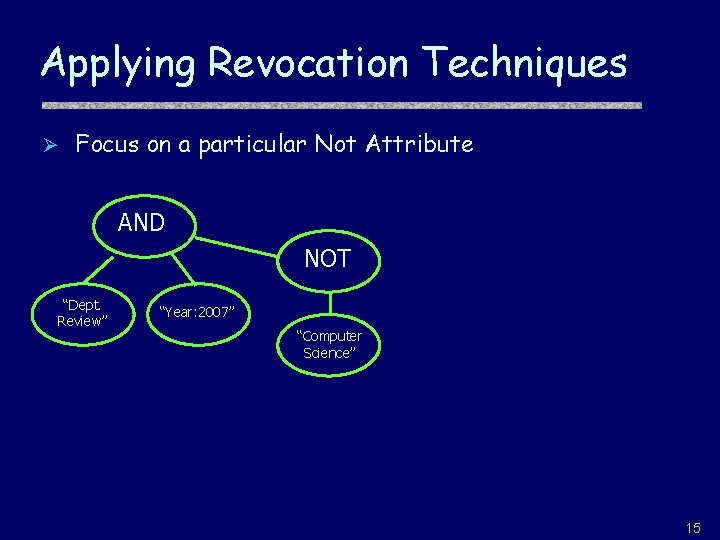
Applying Revocation Techniques Ø Focus on a particular Not Attribute AND NOT “Dept. Review” “Year: 2007” “Computer Science” 15
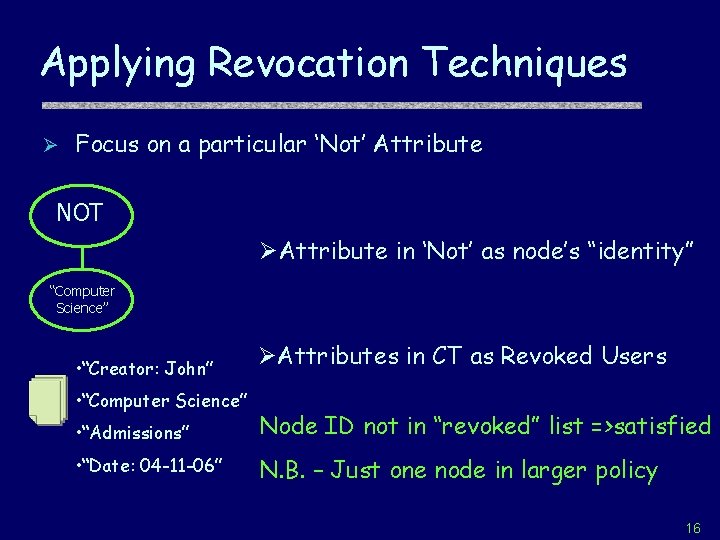
Applying Revocation Techniques Ø Focus on a particular ‘Not’ Attribute NOT ØAttribute in ‘Not’ as node’s “identity” “Computer Science” • “Creator: John” • “Computer Science” ØAttributes in CT as Revoked Users • “Admissions” Node ID not in “revoked” list =>satisfied • “Date: 04 -11 -06” N. B. – Just one node in larger policy 16
![“Polynomial Revocation” [NP 01] Ø Pick a degree n polynomial q( ), q(0)=a • “Polynomial Revocation” [NP 01] Ø Pick a degree n polynomial q( ), q(0)=a •](http://slidetodoc.com/presentation_image_h2/aa8eb9acb84f25248af5ebea5d01d666/image-17.jpg)
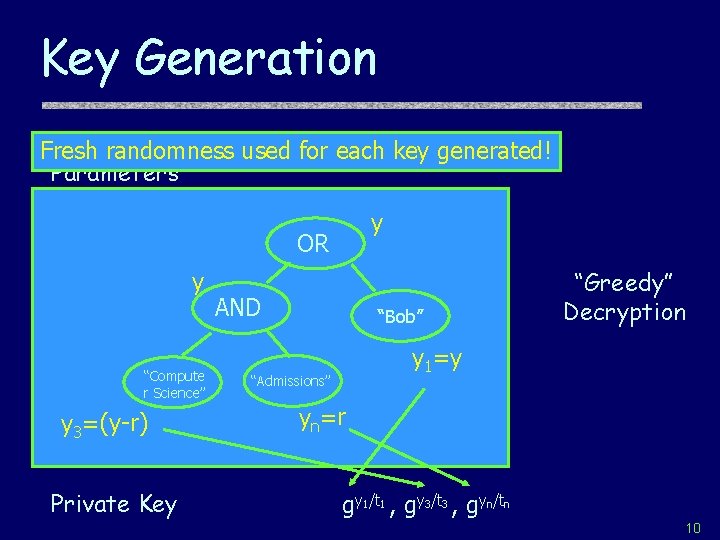
“Polynomial Revocation” [NP 01] Ø Pick a degree n polynomial q( ), q(0)=a • n+1 points to interpolate Ø User t gets q(t) Ø Encryption: • Revoked x 1, …, xn gs , gsq(x 1) , . . . , gsq(xn) , Mgsa gsq(t) Can interpolate to gsq(0)=gsa iff t not in {x 1, …xn} 17
ABE with Negation Ø Push NOTs to leaves Ø Apply ABE key generation • Collusion resistance still key! • Treat non-negated attributes same Ø New Type of Polynomial Revocation at Leaves 18
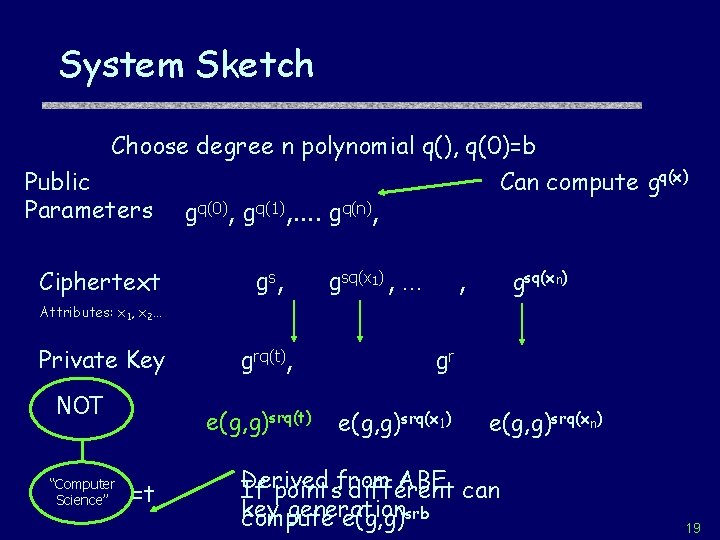
System Sketch Choose degree n polynomial q(), q(0)=b Public Can compute gq(x) Parameters gq(0), gq(1), . . gq(n), Ciphertext g s, gsq(x 1) , … gsq(xn) , Attributes: x 1, x 2… Private Key NOT “Computer Science” grq(t), e(g, g)srq(t) =t gr e(g, g)srq(x 1) e(g, g)srq(xn) Derived ABE can If pointsfrom different key generation compute e(g, g)srb 19
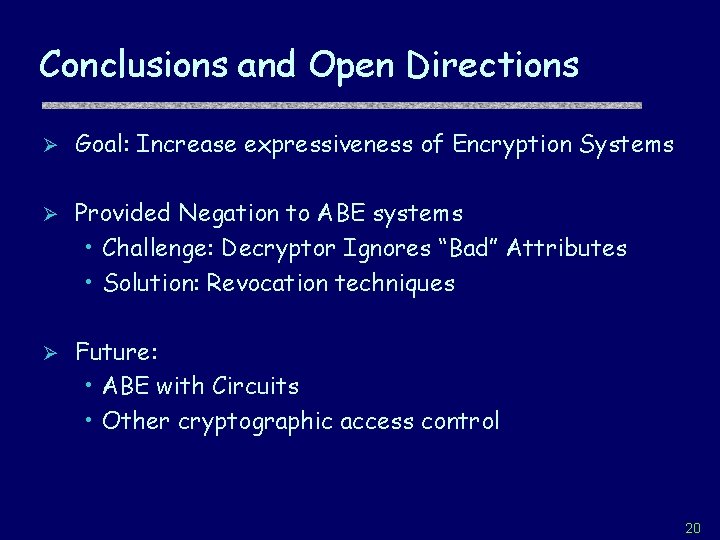
Conclusions and Open Directions Ø Goal: Increase expressiveness of Encryption Systems Ø Provided Negation to ABE systems • Challenge: Decryptor Ignores “Bad” Attributes • Solution: Revocation techniques Ø Future: • ABE with Circuits • Other cryptographic access control 20
Thank You 21
- Slides: 21