AttributeBased Encryption for FineGrained Access Control of Encrypted
Attribute-Based Encryption for Fine-Grained Access Control of Encrypted Data Vipul Goyal UCLA Omkant Pandey UCLA Amit Sahai UCLA Brent Waters SRI 1
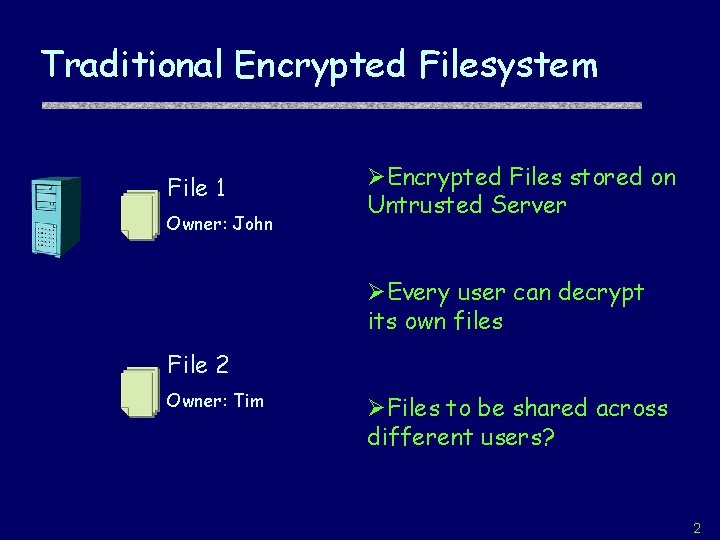
Traditional Encrypted Filesystem File 1 Owner: John ØEncrypted Files stored on Untrusted Server ØEvery user can decrypt its own files File 2 Owner: Tim ØFiles to be shared across different users? 2
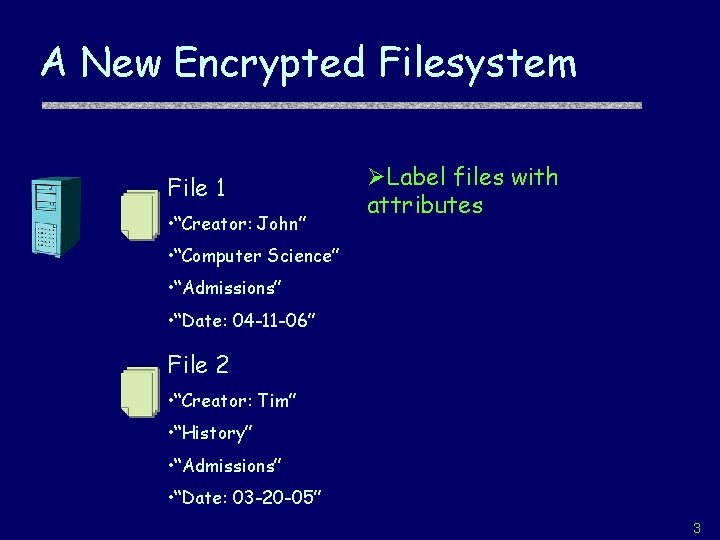
A New Encrypted Filesystem File 1 • “Creator: John” ØLabel files with attributes • “Computer Science” • “Admissions” • “Date: 04 -11 -06” File 2 • “Creator: Tim” • “History” • “Admissions” • “Date: 03 -20 -05” 3
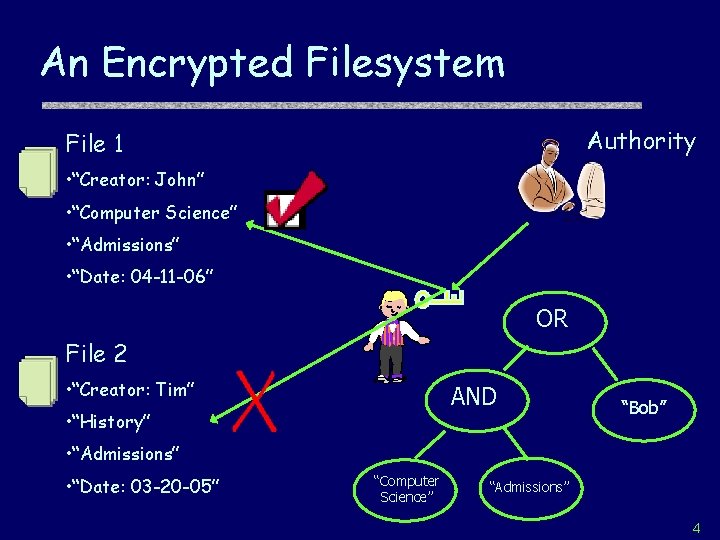
An Encrypted Filesystem Authority File 1 • “Creator: John” • “Computer Science” • “Admissions” • “Date: 04 -11 -06” OR File 2 • “Creator: Tim” AND • “History” “Bob” • “Admissions” • “Date: 03 -20 -05” “Computer Science” “Admissions” 4
![Threshold Attribute-Based Enc. [SW 05] Ø Sahai-Waters introduced ABE, but only for “threshold policies”: Threshold Attribute-Based Enc. [SW 05] Ø Sahai-Waters introduced ABE, but only for “threshold policies”:](http://slidetodoc.com/presentation_image_h/29970b34ec734d64e95c41823fc4b0f5/image-5.jpg)
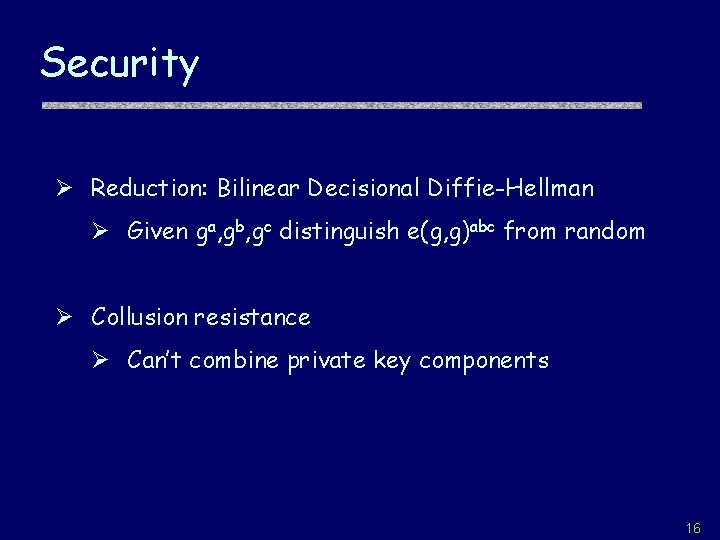
Threshold Attribute-Based Enc. [SW 05] Ø Sahai-Waters introduced ABE, but only for “threshold policies”: • Ciphertext has set of attributes • User has set of attributes • If more than k attributes match, then User can decrypt. Ø Main Application- Biometrics 5
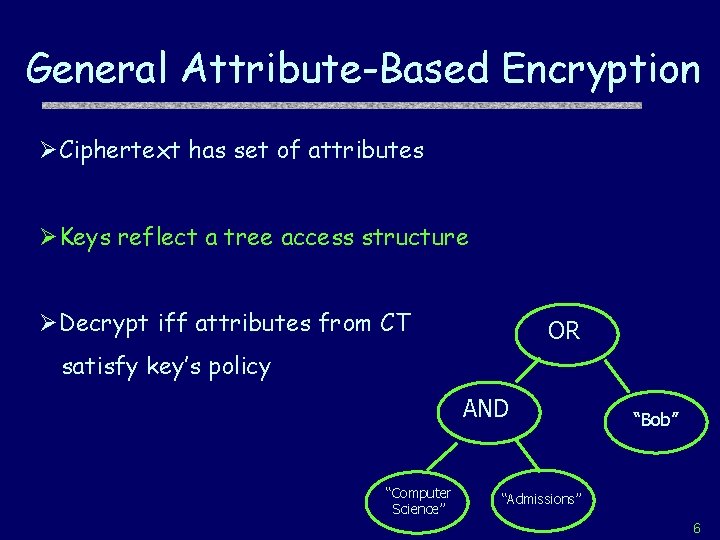
General Attribute-Based Encryption ØCiphertext has set of attributes ØKeys reflect a tree access structure ØDecrypt iff attributes from CT OR satisfy key’s policy AND “Computer Science” “Bob” “Admissions” 6
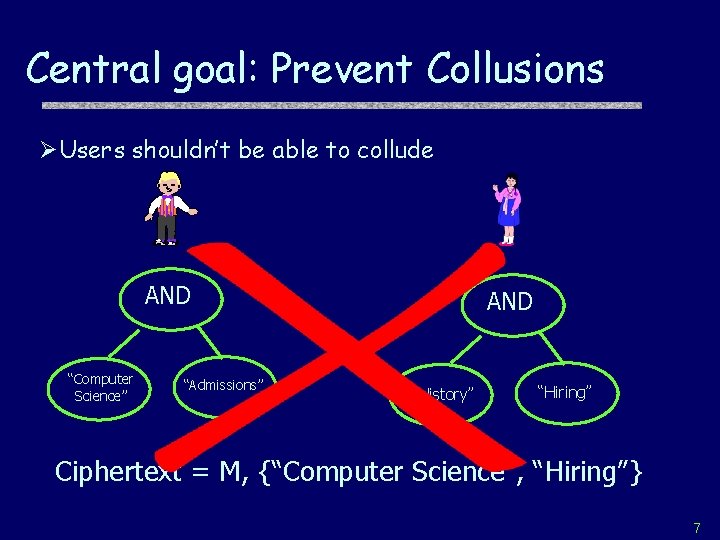
Central goal: Prevent Collusions ØUsers shouldn’t be able to collude AND “Computer Science” “Admissions” AND “History” “Hiring” Ciphertext = M, {“Computer Science”, “Hiring”} 7
![Related Work Ø Access Control [Smart 03], Hidden Credentials [Holt et al. 03 -04] Related Work Ø Access Control [Smart 03], Hidden Credentials [Holt et al. 03 -04]](http://slidetodoc.com/presentation_image_h/29970b34ec734d64e95c41823fc4b0f5/image-8.jpg)
Related Work Ø Access Control [Smart 03], Hidden Credentials [Holt et al. 03 -04] • Not Collusion Resistant Ø Secret Sharing Schemes [Shamir 79, Benaloh 86…] • Allow Collusion 8
Techniques We combine two ideas Ø Bilinear maps Ø General Secret Sharing Schemes 9
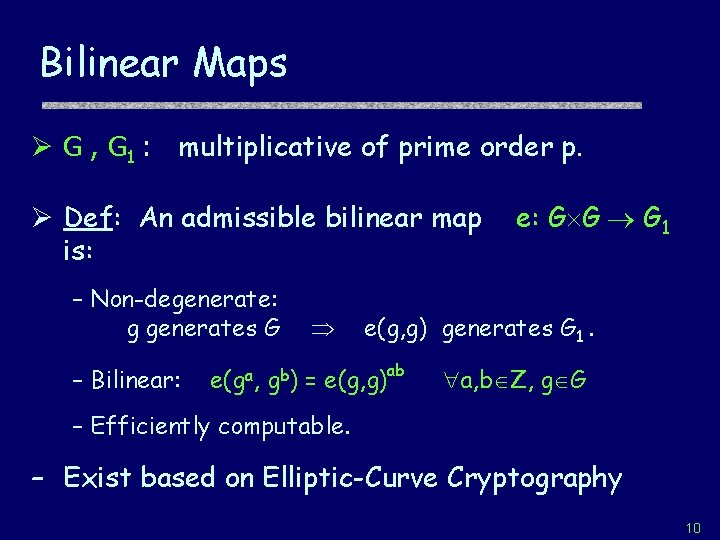
Bilinear Maps Ø G , G 1 : multiplicative of prime order p. Ø Def: An admissible bilinear map is: – Non-degenerate: g generates G – Bilinear: e: G G G 1 e(g, g) generates G 1. e(ga, gb) = e(g, g)ab a, b Z, g G – Efficiently computable. – Exist based on Elliptic-Curve Cryptography 10
![Secret Sharing Ø [Ben 86] Secret Sharing for tree-structure of AND + OR Replicate Secret Sharing Ø [Ben 86] Secret Sharing for tree-structure of AND + OR Replicate](http://slidetodoc.com/presentation_image_h/29970b34ec734d64e95c41823fc4b0f5/image-11.jpg)
Secret Sharing Ø [Ben 86] Secret Sharing for tree-structure of AND + OR Replicate secret for OR’s. Split secrets for AND’s. y OR y AND “Bob” y “Computer Science” (y-r) “Admissions” r 11
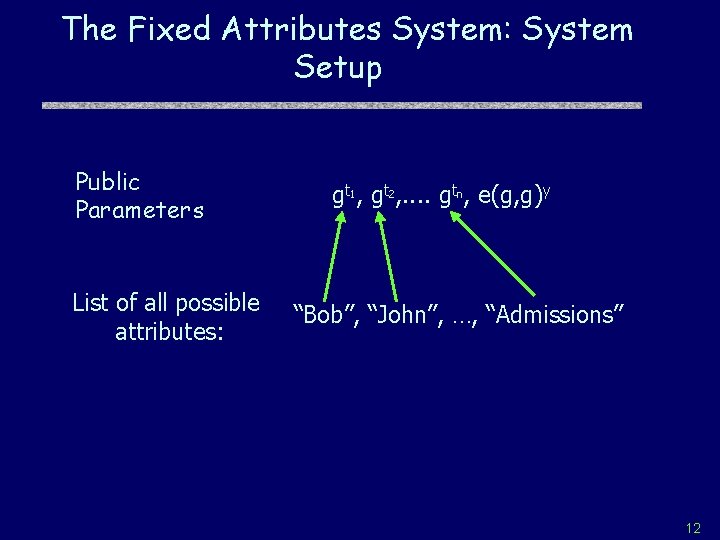
The Fixed Attributes System: System Setup Public Parameters List of all possible attributes: gt 1, gt 2, . . gtn, e(g, g)y “Bob”, “John”, …, “Admissions” 12
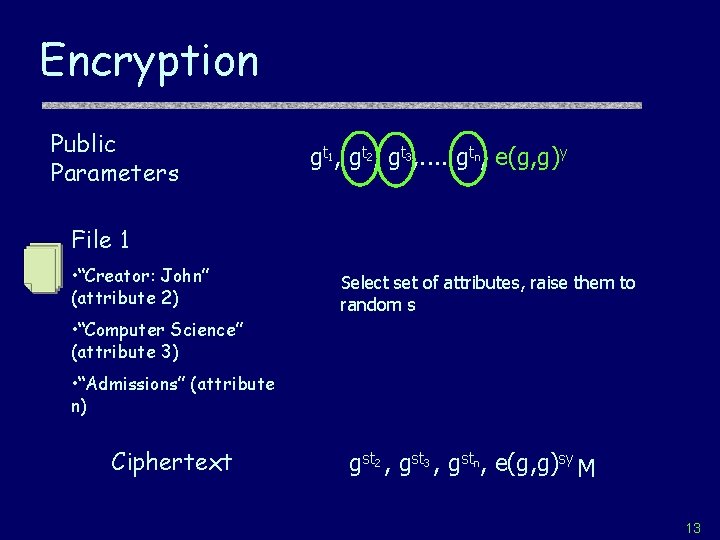
Encryption Public Parameters gt 1, gt 2, gt 3, . . gtn, e(g, g)y File 1 • “Creator: John” (attribute 2) Select set of attributes, raise them to random s • “Computer Science” (attribute 3) • “Admissions” (attribute n) Ciphertext gst 2 , gst 3 , gstn, e(g, g)sy M 13
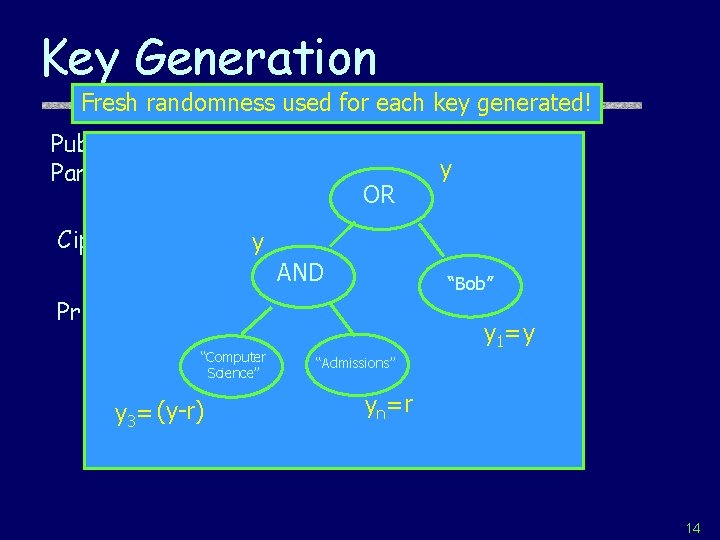
Key Generation Fresh randomness used for each key generated! Public Parameters gt 1, gt 2, . . gtn, e(g, g)y y OR Ciphertext y Private Key gst 2 , gst 3 , gstn, e(g, g)sy M AND “Bob” gy 1/t 1 , gy 3/t 3 , gyn/tn “Computer Science” y 3= (y-r) y 1 = y “Admissions” yn = r 14
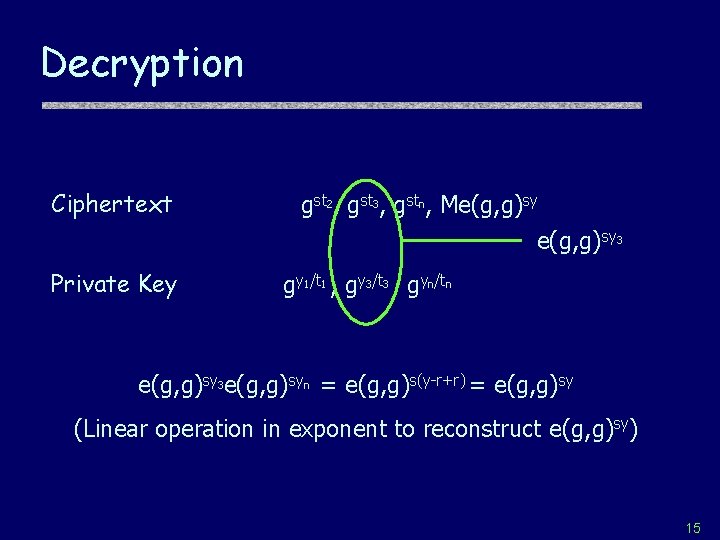
Decryption Ciphertext Private Key gst 2, gst 3, gstn, Me(g, g)sy 3 gy 1/t 1 , gy 3/t 3 , gyn/tn e(g, g)sy 3 e(g, g)syn = e(g, g)s(y-r+r) = e(g, g)sy (Linear operation in exponent to reconstruct e(g, g)sy) 15
Security Ø Reduction: Bilinear Decisional Diffie-Hellman Ø Given ga, gb, gc distinguish e(g, g)abc from random Ø Collusion resistance Ø Can’t combine private key components 16
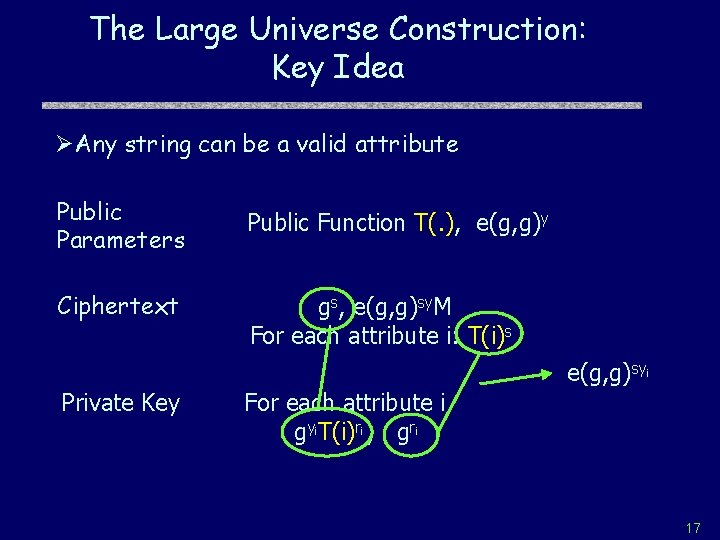
The Large Universe Construction: Key Idea ØAny string can be a valid attribute Public Parameters Ciphertext Public Function T(. ), e(g, g)y gs, e(g, g)sy. M For each attribute i: T(i)s e(g, g)syi Private Key For each attribute i gyi. T(i)ri , gri 17
Extensions ØBuilding from any linear secret sharing scheme Ø In particular, tree of threshold gates… ØDelegation of Private Keys 18
![Delegation ØDerive a key for a more restrictive policy ØSubsumes Hierarchical-IBE [Horwitz-Lynn 02, …] Delegation ØDerive a key for a more restrictive policy ØSubsumes Hierarchical-IBE [Horwitz-Lynn 02, …]](http://slidetodoc.com/presentation_image_h/29970b34ec734d64e95c41823fc4b0f5/image-19.jpg)
Delegation ØDerive a key for a more restrictive policy ØSubsumes Hierarchical-IBE [Horwitz-Lynn 02, …] OR AND “Computer Science” “Bob” Bob’s Assistant “admissions” Year=2006 19
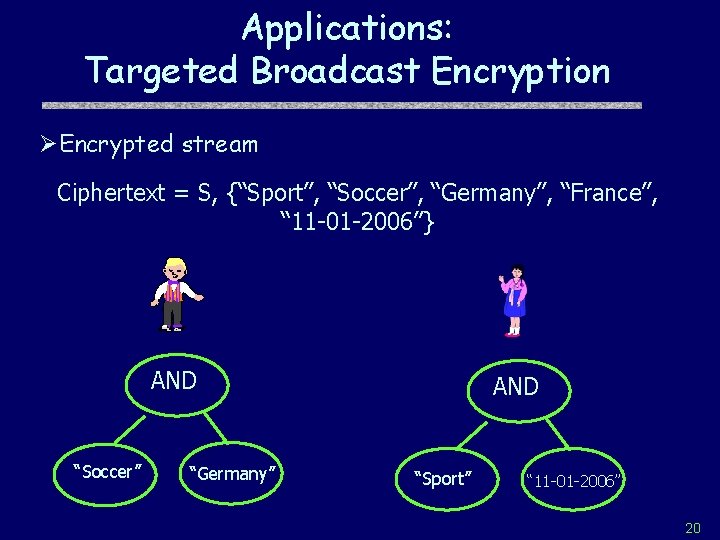
Applications: Targeted Broadcast Encryption ØEncrypted stream Ciphertext = S, {“Sport”, “Soccer”, “Germany”, “France”, “ 11 -01 -2006”} AND “Soccer” “Germany” AND “Sport” “ 11 -01 -2006” 20
Thank You 21
- Slides: 21