Electronic Engineering Mobile and Wireless Networking Lecture 17
Electronic Engineering Mobile and Wireless Networking Lecture 17 Dr. Xinbing Wang 1
Overview of the Course Part 1: Wireless communication systems (Chapter 1) – Flexibility to support roaming – Limitations: Geographical coverage, transmission rate, and transmission errors Part 2: Wireless communication technology – Radio propagation (Chapter 5) – Spread spectrum (Chapter 7) Part 3: Current wireless systems – Cellular network architecture (Chapter 10) – Mobile IP (Chapter 12) – Wireless LAN (Chapter 11/13/14) Part 4; Other wireless networks – – Ad hoc networks (Reading materials) Sensor networks (Reading materials) Wireless PAN (Chapter 15) Satellite systems (Chapter 9) Part 5: Wireless Security Electronic Engineering Dr. Xinbing Wang 2
Part 4: Other Wireless Networks Ad hoc networks – – – Mobility and routing Flooding routing algorithm Dynamic source routing (DSR) Ad hoc On-Demand Distance Vector Routing (AODV) Location-Aided routing (LAR) Quality of Service (Qo. S) in ad hoc networks Sensor networks Wireless PANs Electronic Engineering Dr. Xinbing Wang 3
Mobility Characteristics Mobility patterns may be different – – – people sitting at an airport lounge New York taxi cabs kids playing military movements personal area network Mobility characteristics – speed – predictability direction of movement pattern of movement – uniformity (or lack thereof) of mobility characteristics among different nodes Electronic Engineering Dr. Xinbing Wang 4
Challenges Limited wireless transmission range Broadcast nature of the wireless medium – Hidden terminal problem Packet losses due to transmission errors Mobility-induced route changes Mobility-induced packet losses Battery constraints Potentially frequent network partitions Ease of snooping on wireless transmissions (security hazard) Electronic Engineering Dr. Xinbing Wang 5
Why is Routing in MANET different ? Host mobility – link failure/repair due to mobility may have different characteristics than those due to other causes Rate of link failure/repair may be high when nodes move fast New performance criteria may be used – route stability despite mobility – energy consumption Electronic Engineering Dr. Xinbing Wang 6
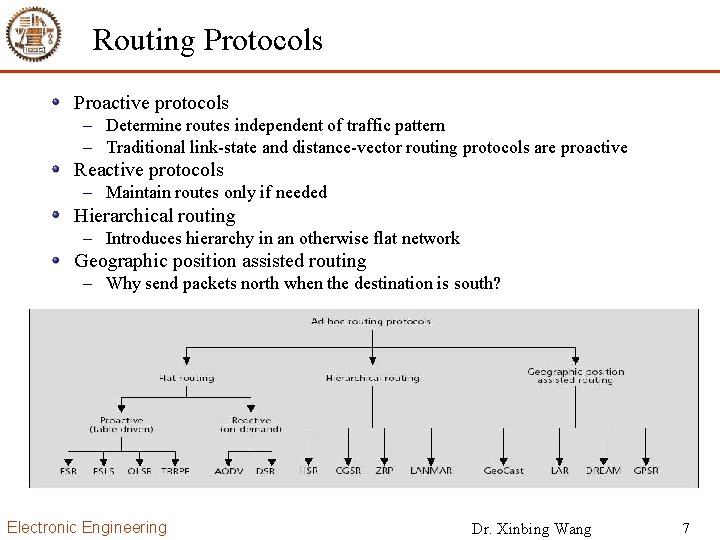
Routing Protocols Proactive protocols – Determine routes independent of traffic pattern – Traditional link-state and distance-vector routing protocols are proactive Reactive protocols – Maintain routes only if needed Hierarchical routing – Introduces hierarchy in an otherwise flat network Geographic position assisted routing – Why send packets north when the destination is south? Electronic Engineering Dr. Xinbing Wang 7
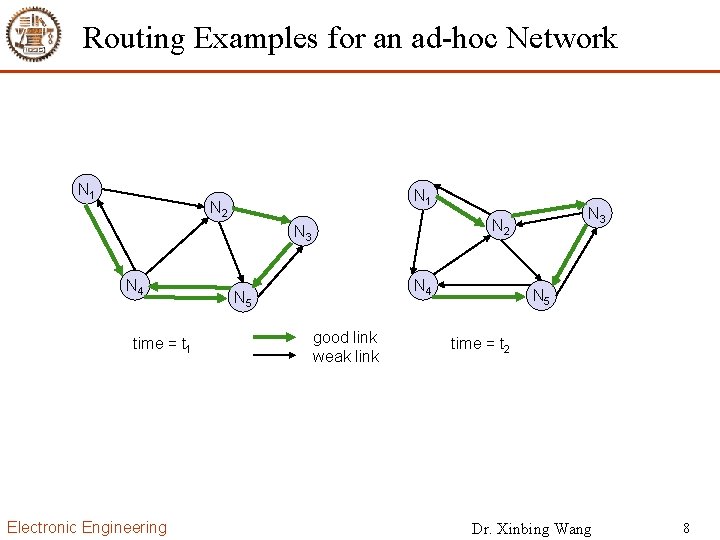
Routing Examples for an ad-hoc Network N 1 N 2 N 3 N 4 time = t 1 Electronic Engineering N 3 N 2 N 4 N 5 good link weak link N 5 time = t 2 Dr. Xinbing Wang 8
Traditional Routing Algorithms Distance Vector – periodic exchange of messages with all physical neighbors that contain information about who can be reached at what distance – selection of the shortest path if several paths available Link State – periodic notification of all routers about the current state of all physical links – router get a complete picture of the network Example – – ARPA packet radio network (1973), DV-Routing every 7. 5 s exchange of routing tables including link quality updating of tables also by reception of packets routing problems solved with limited flooding Electronic Engineering Dr. Xinbing Wang 9
Problems of traditional routing algorithms Dynamic of the topology – frequent changes of connections, connection quality, participants Limited performance of mobile systems – periodic updates of routing tables need energy without contributing to the transmission of user data, sleep modes difficult to realize – limited bandwidth of the system is reduced even more due to the exchange of routing information – links can be asymmetric, i. e. , they can have a direction dependent transmission quality Problem – protocols have been designed for fixed networks with infrequent changes and typically assume symmetric links Electronic Engineering Dr. Xinbing Wang 10
Trade-Off Latency of route discovery – Proactive protocols may have lower latency since routes are maintained at all times – Reactive protocols may have higher latency because a route from X to Y will be found only when X attempts to send to Y Overhead of route discovery/maintenance – Reactive protocols may have lower overhead since routes are determined only if needed – Proactive protocols can (but not necessarily) result in higher overhead due to continuous route updating Which approach achieves a better trade-off depends on the traffic and mobility patterns Electronic Engineering Dr. Xinbing Wang 11
Flooding for Data Delivery Sender S broadcasts data packet P to all its neighbors Each node receiving P forwards P to its neighbors Sequence numbers used to avoid the possibility of forwarding the same packet more than once Packet P reaches destination D provided that D is reachable from sender S Node D does not forward the packet Electronic Engineering Dr. Xinbing Wang 12
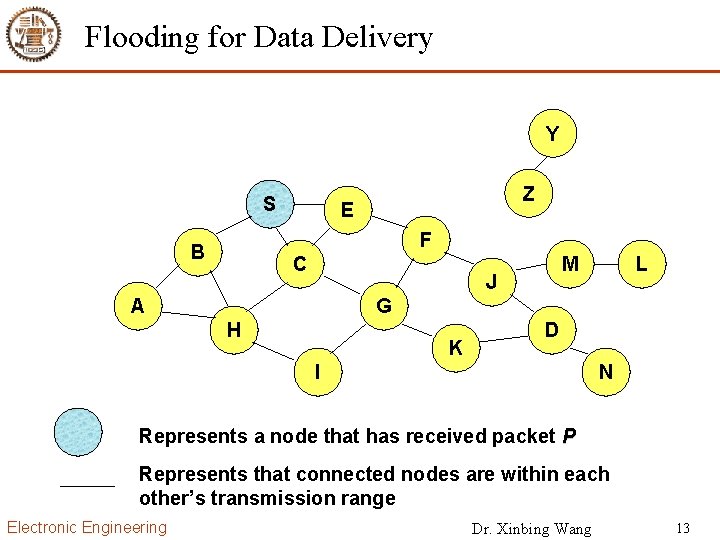
Flooding for Data Delivery Y S Z E F B C M J A L G H K D I N Represents a node that has received packet P Represents that connected nodes are within each other’s transmission range Electronic Engineering Dr. Xinbing Wang 13
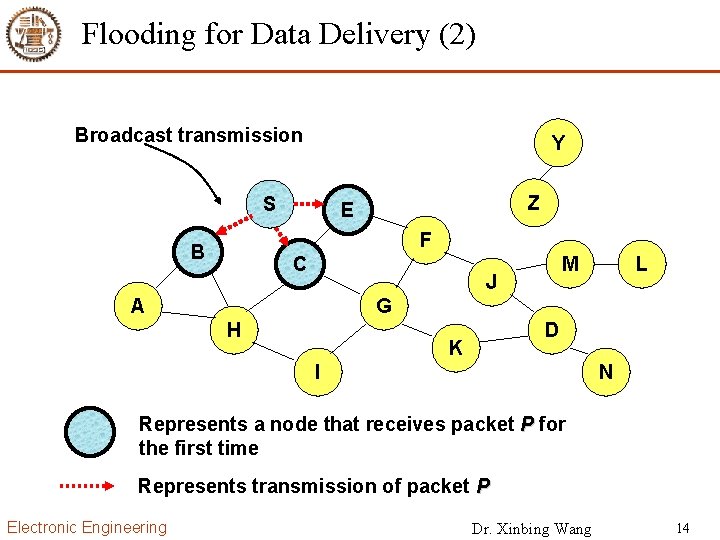
Flooding for Data Delivery (2) Broadcast transmission Y S Z E F B C M J A L G H D K I N Represents a node that receives packet P for the first time Represents transmission of packet P Electronic Engineering Dr. Xinbing Wang 14
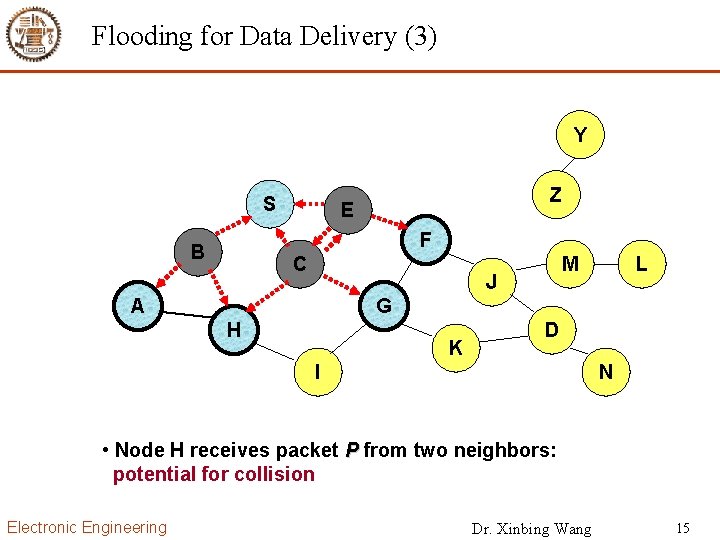
Flooding for Data Delivery (3) Y S Z E F B C M J A L G H K D I N • Node H receives packet P from two neighbors: potential for collision Electronic Engineering Dr. Xinbing Wang 15
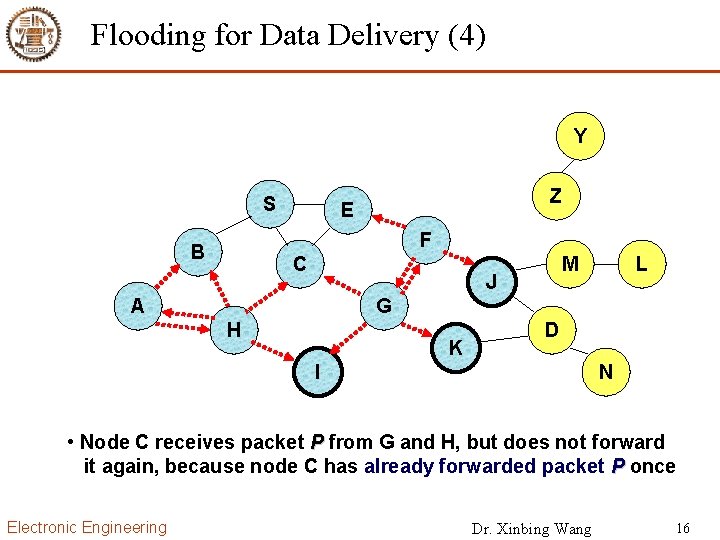
Flooding for Data Delivery (4) Y S Z E F B C M J A L G H K D I N • Node C receives packet P from G and H, but does not forward it again, because node C has already forwarded packet P once Electronic Engineering Dr. Xinbing Wang 16
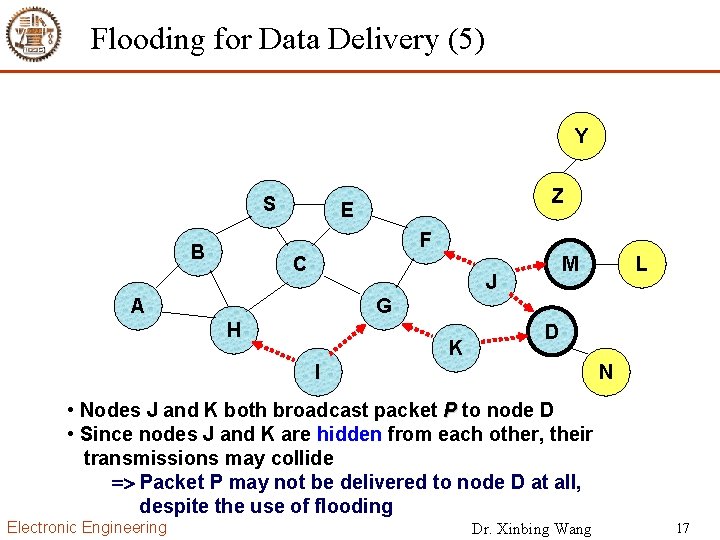
Flooding for Data Delivery (5) Y S Z E F B C M J A L G H K D I N • Nodes J and K both broadcast packet P to node D • Since nodes J and K are hidden from each other, their transmissions may collide => Packet P may not be delivered to node D at all, despite the use of flooding Electronic Engineering Dr. Xinbing Wang 17
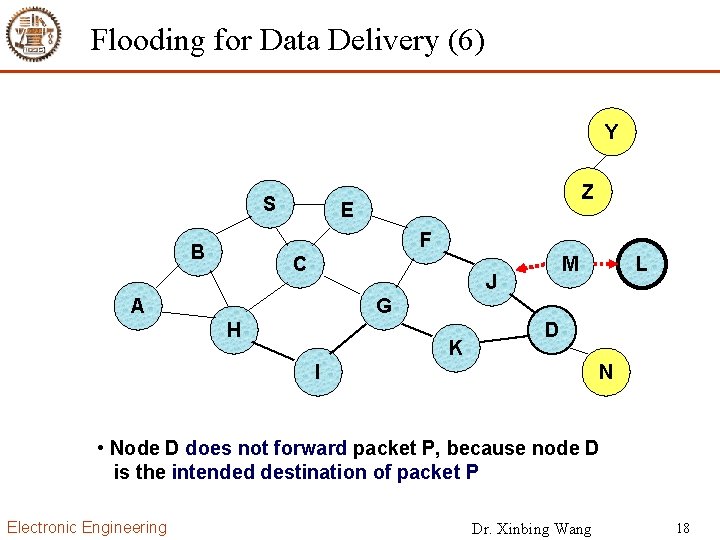
Flooding for Data Delivery (6) Y S Z E F B C M J A L G H K D I N • Node D does not forward packet P, because node D is the intended destination of packet P Electronic Engineering Dr. Xinbing Wang 18
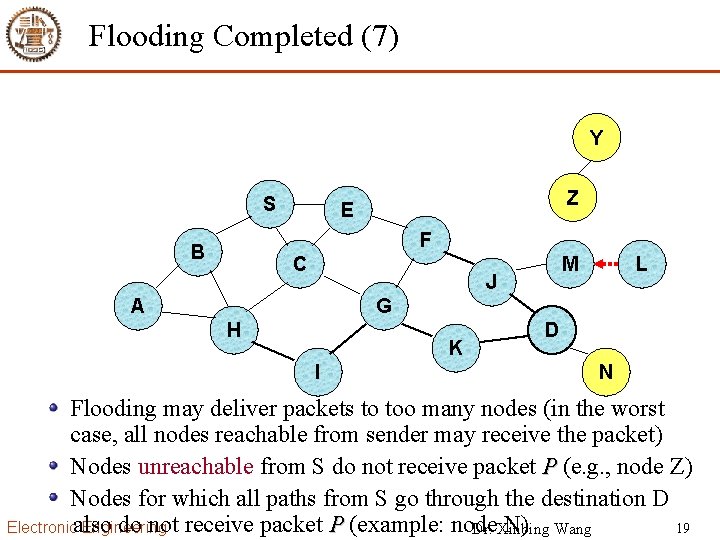
Flooding Completed (7) Y S Z E F B C M J A L G H K I D N Flooding may deliver packets to too many nodes (in the worst case, all nodes reachable from sender may receive the packet) Nodes unreachable from S do not receive packet P (e. g. , node Z) Nodes for which all paths from S go through the destination D do not receive packet P (example: node N) Wang Electronicalso Engineering 19 Dr. Xinbing
Flooding for Data Delivery: Advantages Simplicity May be more efficient than other protocols when rate of information transmission is low enough that the overhead of explicit route discovery/maintenance incurred by other protocols is relatively higher – this scenario may occur, for instance, when nodes transmit small data packets relatively infrequently, and many topology changes occur between consecutive packet transmissions Potentially higher reliability of data delivery – Because packets may be delivered to the destination on multiple paths Electronic Engineering Dr. Xinbing Wang 20
Flooding for Data Delivery: Disadvantages Potentially, very high overhead – Data packets may be delivered to TOO many nodes who do not need to receive them Potentially lower reliability of data delivery – Flooding uses broadcasting -- hard to implement reliable broadcast delivery without significantly increasing overhead Broadcasting in IEEE 802. 11 MAC is unreliable – In our example, nodes J and K may transmit to node D simultaneously, resulting in loss of the packet in this case, destination would not receive the packet at all Electronic Engineering Dr. Xinbing Wang 21
Flooding of Control Packets Many protocols perform (potentially limited) flooding of control packets, instead of data packets The control packets are used to discover routes Discovered routes are subsequently used to send data packet(s) Overhead of control packet flooding is amortized over data packets transmitted between consecutive control packet floods Electronic Engineering Dr. Xinbing Wang 22
Part 4: Other Wireless Networks Ad hoc networks – – – Mobility and routing Flooding routing algorithm Dynamic source routing (DSR) Ad hoc On-Demand Distance Vector Routing (AODV) Location-Aided routing (LAR) Quality of Service (Qo. S) in ad hoc networks Sensor networks Wireless PANs Electronic Engineering Dr. Xinbing Wang 23
![Dynamic Source Routing Y DATA[S, E, F, J, D] S B A Z E Dynamic Source Routing Y DATA[S, E, F, J, D] S B A Z E](http://slidetodoc.com/presentation_image_h/0b0e6f4eb2b266a32d1f980acea4b8d2/image-24.jpg)
Dynamic Source Routing Y DATA[S, E, F, J, D] S B A Z E F C J G H I K M L D N When S sends a data packet to D, the entire route is included in the packet header Intermediate nodes use the source route embedded in the packet’s header to determine to whom the packet should be forwarded Different packets may have different routes, even they have the same source and destination Hence called dynamic source routing Electronic Engineering Dr. Xinbing Wang 24
Assumptions in DSR All nodes are willing to forward packets for other nodes in the network The diameter of an ad-hoc network will not be too large – Packet header will be larger than the payload if route is very longer The node’s speed is moderate – Local route cache will become stale if node’s speed is high All nodes are overhearing (promiscuous) – No energy saving Electronic Engineering Dr. Xinbing Wang 25
DSR: Operation When node S wants to send a packet to node D, but does not know a route to D, node S initiates a route discovery Source node S floods Route Request (RREQ) Each node appends own identifier when forwarding RREQ Node S on receiving RREP, caches the route included in the RREP When node S sends a data packet to D, the entire route is included in the packet header – hence the name source routing Intermediate nodes use the source route included in a packet to determine to whom a packet should be forwarded Electronic Engineering Dr. Xinbing Wang 26
Route Discovery When to perform a Route Discovery ? Every route request packet (RREQ) contains <target address, initiator address, route record, request ID> Each node maintains a list of the < initiator address, request ID> When a node Y receives a RREQ – Discards the route request packet if < initiator address, request ID> is in its list – Return a route reply packet which contains a route from initiator to target If Y is target If Y has an entry in its route cache for a route to target – Append itself address to the route record in RREQ and re-broadcast RREQ Electronic Engineering Dr. Xinbing Wang 27
![Route Reply in DSR Y S E Z RREP [S, E, F, J, D] Route Reply in DSR Y S E Z RREP [S, E, F, J, D]](http://slidetodoc.com/presentation_image_h/0b0e6f4eb2b266a32d1f980acea4b8d2/image-28.jpg)
Route Reply in DSR Y S E Z RREP [S, E, F, J, D] F B C M J A L G H D K I N Represents RREP control message Electronic Engineering Dr. Xinbing Wang 28
More Details of Route Reply in DSR Destination D on receiving the first RREQ, sends a Route Reply (RREP) RREP includes the route from S to D Route Reply can be sent to S by reversing the route in Route Request (RREQ) only if links are guaranteed to be bi-directional – To ensure this, RREQ should be forwarded only if it received on a link that is known to be bi-directional If unidirectional (asymmetric) links are allowed, then RREP may need a route discovery for S from node D – Unless node D already knows a route to node S – If a route discovery is initiated by D for a route to S, then the Route Reply is piggybacked on the Route Request from D. If IEEE 802. 11 MAC is used to send data, then links have to be bidirectional (since Ack is used) Electronic Engineering Dr. Xinbing Wang 29
![Example of Route Maintenance Y Route Error Packet : RERR [J-D] S Z E Example of Route Maintenance Y Route Error Packet : RERR [J-D] S Z E](http://slidetodoc.com/presentation_image_h/0b0e6f4eb2b266a32d1f980acea4b8d2/image-30.jpg)
Example of Route Maintenance Y Route Error Packet : RERR [J-D] S Z E F B C M J A L G H K D I N • J sends a route error to S along route J-F-E-S when it finds link [J-D] broken • Nodes hearing RERR update their route cache to remove all invalid routes related with link J-D Electronic Engineering Dr. Xinbing Wang 30
![More Details on Route Maintenance Route [S, node-1, node-2, ……, node-k, D] Hop-by-hop maintenance More Details on Route Maintenance Route [S, node-1, node-2, ……, node-k, D] Hop-by-hop maintenance](http://slidetodoc.com/presentation_image_h/0b0e6f4eb2b266a32d1f980acea4b8d2/image-31.jpg)
More Details on Route Maintenance Route [S, node-1, node-2, ……, node-k, D] Hop-by-hop maintenance ( MAC or network layer) – How to find link [node-i, node(i+1)] is down ? Utilize MAC level acknowledgement Passive acknowledge (overhearing node (i+1) re-transmission) Insert a bit in packet header to ask an explicit acknowledgement from node (i+1) – How to send route error packet to S? Use the reverse route [node-i, node(i-1), ……, node-1, S] Use node-i route cache to get a route to S Piggybacking route error packet in route discovery packet S End-to-end maintenance (transport or application layer): D sends ACK to S to indicate the route status. But S does not know which link is broken Electronic Engineering Dr. Xinbing Wang 31
Route Optimization: Route Caching Each node caches a new route it learns by any means When node S finds route [S, E, F, J, D] to node D, node S also learns route [S, E, F] to node F When node K receives Route Request [S, C, G] destined for node D, node K learns route [K, G, C, S] to node S When node F forwards Route Reply RREP [S, E, F, J, D], node F learns route [F, J, D] to node D When node E forwards Data [S, E, F, J, D] it learns route [E, F, J, D] to node D A node may also learn a route when it overhears Data Problem: Stale caches may increase overheads Electronic Engineering Dr. Xinbing Wang 32
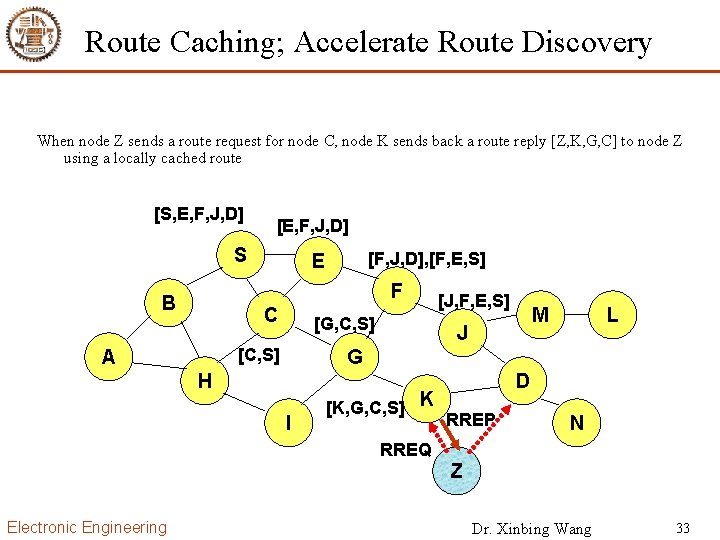
Route Caching; Accelerate Route Discovery When node Z sends a route request for node C, node K sends back a route reply [Z, K, G, C] to node Z using a locally cached route [S, E, F, J, D] [E, F, J, D] S [F, J, D], [F, E, S] E F B C [G, C, S] [C, S] A [J, F, E, S] M J L G H I [K, G, C, S] K D RREP N RREQ Z Electronic Engineering Dr. Xinbing Wang 33
![Route Caching: Reduce Propagation of Route Requests [S, E, F, J, D] [E, F, Route Caching: Reduce Propagation of Route Requests [S, E, F, J, D] [E, F,](http://slidetodoc.com/presentation_image_h/0b0e6f4eb2b266a32d1f980acea4b8d2/image-34.jpg)
Route Caching: Reduce Propagation of Route Requests [S, E, F, J, D] [E, F, J, D] S [F, J, D], [F, E, S] E F B C [G, C, S] [C, S] A [J, F, E, S] M J G H I [K, G, C, S] K D RREP L [D, K, G, , C] N RREQ Z Route Replies (RREP) from node K and D limit flooding of RREQ. Electronic Engineering Dr. Xinbing Wang 34
DSR: Advantages Routes maintained only between nodes who need to communicate – reduces overhead of route maintenance Route caching can further reduce route discovery overhead A single route discovery may yield many routes to the destination, due to intermediate nodes replying from local caches – due to intermediate nodes replying from local caches Electronic Engineering Dr. Xinbing Wang 35
DSR: Disadvantages Packet header size grows with route length due to source routing: Inefficiency Flood of route requests may potentially reach all nodes in the network: RREQ flooding Potential collisions between route requests propagated by neighboring nodes – insertion of random delays before forwarding RREQ Increased contention if too many route replies come back due to nodes replying using their local cache – Route Reply Storm problem: Route Reply Storm Stale caches will lead to increased overhead Electronic Engineering Dr. Xinbing Wang 36
After Class Reading materials – Chapter 1 – Chapter 3 Exercise – Describe the difference between proactive routing and reactive routing – When and how flooding is used in ad hoc networks? – How is the loop-free ensured in on-demand routing protocol? Electronic Engineering Dr. Xinbing Wang 37
- Slides: 37