SYZYGY Engineering Mobile Networking MobileIP Mobile Networking Ad
SYZYGY Engineering Mobile Networking Mobile-IP Mobile Networking Ad Hoc Network (APC) WP-N 1 -IP-701 Latest available information as of 03/26/2006 Will Ivancic 1 © 2004 Syzygy Engineering – Will Ivancic
Outline SYZYGY Engineering • • • Mobile Networking Solutions Mobile-IPv 4 Operation (mip 4) Mobile-IPv 6 Operation (mip 6) Networks In Motion (nemo) Mobile Nodes and Multiple Interfaces in IPv 6 (monami 6) • Ad Hoc Networks 2 © 2004 Syzygy Engineering – Will Ivancic

What is Mobility? • Transportable – Telecommuter – Traveler – Relatively static once connected – Single point of connection – Connectivity • IPv 6 Autoconfiguration • VPN SYZYGY Engineering • Mobile – Mobile Devices • PDAs • Cell Phones – Mobile Networks • Trains • Planes • Automobiles – Connectivity • Mobile-IP • Networks in Motion (NEMO) • Ad Hoc Networks 3 © 2004 Syzygy Engineering – Will Ivancic
Mobile Networking Solutions SYZYGY Engineering • Routing Protocols – Route Optimization – Convergence Time – Sharing Infrastructure – who owns the network? • Mobile-IP – Route Optimization • Optimization for MIPv 6 • No Optimization for NEMOv 6 (Basic) • Optimization can be problematic for security (if reverse tunneling is required) – Convergence Time – Sharing Infrastructure – Security – Relatively Easy to Secure • Domain Name Servers – Route Optimization – Convergence Time – Reliability 4 Source – Will Ivancic
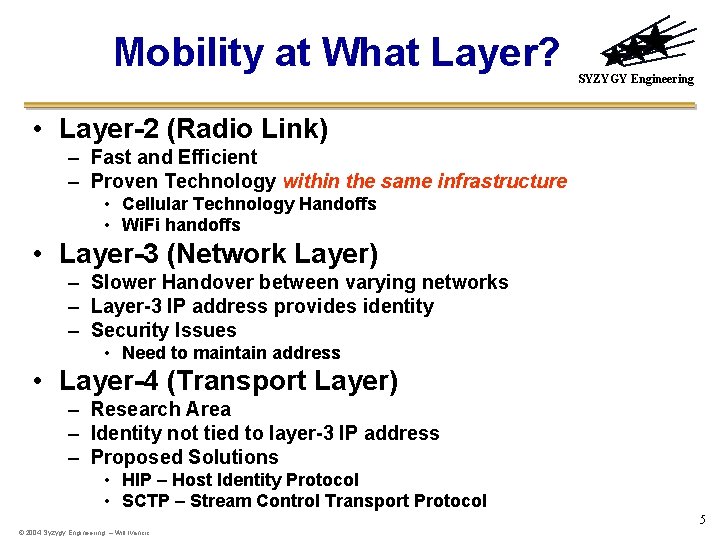
Mobility at What Layer? SYZYGY Engineering • Layer-2 (Radio Link) – Fast and Efficient – Proven Technology within the same infrastructure • Cellular Technology Handoffs • Wi. Fi handoffs • Layer-3 (Network Layer) – Slower Handover between varying networks – Layer-3 IP address provides identity – Security Issues • Need to maintain address • Layer-4 (Transport Layer) – Research Area – Identity not tied to layer-3 IP address – Proposed Solutions • HIP – Host Identity Protocol • SCTP – Stream Control Transport Protocol 5 © 2004 Syzygy Engineering – Will Ivancic
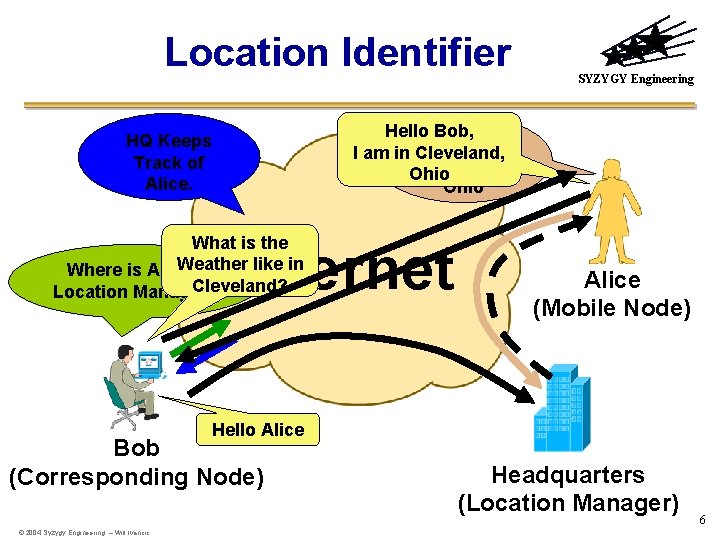
Location Identifier SYZYGY Engineering Hello Bob, I am in Cleveland, Ohio HQ Keeps Track of Alice. What is the Weather like in Where is Alice’s Cleveland? Location Manager? Internet Alice (Mobile Node) Hello Alice Bob (Corresponding Node) © 2004 Syzygy Engineering – Will Ivancic Headquarters (Location Manager) 6
SYZYGY Engineering Moblile-IP Operation IPv 4 7 © 2004 Syzygy Engineering – Will Ivancic

Mobile IPv 4 Header Considerations IPv 4 Header 20 bytes Version IHL Type of Service Identification Time to Live Protocol Total Length Flag s Fragment Offset Header Checksum Source Address Destination Address Options Padding SYZYGY Engineering • Source is always home network address! – Easy to secure due to consistent end-point! – But, results in topologically incorrect address when away from home. • Security Issue, Ingress and Egress Filtering • Reverse Tunneling – Fixes topologically incorrect addressing problem – Eases secure deployment. © 2004 Syzygy Engineering – Will Ivancic 8

Mobile-IP (IPv 4) using Foreign Agents Mobile Node “ ” Foreign Agent 143. 232. 48. 1 Home IP 128. 183. 103 Care-Off-Address 139. 88. 111. 50 Foreign Agent 139. 88. 111. 1 139. 88. 112. 1 NASA Glenn 143. 232. 48. 1 NASA Ames Internet or Intranet Corresponding Node 128. 183. 1 NASA Goddard Home Agent Bi-directional Tunnel if Reverse Tunneling Is specified. 9 Source – Will Ivancic
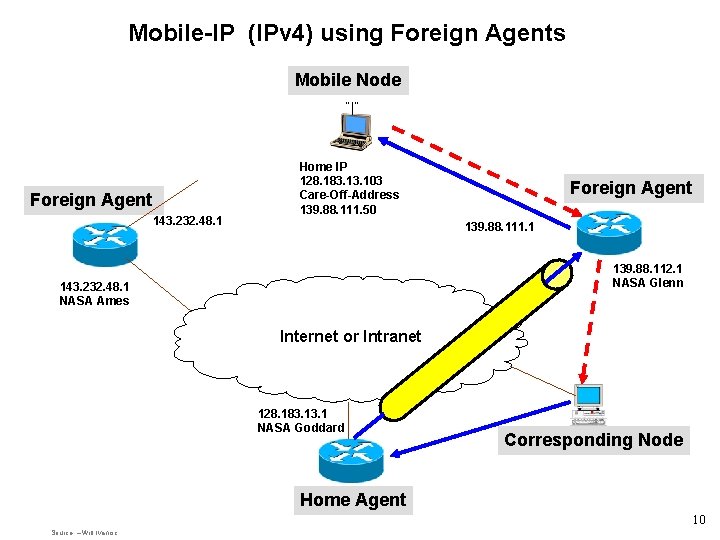
Mobile-IP (IPv 4) using Foreign Agents Mobile Node “ ” Foreign Agent 143. 232. 48. 1 Home IP 128. 183. 103 Care-Off-Address 139. 88. 111. 50 Foreign Agent 139. 88. 111. 1 139. 88. 112. 1 NASA Glenn 143. 232. 48. 1 NASA Ames Internet or Intranet 128. 183. 1 NASA Goddard Corresponding Node Home Agent 10 Source – Will Ivancic
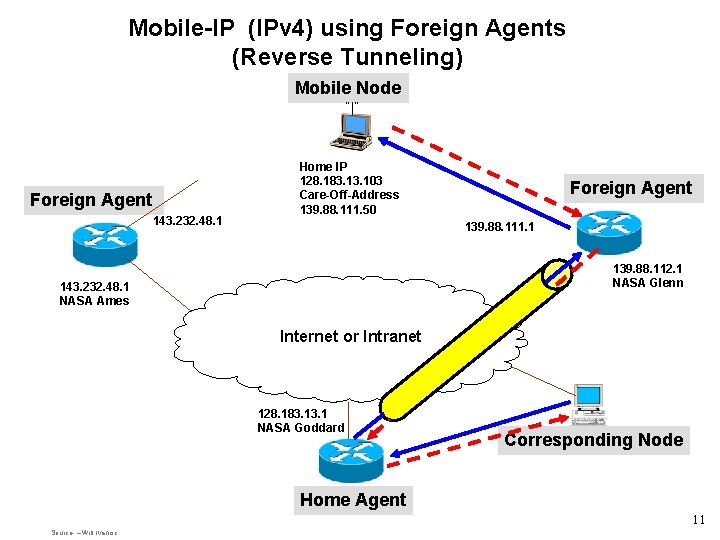
Mobile-IP (IPv 4) using Foreign Agents (Reverse Tunneling) Mobile Node “ ” Foreign Agent 143. 232. 48. 1 Home IP 128. 183. 103 Care-Off-Address 139. 88. 111. 50 Foreign Agent 139. 88. 111. 1 139. 88. 112. 1 NASA Glenn 143. 232. 48. 1 NASA Ames Internet or Intranet 128. 183. 1 NASA Goddard Corresponding Node Home Agent 11 Source – Will Ivancic
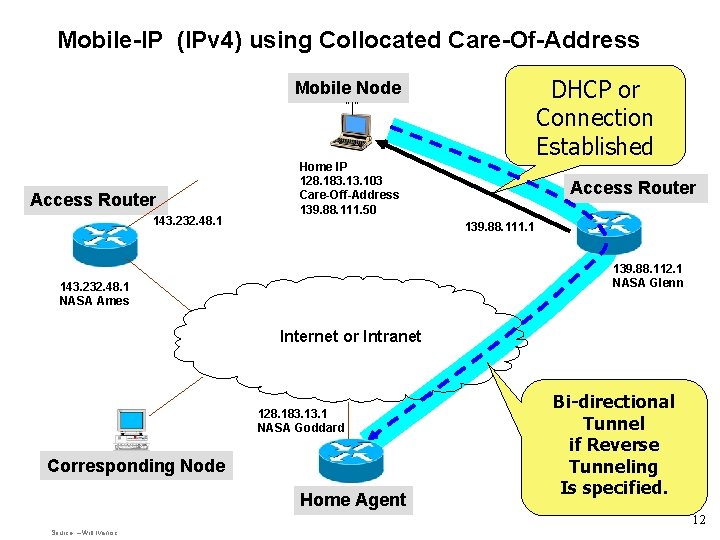
Mobile-IP (IPv 4) using Collocated Care-Of-Address DHCP or Connection Established Mobile Node “ ” Access Router 143. 232. 48. 1 Home IP 128. 183. 103 Care-Off-Address 139. 88. 111. 50 Access Router 139. 88. 111. 1 139. 88. 112. 1 NASA Glenn 143. 232. 48. 1 NASA Ames Internet or Intranet 128. 183. 1 NASA Goddard Corresponding Node Home Agent Bi-directional Tunnel if Reverse Tunneling Is specified. 12 Source – Will Ivancic
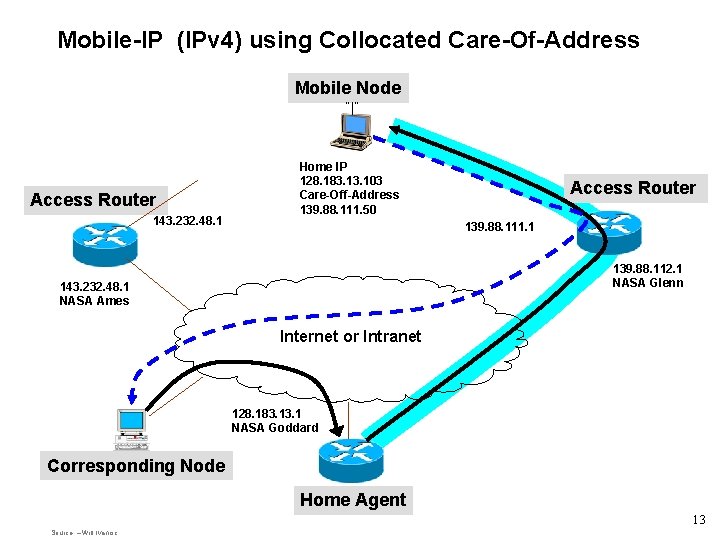
Mobile-IP (IPv 4) using Collocated Care-Of-Address Mobile Node “ ” Access Router 143. 232. 48. 1 Home IP 128. 183. 103 Care-Off-Address 139. 88. 111. 50 Access Router 139. 88. 111. 1 139. 88. 112. 1 NASA Glenn 143. 232. 48. 1 NASA Ames Internet or Intranet 128. 183. 1 NASA Goddard Corresponding Node Home Agent 13 Source – Will Ivancic
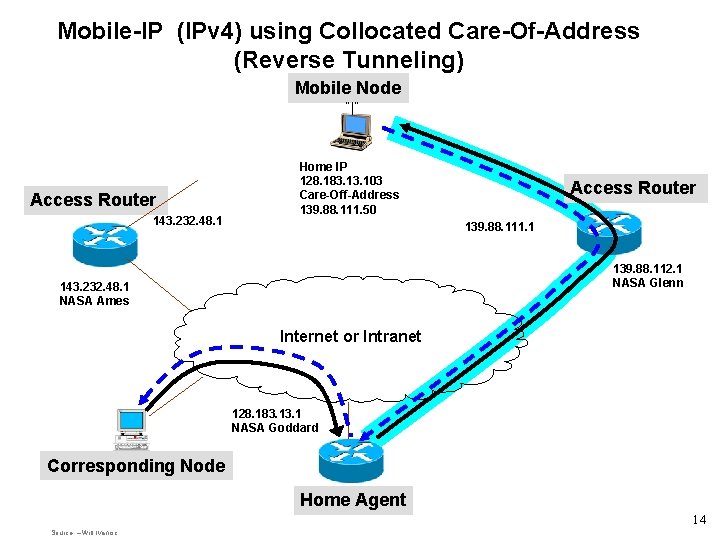
Mobile-IP (IPv 4) using Collocated Care-Of-Address (Reverse Tunneling) Mobile Node “ ” Access Router 143. 232. 48. 1 Home IP 128. 183. 103 Care-Off-Address 139. 88. 111. 50 Access Router 139. 88. 111. 1 139. 88. 112. 1 NASA Glenn 143. 232. 48. 1 NASA Ames Internet or Intranet 128. 183. 1 NASA Goddard Corresponding Node Home Agent 14 Source – Will Ivancic
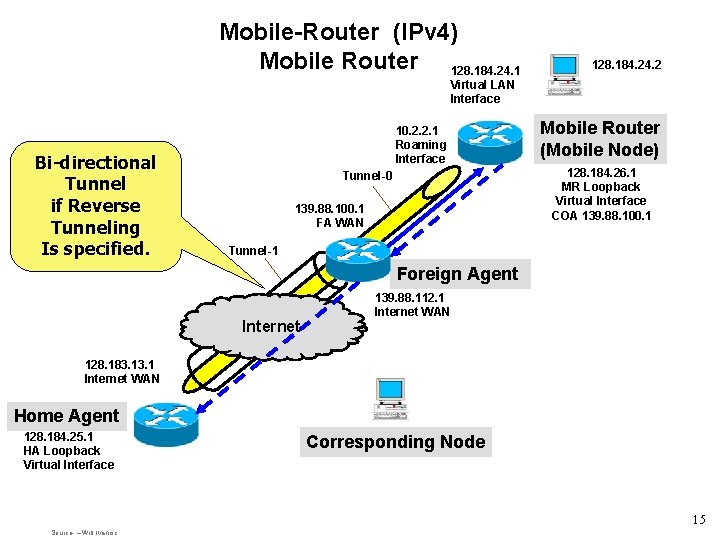
Mobile-Router (IPv 4) Mobile Router 128. 184. 24. 1 128. 184. 2 Virtual LAN Interface Bi-directional Tunnel if Reverse Tunneling Is specified. 10. 2. 2. 1 Roaming Interface Tunnel-0 139. 88. 100. 1 FA WAN Mobile Router (Mobile Node) 128. 184. 26. 1 MR Loopback Virtual Interface COA 139. 88. 100. 1 Tunnel-1 Foreign Agent Internet 139. 88. 112. 1 Internet WAN 128. 183. 1 Internet WAN Home Agent 128. 184. 25. 1 HA Loopback Virtual Interface Corresponding Node 15 Source – Will Ivancic
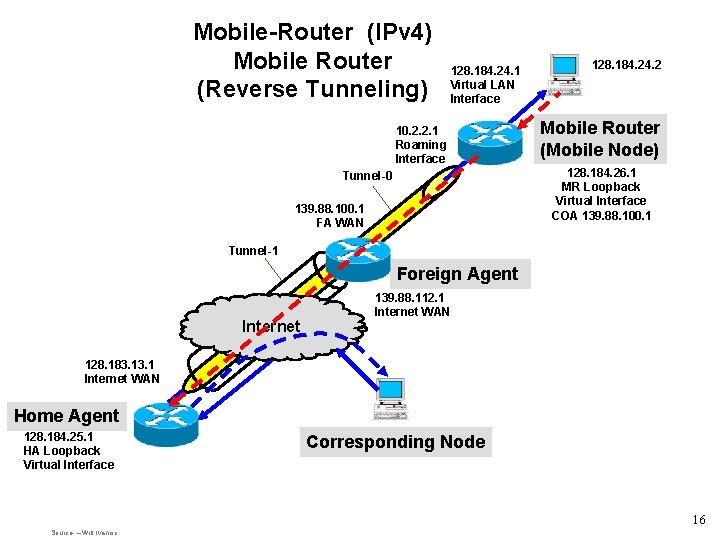
Mobile-Router (IPv 4) Mobile Router (Reverse Tunneling) 128. 184. 24. 1 Virtual LAN Interface 10. 2. 2. 1 Roaming Interface Tunnel-0 139. 88. 100. 1 FA WAN 128. 184. 2 Mobile Router (Mobile Node) 128. 184. 26. 1 MR Loopback Virtual Interface COA 139. 88. 100. 1 Tunnel-1 Foreign Agent Internet 139. 88. 112. 1 Internet WAN 128. 183. 1 Internet WAN Home Agent 128. 184. 25. 1 HA Loopback Virtual Interface Corresponding Node 16 Source – Will Ivancic

Mobile-Router (IPv 4) Collocated Care-Of-Address 128. 184. 24. 1 Virtual LAN Interface 128. 184. 2 Mobile Router (Mobile Node) 10. 2. 2. 1 Roaming Interface 128. 184. 26. 1 MR Loopback Virtual Interface COA 139. 88. 100. 1 Tunnel-0 139. 88. 100. 1 FA WAN Tunnel-1 Foreign Agent Internet 128. 183. 1 Internet WAN 139. 88. 112. 1 Internet WAN No Foreign Agent No Second Tunnel Home Agent 128. 184. 25. 1 HA Loopback Virtual Interface Corresponding Node 17 Source – Will Ivancic
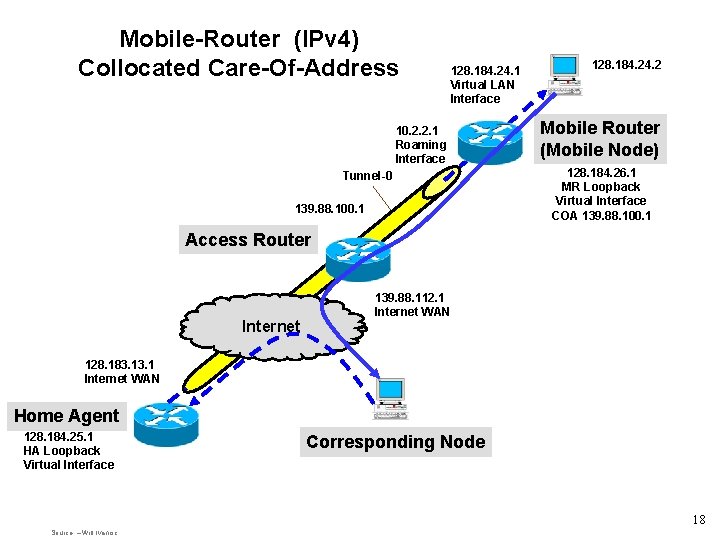
Mobile-Router (IPv 4) Collocated Care-Of-Address 128. 184. 24. 1 Virtual LAN Interface 10. 2. 2. 1 Roaming Interface Tunnel-0 139. 88. 100. 1 128. 184. 2 Mobile Router (Mobile Node) 128. 184. 26. 1 MR Loopback Virtual Interface COA 139. 88. 100. 1 Access Router Internet 139. 88. 112. 1 Internet WAN 128. 183. 1 Internet WAN Home Agent 128. 184. 25. 1 HA Loopback Virtual Interface Corresponding Node 18 Source – Will Ivancic
SYZYGY Engineering Mobile Networking Additional Features • Geographically Distributed Home Agents • Asymmetrical Pathing 19 Source – Will Ivancic
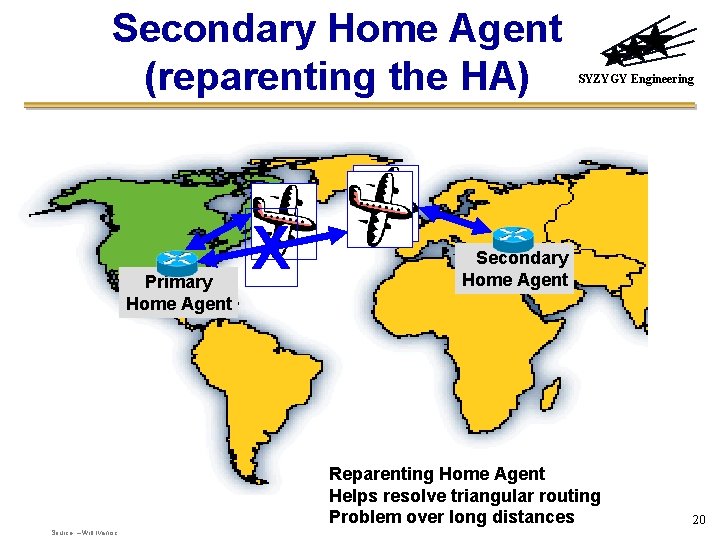
Secondary Home Agent (reparenting the HA) Primary Home Agent X SYZYGY Engineering Secondary Home Agent Reparenting Home Agent Helps resolve triangular routing Problem over long distances Source – Will Ivancic 20
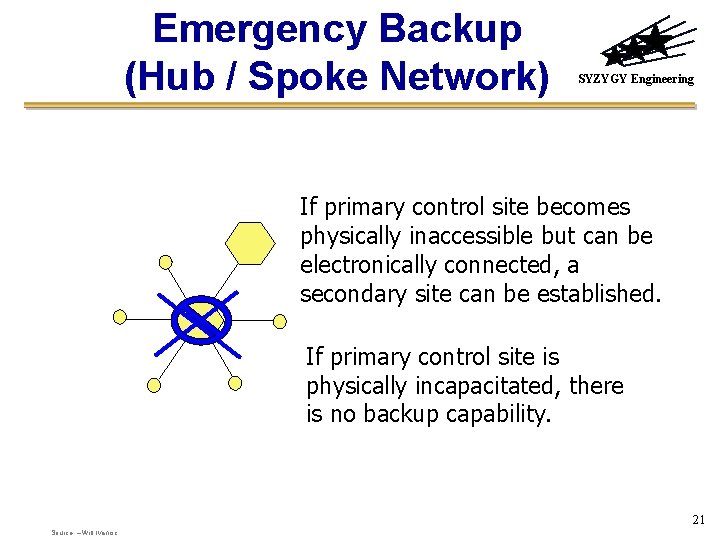
Emergency Backup (Hub / Spoke Network) SYZYGY Engineering If primary control site becomes physically inaccessible but can be electronically connected, a secondary site can be established. If primary control site is physically incapacitated, there is no backup capability. 21 Source – Will Ivancic
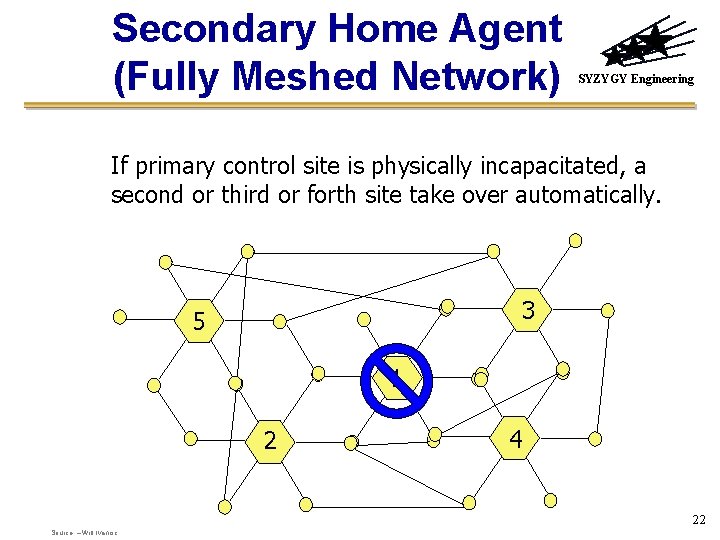
Secondary Home Agent (Fully Meshed Network) SYZYGY Engineering If primary control site is physically incapacitated, a second or third or forth site take over automatically. 3 5 1 2 4 22 Source – Will Ivancic
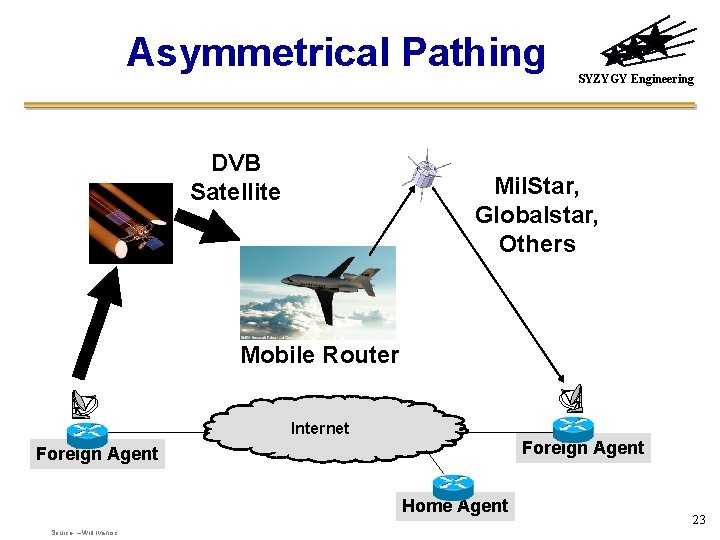
Asymmetrical Pathing DVB Satellite SYZYGY Engineering Mil. Star, Globalstar, Others Mobile Router Internet Foreign Agent Home Agent Source – Will Ivancic 23
SYZYGY Engineering Securing Mobile and Wireless Networks Some ways may be “better” than others! 24 Source – Will Ivancic
Constraints / Tools SYZYGY Engineering • Policy • Architecture • Protocols 25 Source – Will Ivancic
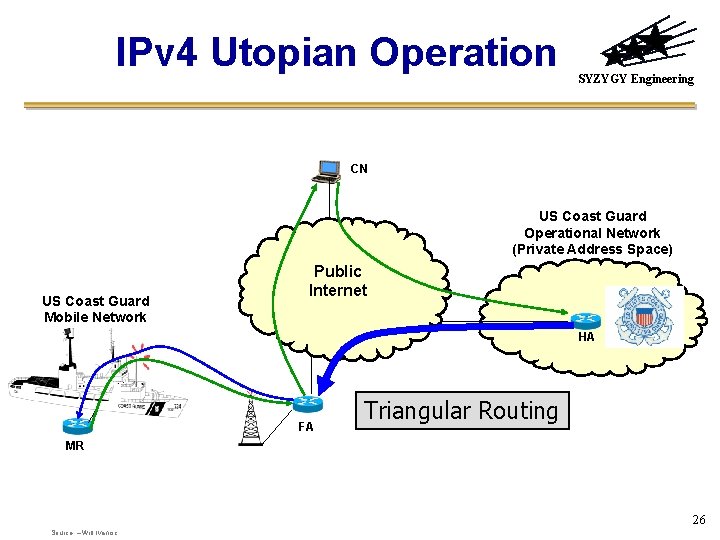
IPv 4 Utopian Operation SYZYGY Engineering CN US Coast Guard Operational Network (Private Address Space) US Coast Guard Mobile Network Public Internet HA FA Triangular Routing MR 26 Source – Will Ivancic
IPv 4 Mobile-IP Addressing SYZYGY Engineering • Source Address is obtained from – Foreign Agent – Static Collocated Care-of-Address (CCo. A) – DHCP via Access Router (Dynamic CCo. A) • Private Address space is not routable via the Open Internet • Topologically Incorrect Addresses should be blocked via Ingress or Egress filtering 27 Source – Will Ivancic
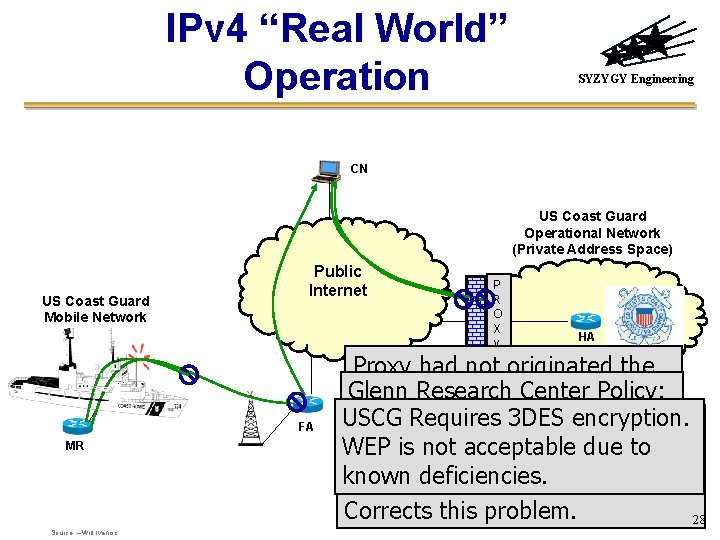
IPv 4 “Real World” Operation SYZYGY Engineering CN US Coast Guard Operational Network (Private Address Space) US Coast Guard Mobile Network Public Internet FA MR Source – Will Ivancic P R O X y HA Proxy had not originated the Glenn Research Center request; therefore, the. Policy: USCG Requires 3 DES encryption. No UDP, IPSec, etc… response is. Egress squelched. Ingress or. No Filtering stops WEP is notstopped acceptable due to Mobile-IP its tracks. Peer-to-peer networking Transmission due tointopologically known deficiencies. What’s your policy? becomes problematic at best. Incorrect source address. IPv 6 Corrects this problem. 28

Current Solution – Reverse Tunneling SYZYGY Engineering CN Adds Overhead and kills route optimization. US Coast Guard Mobile Network US Coast Guard Operational Network (Private Address Space) Public Internet FA MR P R O X y HA Anticipate similar problems for IPv 6. 29 Source – Will Ivancic
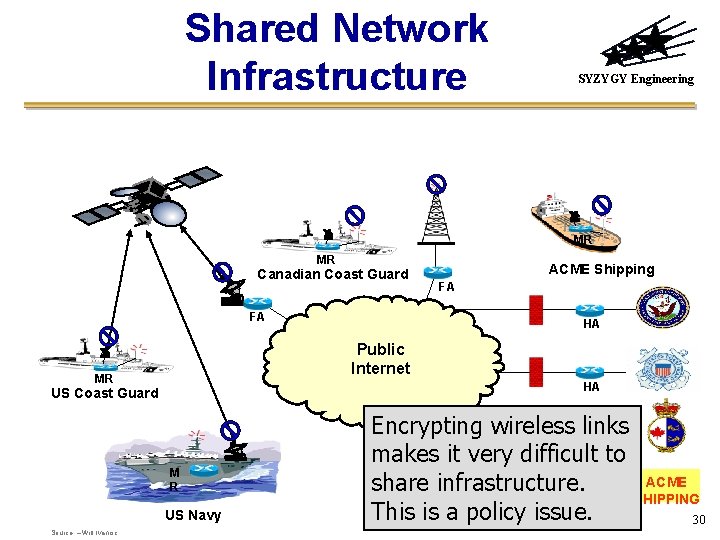
Shared Network Infrastructure SYZYGY Engineering MR MR Canadian Coast Guard FA FA HA Public Internet MR HA US Coast Guard M R US Navy Source – Will Ivancic ACME Shipping Encrypting wireless links HA makes it very difficult to ACME share infrastructure. SHIPPING HA This is a policy issue. 30
SYZYGY Engineering IPv 6 Mobile-IP 31 © 2004 Syzygy Engineering – Will Ivancic
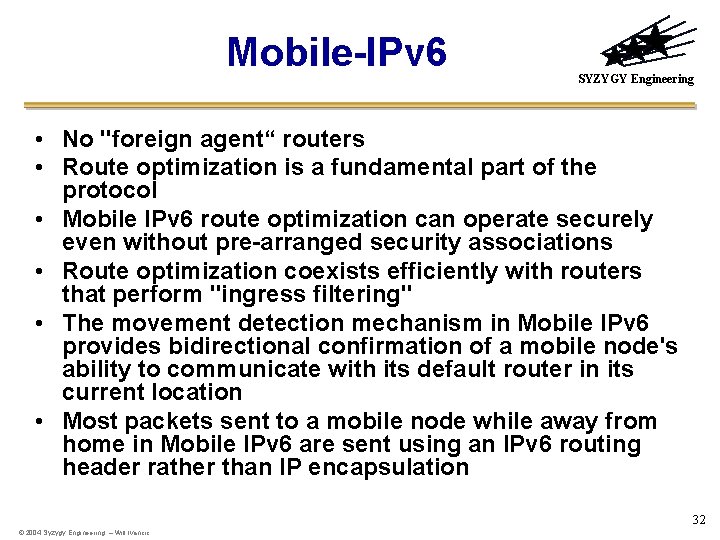
Mobile-IPv 6 SYZYGY Engineering • No "foreign agent“ routers • Route optimization is a fundamental part of the protocol • Mobile IPv 6 route optimization can operate securely even without pre-arranged security associations • Route optimization coexists efficiently with routers that perform "ingress filtering" • The movement detection mechanism in Mobile IPv 6 provides bidirectional confirmation of a mobile node's ability to communicate with its default router in its current location • Most packets sent to a mobile node while away from home in Mobile IPv 6 are sent using an IPv 6 routing header rather than IP encapsulation 32 © 2004 Syzygy Engineering – Will Ivancic

Mobile-IPv 6 SYZYGY Engineering • Modes for communications between the mobile node and a correspondent node – Bidirectional tunneling • Does not require Mobile IPv 6 support from the correspondent node – “Route Optimization“ • Requires the mobile node to register its current binding at the correspondent node. • Packets from the correspondent node can be routed directly to the care-of address of the mobile node 33 Source – Will Ivancic
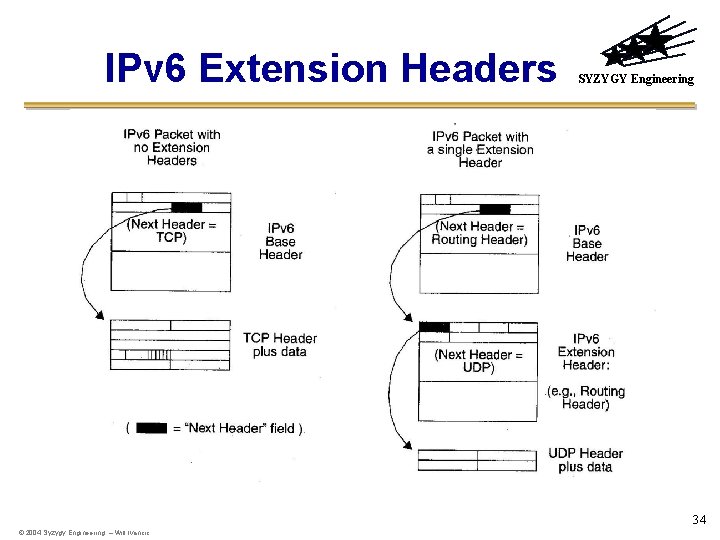
IPv 6 Extension Headers SYZYGY Engineering 34 © 2004 Syzygy Engineering – Will Ivancic
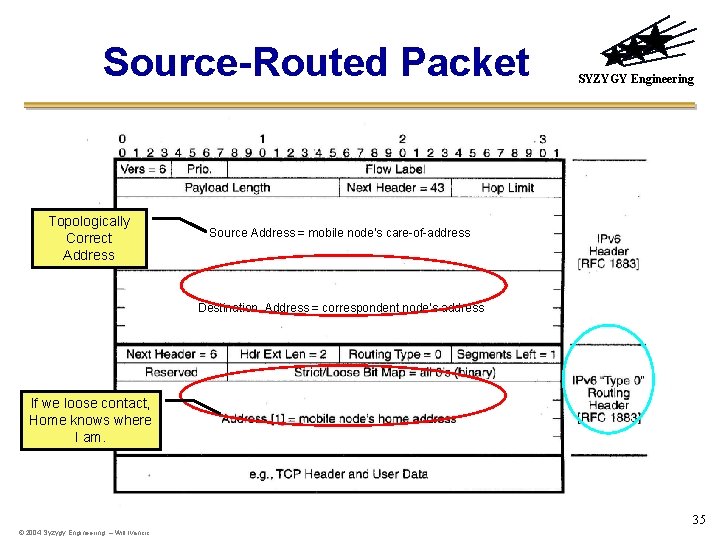
Source-Routed Packet Topologically Correct Address SYZYGY Engineering Source Address = mobile node’s care-of-address Destination Address = correspondent node’s address If we loose contact, Home knows where I am. 35 © 2004 Syzygy Engineering – Will Ivancic

Routing in Mobile IPv 6 SYZYGY Engineering Correspondent which knows the care-of address Mobile Node “visiting” a foreign link Source Routing Tunneling Home Agent Correspondent which does not know the care -of address 36
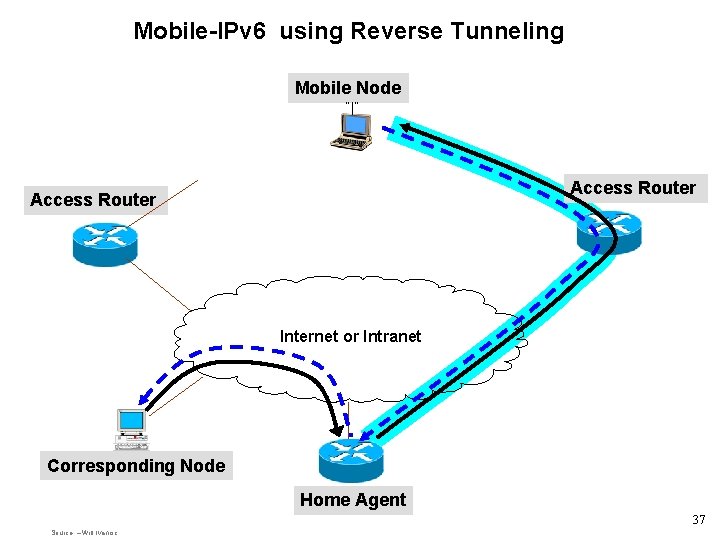
Mobile-IPv 6 using Reverse Tunneling Mobile Node “ ” Access Router Internet or Intranet Corresponding Node Home Agent 37 Source – Will Ivancic
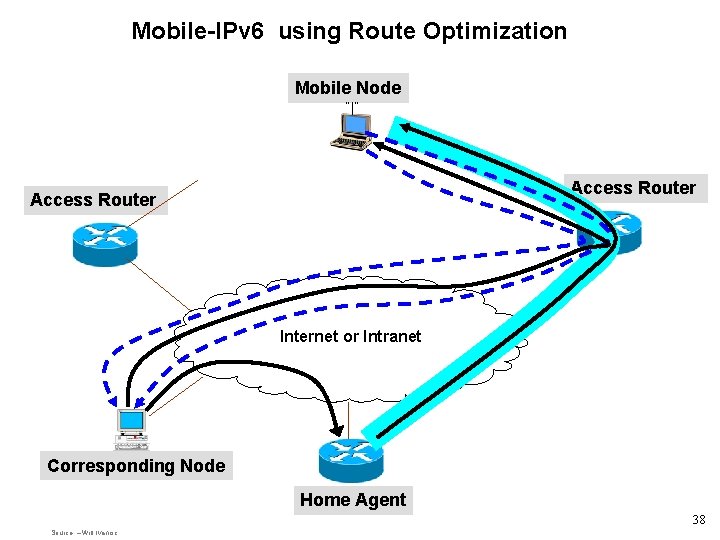
Mobile-IPv 6 using Route Optimization Mobile Node “ ” Access Router Internet or Intranet Corresponding Node Home Agent 38 Source – Will Ivancic
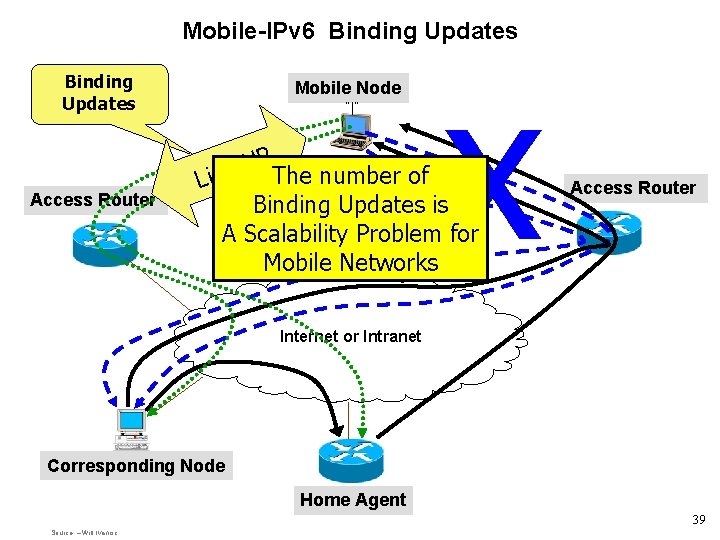
Mobile-IPv 6 Binding Updates Access Router Mobile Node “ ” x P U k The number of Lin Binding Updates is A Scalability Problem for Mobile Networks Access Router Internet or Intranet Corresponding Node Home Agent 39 Source – Will Ivancic
Mobile IPv 6 Security SYZYGY Engineering • Binding Updates use IPsec extension headers, or by the use of the Binding Authorization Data option • Prefix discovery is protected through the use of IPsec extension headers • Mechanisms related to transporting payload packets - such as the Home Address destination option and type 2 routing header have been specified in a manner which restricts their use in attacks 40 Source – Will Ivancic

SYZYGY Engineering NEMO NEtworks in Motion http: //www. ietf. org/html. charters/nemocharter. html http: //www. nal. motlabs. com/nemo/ 41 Source – Will Ivancic
Networks In Motion (NEMO) SYZYGY Engineering • Working Group established in IETF in December 2002 • Concerned with managing the mobility of an entire network, which changes, as a unit, its point of attachment to the Internet and thus its reachability in the topology. 42 Source – Will Ivancic
Goals SYZYGY Engineering • Standardizing some basic support mechanisms based on the bidirectional tunneling approach – Competed January 2005 • Study the possible approaches and issues with providing more optimal routing – Ongoing as of January 2006 43 Source – Will Ivancic
Network Mobility (NEMO) Basic Support Protocol (RFC 3963) SYZYGY Engineering • The basic solution MUST use bi-directional tunnels • MNNs MUST be reachable at a permanent IP address and name. • MUST maintain continuous sessions (both unicast and multicast) between MNNs and arbitrary CNs after IP handover of (one of) the MRs. • The solution MUST not require modifications to any node other than MRs and HAs. • The solution MUST support fixed nodes, mobile hosts and mobile routers in the mobile network. • The solution MUST not prevent the properation of Mobile IPv 6 (i. e. the solution MUST support MIPv 6 -enabled MNNs and MUST also allow MNNs to receive and process Binding Updates from arbitrary Mobile Nodes. ) • The solution MUST treat all the potential configurations the same way (whatever the number of subnets, MNNs, nested levels of MRs, egress interfaces, . . . ) • The solution MUST support mobile networks attaching to other mobile networks (nested mobile networks). 44 Source – Will Ivancic

Work In Progress • • SYZYGY Engineering Route Optimization Load Sharing (monami) Policy Based Routing (monami) Multiple Home Agents from different Service Providers – Security Issues – Desirable for some applications (i. e. air traffic control, airline maintenance, entertainment) 45 Source – Will Ivancic

Basic Mobile Network Support for IPv 6 Mobile Network Binding Nodes Update Mobile Network P Access Router U k n i L x Access Router Internet or Intranet Corresponding Node Home Agent Source – Will Ivancic 46

SYZYGY Engineering Mobile Nodes and Multiple Interfaces in IPv 6 (monami 6) 47
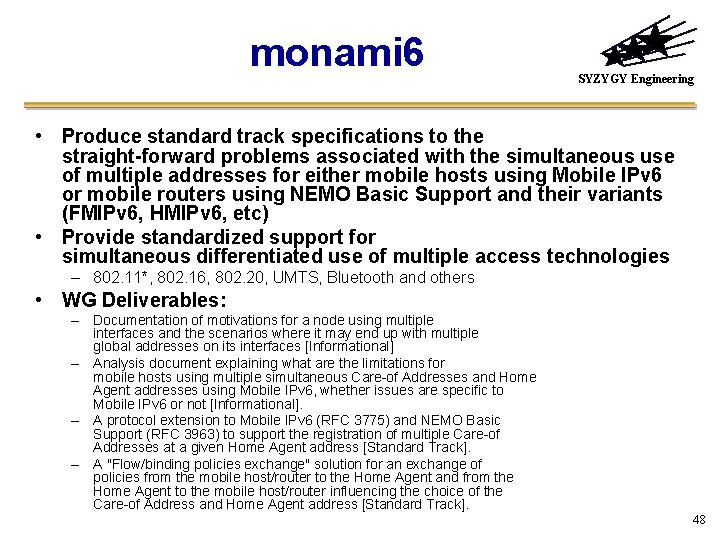
monami 6 SYZYGY Engineering • Produce standard track specifications to the straight-forward problems associated with the simultaneous use of multiple addresses for either mobile hosts using Mobile IPv 6 or mobile routers using NEMO Basic Support and their variants (FMIPv 6, HMIPv 6, etc) • Provide standardized support for simultaneous differentiated use of multiple access technologies – 802. 11*, 802. 16, 802. 20, UMTS, Bluetooth and others • WG Deliverables: – Documentation of motivations for a node using multiple interfaces and the scenarios where it may end up with multiple global addresses on its interfaces [Informational] – Analysis document explaining what are the limitations for mobile hosts using multiple simultaneous Care-of Addresses and Home Agent addresses using Mobile IPv 6, whether issues are specific to Mobile IPv 6 or not [Informational]. – A protocol extension to Mobile IPv 6 (RFC 3775) and NEMO Basic Support (RFC 3963) to support the registration of multiple Care-of Addresses at a given Home Agent address [Standard Track]. – A "Flow/binding policies exchange" solution for an exchange of policies from the mobile host/router to the Home Agent and from the Home Agent to the mobile host/router influencing the choice of the Care-of Address and Home Agent address [Standard Track]. 48
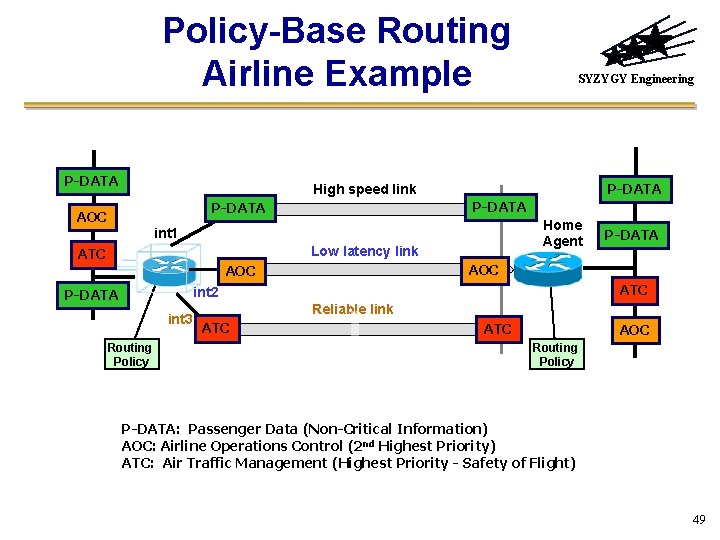
Policy-Base Routing Airline Example P-DATA SYZYGY Engineering P-DATA High speed link P-DATA AOC Home Agent int 1 Low latency link ATC AOC ATC int 2 P-DATA int 3 Routing Policy P-DATA Reliable link ATC AOC Routing Policy P-DATA: Passenger Data (Non-Critical Information) AOC: Airline Operations Control (2 nd Highest Priority) ATC: Air Traffic Management (Highest Priority - Safety of Flight) 49
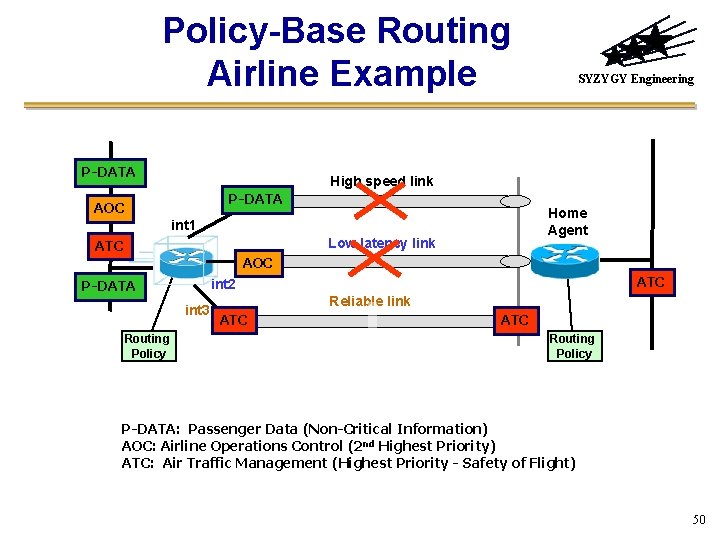
Policy-Base Routing Airline Example P-DATA SYZYGY Engineering High speed link P-DATA AOC Home Agent int 1 Low latency link ATC AOC int 3 Routing Policy ATC int 2 P-DATA Reliable link ATC Routing Policy P-DATA: Passenger Data (Non-Critical Information) AOC: Airline Operations Control (2 nd Highest Priority) ATC: Air Traffic Management (Highest Priority - Safety of Flight) 50
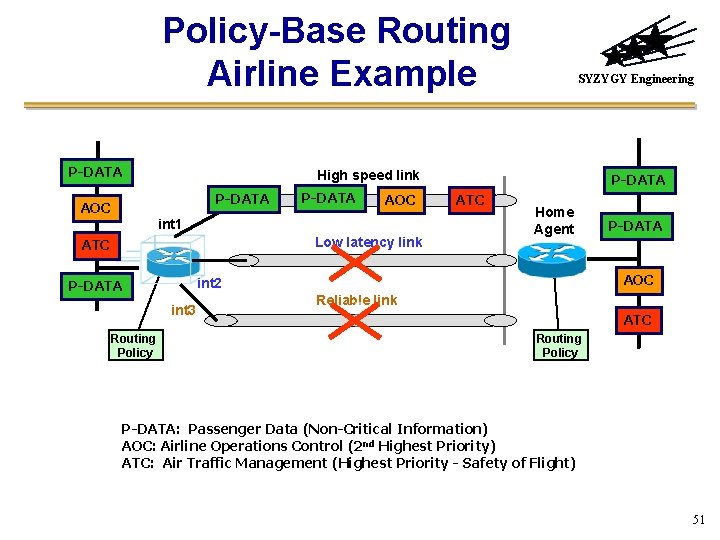
Policy-Base Routing Airline Example P-DATA SYZYGY Engineering High speed link P-DATA AOC int 1 Low latency link ATC P-DATA ATC Home Agent AOC int 2 P-DATA int 3 Routing Policy P-DATA Reliable link ATC Routing Policy P-DATA: Passenger Data (Non-Critical Information) AOC: Airline Operations Control (2 nd Highest Priority) ATC: Air Traffic Management (Highest Priority - Safety of Flight) 51
SYZYGY Engineering Mobile Ad Hoc Networks (MANET) 52 © 2004 Syzygy Engineering – Will Ivancic
MANET Characteristics SYZYGY Engineering • What is Mobile Ad-Hoc Networking (MANET) – Self-configuring and self-organizing network of mobile nodes usually connected via wireless links – Consists of mobile platforms / nodes (e. g. , a router with multiple hosts) which are free to move about arbitrarily. – Initial research and development based on mutual trust and cooperation – MANET routing is a layer-3, network layer technology. • Dynamic, changing, random, multi-hop topologies may require traversing multiple links to reach a destination • May have frequent network partitions and merging • Routing may change because of mobility (or wireless link dynamics – fading) • Routing functionality need to support robust and efficient operation • May require energy-constrained operation Source: Albert Young - Boeing 53

MANET Characteristics SYZYGY Engineering • Bandwidth constrained, variable capacity wireless links • Effective throughput is much less than a radio maximum transmission rate after accounting for the effects of multiple access, fading, noise, propagation path loss and interference • Limited physical security – Increased possibility of eavesdropping, spoofing, and denial-of-service attacks • Ad-hoc network clusters can operate autonomously or be attached at some point(s) to the fixed Internet –Stub network • The decentralized nature of network control in MANETs provides additional robustness against the single points of failure of more centralized approaches. • Equipped with wireless transceivers using antennas which may be omni-directional (broadcast), directional (point-topoint), possibly electronically steerable or a combination. Source: Albert Young - Boeing 54
Applications SYZYGY Engineering • Sensor Webs – Forest Fires Monitoring – Pollution Monitoring – Environmental Monitoring • Inexpensive alternatives or enhancements to cellbased mobile network infrastructures. • Military networking for robust, IP-compliant data services within mobile wireless communication networks consist of highly-dynamic autonomous topology segments. • Homeland Security – Scenarios requiring rapidly-deployable communications with survivable, efficient dynamic networking 55 © 2004 Syzygy Engineering – Will Ivancic
Status of MANET SYZYGY Engineering • Defense Programs are extremely interested in MANETs – Self-Organizing, robust, self-healing – Major research funding source. • IETF MANET working – Promoting a few “experimental” deployments (a reactive and a proactive routing technique) – Using mature components from previous work on experimental reactive and proactive protocols, the WG will develop two Standards track routing protocol specifications: • Reactive MANET Protocol (RMP) • Proactive MANET Protocol (PMP) – Develop a scoped forwarding protocol that can efficiently flood data packets to all participating MANET nodes. The primary purpose of this mechanism is a simplified best effort multicast forwarding function. 56 © 2004 Syzygy Engineering – Will Ivancic
Deployments (Sampling – Many others are available) SYZYGY Engineering • Dynamic MANET On-demand (DYMO) routing protocol – http: //moment. cs. ucsb. edu/dymo/index. php • Ad hoc On Demand Distance Vector (AODV) – http: //www. nmsl. cs. ucsb. edu/~krishna/aodv-linksys/ – http: //w 3. antd. nist. gov/wctg/aodv_kernel/ – http: //crl. se/? go=aodv 6 • Optimized Link State Routing Protocol (OLSR) – Navy Research Lab, INRIA (fr), NIIGATA (jp), GRC, LRI (fr), Communication Research Centre in Canada, Uni. K University • URL for all sources: http: //hipercom. inria. fr/olsr/#code • http: //www. olsr. org/ • Dynamic Source Routing (DSR) – http: //www. monarch. cs. rice. edu/dsr-impl. html – http: //pdos. csail. mit. edu/grid/software. html#install – http: //core. it. uu. se/Ad. Hoc/Dsr. UUImpl 57
Routing Standards and Research SYZYGY Engineering • One Size Does Not Fit All! No single routing protocol works well in all environments – Which approach to choose depends on the traffic and mobility patterns, and Qo. S requirements – Proactive routing protocols Optimized Link State Routing (OLSR), Open Shortest Path First (OSPF) extension • Applicable for relatively stable networks • Suitable for large and dense networks – Reactive routing protocol Ad Hoc On-Demand Distance Vector (AODV), Dynamic Source Routing protocol (DSR), Dynamic MANET On-demand (DYMO) • Enables reactive, multihop routing between participating nodes that wish to communicate. • Applicable to highly dynamic networks – Motivation is for interoperability with the wired – Modification (e. g. neighbor establishment) and scalability enhancements to OSPFv 3 that is designed for IPv 6 – Specifically in reducing the size of Hello packets, and optimizing flooding of routing updates. 58 © 2004 Syzygy Engineering – Will Ivancic
Benefits of IPv 6 in MANETs SYZYGY Engineering • IPv 6 couple together with MANET offers ease and speed of deployment, and decreased dependence on infrastructure • Provide End-to-End Global Addressing • Autoconfiguration of link-local addresses • Possible End-to-End Security with integrated IPSec • Support for source routing • Full support of mobility • No broadcast traffic to hamper wireless network efficiency • Potential support of real-time delivery of data with Qo. S • Potential to utilize Anycast addressing 59 © 2004 Syzygy Engineering – Will Ivancic
Challenges SYZYGY Engineering • Denial of Service – DAD Do. S, Uncooperative Router, etc… – Neighbor Discovery trust and threats • Network Discovery – Reachback, DNS, Key Manager • Security – – IPSec / HAIPES tunnel end-points Security Policies in a dynamic environment Is layer-2 encryption sufficient security? Insecure routing • Attackers may inject erroneous routing information to divert network traffic, or make routing inefficient • Key Management – Lack of key distribution mechanism – Hard to guarantee access to any particular node (e. g. obtain a secret key) 60 © 2004 Syzygy Engineering – Will Ivancic
Challenges SYZYGY Engineering • Duplicate Address Discovery – Not suitable for multi-hop ad hoc networks that have dynamic network topology – Need to address situation where two MANET partitions merge • Radio Technology – Layer-2 media access often incompatible with layer-3 MANET routing protocol • Battery exhaustion threat – A malicious node may interact with a mobile node very often trying to drain the mobile node’s battery • Testing of Applications • Integrating MANET into the Internet 61 © 2004 Syzygy Engineering – Will Ivancic

Integrating MANET into the Internet SYZYGY Engineering • Unicast Address Autoconfiguration • Multicast Name Resolution • Service Discovery • Global Connectivity between MANET and Internet Source: http: //www. adhoc. 6 ants. net/ 62
- Slides: 62