Wireless Networks Wireless Transmission wireless mobile phone subscribers

Wireless Networks
Wireless Transmission • # wireless (mobile) phone subscribers now exceeds # wired phone subscribers • # wireless Internet-connected devices soon to exceed # wireline Internet-connected devices • laptops, Internet-enabled phones promise anytime untethered Internet access • Two important (but different) challenges • wireless: communication over wireless link • mobility: handling the mobile user who changes point of attachment to network v Similarities with wired § § v Differences from wired § v Layer 3 and higher protocols Signal origination: From electrical current, travel along conductor Signal transmission - No fixed path, guidance Antenna § § Signal transmission and reception Same frequency required on each antenna: Share same channel Wireless transmission and reception Antennas v Radiation pattern : Relative strength over three-dimensional area • v v All electromagnetic energy antenna sends, receives Directional antenna: Issues wireless signals along single direction Omnidirectional antenna § Issues, receives wireless signals • Equal strength, clarity. All direction
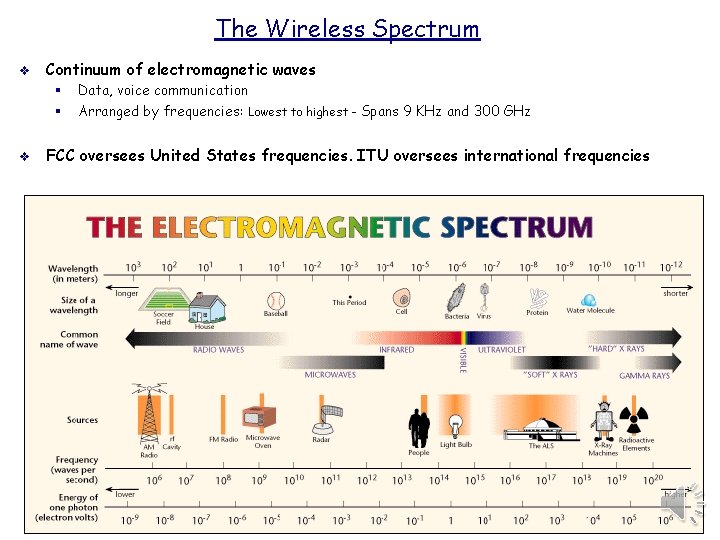
The Wireless Spectrum v Continuum of electromagnetic waves § § v Data, voice communication Arranged by frequencies: Lowest to highest - Spans 9 KHz and 300 GHz FCC oversees United States frequencies. ITU oversees international frequencies
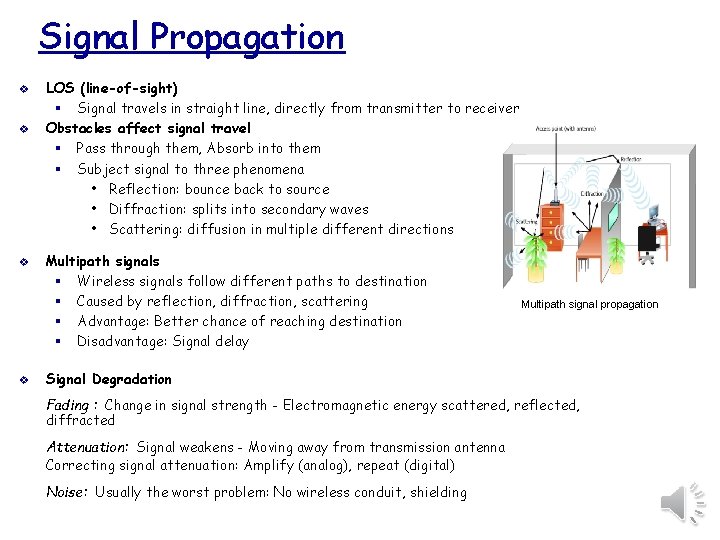
Signal Propagation v v LOS (line-of-sight) § Signal travels in straight line, directly from transmitter to receiver Obstacles affect signal travel § Pass through them, Absorb into them § Subject signal to three phenomena • Reflection: bounce back to source • Diffraction: splits into secondary waves • Scattering: diffusion in multiple different directions Multipath signals § Wireless signals follow different paths to destination § Caused by reflection, diffraction, scattering § Advantage: Better chance of reaching destination § Disadvantage: Signal delay Multipath signal propagation Signal Degradation Fading : Change in signal strength - Electromagnetic energy scattered, reflected, diffracted Attenuation: Signal weakens - Moving away from transmission antenna Correcting signal attenuation: Amplify (analog), repeat (digital) Noise: Usually the worst problem: No wireless conduit, shielding
MIMO A technique which has led to some of the greatest improvements in Wireless communications of late is called Multiple-Input Multiple-Output (MIMO). v MIMO uses multiple transmitters and receivers to transfer more data at the same time. To use MIMO, either the mobile device or the access point needs to support MIMO but for optimal performance and range, both the station and the AP must support MIMO. v In many routers, the antennas are internal. In others you can see (and even upgrade) the higher gain antennas. External antennas can be adjusted for optimum range. v Each antenna in the early protocols (Single Input Single Output) designated one antenna at the router to transmit and the other single antenna at your device to receive data. v The newer protocols invoke MIMO (Multiple Input, Multiple Output) uses multiple antennae at the transmission point and multiple streams, thereby increasing performance significantly. The antennas can be pooled to optimize your stream. MIMO also can deliver four spatial streams of data to your devices. If your devices (laptops, tablets, gaming) do not support MIMO, you cannot get the full benefit of this technology. v It takes advantage of a natural radio-wave phenomenon called multipath where signals bounce off walls and other objects and reach the receiving antenna multiple times via different angles and at slightly different times. v This traditionally interfered with a signal but MIMO actually takes advantage of this by using multiple, smart transmitters and receivers with an added spatial dimension, to increase the overall performance and range. v It really is a fascinating technology and it is expected that our future 5 G rollouts will build on MIMO technology in the small deployed cells.
Frequency Ranges v v v 2. 4 -GHz band (older) § Frequency range: 2. 4– 2. 4835 GHz. 11 unlicensed communications channels. Susceptible to interference Unlicensed § No FCC registration required 5 -GHz band (newer) § Frequency bands • 5. 1 GHz, 5. 3 GHz, 5. 4 GHz, 5. 8 GHz § 24 unlicensed bands, each 20 MHz wide. Used by weather, military radar communications Fixed versus Mobile v Fixed communications wireless systems § § Transmitter, receiver locations do not move Transmitting antenna focuses energy directly toward receiving antenna • § Advantage • • v Point-to-point link results No wasted energy issuing signals More energy used for signal itself Mobile communications wireless systems § Receiver located anywhere within transmitter’s range • Receiver can roam
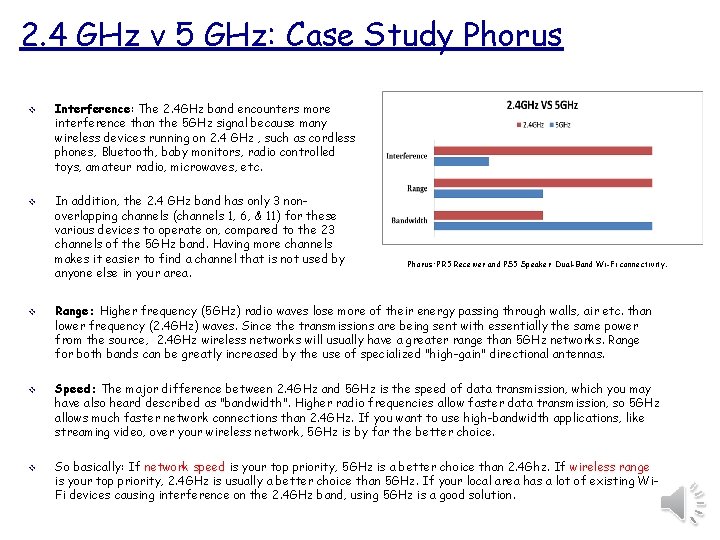
2. 4 GHz v 5 GHz: Case Study Phorus v Interference: The 2. 4 GHz band encounters more interference than the 5 GHz signal because many wireless devices running on 2. 4 GHz , such as cordless phones, Bluetooth, baby monitors, radio controlled toys, amateur radio, microwaves, etc. v In addition, the 2. 4 GHz band has only 3 nonoverlapping channels (channels 1, 6, & 11) for these various devices to operate on, compared to the 23 channels of the 5 GHz band. Having more channels makes it easier to find a channel that is not used by anyone else in your area. Phorus: PR 5 Receiver and PS 5 Speaker Dual-Band Wi-Fi connectivity. v Range: Higher frequency (5 GHz) radio waves lose more of their energy passing through walls, air etc. than lower frequency (2. 4 GHz) waves. Since the transmissions are being sent with essentially the same power from the source, 2. 4 GHz wireless networks will usually have a greater range than 5 GHz networks. Range for both bands can be greatly increased by the use of specialized "high-gain" directional antennas. v Speed: The major difference between 2. 4 GHz and 5 GHz is the speed of data transmission, which you may have also heard described as "bandwidth". Higher radio frequencies allow faster data transmission, so 5 GHz allows much faster network connections than 2. 4 GHz. If you want to use high-bandwidth applications, like streaming video, over your wireless network, 5 GHz is by far the better choice. v So basically: If network speed is your top priority, 5 GHz is a better choice than 2. 4 Ghz. If wireless range is your top priority, 2. 4 GHz is usually a better choice than 5 GHz. If your local area has a lot of existing Wi. Fi devices causing interference on the 2. 4 GHz band, using 5 GHz is a good solution.
802. 11 b, g and n 802. 11 b v v DSSS (direct-sequence spread spectrum) signaling 2. 4 -GHz band: Separated into 22 -MHz channels Throughput: 11 Mbps theoretical but 5 Mbps actual throughput 100 meters distance limit: Node to Access Point 802. 11 g v v Affordable as 802. 11 b Throughput: 54 Mbps theoretical but 20 to 25 Mbps effective 100 meter node range 2. 4 -GHz frequency band: Compatible with 802. 11 b networks 802. 11 a v v v 5 -GHz band - Not congested like 2. 4 -GHz band: Lower interference, requires more transmit power Throughput: 54 Mbps theoretical but 11 and 18 Mbps effective 20 meter distance limit More expensive, least popular Uses Orthogonal Frequency Division Multiplexing (OFDM) (so does 802. 11 g) faster than DSSS 802. 11 n v v v Significant increase in the maximum net data rate from 54 Mbit/s to 600 Mbit/s Uses four spatial streams at a channel width of 40 MHz. 802. 11 n standardized support for multiple-input multiple-output (MIMO), frame aggregation, security improvements It can be used in the 2. 4 GHz or 5 GHz frequency bands. Also Backward compatiable. Channels operating with a width of 40 MHz are another feature incorporated into 802. 11 n; this doubles the channel width from 20 MHz in previous 802. 11 PHYs to transmit data. It can be enabled in the 5 GHz mode, or within the 2. 4 GHz mode if there is knowledge that it will not interfere with any other 802. 11 or non-802. 11 (such as Bluetooth) system using the same frequencies.
Noise Level v v The noise level indicates the amount of background noise in your environment. The higher the noise level, the more likely hood of degraded strength and performance for your wireless signal strength. The closer the value to 0, the greater the noise level. v Negative values indicate less background noise. E. g. -96 d. Bm is a lower noise level than -20 d. Bm. v Those numbers are used to determine the Signal to Noise Ratio v v The signal-to-noise ratio (SNR) is the power ratio between the signal strength and the noise level. This value is represented as a +d. Bm value. In general, you should have a minimum of +25 d. Bm signal-to-noise ratio. Lower values than +25 d. Bm result in poor performance and speeds. For example: If you have a -41 d. Bm signal strength, and a -50 d. Bm noise level, this results in a poor signal-to-noise ratio of +9 d. Bm. If you have a -41 d. Bm signal strength, and a -96 d. Bm noise level, this results in an excellent signalto-noise ratio of +55 d. Bm.
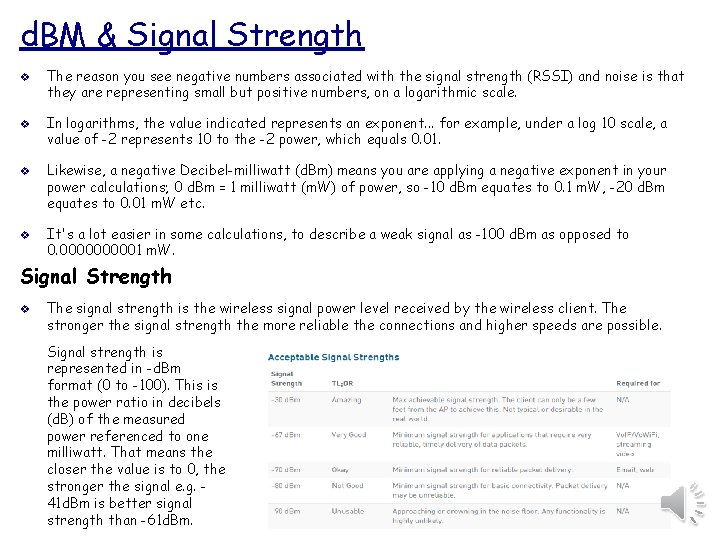
d. BM & Signal Strength v v The reason you see negative numbers associated with the signal strength (RSSI) and noise is that they are representing small but positive numbers, on a logarithmic scale. In logarithms, the value indicated represents an exponent. . . for example, under a log 10 scale, a value of -2 represents 10 to the -2 power, which equals 0. 01. Likewise, a negative Decibel-milliwatt (d. Bm) means you are applying a negative exponent in your power calculations; 0 d. Bm = 1 milliwatt (m. W) of power, so -10 d. Bm equates to 0. 1 m. W, -20 d. Bm equates to 0. 01 m. W etc. It's a lot easier in some calculations, to describe a weak signal as -100 d. Bm as opposed to 0. 000001 m. W. Signal Strength v The signal strength is the wireless signal power level received by the wireless client. The stronger the signal strength the more reliable the connections and higher speeds are possible. Signal strength is represented in -d. Bm format (0 to -100). This is the power ratio in decibels (d. B) of the measured power referenced to one milliwatt. That means the closer the value is to 0, the stronger the signal e. g. 41 d. Bm is better signal strength than -61 d. Bm.
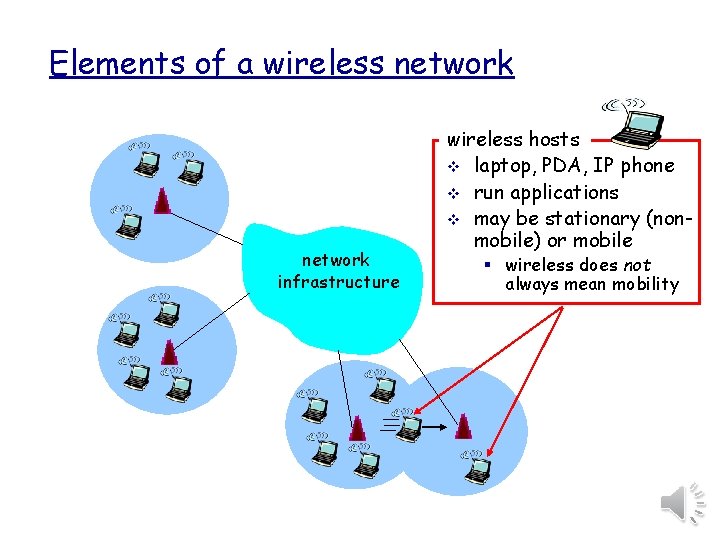
Elements of a wireless network infrastructure wireless hosts v laptop, PDA, IP phone v run applications v may be stationary (nonmobile) or mobile § wireless does not always mean mobility
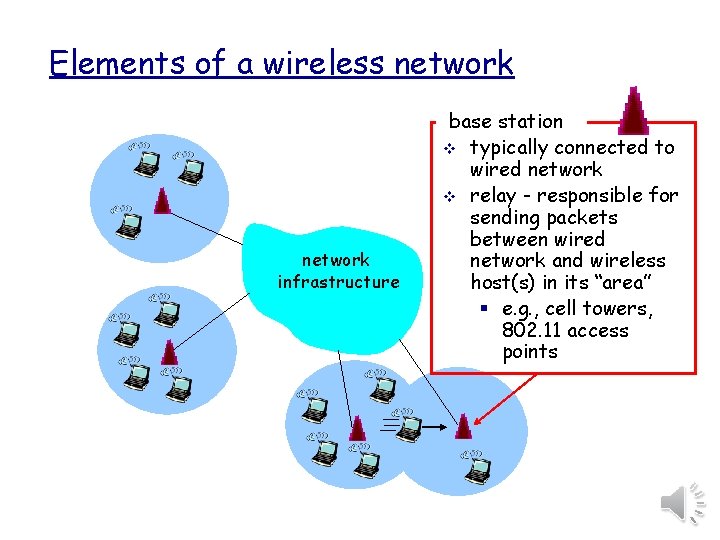
Elements of a wireless network infrastructure base station v typically connected to wired network v relay - responsible for sending packets between wired network and wireless host(s) in its “area” § e. g. , cell towers, 802. 11 access points
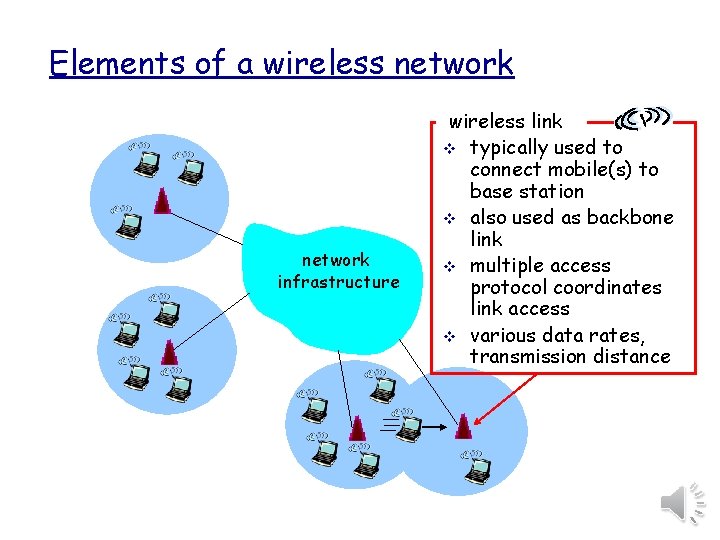
Elements of a wireless network infrastructure wireless link v typically used to connect mobile(s) to base station v also used as backbone link v multiple access protocol coordinates link access v various data rates, transmission distance
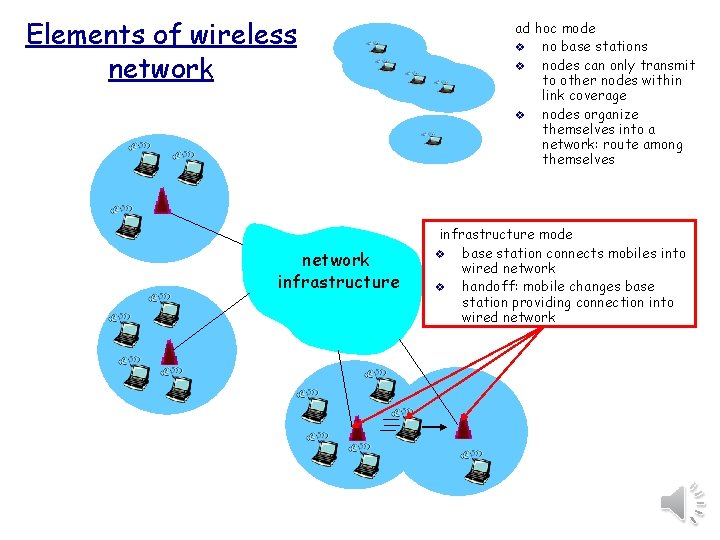
Elements of wireless network infrastructure ad hoc mode v no base stations v nodes can only transmit to other nodes within link coverage v nodes organize themselves into a network: route among themselves infrastructure mode v base station connects mobiles into wired network v handoff: mobile changes base station providing connection into wired network
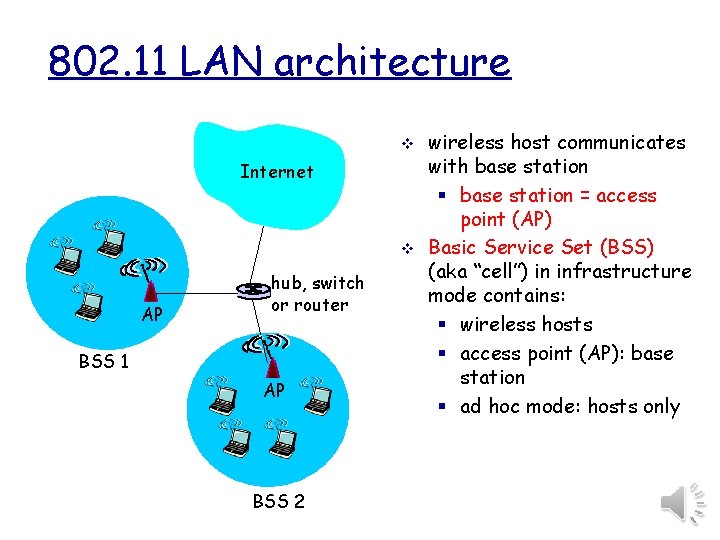
802. 11 LAN architecture v Internet v AP hub, switch or router BSS 1 AP BSS 2 wireless host communicates with base station § base station = access point (AP) Basic Service Set (BSS) (aka “cell”) in infrastructure mode contains: § wireless hosts § access point (AP): base station § ad hoc mode: hosts only
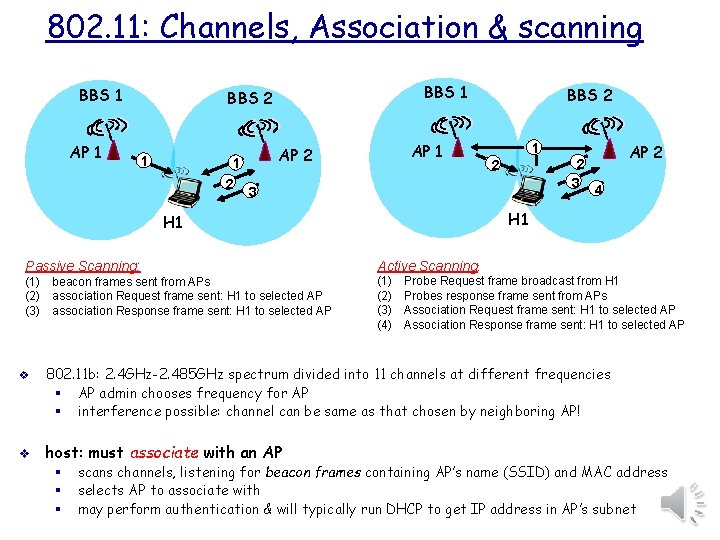
802. 11: Channels, Association & scanning BBS 1 AP 1 BBS 2 1 1 2 AP 1 AP 2 2 2 3 AP 2 4 H 1 Passive Scanning: Active Scanning: (1) beacon frames sent from APs (2) association Request frame sent: H 1 to selected AP (3) association Response frame sent: H 1 to selected AP (1) (2) (3) (4) v 1 3 H 1 v BBS 2 Probe Request frame broadcast from H 1 Probes response frame sent from APs Association Request frame sent: H 1 to selected AP Association Response frame sent: H 1 to selected AP 802. 11 b: 2. 4 GHz-2. 485 GHz spectrum divided into 11 channels at different frequencies § AP admin chooses frequency for AP § interference possible: channel can be same as that chosen by neighboring AP! host: must associate with an AP § § § scans channels, listening for beacon frames containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication & will typically run DHCP to get IP address in AP’s subnet
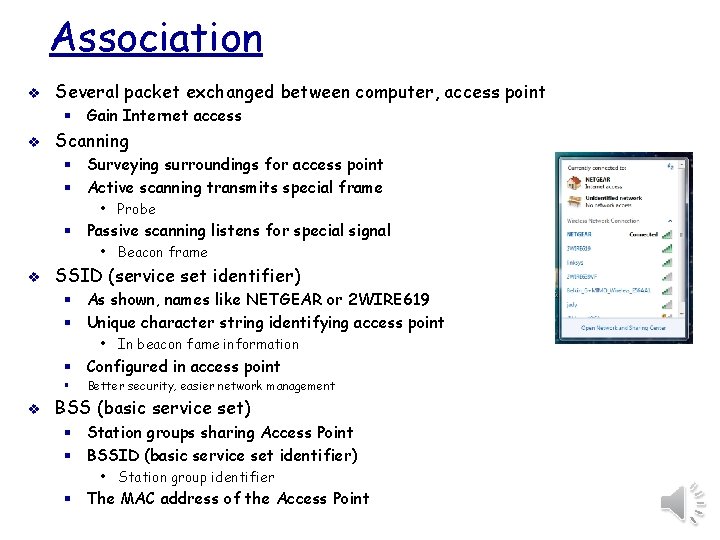
Association v Several packet exchanged between computer, access point § Gain Internet access v Scanning § Surveying surroundings for access point § Active scanning transmits special frame • Probe § Passive scanning listens for special signal • Beacon frame v SSID (service set identifier) § As shown, names like NETGEAR or 2 WIRE 619 § Unique character string identifying access point • In beacon fame information § Configured in access point § v Better security, easier network management BSS (basic service set) § Station groups sharing Access Point § BSSID (basic service set identifier) • Station group identifier § The MAC address of the Access Point
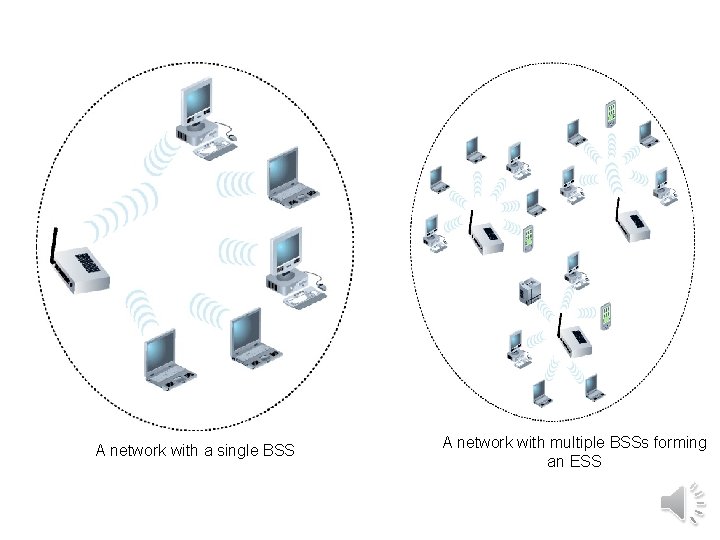
A network with a single BSS A network with multiple BSSs forming an ESS
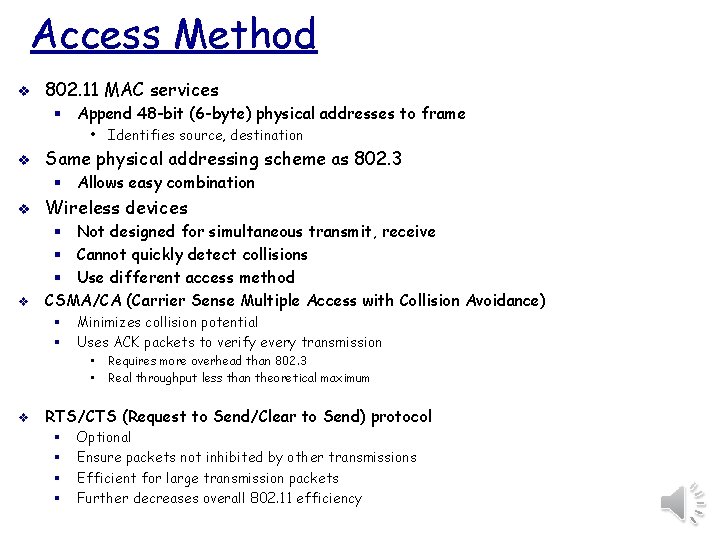
Access Method v 802. 11 MAC services § Append 48 -bit (6 -byte) physical addresses to frame • Identifies source, destination v Same physical addressing scheme as 802. 3 § Allows easy combination v Wireless devices v § Not designed for simultaneous transmit, receive § Cannot quickly detect collisions § Use different access method CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance) § § Minimizes collision potential Uses ACK packets to verify every transmission • • v Requires more overhead than 802. 3 Real throughput less than theoretical maximum RTS/CTS (Request to Send/Clear to Send) protocol § § Optional Ensure packets not inhibited by other transmissions Efficient for large transmission packets Further decreases overall 802. 11 efficiency
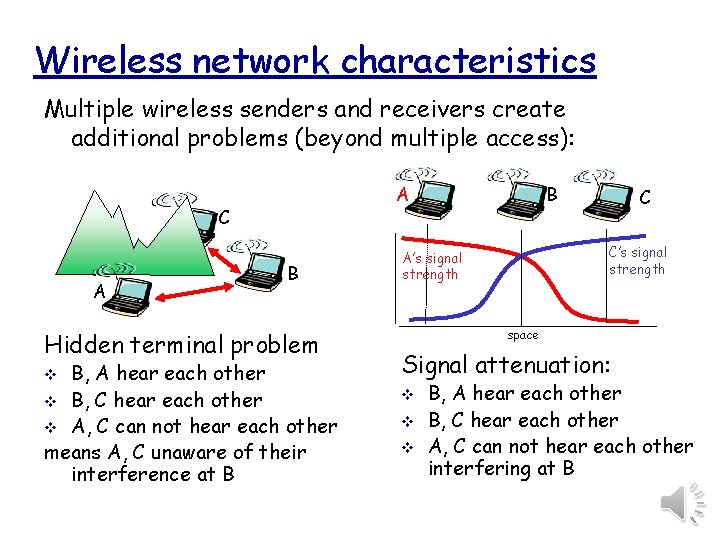
Wireless network characteristics Multiple wireless senders and receivers create additional problems (beyond multiple access): C A B Hidden terminal problem B, A hear each other v B, C hear each other v A, C can not hear each other means A, C unaware of their interference at B v B A C C’s signal strength A’s signal strength space Signal attenuation: v v v B, A hear each other B, C hear each other A, C can not hear each other interfering at B
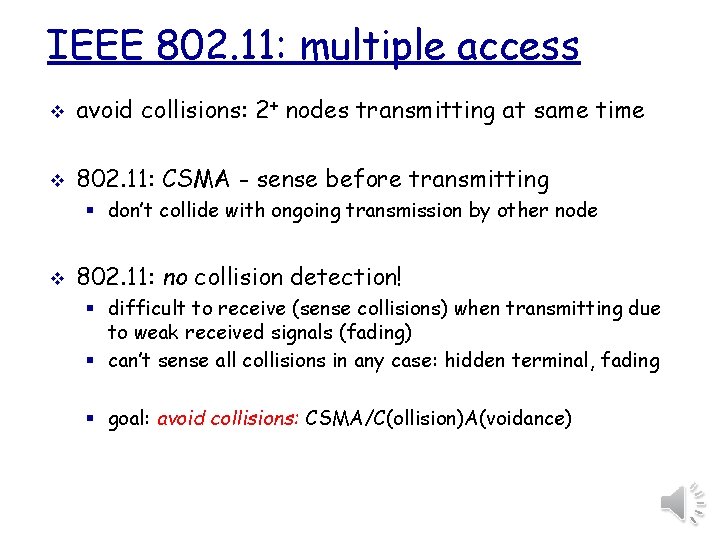
IEEE 802. 11: multiple access v avoid collisions: 2+ nodes transmitting at same time v 802. 11: CSMA - sense before transmitting § don’t collide with ongoing transmission by other node v 802. 11: no collision detection! § difficult to receive (sense collisions) when transmitting due to weak received signals (fading) § can’t sense all collisions in any case: hidden terminal, fading § goal: avoid collisions: CSMA/C(ollision)A(voidance)
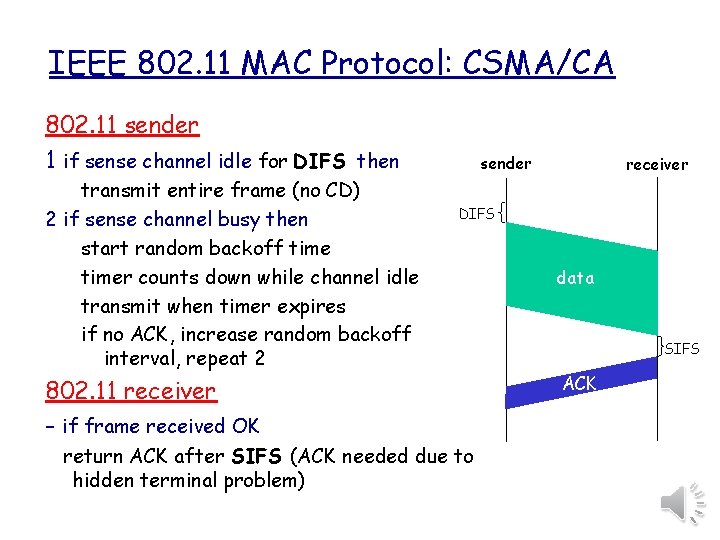
IEEE 802. 11 MAC Protocol: CSMA/CA 802. 11 sender 1 if sense channel idle for DIFS then transmit entire frame (no CD) 2 if sense channel busy then start random backoff timer counts down while channel idle transmit when timer expires if no ACK, increase random backoff interval, repeat 2 sender receiver DIFS 802. 11 receiver - if frame received OK return ACK after SIFS (ACK needed due to hidden terminal problem) data SIFS ACK
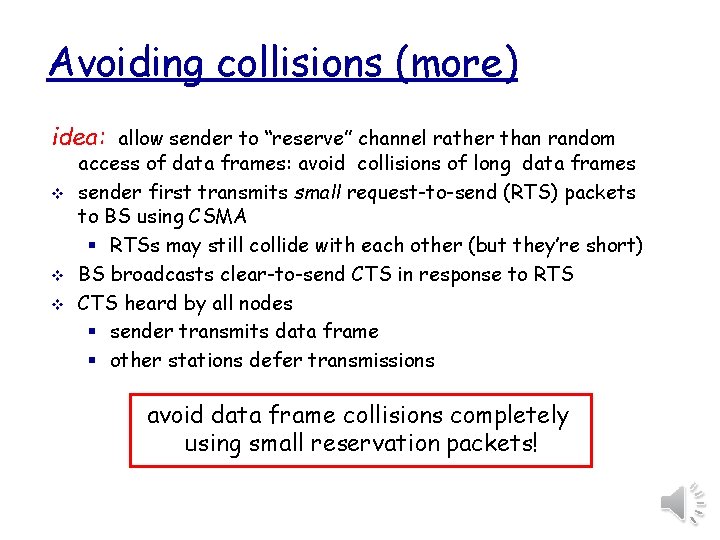
Avoiding collisions (more) idea: allow sender to “reserve” channel rather than random v v v access of data frames: avoid collisions of long data frames sender first transmits small request-to-send (RTS) packets to BS using CSMA § RTSs may still collide with each other (but they’re short) BS broadcasts clear-to-send CTS in response to RTS CTS heard by all nodes § sender transmits data frame § other stations defer transmissions avoid data frame collisions completely using small reservation packets!
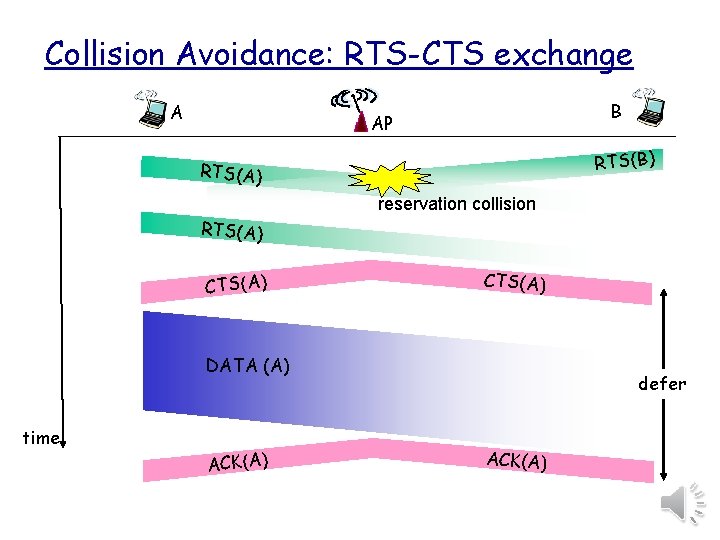
Collision Avoidance: RTS-CTS exchange A B AP RTS(B) RTS(A) reservation collision RTS(A) CTS(A) DATA (A) time ACK(A) defer ACK(A)
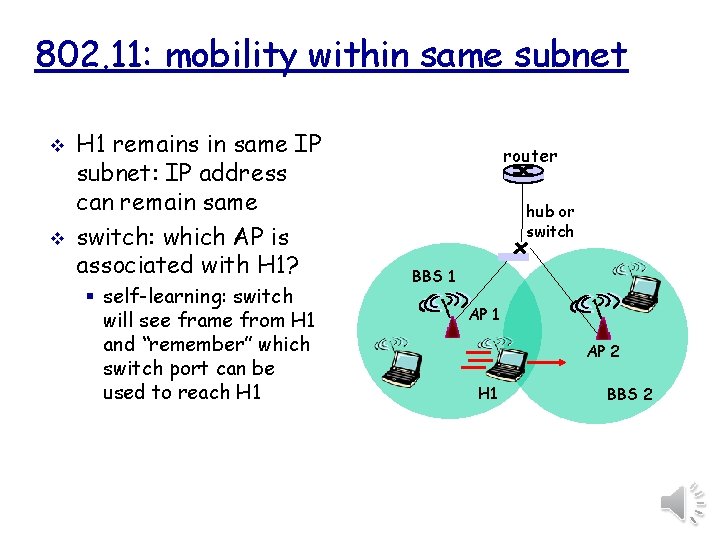
802. 11: mobility within same subnet v v H 1 remains in same IP subnet: IP address can remain same switch: which AP is associated with H 1? § self-learning: switch will see frame from H 1 and “remember” which switch port can be used to reach H 1 router hub or switch BBS 1 AP 2 H 1 BBS 2
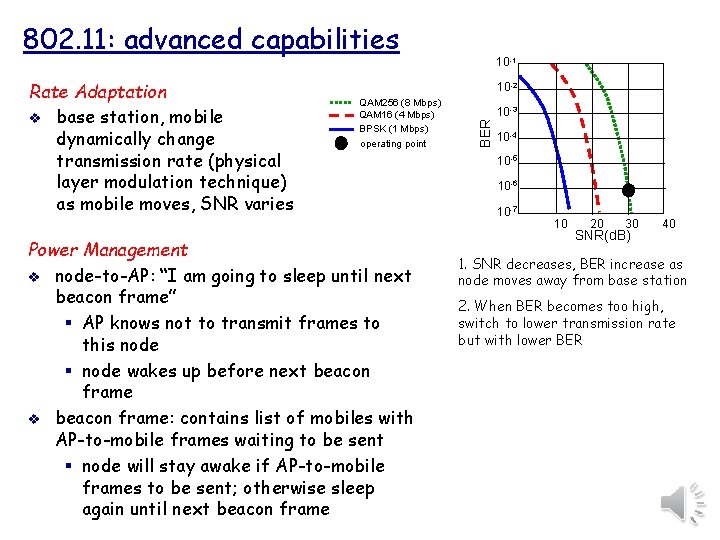
802. 11: advanced capabilities 10 -2 QAM 256 (8 Mbps) QAM 16 (4 Mbps) BPSK (1 Mbps) operating point Power Management v node-to-AP: “I am going to sleep until next beacon frame” § AP knows not to transmit frames to this node § node wakes up before next beacon frame v beacon frame: contains list of mobiles with AP-to-mobile frames waiting to be sent § node will stay awake if AP-to-mobile frames to be sent; otherwise sleep again until next beacon frame 10 -3 BER Rate Adaptation v base station, mobile dynamically change transmission rate (physical layer modulation technique) as mobile moves, SNR varies 10 -1 10 -4 10 -5 10 -6 10 -7 10 20 30 SNR(d. B) 40 1. SNR decreases, BER increase as node moves away from base station 2. When BER becomes too high, switch to lower transmission rate but with lower BER
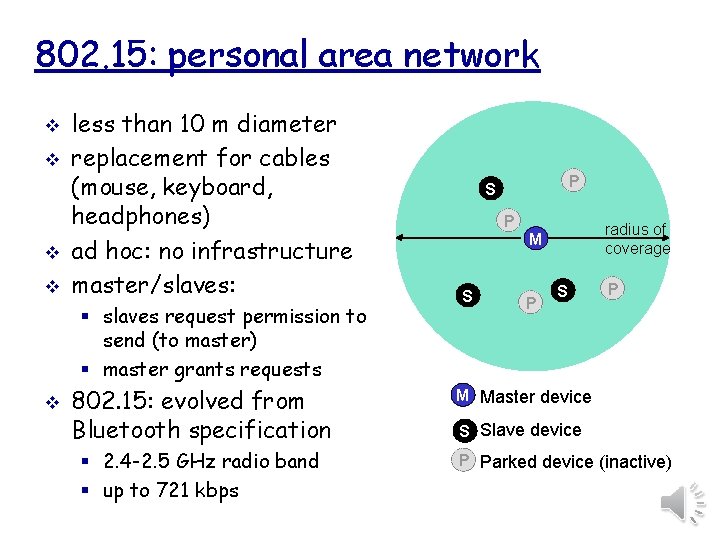
802. 15: personal area network v v less than 10 m diameter replacement for cables (mouse, keyboard, headphones) ad hoc: no infrastructure master/slaves: § slaves request permission to send (to master) § master grants requests v 802. 15: evolved from Bluetooth specification § 2. 4 -2. 5 GHz radio band § up to 721 kbps P S P radius of coverage M S P M Master device S Slave device P Parked device (inactive)
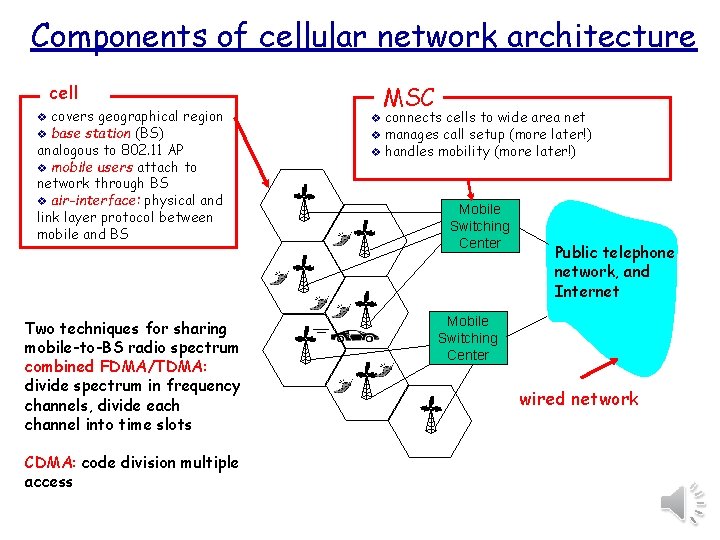
Components of cellular network architecture cell covers geographical region v base station (BS) analogous to 802. 11 AP v mobile users attach to network through BS v air-interface: physical and link layer protocol between mobile and BS v Two techniques for sharing mobile-to-BS radio spectrum combined FDMA/TDMA: divide spectrum in frequency channels, divide each channel into time slots CDMA: code division multiple access MSC connects cells to wide area net v manages call setup (more later!) v handles mobility (more later!) v Mobile Switching Center Public telephone network, and Internet Mobile Switching Center wired network
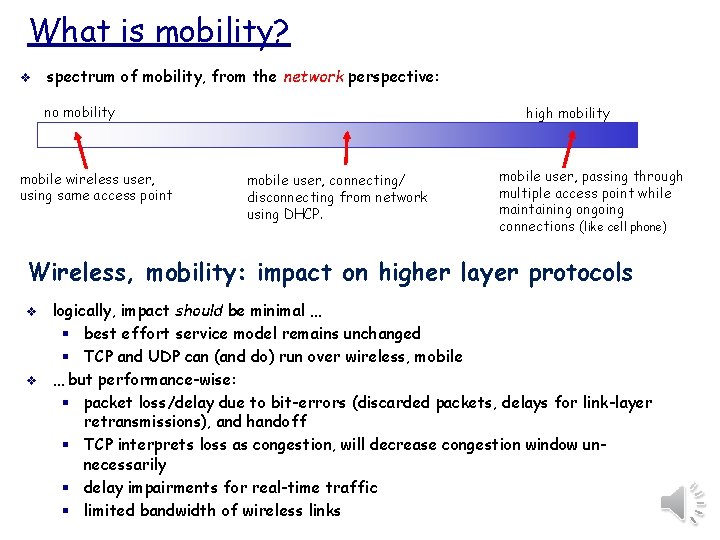
What is mobility? v spectrum of mobility, from the network perspective: no mobility mobile wireless user, using same access point high mobility mobile user, connecting/ disconnecting from network using DHCP. mobile user, passing through multiple access point while maintaining ongoing connections (like cell phone) Wireless, mobility: impact on higher layer protocols v v logically, impact should be minimal … § best effort service model remains unchanged § TCP and UDP can (and do) run over wireless, mobile … but performance-wise: § packet loss/delay due to bit-errors (discarded packets, delays for link-layer retransmissions), and handoff § TCP interprets loss as congestion, will decrease congestion window unnecessarily § delay impairments for real-time traffic § limited bandwidth of wireless links
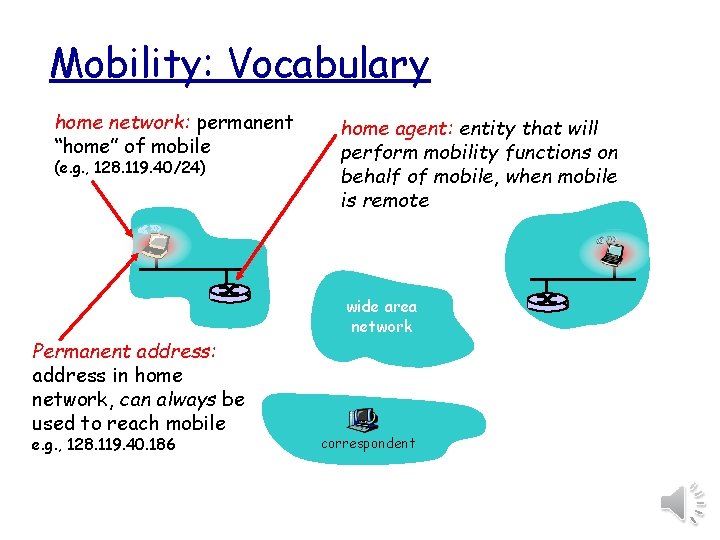
Mobility: Vocabulary home network: permanent “home” of mobile (e. g. , 128. 119. 40/24) Permanent address: address in home network, can always be used to reach mobile e. g. , 128. 119. 40. 186 home agent: entity that will perform mobility functions on behalf of mobile, when mobile is remote wide area network correspondent
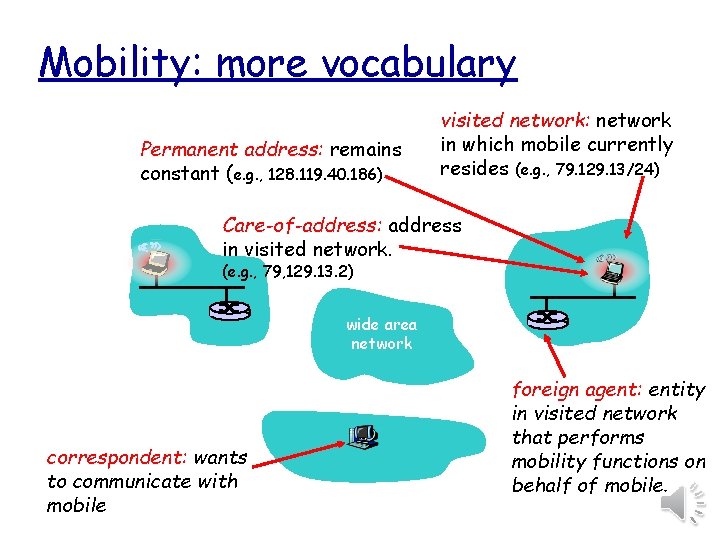
Mobility: more vocabulary Permanent address: remains constant (e. g. , 128. 119. 40. 186) visited network: network in which mobile currently resides (e. g. , 79. 129. 13/24) Care-of-address: address in visited network. (e. g. , 79, 129. 13. 2) wide area network correspondent: wants to communicate with mobile foreign agent: entity in visited network that performs mobility functions on behalf of mobile.
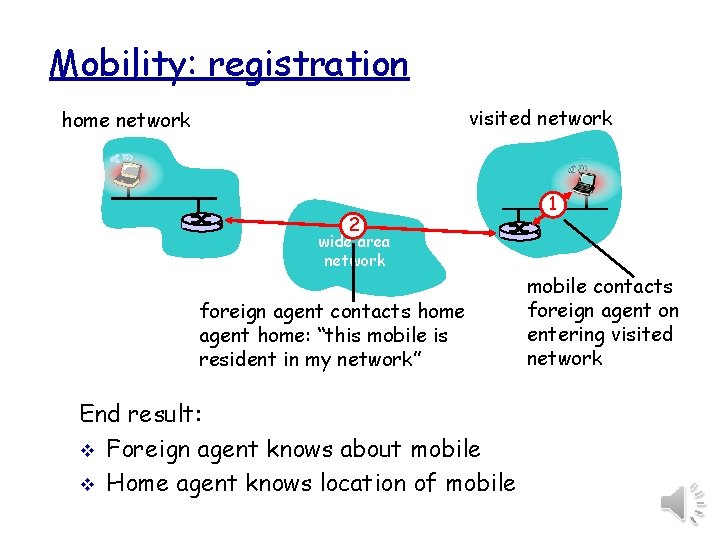
Mobility: registration visited network home network 2 1 wide area network foreign agent contacts home agent home: “this mobile is resident in my network” End result: v Foreign agent knows about mobile v Home agent knows location of mobile contacts foreign agent on entering visited network
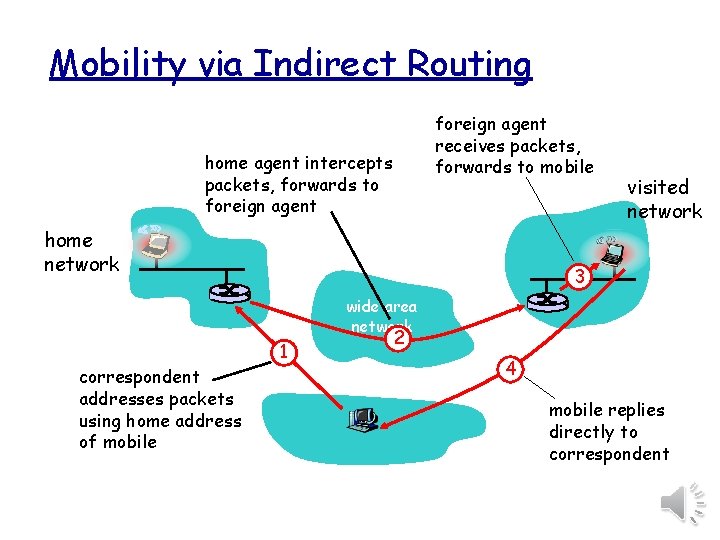
Mobility via Indirect Routing foreign agent receives packets, forwards to mobile home agent intercepts packets, forwards to foreign agent home network visited network 3 wide area network correspondent addresses packets using home address of mobile 1 2 4 mobile replies directly to correspondent
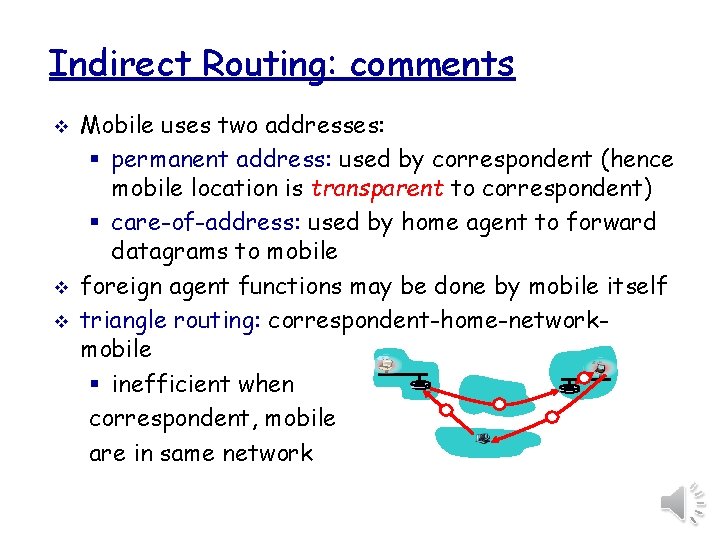
Indirect Routing: comments v v v Mobile uses two addresses: § permanent address: used by correspondent (hence mobile location is transparent to correspondent) § care-of-address: used by home agent to forward datagrams to mobile foreign agent functions may be done by mobile itself triangle routing: correspondent-home-networkmobile § inefficient when correspondent, mobile are in same network
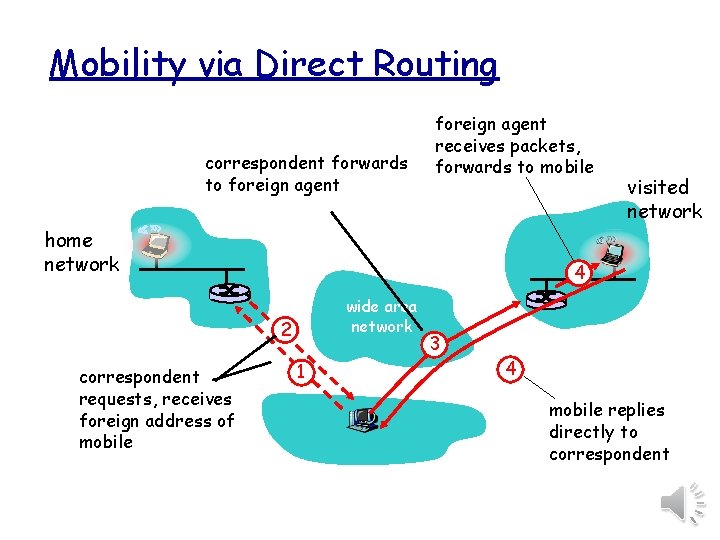
Mobility via Direct Routing correspondent forwards to foreign agent receives packets, forwards to mobile home network 4 wide area network 2 correspondent requests, receives foreign address of mobile visited network 1 3 4 mobile replies directly to correspondent
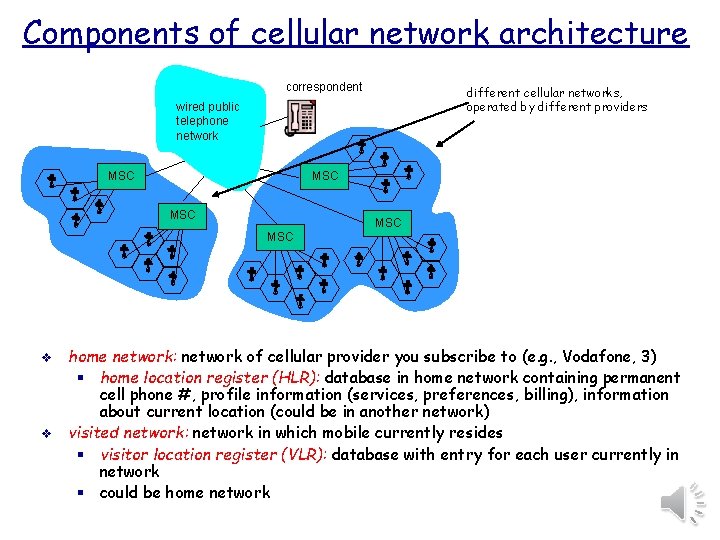
Components of cellular network architecture correspondent different cellular networks, operated by different providers wired public telephone network MSC MSC MSC v v home network: network of cellular provider you subscribe to (e. g. , Vodafone, 3) § home location register (HLR): database in home network containing permanent cell phone #, profile information (services, preferences, billing), information about current location (could be in another network) visited network: network in which mobile currently resides § visitor location register (VLR): database with entry for each user currently in network § could be home network
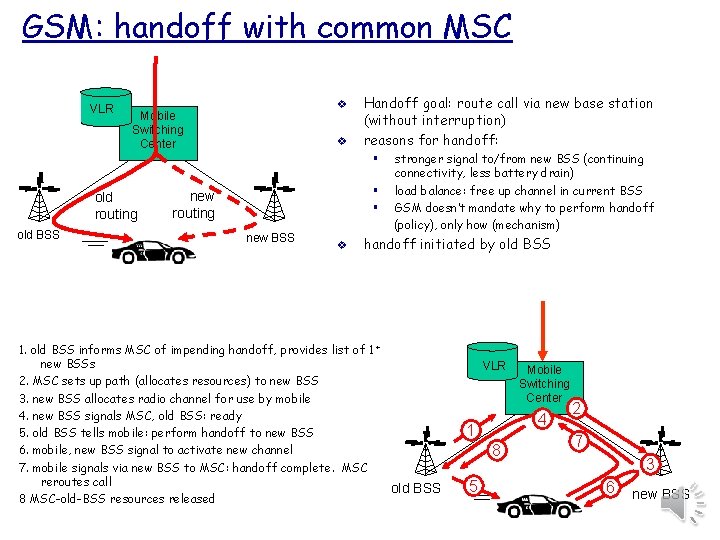
GSM: handoff with common MSC VLR v Mobile Switching Center v Handoff goal: route call via new base station (without interruption) reasons for handoff: § old routing old BSS § § new routing new BSS v stronger signal to/from new BSS (continuing connectivity, less battery drain) load balance: free up channel in current BSS GSM doesn’t mandate why to perform handoff (policy), only how (mechanism) handoff initiated by old BSS 1. old BSS informs MSC of impending handoff, provides list of 1 + new BSSs 2. MSC sets up path (allocates resources) to new BSS 3. new BSS allocates radio channel for use by mobile 4. new BSS signals MSC, old BSS: ready 5. old BSS tells mobile: perform handoff to new BSS 6. mobile, new BSS signal to activate new channel 7. mobile signals via new BSS to MSC: handoff complete. MSC reroutes call old BSS 8 MSC-old-BSS resources released VLR 4 1 8 5 Mobile Switching Center 2 7 3 6 new BSS
Class Test Revision (correct answers in Red) Explain why the checksum values are different in each packet? a. The checksum is different because each packet has to be incremented. b. The checksum is different because errors have occurred. c. The checksum is different because each packet is unique. d. The checksum is not actually different. Why are there are no VLAN fields in the Wireshark traces seen to date? a. There are no VLAN fields as VLANS are illegal in the UK. b. There are no VLAN fields as this is a wide area network trace. c. There are VLAN fields but we just cannot see them. d. There also no VLAN fields. If VLANs are in use, the VLAN tags are normally added and removed by switch ports so they will not be visible at host computers using the network.
The End
- Slides: 39