Digital Signatures Presented by Olga Shishenina Outline o
Digital Signatures Presented by Olga Shishenina
Outline o Cryptographic goals Message Authentication Codes (MACs) o Digital signatures o n n o RSA digital signature Elliptic curve digital signature Comparison of ECDSA and RSA signature 2
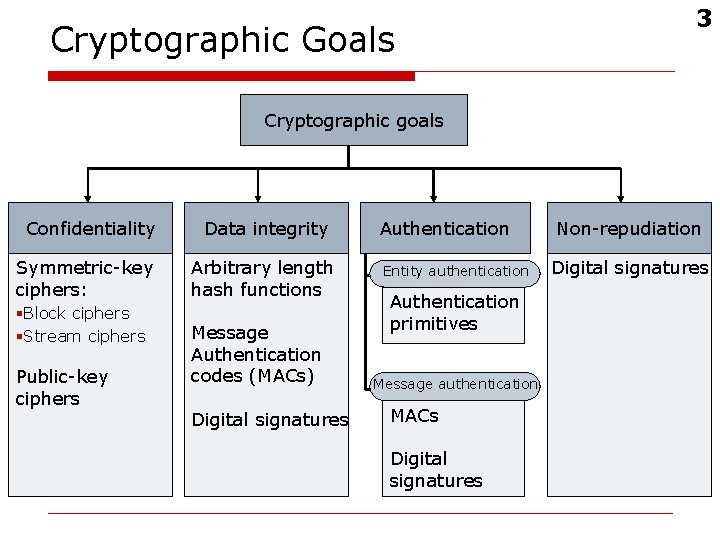
Cryptographic Goals 3 Cryptographic goals Confidentiality Symmetric-key ciphers: §Block ciphers §Stream ciphers Public-key ciphers Data integrity Arbitrary length hash functions Message Authentication codes (MACs) Digital signatures Authentication Entity authentication Authentication primitives Message authentication MACs Digital signatures Non-repudiation Digital signatures
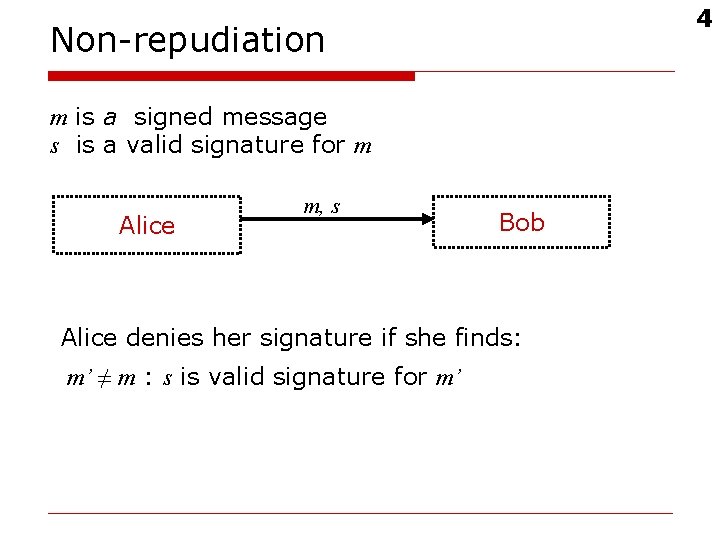
4 Non-repudiation m is a signed message s is a valid signature for m Alice m, s Bob Alice denies her signature if she finds: m’ ≠ m : s is valid signature for m’
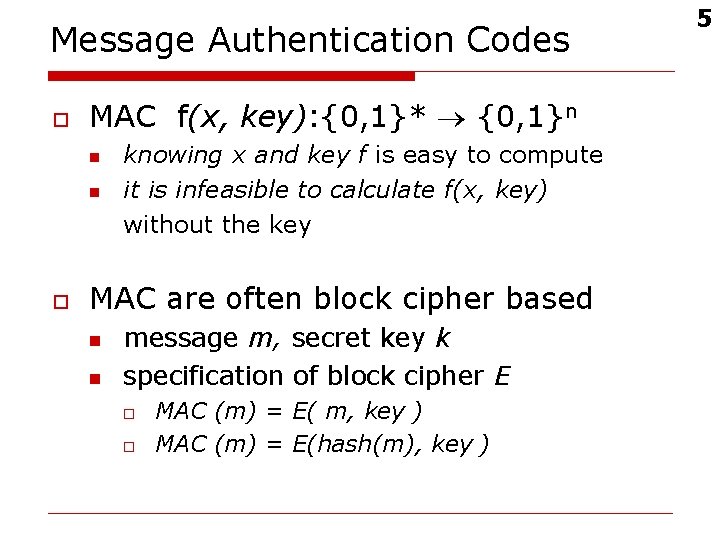
Message Authentication Codes o MAC f(x, key): {0, 1}* {0, 1}n n n o knowing x and key f is easy to compute it is infeasible to calculate f(x, key) without the key MAC are often block cipher based n n message m, secret key k specification of block cipher E o o MAC (m) = E( m, key ) MAC (m) = E(hash(m), key ) 5
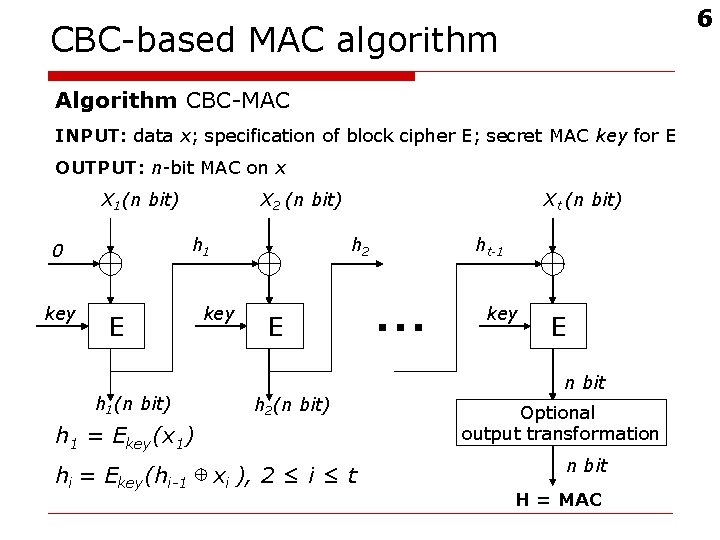
6 CBC-based MAC algorithm Algorithm CBC-MAC INPUT: data x; specification of block cipher E; secret MAC key for E OUTPUT: n-bit MAC on x X 1(n bit) h 1 0 key X 2 (n bit) E h 1(n bit) Xt (n bit) h 2 key E h 2(n bit) h 1 = Ekey(x 1) hi = Ekey(hi-1 xi ), 2 ≤ i ≤ t ht-1 … key E n bit Optional output transformation n bit H = MAC
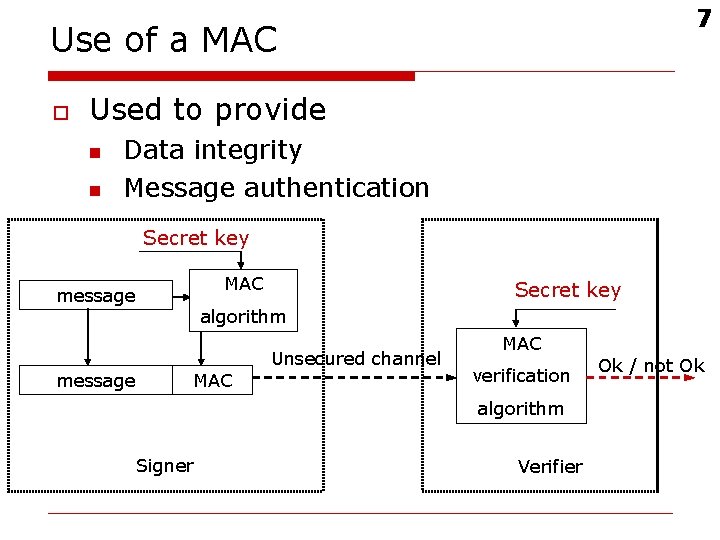
7 Use of a MAC o Used to provide n n Data integrity Message authentication Secret key MAC message Secret key algorithm MAC Unsecured channel MAC verification algorithm Signer Verifier Ok / not Ok
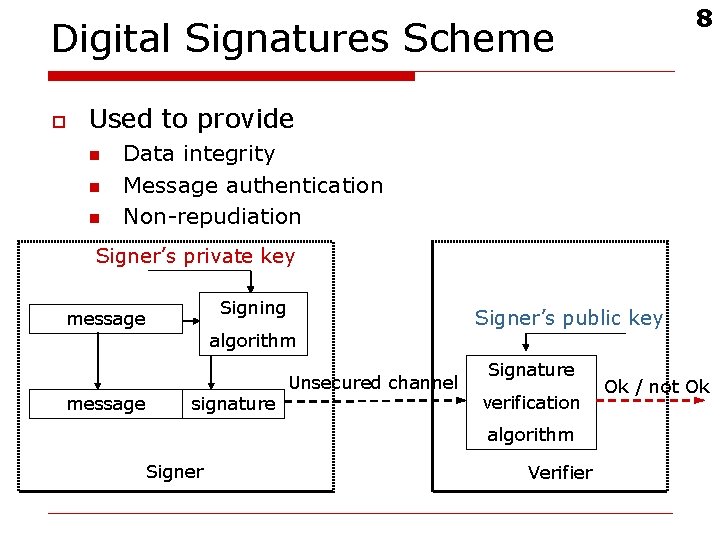
8 Digital Signatures Scheme o Used to provide n n n Data integrity Message authentication Non-repudiation Signer’s private key Signing message algorithm signature Unsecured channel Signer’s public key Signature verification algorithm Signer Verifier Ok / not Ok
Difference between MAC and digital signature o o To prove the validity of a MAC to a third party, you need to reveal the key If you can verify a MAC, you can also create it MAC does not allow a distinction to be made between the parties sharing the key Computing a MAC is (usually) much faster than computing a digital signature n Important for devices with low computing power 9
10 RSA signature algorithm
RSA o o o Developed in 1978 by Rivest, Shamir and Adleman (RSA) Most popular public key cryptosystem Based on the hard problem of “integer factorization” 11
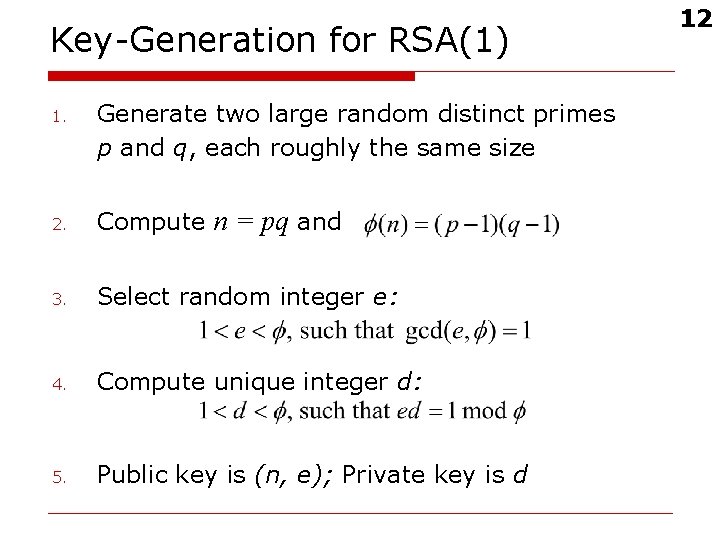
Key-Generation for RSA(1) 1. Generate two large random distinct primes p and q, each roughly the same size 2. Compute n = pq and 3. Select random integer e: 4. Compute unique integer d: 5. Public key is (n, e); Private key is d 12
Key-Generation for RSA(2) o o o Usually numbers with the right bit length are chosen randomly and tested for primality Statistical tests are used to determine the probability that these numbers are primes i. e. Strassen – Test Miller – Rabin – Test There is always an insignificantly low chance that number is not prime 13
14 Used notation o M is a set of elements, called the message space = Zn o MS is a set of elements, called the signing space = Zn o R is a 1 to 1 mapping from M to MS, called the redundancy function o MR is the image of R: {y| y = R(x), xЄ M} o R-1 is the inverse of R: MR M
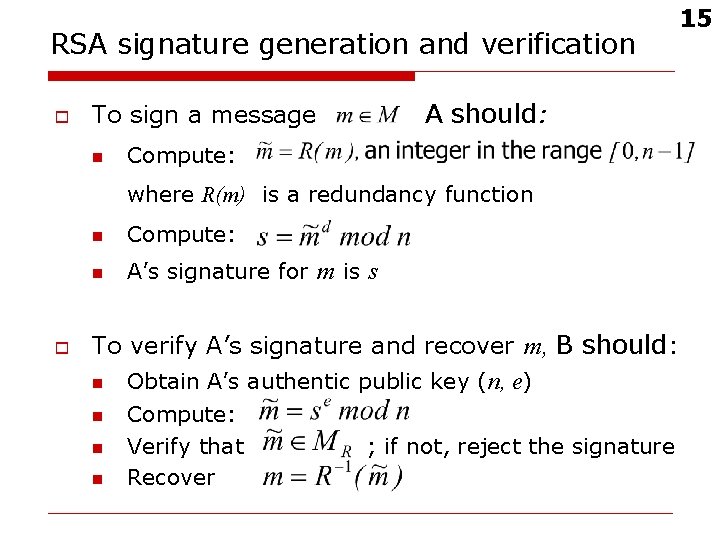
RSA signature generation and verification o A should: To sign a message n Compute: where R(m) is a redundancy function o n Compute: n A’s signature for m is s To verify A’s signature and recover m, B should: n Obtain A’s authentic public key (n, e) n n n Compute: Verify that Recover ; if not, reject the signature 15
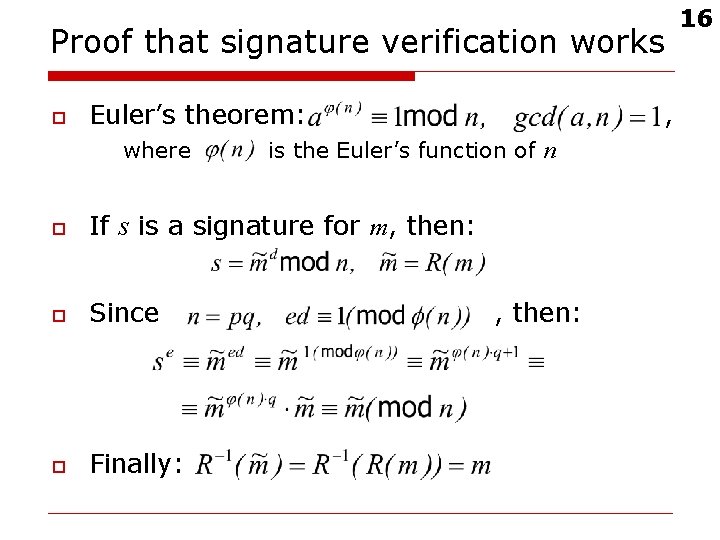
Proof that signature verification works o Euler’s theorem: where , is the Euler’s function of n o If s is a signature for m, then: o Since o Finally: , then: 16
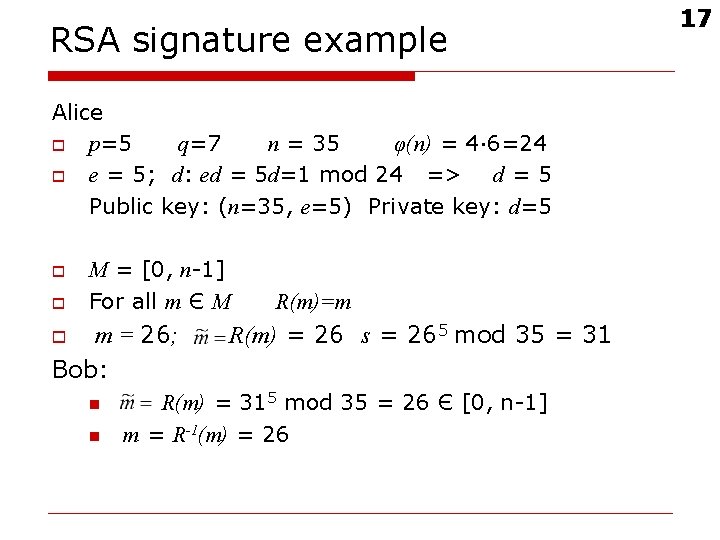
RSA signature example Alice o p=5 q=7 n = 35 φ(n) = 4· 6=24 o e = 5; d: ed = 5 d=1 mod 24 => d = 5 Public key: (n=35, e=5) Private key: d=5 o o M = [0, n-1] For all m Є M m = 26; Bob: o n n R(m)=m R(m) = 26 s = 265 mod 35 = 31 R(m) = 315 mod 35 = 26 Є [0, n-1] m = R-1(m) = 26 17
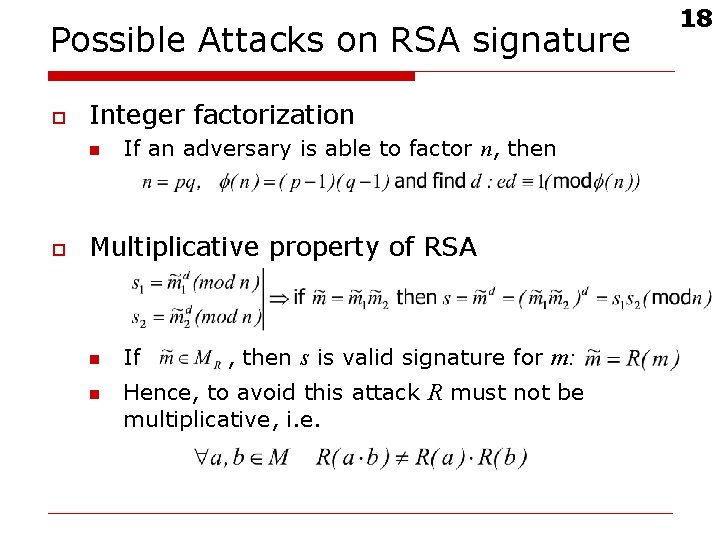
Possible Attacks on RSA signature o Integer factorization n o If an adversary is able to factor n, then Multiplicative property of RSA n n If , then s is valid signature for m: Hence, to avoid this attack R must not be multiplicative, i. e. 18
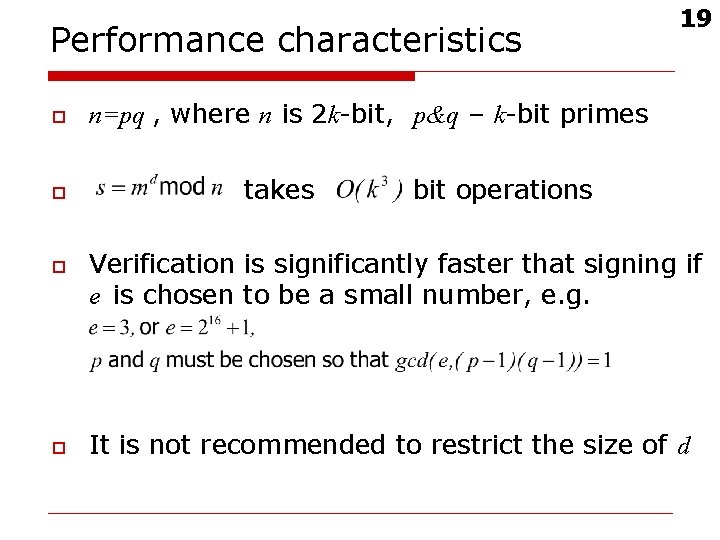
Performance characteristics o o 19 n=pq , where n is 2 k-bit, p&q – k-bit primes takes bit operations Verification is significantly faster that signing if e is chosen to be a small number, e. g. It is not recommended to restrict the size of d
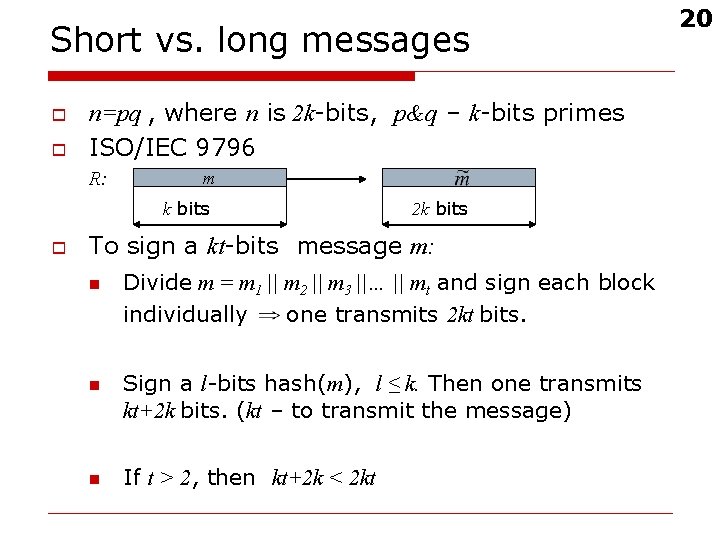
Short vs. long messages o o n=pq , where n is 2 k-bits, p&q – k-bits primes ISO/IEC 9796 R: m k bits o 2 k bits To sign a kt-bits message m: n n n Divide m = m 1 || m 2 || m 3 ||… || mt and sign each block individually one transmits 2 kt bits. Sign a l-bits hash(m), l ≤ k. Then one transmits kt+2 k bits. (kt – to transmit the message) If t > 2, then kt+2 k < 2 kt 20
21 The Elliptic Curve Digital Signature Algorithm (ECDSA)
Elliptic curves (EC) over the reals o A non-singular EC is the set E of solutions to the equation together with a special point O, where has three o distinct roots 22
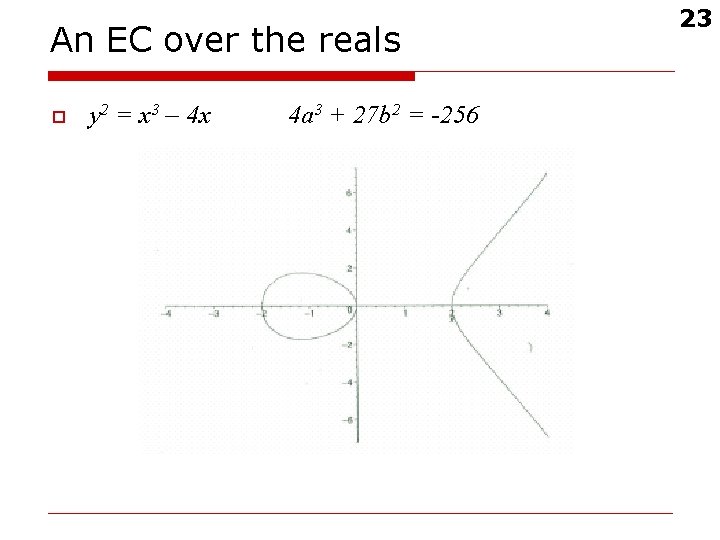
An EC over the reals o y 2 = x 3 – 4 x 4 a 3 + 27 b 2 = -256 23
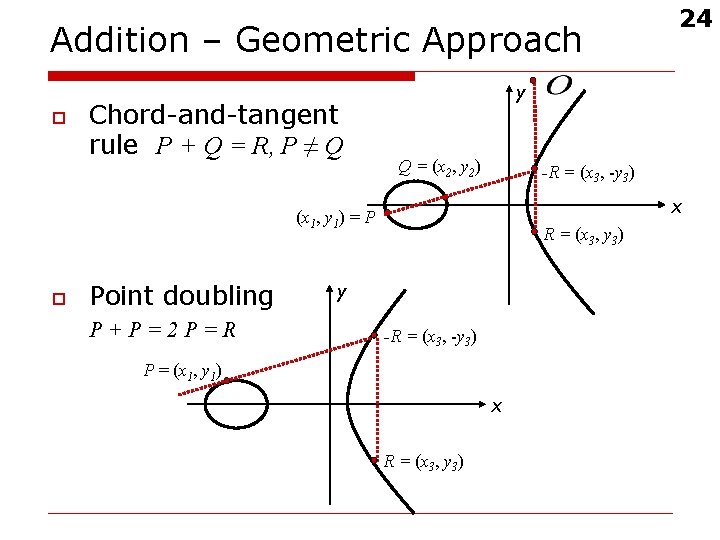
Addition – Geometric Approach o Chord-and-tangent rule P + Q = R, P ≠ Q y Q = (x 2, y 2) -R = (x 3, -y 3) x (x 1, y 1) = P o Point doubling P+P=2 P=R 24 R = (x 3, y 3) y -R = (x 3, -y 3) P = (x 1, y 1) x R = (x 3, y 3)
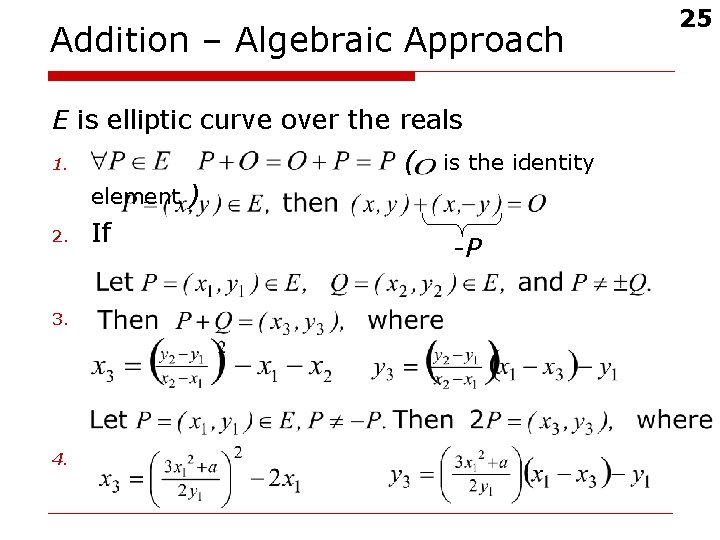
Addition – Algebraic Approach E is elliptic curve over the reals ( 1. is the identity element ) 2. 3. 4. If -P 25
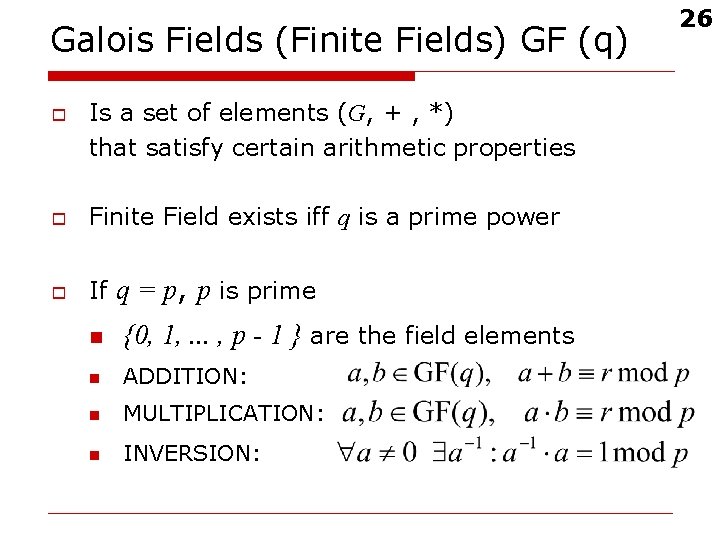
Galois Fields (Finite Fields) GF (q) o Is a set of elements (G, + , *) that satisfy certain arithmetic properties o Finite Field exists iff q is a prime power o If q = p, p is prime n {0, 1, . . . , p - 1 } are the field elements n ADDITION: n MULTIPLICATION: n INVERSION: 26
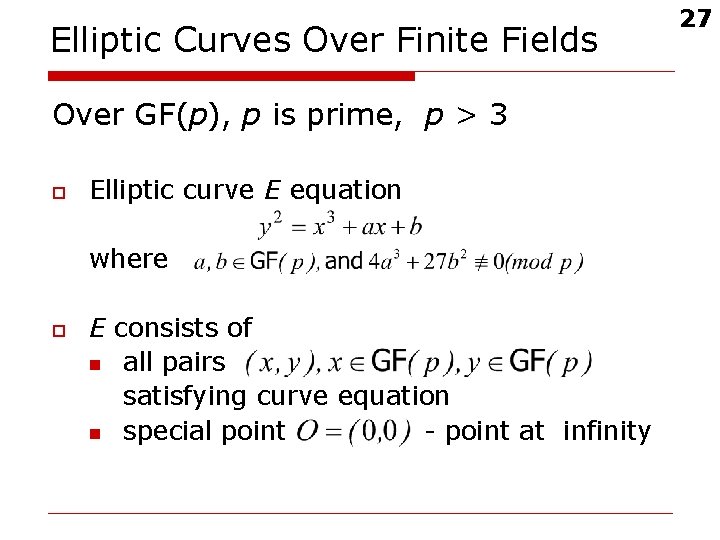
Elliptic Curves Over Finite Fields Over GF(p), p is prime, p > 3 o Elliptic curve E equation where o E consists of n all pairs satisfying curve equation n special point - point at infinity 27
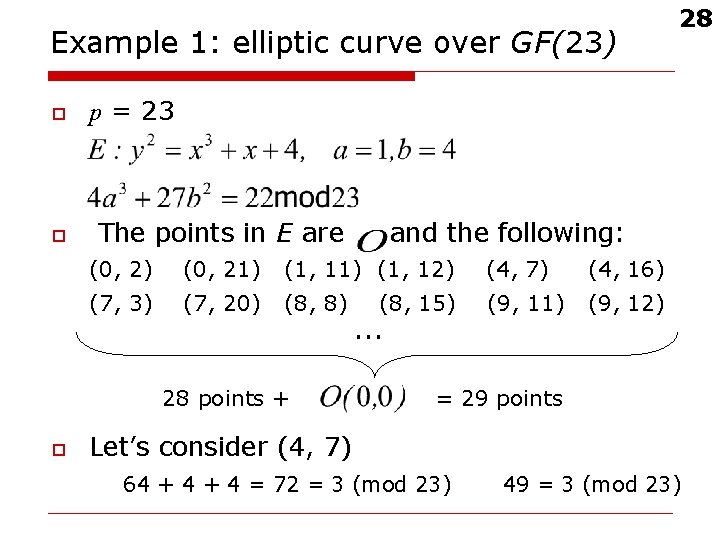
Example 1: elliptic curve over GF(23) o o p = 23 The points in E are and the following: (0, 2) (0, 21) (1, 12) (4, 7) (4, 16) (7, 3) (7, 20) (8, 8) (9, 11) (9, 12) 28 points + o 28 (8, 15) … = 29 points Let’s consider (4, 7) 64 + 4 = 72 = 3 (mod 23) 49 = 3 (mod 23)
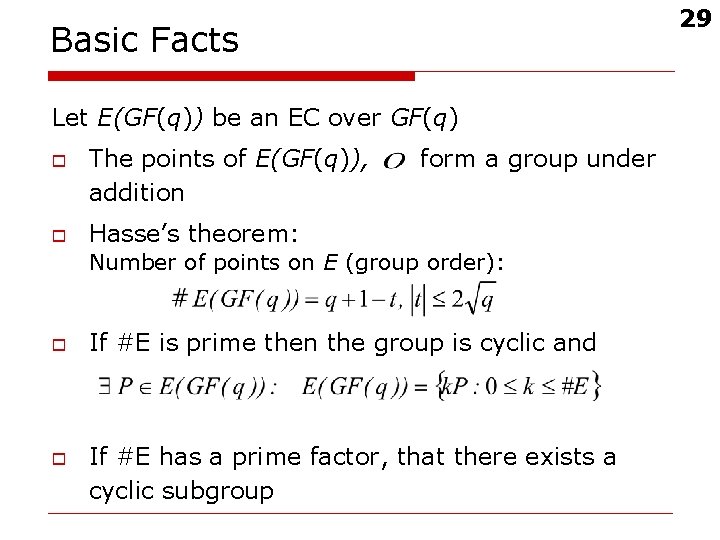
29 Basic Facts Let E(GF(q)) be an EC over GF(q) o o The points of E(GF(q)), addition form a group under Hasse’s theorem: Number of points on E (group order): o o If #E is prime then the group is cyclic and If #E has a prime factor, that there exists a cyclic subgroup
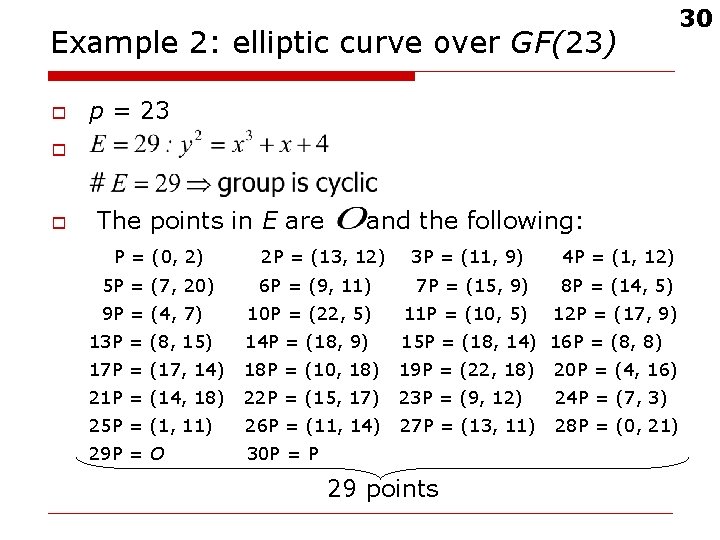
Example 2: elliptic curve over GF(23) o 30 p = 23 o o The points in E are P = (0, 2) and the following: 2 P = (13, 12) 3 P = (11, 9) 4 P = (1, 12) 6 P = (9, 11) 7 P = (15, 9) 8 P = (14, 5) 9 P = (4, 7) 10 P = (22, 5) 11 P = (10, 5) 12 P = (17, 9) 13 P = (8, 15) 14 P = (18, 9) 15 P = (18, 14) 16 P = (8, 8) 17 P = (17, 14) 18 P = (10, 18) 19 P = (22, 18) 20 P = (4, 16) 21 P = (14, 18) 22 P = (15, 17) 23 P = (9, 12) 24 P = (7, 3) 25 P = (1, 11) 26 P = (11, 14) 27 P = (13, 11) 28 P = (0, 21) 29 P = O 30 P = P 5 P = (7, 20) 29 points
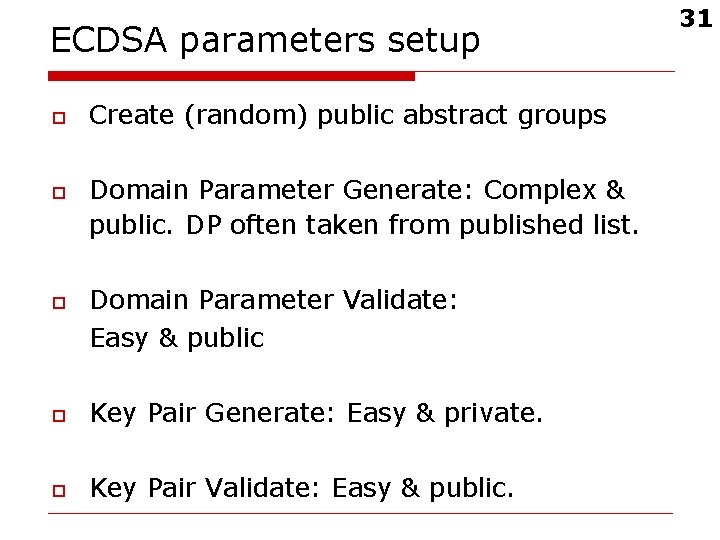
ECDSA parameters setup o o o Create (random) public abstract groups Domain Parameter Generate: Complex & public. DP often taken from published list. Domain Parameter Validate: Easy & public o Key Pair Generate: Easy & private. o Key Pair Validate: Easy & public. 31
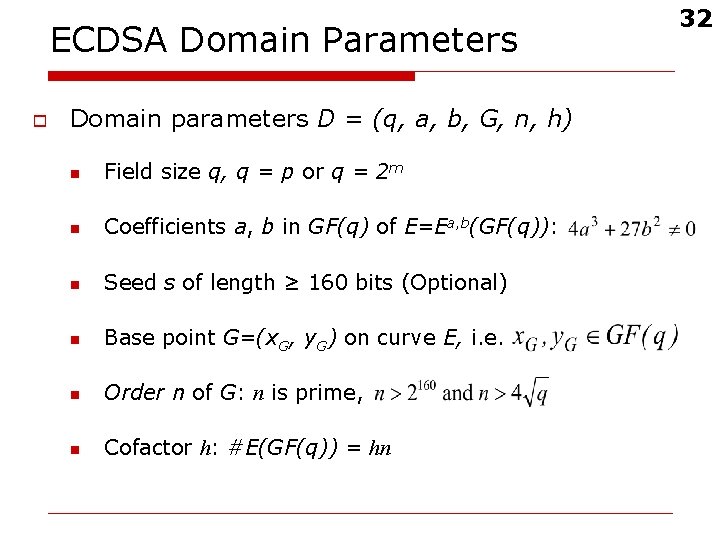
ECDSA Domain Parameters o Domain parameters D = (q, a, b, G, n, h) n Field size q, q = p or q = 2 m n Coefficients a, b in GF(q) of E=Ea, b(GF(q)): n Seed s of length ≥ 160 bits (Optional) n Base point G=(x. G, y. G) on curve E, i. e. n Order n of G: n is prime, n Cofactor h: #E(GF(q)) = hn 32
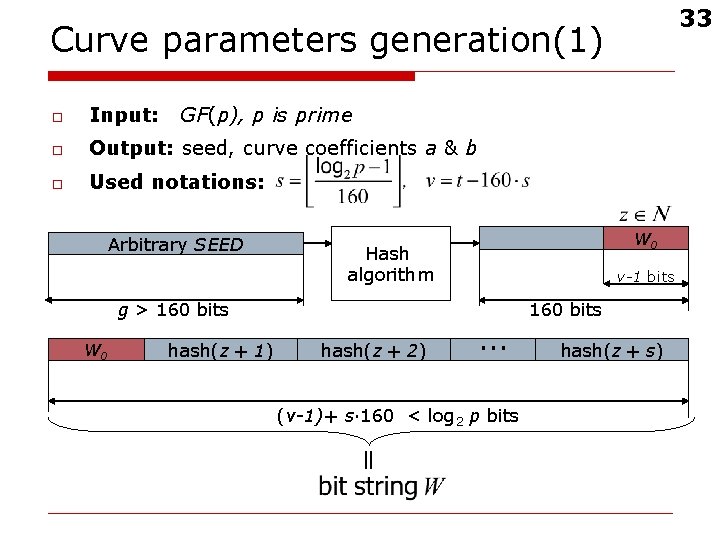
33 Curve parameters generation(1) o Input: GF(p), p is prime o Output: seed, curve coefficients a & b o Used notations: Arbitrary SEED g > 160 bits W 0 hash(z + 1) W 0 Hash algorithm hash(z + 2) v-1 bits … (v-1)+ s· 160 < log 2 p bits 160 bits hash(z + s)
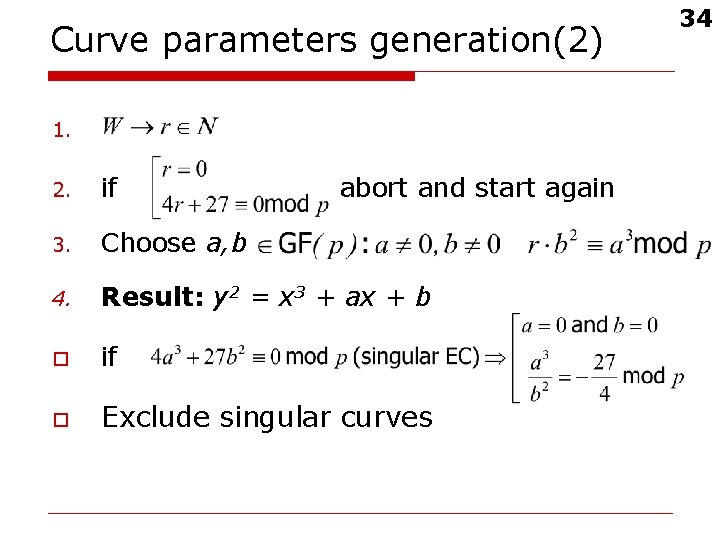
Curve parameters generation(2) 1. 2. if abort and start again 3. Choose a, b 4. Result: y 2 = x 3 + ax + b o if o Exclude singular curves 34
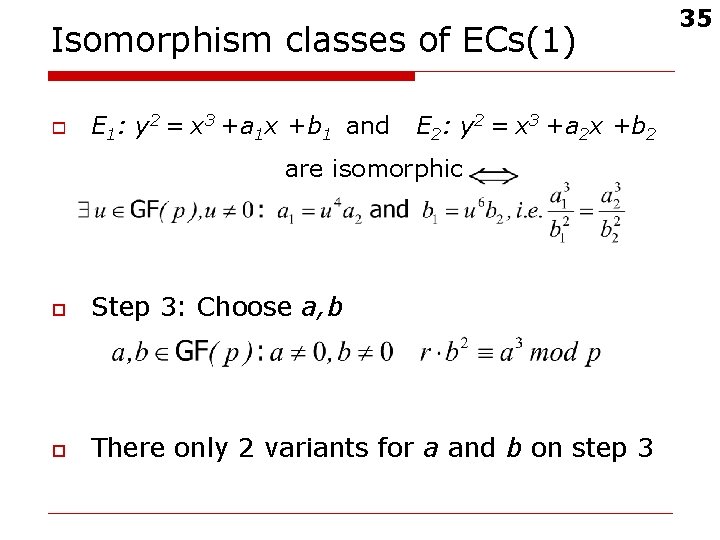
Isomorphism classes of ECs(1) o E 1: y 2 = x 3 +a 1 x +b 1 and E 2: y 2 = x 3 +a 2 x +b 2 are isomorphic o Step 3: Choose a, b o There only 2 variants for a and b on step 3 35
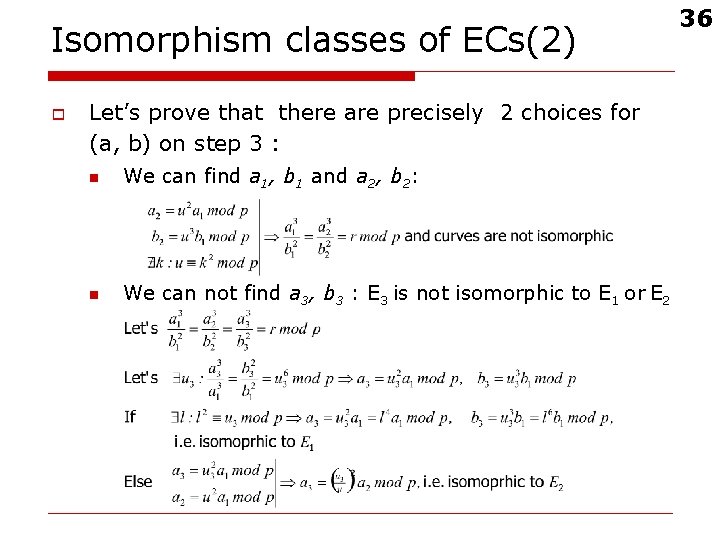
Isomorphism classes of ECs(2) o Let’s prove that there are precisely 2 choices for (a, b) on step 3 : n We can find a 1, b 1 and a 2, b 2: n We can not find a 3, b 3 : E 3 is not isomorphic to E 1 or E 2 36
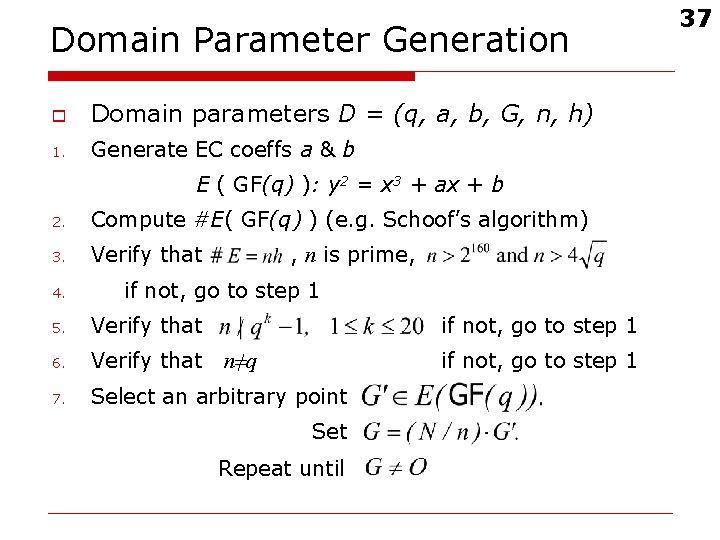
Domain Parameter Generation o Domain parameters D = (q, a, b, G, n, h) 1. Generate EC coeffs a & b E ( GF(q) ): y 2 = x 3 + ax + b 2. Compute #E( GF(q) ) (e. g. Schoof’s algorithm) 3. Verify that 4. , n is prime, if not, go to step 1 5. Verify that if not, go to step 1 6. Verify that 7. Select an arbitrary point if not, go to step 1 n≠q Set Repeat until 37
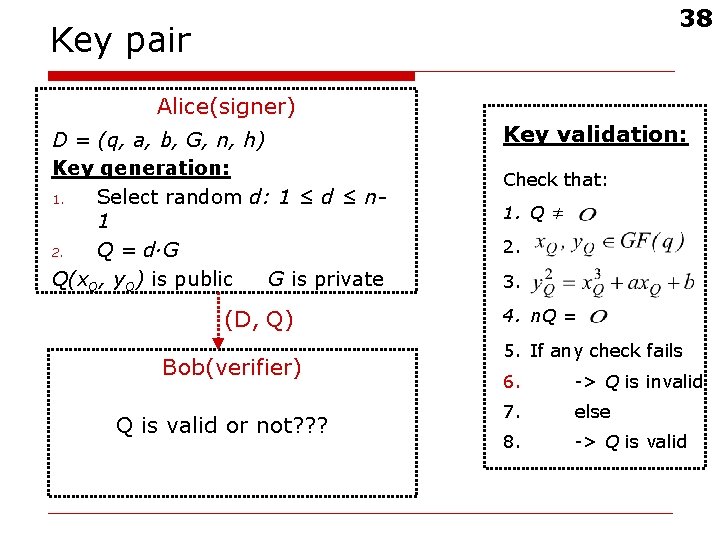
38 Key pair Alice(signer) D = (q, a, b, G, n, h) Key generation: 1. Select random d: 1 ≤ d ≤ n 1 2. Q = d·G Q(x. Q, y. Q) is public G is private (D, Q) Bob(verifier) Q is valid or not? ? ? Key validation: Check that: 1. Q ≠ 2. 3. 4. n. Q = 5. If any check fails 6. -> Q is invalid 7. else 8. -> Q is valid
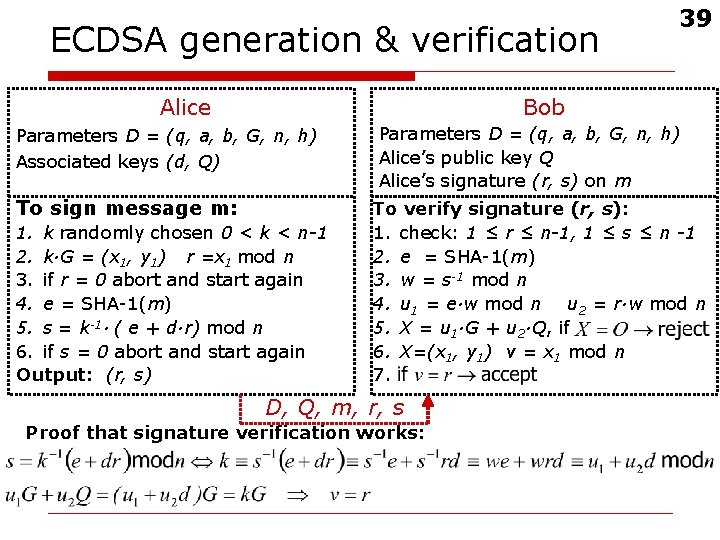
ECDSA generation & verification Alice 39 Bob Parameters D = (q, a, b, G, n, h) Associated keys (d, Q) To sign message m: 1. k randomly chosen 0 < k < n-1 2. k·G = (x 1, y 1) r =x 1 mod n 3. if r = 0 abort and start again 4. e = SHA-1(m) 5. s = k-1· ( e + d·r) mod n 6. if s = 0 abort and start again Output: (r, s) Parameters D = (q, a, b, G, n, h) Alice’s public key Q Alice’s signature (r, s) on m To verify signature (r, s): 1. check: 1 ≤ r ≤ n-1, 1 ≤ s ≤ n -1 2. e = SHA-1(m) 3. w = s-1 mod n 4. u 1 = e·w mod n u 2 = r·w mod n 5. X = u 1·G + u 2·Q, if 6. X=(x 1, y 1) v = x 1 mod n 7. D, Q, m, r, s Proof that signature verification works:
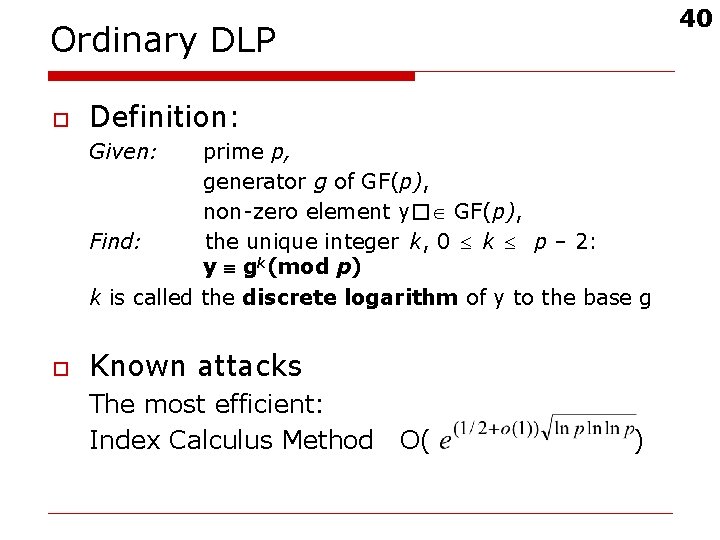
40 Ordinary DLP o Definition: Given: prime p, generator g of GF(p), non‑zero element y� GF(p), Find: the unique integer k, 0 k p – 2: y gk(mod p) k is called the discrete logarithm of y to the base g o Known attacks The most efficient: Index Calculus Method O( )
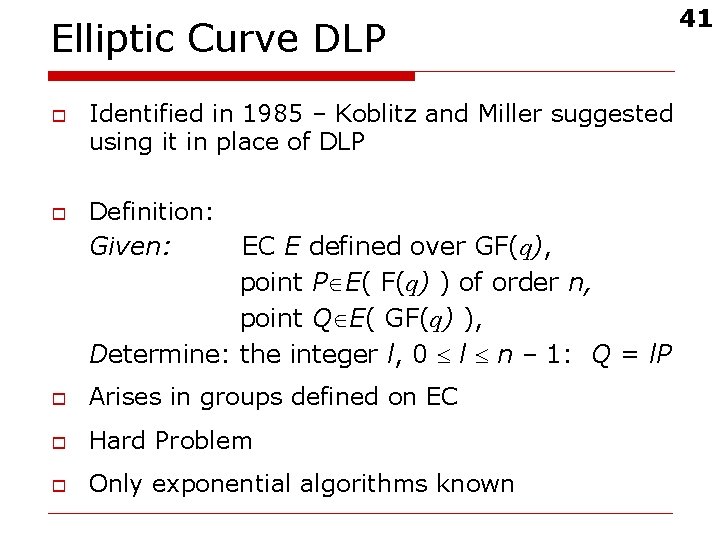
Elliptic Curve DLP o o Identified in 1985 – Koblitz and Miller suggested using it in place of DLP Definition: Given: EC E defined over GF(q), point P E( F(q) ) of order n, point Q E( GF(q) ), Determine: the integer l, 0 l n – 1: Q = l. P o Arises in groups defined on EC o Hard Problem o Only exponential algorithms known 41
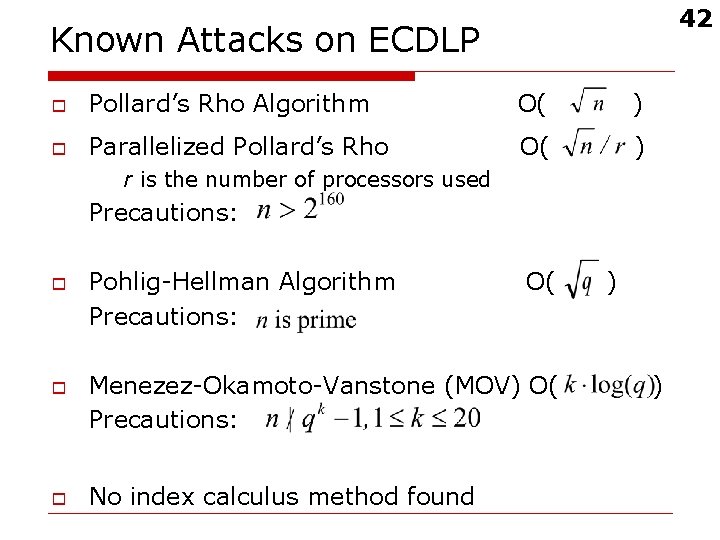
42 Known Attacks on ECDLP o Pollard’s Rho Algorithm O( ) o Parallelized Pollard’s Rho O( ) r is the number of processors used Precautions: o o o Pohlig-Hellman Algorithm Precautions: O( Menezez-Okamoto-Vanstone (MOV) O( Precautions: No index calculus method found ) )
Pollard’s Rho Algorithm(1) 43 To find k where Q=k. P, and n is the group order: o Use a pseudo-random walk through the group o Start at a known point o When a collision occurs, we can find k o Because there is not enough room to store all visited points, we only store distinguished points (points with some distinguishing property, such as the first i lower order bits equal to zero).
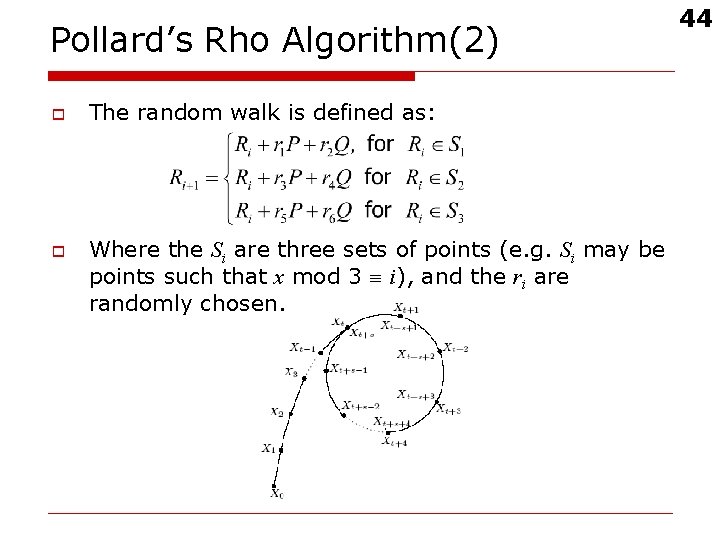
Pollard’s Rho Algorithm(2) o o The random walk is defined as: Where the Si are three sets of points (e. g. Si may be points such that x mod 3 i), and the ri are randomly chosen. 44
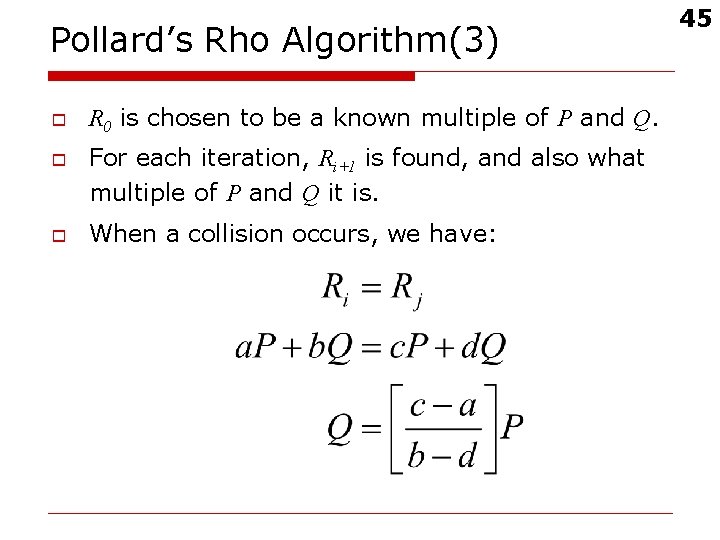
Pollard’s Rho Algorithm(3) o o o R 0 is chosen to be a known multiple of P and Q. For each iteration, Ri+1 is found, and also what multiple of P and Q it is. When a collision occurs, we have: 45
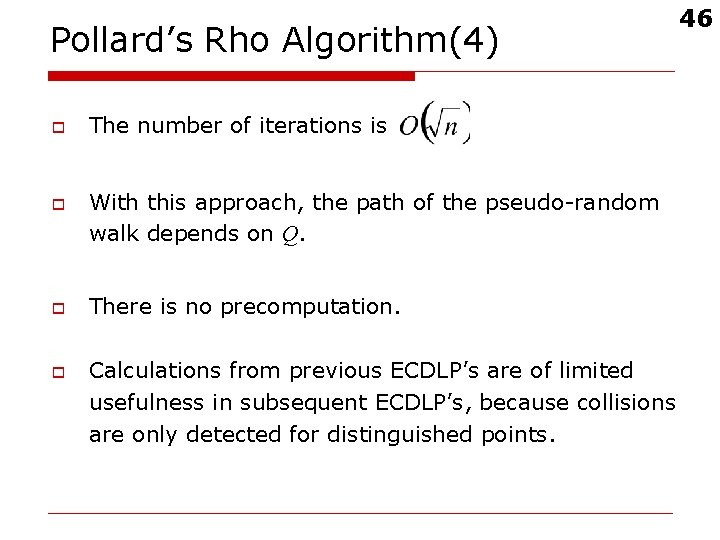
Pollard’s Rho Algorithm(4) o o The number of iterations is With this approach, the path of the pseudo-random walk depends on Q. There is no precomputation. Calculations from previous ECDLP’s are of limited usefulness in subsequent ECDLP’s, because collisions are only detected for distinguished points. 46
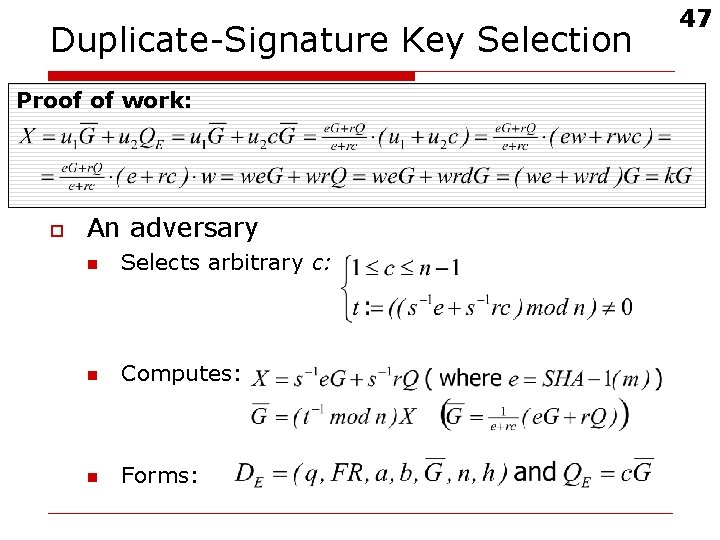
Duplicate-Signature Key Selection Proof of work: D, Q, m, r, s Alice Bob DE, QE, m, r, s Adversary E o An adversary n Selects arbitrary c: n Computes: n Forms: 47
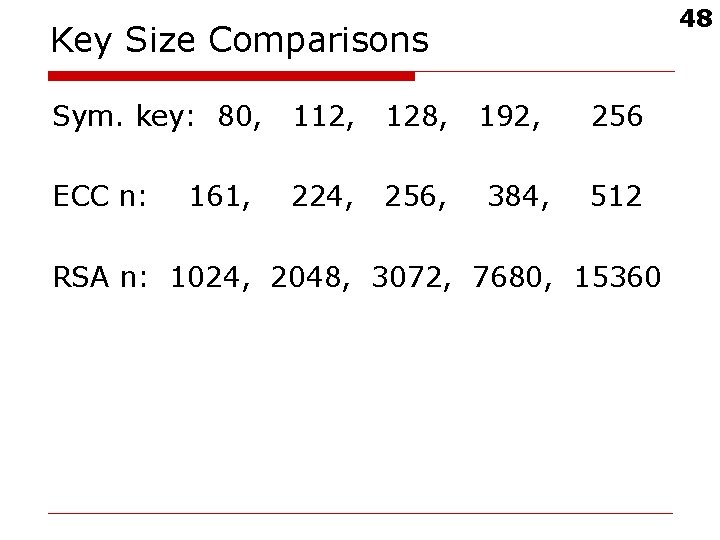
48 Key Size Comparisons Sym. key: 80, 112, 128, ECC n: 224, 256, 161, 192, 384, 256 512 RSA n: 1024, 2048, 3072, 7680, 15360
ECDSA Advantages o o o Elliptic curves offer a much shorter key length than RSA. There are some environments where 1024 -bit RSA can not be implemented, while 163 -bit ECC can. No subexponential-time algorithm is known for the EC discrete logarithm problem. 49
50 Discussion ? ? ?
Exercises(1) o o Does this equation define an EC over GF(17)? y 2 = x 3 + 10 x + 5 Do the points P(2, 0) and Q(6, 3) lie on the elliptic curve y 2 = x 3 + x + 7 over GF(17)? What are the negatives of the following elliptic curve points over GF(17)? P(5, 8) Q(3, 0) R(0, 6) In the elliptic curve group defined by y 2 = x 3 + x + 7 over GF(17), what is P + Q if P = (2, 0) and Q = (1, 3)? 51
Exercises(2) o o Suppose that p > 3 is an odd prime a, b Є GF(p) Further suppose that has 3 distinct roots in GF(p) o Prove that the corresponding elliptic curve E is not cyclic 52
References o o o Don Johnson, Alfred Menezes, The Elliptic Curve Digital Signature, February 2000 http: //www. cacr. math. uwaterloo. ca A. Menezes, P. van Oorschot, S. Vanstone, Handbook of Applied cryptography, CRC Press 1996 http: //www. cacr. math. uwaterloo. ca/hac Douglas R. Stinson Cryptography, Theory and Practice, CRC Press 53
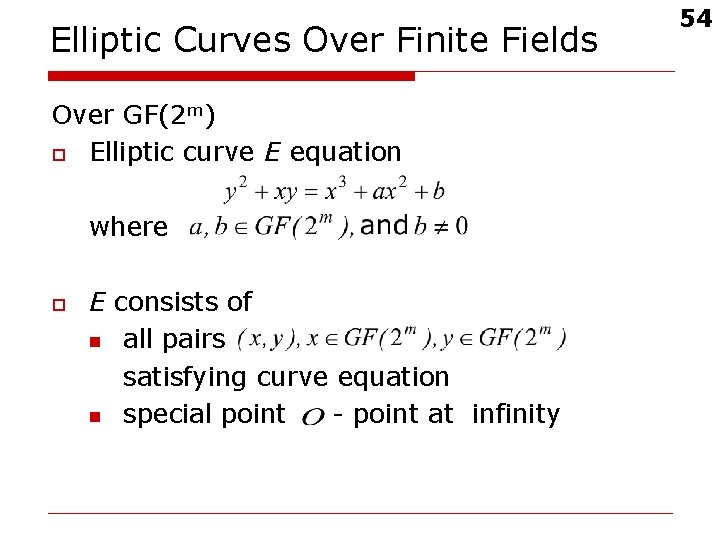
Elliptic Curves Over Finite Fields Over GF(2 m) o Elliptic curve E equation where o E consists of n all pairs satisfying curve equation n special point - point at infinity 54
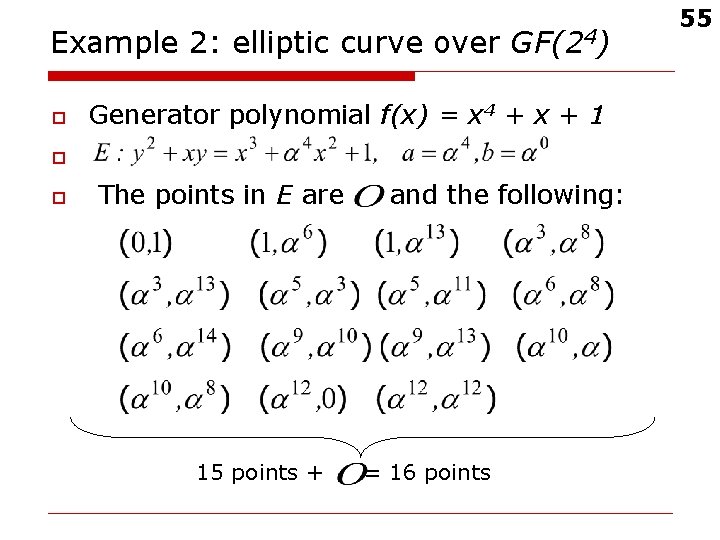
Example 2: elliptic curve over GF(24) o Generator polynomial f(x) = x 4 + x + 1 o o The points in E are 15 points + and the following: = 16 points 55
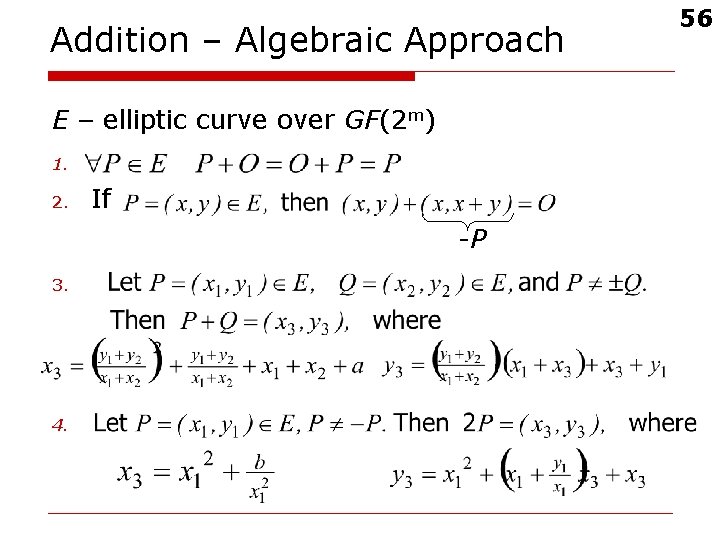
Addition – Algebraic Approach E – elliptic curve over GF(2 m) 1. 2. If -P 3. 4. 56
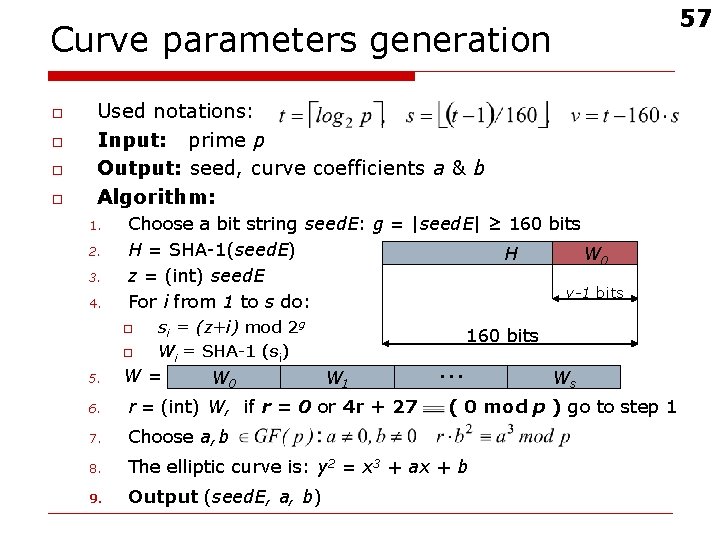
57 Curve parameters generation o o Used notations: Input: prime p Output: seed, curve coefficients a & b Algorithm: 1. 2. 3. 4. Choose a bit string seed. E: g = |seed. E| ≥ 160 bits H = SHA-1(seed. E) H W 0 z = (int) seed. E v-1 bits For i from 1 to s do: o o 5. si = (z+i) mod 2 g Wi = SHA-1 (si) W= W 0 W 1 … 160 bits 6. r = (int) W, if r = 0 or 4 r + 27 7. Choose a, b 8. The elliptic curve is: y 2 = x 3 + ax + b 9. Output (seed. E, a, b) Ws ( 0 mod p ) go to step 1
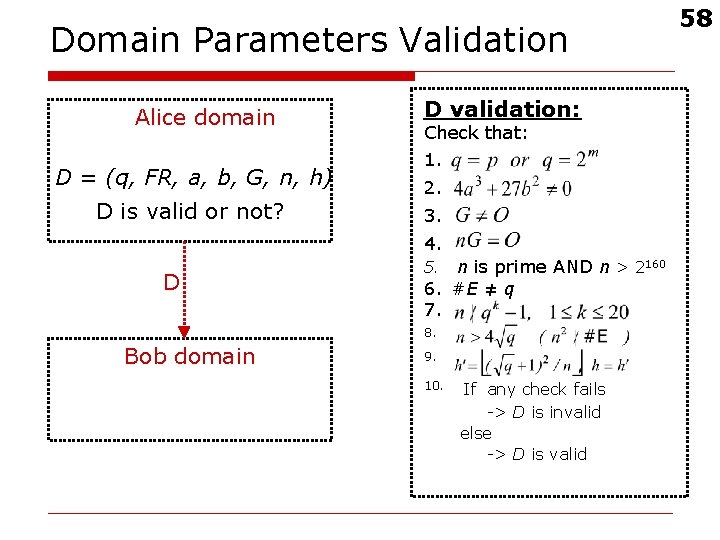
Domain Parameters Validation Alice domain D = (q, FR, a, b, G, n, h) D is valid or not? D validation: Check that: 1. 2. 3. 4. D 5. n is prime AND n > 2160 6. #E ≠ q 7. 8. Bob domain 9. 10. If any check fails -> D is invalid else -> D is valid 58
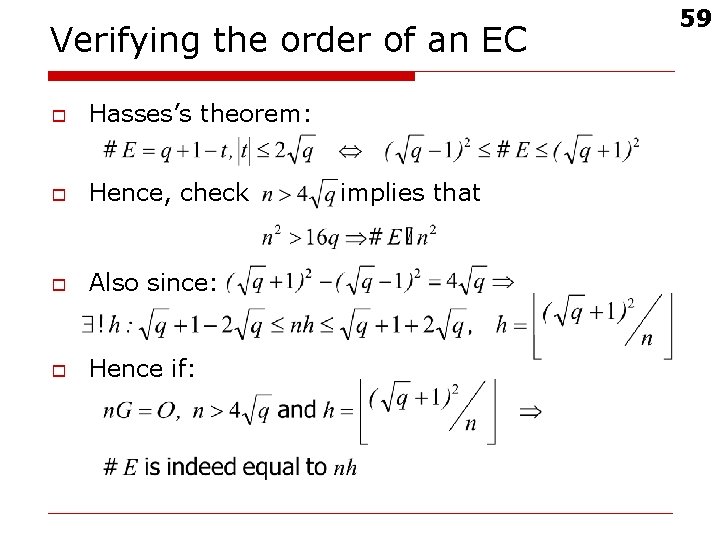
Verifying the order of an EC o Hasses’s theorem: o Hence, check o Also since: o Hence if: implies that 59
Potential CA Services o POP - Proof of possession of private key. Can use zero-knowledge proof. o o PKV - Public Key Validation shows public key makes arithmetic sense. POP and PKV can be considered duals of each other. Doing both provides strong assurance. 60
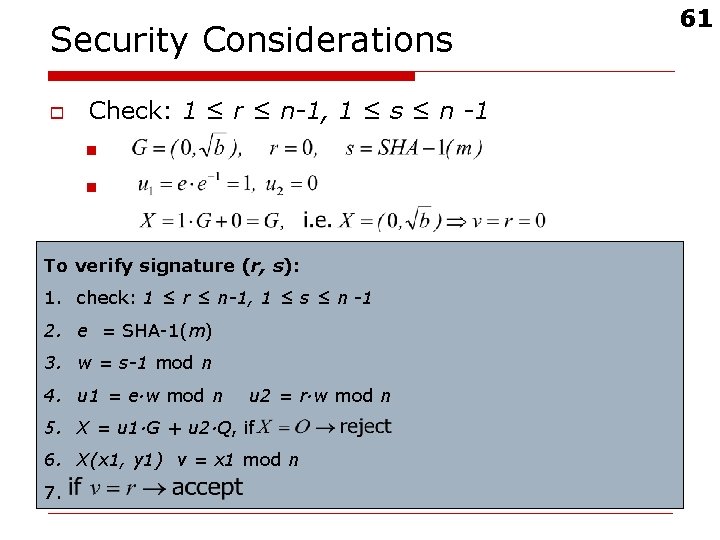
Security Considerations o Check: 1 ≤ r ≤ n-1, 1 ≤ s ≤ n -1 n n o verify Per-message To signature (r, secret s): k: 1. check: 1 ≤ r ≤ n-1, 1 ≤ s ≤ n -1 n 2. e = SHA-1(m) o Repeated usage of k: 3. w = s-1 mod n 4. u 1 = e·w mod n u 2 = r·w mod n 5. X = u 1·G + u 2·Q, if 6. X(x 1, y 1) v = x 1 mod n 7. 61
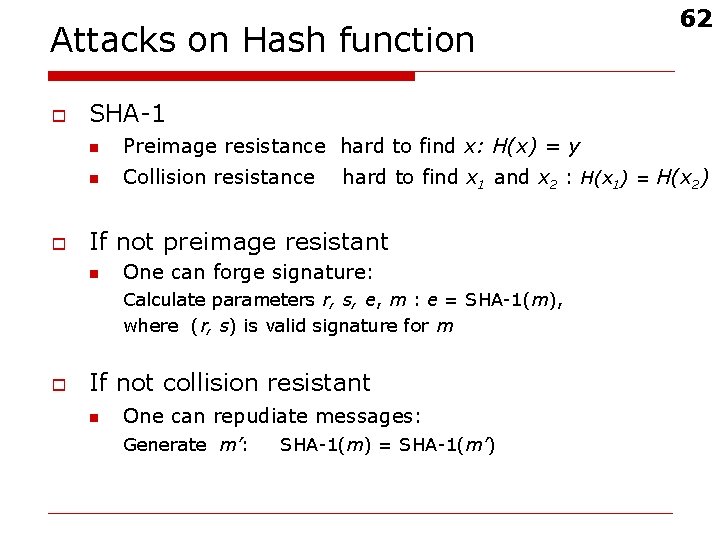
Attacks on Hash function o o SHA-1 n Preimage resistance hard to find x: H(x) = y n Collision resistance hard to find x 1 and x 2 : H(x 1) = H(x 2) If not preimage resistant n One can forge signature: Calculate parameters r, s, e, m : e = SHA-1(m), where (r, s) is valid signature for m o 62 If not collision resistant n One can repudiate messages: Generate m’: SHA-1(m) = SHA-1(m’)
Signature Forgery o Signature Forgery n n A forgery is a signature computed without the signer’s private key selective forgery: an adversary is able to create a valid signature for a particular message chosen a priori n existential forgery – an adversary is able to forge a signature for at least one message 63
- Slides: 63