Digital Signatures DSs The digital signatures cannot be
Digital Signatures (DSs) • The digital signatures cannot be separated from the message and attached to another • The signature is not only tied to signer but also to the message that is being signed • The digital signature needs to be easily verified by other parties • Digital signature schemes therefore consist of two distinct steps: the signing process and the verification process
RSA Signatures • Bob has a document m that Alice agrees to sign. Alice does the following. • Alice chooses two primes: p, q and n=pq, makes (e, n) public with gcd(e, (p-1)(q-1))=1 de≡ 1 (mod φ(n)), she keeps p, q, d secret 。Alice’s signature is y≡md (mod n) 。Alice then makes the pair (y, m) public
How does Bob verify Alice’s Signature • Download Alice’s (e, n) • Compute z≡ye (mod n) • If z=m, then Bob accepts the signature as valid; otherwise the signature is not valid
Blind Signatures (1/2) • Alice chooses n=pq, find e, and solve d as required in RSA scheme, i. e. , ed≡ 1(mod n) • Bod chooses a random k with gcd(k, n)=1, computes t≡kem (mod n) for message m, and sends t to Alice • Alice signs t by computing s≡td (mod n). She returns s to Bob • Bob computes sk-1 (mod n) to get the signed message md
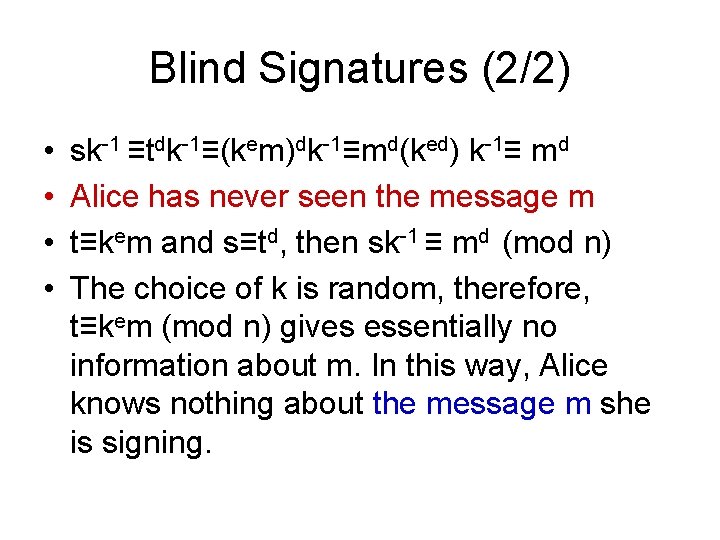
Blind Signatures (2/2) • • sk-1 ≡tdk-1≡(kem)dk-1≡md(ked) k-1≡ md Alice has never seen the message m t≡kem and s≡td, then sk-1 ≡ md (mod n) The choice of k is random, therefore, t≡kem (mod n) gives essentially no information about m. In this way, Alice knows nothing about the message m she is signing.
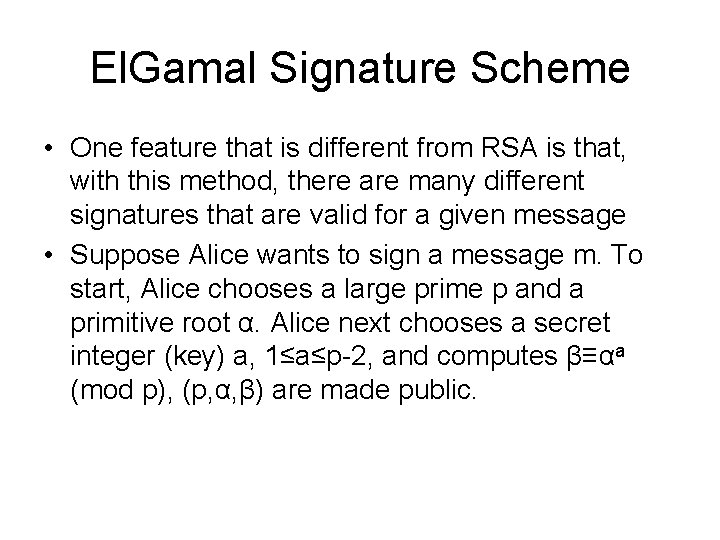
El. Gamal Signature Scheme • One feature that is different from RSA is that, with this method, there are many different signatures that are valid for a given message • Suppose Alice wants to sign a message m. To start, Alice chooses a large prime p and a primitive root α. Alice next chooses a secret integer (key) a, 1≤a≤p-2, and computes β≡αa (mod p), (p, α, β) are made public.
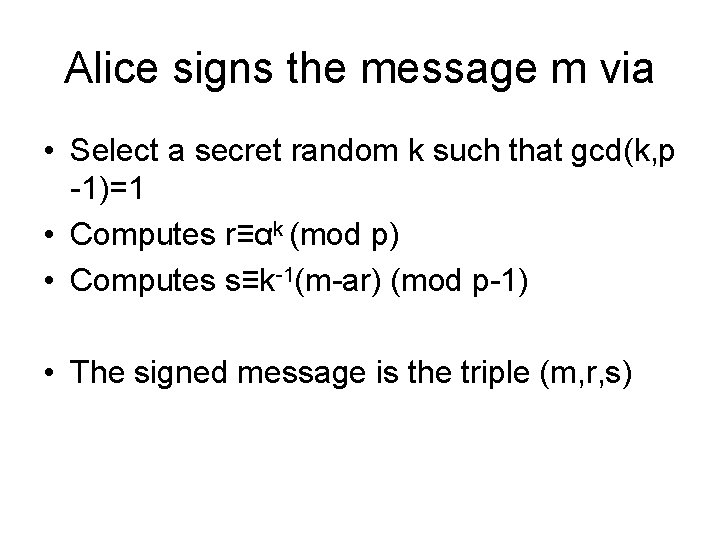
Alice signs the message m via • Select a secret random k such that gcd(k, p -1)=1 • Computes r≡αk (mod p) • Computes s≡k-1(m-ar) (mod p-1) • The signed message is the triple (m, r, s)
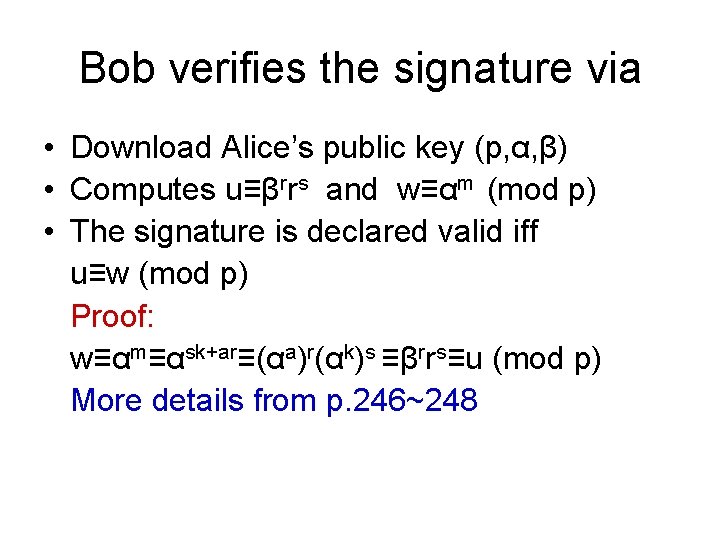
Bob verifies the signature via • Download Alice’s public key (p, α, β) • Computes u≡βrrs and w≡αm (mod p) • The signature is declared valid iff u≡w (mod p) Proof: w≡αm≡αsk+ar≡(αa)r(αk)s ≡βrrs≡u (mod p) More details from p. 246~248
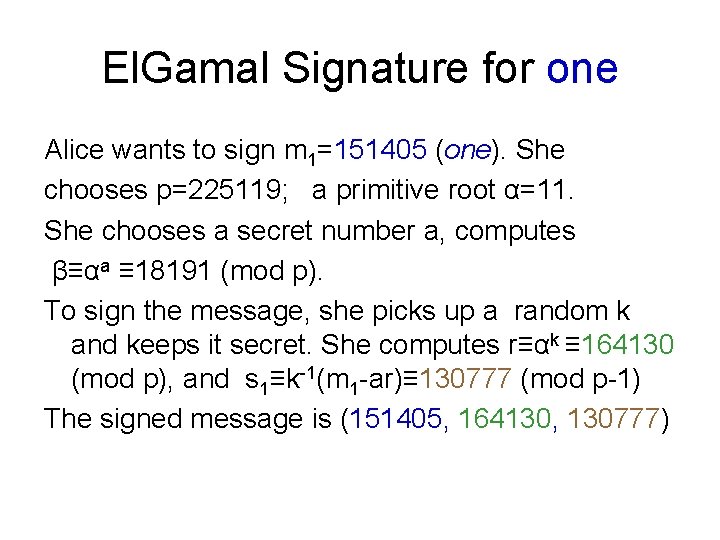
El. Gamal Signature for one Alice wants to sign m 1=151405 (one). She chooses p=225119; a primitive root α=11. She chooses a secret number a, computes β≡αa ≡ 18191 (mod p). To sign the message, she picks up a random k and keeps it secret. She computes r≡αk ≡ 164130 (mod p), and s 1≡k-1(m 1 -ar)≡ 130777 (mod p-1) The signed message is (151405, 164130, 130777)
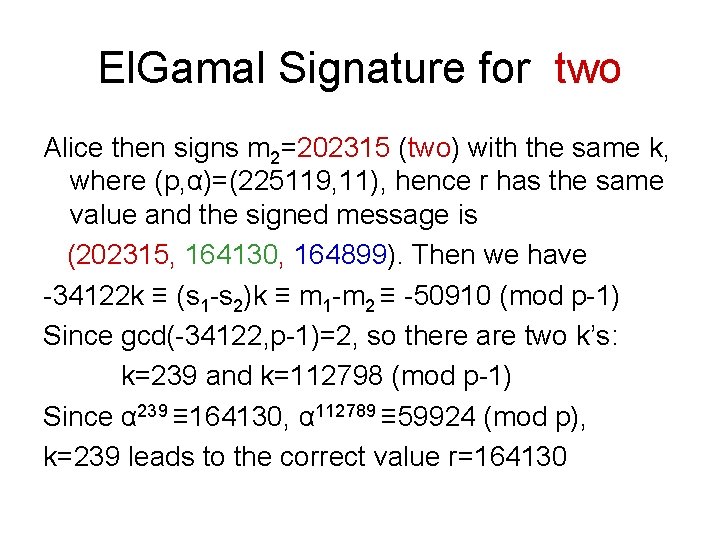
El. Gamal Signature for two Alice then signs m 2=202315 (two) with the same k, where (p, α)=(225119, 11), hence r has the same value and the signed message is (202315, 164130, 164899). Then we have -34122 k ≡ (s 1 -s 2)k ≡ m 1 -m 2 ≡ -50910 (mod p-1) Since gcd(-34122, p-1)=2, so there are two k’s: k=239 and k=112798 (mod p-1) Since α 239 ≡ 164130, α 112789 ≡ 59924 (mod p), k=239 leads to the correct value r=164130
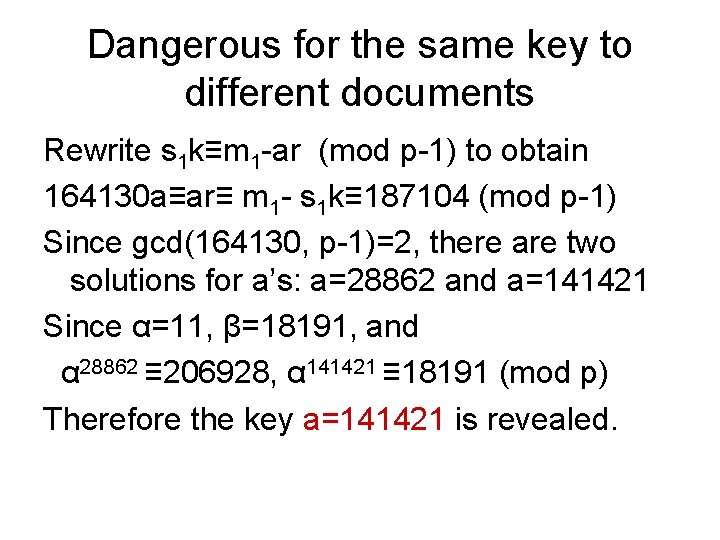
Dangerous for the same key to different documents Rewrite s 1 k≡m 1 -ar (mod p-1) to obtain 164130 a≡ar≡ m 1 - s 1 k≡ 187104 (mod p-1) Since gcd(164130, p-1)=2, there are two solutions for a’s: a=28862 and a=141421 Since α=11, β=18191, and α 28862 ≡ 206928, α 141421 ≡ 18191 (mod p) Therefore the key a=141421 is revealed.
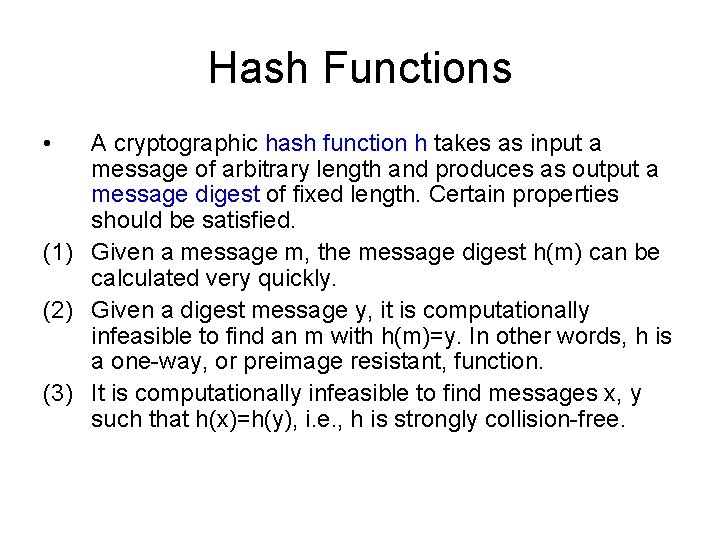
Hash Functions • A cryptographic hash function h takes as input a message of arbitrary length and produces as output a message digest of fixed length. Certain properties should be satisfied. (1) Given a message m, the message digest h(m) can be calculated very quickly. (2) Given a digest message y, it is computationally infeasible to find an m with h(m)=y. In other words, h is a one-way, or preimage resistant, function. (3) It is computationally infeasible to find messages x, y such that h(x)=h(y), i. e. , h is strongly collision-free.
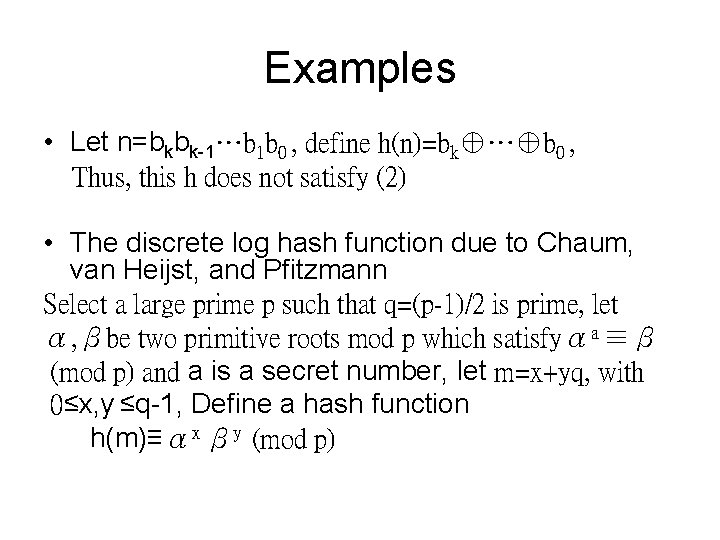
Examples • Let n=bkbk-1…b 1 b 0 , define h(n)=bk⊕…⊕b 0 , Thus, this h does not satisfy (2) • The discrete log hash function due to Chaum, van Heijst, and Pfitzmann Select a large prime p such that q=(p-1)/2 is prime, let α, βbe two primitive roots mod p which satisfyαa ≡β (mod p) and a is a secret number, let m=x+yq, with 0≤x, y ≤q-1, Define a hash function h(m)≡αx βy (mod p)
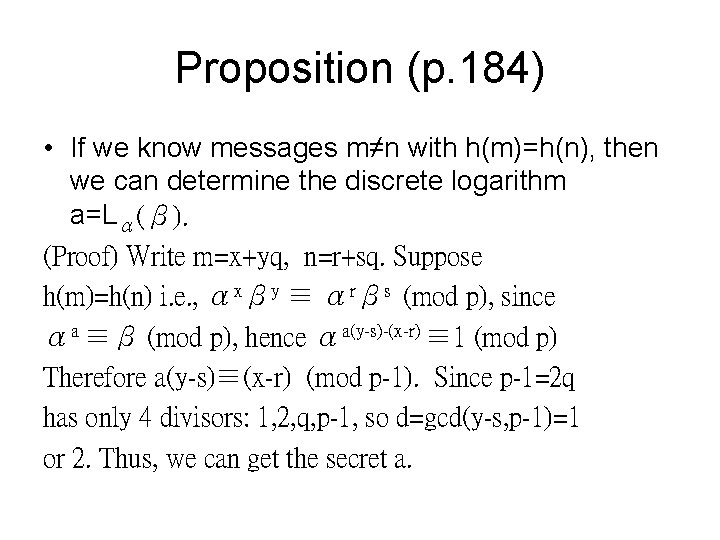
Proposition (p. 184) • If we know messages m≠n with h(m)=h(n), then we can determine the discrete logarithm a=Lα(β). (Proof) Write m=x+yq, n=r+sq. Suppose h(m)=h(n) i. e. , αxβy ≡ αrβs (mod p), since αa ≡β (mod p), hence αa(y-s)-(x-r) ≡ 1 (mod p) Therefore a(y-s)≡(x-r) (mod p-1). Since p-1=2 q has only 4 divisors: 1, 2, q, p-1, so d=gcd(y-s, p-1)=1 or 2. Thus, we can get the secret a.
Other Hash Functions ☺MD family: MD 4, MD 5 due to Rivest ☺NIST’s Secure Hash Algorithm (SHA) which yields a 160 -bit message digest [Stinson] [Schneier] [Menezes et al. ]
Hashing, Signing, and Applications • Sending (m, sig(h(m))) instead of (m, sig(m)) could significantly reduce the size of digital signatures. • An appropriate hash function should be chosen. In particular, in electronic exchanges in E-commerce.
Birthday Attacks • If there are 23 people in a room, the probability 50. 7% that two of them have the same birthday. If there are 30 people, the probability is increasing up to 70%. • The probability of 23 people do not have the same birthday is (1 -1/365)(1 -2/365)…(1 -22/365) = 0. 493
A Birthday Attack on Discrete Log • Suppose we want to evaluate La(b) with a large p. We can do by a birthday attack in the following procedures: 1. The first list contains numbers ak (mod p) for approximately p 1/2 randomly chosen values of k. 2. The first list contains numbers ba-j (mod p) for approximately p 1/2 randomly chosen values of j. There is a good chance that there is a match between some element on the 1 st list and one on the 2 nd list. If so, ak ≡ba-j (mod p) and hence ak+j ≡b (mod p) x≡k+j (mod p-1) is the discrete log solution
Digital Signature Algorithm (DSA) • The NIST proposed the DSA in 1991 and adopted it as a standard in 1994. The message digest is a 160 -bit output of a hash function. The generate keys for DSA proceeds as follows. First, there is an initialization phase:
Initialization Phase • Alice finds a prime q that is 160 bits long and chooses a prime p that satisfies q|p-1. The discrete log problem should be hard for this choice of p (e. g. , p is 512 -bit long). • Let g be a primitive root mod p and let α≡g(p-1)/q (mod p). Then αq ≡ 1 (mod p). • Alice chooses a secret a such that 1≤a<q-1 and calculates β≡αa (mod p) • Alice publishes (p, q, α, β) and keeps a secret
The signing process • 1. 2. 3. 4. Alice signs a message m by the following procedure: Select a random, secret integer k, such that 0<k<q-1 Compute r≡(αk (mod p)) (mod q) Compute s≡k-1(m+ar) (mod q) Alice’s signature for m is (r, s), which she sends to Bob along with m.
Verification • For Bob to verify, he must 1. Download Alice’s public information (p, q, α, β) 2. Compute u≡s-1 m , v≡s-1 r (mod q) 3. Compute w≡( αuβv (mod p)) (mod q) 4. Accept the signature iff w=r
Simple Exercises from p. 252 -255 • Exercises 1, 2, 3, 4 • Computer Problem 1
- Slides: 23