Chapter 2 Crypto Basics MXDXBVTZWVMXNSPBQXLIMSCCSGXSCJXBOVQXCJZMOJZCVC TVWJCZAAXZBCSSCJXBQCJZCOJZCNSPOXBXSBTVWJC JZDXGXXMOZQMSCSCJXBOVQXCJZMOJZCNSPJZHGXXMOSPLH JZDXZAAXZBXHCSCJXTCSGXSCJXBOVQX
Chapter 2: Crypto Basics MXDXBVTZWVMXNSPBQXLIMSCCSGXSCJXBOVQXCJZMOJZCVC TVWJCZAAXZBCSSCJXBQCJZCOJZCNSPOXBXSBTVWJC JZDXGXXMOZQMSCSCJXBOVQXCJZMOJZCNSPJZHGXXMOSPLH JZDXZAAXZBXHCSCJXTCSGXSCJXBOVQX plaintext from Lewis Carroll, Alice in Wonderland The solution is by no means so difficult as you might be led to imagine from the first hasty inspection of the characters. These characters, as any one might readily guess, form a cipher that is to say, they convey a meaning… Edgar Allan Poe, The Gold Bug Part 1 Cryptography 1
Crypto • Cryptology The art and science of making and breaking “secret codes” • Cryptography making “secret codes” • Cryptanalysis breaking “secret codes” • Crypto all of the above (and more) • A cryptographer is someone who uses and studies secret codes • A cryptanalyst is someone who can hack secret codes and read other people’s encrypted messages Part 1 Cryptography 2
How to Speak Crypto cipher or cryptosystem is used to encrypt the plaintext The result of encryption is ciphertext We decrypt ciphertext to recover plaintext key is used to configure a cryptosystem symmetric key cryptosystem uses the same key to encrypt as to decrypt • public key cryptosystem uses a public key to encrypt and a private key to decrypt • • • So, a cipher is a set of rules (algorithm) for converting between plaintext and ciphertext Part 1 Cryptography 3
4 Problems Addressed by Encryption • Suppose a sender wants to send a message to a recipient. An attacker may attempt to • Block the message • Intercept the message • Modify the message • Fabricate an authentic-looking alternate message From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
5 Encryption Terminology • Sender • Recipient • Transmission medium • Interceptor/intruder • Encrypt, encode, or encipher • Decrypt, decode, or decipher • Cryptosystem • Plaintext • Ciphertext From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
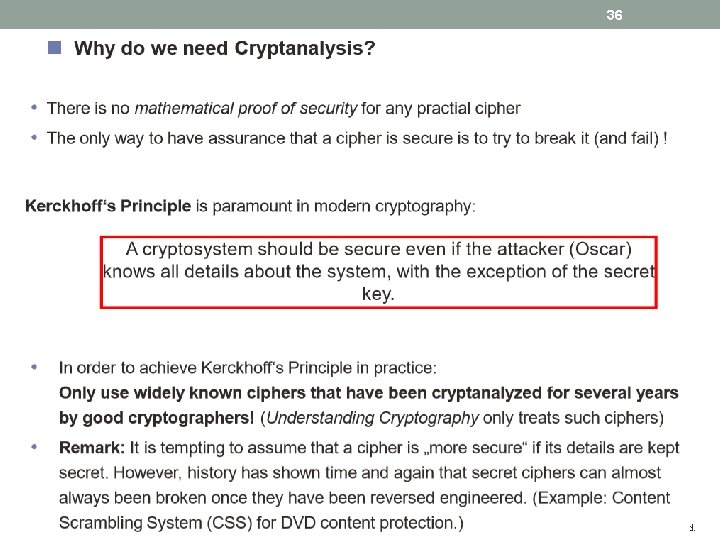
Crypto • Basic assumptions – The system is completely known to the attacker – Only the key is secret – That is, crypto algorithms are not secret • This is known as Kerckhoffs’ Principle • Why do we make such an assumption? – Experience has shown that secret algorithms tend to be weak when exposed ! – Secret algorithms never remain secret ! – Better to find weaknesses beforehand !! Part 1 Cryptography 6
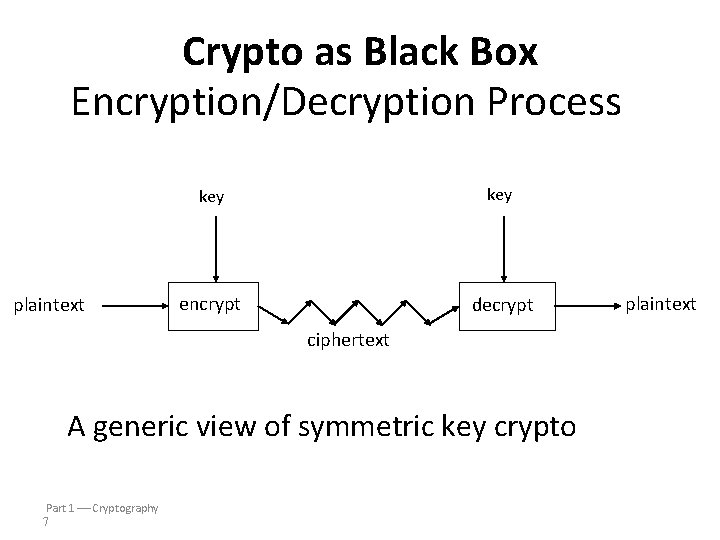
Crypto as Black Box Encryption/Decryption Process plaintext key encrypt decrypt ciphertext A generic view of symmetric key crypto Part 1 Cryptography 7 plaintext
Symmetric vs. Asymmetric
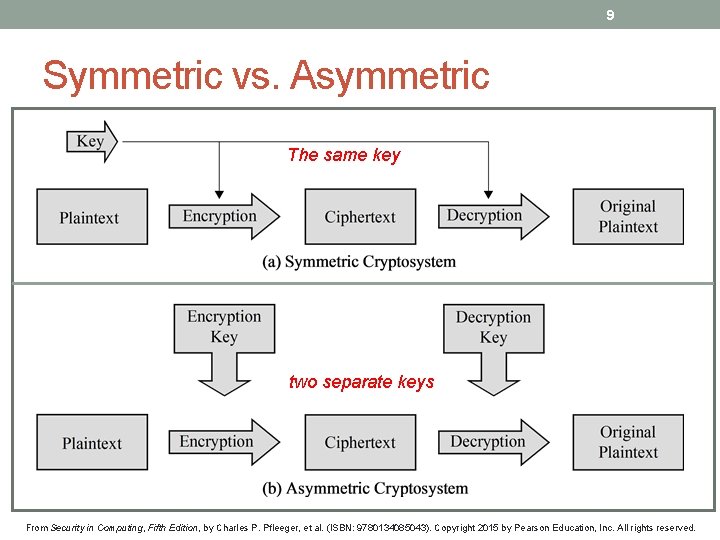
9 Symmetric vs. Asymmetric The same key two separate keys From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
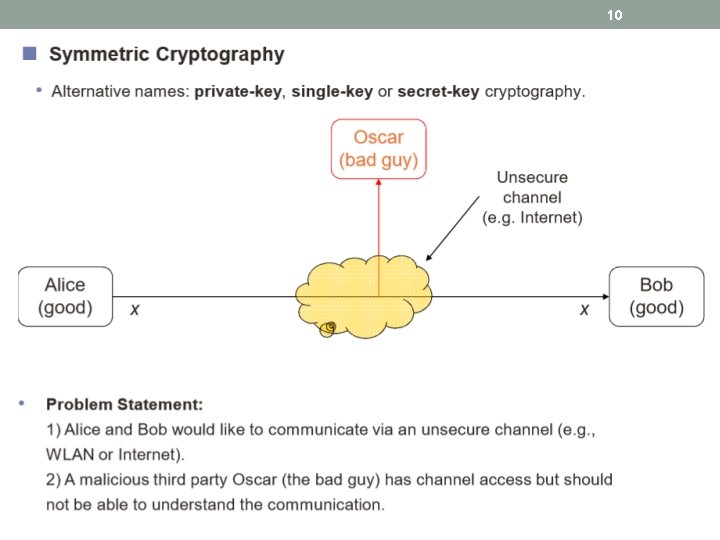
10
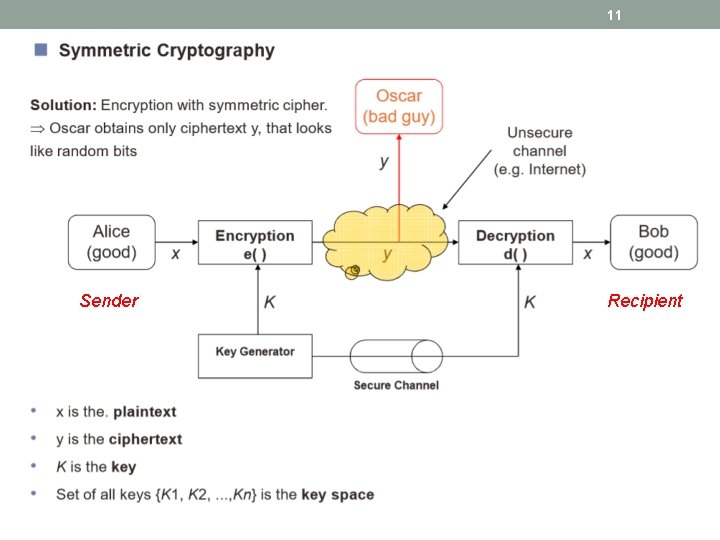
11 Sender Recipient
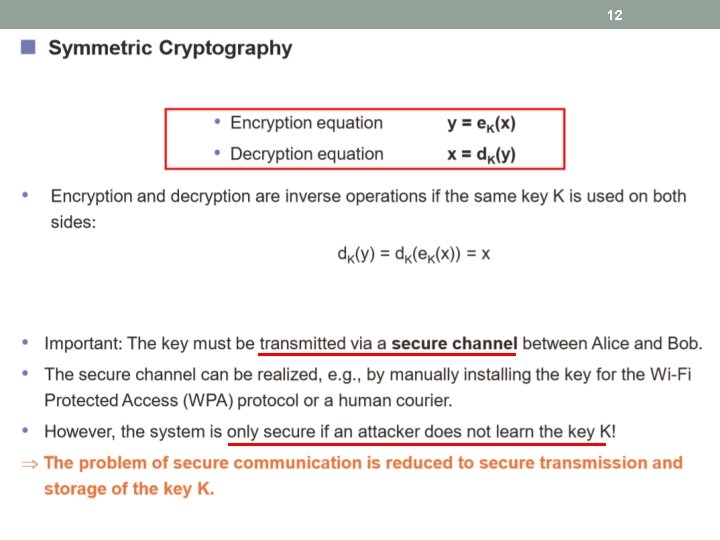
12
13 Stream vs. Block From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.

14 Classification of the Field of Cryptology From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
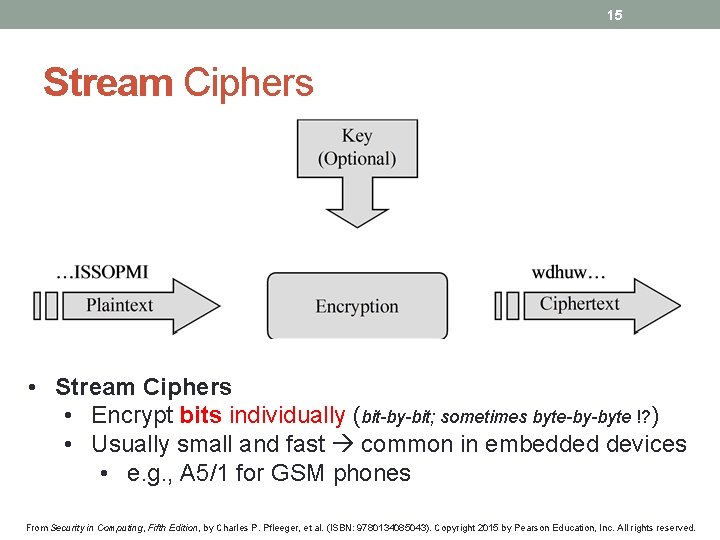
15 Stream Ciphers • Stream Ciphers • Encrypt bits individually (bit-by-bit; sometimes byte-by-byte !? ) • Usually small and fast common in embedded devices • e. g. , A 5/1 for GSM phones From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
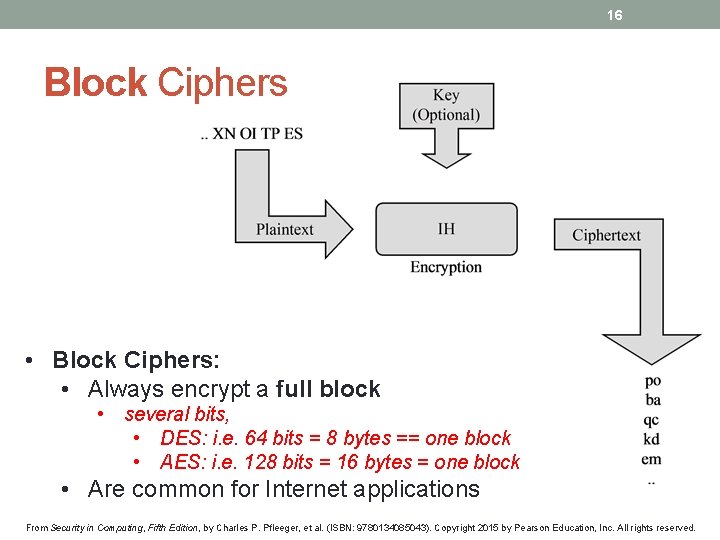
16 Block Ciphers • Block Ciphers: • Always encrypt a full block • several bits, • DES: i. e. 64 bits = 8 bytes == one block • AES: i. e. 128 bits = 16 bytes = one block • Are common for Internet applications From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
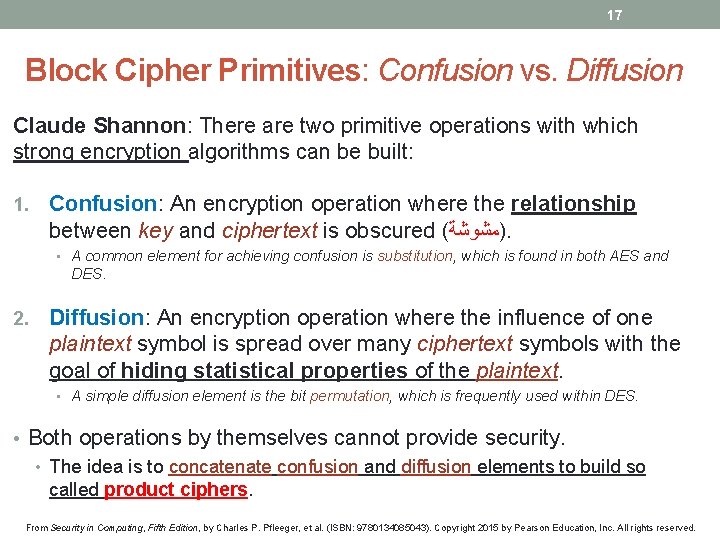
17 Block Cipher Primitives: Confusion vs. Diffusion Claude Shannon: There are two primitive operations with which strong encryption algorithms can be built: 1. Confusion: An encryption operation where the relationship between key and ciphertext is obscured ( )ﻣﺸﻮﺷﺔ. • A common element for achieving confusion is substitution, which is found in both AES and DES. 2. Diffusion: An encryption operation where the influence of one plaintext symbol is spread over many ciphertext symbols with the goal of hiding statistical properties of the plaintext. • A simple diffusion element is the bit permutation, which is frequently used within DES. • Both operations by themselves cannot provide security. • The idea is to concatenate confusion and diffusion elements to build so called product ciphers. From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
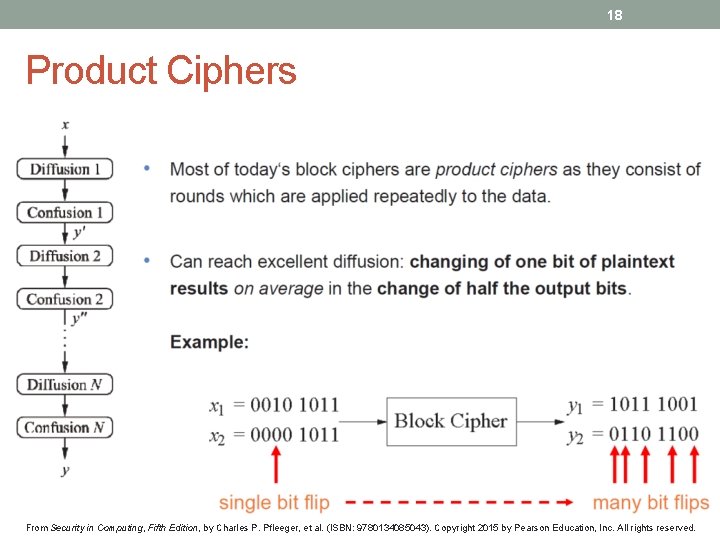
18 Product Ciphers From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
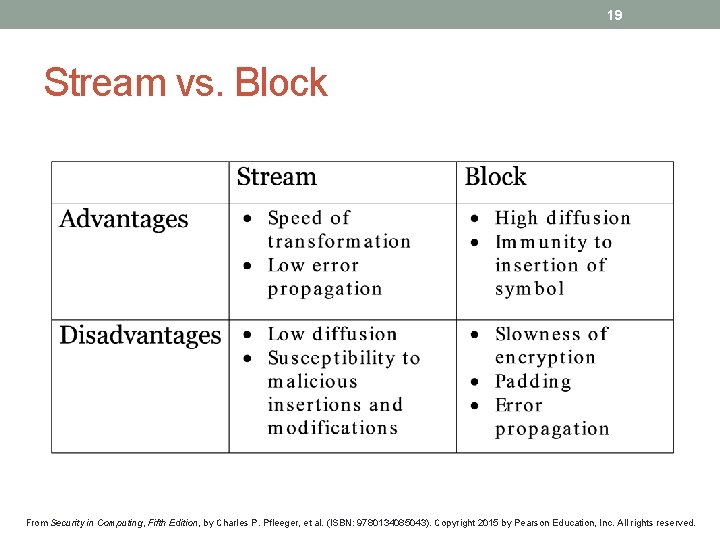
19 Stream vs. Block From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
20 Common Symmetric Encryption Methods From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
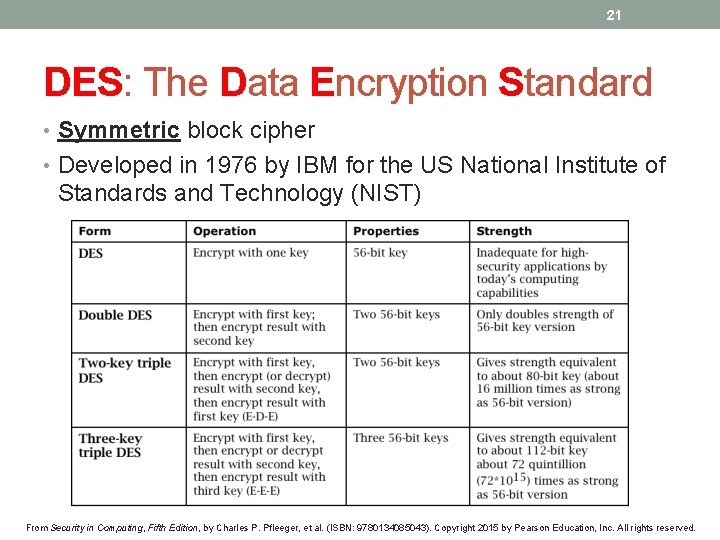
21 DES: The Data Encryption Standard • Symmetric block cipher • Developed in 1976 by IBM for the US National Institute of Standards and Technology (NIST) From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
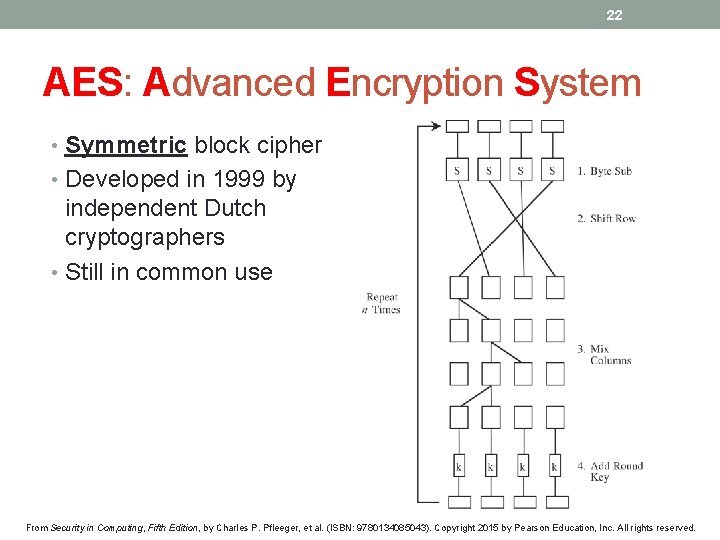
22 AES: Advanced Encryption System • Symmetric block cipher • Developed in 1999 by independent Dutch cryptographers • Still in common use From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
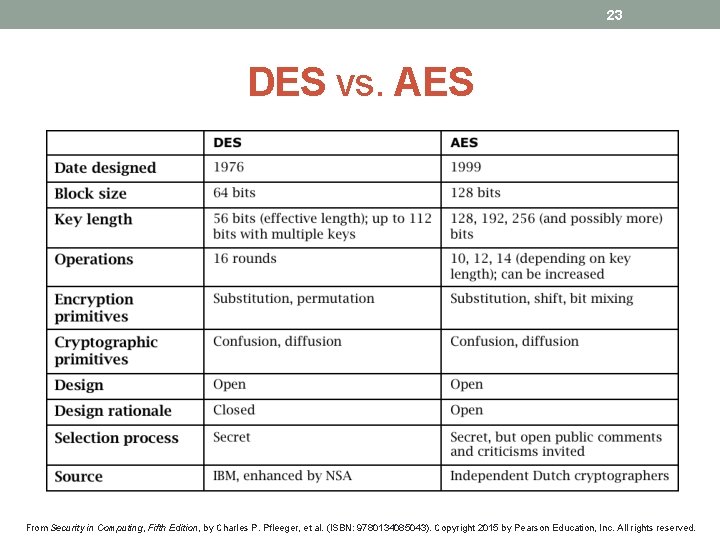
23 DES vs. AES From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
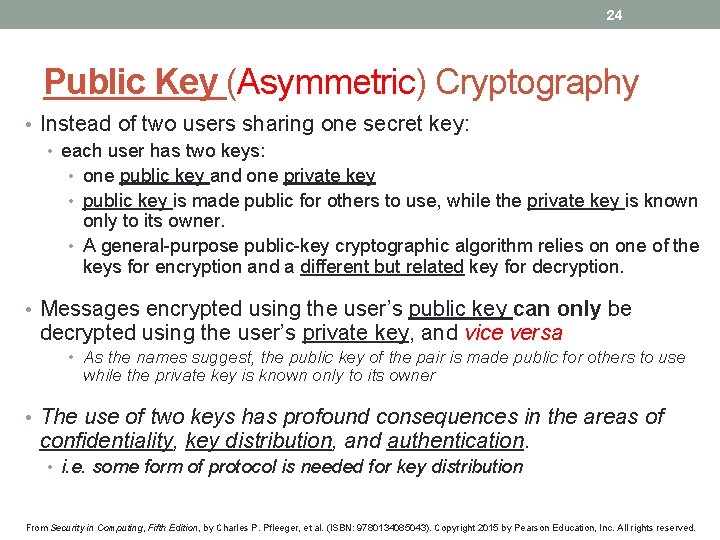
24 Public Key (Asymmetric) Cryptography • Instead of two users sharing one secret key: • each user has two keys: • one public key and one private key • public key is made public for others to use, while the private key is known only to its owner. • A general-purpose public-key cryptographic algorithm relies on one of the keys for encryption and a different but related key for decryption. • Messages encrypted using the user’s public key can only be decrypted using the user’s private key, and vice versa • As the names suggest, the public key of the pair is made public for others to use while the private key is known only to its owner • The use of two keys has profound consequences in the areas of confidentiality, key distribution, and authentication. • i. e. some form of protocol is needed for key distribution From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
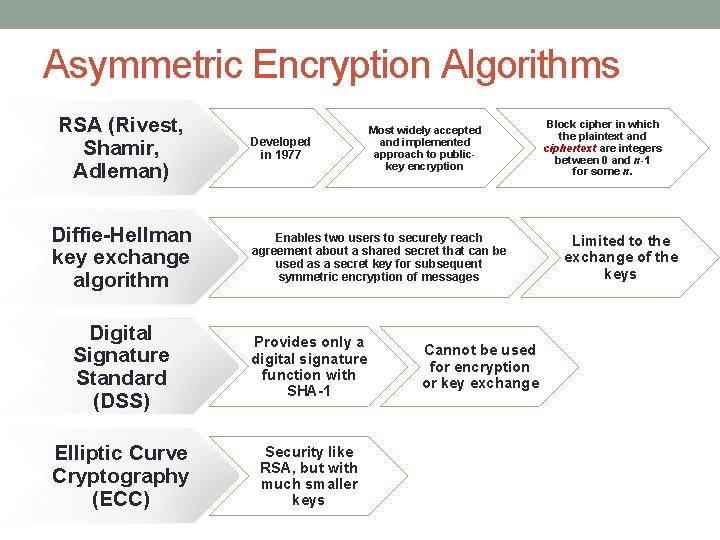
Asymmetric Encryption Algorithms RSA (Rivest, Shamir, Adleman) Diffie-Hellman key exchange algorithm Developed in 1977 Most widely accepted and implemented approach to publickey encryption Enables two users to securely reach agreement about a shared secret that can be used as a secret key for subsequent symmetric encryption of messages Digital Signature Standard (DSS) Provides only a digital signature function with SHA-1 Elliptic Curve Cryptography (ECC) Security like RSA, but with much smaller keys Cannot be used for encryption or key exchange Block cipher in which the plaintext and ciphertext are integers between 0 and n-1 for some n. Limited to the exchange of the keys
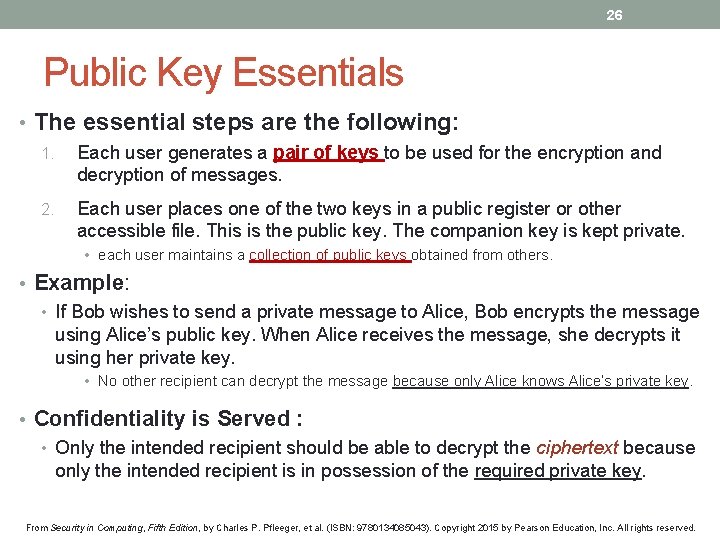
26 Public Key Essentials • The essential steps are the following: 1. Each user generates a pair of keys to be used for the encryption and decryption of messages. 2. Each user places one of the two keys in a public register or other accessible file. This is the public key. The companion key is kept private. • each user maintains a collection of public keys obtained from others. • Example: • If Bob wishes to send a private message to Alice, Bob encrypts the message using Alice’s public key. When Alice receives the message, she decrypts it using her private key. • No other recipient can decrypt the message because only Alice knows Alice’s private key. • Confidentiality is Served : • Only the intended recipient should be able to decrypt the ciphertext because only the intended recipient is in possession of the required private key. From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
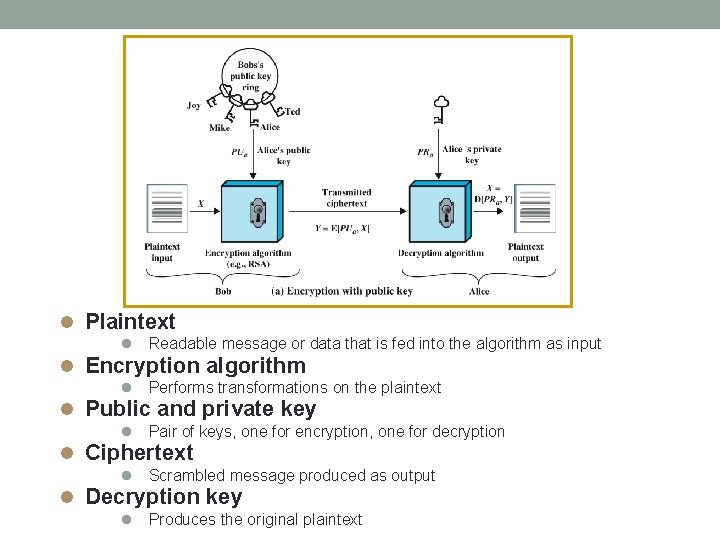
Plaintext Readable message or data that is fed into the algorithm as input Encryption algorithm Performs transformations on the plaintext Public and private key Pair of keys, one for encryption, one for decryption Ciphertext Scrambled message produced as output Decryption key Produces the original plaintext
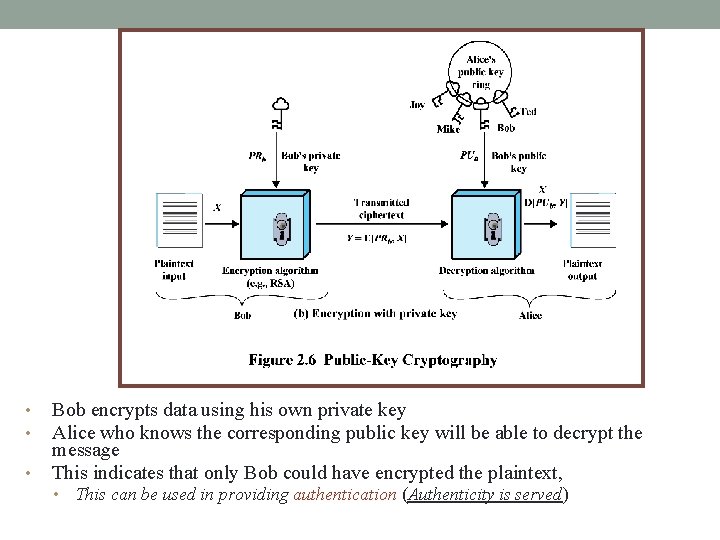
• • • Bob encrypts data using his own private key Alice who knows the corresponding public key will be able to decrypt the message This indicates that only Bob could have encrypted the plaintext, • This can be used in providing authentication (Authenticity is served)
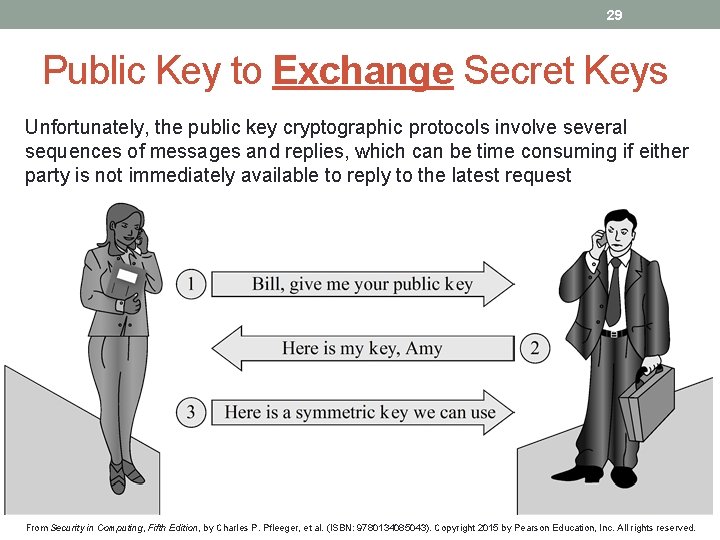
29 Public Key to Exchange Secret Keys Unfortunately, the public key cryptographic protocols involve several sequences of messages and replies, which can be time consuming if either party is not immediately available to reply to the latest request From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
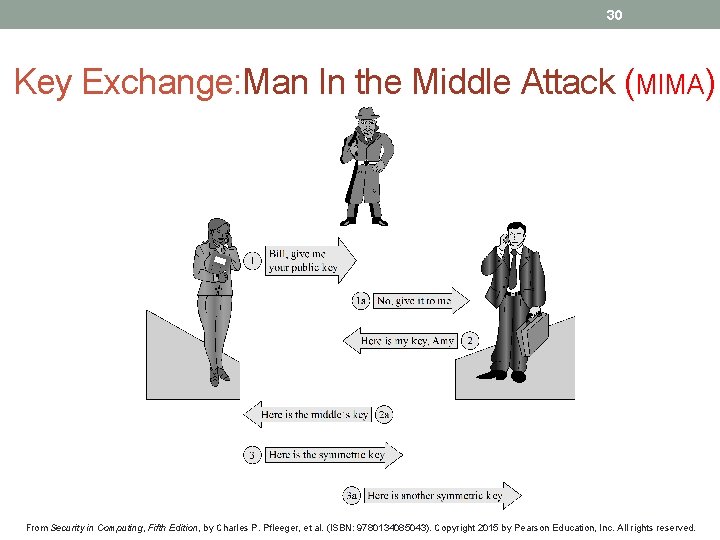
30 Key Exchange: Man In the Middle Attack (MIMA) From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
31 Public-key : Common Misconceptions 1. First misconception is that public-key encryption is more secure from cryptanalysis point of view than symmetric encryption. • In fact, the security of any encryption scheme depends on • (1) the length of the key and (2) the computational work involved in breaking a cipher. • There is nothing in principle about either symmetric or public-key that makes one superior to another 2. A second misconception is that public-key encryption is a generalpurpose technique that has made symmetric encryption obsolete. • On the contrary, because of the computational overhead of current public-key encryption schemes, there seems no foreseeable likelihood that symmetric encryption will be abandoned. 3. Finally, there is a feeling that key distribution is trivial when using publickey encryption, compared to the rather cumbersome handshaking involved with key distribution centers for symmetric encryption. • For public-key distribution, some form of protocol is needed, often involving a central agent, and the procedures involved are no simpler or any more efficient than those required for symmetric encryption. From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
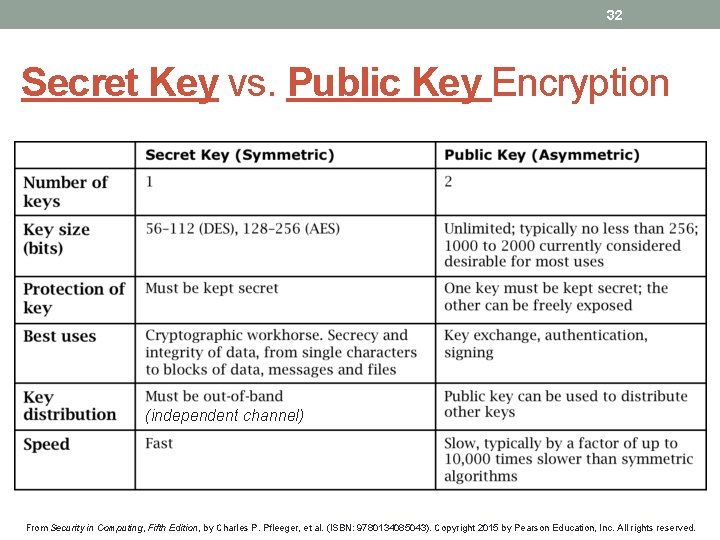
32 Secret Key vs. Public Key Encryption (independent channel) From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
33 Cryptanalysis If the attack is not carried by a brute-force approach, then it is based on one way of Cryptanalysis Methods? ! From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
34 Methods of Cryptanalysis • Break (decrypt) a single message • Recognize patterns in encrypted messages • Infer some meaning without even breaking the encryption • such as from the length or frequency of messages • Easily deduce/infer the key to break one message and perhaps subsequent ones • Find weaknesses (error, bug, flaw) in the implementation or environment of use of encryption by the sender • Find general weaknesses in an encryption algorithm From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
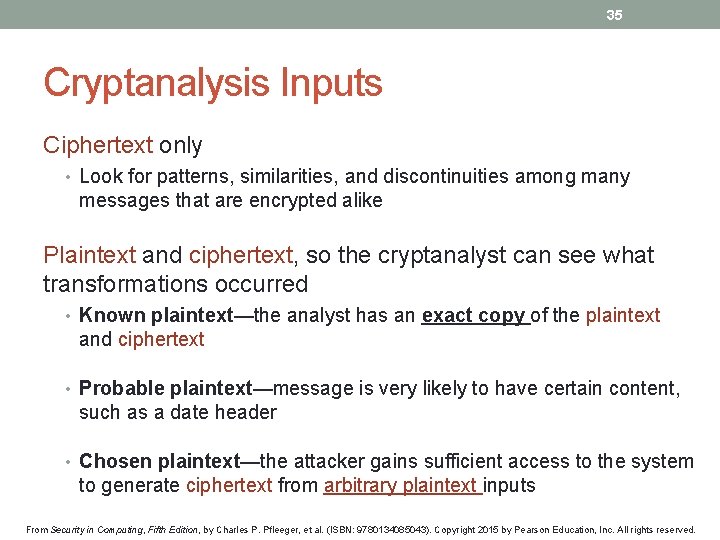
35 Cryptanalysis Inputs Ciphertext only • Look for patterns, similarities, and discontinuities among many messages that are encrypted alike Plaintext and ciphertext, so the cryptanalyst can see what transformations occurred • Known plaintext—the analyst has an exact copy of the plaintext and ciphertext • Probable plaintext—message is very likely to have certain content, such as a date header • Chosen plaintext—the attacker gains sufficient access to the system to generate ciphertext from arbitrary plaintext inputs From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
36 From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.

37 From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
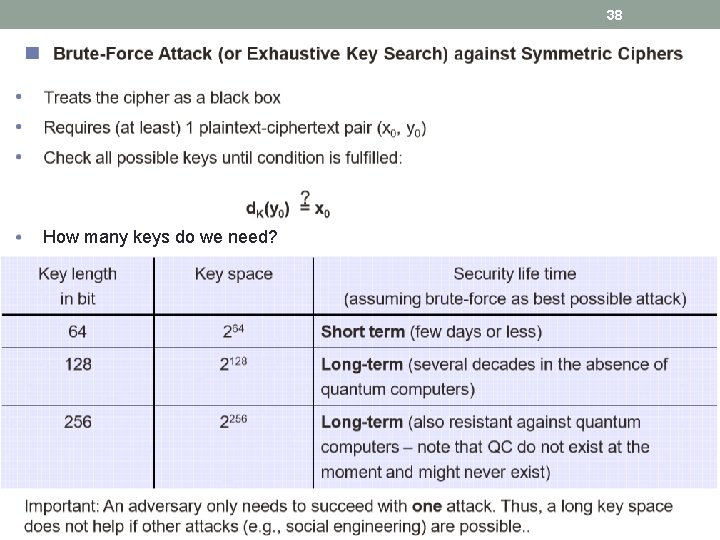
38 How many keys do we need? From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
39 Examples of Encryption Methods From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
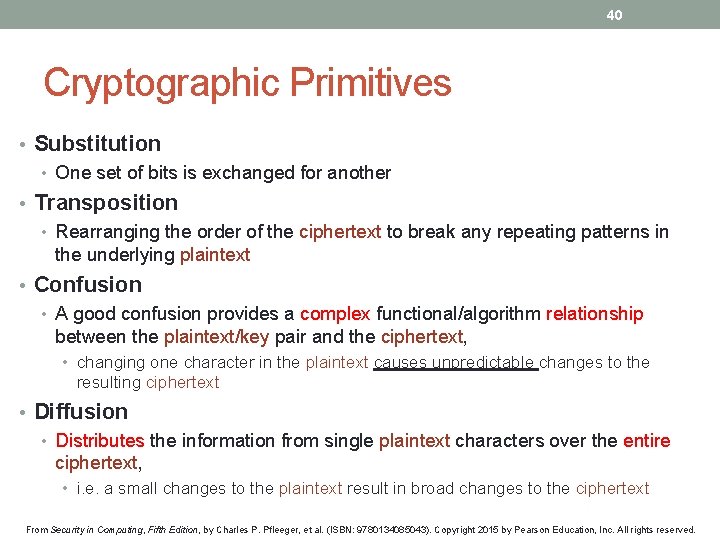
40 Cryptographic Primitives • Substitution • One set of bits is exchanged for another • Transposition • Rearranging the order of the ciphertext to break any repeating patterns in the underlying plaintext • Confusion • A good confusion provides a complex functional/algorithm relationship between the plaintext/key pair and the ciphertext, • changing one character in the plaintext causes unpredictable changes to the resulting ciphertext • Diffusion • Distributes the information from single plaintext characters over the entire ciphertext, • i. e. a small changes to the plaintext result in broad changes to the ciphertext From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
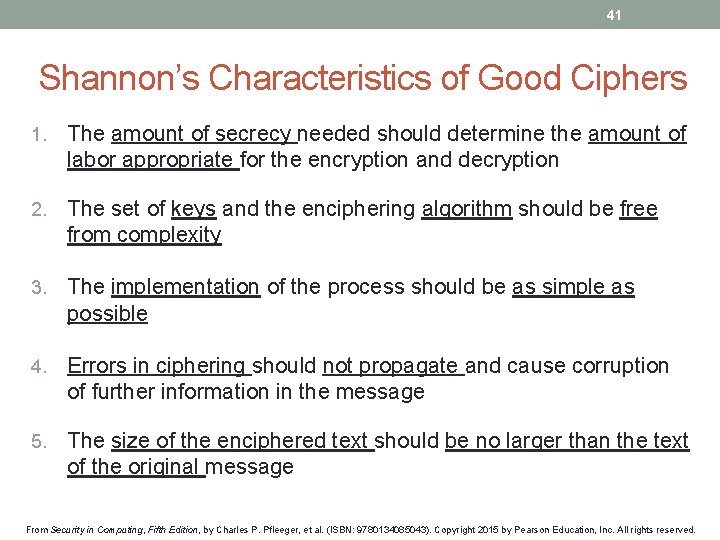
41 Shannon’s Characteristics of Good Ciphers 1. The amount of secrecy needed should determine the amount of labor appropriate for the encryption and decryption 2. The set of keys and the enciphering algorithm should be free from complexity 3. The implementation of the process should be as simple as possible 4. Errors in ciphering should not propagate and cause corruption of further information in the message 5. The size of the enciphered text should be no larger than the text of the original message From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
42 Properties of a Trustworthy Cryptosystem • It is based on sound mathematics • It has been analyzed by competent experts and found to be sound • It has stood the test of time From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
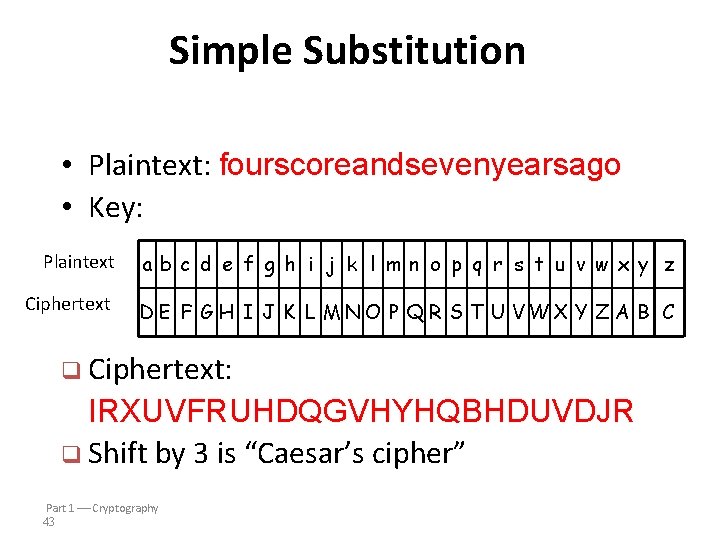
Simple Substitution • Plaintext: fourscoreandsevenyearsago • Key: Plaintext ab c d e f g h i j k l mn o p q r s t u v w x y z Ciphertext D E F G H I J K L MN O P Q R S T U VWX Y Z A B C q Ciphertext: IRXUVFRUHDQGVHYHQBHDUVDJR q Shift by 3 is “Caesar’s cipher” Part 1 Cryptography 43
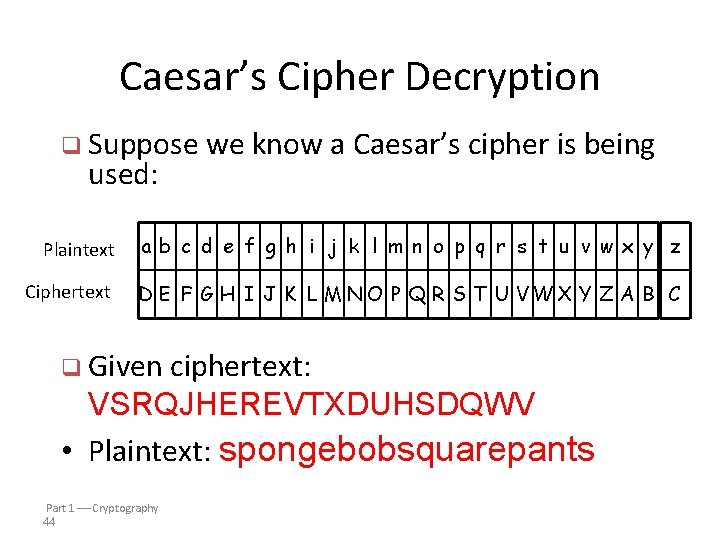
Caesar’s Cipher Decryption q Suppose we know a used: Caesar’s cipher is being Plaintext ab c d e f g h i j k l m n o p q r s t u v w x y z Ciphertext D E F G H I J K L MN O P Q R S T U VWX Y Z A B C q Given ciphertext: VSRQJHEREVTXDUHSDQWV • Plaintext: spongebobsquarepants Part 1 Cryptography 44
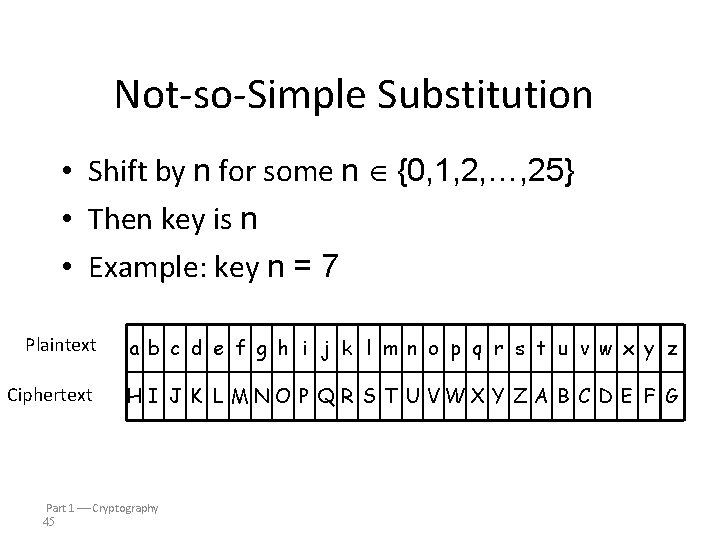
Not-so-Simple Substitution • Shift by n for some n {0, 1, 2, …, 25} • Then key is n • Example: key n = 7 Plaintext a b c d e f g h i j k l m n o p q r s t u v w x y z Ciphertext H I J K L MN O P Q R S T U VWX Y Z A B C D E F G Part 1 Cryptography 45
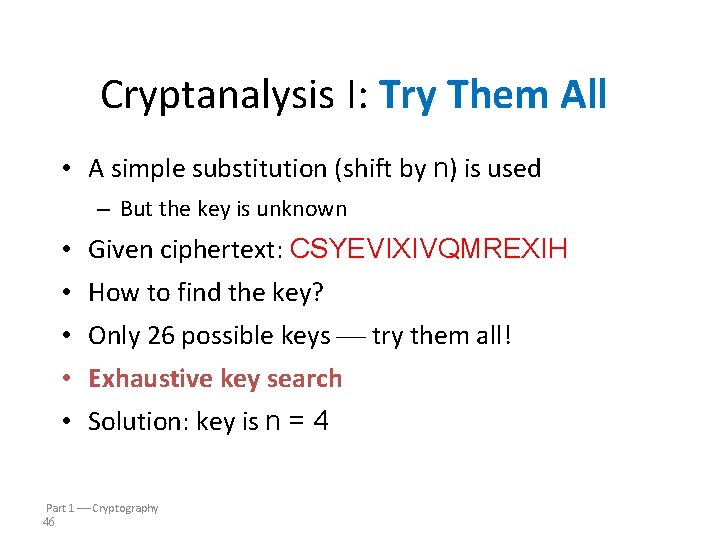
Cryptanalysis I: Try Them All • A simple substitution (shift by n) is used – But the key is unknown • Given ciphertext: CSYEVIXIVQMREXIH • How to find the key? • Only 26 possible keys try them all! • Exhaustive key search • Solution: key is n = 4 Part 1 Cryptography 46
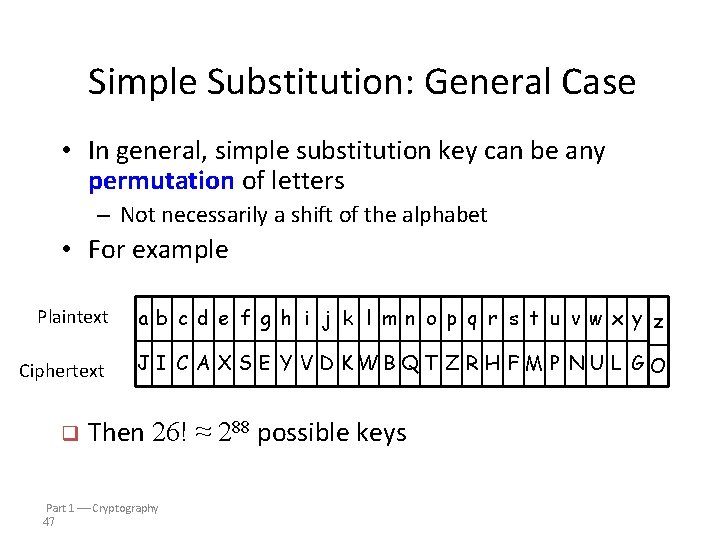
Simple Substitution: General Case • In general, simple substitution key can be any permutation of letters – Not necessarily a shift of the alphabet • For example Plaintext ab c d e f g h i j k l mn o p q r s t u v wx y z Ciphertext J I C A X S E Y V D KWB QT Z R H F M P N U L G O q Then 26! ≈ 288 possible keys Part 1 Cryptography 47
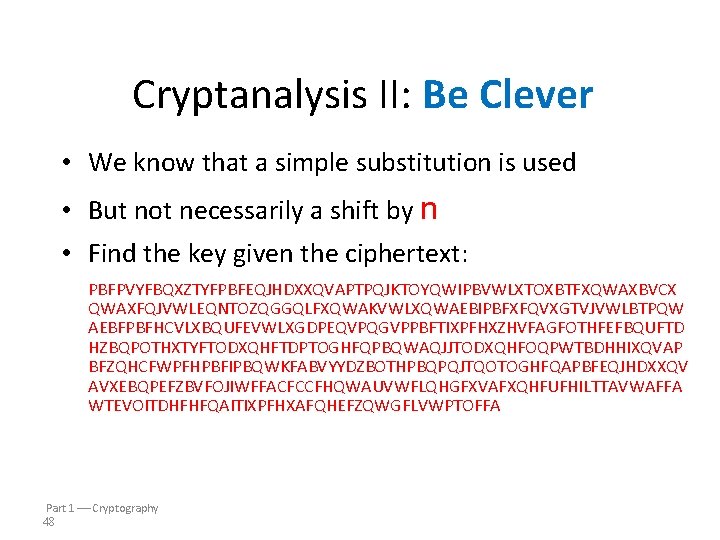
Cryptanalysis II: Be Clever • We know that a simple substitution is used • But not necessarily a shift by n • Find the key given the ciphertext: PBFPVYFBQXZTYFPBFEQJHDXXQVAPTPQJKTOYQWIPBVWLXTOXBTFXQWAXBVCX QWAXFQJVWLEQNTOZQGGQLFXQWAKVWLXQWAEBIPBFXFQVXGTVJVWLBTPQW AEBFPBFHCVLXBQUFEVWLXGDPEQVPQGVPPBFTIXPFHXZHVFAGFOTHFEFBQUFTD HZBQPOTHXTYFTODXQHFTDPTOGHFQPBQWAQJJTODXQHFOQPWTBDHHIXQVAP BFZQHCFWPFHPBFIPBQWKFABVYYDZBOTHPBQPQJTQOTOGHFQAPBFEQJHDXXQV AVXEBQPEFZBVFOJIWFFACFCCFHQWAUVWFLQHGFXVAFXQHFUFHILTTAVWAFFA WTEVOITDHFHFQAITIXPFHXAFQHEFZQWGFLVWPTOFFA Part 1 Cryptography 48
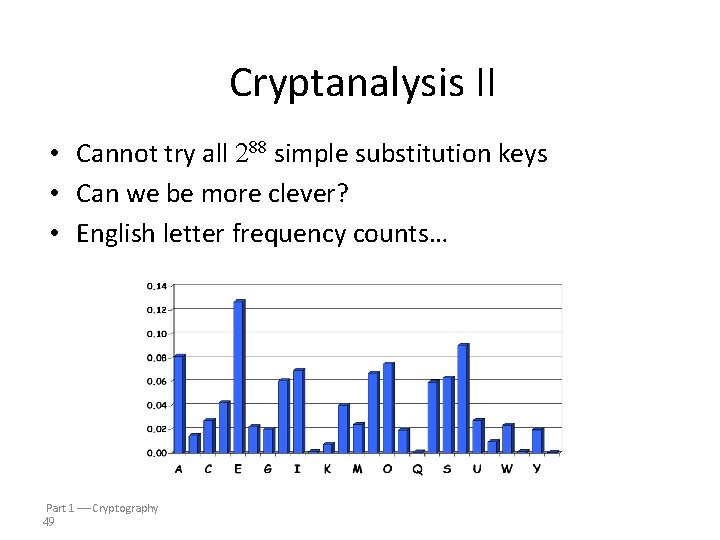
Cryptanalysis II • Cannot try all 288 simple substitution keys • Can we be more clever? • English letter frequency counts… Part 1 Cryptography 49
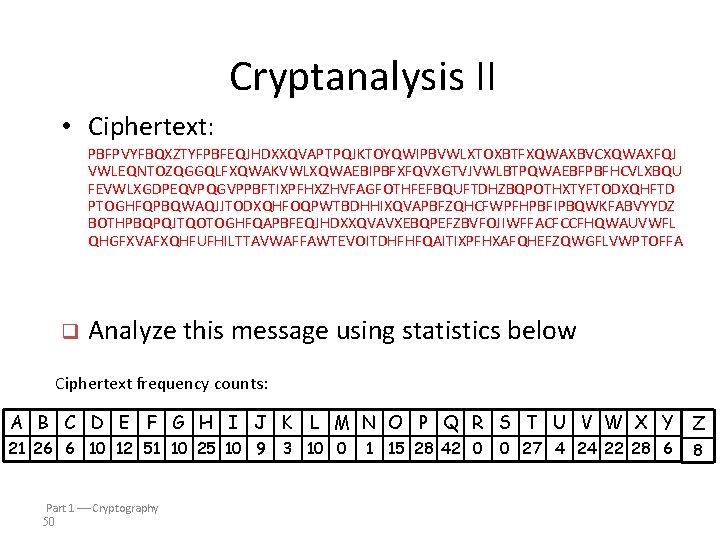
Cryptanalysis II • Ciphertext: PBFPVYFBQXZTYFPBFEQJHDXXQVAPTPQJKTOYQWIPBVWLXTOXBTFXQWAXBVCXQWAXFQJ VWLEQNTOZQGGQLFXQWAKVWLXQWAEBIPBFXFQVXGTVJVWLBTPQWAEBFPBFHCVLXBQU FEVWLXGDPEQVPQGVPPBFTIXPFHXZHVFAGFOTHFEFBQUFTDHZBQPOTHXTYFTODXQHFTD PTOGHFQPBQWAQJJTODXQHFOQPWTBDHHIXQVAPBFZQHCFWPFHPBFIPBQWKFABVYYDZ BOTHPBQPQJTQOTOGHFQAPBFEQJHDXXQVAVXEBQPEFZBVFOJIWFFACFCCFHQWAUVWFL QHGFXVAFXQHFUFHILTTAVWAFFAWTEVOITDHFHFQAITIXPFHXAFQHEFZQWGFLVWPTOFFA q Analyze this message using statistics below Ciphertext frequency counts: A B C D E F G H I J K L M N O P Q R S T U V W X Y Z 21 26 6 10 12 51 10 25 10 9 Part 1 Cryptography 50 3 10 0 1 15 28 42 0 0 27 4 24 22 28 6 8
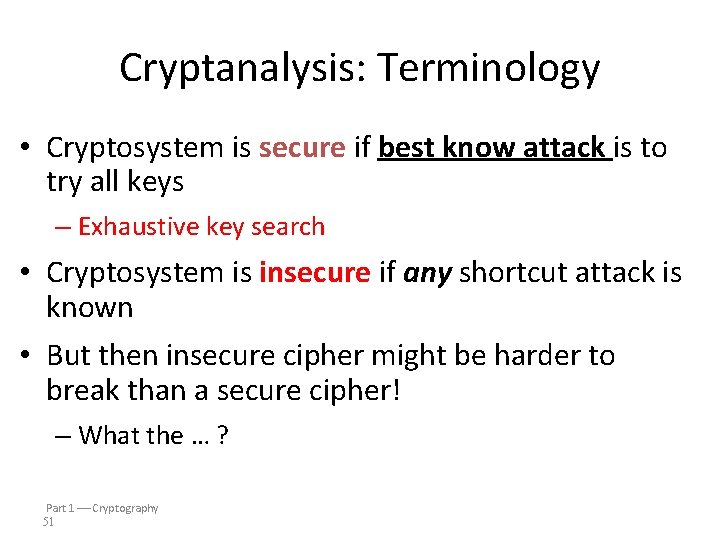
Cryptanalysis: Terminology • Cryptosystem is secure if best know attack is to try all keys – Exhaustive key search • Cryptosystem is insecure if any shortcut attack is known • But then insecure cipher might be harder to break than a secure cipher! – What the … ? Part 1 Cryptography 51
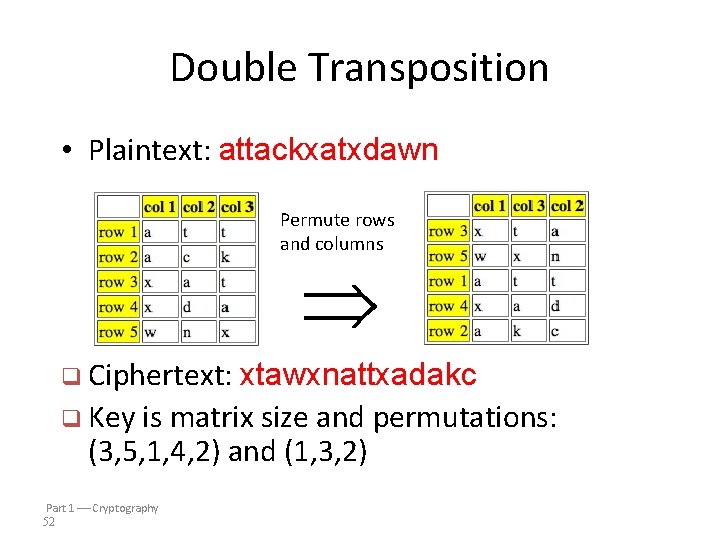
Double Transposition • Plaintext: attackxatxdawn Permute rows and columns q Ciphertext: xtawxnattxadakc q Key is matrix size and permutations: (3, 5, 1, 4, 2) and (1, 3, 2) Part 1 Cryptography 52
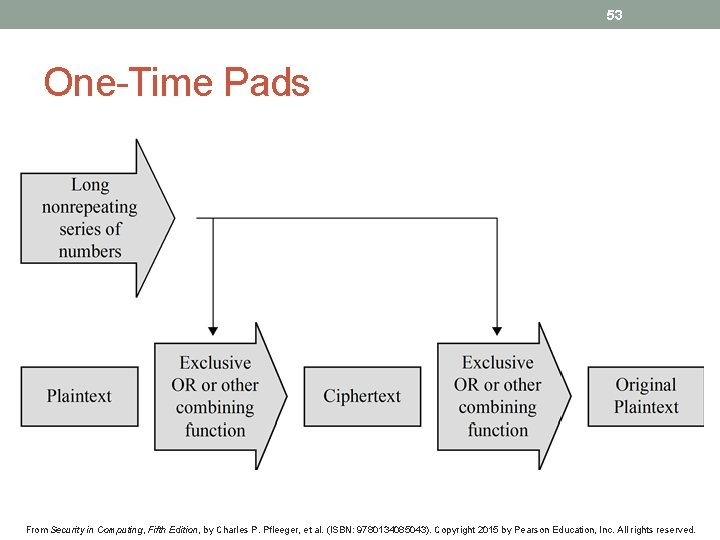
53 One-Time Pads From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
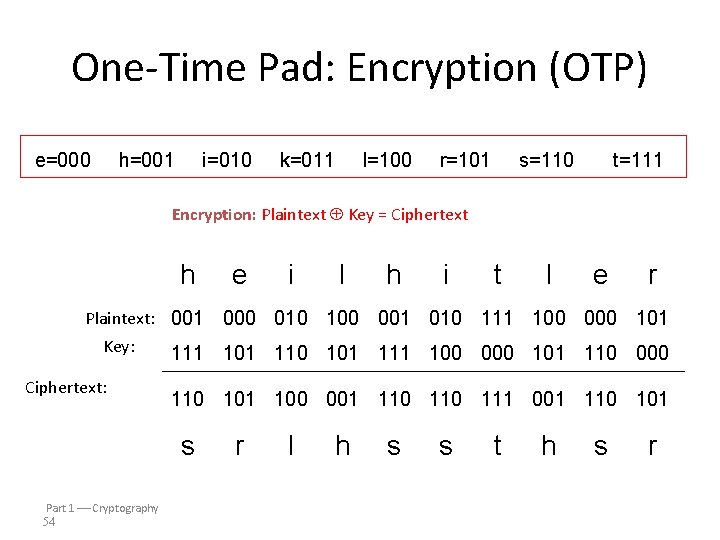
One-Time Pad: Encryption (OTP) e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 Encryption: Plaintext Key = Ciphertext h Plaintext: 001 Key: Ciphertext: i l h i t l e r 000 010 100 001 010 111 100 000 101 111 101 110 101 111 100 000 101 110 000 110 101 100 001 110 111 001 110 101 s Part 1 Cryptography 54 e r l h s s t h s r
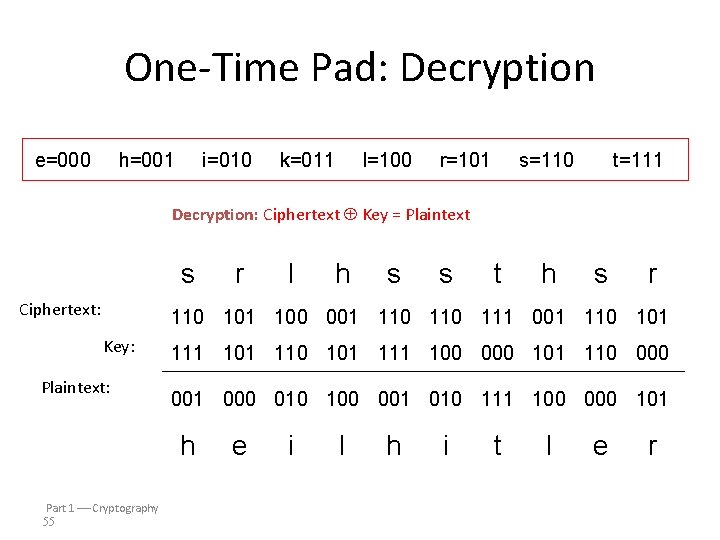
One-Time Pad: Decryption e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 Decryption: Ciphertext Key = Plaintext s Ciphertext: r l h s s t h s r 110 101 100 001 110 111 001 110 101 Key: Plaintext: 111 101 110 101 111 100 000 101 110 001 000 010 100 001 010 111 100 000 101 h Part 1 Cryptography 55 e i l h i t l e r

One-Time Pad Double agent claims following “key” was used: s Ciphertext: “key”: “Plaintext”: r l h s s t h s r 110 101 100 001 110 111 001 110 101 111 000 101 111 100 000 101 110 000 011 010 100 001 010 111 100 000 101 k i l l h i t l e r e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 Part 1 Cryptography 56
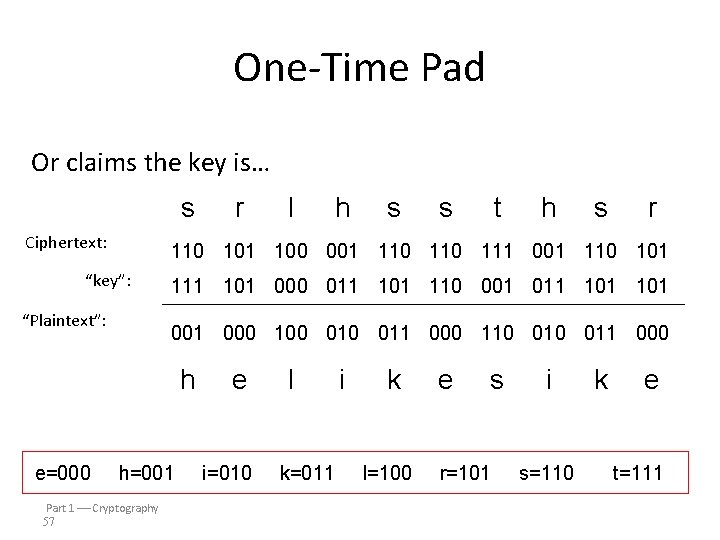
One-Time Pad Or claims the key is… s Ciphertext: “key”: “Plaintext”: r l h s s t h s r 110 101 100 001 110 111 001 110 101 111 101 000 011 101 110 001 011 101 000 100 011 000 110 011 000 h e l i k e s i k e e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 Part 1 Cryptography 57
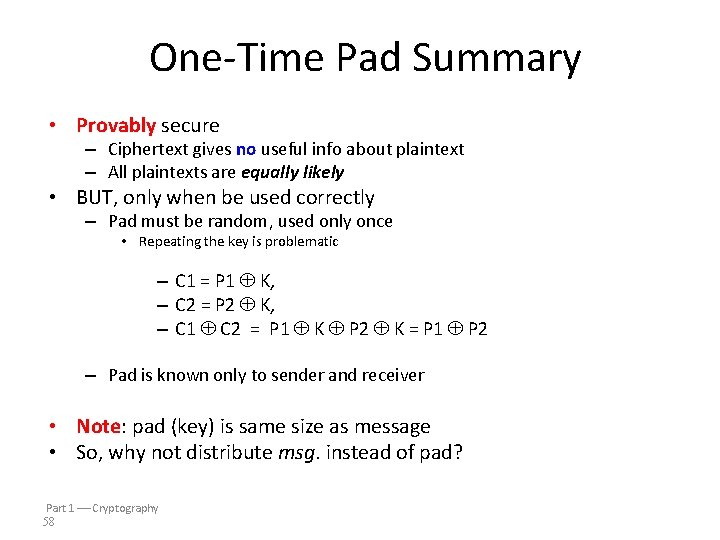
One-Time Pad Summary • Provably secure – Ciphertext gives no useful info about plaintext – All plaintexts are equally likely • BUT, only when be used correctly – Pad must be random, used only once • Repeating the key is problematic – C 1 = P 1 K, – C 2 = P 2 K, – C 1 C 2 = P 1 K P 2 K = P 1 P 2 – Pad is known only to sender and receiver • Note: pad (key) is same size as message • So, why not distribute msg. instead of pad? Part 1 Cryptography 58
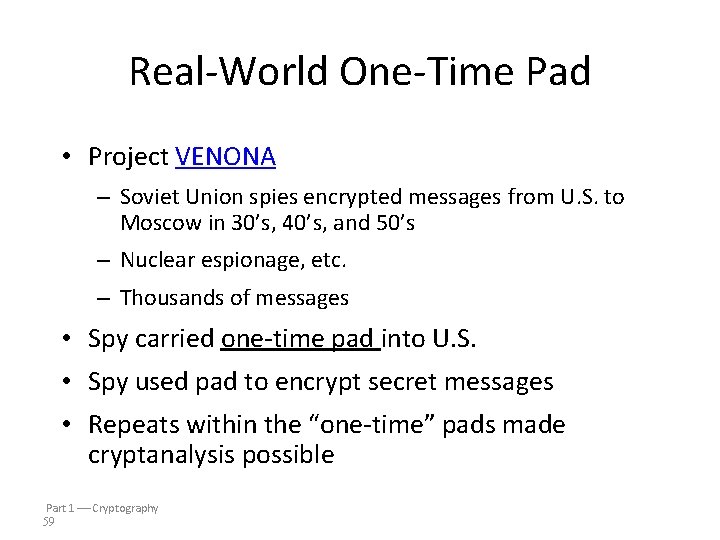
Real-World One-Time Pad • Project VENONA – Soviet Union spies encrypted messages from U. S. to Moscow in 30’s, 40’s, and 50’s – Nuclear espionage, etc. – Thousands of messages • Spy carried one-time pad into U. S. • Spy used pad to encrypt secret messages • Repeats within the “one-time” pads made cryptanalysis possible Part 1 Cryptography 59
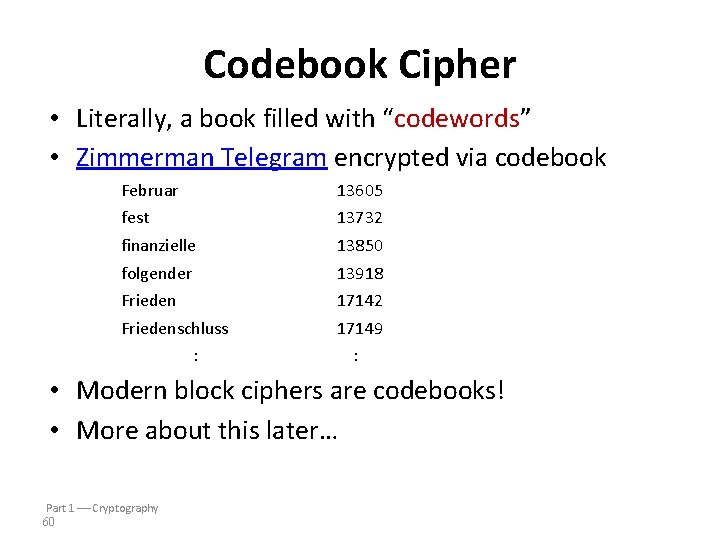
Codebook Cipher • Literally, a book filled with “codewords” • Zimmerman Telegram encrypted via codebook Februar 13605 fest 13732 finanzielle 13850 folgender 13918 Frieden 17142 Friedenschluss 17149 : : • Modern block ciphers are codebooks! • More about this later… Part 1 Cryptography 60
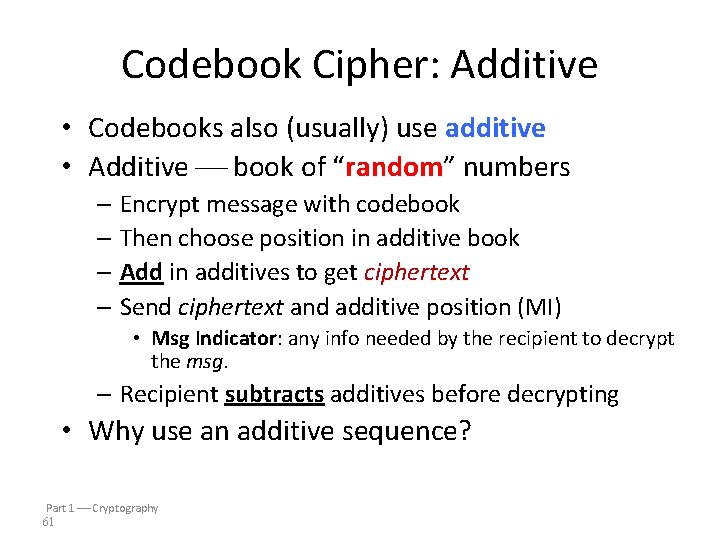
Codebook Cipher: Additive • Codebooks also (usually) use additive • Additive book of “random” numbers – Encrypt message with codebook – Then choose position in additive book – Add in additives to get ciphertext – Send ciphertext and additive position (MI) • Msg Indicator: any info needed by the recipient to decrypt the msg. – Recipient subtracts additives before decrypting • Why use an additive sequence? Part 1 Cryptography 61
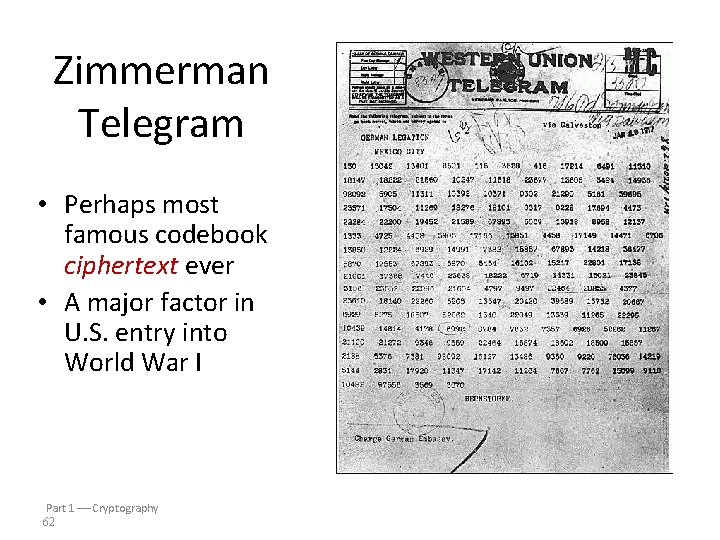
Zimmerman Telegram • Perhaps most famous codebook ciphertext ever • A major factor in U. S. entry into World War I Part 1 Cryptography 62
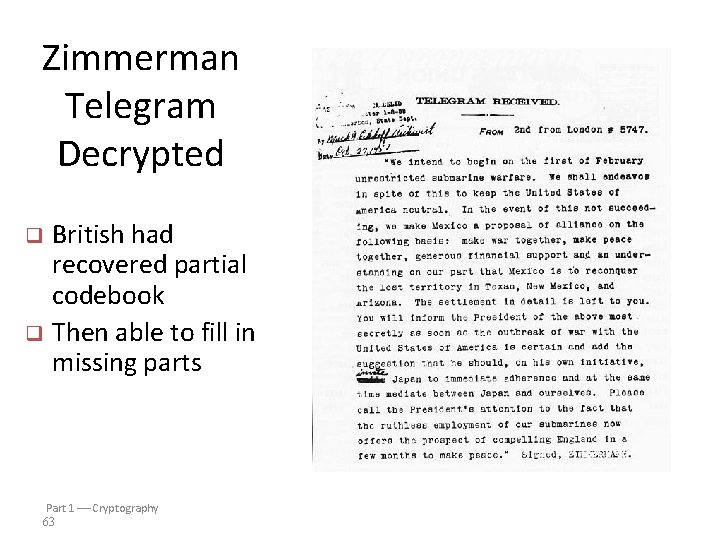
Zimmerman Telegram Decrypted British had recovered partial codebook q Then able to fill in missing parts q Part 1 Cryptography 63
64 Authenticity, Integrity & Identity Verification From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
65 Data Integrity: Error Detecting Codes • Data can be corrupted in transmission or storage by a variety of undesirable phenomenon. • It is useful to have a way to detect (and sometimes correct) such data corruption. • Error Detecting Codes: • Finds out whether a block of data has been modified or not? • Techniques for simple error detecting codes: • Parity checks • Cyclic redundancy checks (CRC) • Techniques for cryptographic error detecting codes: • One-way hash functions • Cryptographic checksums • Digital Signatures From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
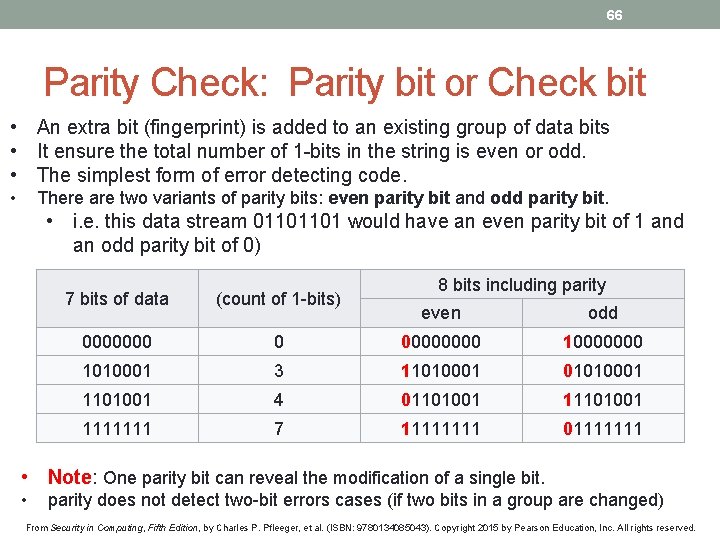
66 Parity Check: Parity bit or Check bit • An extra bit (fingerprint) is added to an existing group of data bits • It ensure the total number of 1 -bits in the string is even or odd. • The simplest form of error detecting code. • There are two variants of parity bits: even parity bit and odd parity bit. • i. e. this data stream 01101101 would have an even parity bit of 1 and an odd parity bit of 0) 7 bits of data (count of 1 -bits) 0000000 8 bits including parity even odd 0 0000 10000000 1010001 3 11010001 01010001 1101001 4 01101001 1111111 7 1111 01111111 • Note: One parity bit can reveal the modification of a single bit. • parity does not detect two-bit errors cases (if two bits in a group are changed) From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
67 One-Way Hash Function • A one-way function can be useful in creating a change detection algorithm. • Often, elements or components of the file are not bound together in any way ! (parity bit not useful any more) • Cryptography can be used to seal a file, encasing it so that any change becomes apparent. • One technique for providing the seal is to compute a function, sometimes called a hash or checksum or message digest of the file. • i. e. the MD 5 hashing algorithm is a one-way cryptographic function that accepts a message of any length as input and returns as output a fixed-length digest value to authenticate the original message, verify data integrity, and detect unintentional data corruption. . From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
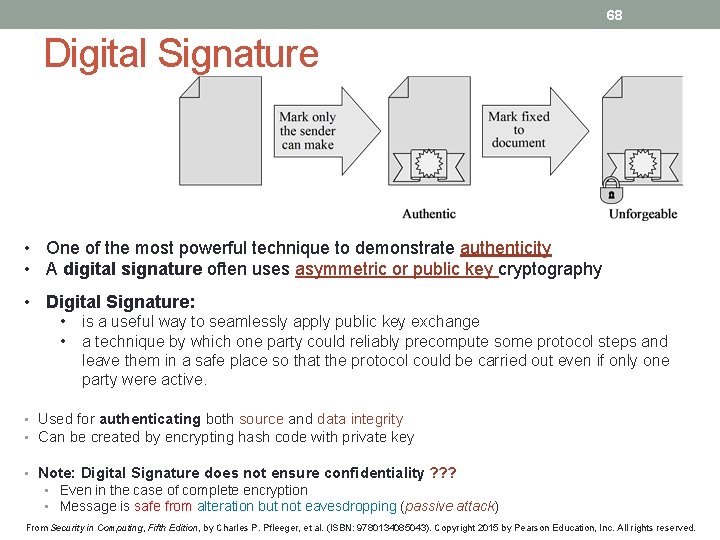
68 Digital Signature • One of the most powerful technique to demonstrate authenticity • A digital signature often uses asymmetric or public key cryptography • Digital Signature: • • is a useful way to seamlessly apply public key exchange a technique by which one party could reliably precompute some protocol steps and leave them in a safe place so that the protocol could be carried out even if only one party were active. • Used for authenticating both source and data integrity • Can be created by encrypting hash code with private key • Note: Digital Signature does not ensure confidentiality ? ? ? • Even in the case of complete encryption • Message is safe from alteration but not eavesdropping (passive attack) From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
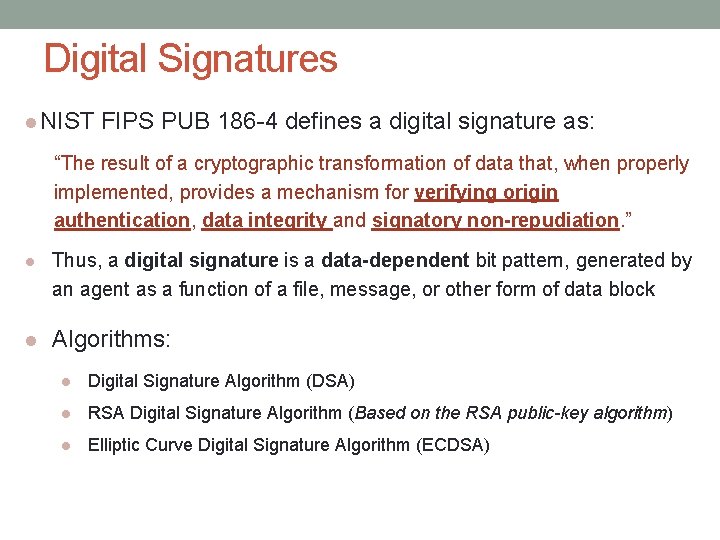
Digital Signatures NIST FIPS PUB 186 -4 defines a digital signature as: “The result of a cryptographic transformation of data that, when properly implemented, provides a mechanism for verifying origin authentication, data integrity and signatory non-repudiation. ” Thus, a digital signature is a data-dependent bit pattern, generated by an agent as a function of a file, message, or other form of data block Algorithms: Digital Signature Algorithm (DSA) RSA Digital Signature Algorithm (Based on the RSA public-key algorithm) Elliptic Curve Digital Signature Algorithm (ECDSA)
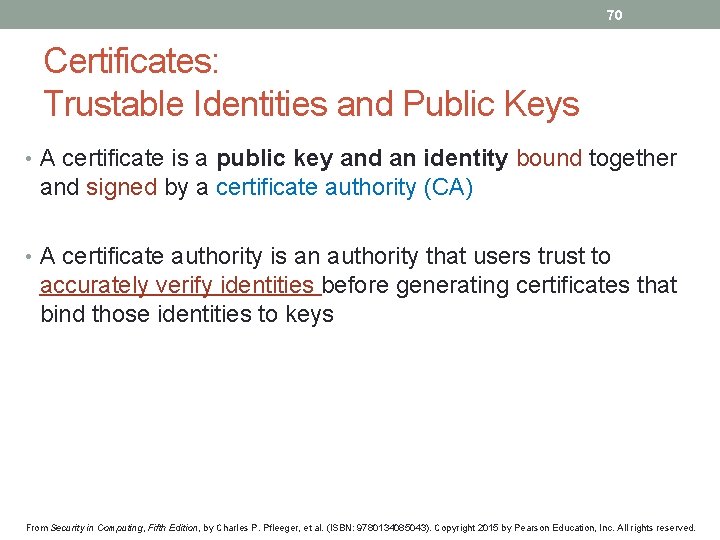
70 Certificates: Trustable Identities and Public Keys • A certificate is a public key and an identity bound together and signed by a certificate authority (CA) • A certificate authority is an authority that users trust to accurately verify identities before generating certificates that bind those identities to keys From Security in Computing, Fifth Edition, by Charles P. Pfleeger, et al. (ISBN: 9780134085043). Copyright 2015 by Pearson Education, Inc. All rights reserved.
Summary
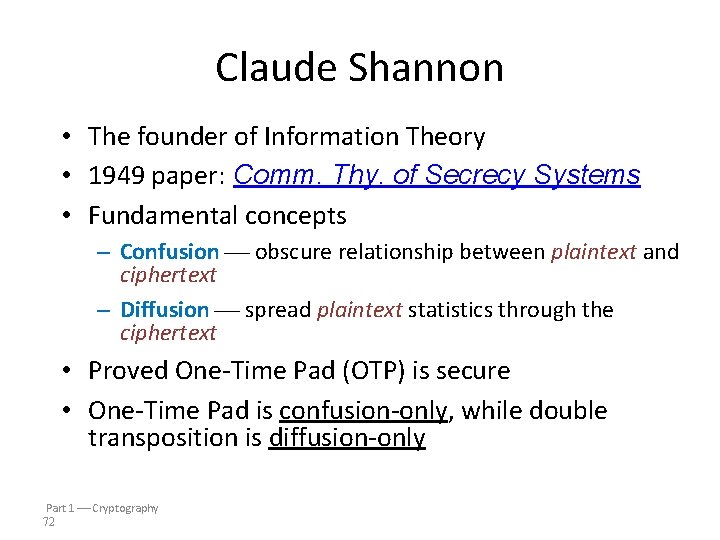
Claude Shannon • The founder of Information Theory • 1949 paper: Comm. Thy. of Secrecy Systems • Fundamental concepts – Confusion obscure relationship between plaintext and ciphertext – Diffusion spread plaintext statistics through the ciphertext • Proved One-Time Pad (OTP) is secure • One-Time Pad is confusion-only, while double transposition is diffusion-only Part 1 Cryptography 72
Taxonomy of Cryptography • Symmetric Key – Same key for encryption and decryption – Modern types: Stream ciphers, Block ciphers • Public Key (or “asymmetric” crypto) – Two keys, one for encryption (public), and one for decryption (private) – And digital signatures nothing comparable in symmetric key crypto • Hash algorithms – Can be viewed as “one way” crypto Part 1 Cryptography 73
Taxonomy of Cryptanalysis • From perspective of info available to Trudy… – Ciphertext only Trudy’s worst case scenario – Known plaintext – Chosen plaintext • “Lunchtime attack” • Some protocols will encrypt chosen data – Adaptively chosen plaintext – Forward search (public key crypto) • Expecting a msg. , encrypting it (with the public key of the recipient), and comparing the result with the intercepted msg. Part 1 Cryptography 74
- Slides: 74