FIPS 201 Framework Special Pubs 800 73 76
FIPS 201 Framework: Special Pubs 800 -73, 76, 78 Jim Dray HSPD-12 Workshop May 4/5, 2005
Special Publication 800 -73 • PIV card application definition o NOT a general purpose card platform spec! Part 1: Common data model and migration • Part 2: Transition card interfaces • Part 3: End point specification •
Part 1: Mandatory Data Objects • PIV credential element objects o o o Card Capability Container: Discovery Cardholder Unique Identifier: PACS 2. 2 PIV Authentication Key Fingerprint Buffers (2) Security Object
Part 1: Optional Data Objects • Optional PIV credential element objects o o o Printed Information Facial Image Digital Signature Key Management Key Card Authentication Key
Part 1: Migration Issues Some agencies have smart card deployments • Government Smart Card Interoperability Specification (NISTIR 6887) • Migration path is based on continuity of the PIV data model • Legacy agencies MAY use Part 2 transition specification •
SP 800 -73 Part 2 Essentially a PIV profile of GSC-IS • Maintains the GSC-IS dual card interfaces • o o File system Virtual Machine Developed by the Government Smart Card Interagency Advisory Board • Part 2 is informative •
SP 800 -73 Part 3 Unified card command interface • Compliant with existing international standards (ISO 7816) • Technology neutrality: Implementable on any card platform • Essential features for: • o o High degree of PIV card interoperability Future-proofing PIV framework
Part 3: Data Model Data model is common to both Parts 2 and 3 • Different identifiers (BER-TLV) used at the card edge in Part 3 •
Part 3: Standard Namespaces ASN. 1 Object Identifiers in the PIV arc of the Computer Security Object Register at the Client Application Programming Interface • PIV RID is the root of card Application Identifiers(AIDs) • BER-TLV tags for data objects at the card interface •
Part 3: PIV Card Application • • • AID is ‘A 0 00 00 xx xx 00 00 10 00 01 00’ Full PIV RID to be published by NIST Access Control Rules applied to PIV credential objects Provides a set of 8 ISO compliant card interface commands Restricted functionality in contactless mode
Part 3: Client Application Programming Interface Equivalent to GSC-IS Basic Services Interface • Provides 9 higher level commands • Implemented by middleware • PIV middleware is MUCH simpler than GSC-IS middleware because card command mapping is not required •
Part 3: Reference Implementation • • • Part 3 compliant implementation PIV card application running in a card simulator Middleware Publicly available Basis for conformance tests Estimated completion date June 25
SP 800 -73 Summary PIV II card application and client application programming interface spec • Informative Part 2 transition specification for migrating legacy GSC-IS deployments • Normative Part 3 end point specification • All agencies are to reach full deployment of Part 3 PIV cards by the end of their PIV II Phase, regardless of the migration path chosen. •
Special Publication 800 -78 Overview • FIPS 201 relies on cryptography o o o To protect objects stored on the PIV card To authenticate the PIV card or cardholder To authenticate the source and integrity of status information
Cryptographic Strength Requirements • SP 800 -78 mandates a transition from 80 bit strength to 112 bits of strength by 1/1/2011 o • Cryptographic keys that provide long term data protection transition by 1/1/2009 to provide two years “forward security” Elliptic Curve Cryptography is specified with a minimum of 112 bits of strength (224 bit keys) o Avoid transition issues
Cryptographic Objects Stored on the PIV Card • FIPS 201 specified o o Cryptographic keys Digitally signed objects • CHUID • Biometrics • X. 509 Certificates • SP 800 -073 specified o Authentication/Integrity Object
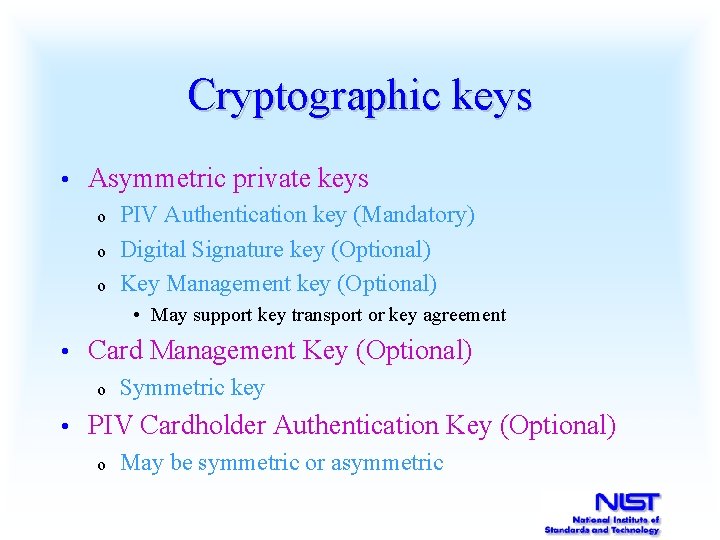
Cryptographic keys • Asymmetric private keys o o o PIV Authentication key (Mandatory) Digital Signature key (Optional) Key Management key (Optional) • May support key transport or key agreement • Card Management Key (Optional) o • Symmetric key PIV Cardholder Authentication Key (Optional) o May be symmetric or asymmetric
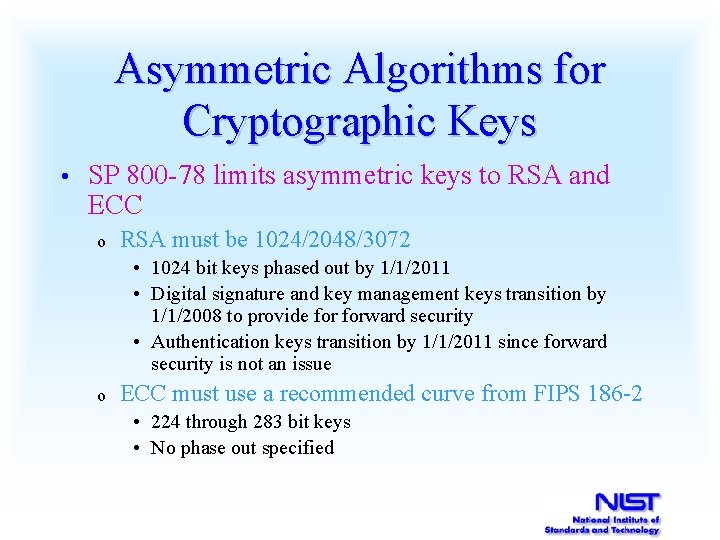
Asymmetric Algorithms for Cryptographic Keys • SP 800 -78 limits asymmetric keys to RSA and ECC o RSA must be 1024/2048/3072 • 1024 bit keys phased out by 1/1/2011 • Digital signature and key management keys transition by 1/1/2008 to provide forward security • Authentication keys transition by 1/1/2011 since forward security is not an issue o ECC must use a recommended curve from FIPS 186 -2 • 224 through 283 bit keys • No phase out specified
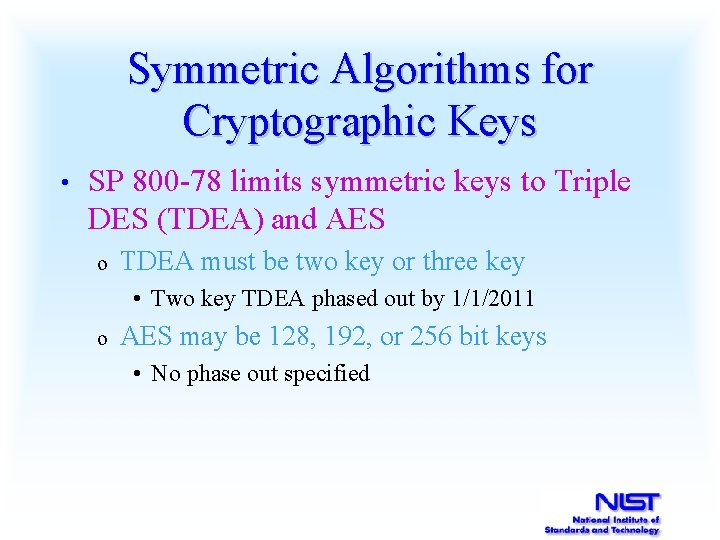
Symmetric Algorithms for Cryptographic Keys • SP 800 -78 limits symmetric keys to Triple DES (TDEA) and AES o TDEA must be two key or three key • Two key TDEA phased out by 1/1/2011 o AES may be 128, 192, or 256 bit keys • No phase out specified
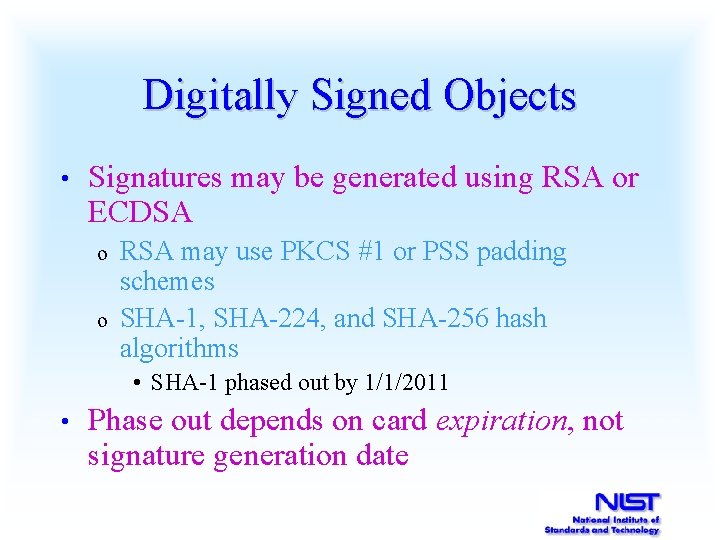
Digitally Signed Objects • Signatures may be generated using RSA or ECDSA o o RSA may use PKCS #1 or PSS padding schemes SHA-1, SHA-224, and SHA-256 hash algorithms • SHA-1 phased out by 1/1/2011 • Phase out depends on card expiration, not signature generation date
SP 800 -73 Security Object ICAO Authentication/Integrity Object • Digitally signed hash table • o o The table includes a message digest for each of the objects (CHUID, keys, etc. ) stored on the card Message digests are generated using SHA-1, SHA-224, or SHA-256 • SHA-1 phased out by 1/1/2011 o Signature requirements from previous slide
Status Information FIPS 201 relies upon digitally signed X. 509 CRLs and OCSP responses to distribute status information • Signatures may be generated using RSA or ECDSA • o o RSA may use PKCS #1 or PSS padding schemes SHA-1, SHA-224, and SHA-256 hash algorithms • SHA-1 phased out by 1/1/2011 • Phase out depends on signature generation date
Special Publication 800 -76 Biometric Data Specification for Personal Identity Verification • Major issue: Minutia vs. full image • o o o • File size Interoperability Privacy Still in draft form
Contact Information Curt Barker (william. barker@nist. gov): PIV Program Manager Jim Dray (james. dray@nist. gov ): SP 800 -73 Terry Schwarzhoff (teresa. schwarzhoff@nist. gov): NIST Smart Card Program Manager, Standards Lead NIST PIV Website: http: //csrc. nist. gov/piv-project
- Slides: 24