CTF 101 College of Charleston Cyber Security Club
CTF 101 College of Charleston Cyber Security Club Dr. X
Today’s topics ● ● What is a CTF Forensics - we love to hate them Pwn & RE Crypto - for those who love math (don’t we all) ● Web

What is a CTF? Capture the Flag is a computer security competition where teams compete to solve challenges of varying difficulty to score points. Originally a children's game to simulate small team combat based on defending a flag, while attempting to capture the opposing team’s flag
CTF Styles ● ● Wargames - overthewire Hackquest - SANS holiday challenge Jeopardy Attack & Defend
CTF Challenges ● Cryptography - for the love of math! ● Forensics - needle in haystack problems ● Reverse Engineering - how does the application work ● PWN/Exploit - write or use a known exploit ● Web - uncover weaknesses in web apps

Why? ● ● ● Knowledge Hands-on Research Friends Fun!!!
Forensics A love-hate situation
Forensic Challenges ● ● Network File / Steganography Disk Image Memory
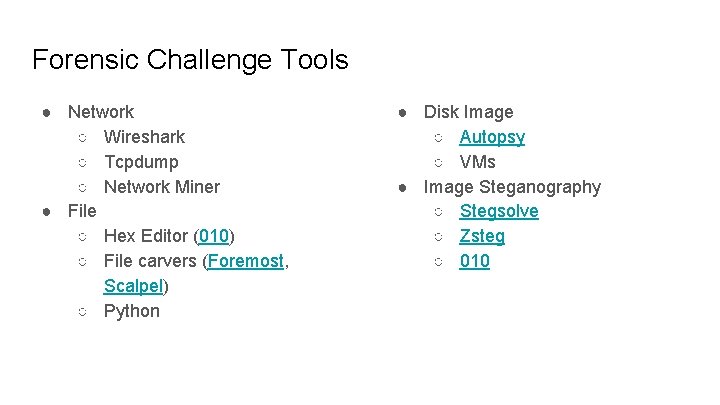
Forensic Challenge Tools ● Network ○ Wireshark ○ Tcpdump ○ Network Miner ● File ○ Hex Editor (010) ○ File carvers (Foremost, Scalpel) ○ Python ● Disk Image ○ Autopsy ○ VMs ● Image Steganography ○ Stegsolve ○ Zsteg ○ 010
PWN & RE Just because. . .
RE Tools ● ● ● Z 3 Decompilers GDB Gidra (free… from NSA) Pure, old, programmer knowledge and patience
PWN ● Buffer overflow, string formatting, . . . ● Tools ○ ○ ○ Decompiler Metasploit Pwntools


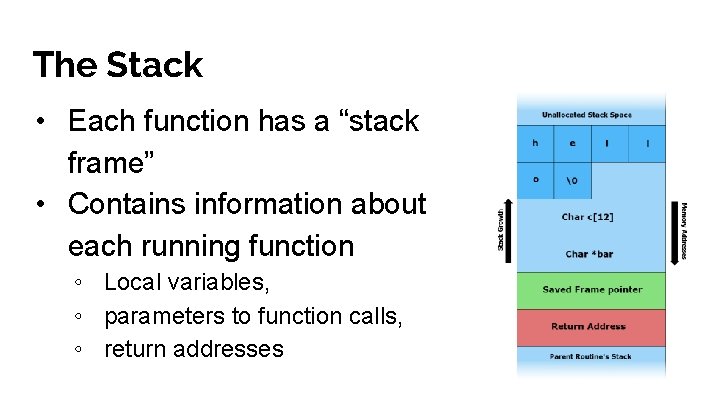
The Stack • Each function has a “stack frame” • Contains information about each running function ◦ Local variables, ◦ parameters to function calls, ◦ return addresses
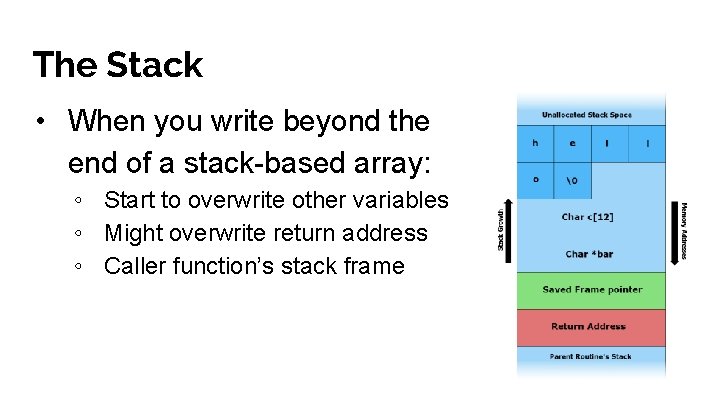
The Stack • When you write beyond the end of a stack-based array: ◦ Start to overwrite other variables ◦ Might overwrite return address ◦ Caller function’s stack frame
Crypto Math rocks!
Encoding vs Ciphers vs Hashing ● Encoding ○ Base 64 ● Ciphers ○ ○ ○ Atbash ROT 13 Caesar Vigenere Tools: rumkin cipher page. . . your code! ● Hashing tools ○ ○ John Hashcat

Web ‘Nough said
Tools for web app security ● Web Browser! ● Web Proxying Tool(s) ○ Burp Suite ○ Fiddler ○ mitmproxy ○ Nikto ○ Zap. Proxy ● SQLMap - Automatic SQL injection and database takeover tool ● Ysoserial - tool for exploiting unsafe object deserialization vulnerabilities ● SSLyze - deep analysis of the SSL/TLS configuration of web servers/applications. ● Google - Everything ● Your very own Critical Thinking Skills™

Learning web app security ● Mutillidae, ● OWASP Top 10 ● Audi-1 SQL Labs ○ Tons of exercises for learning different forms SQLi in-depth + Bypasses + Video Walkthroughs Juice-Shop - Modern Vulnerable Web Application Hack. me - Build, host and share vulnerable web apps in a sandboxed environment for free Rapid 7 Hacka. Zon - “real world” vulnerable test site that is an online storefront built with modern technologies Hackthe. Box. eu - Awesome Pentesting Labs ● ● Super Great List of Web App Sec Resources (This has EVERYTHING) ● https: //github. com/infoslack/awesome-web-hacking Books - Web Application Hackers Handbook II Youtuber(s) - webpwnized , hackersploit - Learn all about Web Application Vulnerabilities from A-Z
Hands on time!! CTF - Forensics ● ● Time and correctness will score your points! Every time you capture a flag, send! You are only allowed 3 trials (for the non-root-me challenges) Image steganography ○ ○ Download zip file Find image Find the flag hidden in the image Send to Carson with private message on slack ● Network traffic ○ ○ Create an account on root-me. org Go to root-me. org, challenges, network Solve the ftp, telnet, ethernet challenges Take a screenshot and send!
Hands on time! CTF - RE • Find the file PYTHON 3. pyc • Answer the corresponding questions in PYTHON 3. txt • Send to Seth on slack private message
Hands on time! - Crypto No sleeping here Find the passwords. docx and crack the passwords Send to Carson!
Hands on time! CTF - Web ● ● Go to root-me. org Solve three challenges of your choice from web-client and web-server Send screenshot to Seth Time is up at 6: 20 pm!!!
Acknowledgement Thank you Hack @ UCF for this awesome slides that you had open on the web ; )
- Slides: 26