Chapter 2 Crypto Basics How to speak crypto
Chapter 2 Crypto Basics How to speak crypto Substitution Cipher Transposition Cipher One-Time Pad codebook Crypto history Taxonomy 1
Crypto l l Cryptology The art and science of making and breaking “secret codes” Cryptography making “secret codes” Cryptanalysis breaking “secret codes” Crypto all of the above (and more) Chapter 2 Crypto Basics 2
How to Speak Crypto l l l A cipher or cryptosystem is used to encrypt the plaintext The result of encryption is ciphertext We decrypt ciphertext to recover plaintext A key is used to configure a cryptosystem A symmetric key cryptosystem uses the same key to encrypt as to decrypt A public key cryptosystem uses a public key to encrypt and a private key to decrypt (sign) Chapter 2 Crypto Basics 3
Crypto l Basis assumption l l l Also known as Kerckhoffs Principle l l The system is completely known to the attacker Only the key is secret Crypto algorithms are not secret Why do we make this assumption? l l l Experience has shown that secret algorithms are weak when exposed Secret algorithms never remain secret Better to find weaknesses beforehand Chapter 2 Crypto Basics 4
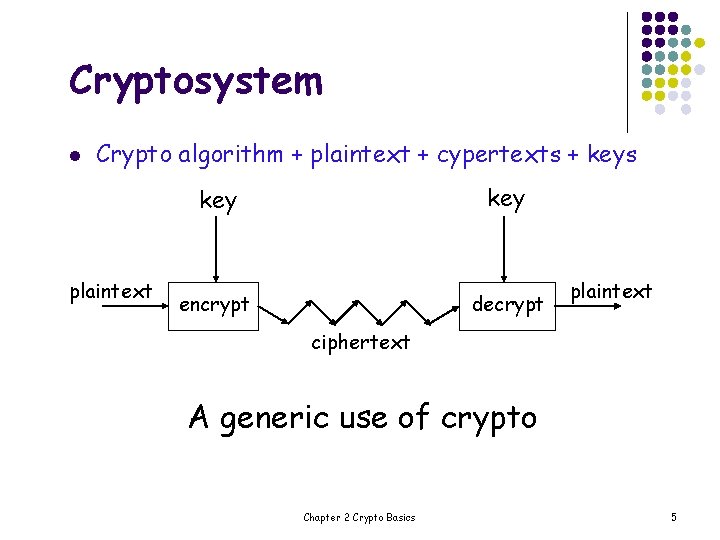
Cryptosystem l Crypto algorithm + plaintext + cypertexts + keys plaintext key encrypt decrypt plaintext ciphertext A generic use of crypto Chapter 2 Crypto Basics 5
Elements of crypto algorithm l l Before computers, ciphers consisted of character-based algorithms. Substitution ciphers l l Transposition ciphers l l Each character in the plaintext is substituted for another character in the ciphertext. Plaintext remains the same, but the order of characters is shuffled around. Most good cryto algorithms combine these two elements. Chapter 2 Crypto Basics 6
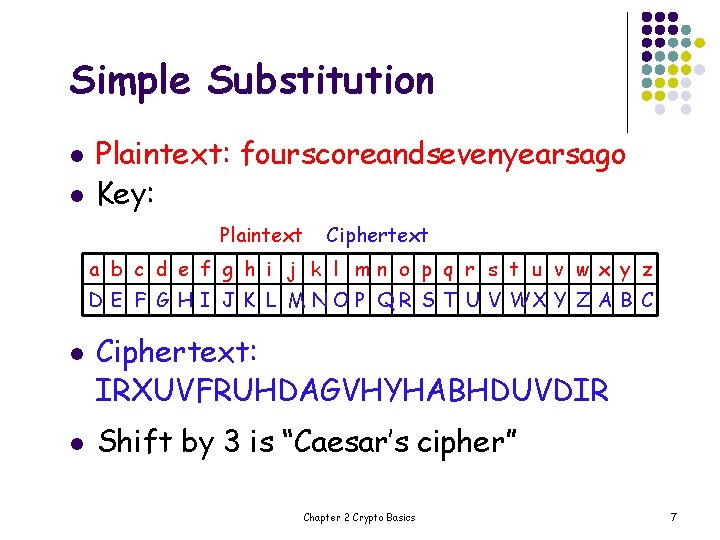
Simple Substitution l l Plaintext: fourscoreandsevenyearsago Key: Plaintext Ciphertext a b c d e f g h i j k l mn o p q r s t u v w x y z D E F G H I J K L M N O P Q R S T U V WX Y Z A B C l l Ciphertext: IRXUVFRUHDAGVHYHABHDUVDIR Shift by 3 is “Caesar’s cipher” Chapter 2 Crypto Basics 7
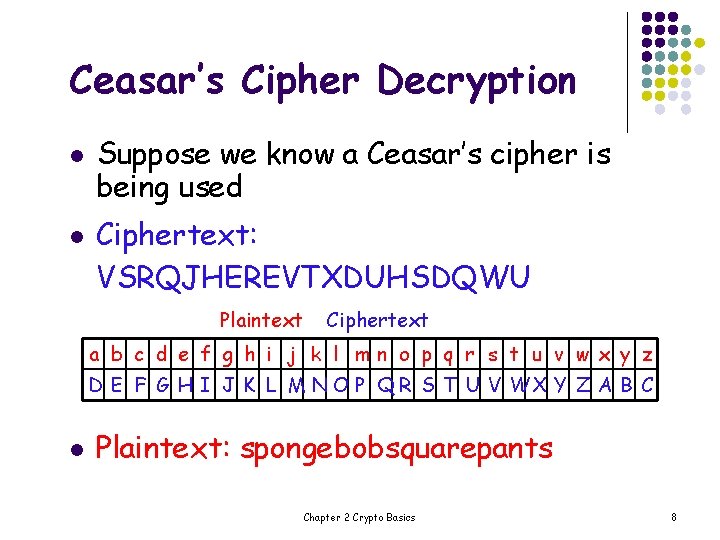
Ceasar’s Cipher Decryption l l Suppose we know a Ceasar’s cipher is being used Ciphertext: VSRQJHEREVTXDUHSDQWU Plaintext Ciphertext a b c d e f g h i j k l mn o p q r s t u v w x y z D E F G H I J K L M N O P Q R S T U V WX Y Z A B C l Plaintext: spongebobsquarepants Chapter 2 Crypto Basics 8
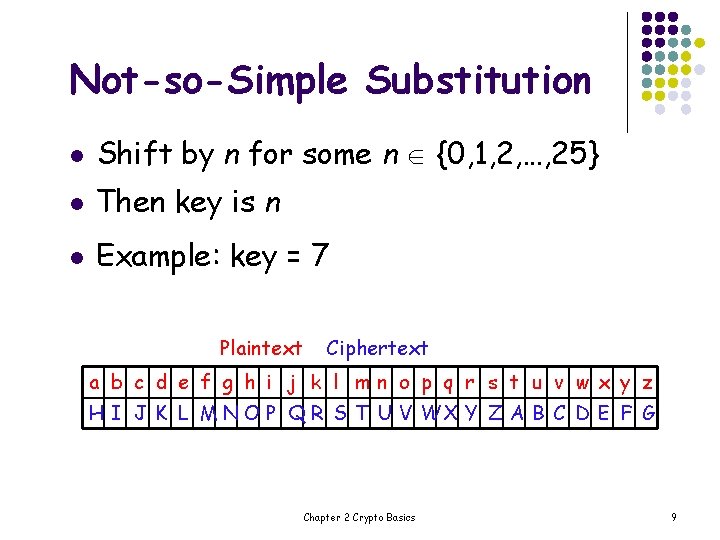
Not-so-Simple Substitution l Shift by n for some n {0, 1, 2, …, 25} l Then key is n l Example: key = 7 Plaintext Ciphertext a b c d e f g h i j k l mn o p q r s t u v w x y z H I J K L M N O P Q R S T U V WX Y Z A B C D E F G Chapter 2 Crypto Basics 9
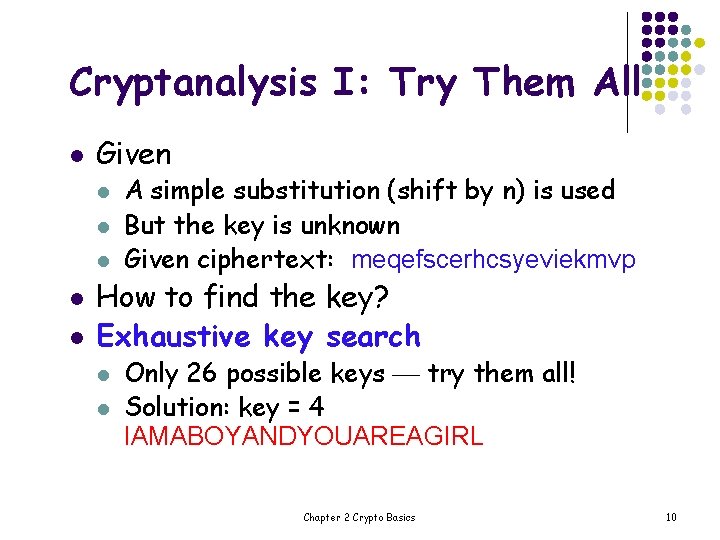
Cryptanalysis I: Try Them All l Given l l l A simple substitution (shift by n) is used But the key is unknown Given ciphertext: meqefscerhcsyeviekmvp How to find the key? Exhaustive key search l l Only 26 possible keys try them all! Solution: key = 4 IAMABOYANDYOUAREAGIRL Chapter 2 Crypto Basics 10
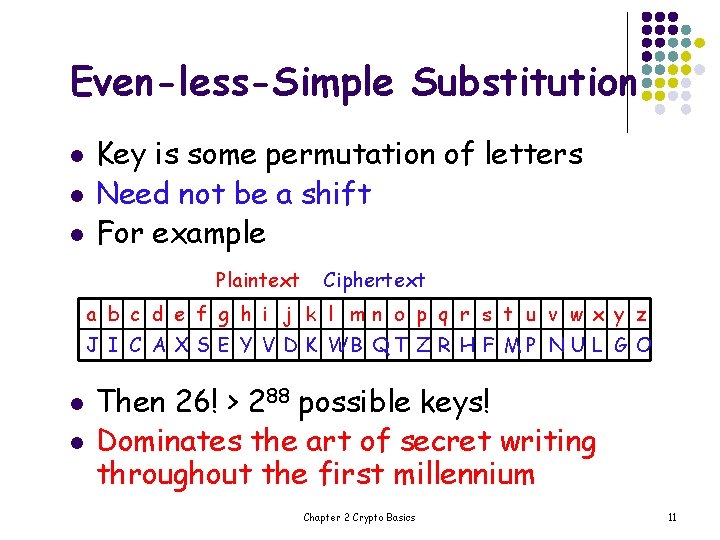
Even-less-Simple Substitution l l l Key is some permutation of letters Need not be a shift For example Plaintext Ciphertext a b c d e f g h i j k l mn o p q r s t u v w x y z J I C A X S E Y V D K WB Q T Z R H F M P N U L G O l l Then 26! > 288 possible keys! Dominates the art of secret writing throughout the first millennium Chapter 2 Crypto Basics 11
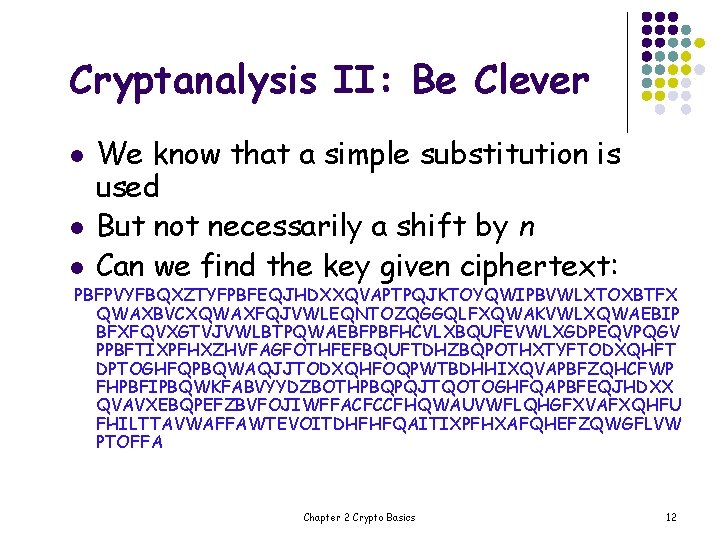
Cryptanalysis II: Be Clever l l l We know that a simple substitution is used But not necessarily a shift by n Can we find the key given ciphertext: PBFPVYFBQXZTYFPBFEQJHDXXQVAPTPQJKTOYQWIPBVWLXTOXBTFX QWAXBVCXQWAXFQJVWLEQNTOZQGGQLFXQWAKVWLXQWAEBIP BFXFQVXGTVJVWLBTPQWAEBFPBFHCVLXBQUFEVWLXGDPEQVPQGV PPBFTIXPFHXZHVFAGFOTHFEFBQUFTDHZBQPOTHXTYFTODXQHFT DPTOGHFQPBQWAQJJTODXQHFOQPWTBDHHIXQVAPBFZQHCFWP FHPBFIPBQWKFABVYYDZBOTHPBQPQJTQOTOGHFQAPBFEQJHDXX QVAVXEBQPEFZBVFOJIWFFACFCCFHQWAUVWFLQHGFXVAFXQHFU FHILTTAVWAFFAWTEVOITDHFHFQAITIXPFHXAFQHEFZQWGFLVW PTOFFA Chapter 2 Crypto Basics 12
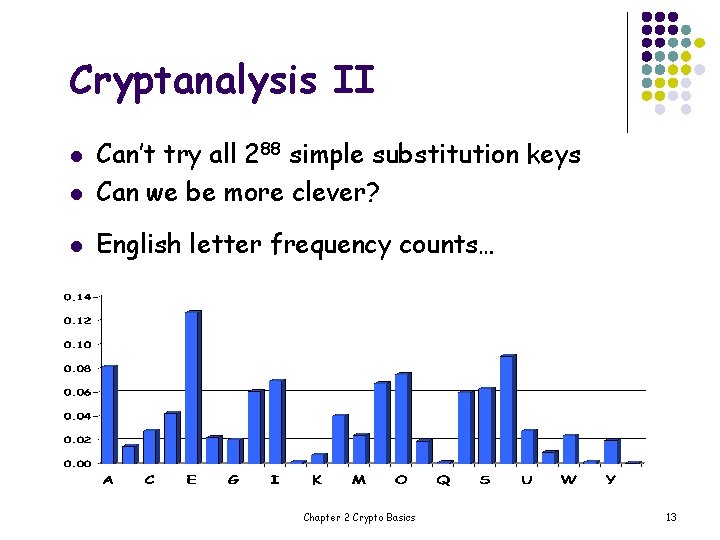
Cryptanalysis II l Can’t try all 288 simple substitution keys Can we be more clever? l English letter frequency counts… l Chapter 2 Crypto Basics 13
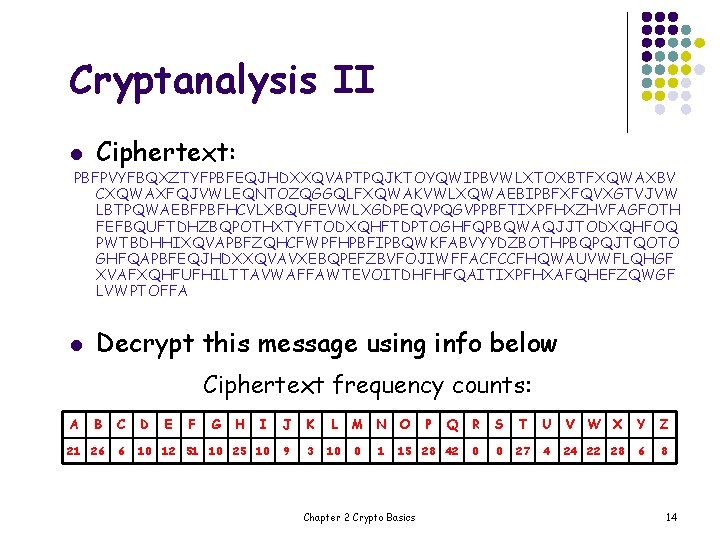
Cryptanalysis II l Ciphertext: PBFPVYFBQXZTYFPBFEQJHDXXQVAPTPQJKTOYQWIPBVWLXTOXBTFXQWAXBV CXQWAXFQJVWLEQNTOZQGGQLFXQWAKVWLXQWAEBIPBFXFQVXGTVJVW LBTPQWAEBFPBFHCVLXBQUFEVWLXGDPEQVPQGVPPBFTIXPFHXZHVFAGFOTH FEFBQUFTDHZBQPOTHXTYFTODXQHFTDPTOGHFQPBQWAQJJTODXQHFOQ PWTBDHHIXQVAPBFZQHCFWPFHPBFIPBQWKFABVYYDZBOTHPBQPQJTQOTO GHFQAPBFEQJHDXXQVAVXEBQPEFZBVFOJIWFFACFCCFHQWAUVWFLQHGF XVAFXQHFUFHILTTAVWAFFAWTEVOITDHFHFQAITIXPFHXAFQHEFZQWGF LVWPTOFFA l Decrypt this message using info below Ciphertext frequency counts: A B C D E F G H I J K L M N O Q R S T U V W X Y Z 21 26 6 10 12 51 10 25 10 9 3 10 0 15 28 42 0 0 27 4 24 22 28 6 8 1 Chapter 2 Crypto Basics P 14
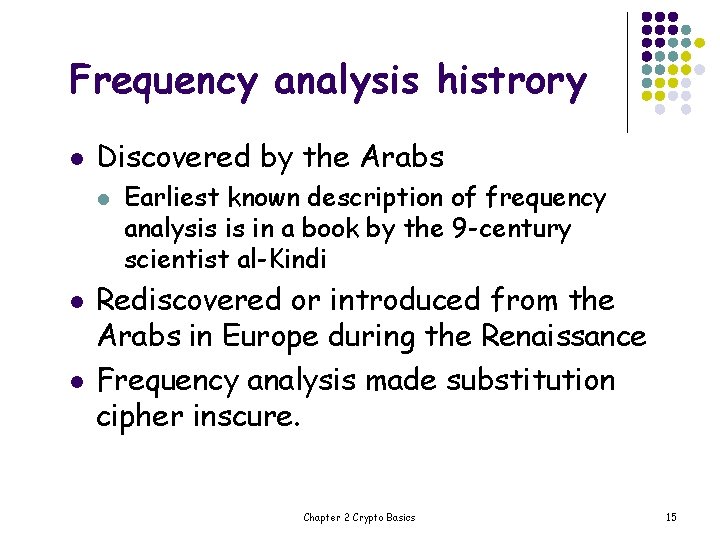
Frequency analysis histrory l Discovered by the Arabs l l l Earliest known description of frequency analysis is in a book by the 9 -century scientist al-Kindi Rediscovered or introduced from the Arabs in Europe during the Renaissance Frequency analysis made substitution cipher inscure. Chapter 2 Crypto Basics 15
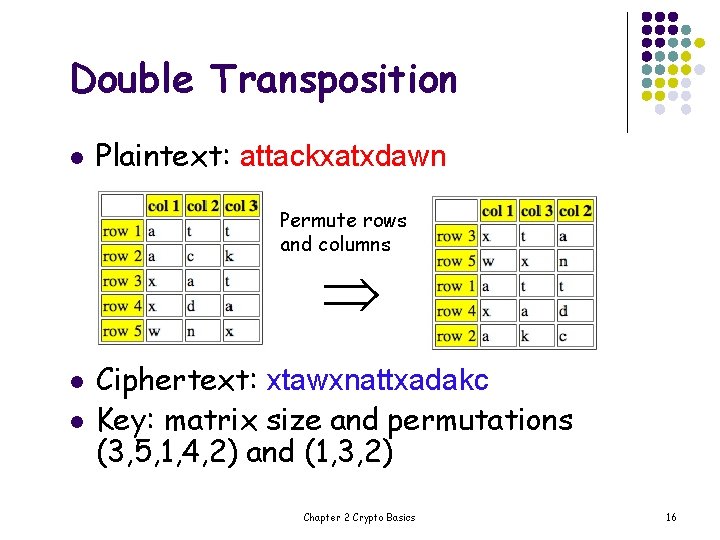
Double Transposition l Plaintext: attackxatxdawn Permute rows and columns l l Ciphertext: xtawxnattxadakc Key: matrix size and permutations (3, 5, 1, 4, 2) and (1, 3, 2) Chapter 2 Crypto Basics 16
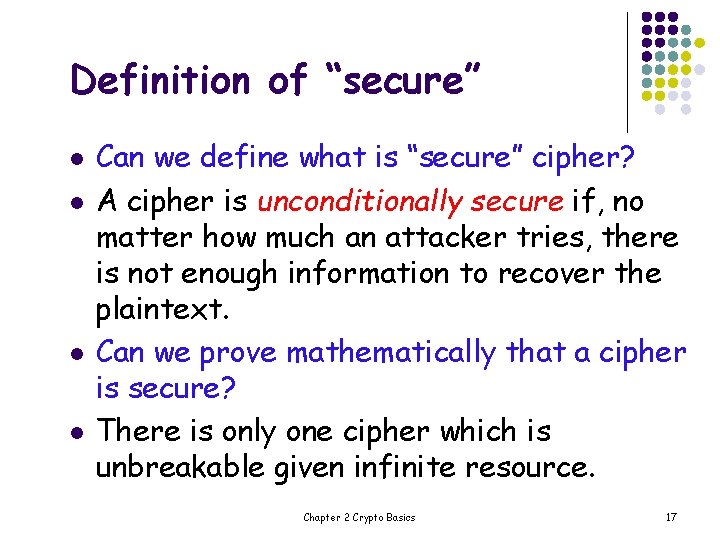
Definition of “secure” l l Can we define what is “secure” cipher? A cipher is unconditionally secure if, no matter how much an attacker tries, there is not enough information to recover the plaintext. Can we prove mathematically that a cipher is secure? There is only one cipher which is unbreakable given infinite resource. Chapter 2 Crypto Basics 17
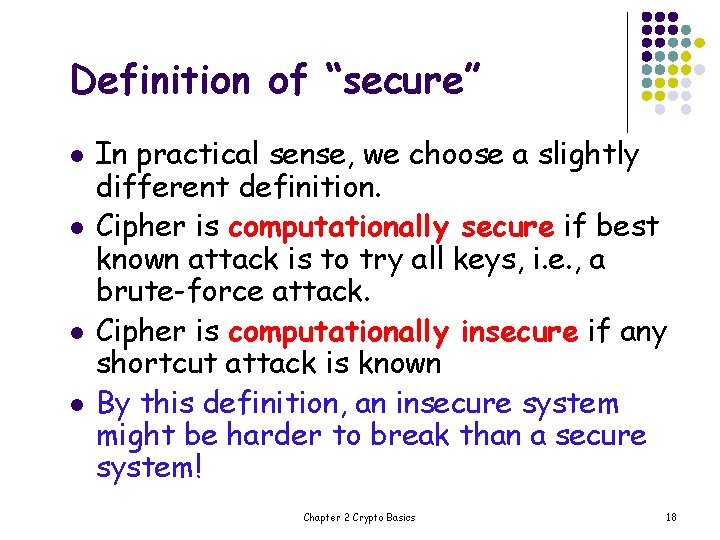
Definition of “secure” l l In practical sense, we choose a slightly different definition. Cipher is computationally secure if best known attack is to try all keys, i. e. , a brute-force attack. Cipher is computationally insecure if any shortcut attack is known By this definition, an insecure system might be harder to break than a secure system! Chapter 2 Crypto Basics 18
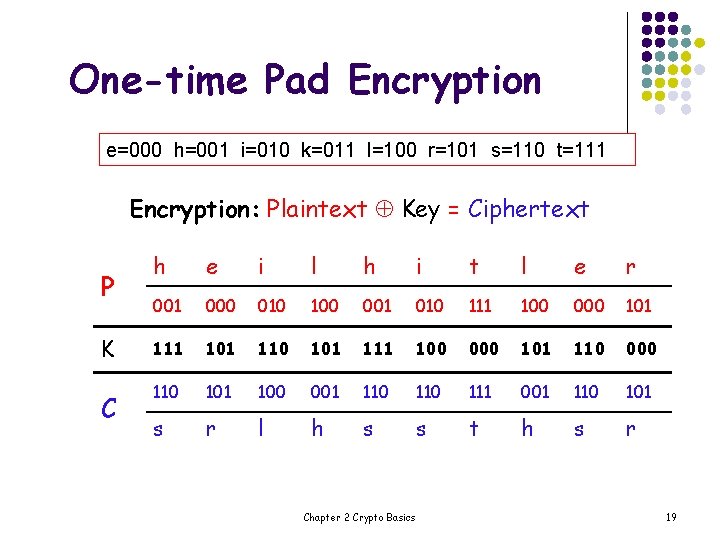
One-time Pad Encryption e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 Encryption: Plaintext Key = Ciphertext P K C h e i l h i t l e r 001 000 010 100 001 010 111 100 000 101 111 101 110 101 111 100 000 101 110 000 110 101 100 001 110 111 001 110 101 s r l h s s t h s r Chapter 2 Crypto Basics 19
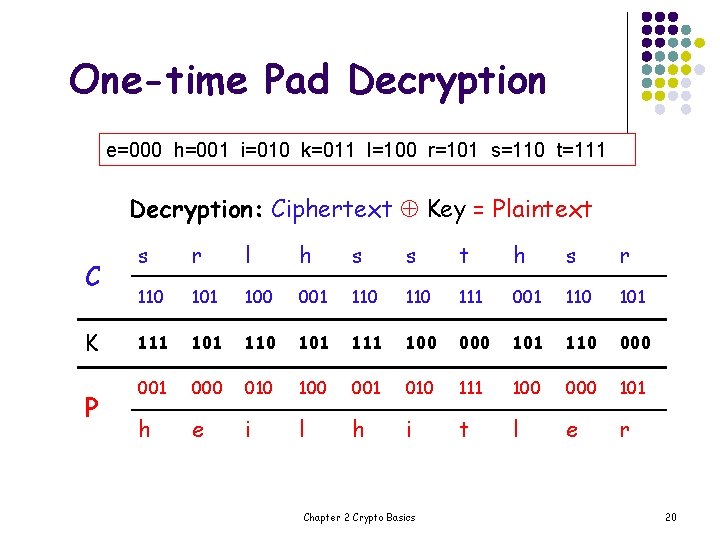
One-time Pad Decryption e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 Decryption: Ciphertext Key = Plaintext C K P s r l h s s t h s r 110 101 100 001 110 111 001 110 101 111 100 000 101 110 001 000 010 100 001 010 111 100 000 101 h e i l h i t l e r Chapter 2 Crypto Basics 20
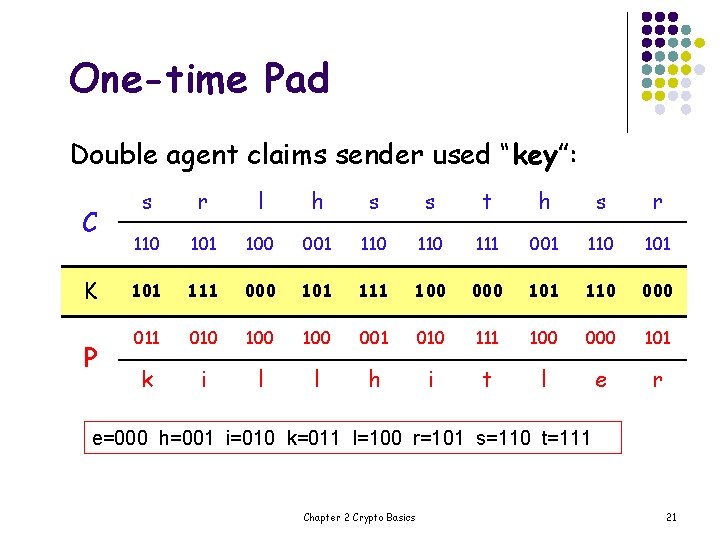
One-time Pad Double agent claims sender used “key”: C K P s r l h s s t h s r 110 101 100 001 110 111 001 110 101 111 000 101 111 100 000 101 110 000 011 010 100 001 010 111 100 000 101 k i l l h i t l e r e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 Chapter 2 Crypto Basics 21
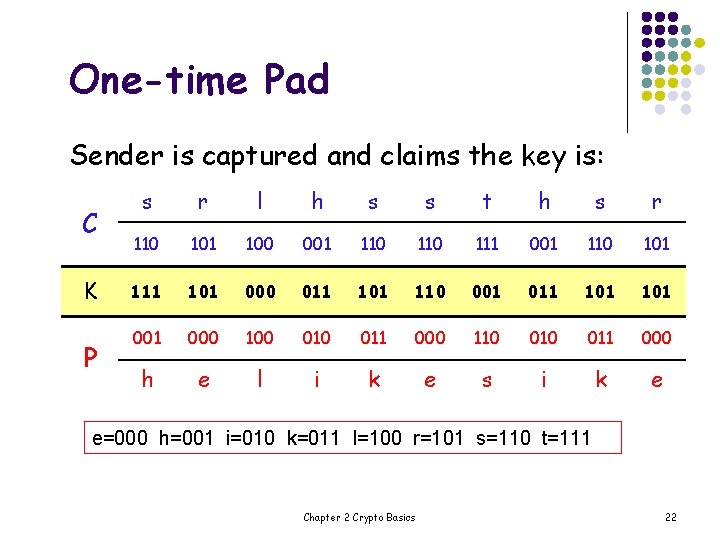
One-time Pad Sender is captured and claims the key is: C K P s r l h s s t h s r 110 101 100 001 110 111 001 110 101 111 101 000 011 101 110 001 011 101 000 100 011 000 110 011 000 h e l i k e s i k e e=000 h=001 i=010 k=011 l=100 r=101 s=110 t=111 Chapter 2 Crypto Basics 22
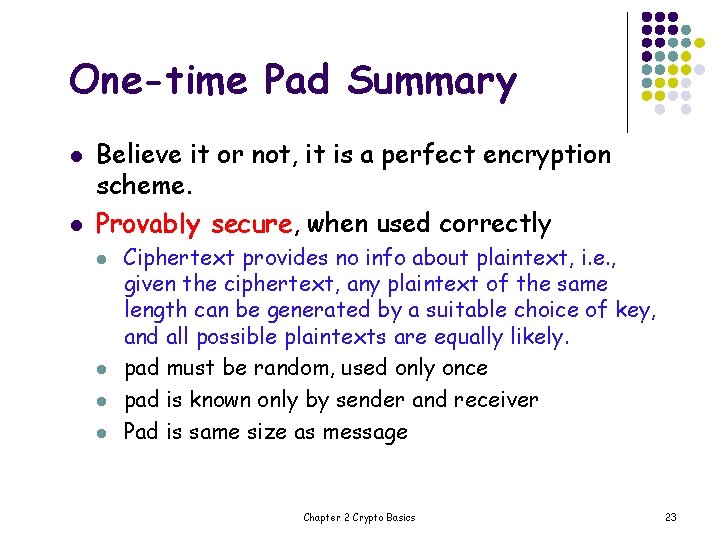
One-time Pad Summary l l Believe it or not, it is a perfect encryption scheme. Provably secure, when used correctly l l Ciphertext provides no info about plaintext, i. e. , given the ciphertext, any plaintext of the same length can be generated by a suitable choice of key, and all possible plaintexts are equally likely. pad must be random, used only once pad is known only by sender and receiver Pad is same size as message Chapter 2 Crypto Basics 23
One-time Pad Summary l l The pad is the same length as the message and the pad(key) must be securely transmitted to the recipient before the ciphertext can be decrypted. Then, if we can securely transmit the pad, why not transmit the message(plaintext) the same way as the pad(key)? Chapter 2 Crypto Basics 24
Real-world One-time Pad l Project VENONA l l l Soviet spy messages from U. S. in 1940’s Nuclear espionage, etc. Thousands of messaged Spy carried one-time pad into U. S. Spy used pad to encrypt secret messages Repeats within the “one-time” pads made cryptanalysis possible Chapter 2 Crypto Basics 25
![VENONA Decrypt (1944) [C% Ruth] learned that her husband [v] was called up by VENONA Decrypt (1944) [C% Ruth] learned that her husband [v] was called up by](http://slidetodoc.com/presentation_image/14926bc4eb4e57fd1d74fe1c30930d50/image-26.jpg)
VENONA Decrypt (1944) [C% Ruth] learned that her husband [v] was called up by the army but he was not sent to the front. He is a mechanical engineer and is now working at the ENORMOUS [ENORMOZ] [vi] plant in SANTA FE, New Mexico. [45 groups unrecoverable] detain VOLOK [vii] who is working in a plant on ENORMOUS. He is a FELLOWCOUNTRYMAN [ZEMLYa. K] [viii]. Yesterday he learned that they had dismissed him from his work. His active work in progressive organizations in the past was cause of his dismissal. In the FELLOWCOUNTRYMAN line LIBERAL is in touch with CHESTER [ix]. They meet once a month for the payment of dues. CHESTER is interested in whether we are satisfied with the collaboration and whethere are not any misunderstandings. He does not inquire about specific items of work [KONKRETNAYa RABOTA]. In as much as CHESTER knows about the role of LIBERAL's group we beg consent to ask C. through LIBERAL about leads from among people who are working on ENOURMOUS and in other technical fields. l l l “Ruth” == Ruth Greenglass “Liberal” == Julius Rosenberg “Enormous” == the atomic bomb Chapter 2 Crypto Basics 26
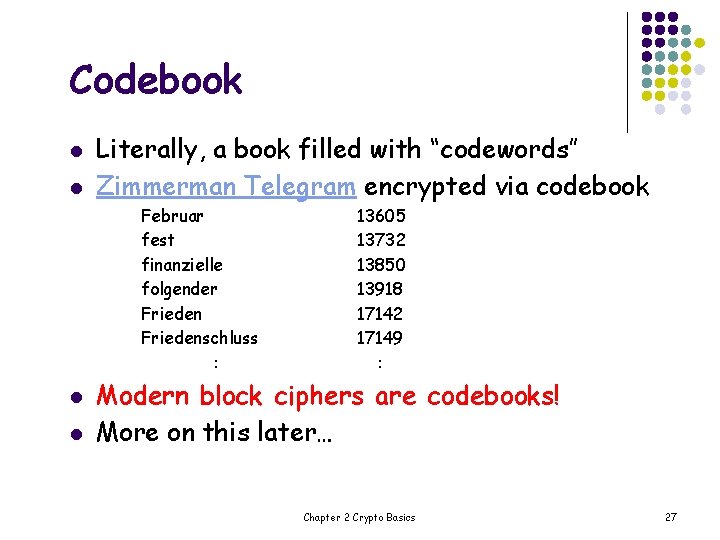
Codebook l l Literally, a book filled with “codewords” Zimmerman Telegram encrypted via codebook Februar fest finanzielle folgender Friedenschluss : l l 13605 13732 13850 13918 17142 17149 : Modern block ciphers are codebooks! More on this later… Chapter 2 Crypto Basics 27
Zimmerman Telegram l l l One of most famous codebook ciphers ever Led to US entry in WWI Ciphertext shown here… Chapter 2 Crypto Basics 28
Zimmerman Telegram Decrypted l l British had recovered partial codebook Able to fill in missing parts Chapter 2 Crypto Basics 29
A Few Historical Items l l Crypto timeline l Answers. com l Wikipedia Transposition cipher l l Substitution cipher l l l Spartan Scytale[saiteil] Caesar’s cipher Poe’s The Gold Bug: See here Election of 1876 Chapter 2 Crypto Basics 30
Election of 1876 l l l “Rutherfraud” Hayes vs “Swindling” Tilden: Popular vote was virtual tie Electoral college delegations for 4 states (including Florida) in dispute Commission: All 4 states to Hayes Tilden accused Hayes of bribery Was it true? Chapter 2 Crypto Basics 31
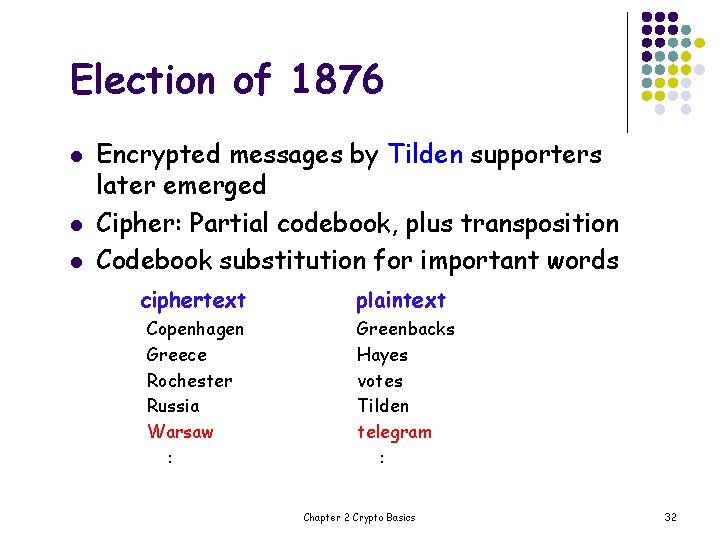
Election of 1876 l l l Encrypted messages by Tilden supporters later emerged Cipher: Partial codebook, plus transposition Codebook substitution for important words ciphertext plaintext Copenhagen Greece Rochester Russia Warsaw : Greenbacks Hayes votes Tilden telegram : Chapter 2 Crypto Basics 32
Election of 1876 l l l Apply codebook to original message Pad message to multiple of 5 words (total length, 10, 15, 20, 25 or 30 words) For each length, a fixed permutation applied to resulting message Permutations found by comparing many messages of same length Note that the same key is applied to all messages of a given length Chapter 2 Crypto Basics 33
Election of 1876 l l l Ciphertext: Warsaw they read all unchanged last are idiots can’t situation Codebook: Warsaw telegram Transposition: 9, 3, 6, 1, 10, 5, 2, 7, 4, 8 Plaintext: Can’t read last telegram. Situation unchanged. They are all idiots. A weak cipher made worse by reuse of key Lesson: Don’t reuse/overuse keys! Chapter 2 Crypto Basics 34
Early 20 th Century l l l WWI Zimmerman Telegram “Gentlemen do not read each other’s mail” Henry L. Stimson, Secretary of State, 1929 WWII golden age of cryptanalysis l l Japanese Purple (codename MAGIC) German Enigma (codename ULTRA) Chapter 2 Crypto Basics 35
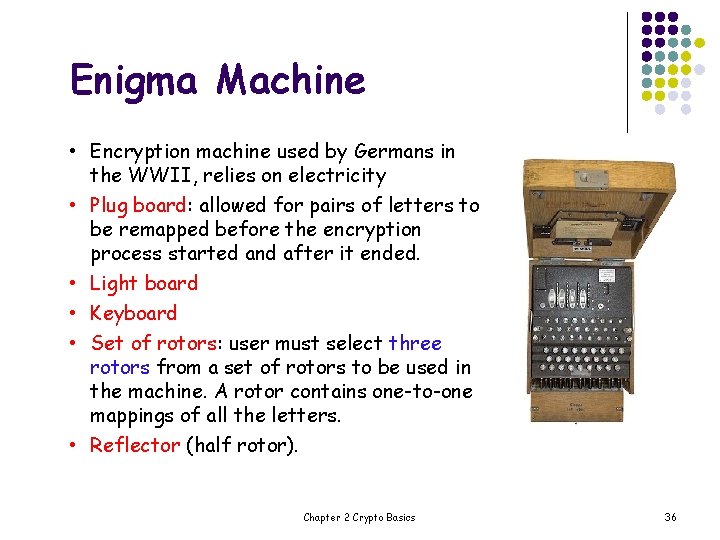
Enigma Machine • Encryption machine used by Germans in the WWII, relies on electricity • Plug board: allowed for pairs of letters to be remapped before the encryption process started and after it ended. • Light board • Keyboard • Set of rotors: user must select three rotors from a set of rotors to be used in the machine. A rotor contains one-to-one mappings of all the letters. • Reflector (half rotor). Chapter 2 Crypto Basics 36
How does it work? l Current passes through: ― ― ― l the plug board, the three rotors, the reflector which reverses the current, back through the three rotors, back through the plug board then the encrypted letter is lit on the display. For each letter, the rotors rotate. The rotors rotate such as the right most rotor must complete one revolution before the middle rotor rotated one position and so on. Chapter 2 Crypto Basics 37
Letters Remapped l The whole encryption process for a single letter contains a minimum of 7 remappings (the current passes through the rotors twice) and a maximum of 9 remappings (if the letter has a connection in the plug board). ― ― ― Plug board performs the first remapping, if the letter has a connection in the plug board. Rotors remap letters. Each rotor contains one-to-one mappings of letters but since the rotors rotate on each key press, the mappings of the rotors change on every key press. The reflector does one more remapping, the one-to-one mappings are always the same. Chapter 2 Crypto Basics 38
Decryption l l Need the encrypted message, and know which rotors were used, the connections on the plug board and the initial settings of the rotors. Without the knowledge of the state of the machine when the original message was typed in, it is extremely difficult to decode a message. Chapter 2 Crypto Basics 39
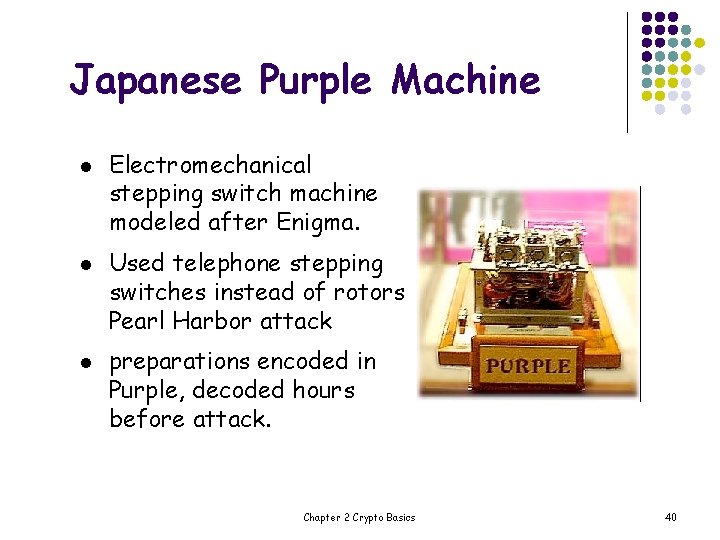
Japanese Purple Machine l l l Electromechanical stepping switch machine modeled after Enigma. Used telephone stepping switches instead of rotors Pearl Harbor attack preparations encoded in Purple, decoded hours before attack. Chapter 2 Crypto Basics 40
Post-WWII History l l l l Claude Shannon father of the science of information theory Computer revolution lots of data Data Encryption Standard (DES), 70’s Public Key cryptography, 70’s CRYPTO conferences, 80’s Advanced Encryption Standard (AES), 90’s Crypto moved out of classified world Chapter 2 Crypto Basics 41
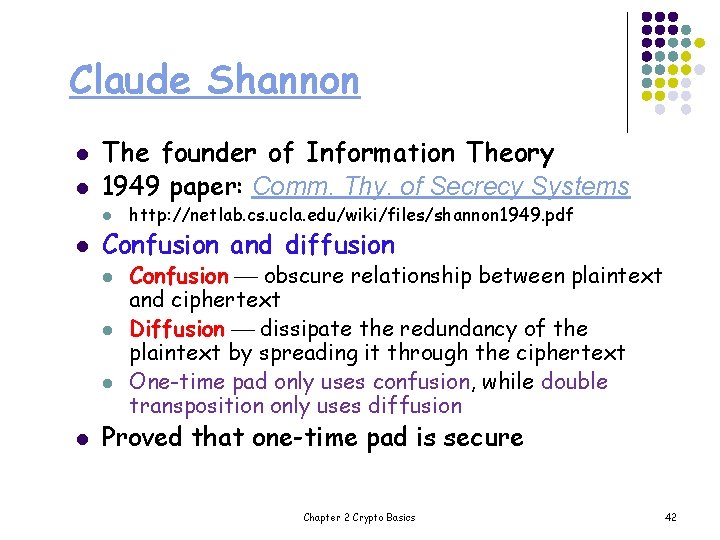
Claude Shannon l l The founder of Information Theory 1949 paper: Comm. Thy. of Secrecy Systems l l Confusion and diffusion l l http: //netlab. cs. ucla. edu/wiki/files/shannon 1949. pdf Confusion obscure relationship between plaintext and ciphertext Diffusion dissipate the redundancy of the plaintext by spreading it through the ciphertext One-time pad only uses confusion, while double transposition only uses diffusion Proved that one-time pad is secure Chapter 2 Crypto Basics 42
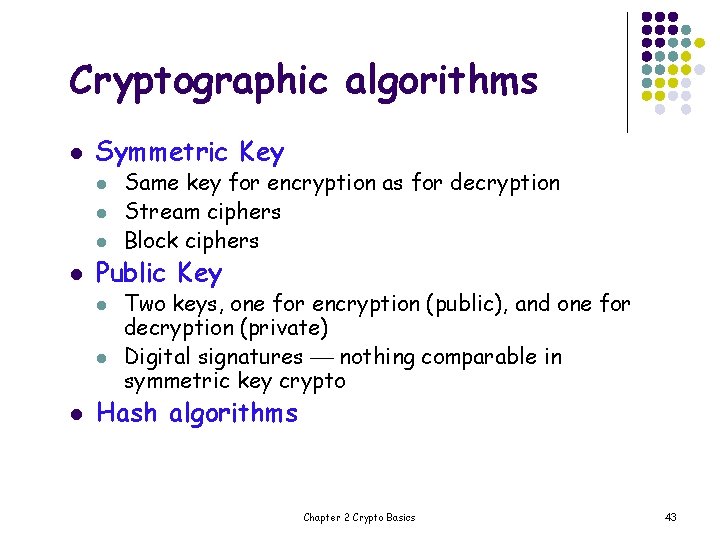
Cryptographic algorithms l Symmetric Key l l Public Key l l l Same key for encryption as for decryption Stream ciphers Block ciphers Two keys, one for encryption (public), and one for decryption (private) Digital signatures nothing comparable in symmetric key crypto Hash algorithms Chapter 2 Crypto Basics 43
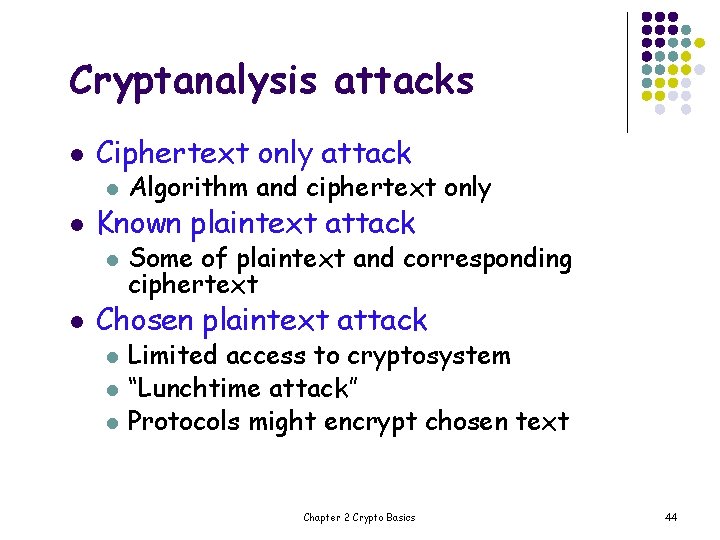
Cryptanalysis attacks l l l Ciphertext only attack l Algorithm and ciphertext only l Some of plaintext and corresponding ciphertext Known plaintext attack Chosen plaintext attack l l l Limited access to cryptosystem “Lunchtime attack” Protocols might encrypt chosen text Chapter 2 Crypto Basics 44
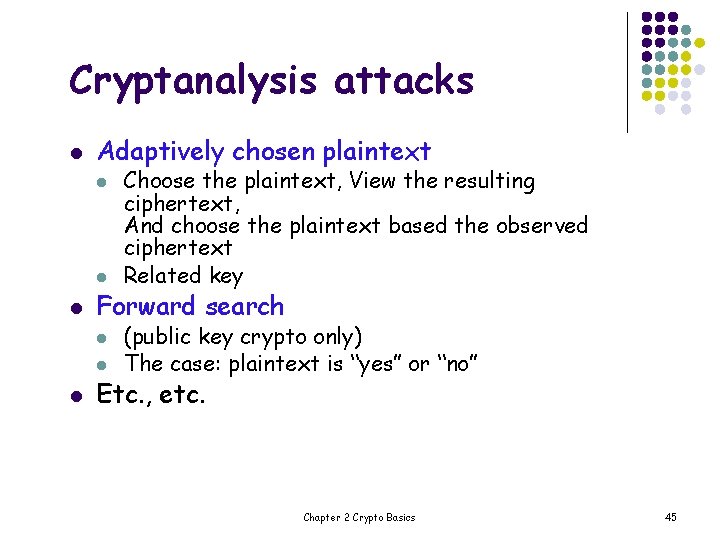
Cryptanalysis attacks l Adaptively chosen plaintext l l l Forward search l l l Choose the plaintext, View the resulting ciphertext, And choose the plaintext based the observed ciphertext Related key (public key crypto only) The case: plaintext is “yes” or “no” Etc. , etc. Chapter 2 Crypto Basics 45
- Slides: 45