Application Layer Jim Kurose and Keith Ross Computer
![Electronic Mail: SMTP [RFC 2821] r uses TCP to reliably transfer email message from Electronic Mail: SMTP [RFC 2821] r uses TCP to reliably transfer email message from](https://slidetodoc.com/presentation_image_h2/247b2a95e1a2821124c4fb9c321e7d0d/image-43.jpg)
- Slides: 72
Application Layer* *Jim Kurose and Keith Ross “Computer Networking: A Top Down Approach Featuring the Internet”, 3 rd edition. , Addison-Wesley, July 2004.
Application layer r Principles of network applications r Web and HTTP r Electronic Mail m SMTP, POP 3, IMAP r Socket programming with TCP r Socket programming with UDP
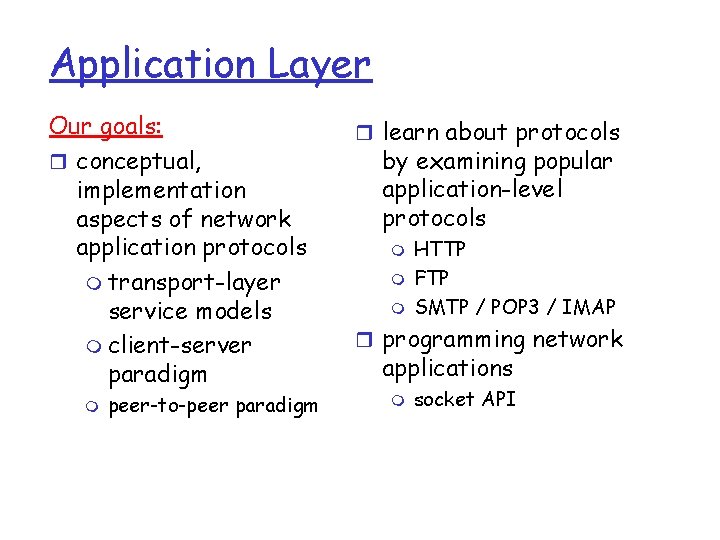
Application Layer Our goals: r conceptual, implementation aspects of network application protocols m transport-layer service models m client-server paradigm m peer-to-peer paradigm r learn about protocols by examining popular application-level protocols m m m HTTP FTP SMTP / POP 3 / IMAP r programming network applications m socket API
Some network apps r E-mail r Internet telephone r Web r Real-time video r Instant messaging r Remote login r P 2 P file sharing r Multi-user network games r Streaming stored video clips conference r Massive parallel computing
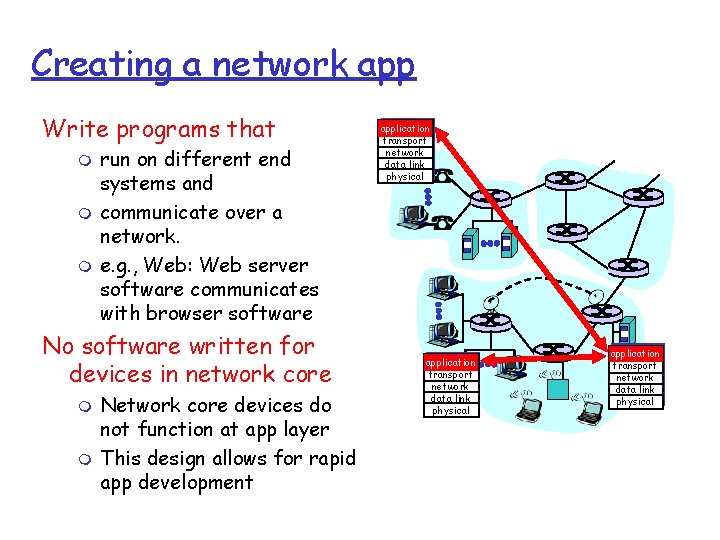
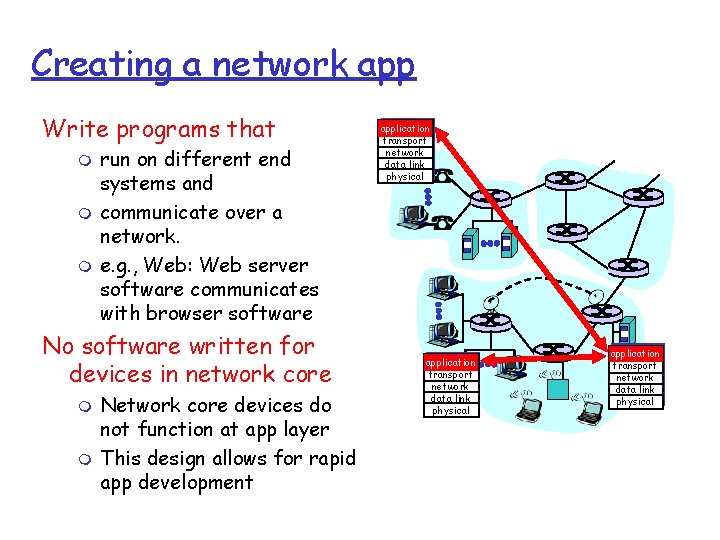
Creating a network app Write programs that m m m run on different end systems and communicate over a network. e. g. , Web: Web server software communicates with browser software No software written for devices in network core m m Network core devices do not function at app layer This design allows for rapid app development application transport network data link physical
Application layer r Principles of network applications r Web and HTTP r Electronic Mail m SMTP, POP 3, IMAP r Socket programming with TCP r Socket programming with UDP
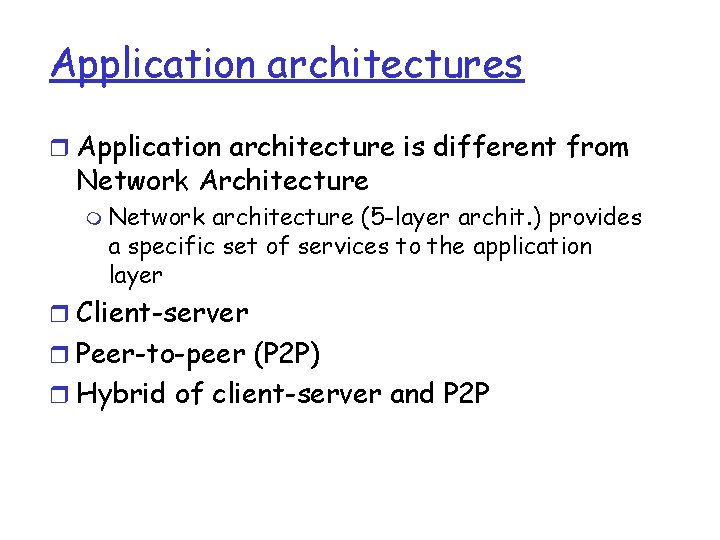
Application architectures r Application architecture is different from Network Architecture m Network architecture (5 -layer archit. ) provides a specific set of services to the application layer r Client-server r Peer-to-peer (P 2 P) r Hybrid of client-server and P 2 P
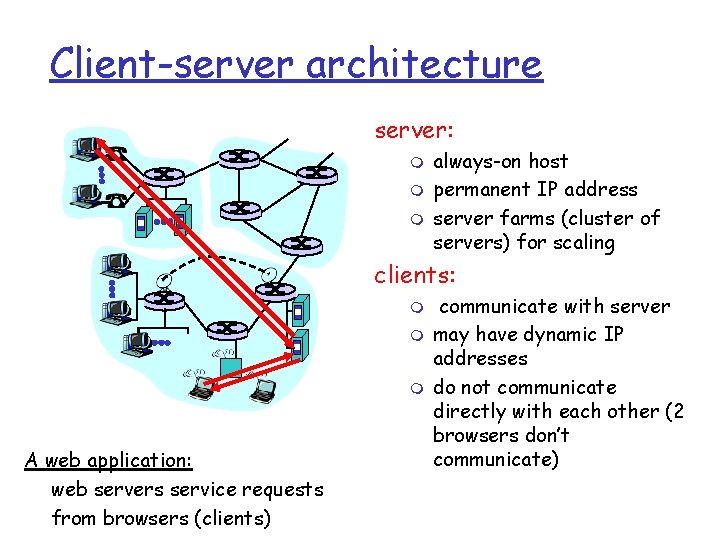
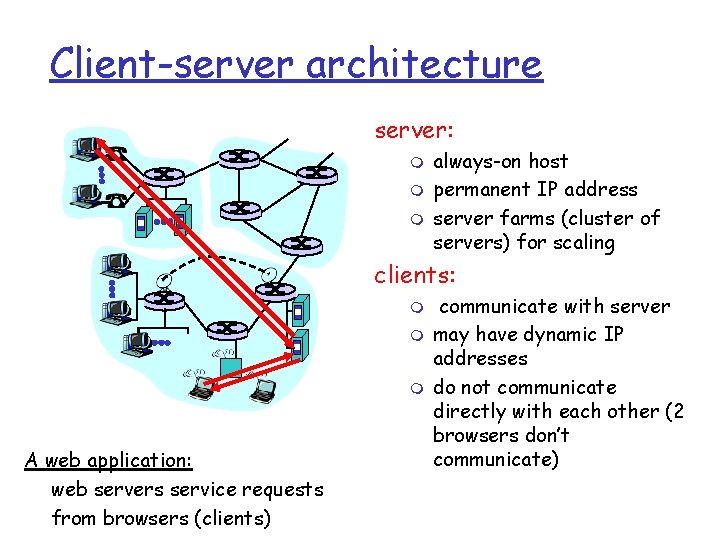
Client-server architecture server: m m m always-on host permanent IP address server farms (cluster of servers) for scaling clients: m m m A web application: web servers service requests from browsers (clients) communicate with server may have dynamic IP addresses do not communicate directly with each other (2 browsers don’t communicate)
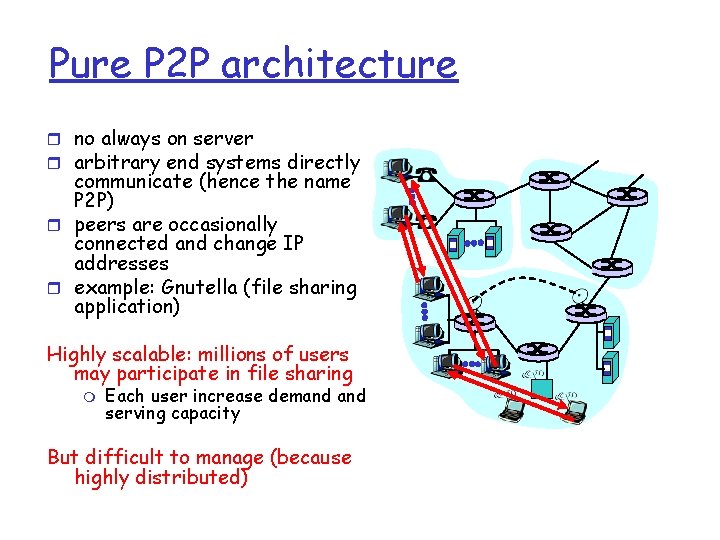
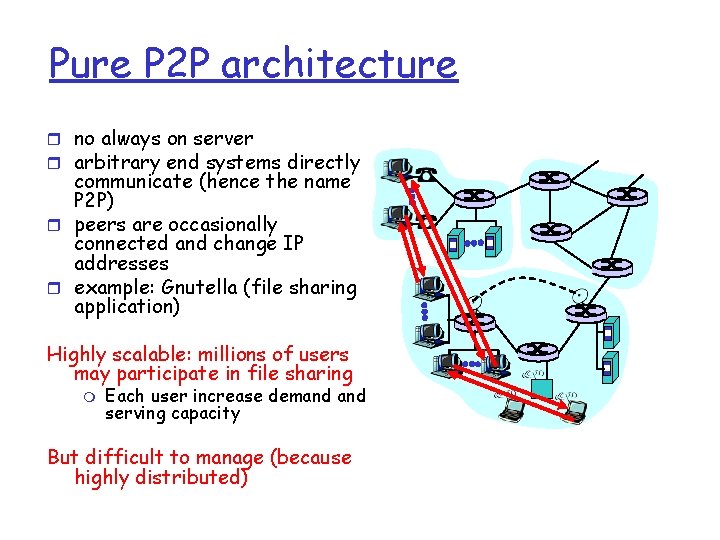
Pure P 2 P architecture r no always on server r arbitrary end systems directly communicate (hence the name P 2 P) r peers are occasionally connected and change IP addresses r example: Gnutella (file sharing application) Highly scalable: millions of users may participate in file sharing m Each user increase demand serving capacity But difficult to manage (because highly distributed)
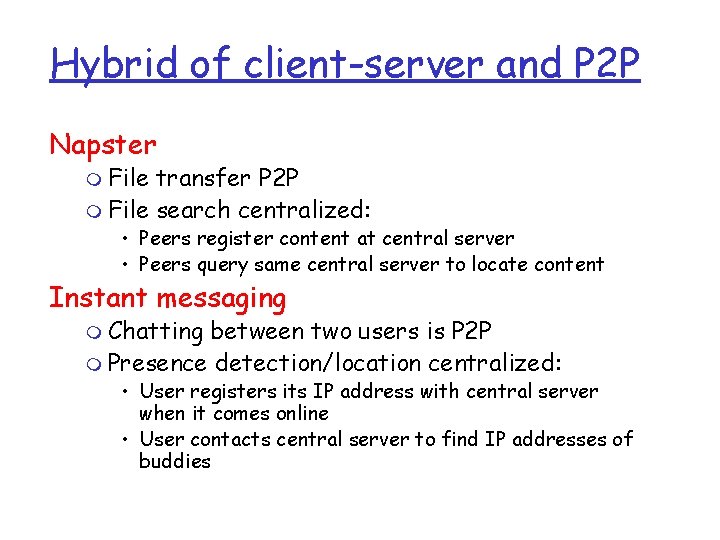
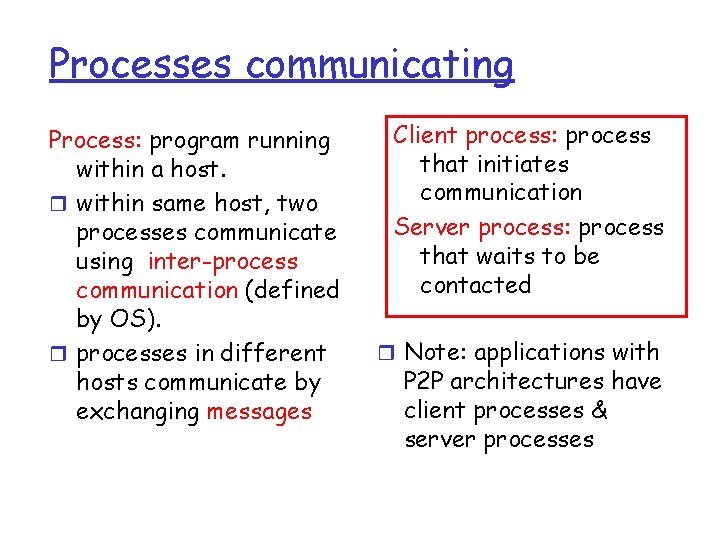
Hybrid of client-server and P 2 P Napster m File transfer P 2 P m File search centralized: • Peers register content at central server • Peers query same central server to locate content Instant messaging m Chatting between two users is P 2 P m Presence detection/location centralized: • User registers its IP address with central server when it comes online • User contacts central server to find IP addresses of buddies
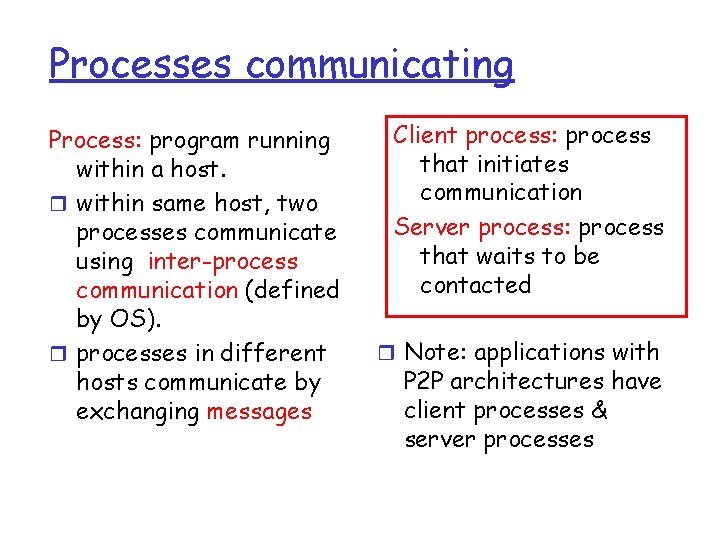
Processes communicating Process: program running within a host. r within same host, two processes communicate using inter-process communication (defined by OS). r processes in different hosts communicate by exchanging messages Client process: process that initiates communication Server process: process that waits to be contacted r Note: applications with P 2 P architectures have client processes & server processes
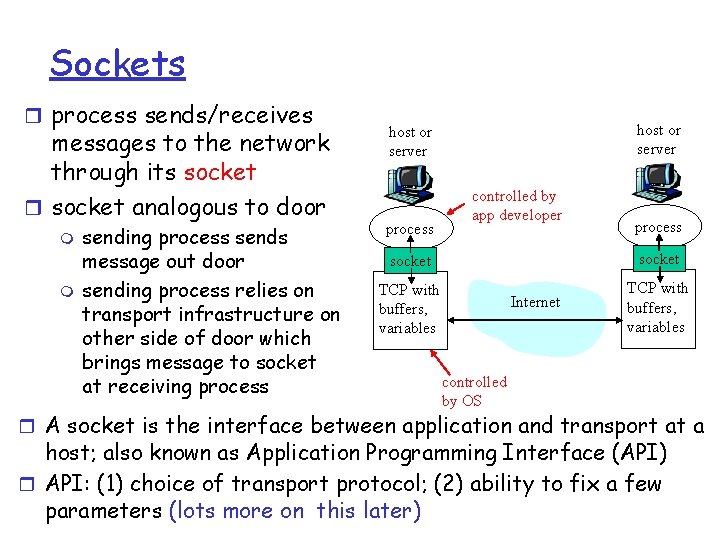
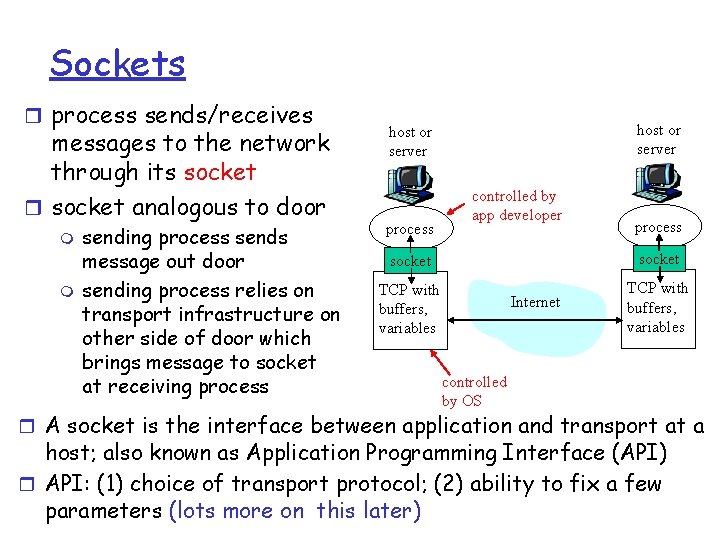
Sockets r process sends/receives messages to the network through its socket r socket analogous to door m m sending process sends message out door sending process relies on transport infrastructure on other side of door which brings message to socket at receiving process host or server process controlled by app developer process socket TCP with buffers, variables Internet TCP with buffers, variables controlled by OS r A socket is the interface between application and transport at a host; also known as Application Programming Interface (API) r API: (1) choice of transport protocol; (2) ability to fix a few parameters (lots more on this later)
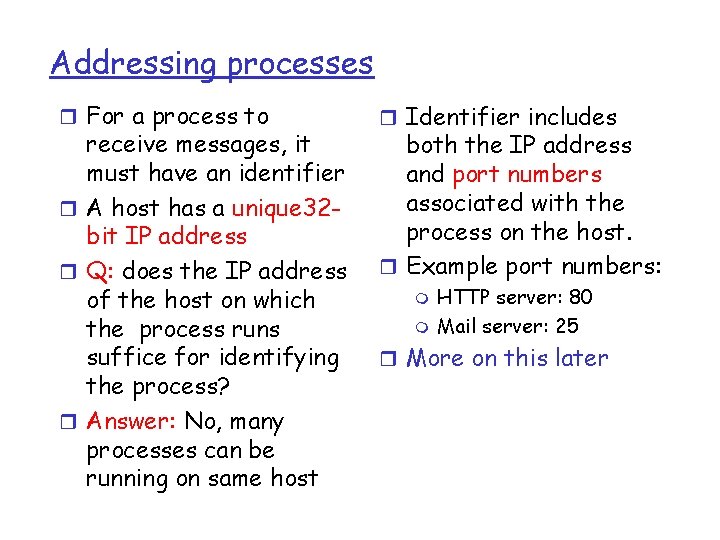
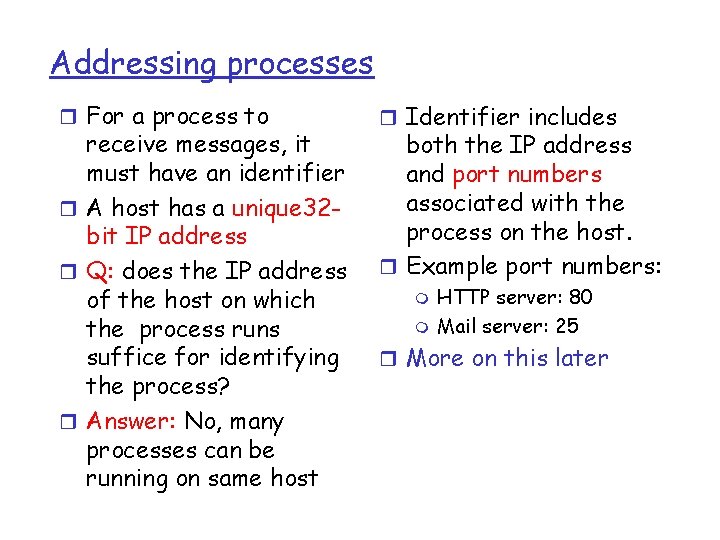
Addressing processes r For a process to receive messages, it must have an identifier r A host has a unique 32 bit IP address r Q: does the IP address of the host on which the process runs suffice for identifying the process? r Answer: No, many processes can be running on same host r Identifier includes both the IP address and port numbers associated with the process on the host. r Example port numbers: m m HTTP server: 80 Mail server: 25 r More on this later
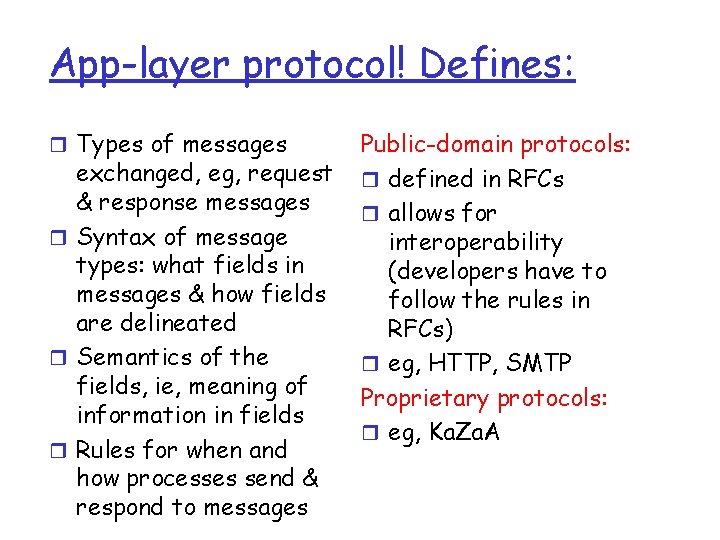
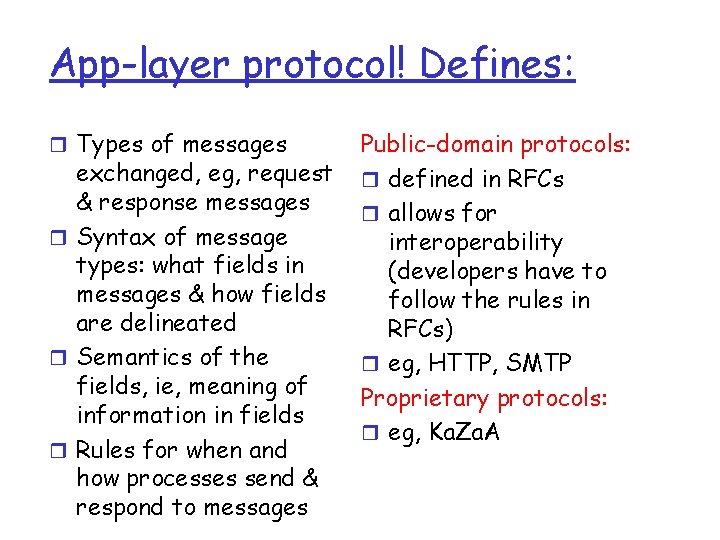
App-layer protocol! Defines: r Types of messages exchanged, eg, request & response messages r Syntax of message types: what fields in messages & how fields are delineated r Semantics of the fields, ie, meaning of information in fields r Rules for when and how processes send & respond to messages Public-domain protocols: r defined in RFCs r allows for interoperability (developers have to follow the rules in RFCs) r eg, HTTP, SMTP Proprietary protocols: r eg, Ka. Za. A
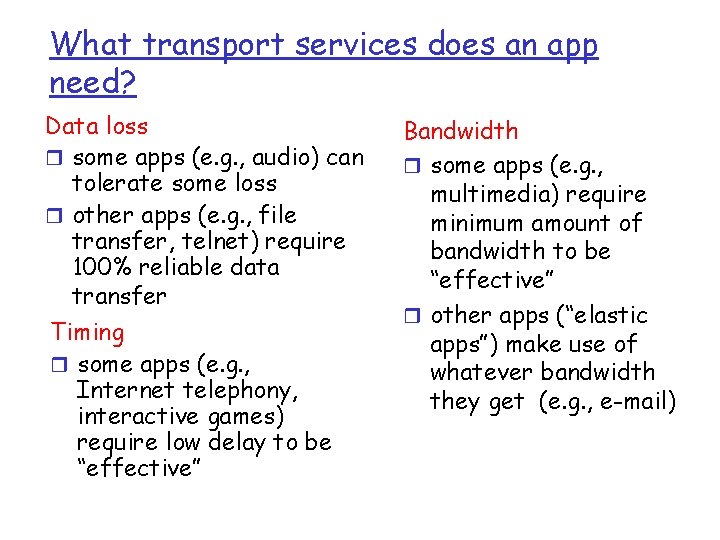
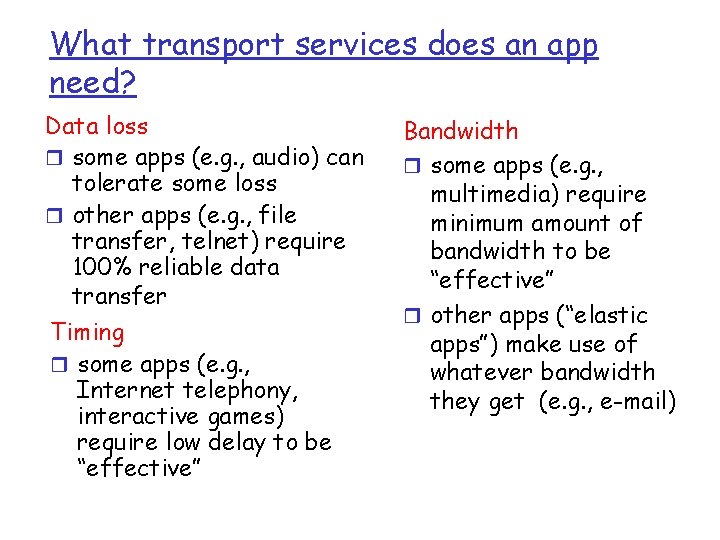
What transport services does an app need? Data loss r some apps (e. g. , audio) can tolerate some loss r other apps (e. g. , file transfer, telnet) require 100% reliable data transfer Timing r some apps (e. g. , Internet telephony, interactive games) require low delay to be “effective” Bandwidth r some apps (e. g. , multimedia) require minimum amount of bandwidth to be “effective” r other apps (“elastic apps”) make use of whatever bandwidth they get (e. g. , e-mail)
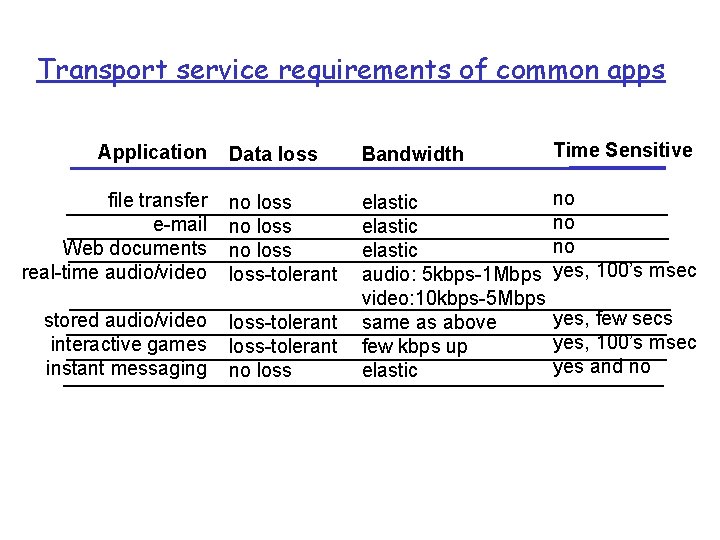
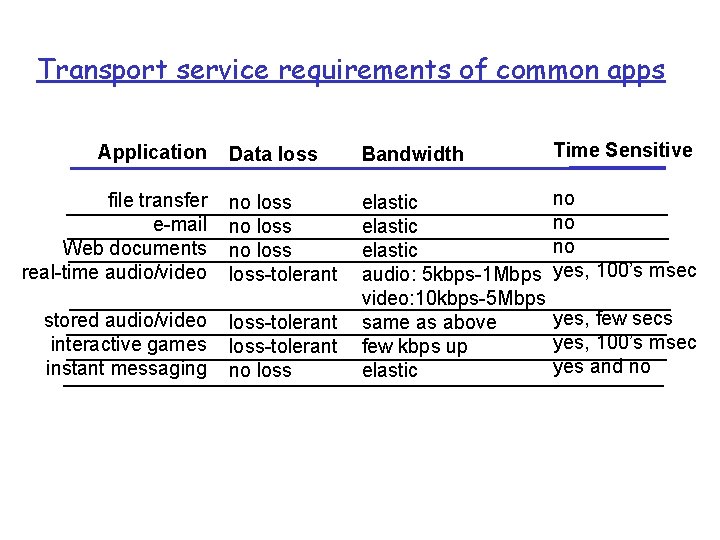
Transport service requirements of common apps Data loss Bandwidth Time Sensitive file transfer e-mail Web documents real-time audio/video no loss-tolerant no no no yes, 100’s msec stored audio/video interactive games instant messaging loss-tolerant no loss elastic audio: 5 kbps-1 Mbps video: 10 kbps-5 Mbps same as above few kbps up elastic Application yes, few secs yes, 100’s msec yes and no
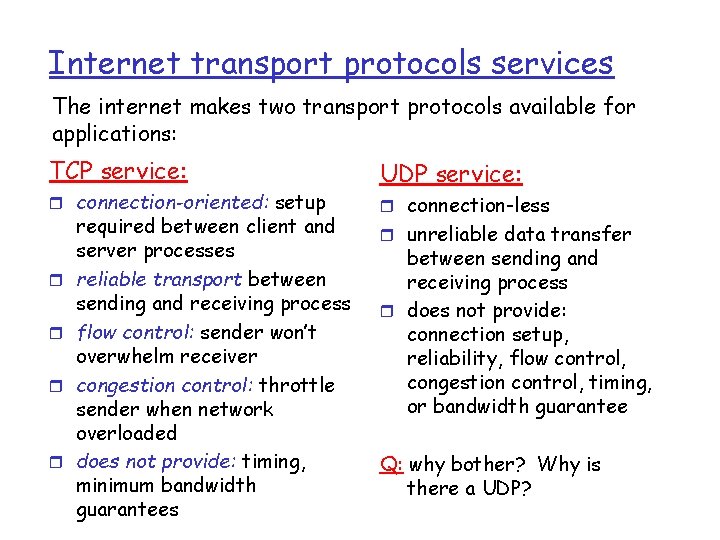
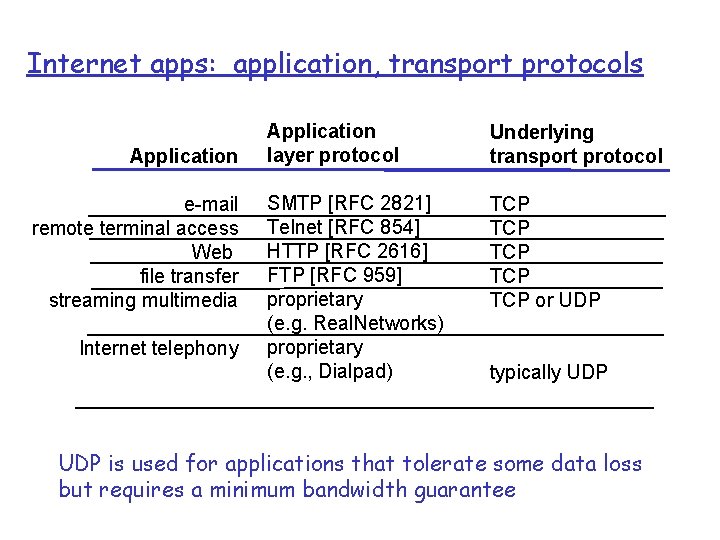
Internet transport protocols services The internet makes two transport protocols available for applications: TCP service: r connection-oriented: setup r r required between client and server processes reliable transport between sending and receiving process flow control: sender won’t overwhelm receiver congestion control: throttle sender when network overloaded does not provide: timing, minimum bandwidth guarantees UDP service: r connection-less r unreliable data transfer between sending and receiving process r does not provide: connection setup, reliability, flow control, congestion control, timing, or bandwidth guarantee Q: why bother? Why is there a UDP?
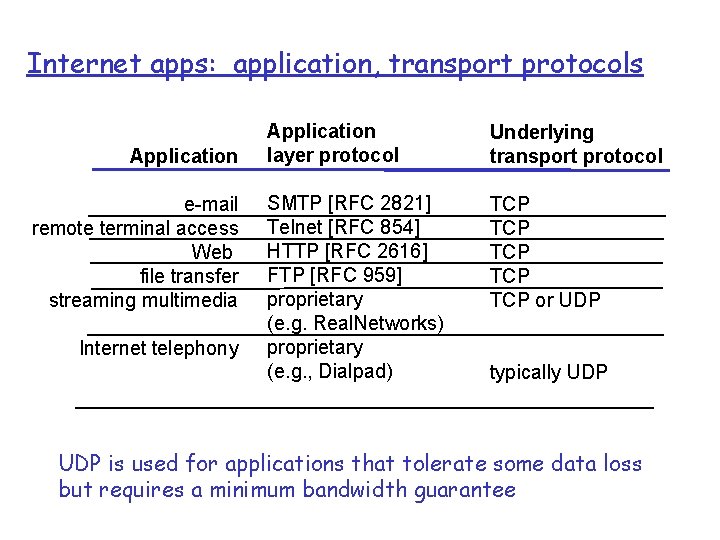
Internet apps: application, transport protocols Application e-mail remote terminal access Web file transfer streaming multimedia Internet telephony Application layer protocol Underlying transport protocol SMTP [RFC 2821] Telnet [RFC 854] HTTP [RFC 2616] FTP [RFC 959] proprietary (e. g. Real. Networks) proprietary (e. g. , Dialpad) TCP TCP TCP or UDP typically UDP is used for applications that tolerate some data loss but requires a minimum bandwidth guarantee
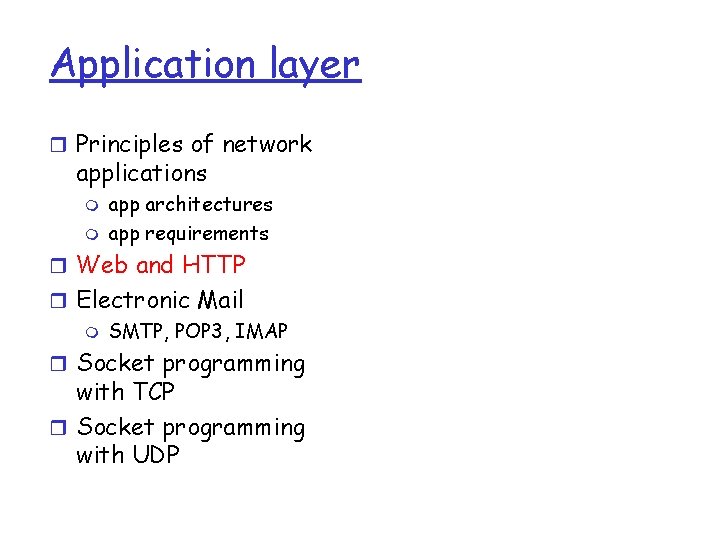
Application layer r Principles of network applications m m app architectures app requirements r Web and HTTP r Electronic Mail m SMTP, POP 3, IMAP r Socket programming with TCP r Socket programming with UDP
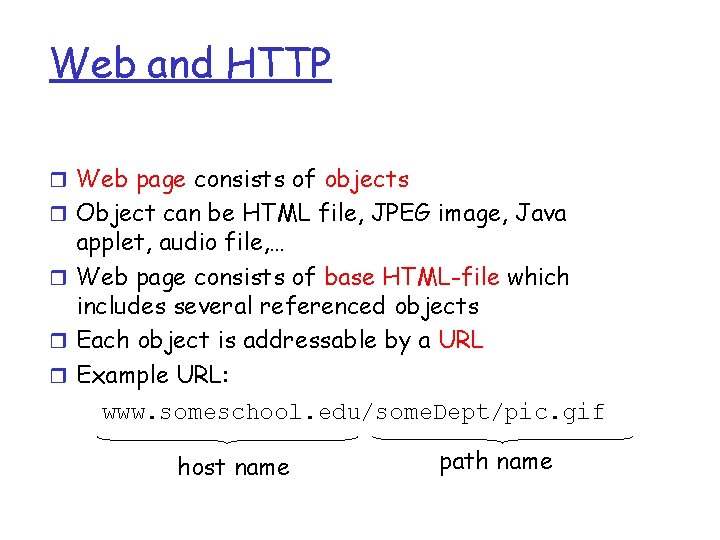
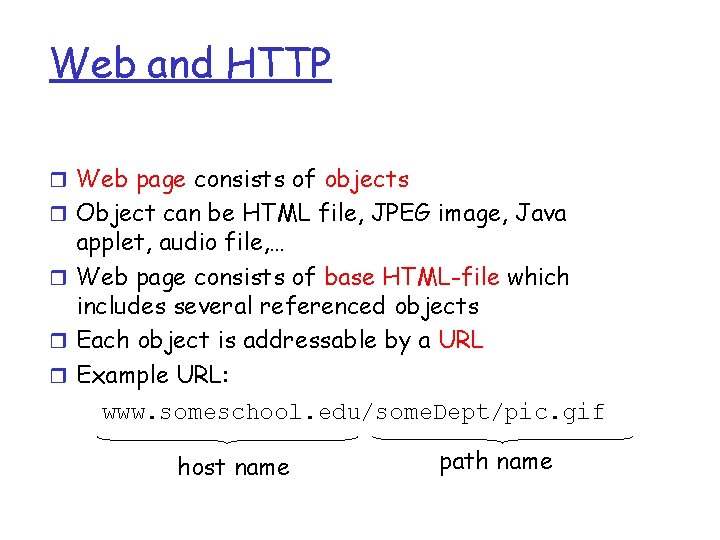
Web and HTTP r Web page consists of objects r Object can be HTML file, JPEG image, Java applet, audio file, … r Web page consists of base HTML-file which includes several referenced objects r Each object is addressable by a URL r Example URL: www. someschool. edu/some. Dept/pic. gif host name path name
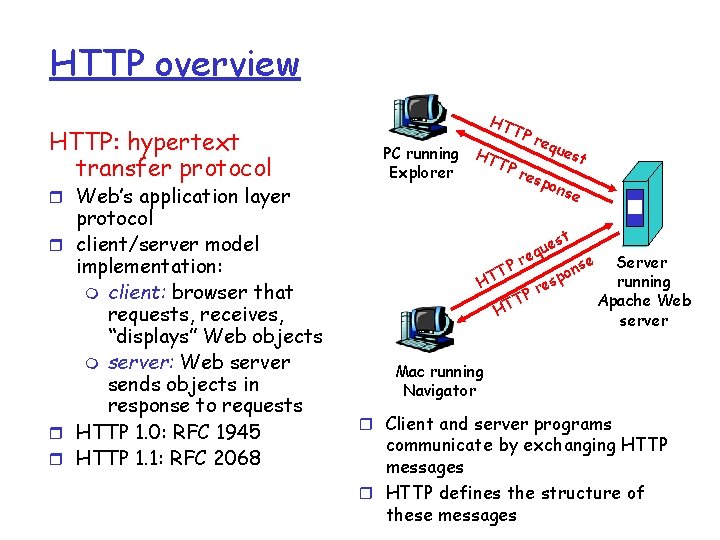
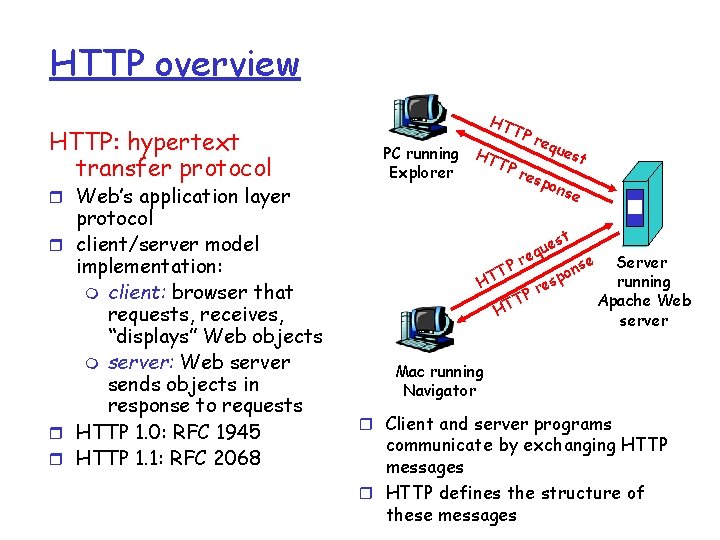
HTTP overview HTTP: hypertext transfer protocol r Web’s application layer protocol r client/server model implementation: m client: browser that requests, receives, “displays” Web objects m server: Web server sends objects in response to requests r HTTP 1. 0: RFC 1945 r HTTP 1. 1: RFC 2068 HT TP req ues PC running HT t TP res Explorer pon se t es u q e r TP HT HT r TP e n spo se Server running Apache Web server Mac running Navigator r Client and server programs communicate by exchanging HTTP messages r HTTP defines the structure of these messages
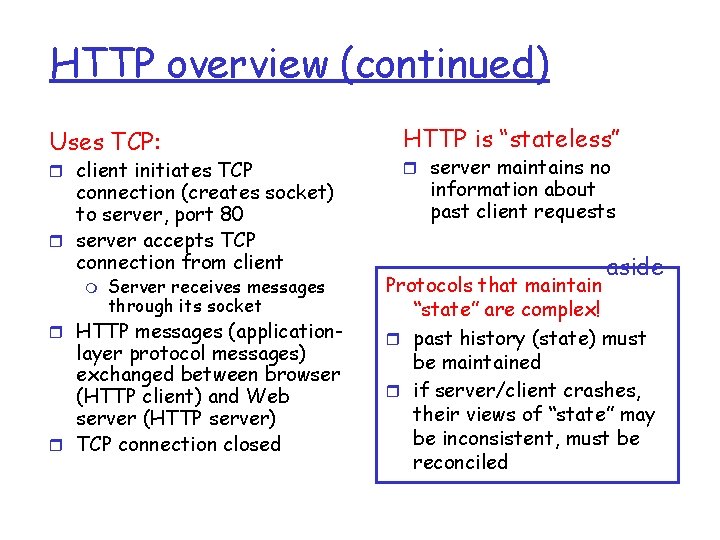
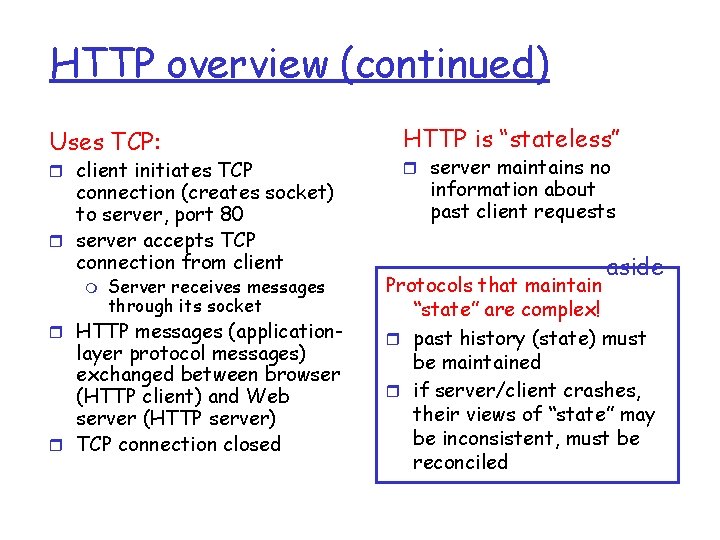
HTTP overview (continued) Uses TCP: r client initiates TCP connection (creates socket) to server, port 80 r server accepts TCP connection from client m Server receives messages through its socket r HTTP messages (application- layer protocol messages) exchanged between browser (HTTP client) and Web server (HTTP server) r TCP connection closed HTTP is “stateless” r server maintains no information about past client requests aside Protocols that maintain “state” are complex! r past history (state) must be maintained r if server/client crashes, their views of “state” may be inconsistent, must be reconciled
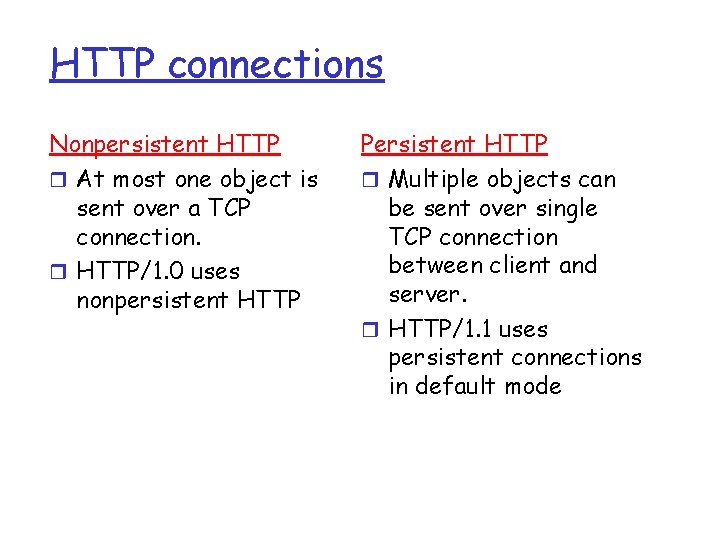
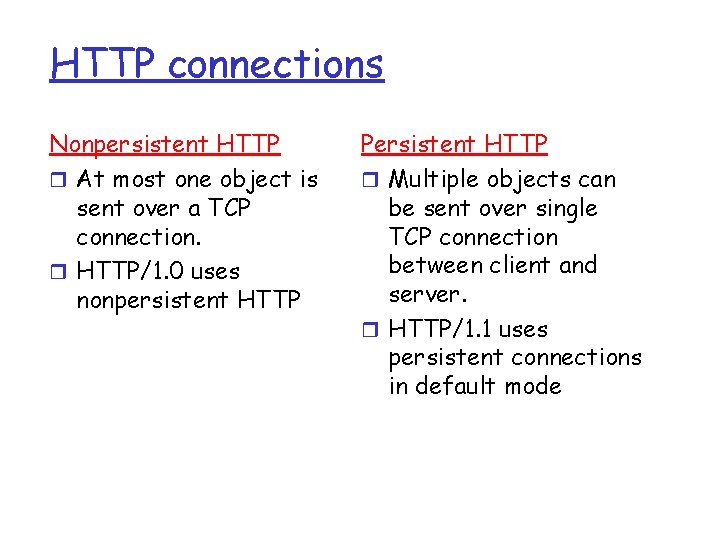
HTTP connections Nonpersistent HTTP r At most one object is sent over a TCP connection. r HTTP/1. 0 uses nonpersistent HTTP Persistent HTTP r Multiple objects can be sent over single TCP connection between client and server. r HTTP/1. 1 uses persistent connections in default mode
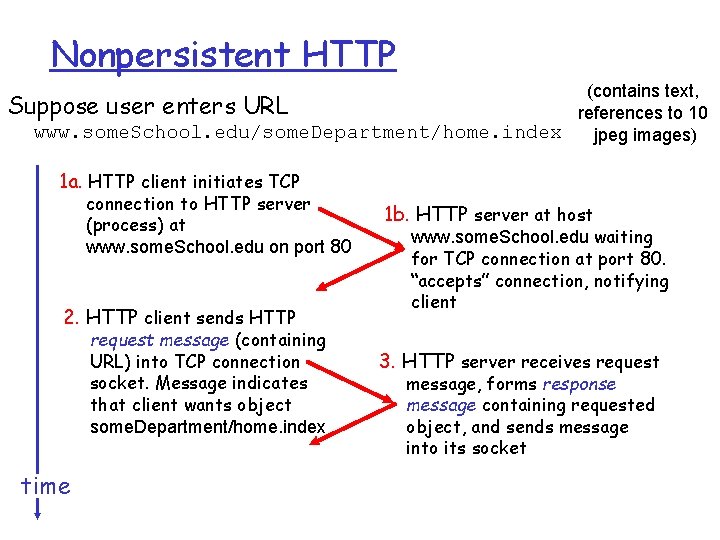
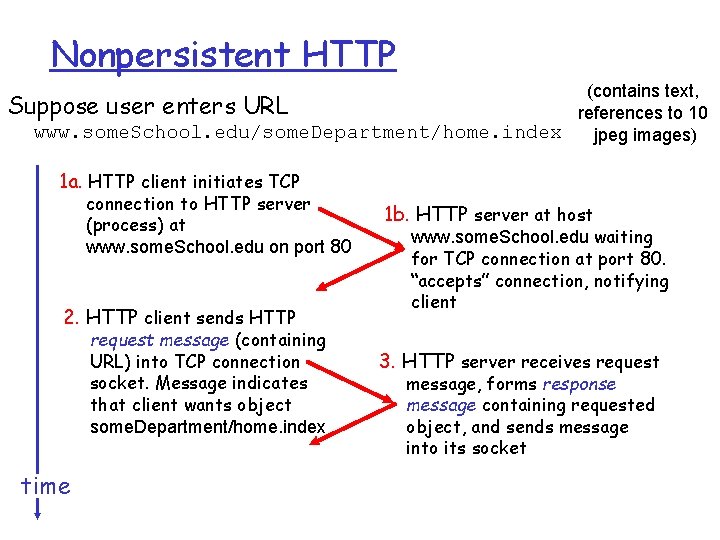
Nonpersistent HTTP (contains text, Suppose user enters URL references to 10 www. some. School. edu/some. Department/home. index jpeg images) 1 a. HTTP client initiates TCP connection to HTTP server (process) at www. some. School. edu on port 80 2. HTTP client sends HTTP request message (containing URL) into TCP connection socket. Message indicates that client wants object some. Department/home. index time 1 b. HTTP server at host www. some. School. edu waiting for TCP connection at port 80. “accepts” connection, notifying client 3. HTTP server receives request message, forms response message containing requested object, and sends message into its socket
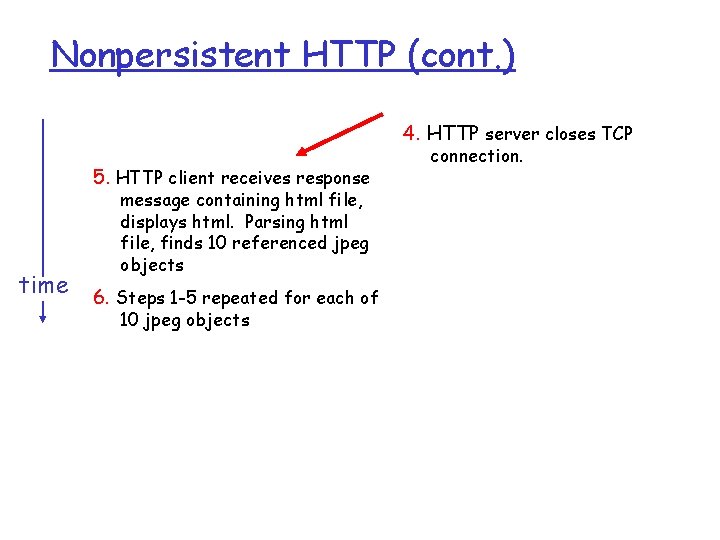
Nonpersistent HTTP (cont. ) 4. HTTP server closes TCP 5. HTTP client receives response message containing html file, displays html. Parsing html file, finds 10 referenced jpeg objects time 6. Steps 1 -5 repeated for each of 10 jpeg objects connection.
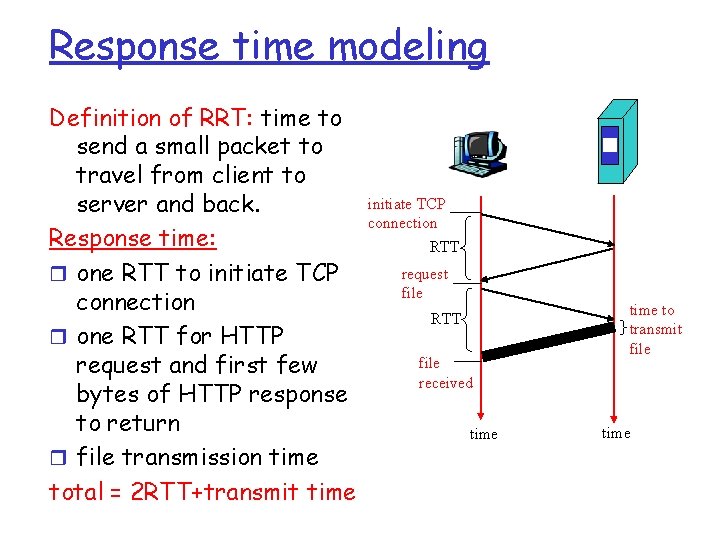
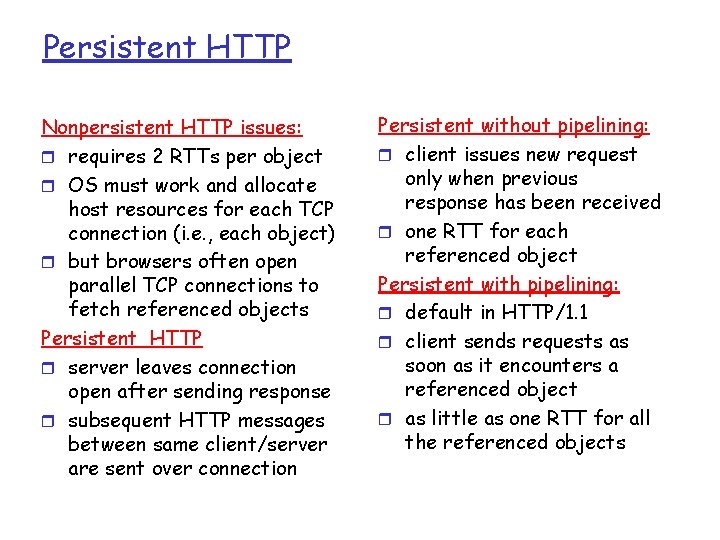
Response time modeling Definition of RRT: time to send a small packet to travel from client to server and back. Response time: r one RTT to initiate TCP connection r one RTT for HTTP request and first few bytes of HTTP response to return r file transmission time total = 2 RTT+transmit time initiate TCP connection RTT request file RTT file received time to transmit file time
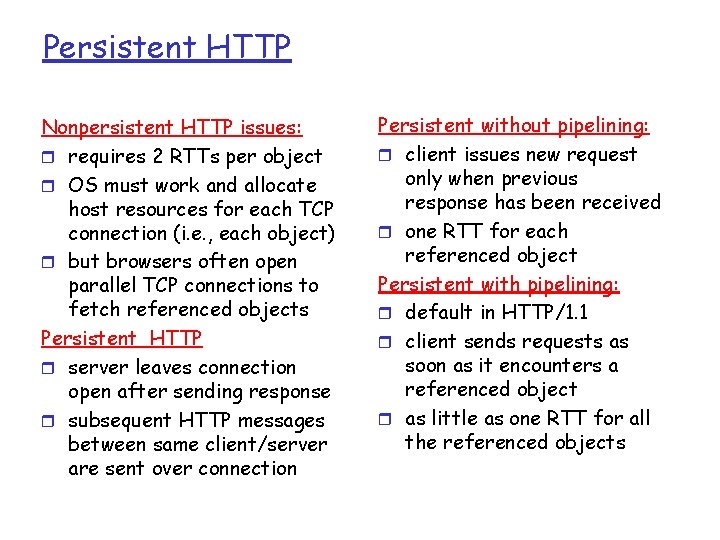
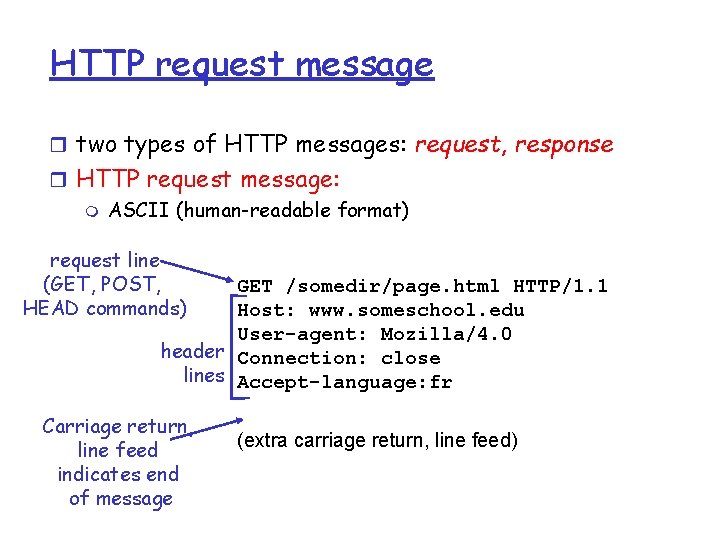
Persistent HTTP Nonpersistent HTTP issues: r requires 2 RTTs per object r OS must work and allocate host resources for each TCP connection (i. e. , each object) r but browsers often open parallel TCP connections to fetch referenced objects Persistent HTTP r server leaves connection open after sending response r subsequent HTTP messages between same client/server are sent over connection Persistent without pipelining: r client issues new request only when previous response has been received r one RTT for each referenced object Persistent with pipelining: r default in HTTP/1. 1 r client sends requests as soon as it encounters a referenced object r as little as one RTT for all the referenced objects
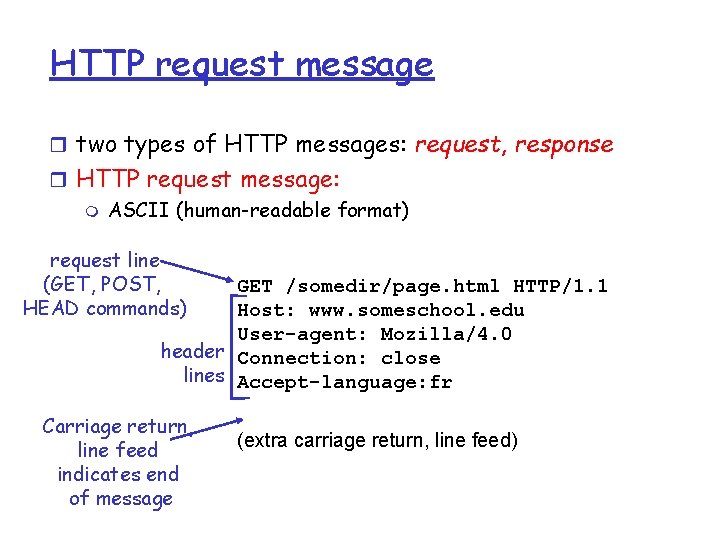
HTTP request message r two types of HTTP messages: request, response r HTTP request message: m ASCII (human-readable format) request line (GET, POST, HEAD commands) GET /somedir/page. html HTTP/1. 1 Host: www. someschool. edu User-agent: Mozilla/4. 0 header Connection: close lines Accept-language: fr Carriage return, line feed indicates end of message (extra carriage return, line feed)
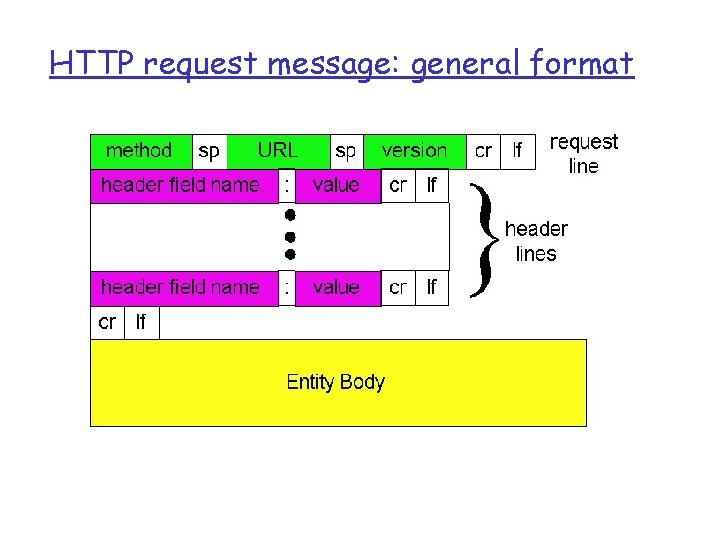
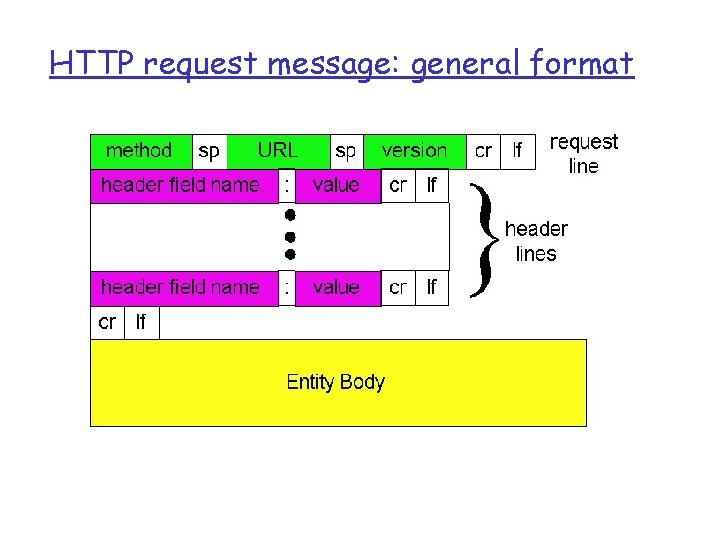
HTTP request message: general format
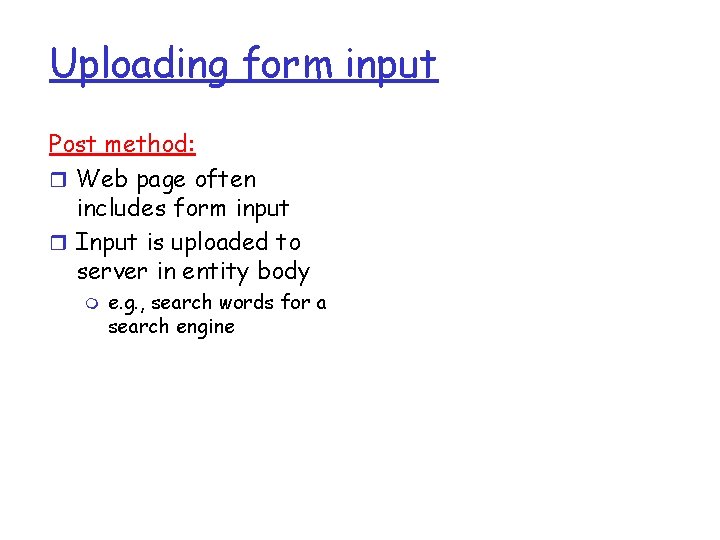
Uploading form input Post method: r Web page often includes form input r Input is uploaded to server in entity body m e. g. , search words for a search engine
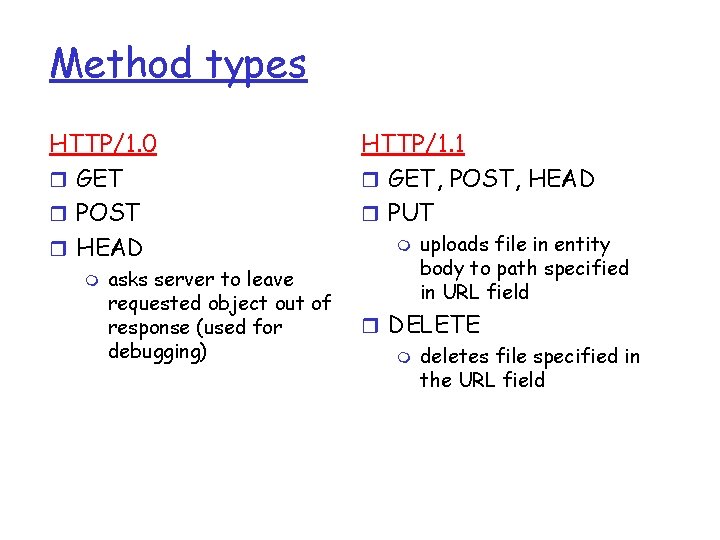
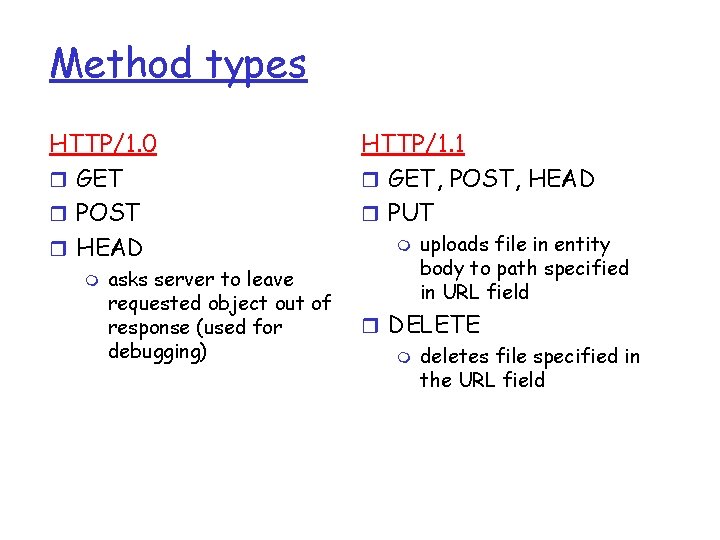
Method types HTTP/1. 0 r GET r POST r HEAD m asks server to leave requested object out of response (used for debugging) HTTP/1. 1 r GET, POST, HEAD r PUT m uploads file in entity body to path specified in URL field r DELETE m deletes file specified in the URL field
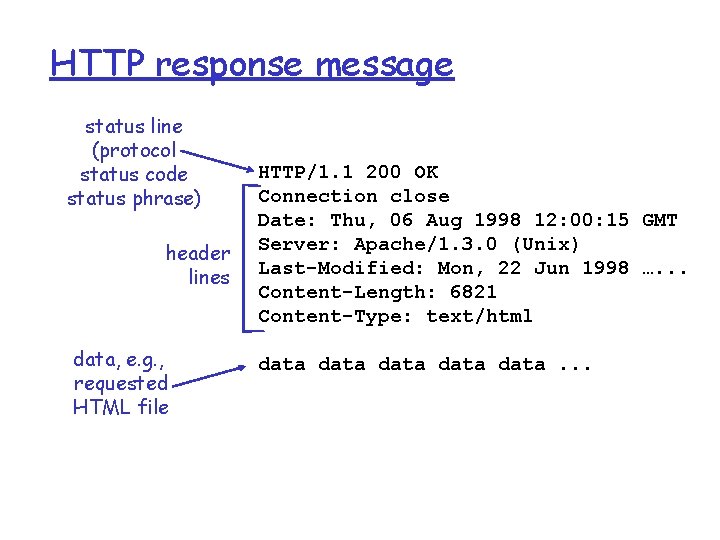
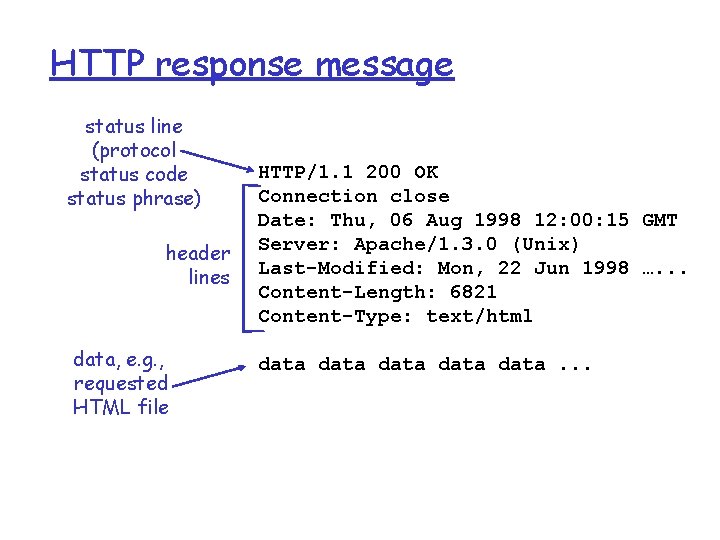
HTTP response message status line (protocol status code status phrase) header lines data, e. g. , requested HTML file HTTP/1. 1 200 OK Connection close Date: Thu, 06 Aug 1998 12: 00: 15 GMT Server: Apache/1. 3. 0 (Unix) Last-Modified: Mon, 22 Jun 1998 …. . . Content-Length: 6821 Content-Type: text/html data data. . .
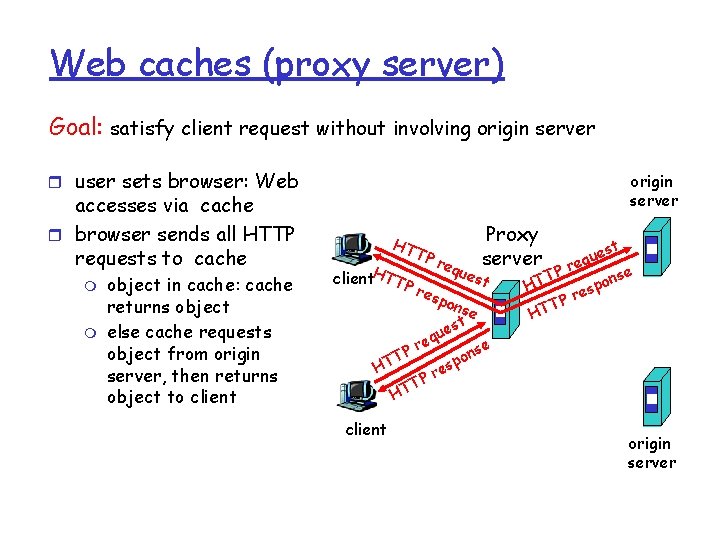
HTTP response status codes In first line in server->client response message. A few sample codes: 200 OK m request succeeded, requested object later in this message 301 Moved Permanently m requested object moved, new location specified later in this message (Location: ) 400 Bad Request m request message not understood by server 404 Not Found m requested document not found on this server 505 HTTP Version Not Supported
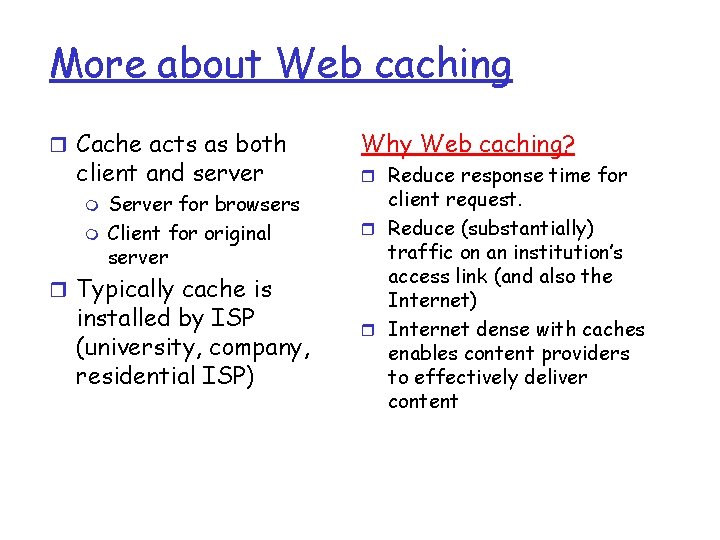
Web caches (proxy server) Goal: satisfy client request without involving origin server r user sets browser: Web accesses via cache r browser sends all HTTP requests to cache m m object in cache: cache returns object else cache requests object from origin server, then returns object to client origin server HT client. HTTP TP req Proxy server ues t res pon se t s ue q re P nse o T p HT es r TP T H client est u q e Pr T nse o p HT res P T HT origin server
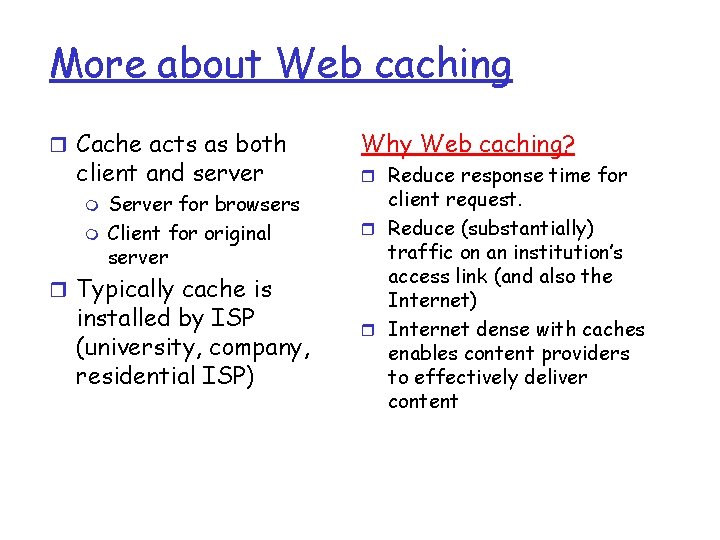
More about Web caching r Cache acts as both client and server m m Server for browsers Client for original server r Typically cache is installed by ISP (university, company, residential ISP) Why Web caching? r Reduce response time for client request. r Reduce (substantially) traffic on an institution’s access link (and also the Internet) r Internet dense with caches enables content providers to effectively deliver content
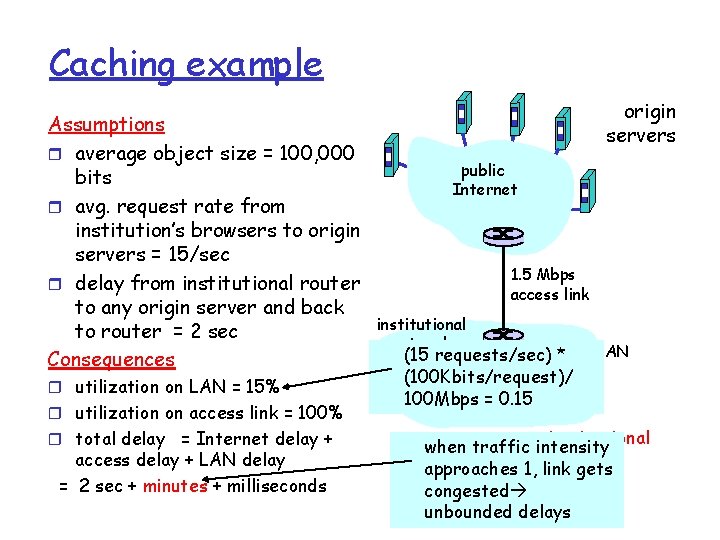
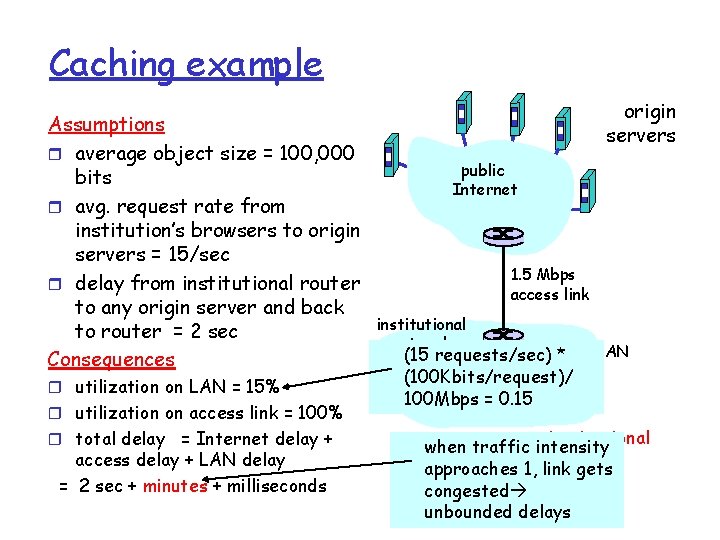
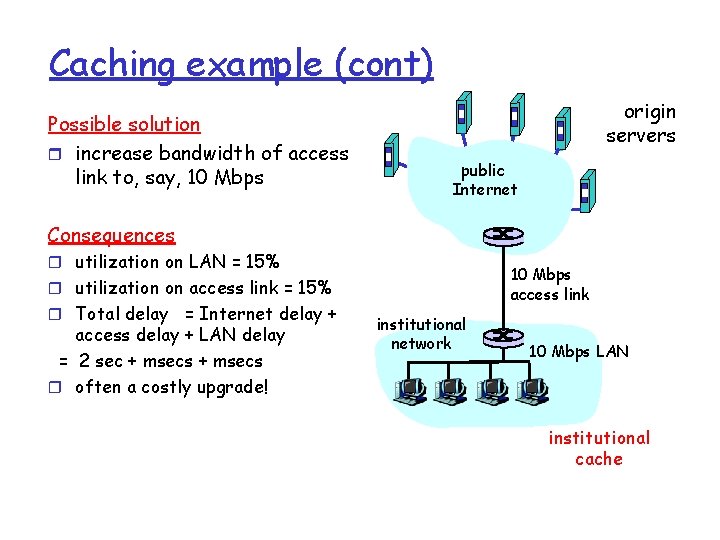
Caching example Assumptions r average object size = 100, 000 bits r avg. request rate from institution’s browsers to origin servers = 15/sec r delay from institutional router to any origin server and back to router = 2 sec Consequences r utilization on LAN = 15% r utilization on access link = 100% r total delay = Internet delay + access delay + LAN delay = 2 sec + minutes + milliseconds origin servers public Internet 1. 5 Mbps access link institutional network 10 Mbps LAN (15 requests/sec) * (100 Kbits/request)/ 100 Mbps = 0. 15 institutional when traffic intensity cache approaches 1, link gets congested unbounded delays
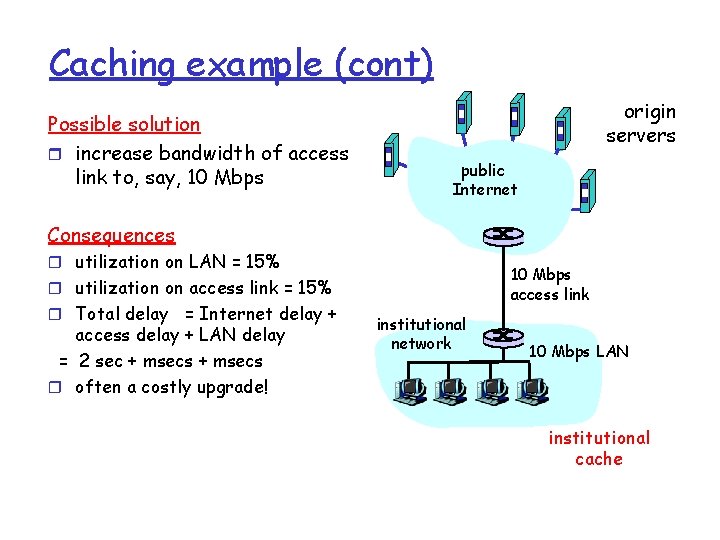
Caching example (cont) Possible solution r increase bandwidth of access link to, say, 10 Mbps origin servers public Internet Consequences r utilization on LAN = 15% 10 Mbps access link r utilization on access link = 15% r Total delay = Internet delay + access delay + LAN delay = 2 sec + msecs r often a costly upgrade! institutional network 10 Mbps LAN institutional cache
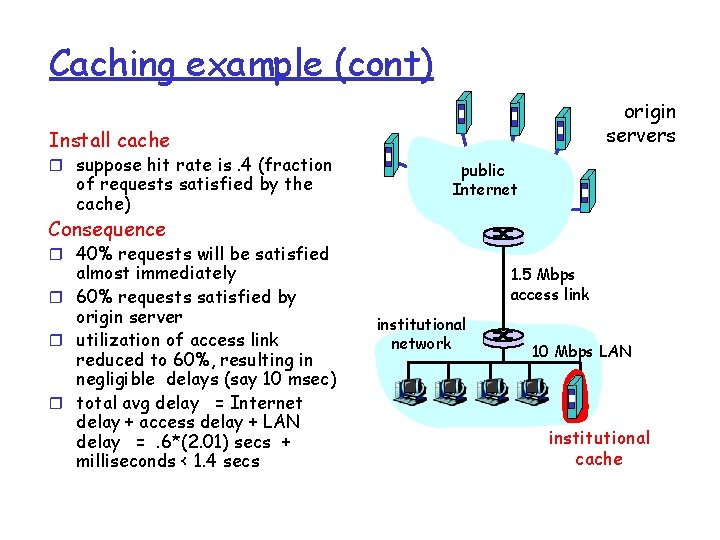
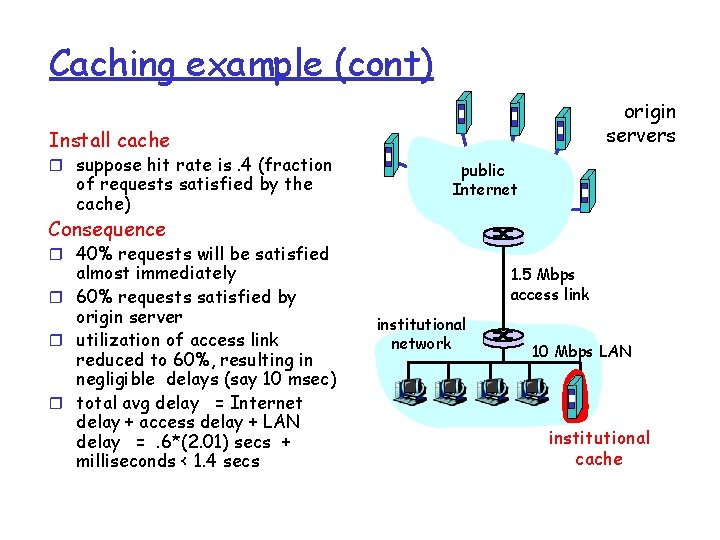
Caching example (cont) origin servers Install cache r suppose hit rate is. 4 (fraction of requests satisfied by the cache) public Internet Consequence r 40% requests will be satisfied almost immediately r 60% requests satisfied by origin server r utilization of access link reduced to 60%, resulting in negligible delays (say 10 msec) r total avg delay = Internet delay + access delay + LAN delay =. 6*(2. 01) secs + milliseconds < 1. 4 secs 1. 5 Mbps access link institutional network 10 Mbps LAN institutional cache
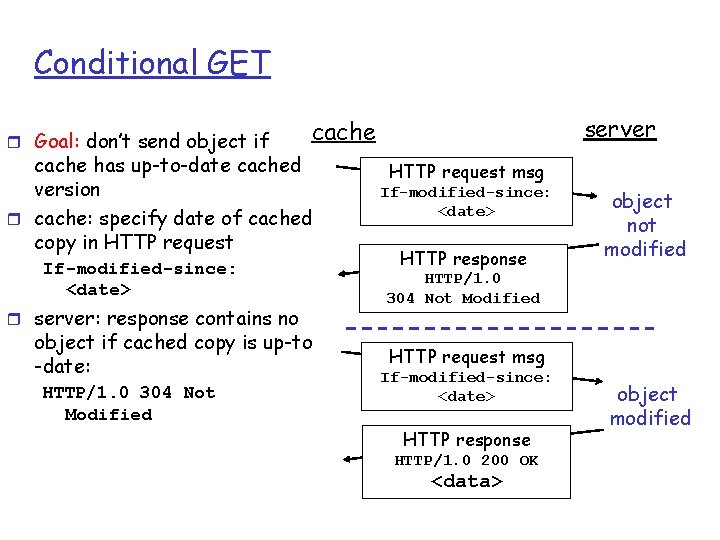
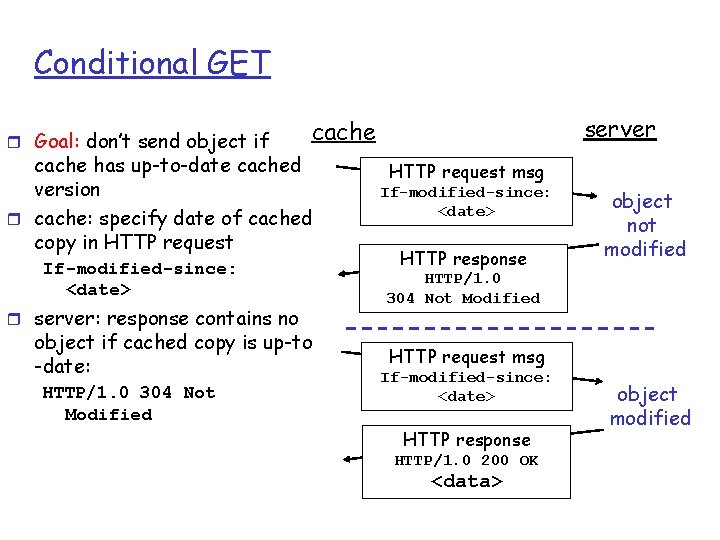
Conditional GET r Goal: don’t send object if cache has up-to-date cached version r cache: specify date of cached copy in HTTP request If-modified-since: <date> r server: response contains no object if cached copy is up-to -date: HTTP/1. 0 304 Not Modified server cache HTTP request msg If-modified-since: <date> HTTP response object not modified HTTP/1. 0 304 Not Modified HTTP request msg If-modified-since: <date> HTTP response HTTP/1. 0 200 OK <data> object modified
Application layer r Principles of network applications r Web and HTTP r Electronic Mail m SMTP, POP 3, IMAP r Socket programming with TCP r Socket programming with UDP
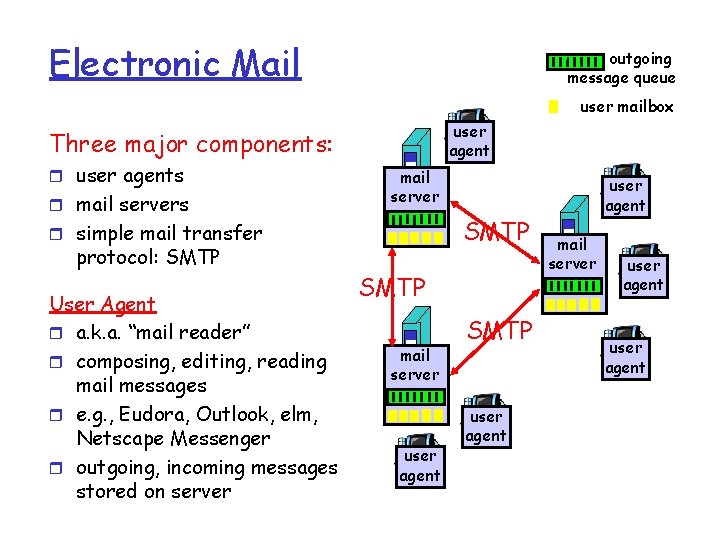
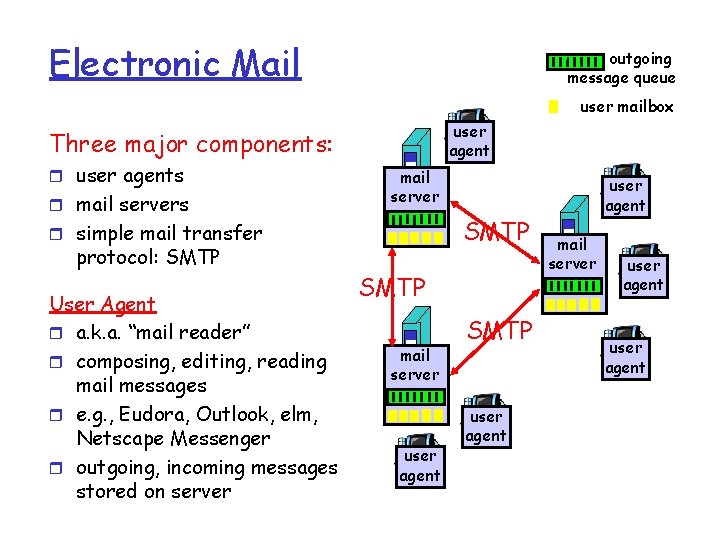
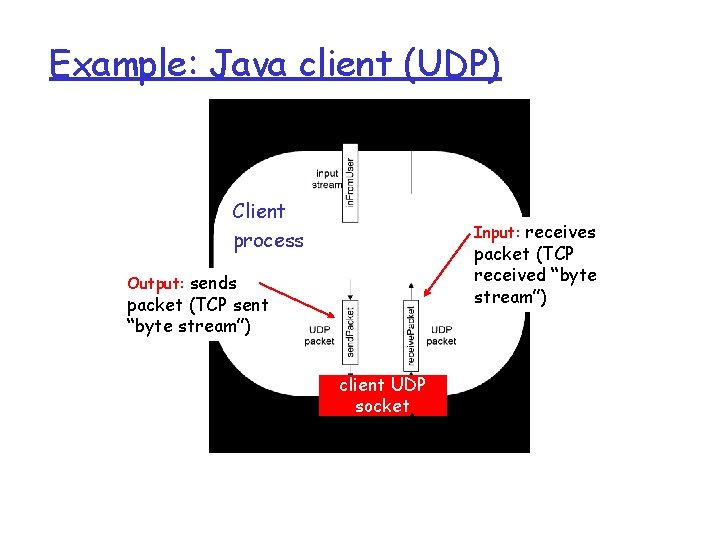
Electronic Mail outgoing message queue user mailbox user agent Three major components: r user agents r mail servers mail server SMTP r simple mail transfer protocol: SMTP User Agent r a. k. a. “mail reader” r composing, editing, reading mail messages r e. g. , Eudora, Outlook, elm, Netscape Messenger r outgoing, incoming messages stored on server SMTP mail server user agent SMTP user agent mail server user agent
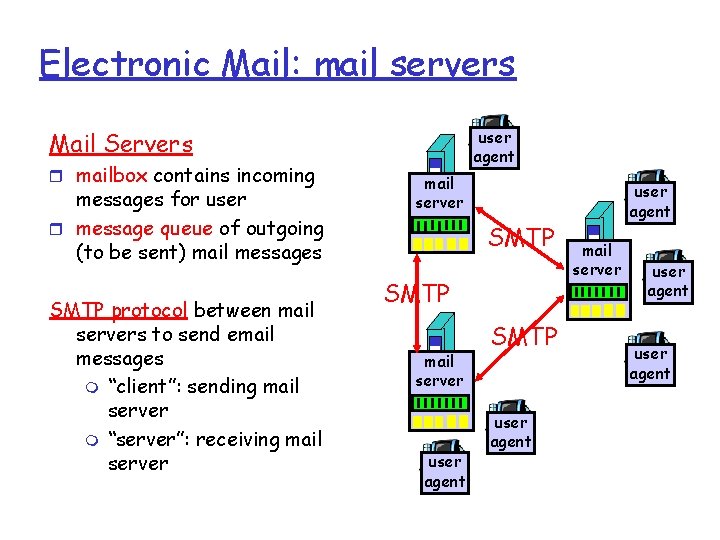
Electronic Mail: mail servers user agent Mail Servers r mailbox contains incoming messages for user r message queue of outgoing (to be sent) mail messages SMTP protocol between mail servers to send email messages m “client”: sending mail server m “server”: receiving mail server SMTP mail server user agent SMTP user agent mail server user agent
![Electronic Mail SMTP RFC 2821 r uses TCP to reliably transfer email message from Electronic Mail: SMTP [RFC 2821] r uses TCP to reliably transfer email message from](https://slidetodoc.com/presentation_image_h2/247b2a95e1a2821124c4fb9c321e7d0d/image-43.jpg)
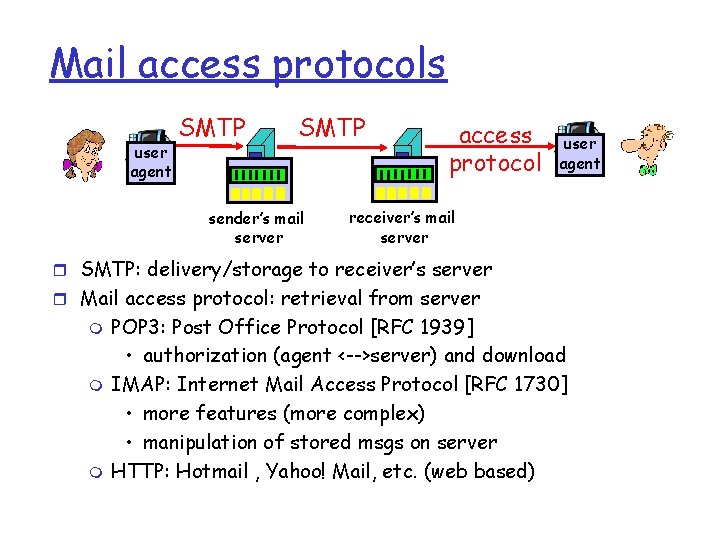
Electronic Mail: SMTP [RFC 2821] r uses TCP to reliably transfer email message from client to server, port 25 r direct transfer: sending server to receiving server m Does not send message to intermediate mail-server r three phases of transfer handshaking (greeting) between servers m transfer of messages m closure r command/response interaction m commands: ASCII text m response: status code and phrase m r messages must be in 7 -bit ASCII (i. e. , limited to text)
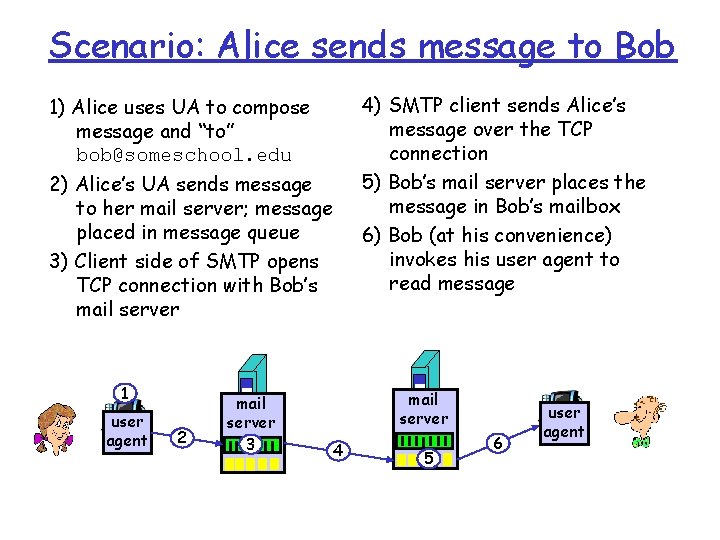
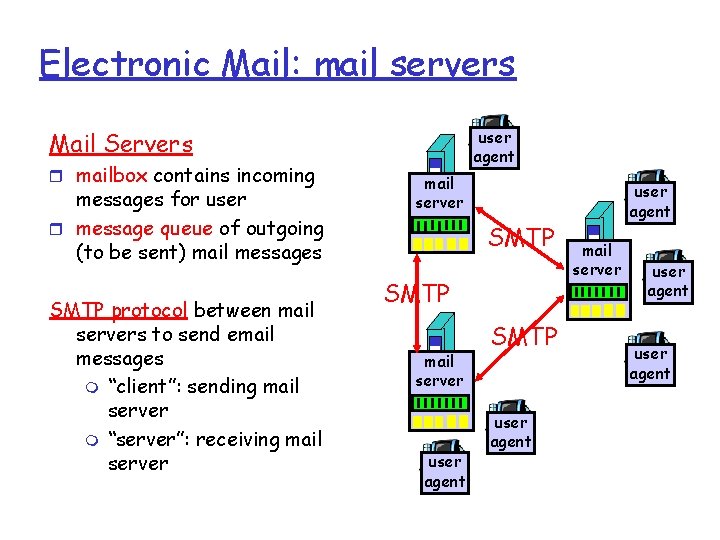
Scenario: Alice sends message to Bob 4) SMTP client sends Alice’s message over the TCP connection 5) Bob’s mail server places the message in Bob’s mailbox 6) Bob (at his convenience) invokes his user agent to read message 1) Alice uses UA to compose message and “to” bob@someschool. edu 2) Alice’s UA sends message to her mail server; message placed in message queue 3) Client side of SMTP opens TCP connection with Bob’s mail server 1 user agent 2 mail server 3 mail server 4 5 6 user agent
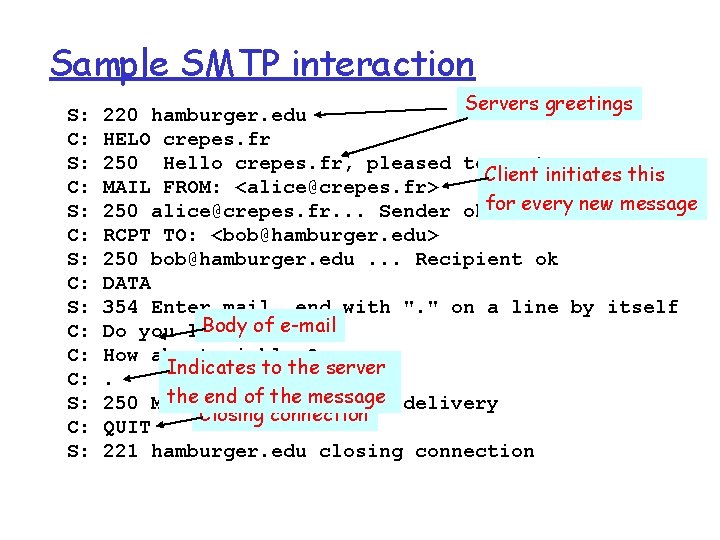
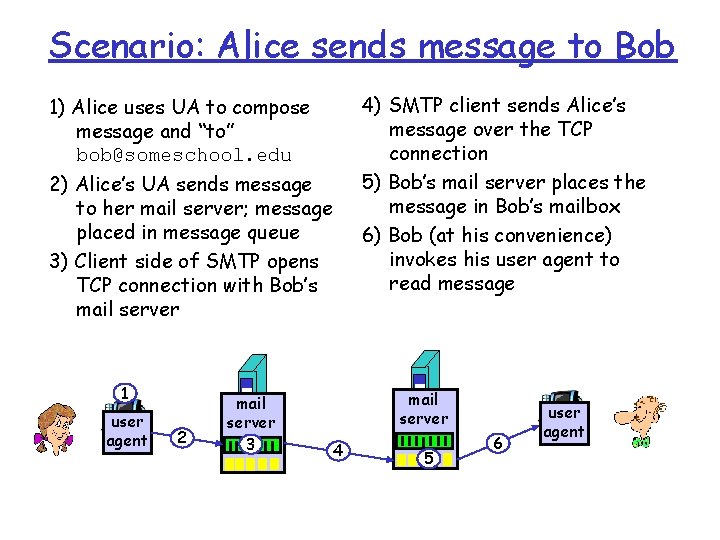
Sample SMTP interaction S: C: S: C: C: C: S: Servers greetings 220 hamburger. edu HELO crepes. fr 250 Hello crepes. fr, pleased to meet you Client initiates this MAIL FROM: <alice@crepes. fr> 250 alice@crepes. fr. . . Sender okfor every new message RCPT TO: <bob@hamburger. edu> 250 bob@hamburger. edu. . . Recipient ok DATA 354 Enter mail, end with ". " on a line by itself Bodyketchup? of e-mail Do you like How about pickles? Indicates to the server. the end of the message 250 Message accepted for delivery Closing connection QUIT 221 hamburger. edu closing connection
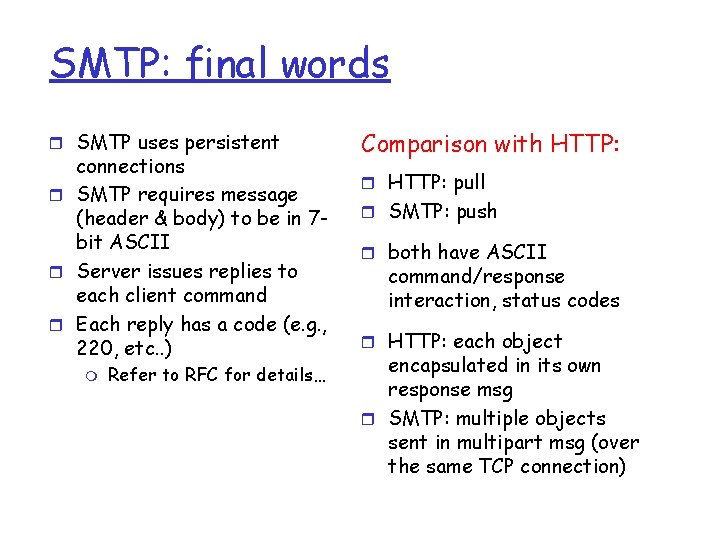
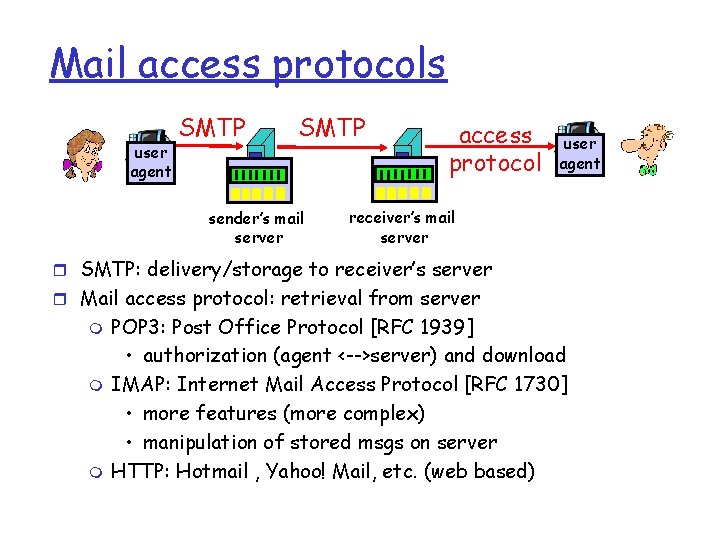
SMTP: final words r SMTP uses persistent connections r SMTP requires message (header & body) to be in 7 bit ASCII r Server issues replies to each client command r Each reply has a code (e. g. , 220, etc. . ) m Refer to RFC for details… Comparison with HTTP: r HTTP: pull r SMTP: push r both have ASCII command/response interaction, status codes r HTTP: each object encapsulated in its own response msg r SMTP: multiple objects sent in multipart msg (over the same TCP connection)
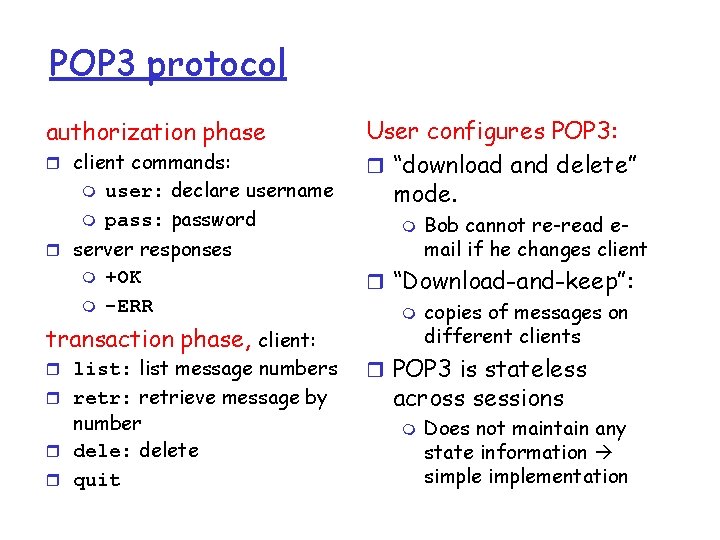
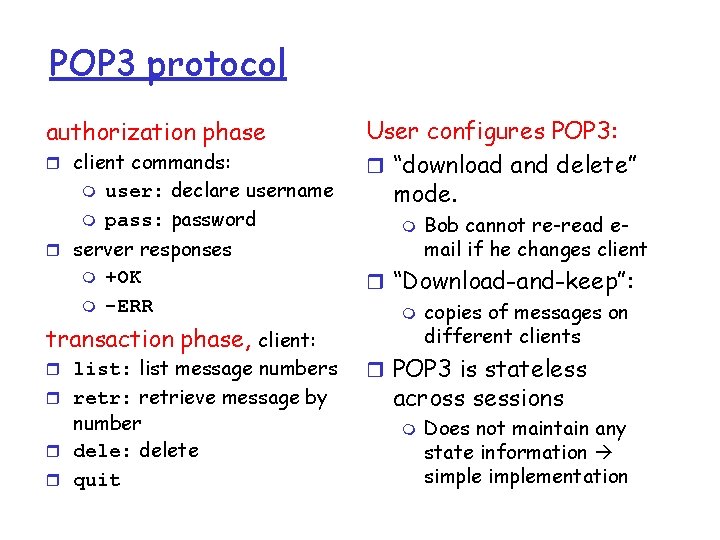
Mail access protocols user agent SMTP sender’s mail server access protocol user agent receiver’s mail server r SMTP: delivery/storage to receiver’s server r Mail access protocol: retrieval from server m m m POP 3: Post Office Protocol [RFC 1939] • authorization (agent <-->server) and download IMAP: Internet Mail Access Protocol [RFC 1730] • more features (more complex) • manipulation of stored msgs on server HTTP: Hotmail , Yahoo! Mail, etc. (web based)
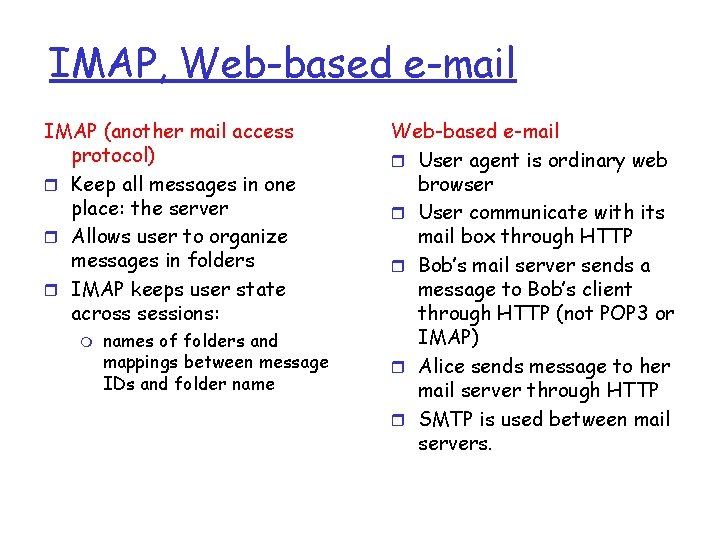
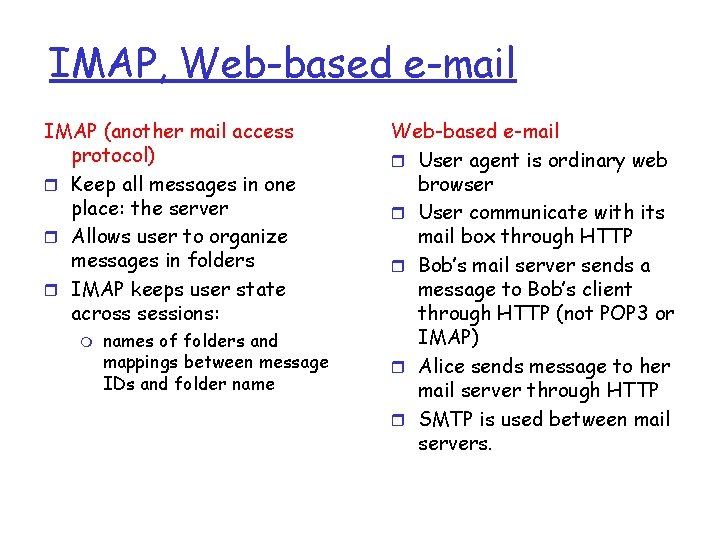
POP 3 protocol authorization phase r client commands: m m user: declare username pass: password r server responses m m +OK -ERR transaction phase, client: r list: list message numbers r retr: retrieve message by number r dele: delete r quit User configures POP 3: r “download and delete” mode. m Bob cannot re-read email if he changes client r “Download-and-keep”: m copies of messages on different clients r POP 3 is stateless across sessions m Does not maintain any state information simplementation
IMAP, Web-based e-mail IMAP (another mail access protocol) r Keep all messages in one place: the server r Allows user to organize messages in folders r IMAP keeps user state across sessions: m names of folders and mappings between message IDs and folder name Web-based e-mail r User agent is ordinary web browser r User communicate with its mail box through HTTP r Bob’s mail server sends a message to Bob’s client through HTTP (not POP 3 or IMAP) r Alice sends message to her mail server through HTTP r SMTP is used between mail servers.
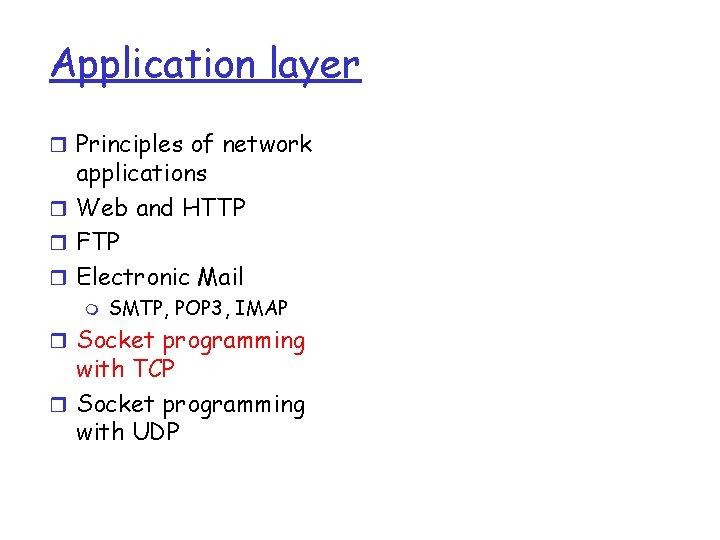
Application layer r Principles of network applications r Web and HTTP r FTP r Electronic Mail m SMTP, POP 3, IMAP r Socket programming with TCP r Socket programming with UDP
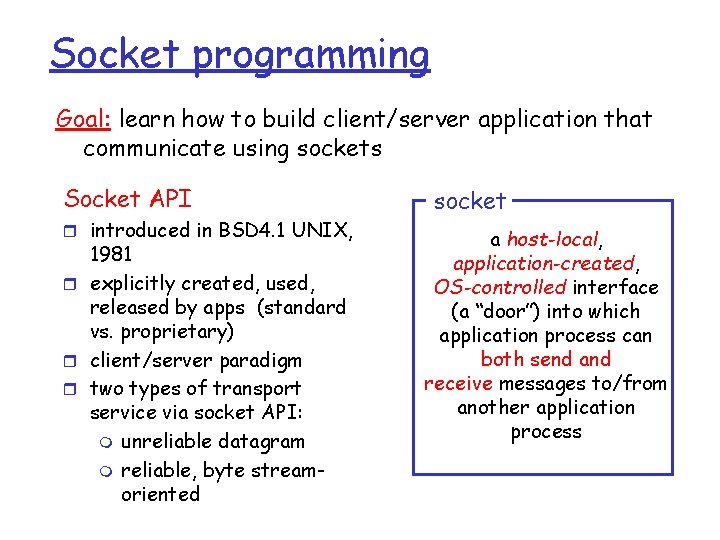
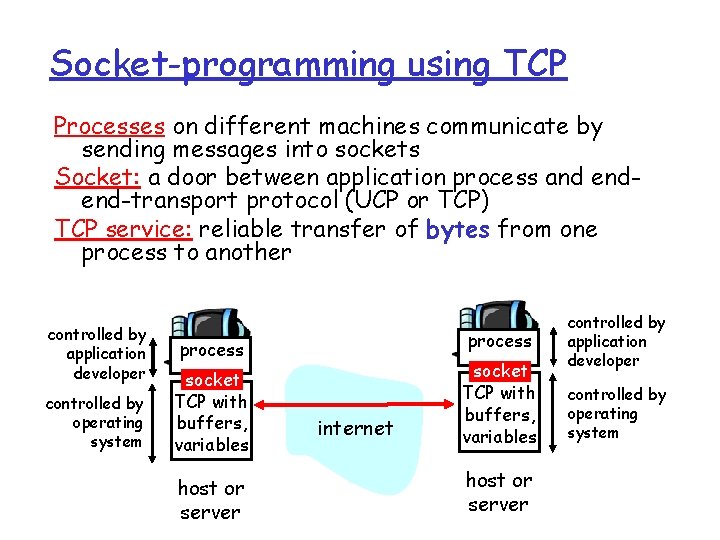
Socket programming Goal: learn how to build client/server application that communicate using sockets Socket API r introduced in BSD 4. 1 UNIX, 1981 r explicitly created, used, released by apps (standard vs. proprietary) r client/server paradigm r two types of transport service via socket API: m unreliable datagram m reliable, byte streamoriented socket a host-local, application-created, OS-controlled interface (a “door”) into which application process can both send and receive messages to/from another application process
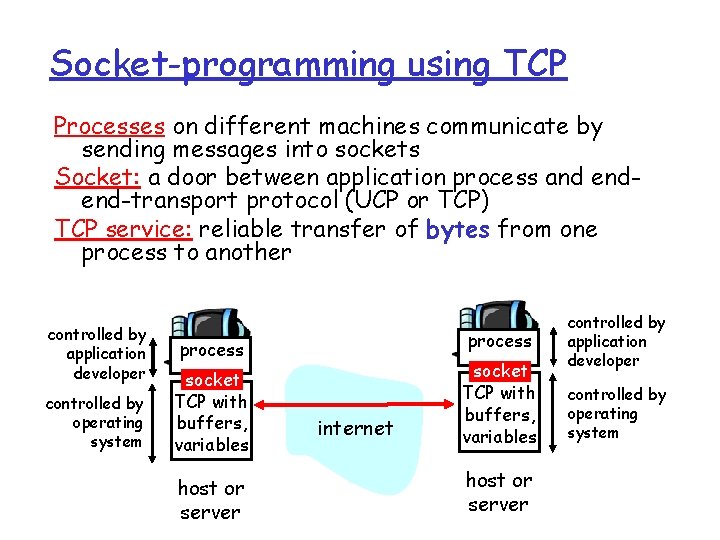
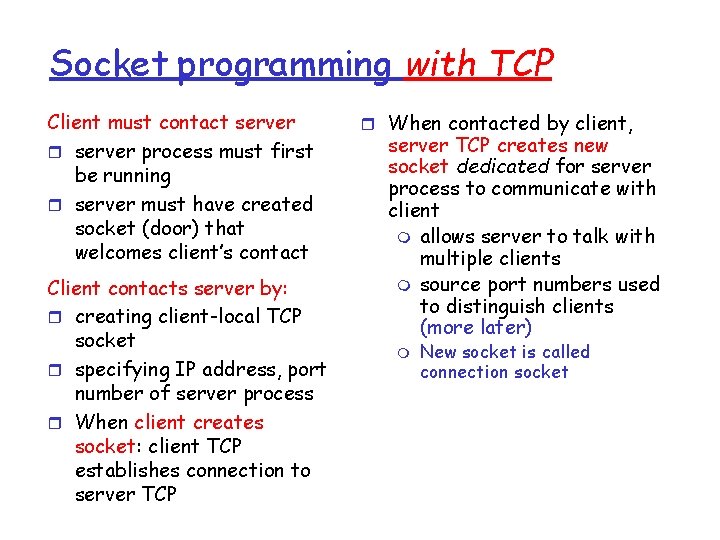
Socket-programming using TCP Processes on different machines communicate by sending messages into sockets Socket: a door between application process and endend-transport protocol (UCP or TCP) TCP service: reliable transfer of bytes from one process to another controlled by application developer controlled by operating system process socket TCP with buffers, variables host or server internet socket TCP with buffers, variables host or server controlled by application developer controlled by operating system
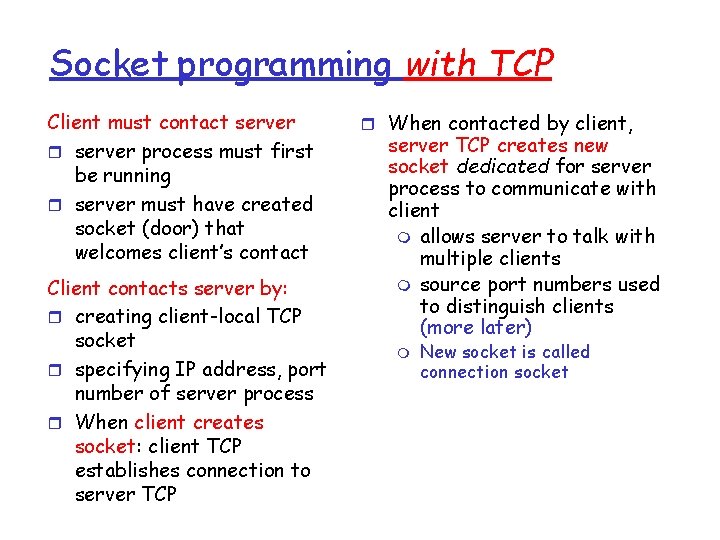
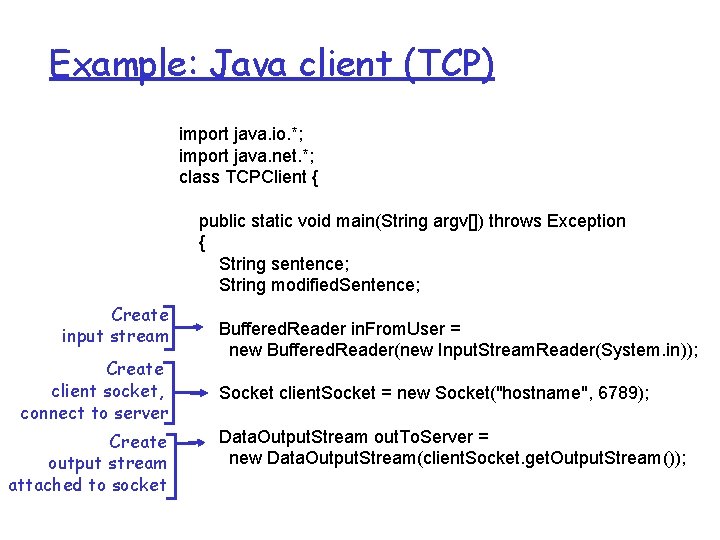
Socket programming with TCP Client must contact server r server process must first be running r server must have created socket (door) that welcomes client’s contact Client contacts server by: r creating client-local TCP socket r specifying IP address, port number of server process r When client creates socket: client TCP establishes connection to server TCP r When contacted by client, server TCP creates new socket dedicated for server process to communicate with client m allows server to talk with multiple clients m source port numbers used to distinguish clients (more later) m New socket is called connection socket
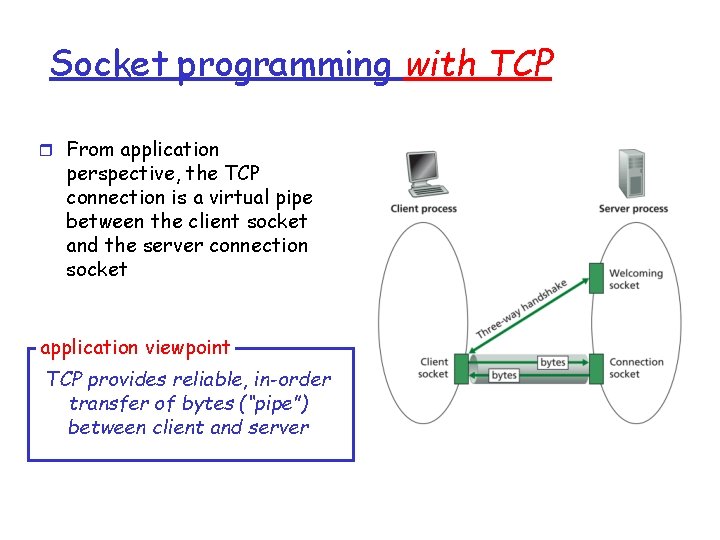
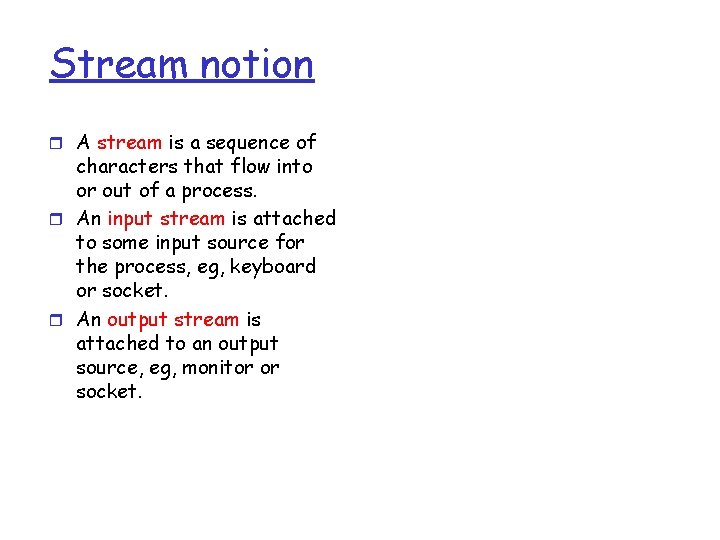
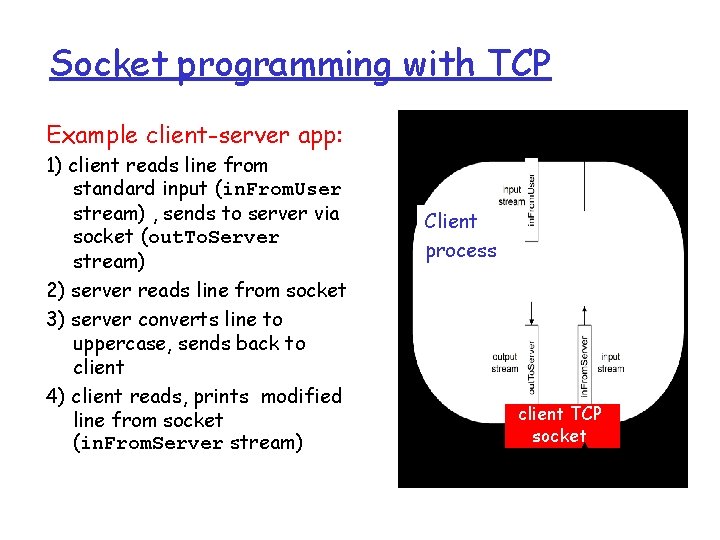
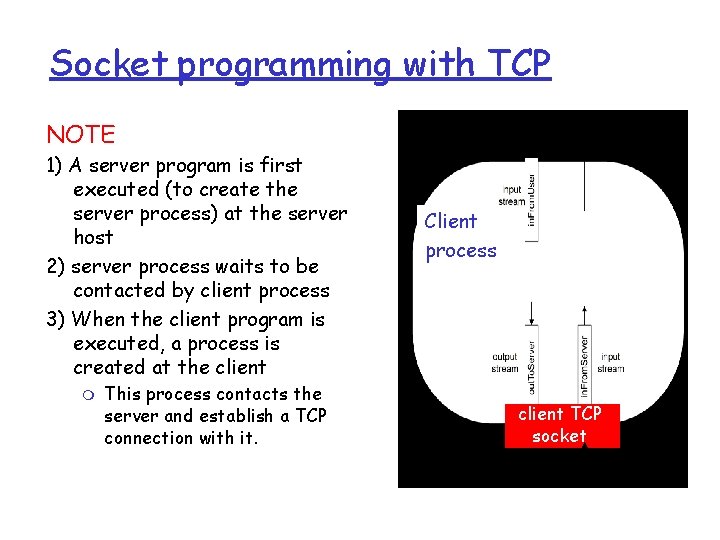
Socket programming with TCP r From application perspective, the TCP connection is a virtual pipe between the client socket and the server connection socket application viewpoint TCP provides reliable, in-order transfer of bytes (“pipe”) between client and server
Stream notion r A stream is a sequence of characters that flow into or out of a process. r An input stream is attached to some input source for the process, eg, keyboard or socket. r An output stream is attached to an output source, eg, monitor or socket.
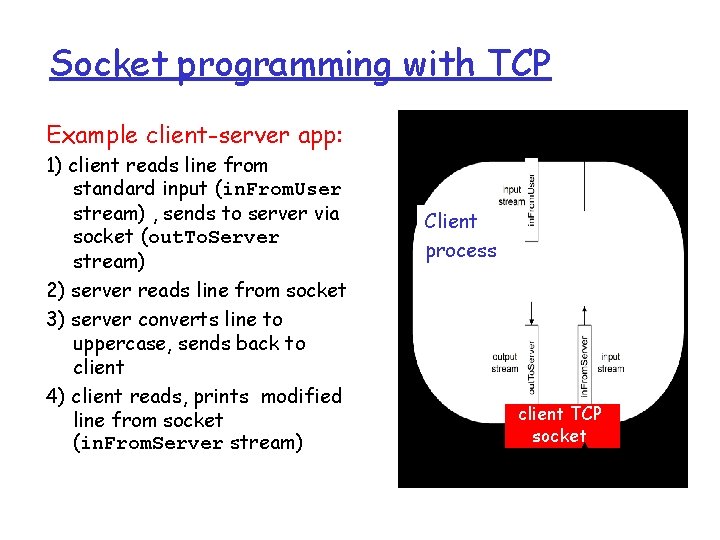
Socket programming with TCP Example client-server app: 1) client reads line from standard input (in. From. User stream) , sends to server via socket (out. To. Server stream) 2) server reads line from socket 3) server converts line to uppercase, sends back to client 4) client reads, prints modified line from socket (in. From. Server stream) Client process client TCP socket
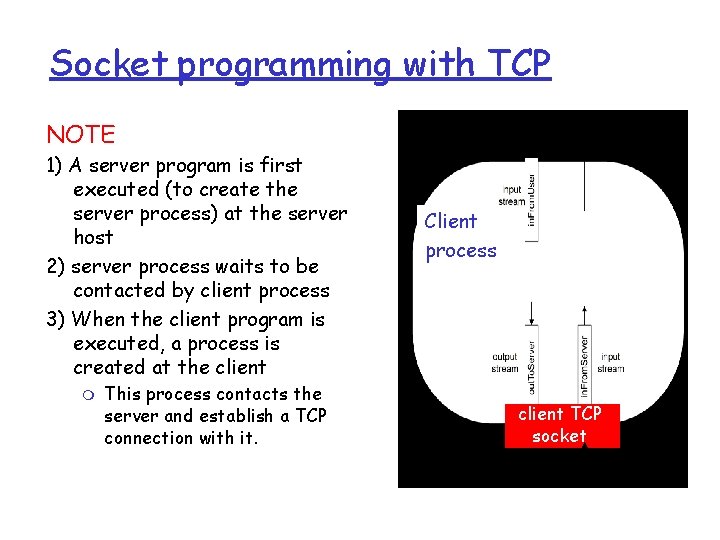
Socket programming with TCP NOTE 1) A server program is first executed (to create the server process) at the server host 2) server process waits to be contacted by client process 3) When the client program is executed, a process is created at the client m This process contacts the server and establish a TCP connection with it. Client process client TCP socket
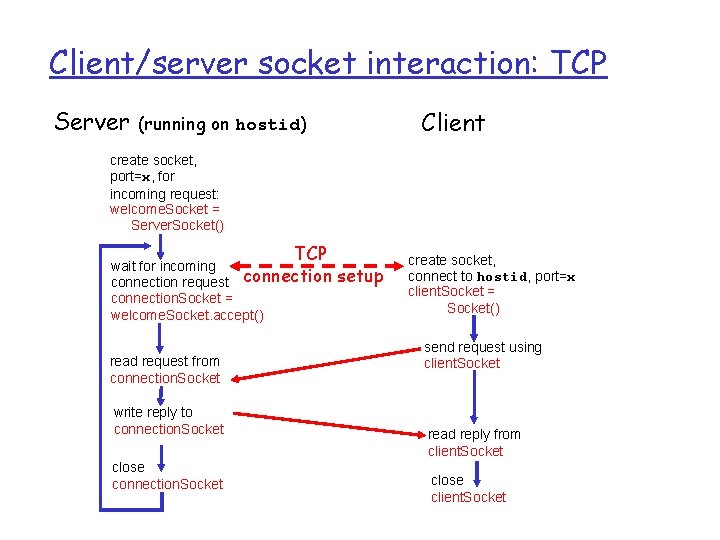
Client/server socket interaction: TCP Server Client (running on hostid) create socket, port=x, for incoming request: welcome. Socket = Server. Socket() TCP wait for incoming connection request connection. Socket = welcome. Socket. accept() read request from connection. Socket write reply to connection. Socket close connection. Socket setup create socket, connect to hostid, port=x client. Socket = Socket() send request using client. Socket read reply from client. Socket close client. Socket
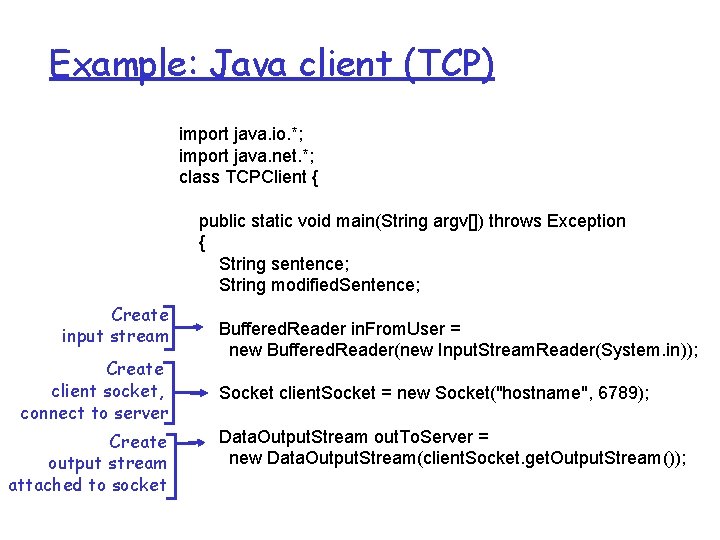
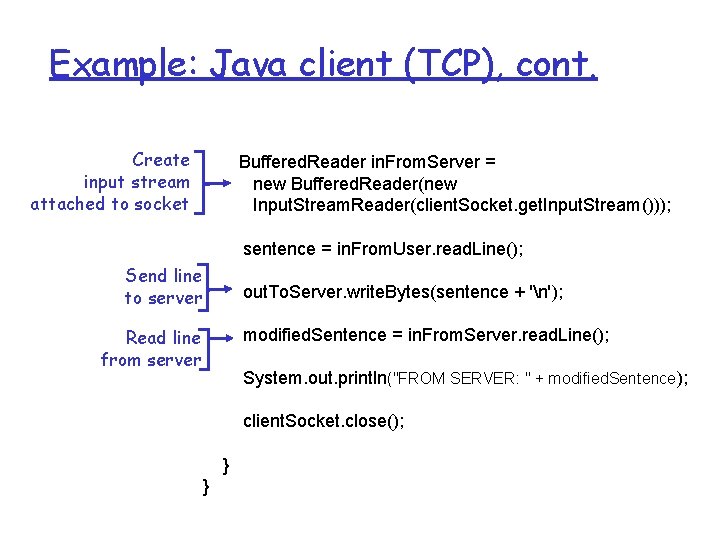
Example: Java client (TCP) import java. io. *; import java. net. *; class TCPClient { public static void main(String argv[]) throws Exception { String sentence; String modified. Sentence; Create input stream Create client socket, connect to server Create output stream attached to socket Buffered. Reader in. From. User = new Buffered. Reader(new Input. Stream. Reader(System. in)); Socket client. Socket = new Socket("hostname", 6789); Data. Output. Stream out. To. Server = new Data. Output. Stream(client. Socket. get. Output. Stream());
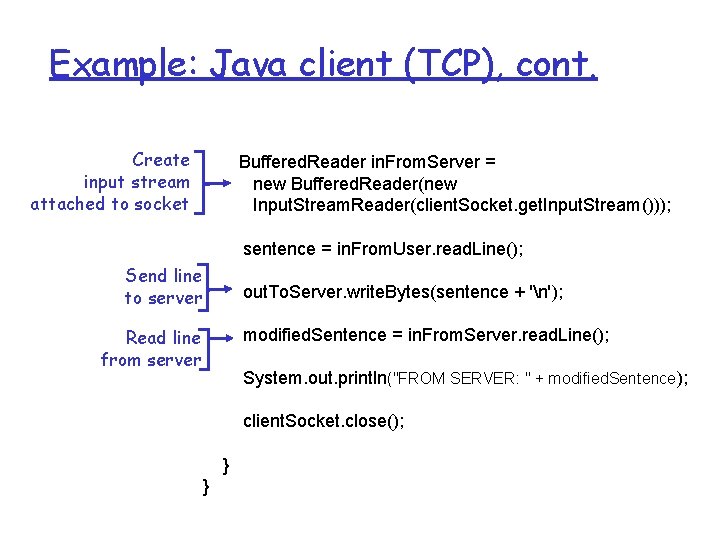
Example: Java client (TCP), cont. Create input stream attached to socket Buffered. Reader in. From. Server = new Buffered. Reader(new Input. Stream. Reader(client. Socket. get. Input. Stream())); sentence = in. From. User. read. Line(); Send line to server out. To. Server. write. Bytes(sentence + 'n'); Read line from server modified. Sentence = in. From. Server. read. Line(); System. out. println("FROM SERVER: " + modified. Sentence); client. Socket. close(); } }
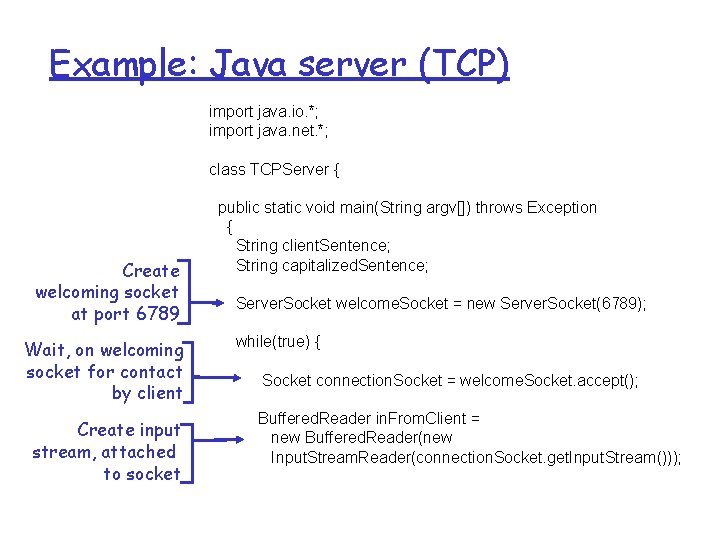
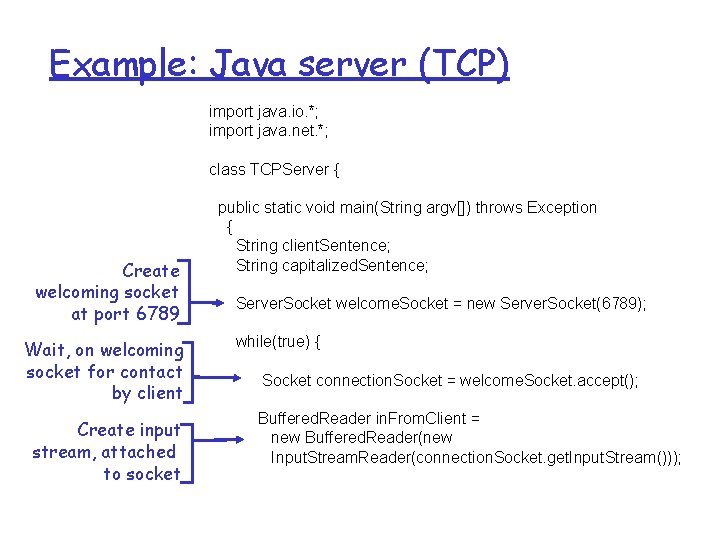
Example: Java server (TCP) import java. io. *; import java. net. *; class TCPServer { Create welcoming socket at port 6789 Wait, on welcoming socket for contact by client Create input stream, attached to socket public static void main(String argv[]) throws Exception { String client. Sentence; String capitalized. Sentence; Server. Socket welcome. Socket = new Server. Socket(6789); while(true) { Socket connection. Socket = welcome. Socket. accept(); Buffered. Reader in. From. Client = new Buffered. Reader(new Input. Stream. Reader(connection. Socket. get. Input. Stream()));
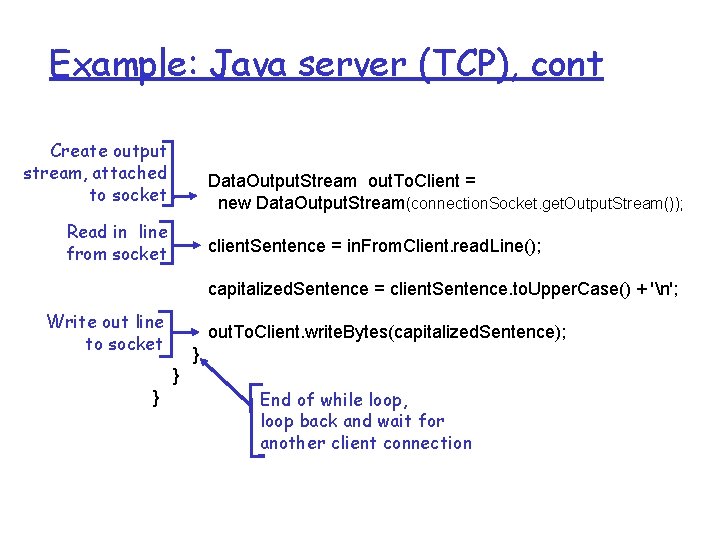
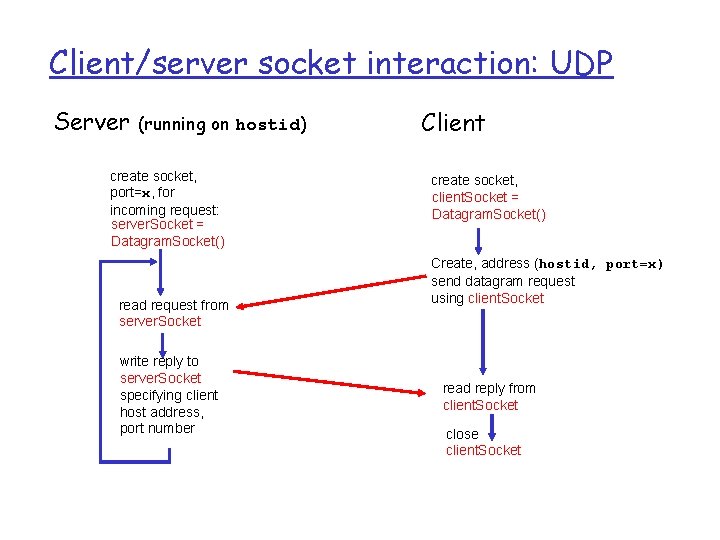
Example: Java server (TCP), cont Create output stream, attached to socket Data. Output. Stream out. To. Client = new Data. Output. Stream(connection. Socket. get. Output. Stream()); Read in line from socket client. Sentence = in. From. Client. read. Line(); capitalized. Sentence = client. Sentence. to. Upper. Case() + 'n'; Write out line to socket out. To. Client. write. Bytes(capitalized. Sentence); } } } End of while loop, loop back and wait for another client connection
Application layer r Principles of network applications r Web and HTTP r FTP r Electronic Mail m SMTP, POP 3, IMAP r Socket programming with TCP r Socket programming with UDP
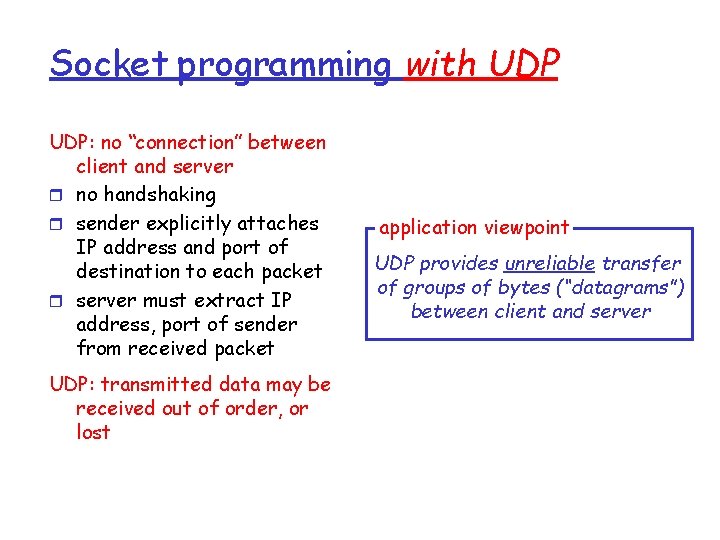
Socket programming with UDP: no “connection” between client and server r no handshaking r sender explicitly attaches IP address and port of destination to each packet r server must extract IP address, port of sender from received packet UDP: transmitted data may be received out of order, or lost application viewpoint UDP provides unreliable transfer of groups of bytes (“datagrams”) between client and server
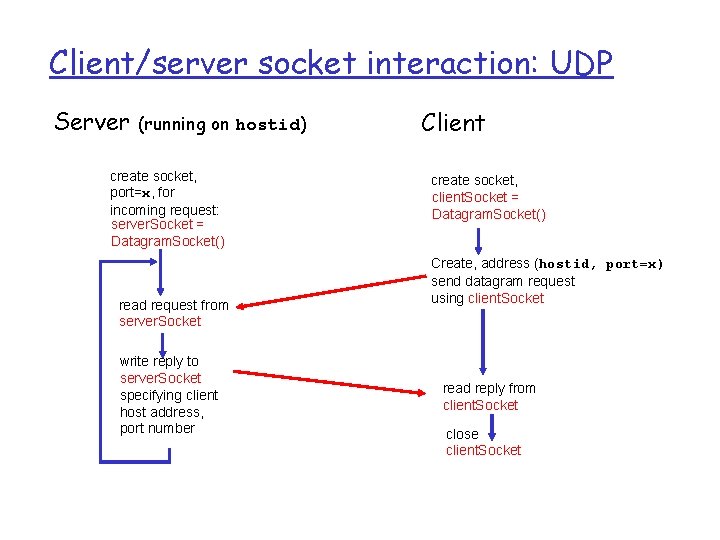
Client/server socket interaction: UDP Server (running on hostid) create socket, port=x, for incoming request: server. Socket = Datagram. Socket() read request from server. Socket write reply to server. Socket specifying client host address, port number Client create socket, client. Socket = Datagram. Socket() Create, address (hostid, port=x) send datagram request using client. Socket read reply from client. Socket close client. Socket
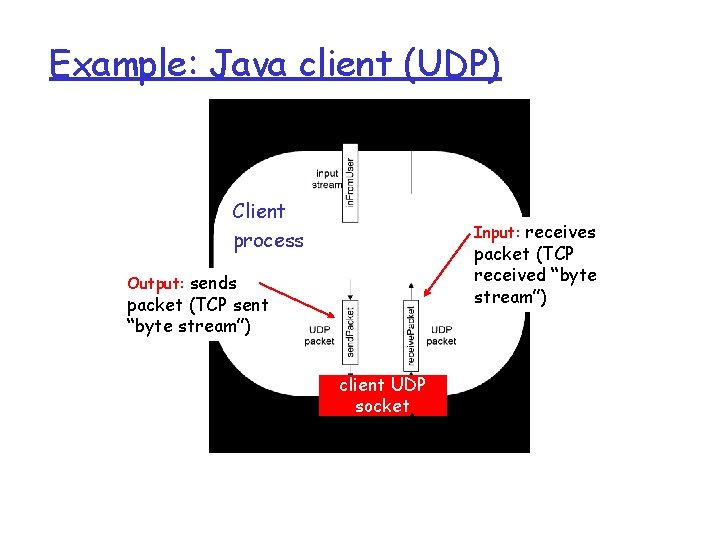
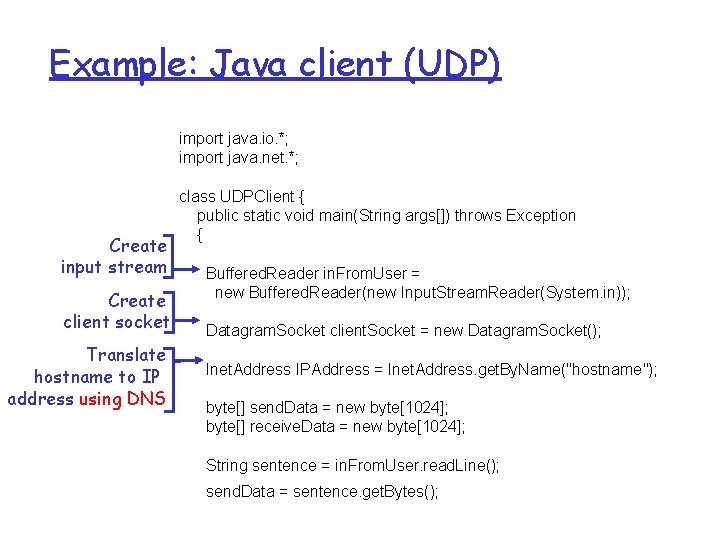
Example: Java client (UDP) Client process Input: receives packet (TCP received “byte stream”) Output: sends packet (TCP sent “byte stream”) client UDP socket
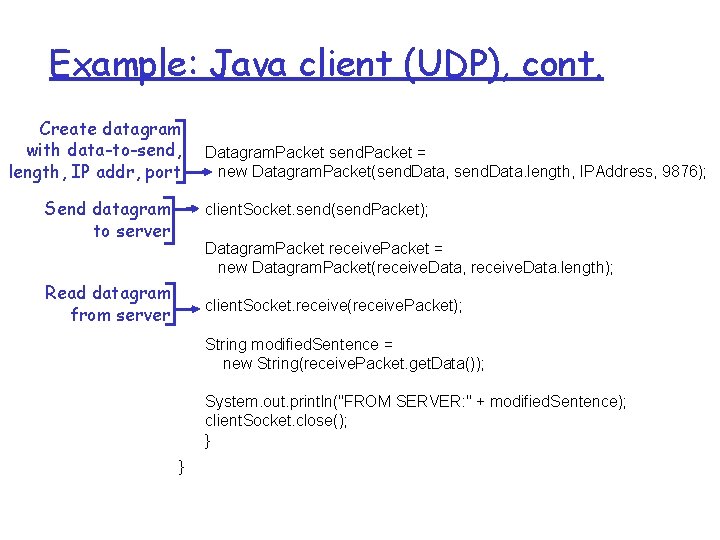
Example: Java client (UDP) import java. io. *; import java. net. *; Create input stream Create client socket Translate hostname to IP address using DNS class UDPClient { public static void main(String args[]) throws Exception { Buffered. Reader in. From. User = new Buffered. Reader(new Input. Stream. Reader(System. in)); Datagram. Socket client. Socket = new Datagram. Socket(); Inet. Address IPAddress = Inet. Address. get. By. Name("hostname"); byte[] send. Data = new byte[1024]; byte[] receive. Data = new byte[1024]; String sentence = in. From. User. read. Line(); send. Data = sentence. get. Bytes();
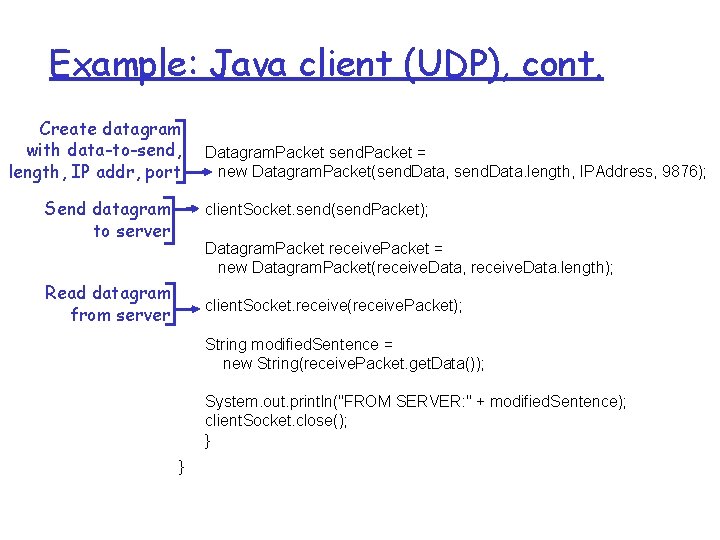
Example: Java client (UDP), cont. Create datagram with data-to-send, length, IP addr, port Send datagram to server Datagram. Packet send. Packet = new Datagram. Packet(send. Data, send. Data. length, IPAddress, 9876); client. Socket. send(send. Packet); Datagram. Packet receive. Packet = new Datagram. Packet(receive. Data, receive. Data. length); Read datagram from server client. Socket. receive(receive. Packet); String modified. Sentence = new String(receive. Packet. get. Data()); System. out. println("FROM SERVER: " + modified. Sentence); client. Socket. close(); } }
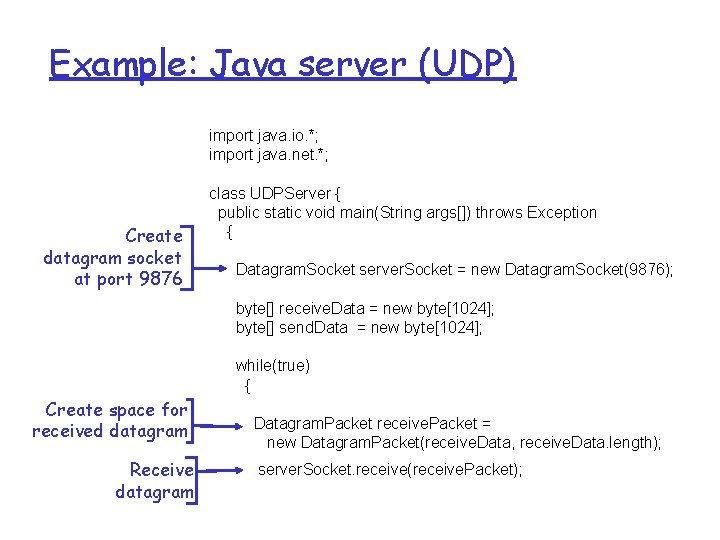
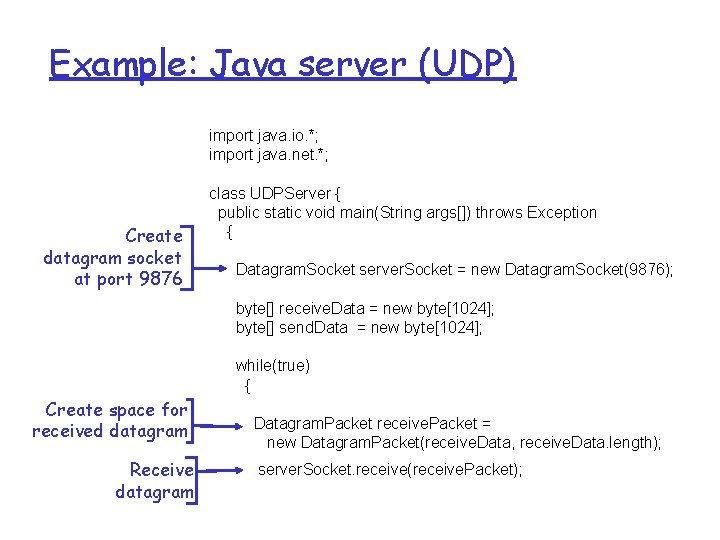
Example: Java server (UDP) import java. io. *; import java. net. *; Create datagram socket at port 9876 class UDPServer { public static void main(String args[]) throws Exception { Datagram. Socket server. Socket = new Datagram. Socket(9876); byte[] receive. Data = new byte[1024]; byte[] send. Data = new byte[1024]; while(true) { Create space for received datagram Receive datagram Datagram. Packet receive. Packet = new Datagram. Packet(receive. Data, receive. Data. length); server. Socket. receive(receive. Packet);
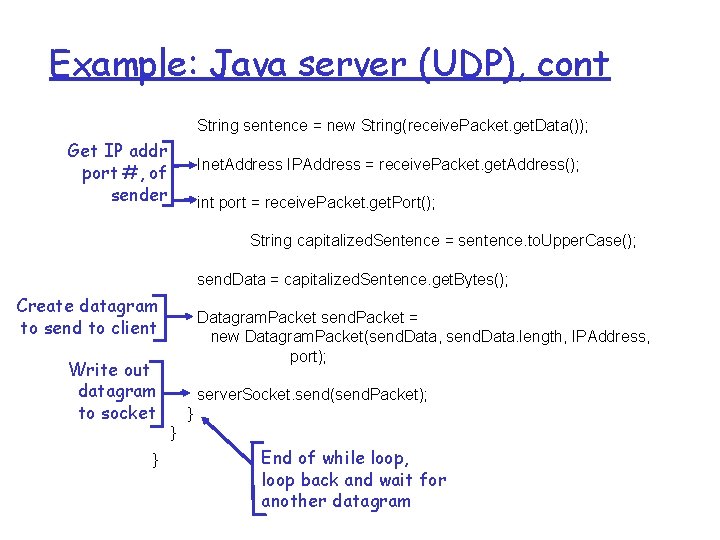
Example: Java server (UDP), cont String sentence = new String(receive. Packet. get. Data()); Get IP addr port #, of sender Inet. Address IPAddress = receive. Packet. get. Address(); int port = receive. Packet. get. Port(); String capitalized. Sentence = sentence. to. Upper. Case(); send. Data = capitalized. Sentence. get. Bytes(); Create datagram to send to client Write out datagram to socket } Datagram. Packet send. Packet = new Datagram. Packet(send. Data, send. Data. length, IPAddress, port); server. Socket. send(send. Packet); } } End of while loop, loop back and wait for another datagram
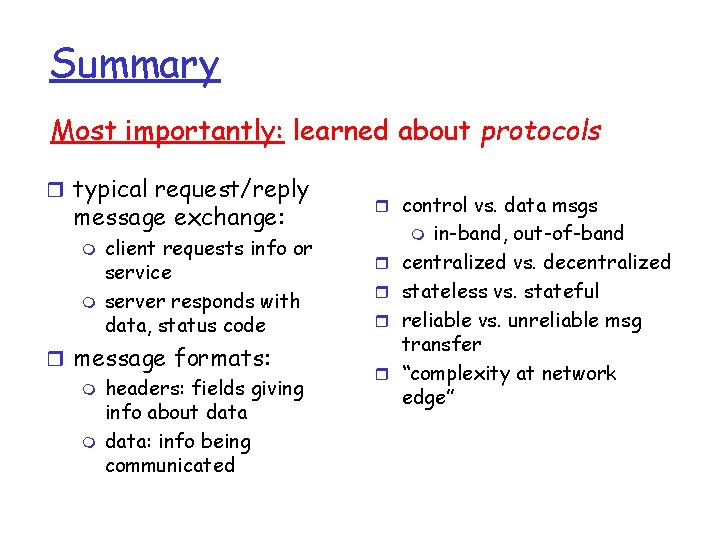
Summary Our study of network apps now complete! r Application architectures m client-server m P 2 P m hybrid r application service requirements: m reliability, bandwidth, delay r Internet transport service model m m connection-oriented, reliable: TCP unreliable, datagrams: UDP r specific protocols: m HTTP m FTP m SMTP, POP, IMAP m DNS r socket programming
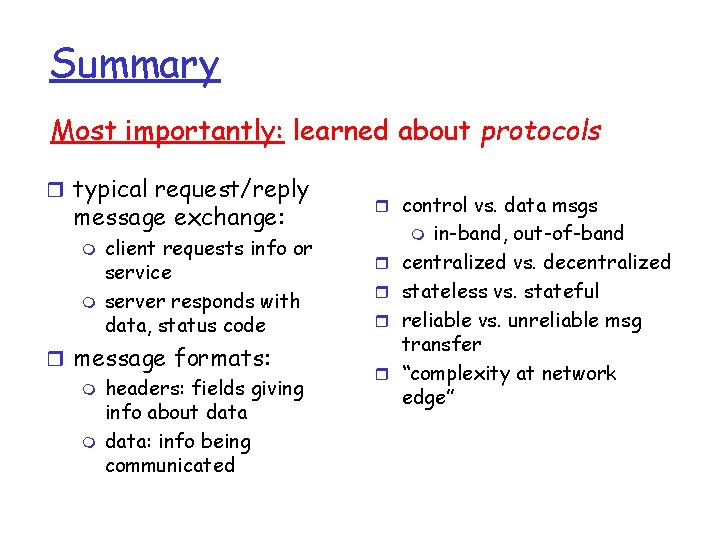
Summary Most importantly: learned about protocols r typical request/reply message exchange: m m client requests info or service server responds with data, status code r message formats: m headers: fields giving info about data m data: info being communicated r control vs. data msgs in-band, out-of-band centralized vs. decentralized stateless vs. stateful reliable vs. unreliable msg transfer “complexity at network edge” m r r