Windows Vista IPSec MCSE SecurityMessaging MVPMCT BS 7799ISO

Windows Vista網路架構、 防火牆與 IPSec 的功能改進 謝合宜 微軟特約技術顧問 MCSE : Security/Messaging MVP/MCT BS 7799/ISO 27001 Lead Auditor



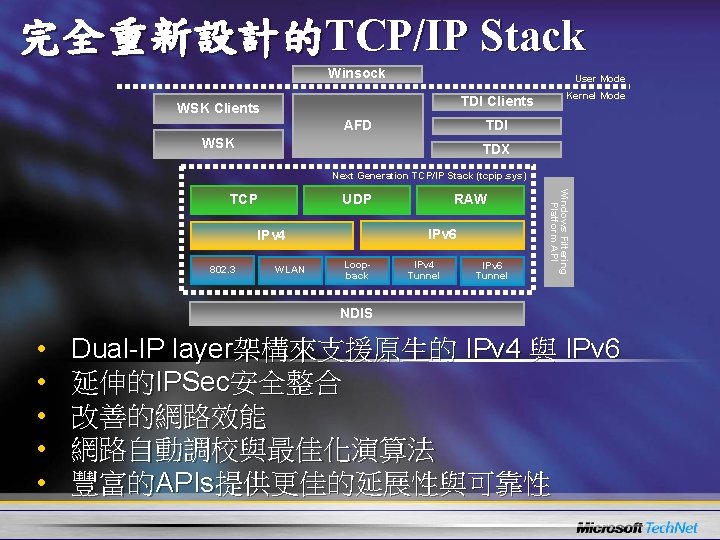
完全重新設計的TCP/IP Stack Winsock User Mode TDI Clients WSK Clients AFD Kernel Mode TDI WSK TDX Next Generation TCP/IP Stack (tcpip. sys) IPv 6 IPv 4 802. 3 RAW UDP WLAN Loopback IPv 4 Tunnel IPv 6 Tunnel Windows Filtering Platform API TCP NDIS • • • Dual-IP layer架構來支援原生的 IPv 4 與 IPv 6 延伸的IPSec安全整合 改善的網路效能 網路自動調校與最佳化演算法 豐富的APIs提供更佳的延展性與可靠性
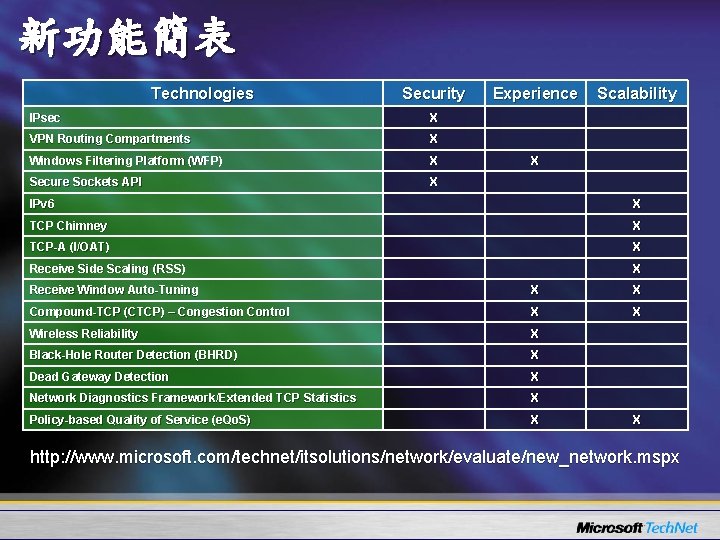
新功能簡表 Technologies Security IPsec X VPN Routing Compartments X Windows Filtering Platform (WFP) X Secure Sockets API X Experience Scalability X IPv 6 X TCP Chimney X TCP-A (I/OAT) X Receive Side Scaling (RSS) X Receive Window Auto-Tuning X X Compound-TCP (CTCP) – Congestion Control X X Wireless Reliability X Black-Hole Router Detection (BHRD) X Dead Gateway Detection X Network Diagnostics Framework/Extended TCP Statistics X Policy-based Quality of Service (e. Qo. S)) X X http: //www. microsoft. com/technet/itsolutions/network/evaluate/new_network. mspx
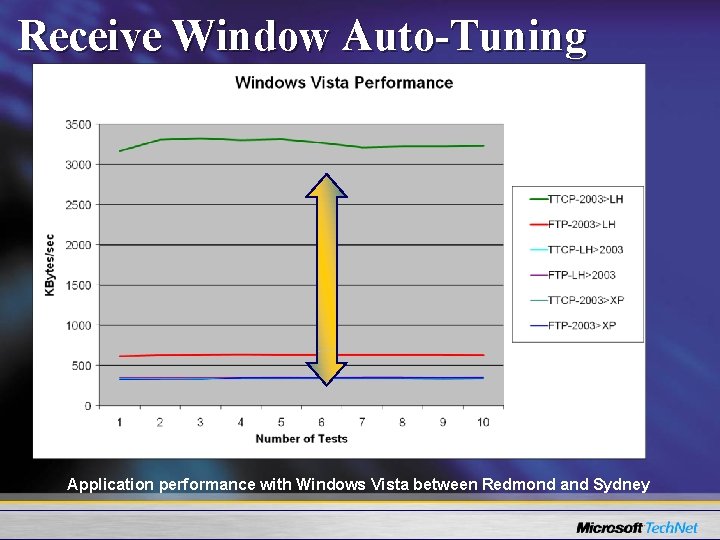
Receive Window Auto-Tuning Application performance with Windows Vista between Redmond and Sydney
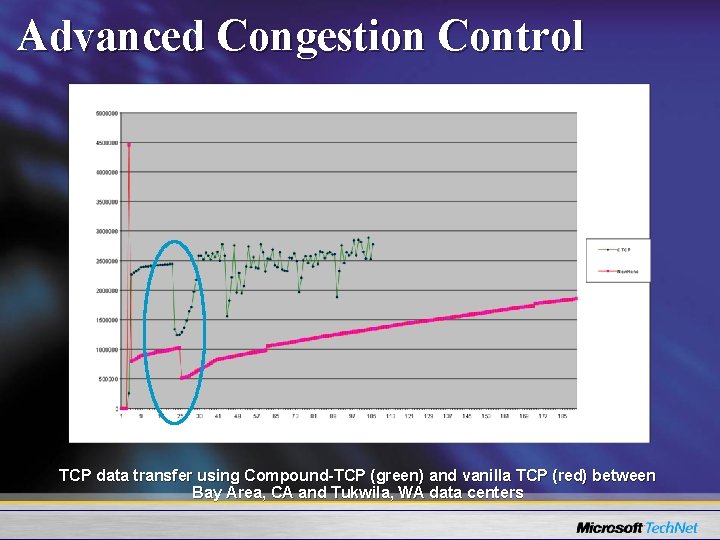
Advanced Congestion Control TCP data transfer using Compound-TCP (green) and vanilla TCP (red) between Bay Area, CA and Tukwila, WA data centers
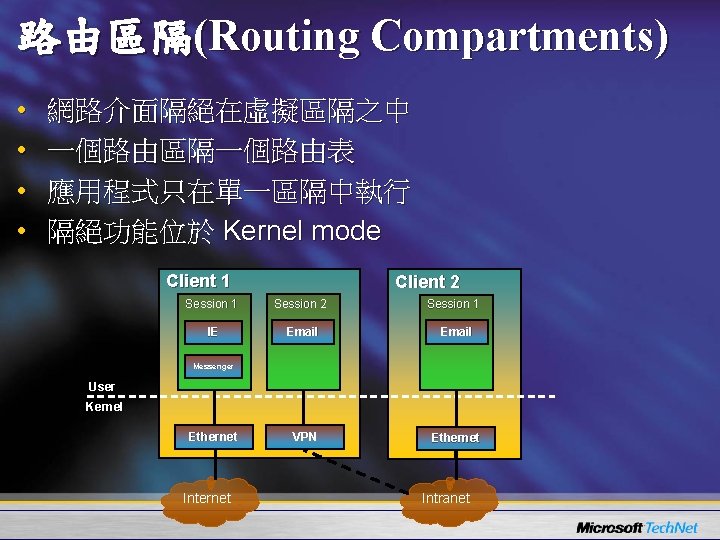
路由區隔(Routing Compartments) • • 網路介面隔絕在虛擬區隔之中 一個路由區隔一個路由表 應用程式只在單一區隔中執行 隔絕功能位於 Kernel mode Client 1 Client 2 Session 1 Session 2 Session 1 IE Email VPN Ethernet Messenger User Kernel Ethernet Intranet
Qo. S Policies的情境 • Source/Destination IPv 4/IPv 6 addresses • Protocol • Source or destination ports • Application
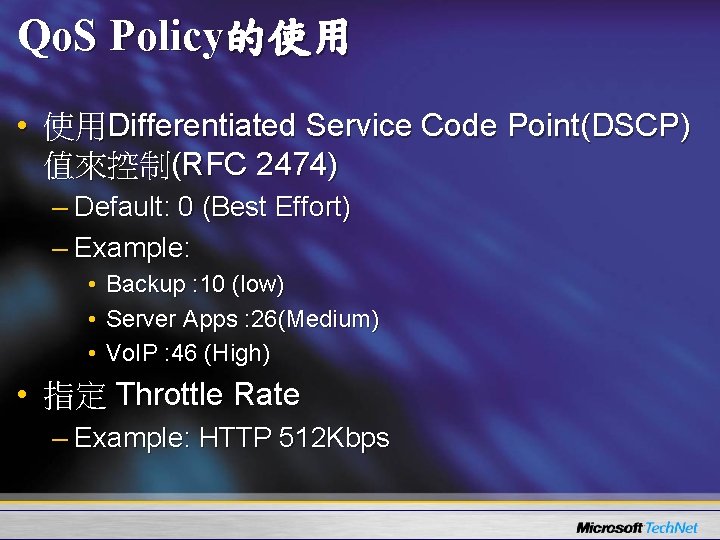
Qo. S Policy的使用 • 使用Differentiated Service Code Point(DSCP) 值來控制(RFC 2474) – Default: 0 (Best Effort) – Example: • Backup : 10 (low) • Server Apps : 26(Medium) • Vo. IP : 46 (High) • 指定 Throttle Rate – Example: HTTP 512 Kbps
Qo. S Policy u. Qo. S Policy for Live Messenger Traffic
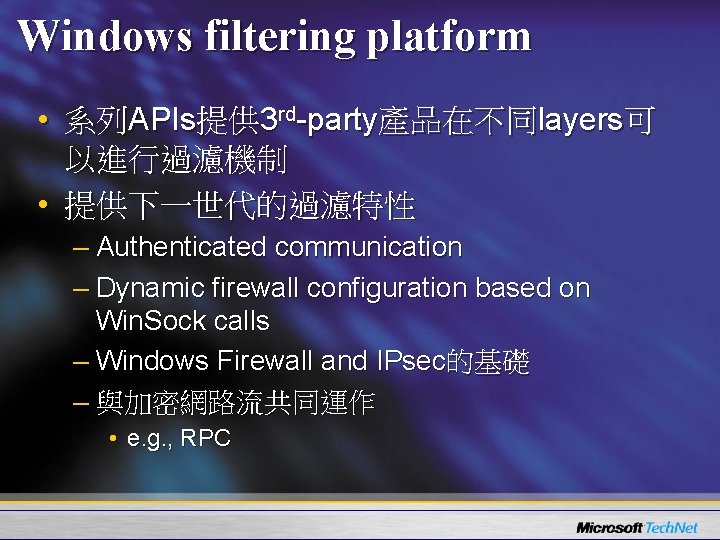
Windows filtering platform • 系列APIs提供 3 rd-party產品在不同layers可 以進行過濾機制 • 提供下一世代的過濾特性 – Authenticated communication – Dynamic firewall configuration based on Win. Sock calls – Windows Firewall and IPsec的基礎 – 與加密網路流共同運作 • e. g. , RPC


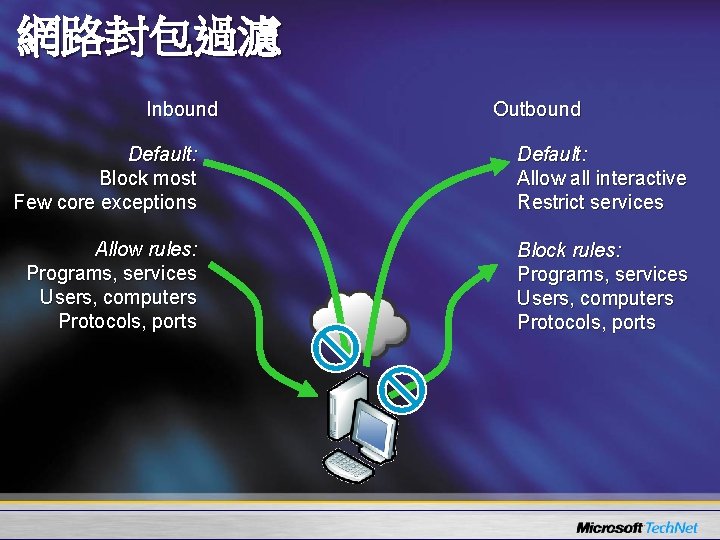
網路封包過濾 Inbound Outbound Default: Block most Few core exceptions Default: Allow all interactive Restrict services Allow rules: Programs, services Users, computers Protocols, ports Block rules: Programs, services Users, computers Protocols, ports
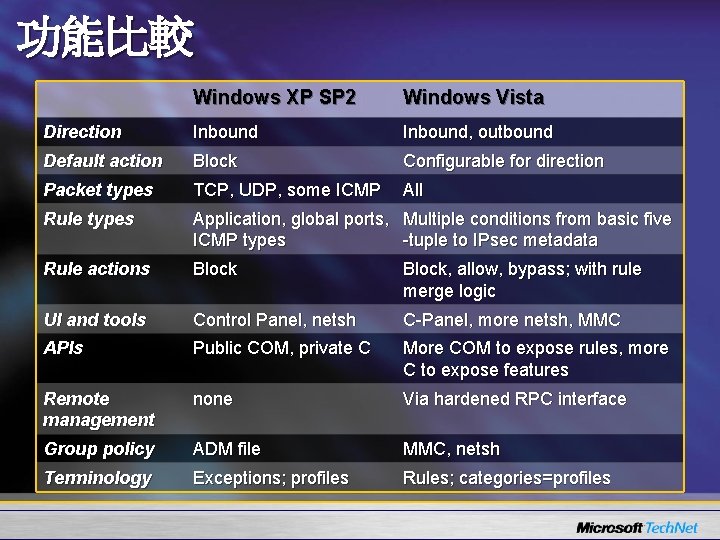
功能比較 Windows XP SP 2 Windows Vista Direction Inbound, outbound Default action Block Configurable for direction Packet types TCP, UDP, some ICMP All Rule types Application, global ports, Multiple conditions from basic five ICMP types -tuple to IPsec metadata Rule actions Block, allow, bypass; with rule merge logic UI and tools Control Panel, netsh C-Panel, more netsh, MMC APIs Public COM, private C More COM to expose rules, more C to expose features Remote management none Via hardened RPC interface Group policy ADM file MMC, netsh Terminology Exceptions; profiles Rules; categories=profiles

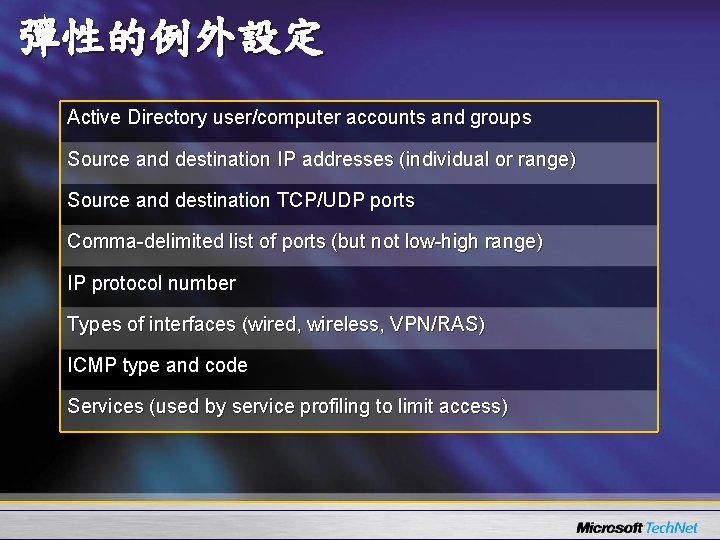
彈性的例外設定 Active Directory user/computer accounts and groups Source and destination IP addresses (individual or range) Source and destination TCP/UDP ports Comma-delimited list of ports (but not low-high range) IP protocol number Types of interfaces (wired, wireless, VPN/RAS) ICMP type and code Services (used by service profiling to limit access)

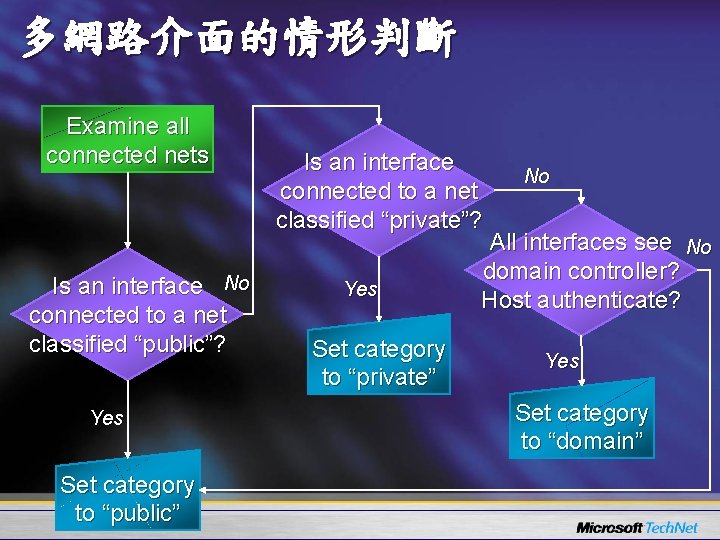
多網路介面的情形判斷 Examine all connected nets Is an interface No connected to a net classified “public”? Yes Set category to “public” Is an interface connected to a net classified “private”? Yes Set category to “private” No All interfaces see No domain controller? Host authenticate? Yes Set category to “domain”

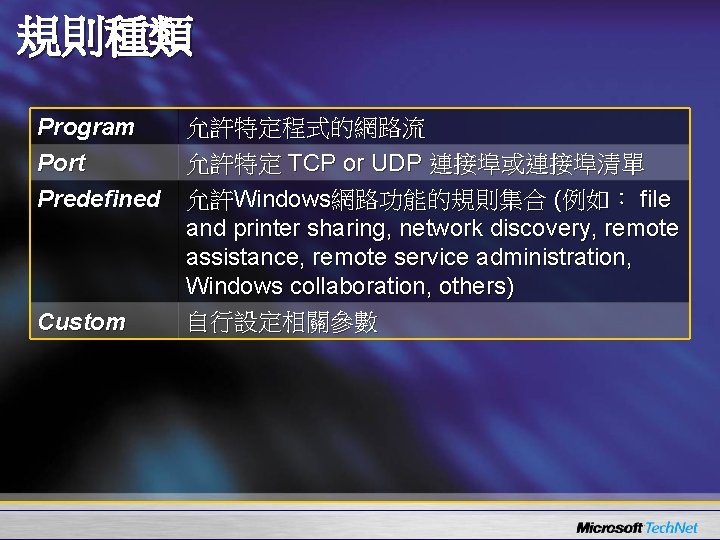
規則種類 允許特定程式的網路流 Program 允許特定 TCP or UDP 連接埠或連接埠清單 Port Predefined 允許Windows網路功能的規則集合 (例如: file and printer sharing, network discovery, remote assistance, remote service administration, Windows collaboration, others) 自行設定相關參數 Custom
Windows Firewall with Advanced Security • Profile設定 • 規則設定
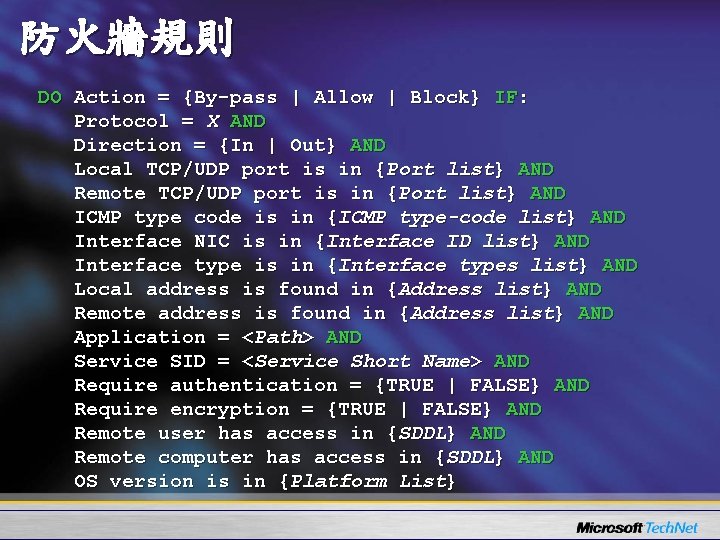
防火牆規則 DO Action = {By-pass | Allow | Block} IF: Protocol = X AND Direction = {In | Out} AND Local TCP/UDP port is in {Port list} AND Remote TCP/UDP port is in {Port list} AND ICMP type code is in {ICMP type-code list} AND Interface NIC is in {Interface ID list} AND Interface type is in {Interface types list} AND Local address is found in {Address list} AND Remote address is found in {Address list} AND Application = <Path> AND Service SID = <Service Short Name> AND Require authentication = {TRUE | FALSE} AND Require encryption = {TRUE | FALSE} AND Remote user has access in {SDDL} AND Remote computer has access in {SDDL} AND OS version is in {Platform List}
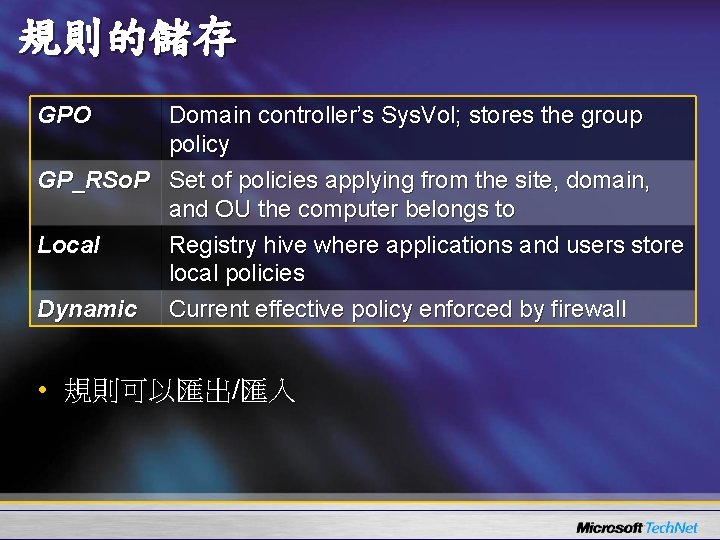
規則的儲存 GPO Domain controller’s Sys. Vol; stores the group policy GP_RSo. P Set of policies applying from the site, domain, and OU the computer belongs to Local Registry hive where applications and users store local policies Dynamic Current effective policy enforced by firewall • 規則可以匯出/匯入
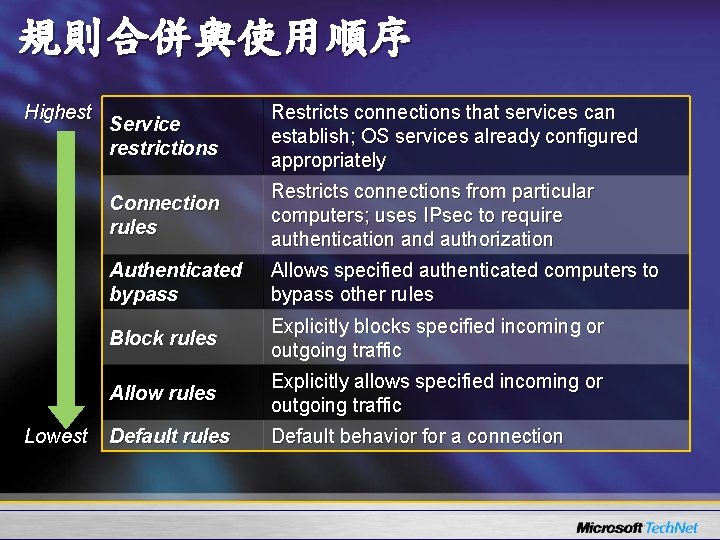
規則合併與使用順序 Highest Lowest Service restrictions Restricts connections that services can establish; OS services already configured appropriately Connection rules Restricts connections from particular computers; uses IPsec to require authentication and authorization Authenticated bypass Allows specified authenticated computers to bypass other rules Block rules Explicitly blocks specified incoming or outgoing traffic Allow rules Explicitly allows specified incoming or outgoing traffic Default rules Default behavior for a connection


Windows Firewall with Advanced Security • 規則匯出與監視

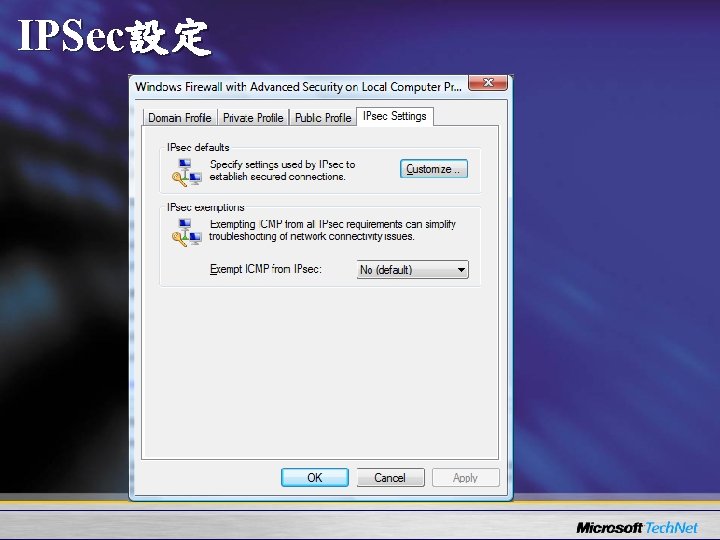
IPSec設定
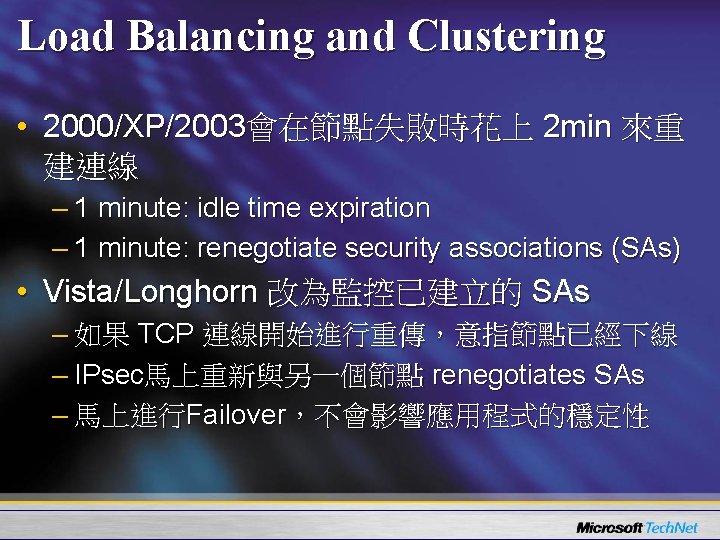
Load Balancing and Clustering • 2000/XP/2003會在節點失敗時花上 2 min 來重 建連線 – 1 minute: idle time expiration – 1 minute: renegotiate security associations (SAs) • Vista/Longhorn 改為監控已建立的 SAs – 如果 TCP 連線開始進行重傳,意指節點已經下線 – IPsec馬上重新與另一個節點 renegotiates SAs – 馬上進行Failover,不會影響應用程式的穩定性
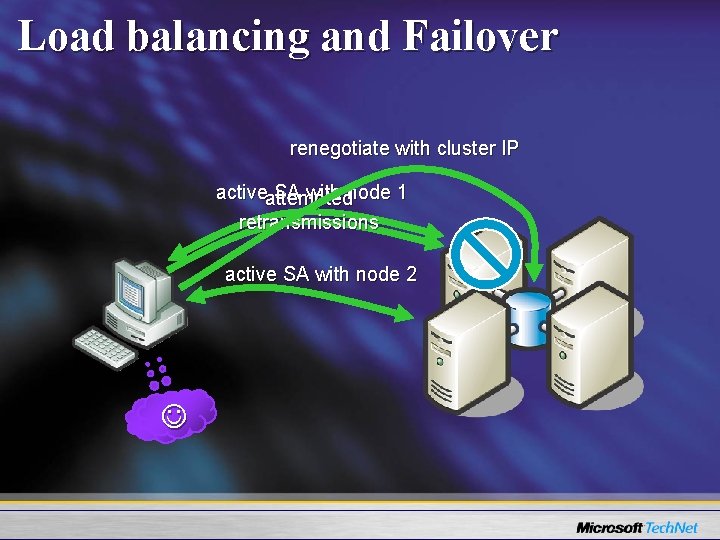
Load balancing and Failover renegotiate with cluster IP activeattempted SA with node 1 retransmissions active SA with node 2
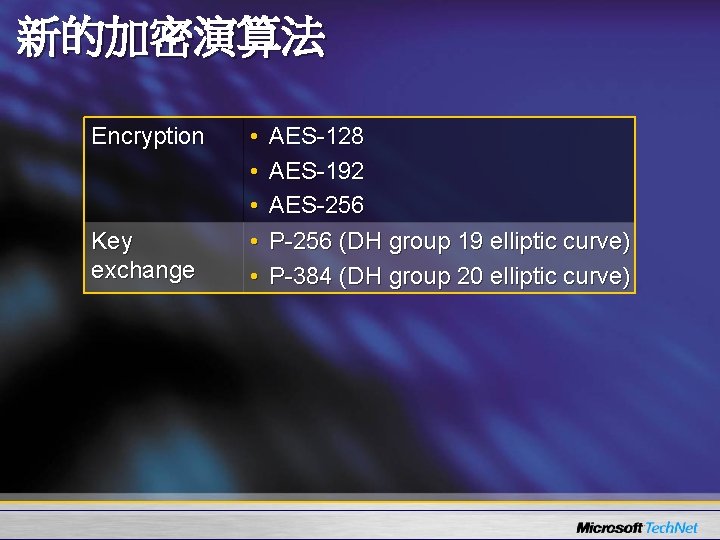
新的加密演算法 Encryption Key exchange • • • AES-128 AES-192 AES-256 P-256 (DH group 19 elliptic curve) P-384 (DH group 20 elliptic curve)



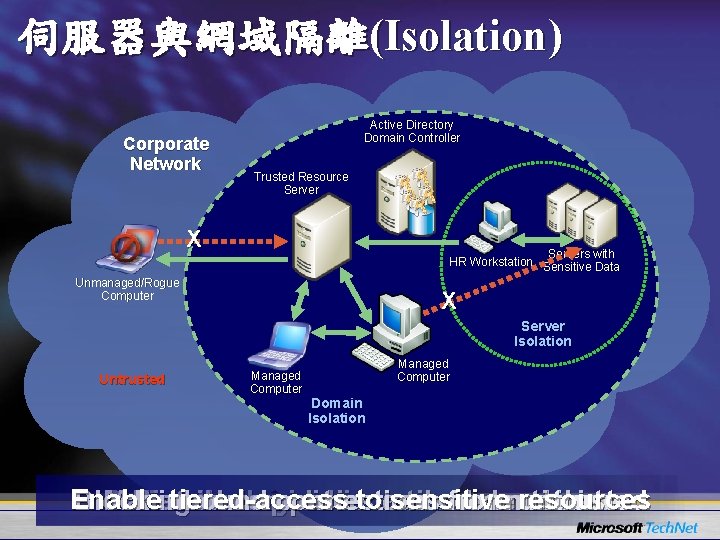
伺服器與網域隔離(Isolation) Corporate Network Active Directory Domain Controller Trusted Resource Server X Servers with HR Workstation Sensitive Data Unmanaged/Rogue Computer X Server Isolation Untrusted Managed Computer Domain Isolation Enable tiered-access toand sensitive resources Block inbound connections from untrusted Managed can communicate Define Distribute thecomputers logical policies isolation credentials boundaries


Home Work • Server and Domain Isolation with Microsoft Windows – http: //www. microsoft. com/downloads/details. aspx? Family. ID=9 a 3 e 2 b 2 b-695 d 4 ff 9 -bcb 1 -5 f 2 f 3001845 e&Display. Lang=en • Network Location Types in Windows Vista – http: //www. microsoft. com/technet/community/columns/cableguy/cg 0906. mspx • The New Windows Firewall in Windows Vista and Windows Server "Longhorn" – http: //www. microsoft. com/technet/community/columns/cableguy/cg 0106. mspx
For More Information… • Tech. Net – www. microsoft. com/taiwan/technet • Windows Vista – www. microsoft. com/taiwan/windowsvista • Windows Vista: Resources for IT Professional – www. microsoft. com/technet/windowsvista/def ault. mspx • MVP Community社群網站 – www. microsoft. com/taiwan/community

- Slides: 45