Terrorists and Emerging Technologies Gary Ackerman Director Unconventional



- Slides: 63
Terrorists and Emerging Technologies Gary Ackerman Director, Unconventional Weapons and Technology Division, START Mad Scientist: AI, Robotics & Autonomy in Multi-Domain Battle 2030 -2050 March 8, 2017 The START Consortium is supported by the U. S. Department of Homeland Security (DHS) Science and Technology Directorate’s Office of University Programs. Any opinions, findings, conclusions or recommendations presented here are solely the authors’ and are not representative of DHS or the United States Government.
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Preview 1. 2. 3. 4. 5. 6. 7. Preamble… The Basics The Attraction of AI, Robotics & Autonomy Chances of Success T-TAM Considering Dynamics Current Developments – Early Warning Indicators? 8. Where Might We Be Going? § Postscript: AI as the enemy
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Preamble…
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security

National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Background There be monsters thar…
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security How Do Emerging Technologies Empower Terrorists? “Give me a lever long enough and a fulcrum on which to place it and I shall move the world” – Archimedes The gravest danger our Nation faces lies at the crossroads of radicalism and technology – National Security Strategy (2002) “The IQ level required for a single individual to destroy the world decreases by one point every year” – Eliezer Yudkowsky “But the world is changing with accelerating speed…We know all too well, after 9/11, just how technology and globalization has put power once reserved for states in the hands of individuals, raising the capacity of terrorists to do harm” – President Obama (2014)
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security (One) Definition of Terrorism The intentional use or threatened use of violence by an ideologically motivated non-state actor in a manner that would be regarded in wartime as contravening international humanitarian law and that is directed against victims selected for their symbolic or representative value, as a means of instilling anxiety in, transmitting one or more messages to, and thereby manipulating the attitudes and behavior of a wider target audience or audiences.
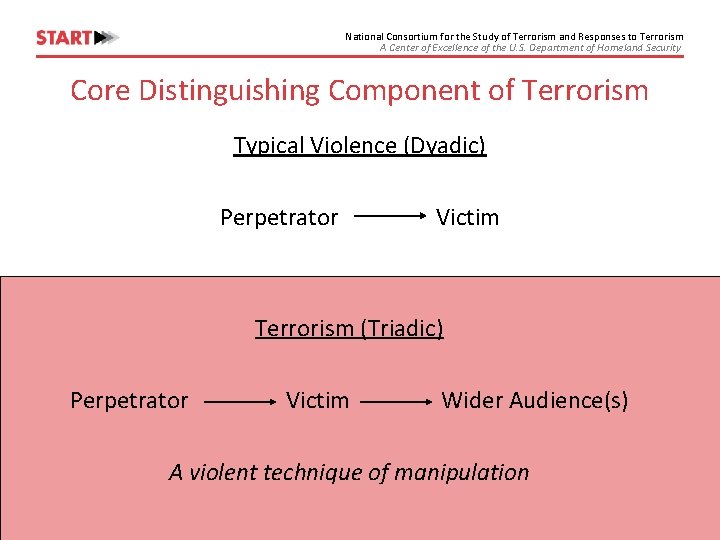
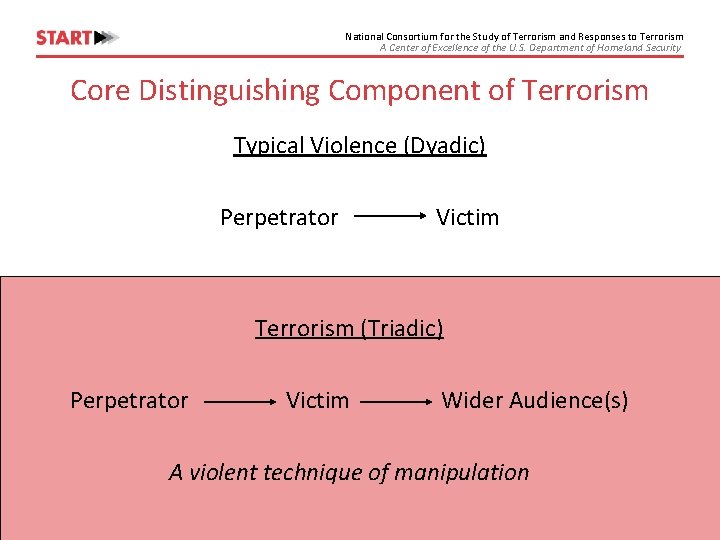
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Core Distinguishing Component of Terrorism Typical Violence (Dyadic) Perpetrator Victim Terrorism (Triadic) Perpetrator Victim Wider Audience(s) A violent technique of manipulation
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security (One) Definition of Technology The manipulation of natural phenomena as a means of fulfilling a human purpose. Disruptive Technology: technology that provides a new dimension of value/performance, that is at first lower in performance than existing technologies along traditional dimensions.
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Supervillains or Luddites? vs.
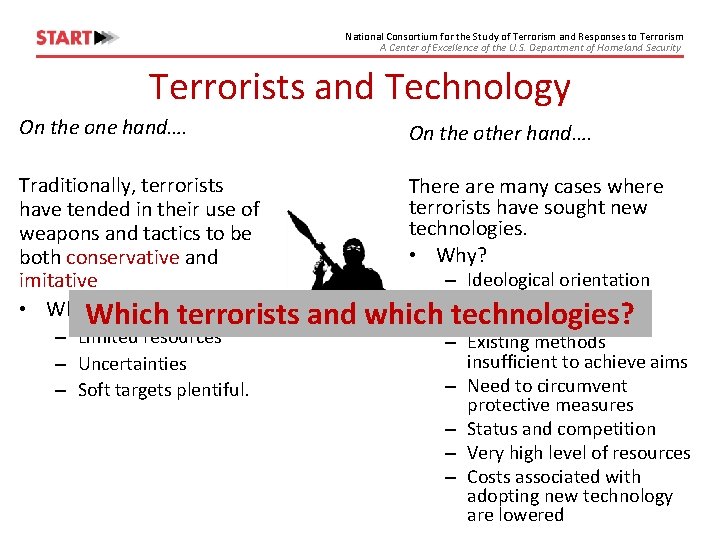
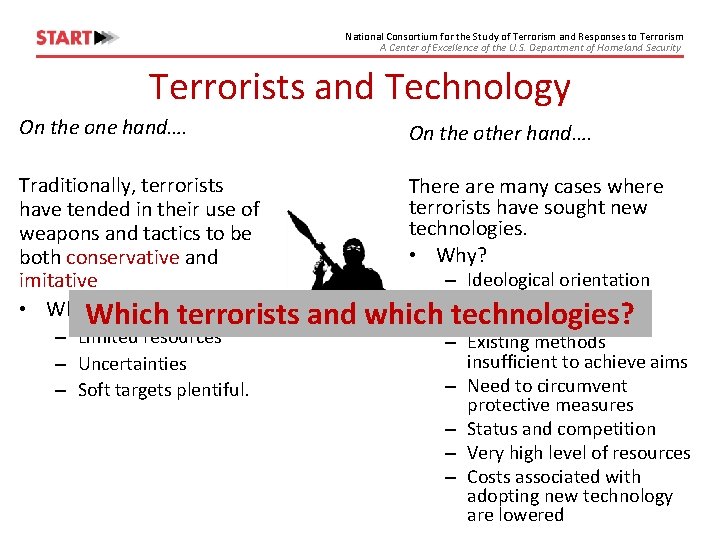
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Terrorists and Technology On the one hand…. On the other hand…. Traditionally, terrorists have tended in their use of weapons and tactics to be both conservative and imitative • Why? Which terrorists There are many cases where terrorists have sought new technologies. • Why? – Limited resources – Uncertainties – Soft targets plentiful. and – Ideological orientation towards innovating which technologies? technologically – Existing methods insufficient to achieve aims – Need to circumvent protective measures – Status and competition – Very high level of resources – Costs associated with adopting new technology are lowered
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security “Prediction is very difficult, especially about the future. ” Yogi Berra- 1962) Niels Bohr (1885 “For man does not even know his hour: like fish caught in a fatal net, like birds seized in a snare, so are men caught in the moment of disaster when it falls upon them suddenly. ” Ecclesiastes 9: 12
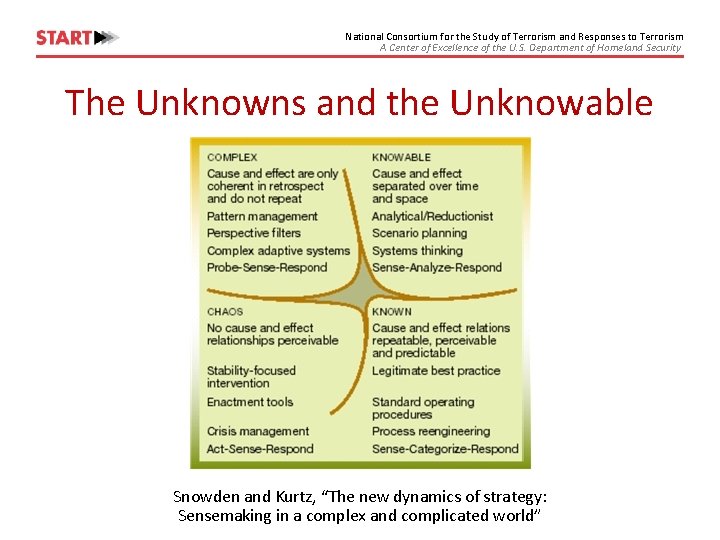
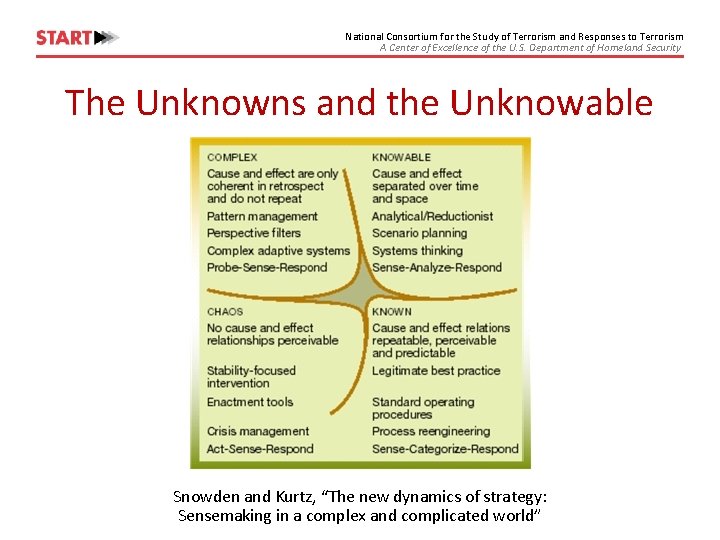
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security The Unknowns and the Unknowable Snowden and Kurtz, “The new dynamics of strategy: Sensemaking in a complex and complicated world”
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security The Attraction of AI, Robotics & Autonomy
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Fundamental Driver of Terrorist Innovation • Perceived gap in performance between what is desired and status quo that cannot be addressed with existing means and methods. …So, assuming such a perceived gap exists, why might AI, robotics and/or autonomous systems be attractive to terrorists and other violent non-state actors?
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Reason 1 • Taking the human out of the loop (same as for military) – Reducing the need for labor which reduces human resource costs • e. g. , VBIED: terrorist equivalent of a guided missile, but substantial resources must be devoted to radicalizing, recruiting and training an operative who can only be used once; autonomous VBIEDs would free up resources. • Often very important for terrorists operating with constrained resources. – More difficult to apprehend / kill in tactical situations • E. g. , teleoperated sniper rifles • Increased operational success rates.
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Reason 2 • Lengthens the lever of asymmetry – Autonomy allows for fewer terrorists to have greater effect • E. g. , one operative controlling 500 explosive drones – Overwhelm defenses – Better attack planning and C 4 ISR – In 2030 -2050 timeframe, rival some state forces conventionally?
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Reason 3 • Heighten psychological impact of attacks – Enemy can be everywhere and anywhere (FUD) • E. g. , send drones into homes – Harder to protect against, so could enhance loss of faith in government institutions – Feeds into inherent human fears about malevolent technology
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Reason 4 • Present new opportunities for exploitation – Turning our own systems against us • E. g. , hacking driverless cars
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Reason 5 • Undermine emerging technologies – Show these new technologies cannot be trusted • E. g. , Ted Kaczynski; Individualidades Tendiendo a lo Salvaje (ITS)
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Then again… • Just like with any innovation, risks and uncertainties – also often sunk start-up costs • Just like with any organization, guardians of the status quo will resist • BUT: younger generation (as we are seeing with groups like ISIS) are more comfortable with latest technologies like AI, robotics and often drawn towards them – Resistance likely to ebb over time
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Will They Succeed?
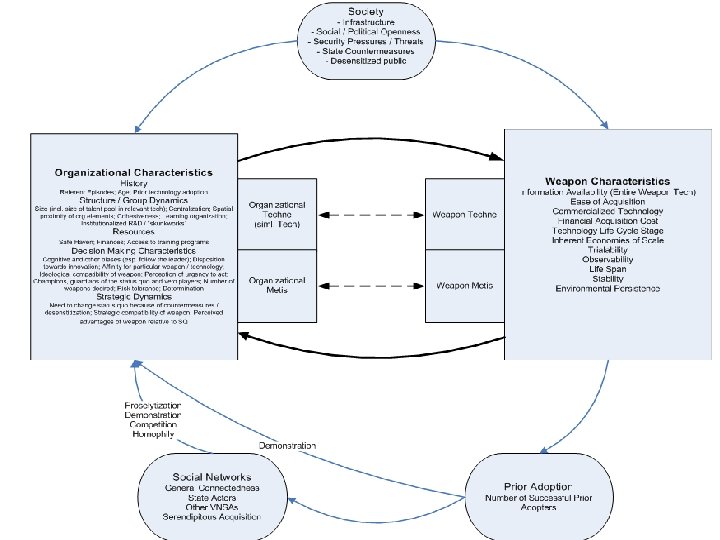
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Success Factors • Many contributors to success or failure of adoption attempts – Most are contextual, especially to the environment and organization • E. g. , Internal champions, safe havens, cognitive biases, societal infrastructure, demonstration, security pressures – Key elements are techne and mētis • Focus on complex technological innovations
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security “Designing Danger” Complex Engineering by Violent Non-State Actors • The process of adoption and deployment often requires the complex application of knowledge and materials in a practical context. • Thus, when it comes to the assessment of such threats, much of the analysis hinges upon being able to accurately judge the desire and capability of adversaries to successfully carry out complex engineering operations. • Project Objectives: Examine violent non-state actor ability to undertake complex engineering projects and, in turn, the feasibility of a non-state adoption project in light of emerging technologies.
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Definition • Complex Engineering Task: In the context of this project, a complex engineering task undertaken by a violent non-state actor (VNSA) is one that involves: – Multiple components (sub-tasks) of different types (e. g. , mechanical, chemical, machining) that must integrate properly in order for the effort to succeed – The manpower of more than just one person – A variety of technical skills – A more sophisticated effort than standard operations for the context (time and place) in which the VNSA is operating
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Research q Surveyed existing literature to understand: • The conditions under which terrorists / VNSAs undertake complex engineering tasks • The factors (causes; drivers) that prompt terrorist actors to undertake these tasks • The process by which the tasks are undertaken • The determinants of success or failure at these complex engineering tasks q Modeled and completed comparative analysis using the Terrorist Technology Adoption Model (T-TAM) coding profiles for: ISIS, Hizballah, AQ Central and a generic apocalyptic millenarian cult modeled on Aum Shinrikyo
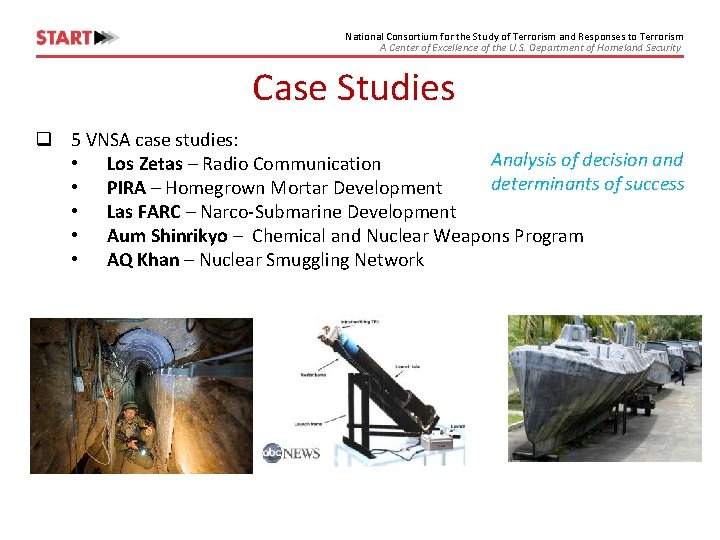
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Case Studies q 5 VNSA case studies: Analysis of decision and • Los Zetas – Radio Communication determinants of success • PIRA – Homegrown Mortar Development • Las FARC – Narco-Submarine Development • Aum Shinrikyo – Chemical and Nuclear Weapons Program • AQ Khan – Nuclear Smuggling Network
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Designing Danger: Journal of Strategic Security
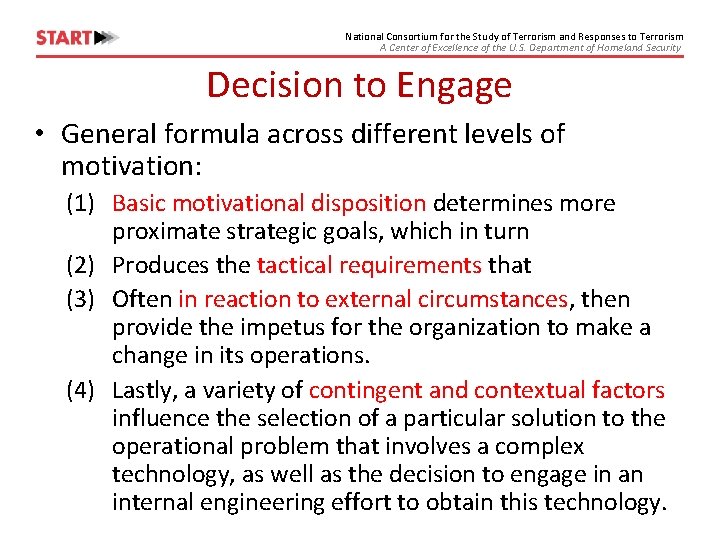
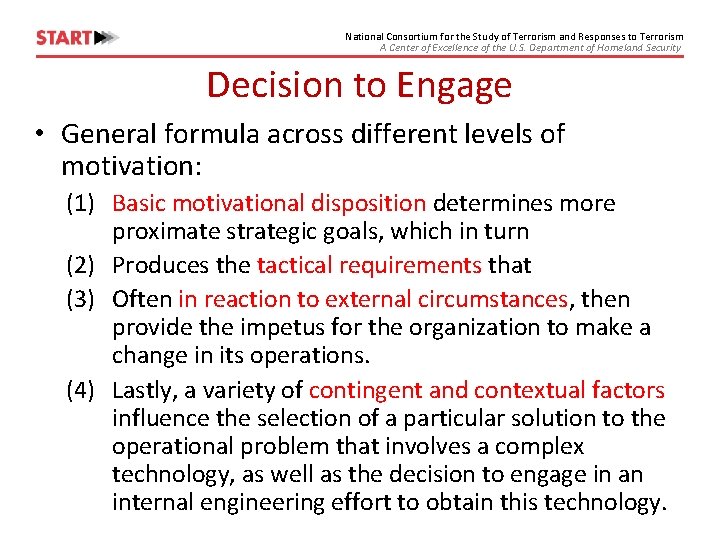
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Decision to Engage • General formula across different levels of motivation: (1) Basic motivational disposition determines more proximate strategic goals, which in turn (2) Produces the tactical requirements that (3) Often in reaction to external circumstances, then provide the impetus for the organization to make a change in its operations. (4) Lastly, a variety of contingent and contextual factors influence the selection of a particular solution to the operational problem that involves a complex technology, as well as the decision to engage in an internal engineering effort to obtain this technology.
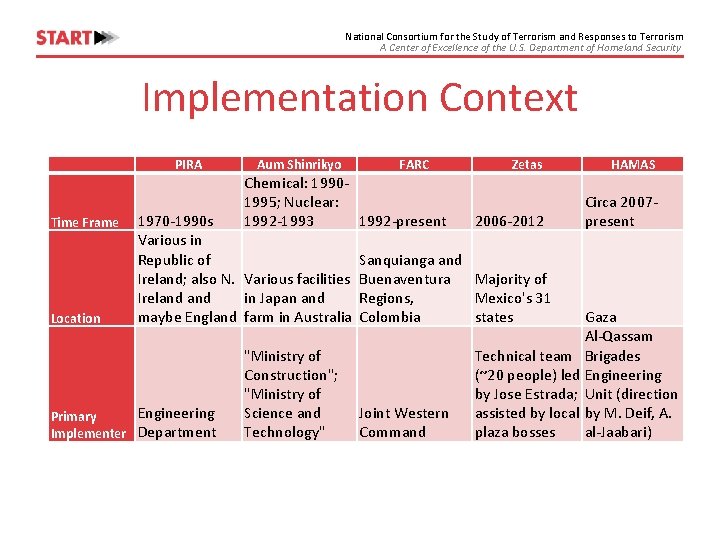
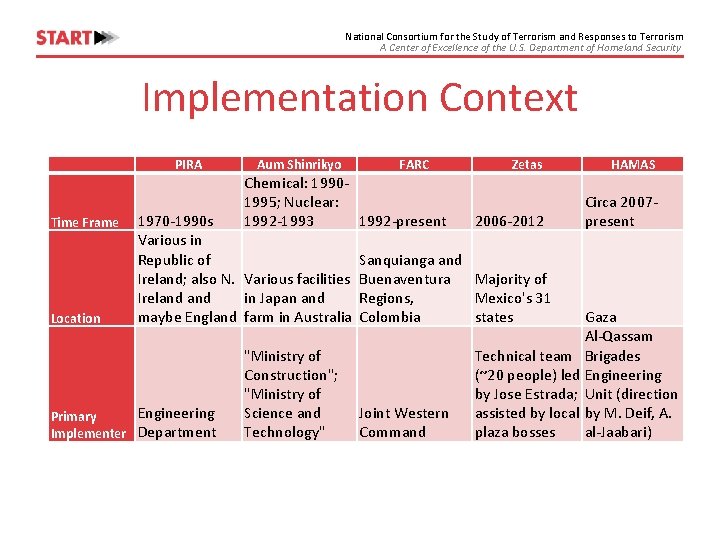
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Implementation Context PIRA Time Frame Location Aum Shinrikyo Chemical: 19901995; Nuclear: 1992 -1993 1992 -present 1970 -1990 s Various in Republic of Ireland; also N. Various facilities Ireland in Japan and maybe England farm in Australia Engineering Primary Implementer Department FARC "Ministry of Construction"; "Ministry of Science and Technology" Zetas HAMAS 2006 -2012 Circa 2007 present Sanquianga and Buenaventura Majority of Regions, Mexico's 31 Colombia states Joint Western Command Gaza Al-Qassam Technical team Brigades (~20 people) led Engineering by Jose Estrada; Unit (direction assisted by local by M. Deif, A. plaza bosses al-Jaabari)
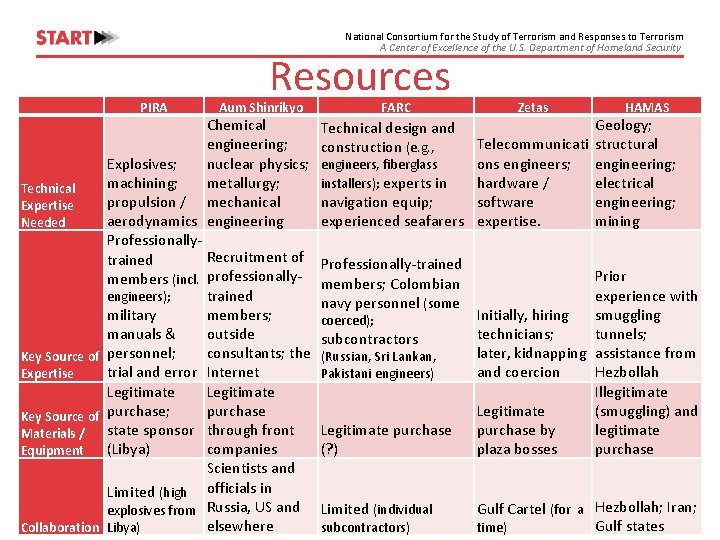
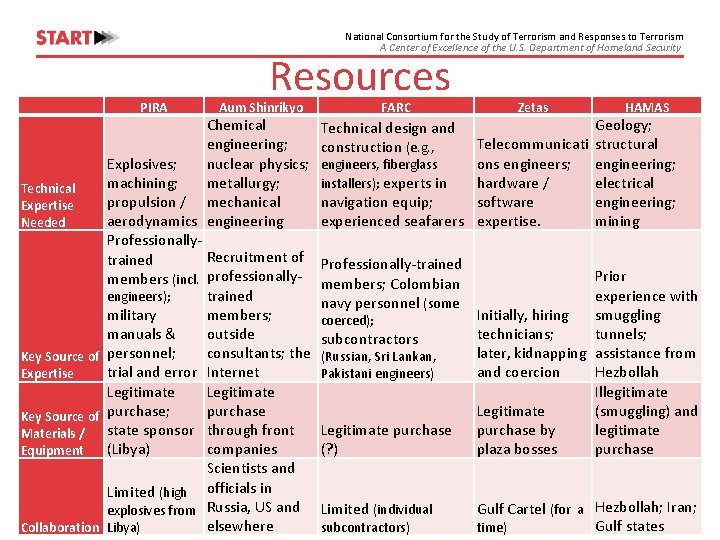
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security PIRA Resources Aum Shinrikyo Chemical engineering; Explosives; nuclear physics; machining; metallurgy; Technical propulsion / mechanical Expertise aerodynamics engineering Needed Professionally. Recruitment of trained members (incl. professionallytrained engineers); military members; manuals & outside consultants; the Key Source of personnel; trial and error Internet Expertise Legitimate purchase Key Source of purchase; state sponsor through front Materials / (Libya) companies Equipment Scientists and Limited (high officials in explosives from Russia, US and elsewhere Collaboration Libya) FARC Zetas HAMAS Geology; Telecommunicati structural ons engineers; engineering; engineers, fiberglass installers); experts in hardware / electrical navigation equip; software engineering; experienced seafarers expertise. mining Technical design and construction (e. g. , Professionally-trained members; Colombian navy personnel (some coerced); subcontractors (Russian, Sri Lankan, Pakistani engineers) Legitimate purchase (? ) Limited (individual subcontractors) Prior experience with Initially, hiring smuggling technicians; tunnels; later, kidnapping assistance from and coercion Hezbollah Illegitimate Legitimate (smuggling) and purchase by legitimate plaza bosses purchase Gulf Cartel (for a Hezbollah; Iran; Gulf states time)
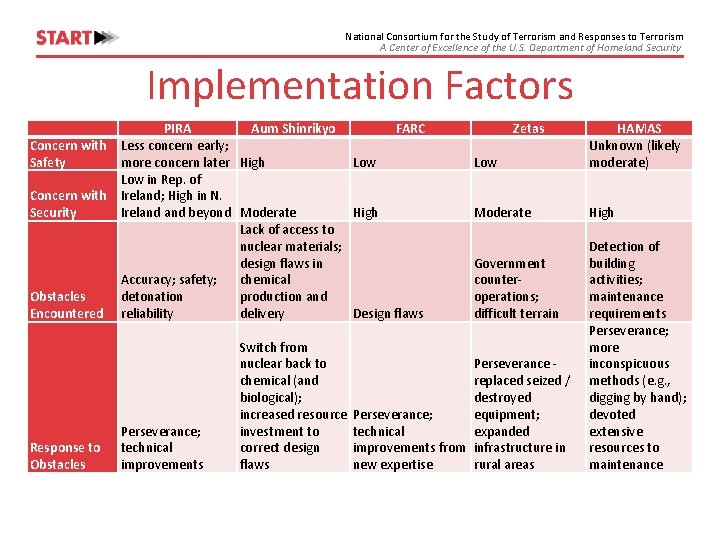
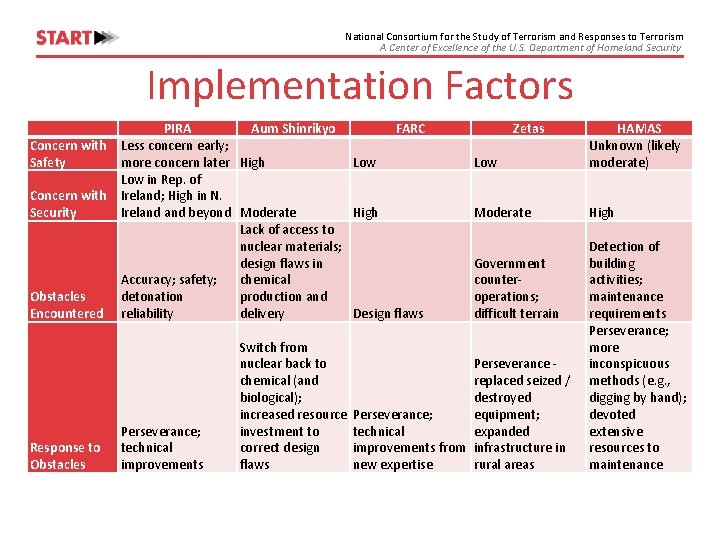
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Implementation Factors PIRA Aum Shinrikyo FARC Concern with Less concern early; Safety more concern later High Low in Rep. of Concern with Ireland; High in N. High Security Ireland beyond Moderate Lack of access to nuclear materials; design flaws in chemical Accuracy; safety; production and Obstacles detonation delivery Design flaws Encountered reliability Response to Obstacles Perseverance; technical improvements Switch from nuclear back to chemical (and biological); increased resource investment to correct design flaws Zetas Low HAMAS Unknown (likely moderate) Moderate High Government counteroperations; difficult terrain Perseverance replaced seized / destroyed equipment; Perseverance; technical expanded improvements from infrastructure in new expertise rural areas Detection of building activities; maintenance requirements Perseverance; more inconspicuous methods (e. g. , digging by hand); devoted extensive resources to maintenance
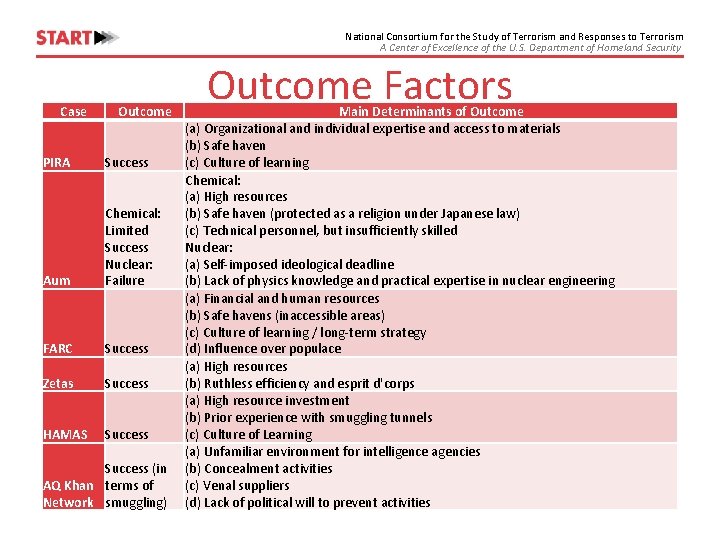
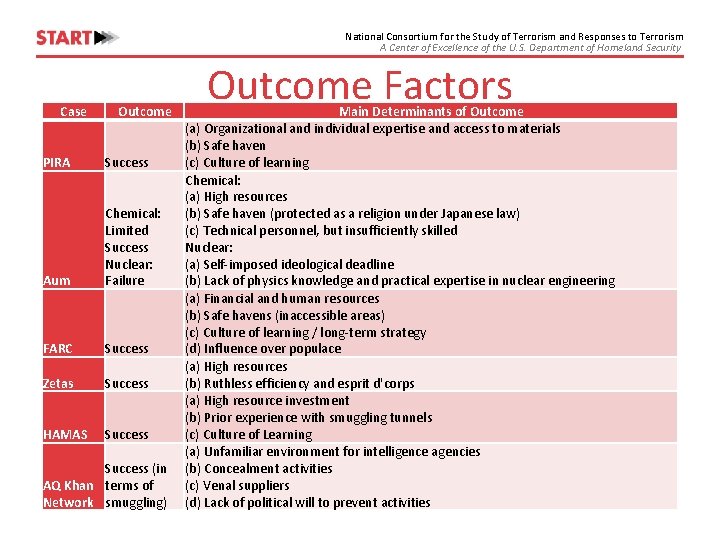
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Case Outcome PIRA Success Aum Chemical: Limited Success Nuclear: Failure FARC Success Zetas Success HAMAS Success (in AQ Khan terms of Network smuggling) Outcome Factors Main Determinants of Outcome (a) Organizational and individual expertise and access to materials (b) Safe haven (c) Culture of learning Chemical: (a) High resources (b) Safe haven (protected as a religion under Japanese law) (c) Technical personnel, but insufficiently skilled Nuclear: (a) Self-imposed ideological deadline (b) Lack of physics knowledge and practical expertise in nuclear engineering (a) Financial and human resources (b) Safe havens (inaccessible areas) (c) Culture of learning / long-term strategy (d) Influence over populace (a) High resources (b) Ruthless efficiency and esprit d'corps (a) High resource investment (b) Prior experience with smuggling tunnels (c) Culture of Learning (a) Unfamiliar environment for intelligence agencies (b) Concealment activities (c) Venal suppliers (d) Lack of political will to prevent activities
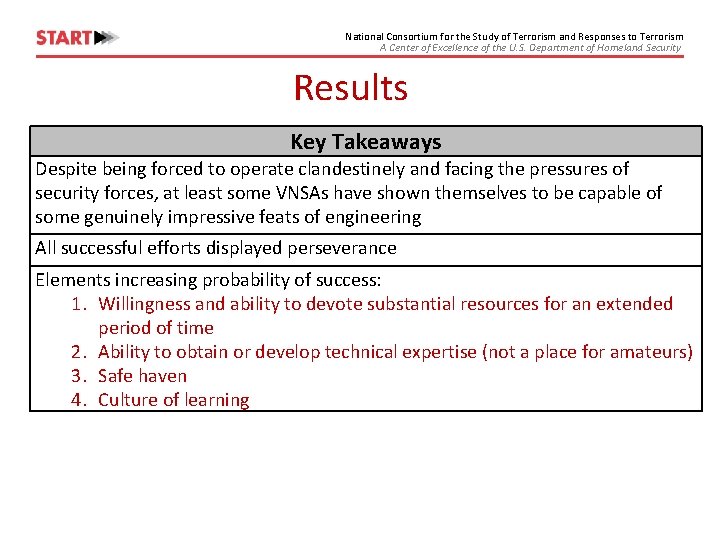
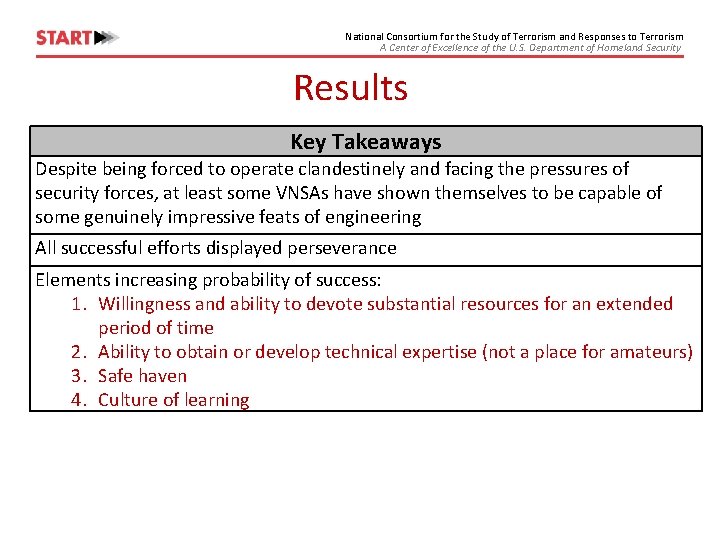
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Results Key Takeaways Despite being forced to operate clandestinely and facing the pressures of security forces, at least some VNSAs have shown themselves to be capable of some genuinely impressive feats of engineering All successful efforts displayed perseverance Elements increasing probability of success: 1. Willingness and ability to devote substantial resources for an extended period of time 2. Ability to obtain or develop technical expertise (not a place for amateurs) 3. Safe haven 4. Culture of learning
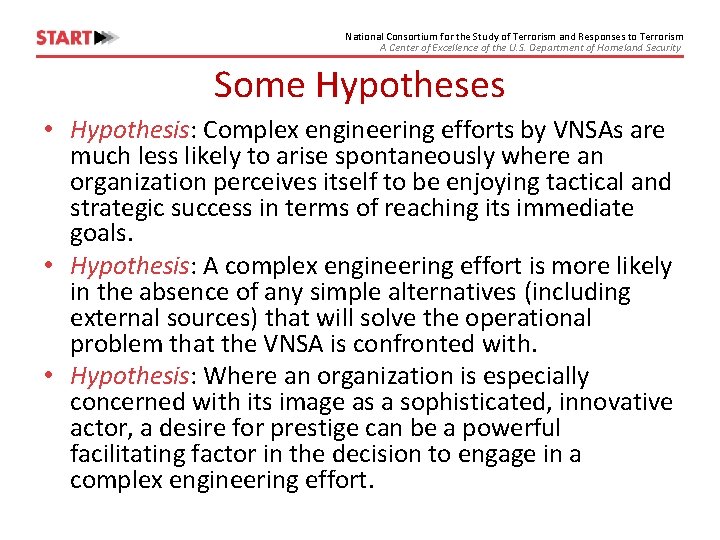
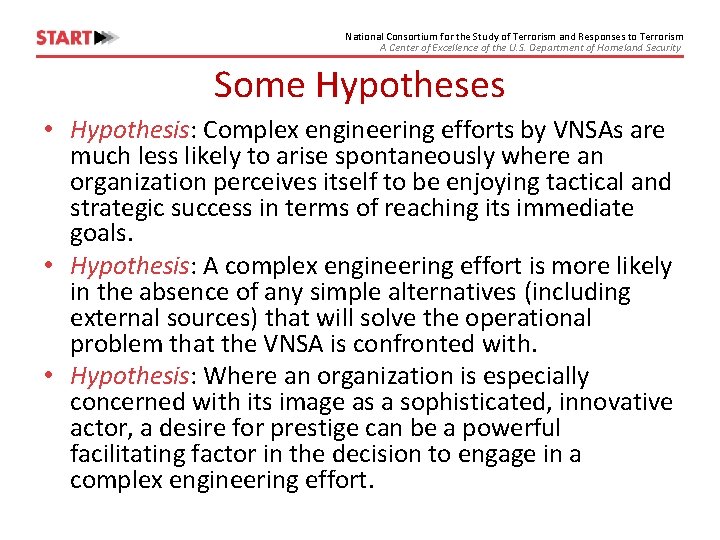
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Some Hypotheses • Hypothesis: Complex engineering efforts by VNSAs are much less likely to arise spontaneously where an organization perceives itself to be enjoying tactical and strategic success in terms of reaching its immediate goals. • Hypothesis: A complex engineering effort is more likely in the absence of any simple alternatives (including external sources) that will solve the operational problem that the VNSA is confronted with. • Hypothesis: Where an organization is especially concerned with its image as a sophisticated, innovative actor, a desire for prestige can be a powerful facilitating factor in the decision to engage in a complex engineering effort.
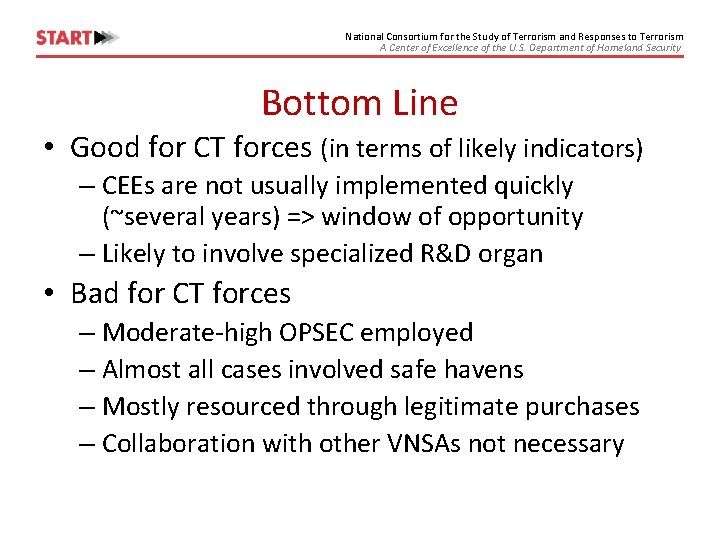
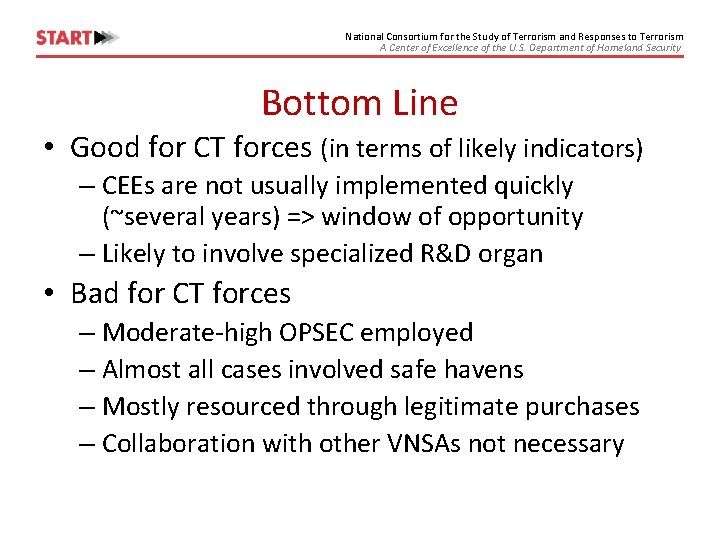
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Bottom Line • Good for CT forces (in terms of likely indicators) – CEEs are not usually implemented quickly (~several years) => window of opportunity – Likely to involve specialized R&D organ • Bad for CT forces – Moderate-high OPSEC employed – Almost all cases involved safe havens – Mostly resourced through legitimate purchases – Collaboration with other VNSAs not necessary
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Terrorist Technology Adoption Model
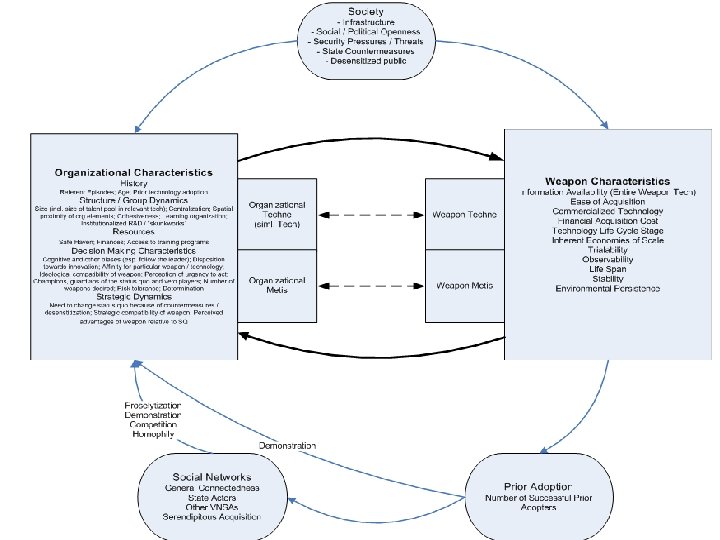
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security A. Terrorist Technology Adoption Model (T-TAM)
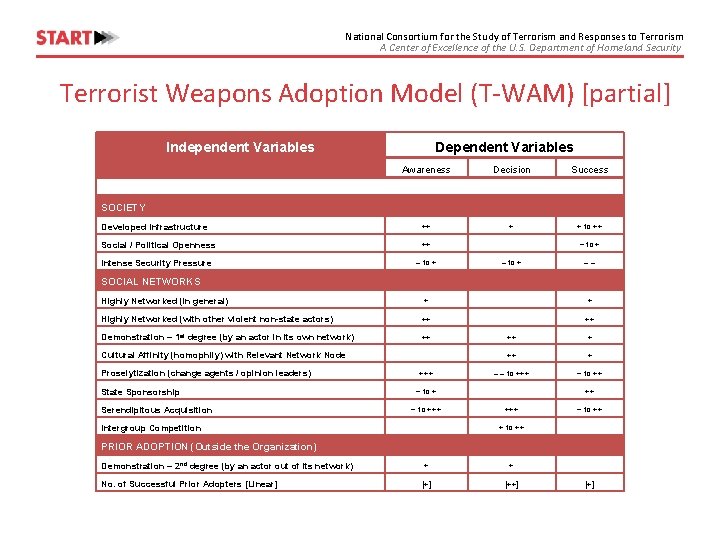
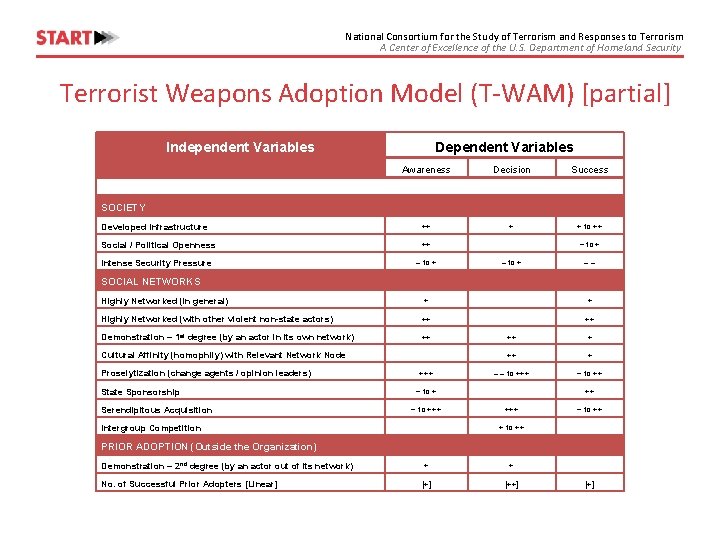
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Terrorist Weapons Adoption Model (T-WAM) [partial] Independent Variables Dependent Variables Awareness Decision Success Developed Infrastructure ++ + + to ++ Social / Political Openness ++ Intense Security Pressure – to + SOCIETY ~ to + –– SOCIAL NETWORKS Highly Networked (in general) + + Highly Networked (with other violent non-state actors) ++ ++ Demonstration – 1 st degree (by an actor in its own network) ++ Cultural Affinity (homophily) with Relevant Network Node Proselytization (change agents / opinion leaders) State Sponsorship Serendipitous Acquisition +++ ++ + – – to +++ ~ to +++ Intergroup Competition ++ +++ ~ to ++ + to ++ PRIOR ADOPTION (Outside the Organization) Demonstration – 2 nd degree (by an actor out of its network) + + No. of Successful Prior Adopters [Linear] [++] [+]

National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Model Results Summary
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Illustrative Application Technology vs by vs vs
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Findings & Implications • Key Finding: Multiple failure points along road to technology adoption success => don’t jump to conclusions about the terrorist threat posed by new technology – Policy Implication: Don’t try and curtail terrorist awareness – rather techne and mētis • Key Finding: Terrorist-Technology Dyad is central; not technology alone – Policy Implication: Finding the salient ones provides guidance in resolving dual-use dilemma posed by emerging technology • Key Finding: It is possible to identify most dangerous terrorist -technology dyads using T-TAM as an operational framework – Prioritizes terrorists most likely to adopt any specific emerging technology – Utilizes observable or inferable attributes – Can be readily updated to reflect organizational / environmental changes
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Considering Dynamics
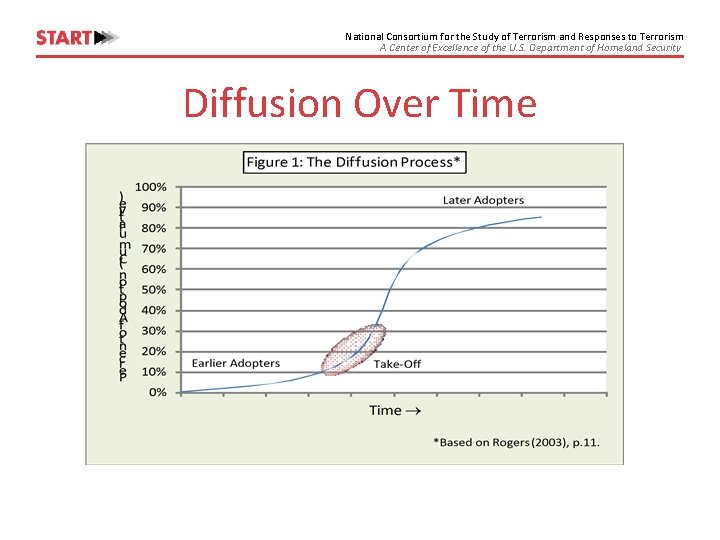
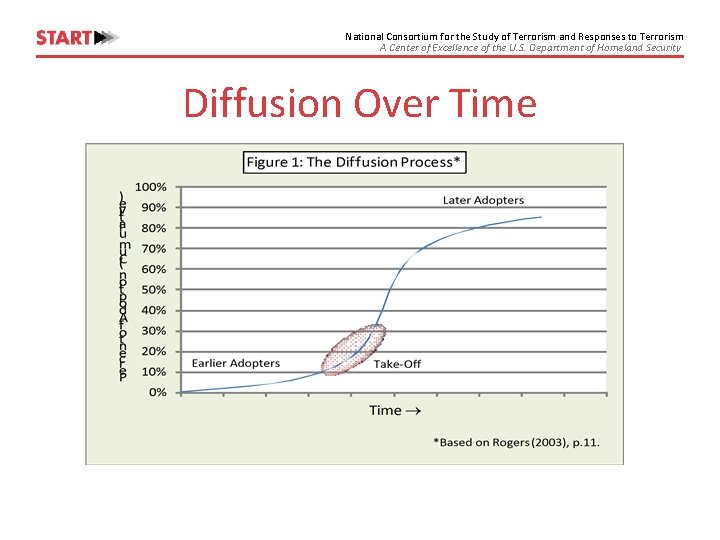
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Diffusion Over Time
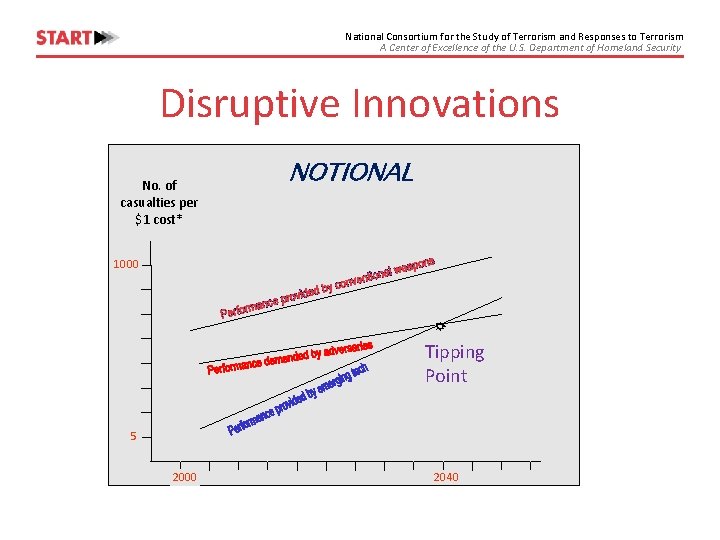
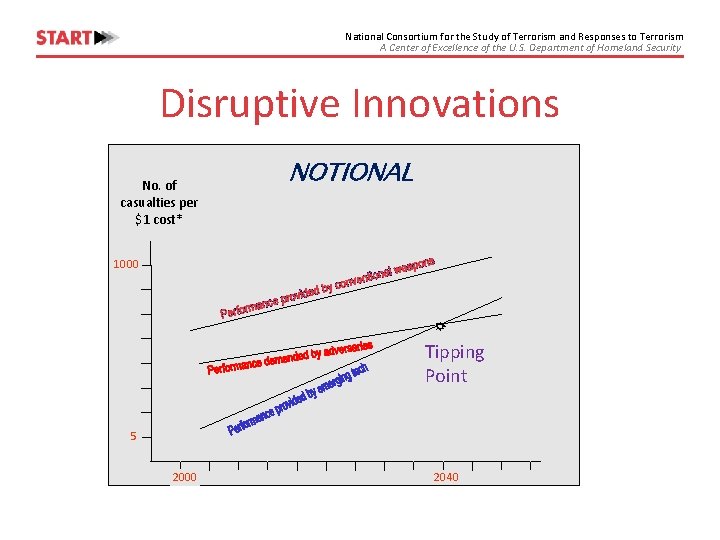
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Disruptive Innovations No. of casualties per $1 cost* NOTIONAL 1000 Tipping Point 5 2000 2040
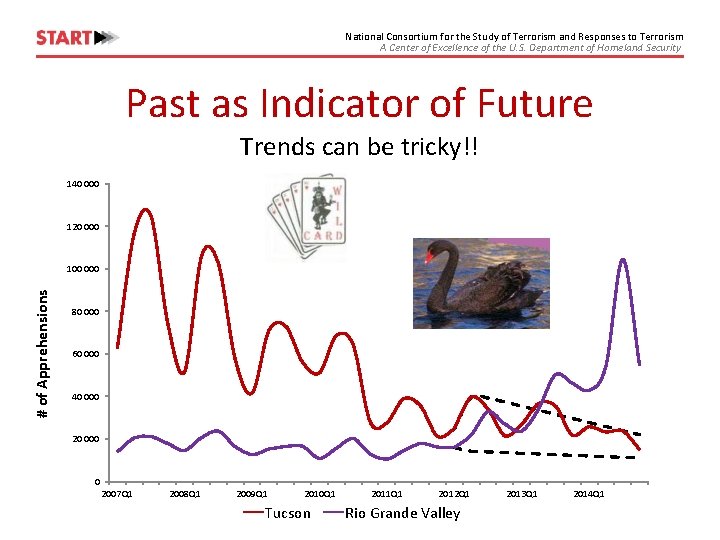
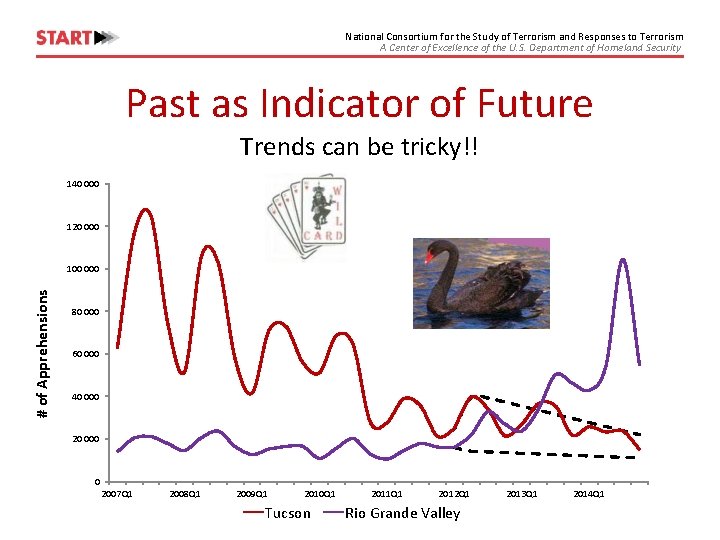
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Past as Indicator of Future Trends can be tricky!! 140 000 120 000 # of Apprehensions 100 000 80 000 60 000 40 000 20 000 0 2007 Q 1 2008 Q 1 2009 Q 1 2010 Q 1 Tucson 2011 Q 1 2012 Q 1 Rio Grande Valley 2013 Q 1 2014 Q 1
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Current Developments – Early Warning Indicators?
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Trends • Increasing interest in new technologies – E. g. , Calls for engineers by ISIS • New adversaries – Terror-crime nexus (e. g. , synthetic chem industry) – Obscure ideologies (e. g. , ITS) • Rapidly evolving technologies
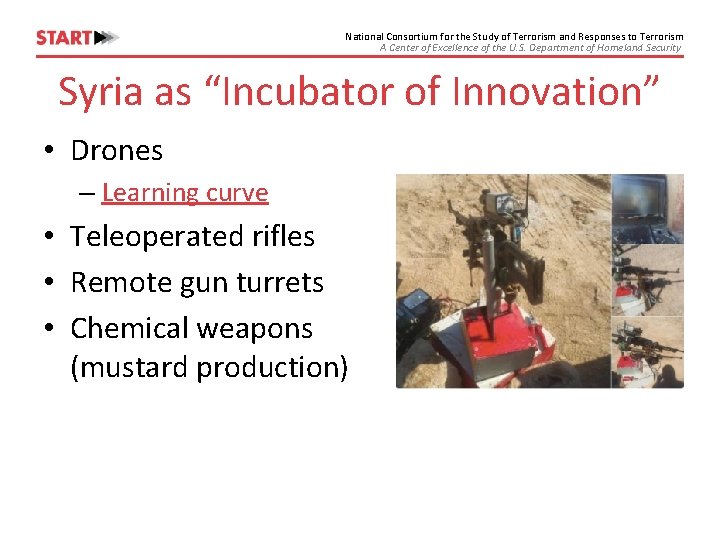
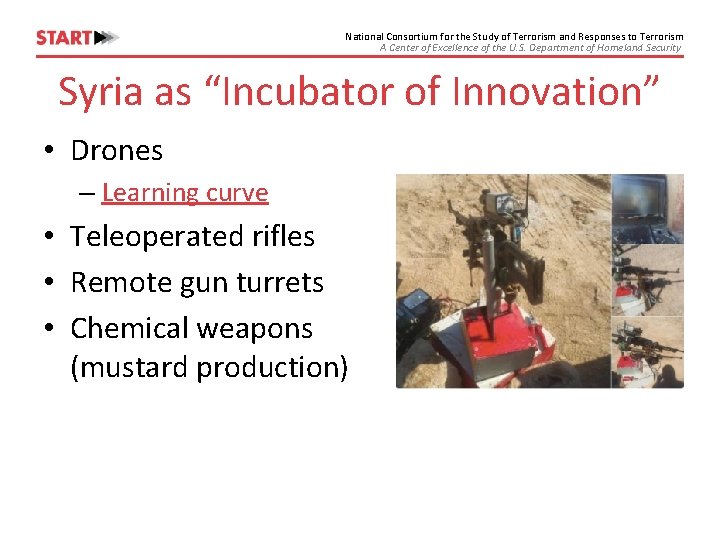
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Syria as “Incubator of Innovation” • Drones – Learning curve • Teleoperated rifles • Remote gun turrets • Chemical weapons (mustard production)
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Where Might We Be Going? 2030 – 2050
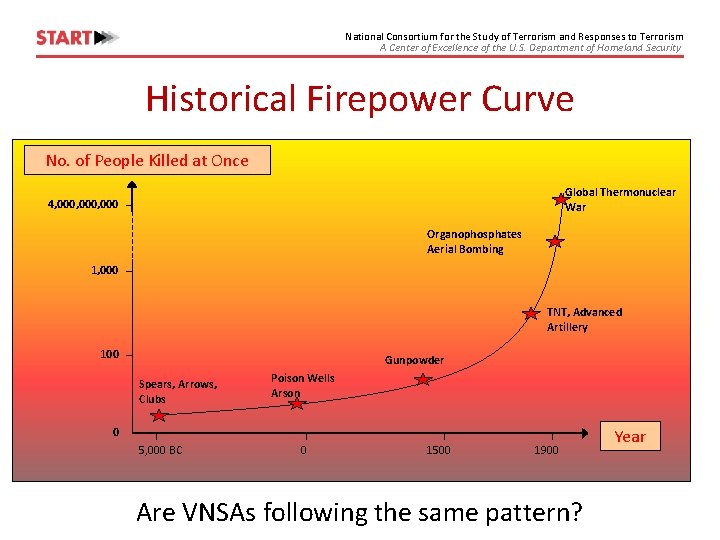
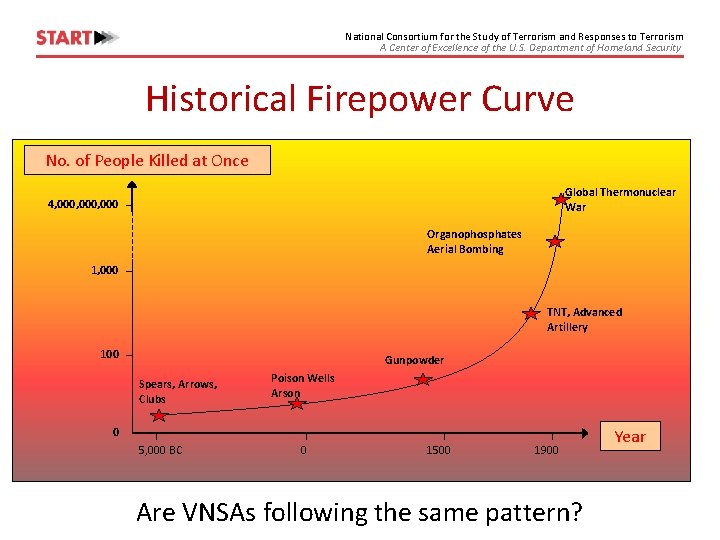
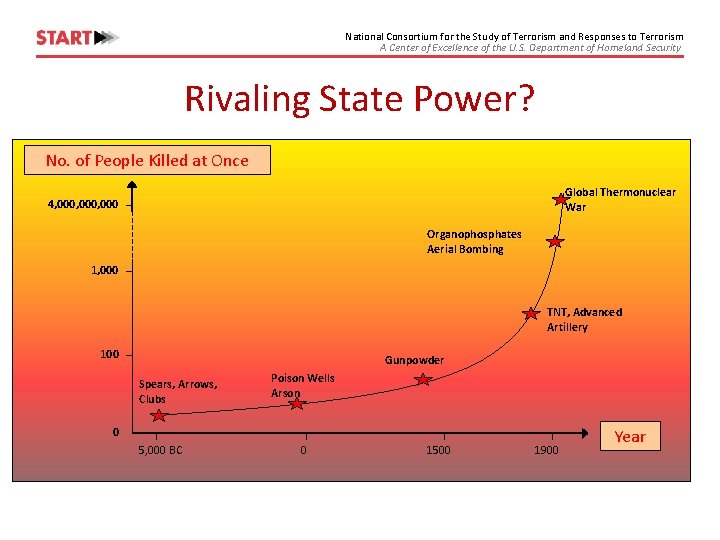
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Historical Firepower Curve No. of People Killed at Once Global Thermonuclear War 4, 000, 000 Organophosphates Aerial Bombing 1, 000 TNT, Advanced Artillery 100 Gunpowder Spears, Arrows, Clubs Poison Wells Arson 0 5, 000 BC 0 1500 1900 Are VNSAs following the same pattern? Year
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security New Forms of Attack? • Autonomous swarms (see opening scenarios) • Large-scale hacking of new autonomous / AI systems – Infrastructure (e. g. , vehicles) – Decision aids • A becomes B • Build-in catastrophic failure for emergent systems
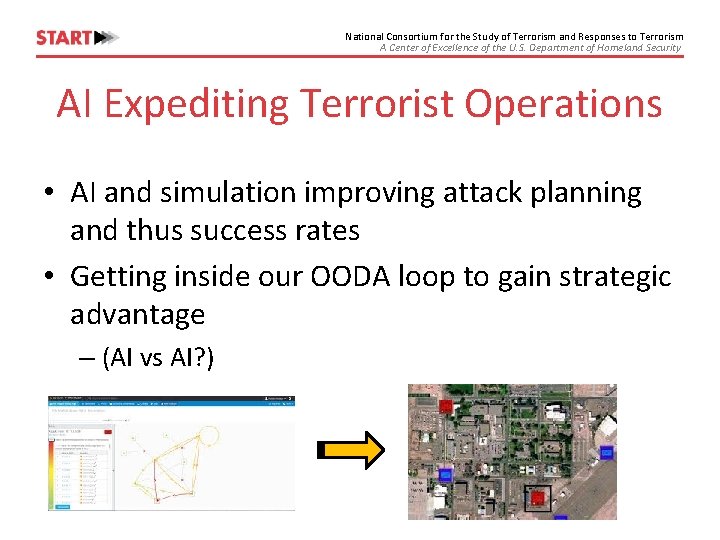
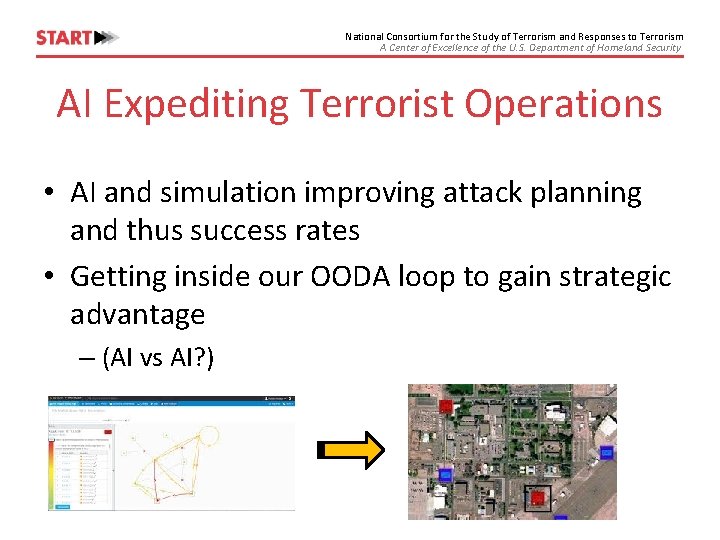
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security AI Expediting Terrorist Operations • AI and simulation improving attack planning and thus success rates • Getting inside our OODA loop to gain strategic advantage – (AI vs AI? )
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Adjunct Technologies • Additive manufacturing (provides the swarms) • Software replication (marginal cost to proliferate an AI is close to zero)
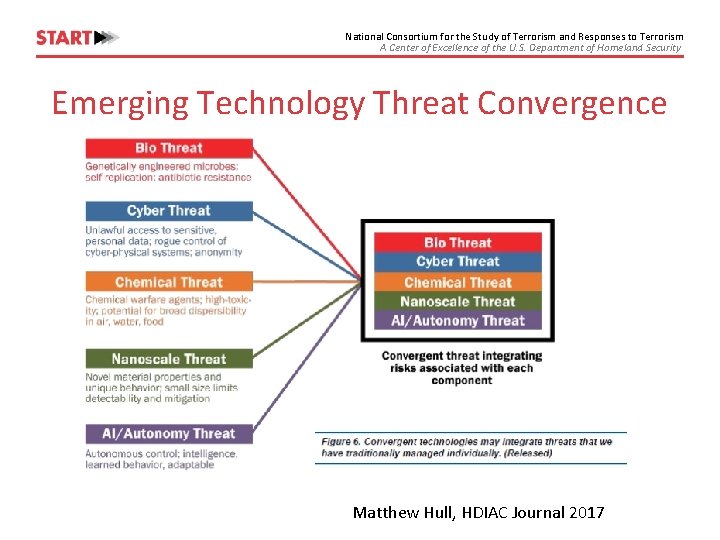
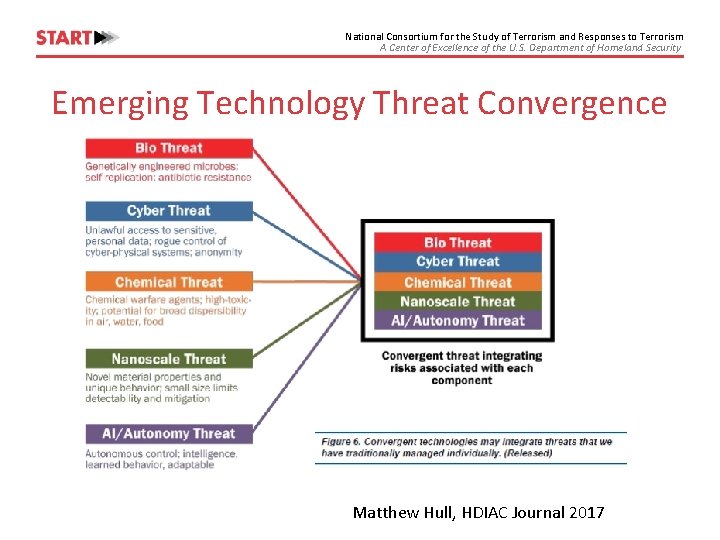
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Emerging Technology Threat Convergence Matthew Hull, HDIAC Journal 2017
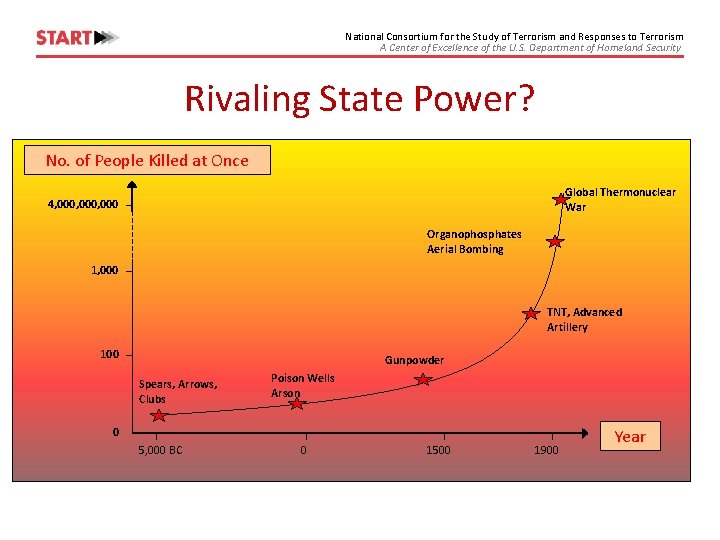
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Rivaling State Power? No. of People Killed at Once Global Thermonuclear War 4, 000, 000 Organophosphates Aerial Bombing 1, 000 TNT, Advanced Artillery 100 Gunpowder Spears, Arrows, Clubs Poison Wells Arson 0 5, 000 BC 0 1500 1900 Year
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Postscript: AI as the Enemy • Based on the ideas of Bostrum, Barret & Baum, Torres, etc. • Number of pathways by which fully sentient artificial consciousness (strong AI) could be achieved by 2030 -2050. – Likelihood that resulting AI could rapidly become a superintelligence • Convincing argument that the new intelligence would have goals that are at variance with those of the US (if not humanity in general) • Due to the knowledge processing power and exponentially greater speed of the new intelligence, would have little recourse after it comes into being – Robotics (together with other cyber, nano and biotech) systems would vastly empower the nascent AI => Early detection and control might be only avenues to preclude existential threat

National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Parting Thoughts
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Red Queen Effect? Let no one suppose that evolution will ever exempt us from struggles. 'You forget, ' said the Devil, with a chuckle, 'that I have been evolving too. ' - William Ralph Inge
National Consortium for the Study of Terrorism and Responses to Terrorism “The danger is not that we shall read the signals and indicators with too little skill; the danger is in a poverty of expectations – a routine obsession with a few dangers that may be familiar rather than likely. . The planner should think in subtler and more variegated terms and allow for a wider range of contingencies. ” - Thomas C. Schelling, foreword to Warning and Decision
National Consortium for the Study of Terrorism and Responses to Terrorism A Center of Excellence of the U. S. Department of Homeland Security Thank You Gary Ackerman gackerman@start. umd. edu (301) 405 -6656 www. start. umd. edu