Jericho Forum at RSA 2009 The disappearing perimeter

- Slides: 31
Jericho Forum at RSA 2009 The disappearing perimeter and The need for secure collaboration Bob West Founder and CEO, Echelon One, & Jericho Forum® Board Member
About the Jericho Forum § Original Vision and Mission: The Jericho Forum aims to drive and influence development of security standards that will meet future business needs These standards will: – Facilitate the secure interoperation, collaboration and commerce over open networks – Be based on a security architecture and design approach that responds to “de perimeterization”. § § § Today, globally, more than fifty blue chip user organisations, from all sectors, are working together to solve the problems posed by de perimeterization The Open Group hosts the Jericho Forum Everything the Jericho Forum publishes is free and open source: http: //www. opengroup. org/jericho/publications. htm
De perimeterization Trends and Signs § Key indicators that your organization is becoming de perimeterized: • Mismatch of the (legal) business border, the physical border and network perimeter • Business demanding to directly interconnect systems where collaborative relationships exist • Good network connectivity and access for all business / operational relationships • Distributed / shared applications across business / operational relationships • Applications that bypasses perimeter security
Business Requirements § Collaboration With staff, partners, JV’s, competitors, outsourcers, suppliers, customers etc. § Data needs to exist everywhere We should be concerned primarily with information loss not loss of the physical asset § Pervasive access is mandatory We should be worried about inappropriate access – not access itself
Derived Business Requirements Computing should: § Work anywhere § Any IP, anytime, anywhere (“Martini” model) § Be secure § Be self defending § Capable of identifying itself § Capable of identifying its user § Have a defined level of trust § Have trust based on environment Work the same irrespective of whether the device is on the Internet or the Intranet.
So who’s done it ? . . one example § BP declares war on the LAN By putting de perimeterization into practice, BP's technology director is hoping to make his company's computers more secure Energy group BP has shifted thousands of its employees off its LAN in an attempt to repel organised cyber criminals. Rather than rely on a strong network perimeter to secure its systems, BP has decided that these laptops have to be capable of coping with the worst that malicious hackers can throw at it, without relying on a network firewall. Ken Douglas, technology director of BP, told the UK Technology Innovation & Growth Forum in London on Monday that 18, 000 of BP's 85, 000 laptops now connect straight to the Internet even when they're in the office. http: //news. zdnet. co. uk/security/0, 1000000189, 39253439, 00. htm
So who’s done it ? . . and another § ICI set for big savings by switching internet traffic to DSL ICI is poised to sign a deal that could save it millions of pounds by allowing it to transfer non essential internet traffic from its wide area network. . . . …. . With non essential traffic removed, the Wan would be reserved for transferring business critical data. This would allow the chemicals company to run its network for far longer without upgrading its bandwidth. ICI's Wan connects its 30, 000 employees worldwide, but a recent internal audit of the firm's network usage found that 30% of traffic was browser based. Cliff Saran http: //www. computerweekly. com/Articles/Article. aspx? li. Article. ID=220002
So who’s done it ? . . and another § KLM to save £ 2 m through laptop self support plan KLM Royal Dutch Airlines expects to save £ 2 m in support costs by giving staff an allowance to buy and maintain their own laptops…… ……This project follows the path advocated by security user group the Jericho Forum, protecting data rather than perimeters, said van Deth. John Paul Kamath 16 July 2007 http: //www. computerweekly. com/Articles/Article. aspx
Short History of the Jericho Forum § In 2004 we began by alerting the industry to the effects and challenges that the impacts of de perimeterization poses to securing our networked systems § In 2007 we started developing a "collaboration" (Collaboration Oriented Architectures) framework, to show to architect effective secure solutions Today - we’ve gone a long way towards delivering these § In 2009 the next natural step is to raise awareness and understanding on how to collaborate safely and securely in "the cloud".
History a Bit More Detail § In 2004, Jericho Forum thought leaders asked the IT industry : – When corporate perimeters crumble due to business drivers demands for greater connectivity with collaborators over the Internet: • How do you secure it? • How do you collaborate in it? ” § § § We called the crumbling perimeters problem de-perimeterization We analyzed the architectural space that needs to be secured We wrote “position papers” on many of these, and have delivered two key deliverables: – Design Principles (Jericho Forum Commandments) • Questions that evaluate how far IT architecture meets the criteria for secure operation in a deperimeterized environment • The implications are that your IT systems should work the same way irrespective of whether you are inside or outside your corporate perimeter – Collaboration Oriented Architectures (COA) Framework • Identification of key components that need to be considered when designing a secure architecture • A practical framework showing an organization how to create the right architecture for secure business collaboration in their enterprise.
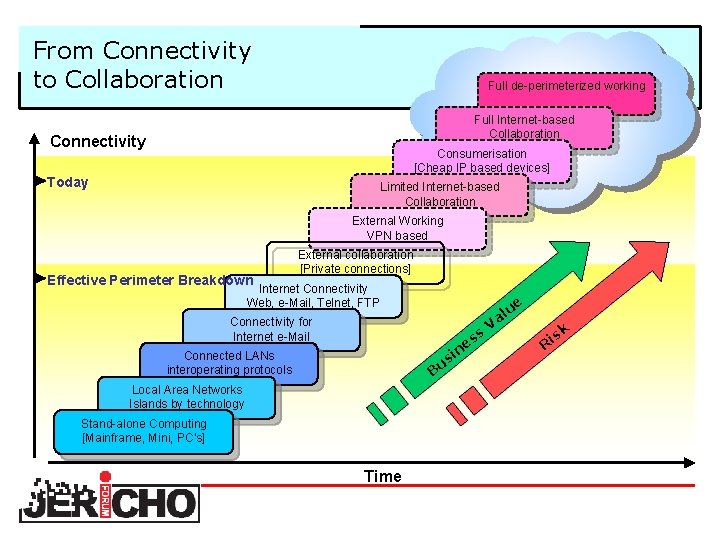
Connectivity § Computing history can be defined in terms in increasing connectivity over time: – – – starting from stand alone Through islands of LANs, then connected LANs Then Internet email Then Web Then collaboration using VPNs To today: collaboration over the Internet, for enterprise and consumerization § Tomorrow: – Full Internet based collaboration – Leading to full de perimeterized collaboration
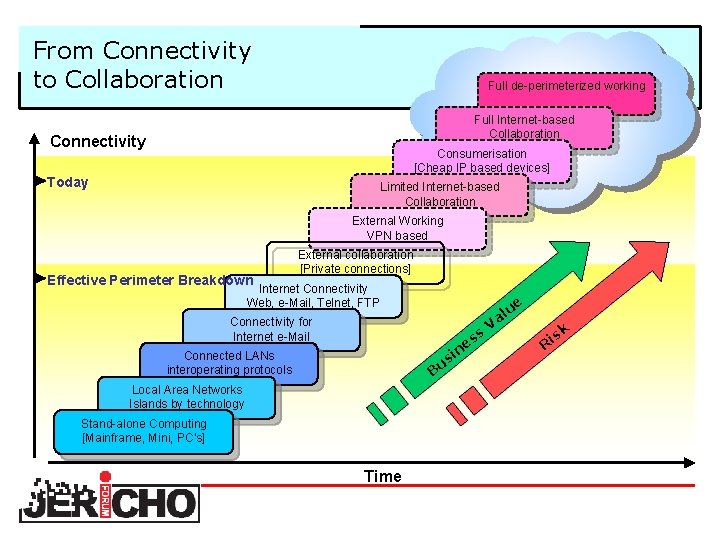
From Connectivity to Collaboration Full de-perimeterized working Full Internet-based Collaboration Connectivity Consumerisation [Cheap IP based devices] Today Limited Internet-based Collaboration External Working VPN based Effective Perimeter Breakdown External collaboration [Private connections] Internet Connectivity Web, e-Mail, Telnet, FTP Connectivity for Internet e-Mail ue s es n si u B Connected LANs interoperating protocols Local Area Networks Islands by technology Stand-alone Computing [Mainframe, Mini, PC’s] Time l Va k s Ri
Our 2 Key Deliverables to date § Design principles § Collaboration Oriented Architectures(COA) framework
Architecting for a Jericho Forum future § De perimeterization is what is happening to all networked computing systems § The Jericho Forum blueprint is the generic concept of how to respond the concept – our design principles supporting this is our “commandments” § Collaboration Oriented Architectures (COA) are a structure and components to enable de perimeterized working and collaboration § COA is not a single solution; it is deliberately plural
1 st Key Deliverable “Commandments” (Design Principles) paper § The Jericho Forum “Commandments” are freely available from the Jericho Forum Website http: //www. jerichoforum. org/publications. htm
An Introduction to the Commandments The design principles: Our benchmark by which concepts, solutions, standards and systems can be assessed and measured as meeting de perimeterization challenges § Comprise 11 “commandments” – – – Fundamentals (3) Surviving in a hostile world (2) The need for trust (2) Identity, management and federation (1) Access to data (3)
Fundamentals (1) 1. The scope and level of protection must be specific and appropriate to the asset at risk § Business demands that security enables business agility and is cost effective. § Whereas boundary firewalls may continue to provide basic network protection, individual systems and data will need to be capable of protecting themselves. § In general, it’s easier to protect an asset the closer protection is provided.
Fundamentals (2) 2. Security mechanisms must be pervasive, simple, scalable and easy to manage § Unnecessary complexity is a threat to good security. § Coherent security principles are required which span all tiers of the architecture. § Security mechanisms must scale: – from small objects to large objects. § To be both simple and scalable, interoperable security “building blocks” need to be capable of being combined to provide the required security mechanisms.
Fundamentals (3) 3. Assume context at your peril § Security solutions designed for one environment may not be transferable to work in another: – thus it is important to understand the limitations of any security solution. § Problems, limitations and issues can come from a variety of sources, including: – Geographic – Legal – Technical – Acceptability of risk, etc.
Surviving in a hostile world 4. Devices and applications must communicate using open, secure protocols. 5. All devices must be capable of maintaining their security policy on an untrusted network.
The need for trust 6. All people, processes, technology must have declared and transparent levels of trust for any transaction to take place. 7. Mutual trust assurance levels must be determinable.
Identity, Management and Federation 8. Authentication, authorisation and accountability must interoperate / exchange outside of your locus / area of control.
Access to data 9. Access to data should be controlled by security attributes of the data itself. 10. Data privacy (and security of any asset of sufficiently high value) requires a segregation of duties/privileges. 11. By default, data must be appropriately secured both in storage and in transit.
2 nd Key Deliverable Collaboration Oriented Architectures (COA) fwk § The Collaboration Oriented Architectures framework lays out a set of design principles focusing on – Protection against security challenges caused by increased collaboration – Leveraging the business potential offered by Web 2. 0 and other externalization technologies This practical framework is geared to showing each organization how to architect for safe business collaboration in a way that fits individual needs § Implementing COA builds upon existing standards and practices to enable effective and secure collaboration § Developing a set of best practice principles addressing secure collaboration in the cloud is the obvious – and indeed important next goal for us §
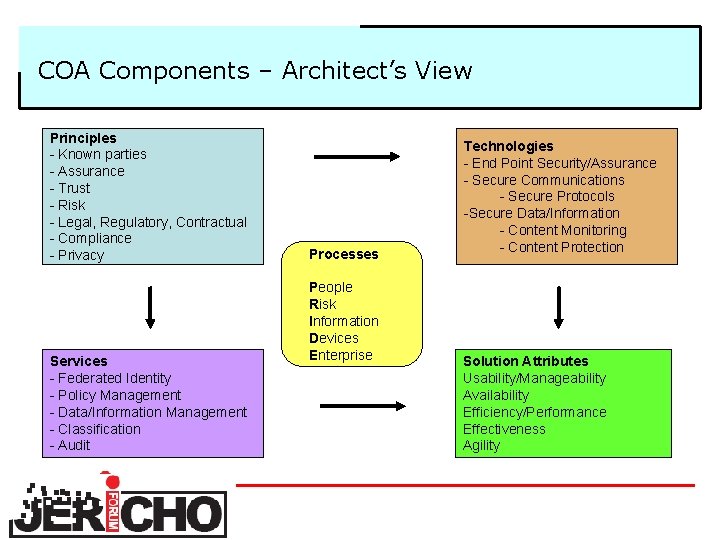
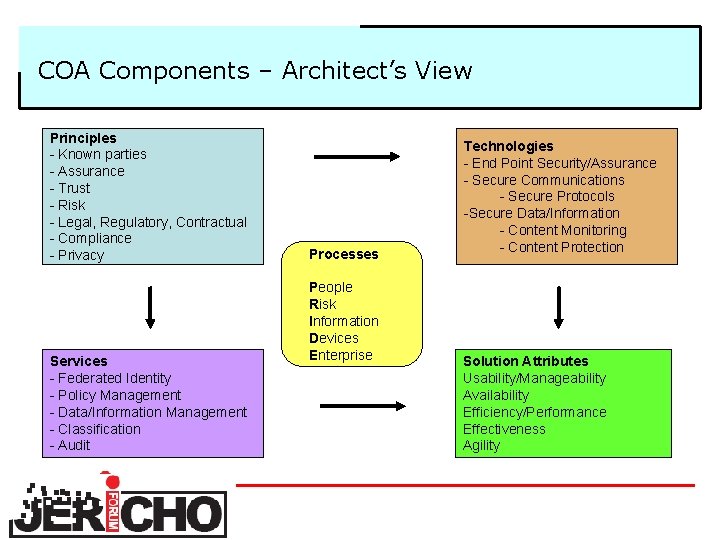
COA Components – Architect’s View Principles - Known parties - Assurance - Trust - Risk - Legal, Regulatory, Contractual - Compliance - Privacy Services - Federated Identity - Policy Management - Data/Information Management - Classification - Audit Processes People Risk Information Devices Enterprise Technologies - End Point Security/Assurance - Secure Communications - Secure Protocols -Secure Data/Information - Content Monitoring - Content Protection Solution Attributes Usability/Manageability Availability Efficiency/Performance Effectiveness Agility
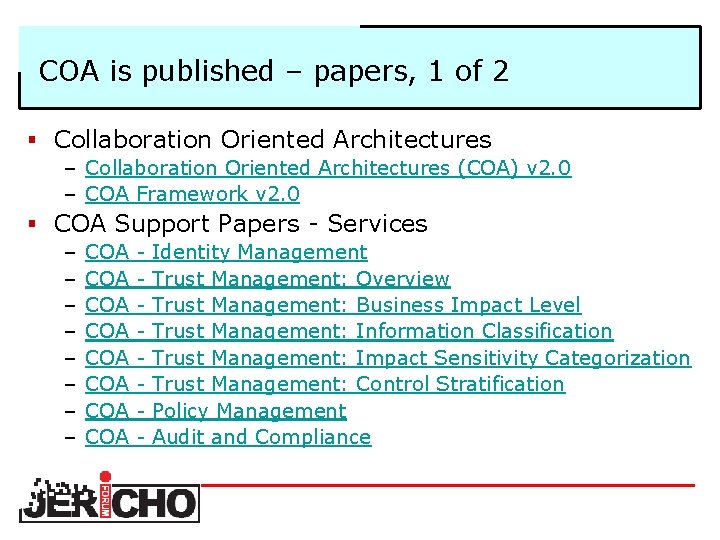
COA is published – papers, 1 of 2 § Collaboration Oriented Architectures – Collaboration Oriented Architectures (COA) v 2. 0 – COA Framework v 2. 0 § COA Support Papers Services – – – – COA COA Identity Management Trust Management: Overview Trust Management: Business Impact Level Trust Management: Information Classification Trust Management: Impact Sensitivity Categorization Trust Management: Control Stratification Policy Management Audit and Compliance
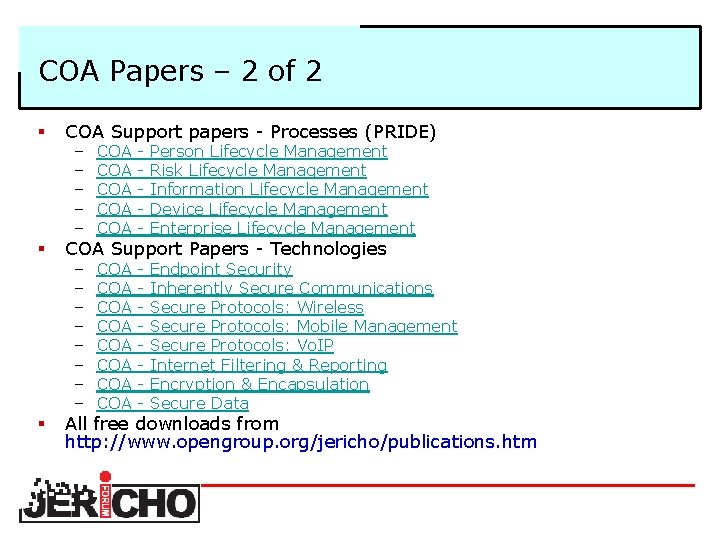
COA Papers – 2 of 2 § COA Support papers Processes (PRIDE) § COA Support Papers Technologies § All free downloads from http: //www. opengroup. org/jericho/publications. htm – – – COA COA COA Person Lifecycle Management Risk Lifecycle Management Information Lifecycle Management Device Lifecycle Management Enterprise Lifecycle Management – – – – COA COA Endpoint Security Inherently Secure Communications Secure Protocols: Wireless Secure Protocols: Mobile Management Secure Protocols: Vo. IP Internet Filtering & Reporting Encryption & Encapsulation Secure Data
Types of Collaboration § One size doesn’t fit all Each organization needs: – A clear vision of their business objectives – Necessary services – communication, conferencing, workflow, management, etc. – The collaboration oriented architecture they need to design to securely meet those objectives § COA is a framework geared to showing an organisation how to create the right architecture for secure business collaboration.
The future § Many and in some cases most network security perimeters will disappear § Like it or not de perimeterization is happening § The business and operational drivers will already exist within your organisation § It's already started and it's only a matter of: – how fast, – how soon and – whether you decide to control it § And the next challenge – Secure collaboration in Cloud Computing
Recalling from 2004 to today … § In 2004 we began by alerting the industry to the impact and challenges of de perimeterization. We’re still doing that, but it’s now well established. § In 2007 we started developing a "collaboration" framework (COA) to show to architect effective solutions. We’ve delivered it. § In 2009 the next natural step is to raise awareness and understanding on how to collaborate safely and securely in "the cloud". New Vision: To enable increased confidence and operational efficiencies in collaboration and commerce for all stakeholders in the context of emerging cloud models Same Mission: Act as a catalyst to accelerate the achievement of the collective vision www. jerichoforum. org
