Connection Oriented Mobility Using Edge Point Interactivity Sandeep
Connection Oriented Mobility Using Edge Point Interactivity Sandeep Davu Networking and Media Communications Research Laboratories Computer Science Department Kent State University
AGENDA • • Problem Statement Related Work Proposed Scheme -- IPMN Implementation 2 -Layer IPMN Performance Analysis Modeling of 3 -Layer IPMN Conclusion
AGENDA • Problem Statement – Mobility Management – Short Comings of current network – More higher layer specific approach needed • • Related Work Proposed Scheme Performance Analysis Conclusion
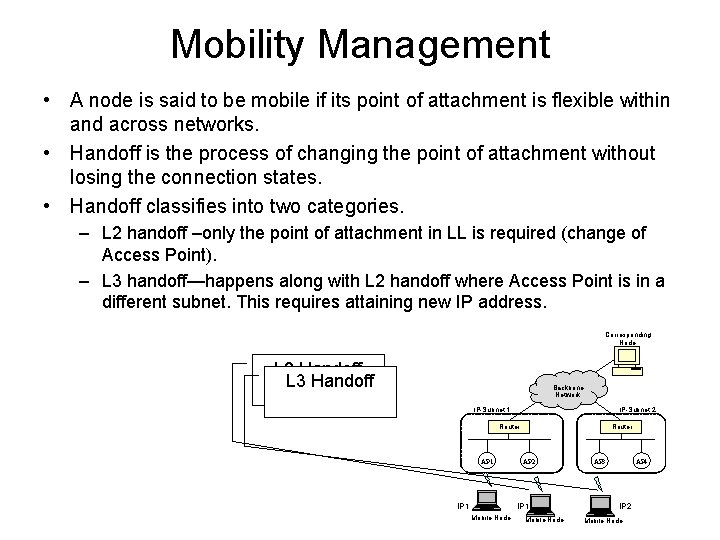
Mobility Management • A node is said to be mobile if its point of attachment is flexible within and across networks. • Handoff is the process of changing the point of attachment without losing the connection states. • Handoff classifies into two categories. – L 2 handoff –only the point of attachment in LL is required (change of Access Point). – L 3 handoff—happens along with L 2 handoff where Access Point is in a different subnet. This requires attaining new IP address. Corresponding Node L 2 Handoff L 3 Handoff Backbone Network IP-Subnet 1 IP-Subnet 2 Router AP 1 IP 1 Router AP 2 IP 1 Mobile Node AP 3 AP 4 IP 2 Mobile Node
Short comings of network • OS and network architecture did not envision wireless and mobility. • Error Prone nature of the wireless links – not as rigid as Ethernet. • State full nature of connection oriented networks – robust retransmissions. • A transport layer connection is identified by a four tuple <source address, source port, destination address, destination port> maintained at either end points. • A L 3 handoff requires a network address change for the Mobile Node rendering the current TCP connection useless. • Unexpected disconnections and moving end points. • Rapidly Converging 3 G and 4 G networks and strong need to have seamless mobility • Is there an effective way to handle this? ? ?
Protocol Re-organization • Principle – Most network complexities are better handled at higher layers and end-systems. • Protocol extension needed for mobility and justifies the design principle employed. • Mobility in wireless networks (802. 11 MAC) involves more than one network layer to perform a handoff. • cross-layer interaction between networking layers to achieve high performance loss-free handoffs. • Event based approach with no timer latencies to kick off actions.
Are current approaches not enough? ? ? • There are several approaches proposed which address one particular area of mobility • Solutions proposed in one layer (either IP or TCP). • Interoperability between layers was hindered. • Indirect performance implications even if the problem was addressed directly.
AGENDA • Problem Statement • Related Work – Network Layer Solutions – Higher Layer Solutions • Mobility Management • Performance Tuning • Proposed Scheme • Performance Analysis • Conclusion
Network Layer Solutions • Mobile IP provided the first effective crack in handling mobility. • Route Optimization provides a solution for triangulation problem. • Hint based handoffs used triggers from lower layers as hints to perform fast handoff. • The RAT (Reverse Address Translation) architecture, based on the network address translation (NAT) protocol, uses packet redirection service between CH and MN to support IP mobility.
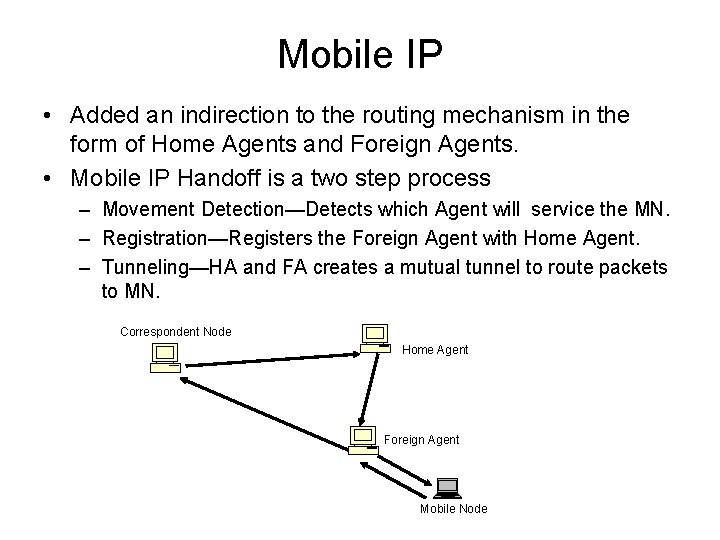
Mobile IP • Added an indirection to the routing mechanism in the form of Home Agents and Foreign Agents. • Mobile IP Handoff is a two step process – Movement Detection—Detects which Agent will service the MN. – Registration—Registers the Foreign Agent with Home Agent. – Tunneling—HA and FA creates a mutual tunnel to route packets to MN. Correspondent Node Home Agent Foreign Agent Mobile Node
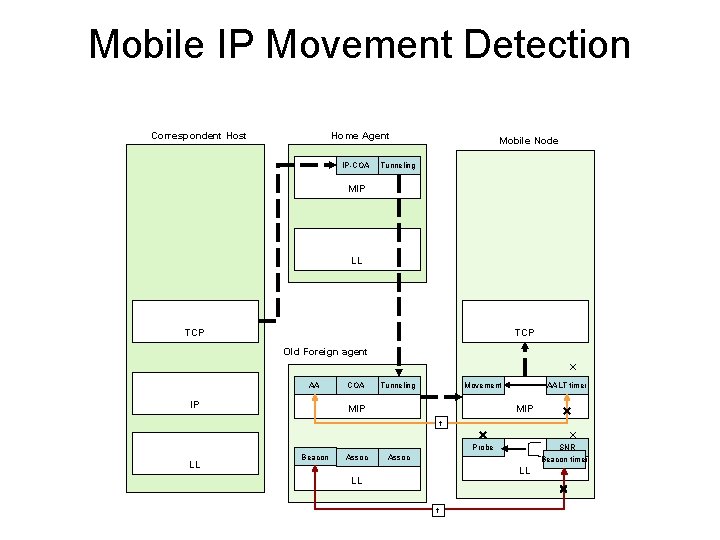
Mobile IP Movement Detection Correspondent Host Home Agent IP-COA Mobile Node Tunneling MIP LL TCP Old Foreign agent AA IP COA Tunneling Movement MIP AALT timer MIP t Probe LL Beacon Assoc SNR Beacon timer Assoc LL LL t
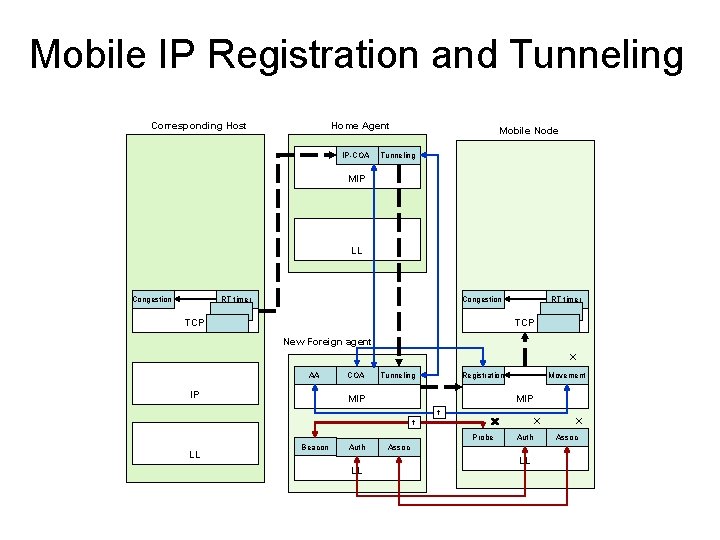
Mobile IP Registration and Tunneling Corresponding Host Home Agent IP-COA Mobile Node Tunneling MIP LL Congestion RT timer Congestion TCP RT timer TCP New Foreign agent AA IP COA Tunneling Registration MIP Movement MIP t t Probe LL Beacon Auth LL Auth Assoc LL Assoc
Higher Level Solutions • Split Connection Approach – I-TCP was a split approach to the end-to-end connection where the connection was split at the Base Station or Access Point. – MSOCKS[8] achieves connection redirection using split connection proxy. • End-to-End Approach – TCP-R is based on an idea- same as ours, renewing the connection to handle the new IP address. • Performance Tuning – Freeze TCP freezes the connection during the course of a handoff by advertising a zero window at the MN.
AGENDA • • Problem Statement Related Work Network Layer Solutions Proposed Scheme – IPMN Architecture – 2 Layer implementation (experiment and performance) Performance Analysis IPMN 3 -Layer Modeling • Conclusion
Our Scheme • Uses rapid cross layer interactivity to provide high performance connection oriented mobility support. • Based on the Interactive Transparent Networking (In. Tra. N) paradigm – focused on ordered cross layer interactivity, developed recently in the Media. Net Lab. • Interactive Protocol for Mobile Networks (IPMN) allows event based access to protocol states even by network layer processes or even by L 7 processes. • This mobility solution does not require any functional change in the classical TCP/IP network, can avoid FA or HA (thus the need of an infrastructure!), can avoid triangulation, is loss-free, and above all offer much faster handoff.
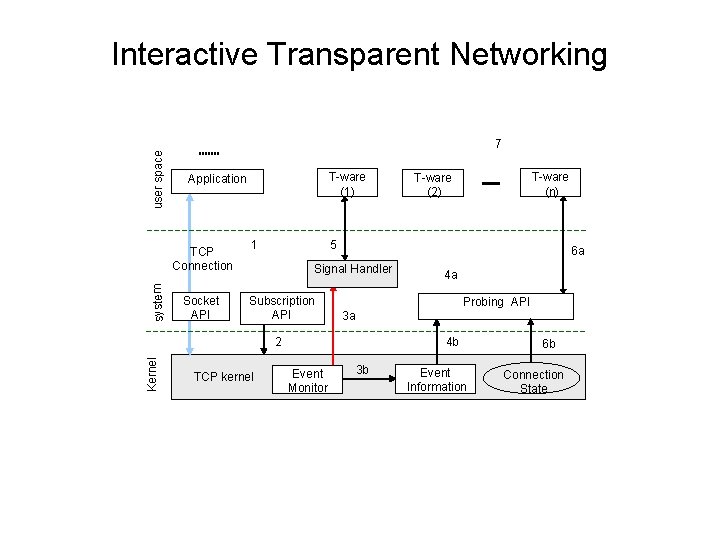
user space Interactive Transparent Networking 7 TCP Connection system T-ware (1) Application Socket API 1 5 6 a Signal Handler Subscription API Kernel 4 a Probing API 3 a 4 b 2 TCP kernel T-ware (n) T-ware (2) Event Monitor 3 b Event Information 6 b Connection State
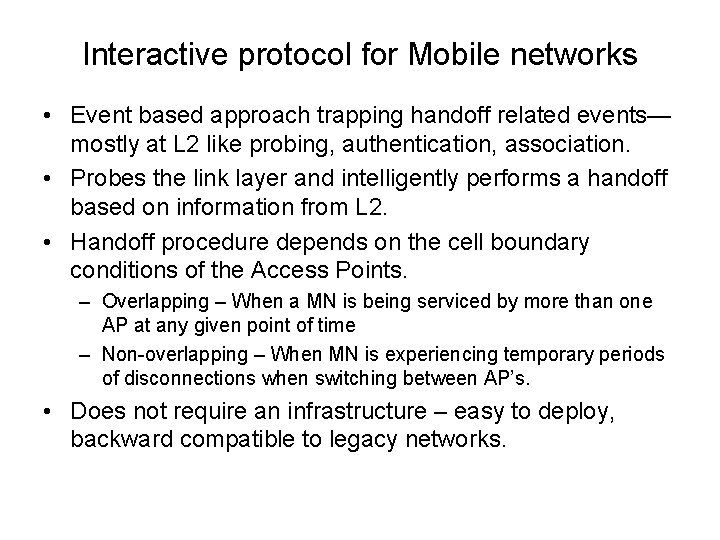
Interactive protocol for Mobile networks • Event based approach trapping handoff related events— mostly at L 2 like probing, authentication, association. • Probes the link layer and intelligently performs a handoff based on information from L 2. • Handoff procedure depends on the cell boundary conditions of the Access Points. – Overlapping – When a MN is being serviced by more than one AP at any given point of time – Non-overlapping – When MN is experiencing temporary periods of disconnections when switching between AP’s. • Does not require an infrastructure – easy to deploy, backward compatible to legacy networks.
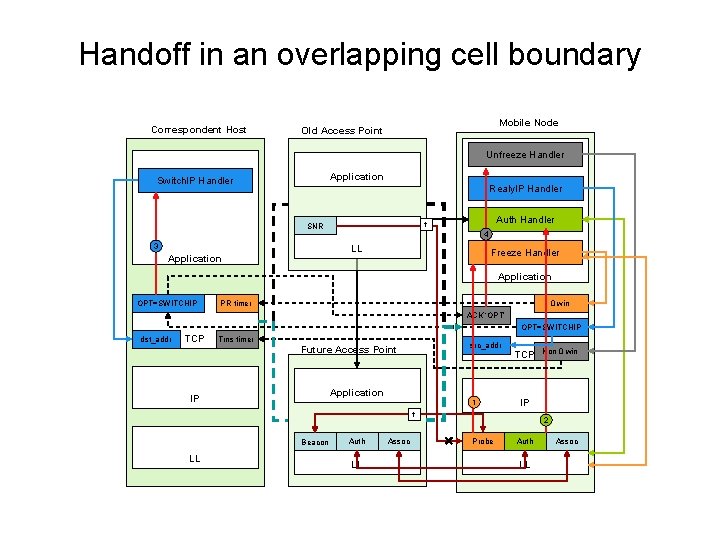
Handoff in an overlapping cell boundary Correspondent Host Mobile Node Old Access Point Unfreeze Handler Application Switch. IP Handler Realy. IP Handler 3 Auth Handler t SNR 4 LL Application Freeze Handler Application OPT=SWITCHIP PR timer 0 win ACK ‘OPT’ OPT=SWITCHIP dst_addr TCP Trns timer src_addr Future Access Point Application IP 1 TCP IP t Beacon LL Auth LL Assoc Non 0 win 2 Probe Auth LL Assoc
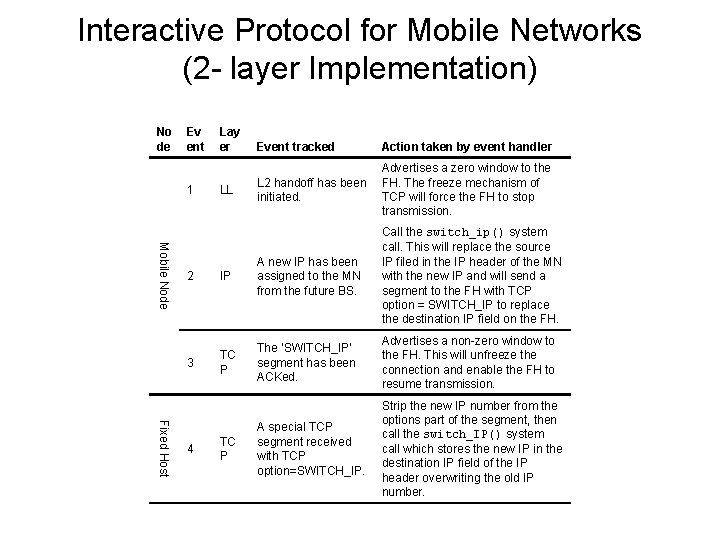
Interactive Protocol for Mobile Networks (2 - layer Implementation) No de Ev ent 1 Lay er LL Mobile Node Event tracked Action taken by event handler L 2 handoff has been initiated. Advertises a zero window to the FH. The freeze mechanism of TCP will force the FH to stop transmission. Call the switch_ip() system call. This will replace the source IP filed in the IP header of the MN with the new IP and will send a segment to the FH with TCP option = SWITCH_IP to replace the destination IP field on the FH. Fixed Host 2 IP A new IP has been assigned to the MN from the future BS. 3 TC P The ‘SWITCH_IP’ segment has been ACKed. Advertises a non-zero window to the FH. This will unfreeze the connection and enable the FH to resume transmission. A special TCP segment received with TCP option=SWITCH_IP. Strip the new IP number from the options part of the segment, then call the switch_IP() system call which stores the new IP in the destination IP field of the IP header overwriting the old IP number. 4 TC P
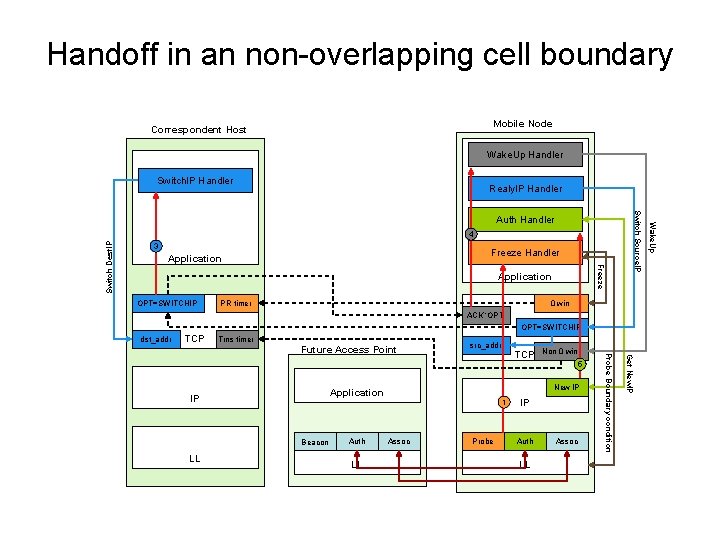
Handoff in an non-overlapping cell boundary Mobile Node Correspondent Host Wake. Up Handler Switch. IP Handler Realy. IP Handler Freeze Switch Dest. IP Freeze Handler Application OPT=SWITCHIP PR timer 0 win ACK ‘OPT’ OPT=SWITCHIP dst_addr TCP Trns timer src_addr Non 0 win 5 Beacon LL New IP Application IP Auth LL 1 Assoc Probe IP Auth LL Assoc Get New. IP TCP Probe Boundary condition Future Access Point Wake. Up 4 3 Switch Source. IP Auth Handler
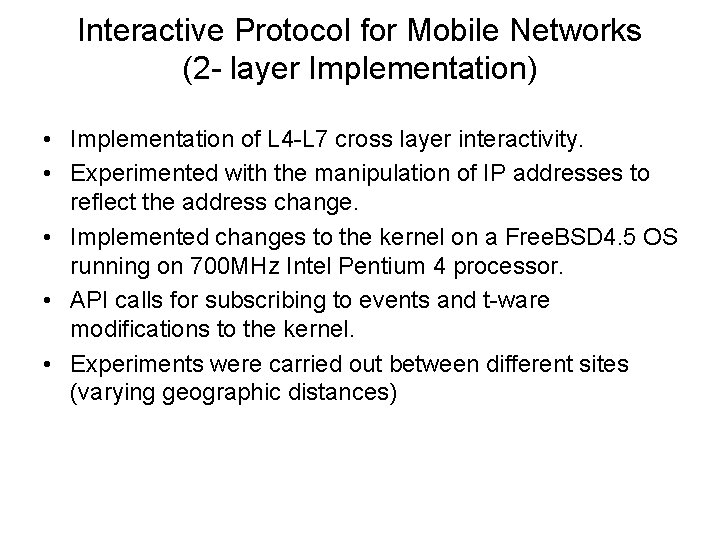
Interactive Protocol for Mobile Networks (2 - layer Implementation) • Implementation of L 4 -L 7 cross layer interactivity. • Experimented with the manipulation of IP addresses to reflect the address change. • Implemented changes to the kernel on a Free. BSD 4. 5 OS running on 700 MHz Intel Pentium 4 processor. • API calls for subscribing to events and t-ware modifications to the kernel. • Experiments were carried out between different sites (varying geographic distances)
Interactive Protocol for Mobile Networks (2 - layer Implementation)
AGENDA • • • Problem Statement Related Work Network Layer Solutions Proposed Scheme Performance Analysis – Experiment Setup – Performance results • Modeling 3 -Layer Handoff. • Conclusion
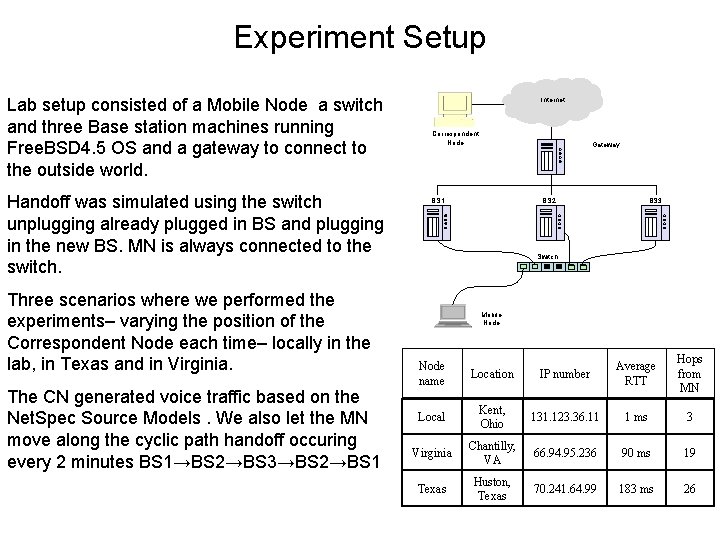
Experiment Setup Lab setup consisted of a Mobile Node a switch and three Base station machines running Free. BSD 4. 5 OS and a gateway to connect to the outside world. Handoff was simulated using the switch unplugging already plugged in BS and plugging in the new BS. MN is always connected to the switch. Three scenarios where we performed the experiments– varying the position of the Correspondent Node each time– locally in the lab, in Texas and in Virginia. The CN generated voice traffic based on the Net. Spec Source Models. We also let the MN move along the cyclic path handoff occuring every 2 minutes BS 1→BS 2→BS 3→BS 2→BS 1 Internet Correspondent Node Gateway BS 1 BS 2 BS 3 Switch Mobile Node IP number Average RTT Hops from MN Kent, Ohio 131. 123. 36. 11 1 ms 3 Virginia Chantilly, VA 66. 94. 95. 236 90 ms 19 Texas Huston, Texas 70. 241. 64. 99 183 ms 26 Node name Location Local
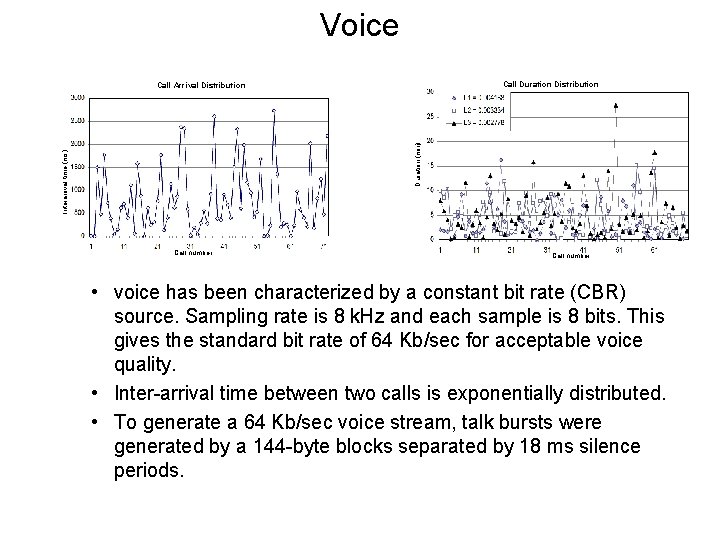
Voice Call Duration Distribution Interarrival time (ms) Duration (min) Call Arrival Distribution Call number • voice has been characterized by a constant bit rate (CBR) source. Sampling rate is 8 k. Hz and each sample is 8 bits. This gives the standard bit rate of 64 Kb/sec for acceptable voice quality. • Inter-arrival time between two calls is exponentially distributed. • To generate a 64 Kb/sec voice stream, talk bursts were generated by a 144 -byte blocks separated by 18 ms silence periods.
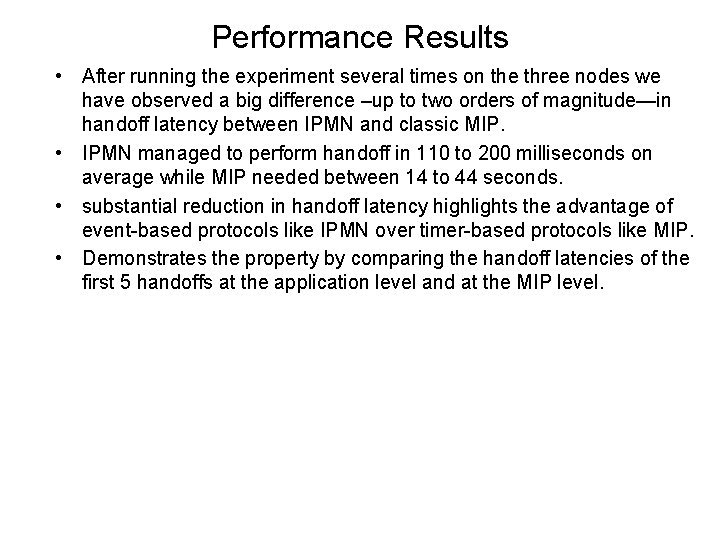
Performance Results • After running the experiment several times on the three nodes we have observed a big difference –up to two orders of magnitude—in handoff latency between IPMN and classic MIP. • IPMN managed to perform handoff in 110 to 200 milliseconds on average while MIP needed between 14 to 44 seconds. • substantial reduction in handoff latency highlights the advantage of event-based protocols like IPMN over timer-based protocols like MIP. • Demonstrates the property by comparing the handoff latencies of the first 5 handoffs at the application level and at the MIP level.
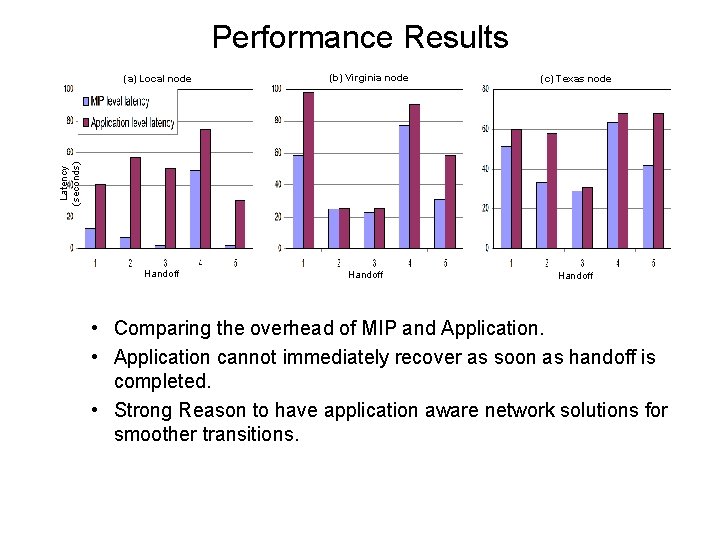
Performance Results (b) Virginia node (c) Texas node Latency (seconds) (a) Local node Handoff • Comparing the overhead of MIP and Application. • Application cannot immediately recover as soon as handoff is completed. • Strong Reason to have application aware network solutions for smoother transitions.
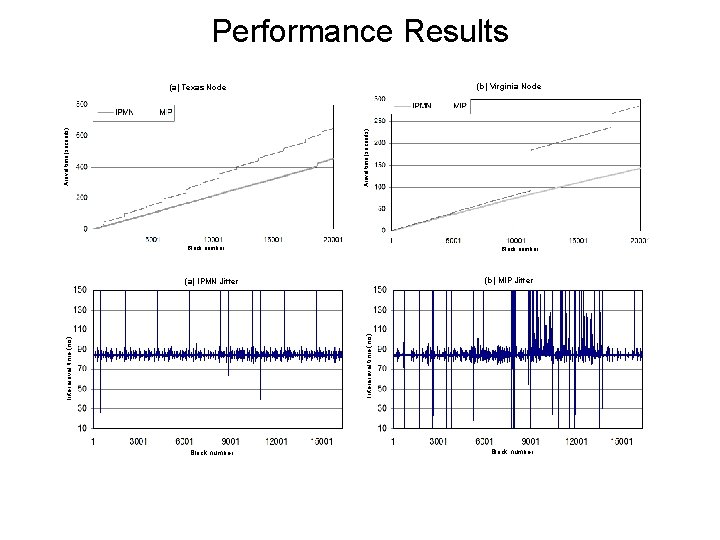
Performance Results (b) Virginia Node Arrival time (seconds) (a) Texas Node Block number (b) MIP Jitter Interarrival time (ms) (a) IPMN Jitter Block number
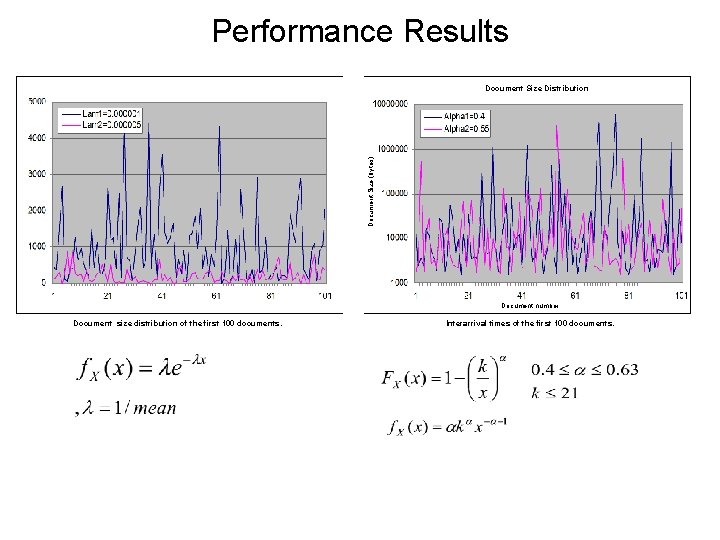
Performance Results Document Size (bytes) Document Size Distribution Document number Document size distribution of the first 100 documents. Interarrival times of the first 100 documents.
Performance Results
AGENDA • • Problem Statement Related Work Network Layer Solutions Proposed Scheme Performance Analysis Modeling 3 -Layer Handoff Performance Analysis Conclusion
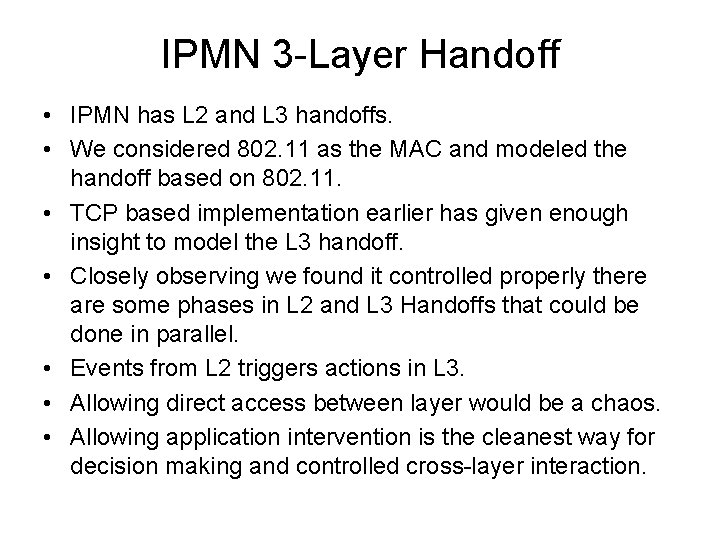
IPMN 3 -Layer Handoff • IPMN has L 2 and L 3 handoffs. • We considered 802. 11 as the MAC and modeled the handoff based on 802. 11. • TCP based implementation earlier has given enough insight to model the L 3 handoff. • Closely observing we found it controlled properly there are some phases in L 2 and L 3 Handoffs that could be done in parallel. • Events from L 2 triggers actions in L 3. • Allowing direct access between layer would be a chaos. • Allowing application intervention is the cleanest way for decision making and controlled cross-layer interaction.
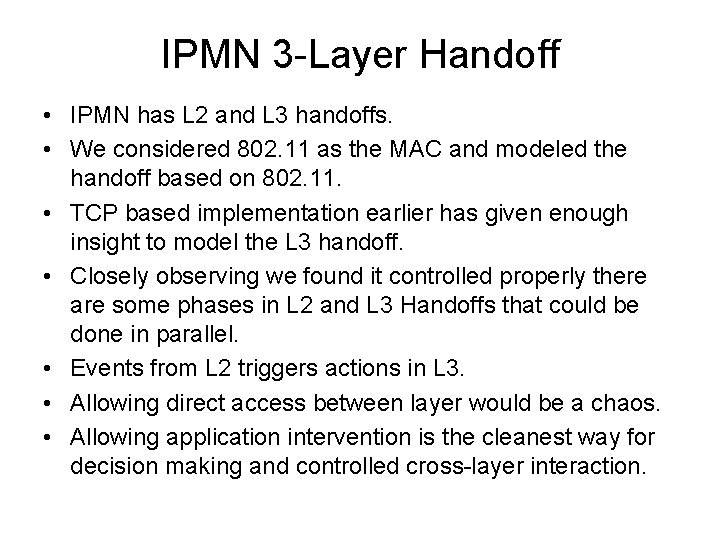
IPMN 3 -Layer Handoff • IPMN has L 2 and L 3 handoffs. • We considered 802. 11 as the MAC and modeled the handoff based on 802. 11. • TCP based implementation earlier has given enough insight to model the L 3 handoff. • Closely observing we found it controlled properly there are some phases in L 2 and L 3 Handoffs that could be done in parallel. • Events from L 2 triggers actions in L 3. • Allowing direct access between layer would be a chaos. • Allowing application intervention is the cleanest way for decision making and controlled cross-layer interaction.
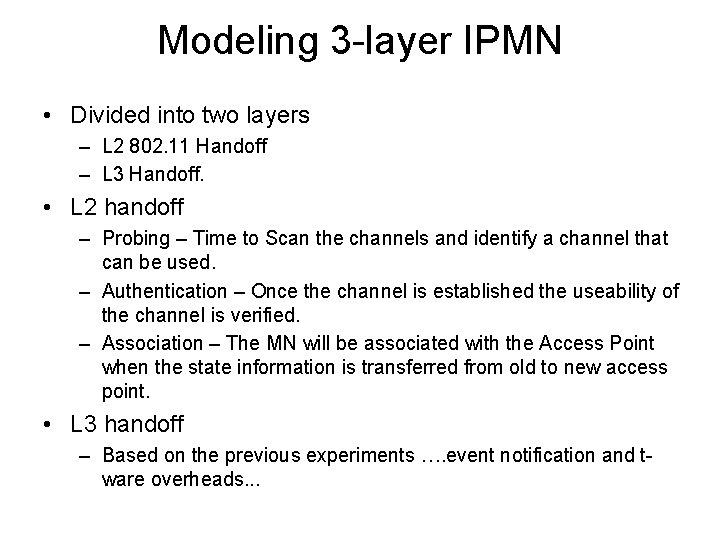
Modeling 3 -layer IPMN • Divided into two layers – L 2 802. 11 Handoff – L 3 Handoff. • L 2 handoff – Probing – Time to Scan the channels and identify a channel that can be used. – Authentication – Once the channel is established the useability of the channel is verified. – Association – The MN will be associated with the Access Point when the state information is transferred from old to new access point. • L 3 handoff – Based on the previous experiments …. event notification and tware overheads. . .
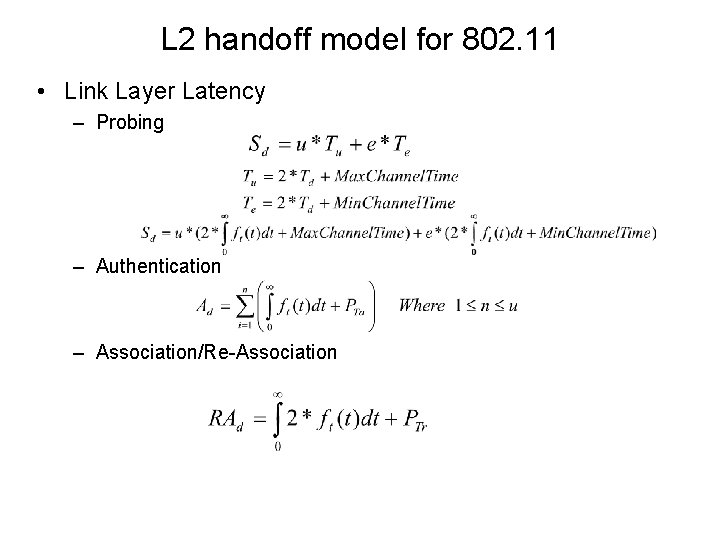
L 2 handoff model for 802. 11 • Link Layer Latency – Probing – Authentication – Association/Re-Association
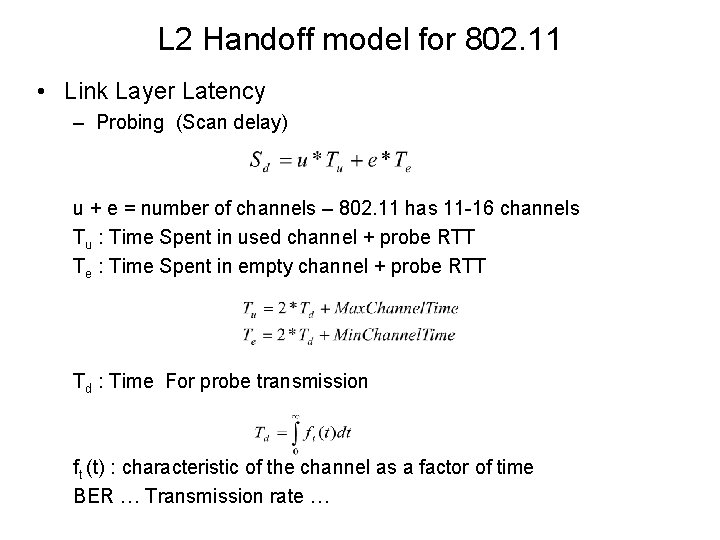
L 2 Handoff model for 802. 11 • Link Layer Latency – Probing (Scan delay) u + e = number of channels – 802. 11 has 11 -16 channels Tu : Time Spent in used channel + probe RTT Te : Time Spent in empty channel + probe RTT Td : Time For probe transmission ft (t) : characteristic of the channel as a factor of time BER … Transmission rate …
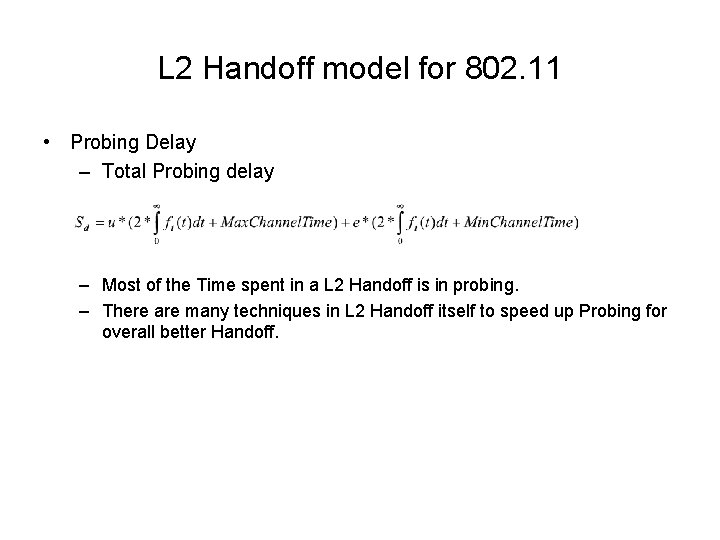
L 2 Handoff model for 802. 11 • Probing Delay – Total Probing delay – Most of the Time spent in a L 2 Handoff is in probing. – There are many techniques in L 2 Handoff itself to speed up Probing for overall better Handoff.
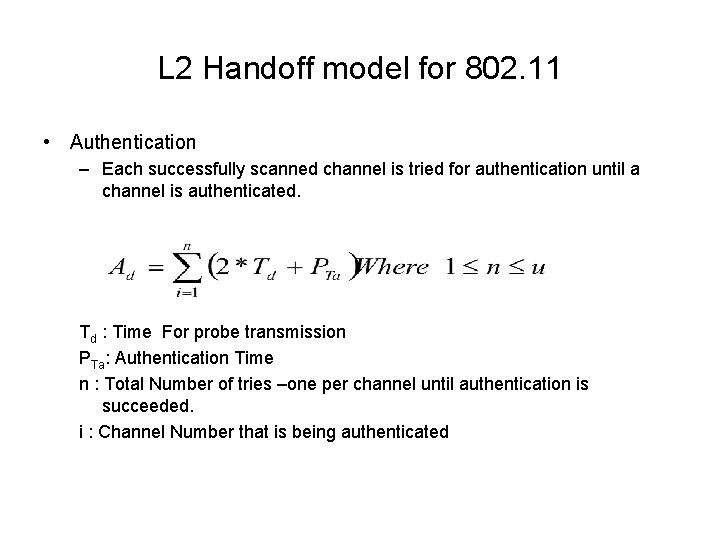
L 2 Handoff model for 802. 11 • Authentication – Each successfully scanned channel is tried for authentication until a channel is authenticated. Td : Time For probe transmission PTa: Authentication Time n : Total Number of tries –one per channel until authentication is succeeded. i : Channel Number that is being authenticated
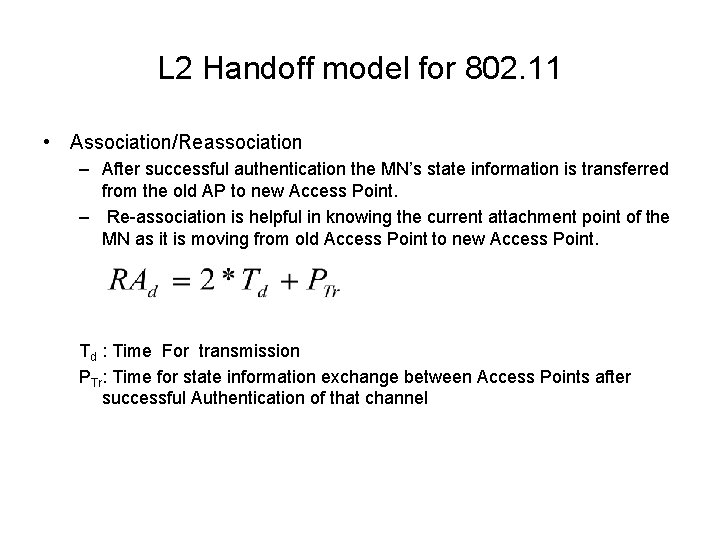
L 2 Handoff model for 802. 11 • Association/Reassociation – After successful authentication the MN’s state information is transferred from the old AP to new Access Point. – Re-association is helpful in knowing the current attachment point of the MN as it is moving from old Access Point to new Access Point. Td : Time For transmission PTr: Time for state information exchange between Access Points after successful Authentication of that channel
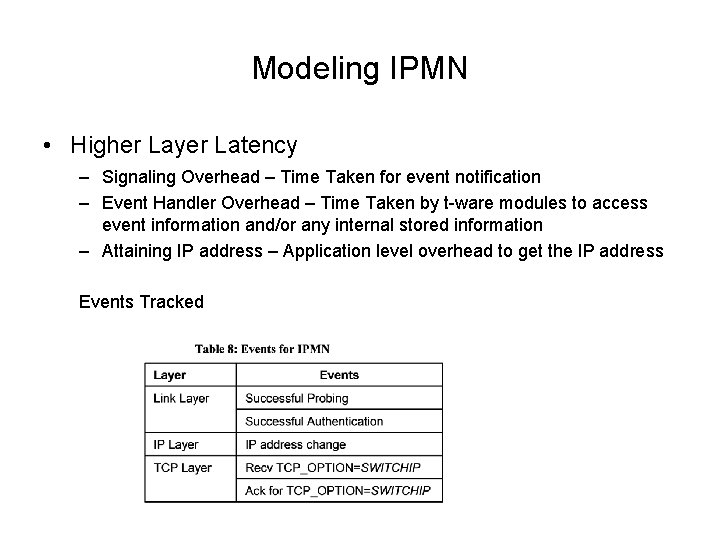
Modeling IPMN • Higher Layer Latency – Signaling Overhead – Time Taken for event notification – Event Handler Overhead – Time Taken by t-ware modules to access event information and/or any internal stored information – Attaining IP address – Application level overhead to get the IP address Events Tracked
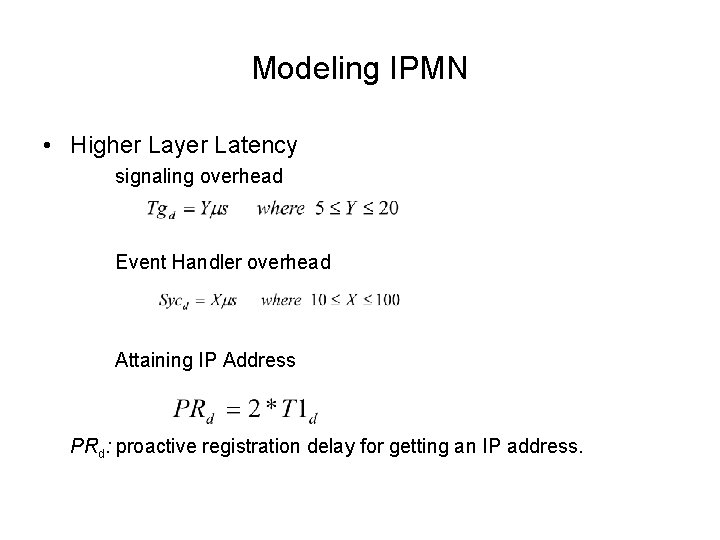
Modeling IPMN • Higher Layer Latency signaling overhead Event Handler overhead Attaining IP Address PRd: proactive registration delay for getting an IP address.
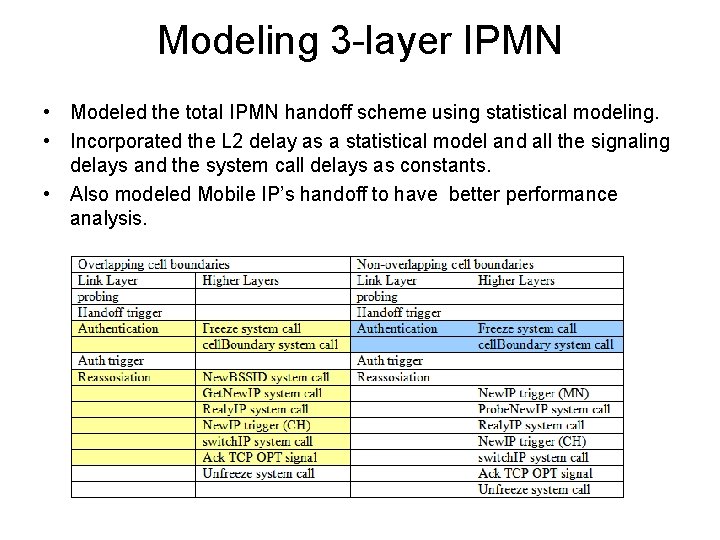
Modeling 3 -layer IPMN • Modeled the total IPMN handoff scheme using statistical modeling. • Incorporated the L 2 delay as a statistical model and all the signaling delays and the system call delays as constants. • Also modeled Mobile IP’s handoff to have better performance analysis.
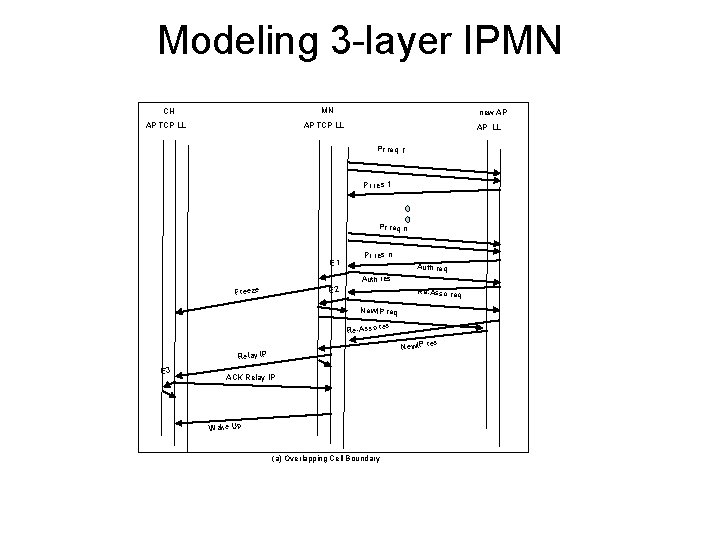
Modeling 3 -layer IPMN MN CH new AP AP TCP LL AP LL Pr req 1 Pr res 1 Pr req n E 1 Pr res n Auth req Auth res E 2 Freeze Re-Asso req New. IP req Re-Asso res New. IP Relay IP E 3 ACK Relay IP Wake Up (a) Overlapping Cell Boundary res
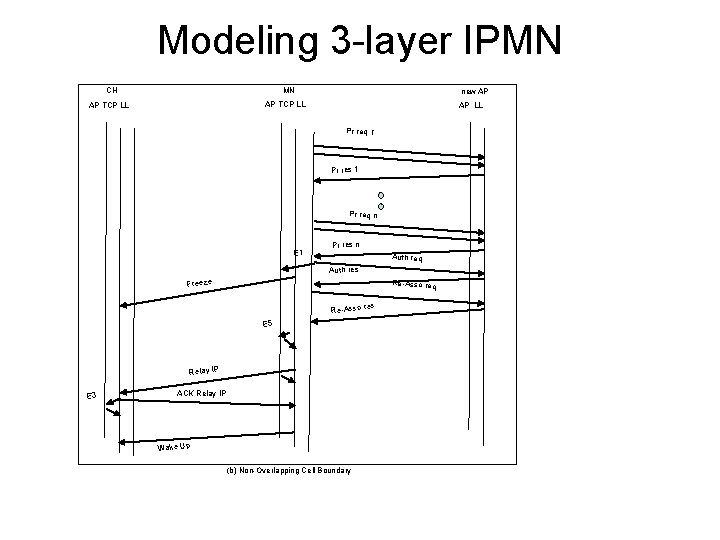
Modeling 3 -layer IPMN MN CH new AP AP TCP LL AP LL Pr req 1 Pr res 1 Pr req n E 1 Pr res n Auth req Auth res Freeze Re-Asso req Re-Asso E 5 Relay IP E 3 ACK Relay IP Wake Up (b) Non-Overlapping Cell Boundary res
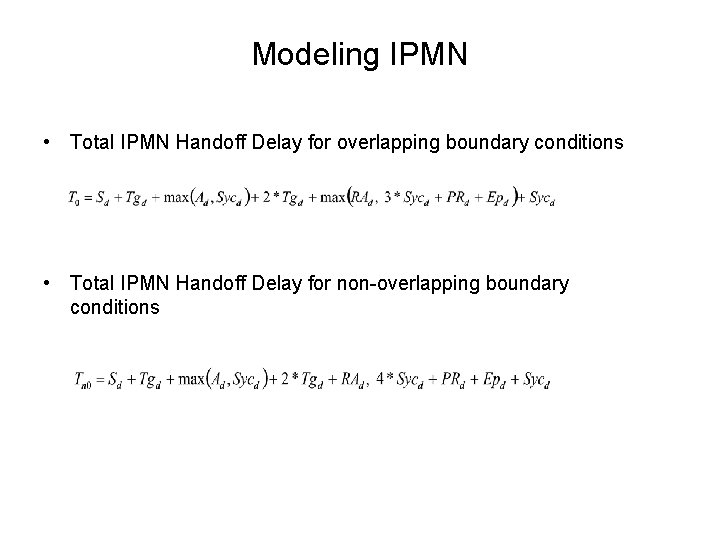
Modeling IPMN • Total IPMN Handoff Delay for overlapping boundary conditions • Total IPMN Handoff Delay for non-overlapping boundary conditions
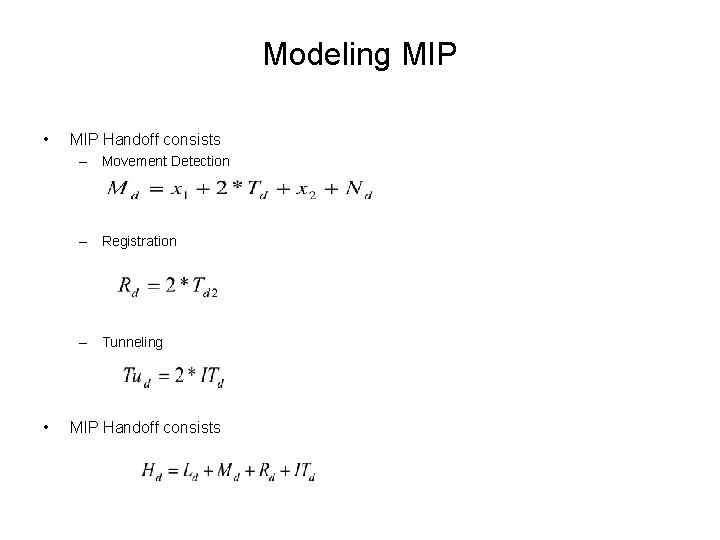
Modeling MIP • MIP Handoff consists – Movement Detection – Registration – Tunneling • MIP Handoff consists
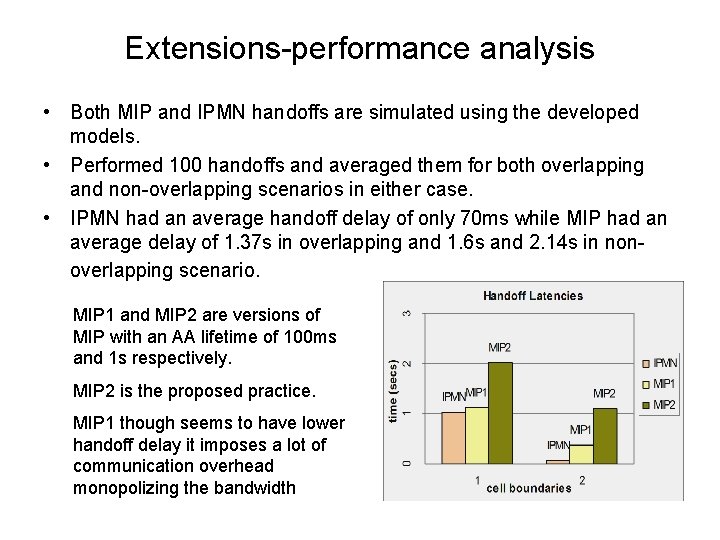
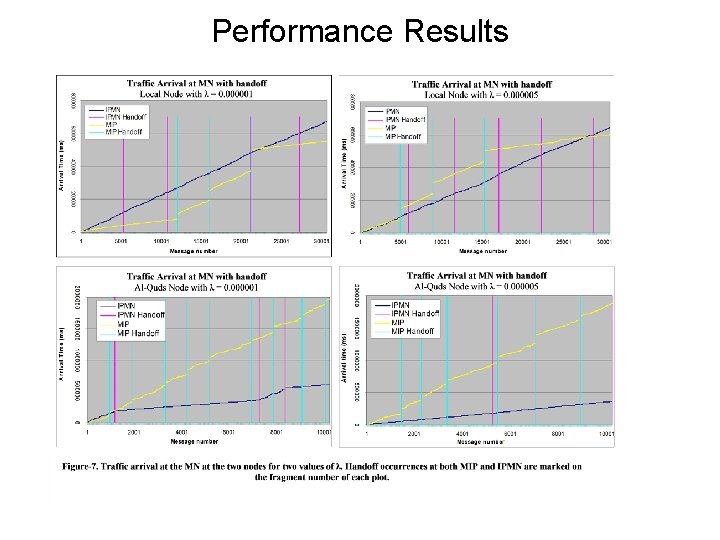
Extensions-performance analysis • Both MIP and IPMN handoffs are simulated using the developed models. • Performed 100 handoffs and averaged them for both overlapping and non-overlapping scenarios in either case. • IPMN had an average handoff delay of only 70 ms while MIP had an average delay of 1. 37 s in overlapping and 1. 6 s and 2. 14 s in nonoverlapping scenario. MIP 1 and MIP 2 are versions of MIP with an AA lifetime of 100 ms and 1 s respectively. MIP 2 is the proposed practice. MIP 1 though seems to have lower handoff delay it imposes a lot of communication overhead monopolizing the bandwidth
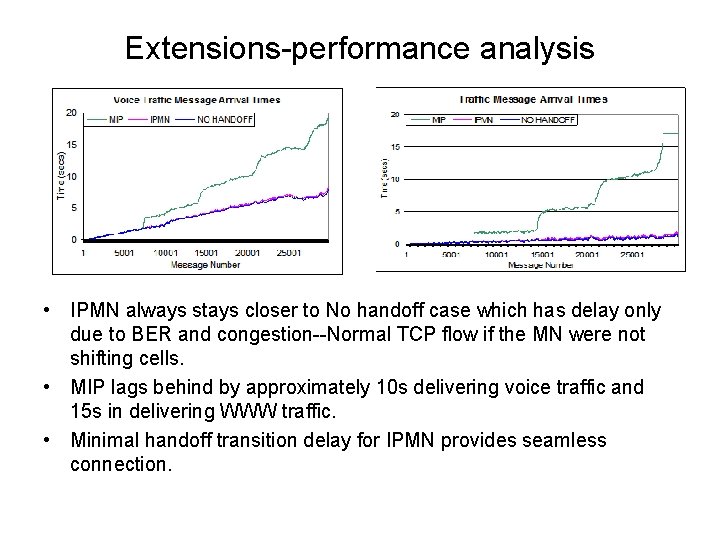
Extensions-performance analysis • IPMN always stays closer to No handoff case which has delay only due to BER and congestion--Normal TCP flow if the MN were not shifting cells. • MIP lags behind by approximately 10 s delivering voice traffic and 15 s in delivering WWW traffic. • Minimal handoff transition delay for IPMN provides seamless connection.
AGENDA • • Problem Statement Related Work Network Layer Solutions Proposed Scheme Performance Analysis Modeling 3 layer IPMN Conclusion
Conclusion • We have presented high performance mobility protocol which uses rapid cross layer interactivity. • Eliminates routing indirection (triangulation) by explicitly specifying the application about the underlying network change. • Flexibly manipulating the underlying network states transparently from L 7 to reflect network address changes— thus eliminating the L 3 movement detection. • MIP’s timer based rediscovery of already existing state information in lower layers makes it sluggish. • Our scheme uses this and other information from lower layers to intelligently perform handoff– proactive or reactive.
Conclusion • Most interesting claim- solution is based on L 7 disposable transientware processes. • Demonstrated in this case one possible intelligent schema for high performance TCP/IP mobility handling. • Further improvements and replacements by more powerful schemes are easy to incorporate– flexibility of L 7 transientware. • Demonstrated mobility solution did not require any functional change in classical TCP/IP layers. • Performance Results indicate the effectiveness and efficiency of our even-based scheme.
- Slides: 51