Centralizing and Automating People Soft Authority Management Security



- Slides: 30
Centralizing and Automating People. Soft Authority Management (Security) Session #20647 March 14, 2006 Alliance 2006 Conference Nashville, Tennessee
Your Presenters Kevin Dale – Information System Analyst − At Stanford since July 2001 – • Business Analyst for Financial Aid, Student Records and Security. • Lead for the Authority Manager Automation Project. Minh Nguyen – Software Architect − At Stanford since June 1997 – • Lead the development of Authority Manager, version 3. 0 • Part of the Signet core development 2
Stanford University • Founded in 1891 • Private university • 6, 753 undergraduate • 8, 093 graduate • 1, 775 faculty • 7, 565 staff Located 30 miles south of San Francisco and just north of Silicon Valley. 3
Your Organization and Oracle Campus Solutions 8 SP 1 • People. Tools 8. 22. 05 Enterprise Portal 8. 8 SP 1 • People. Tools 8. 44. 03 Enterprise Learning Management 8. 8 SP 1 • People. Tools 8. 45. 12 Oracle e-Business Suite 11. 5. 9 4
Agenda Authority Manager – Signet • • • What is Signet? Features Benefits Concepts Technologies People. Soft • • • Before Automation Project Goals How it Works – Business Process Demo How it Works - Technical Metrics Questions and Answers 5

Signet Minh Nguyen
What is Signet? Privilege Management System Web application • Toolkit/API • XML Schema • Open Source Project from NMI-EDIT Consortium Based on Stanford’s Authority Manager 7
NMI-EDIT Consortium • Comprises Internet 2 and EDUCAUSE − NSF Middleware Initiative (NMI)-Enterprise and Desktop Integration Technologies Consortium (EDIT) • Funded in 2001 by NSF Middleware Initiative • Researches and develops inter-institutional Identity and Access Management tools • Guided by MACE – Middleware Architecture Committee for Education − Group of R&E IT architects from US, Europe, and Australia 8
Features • Grant/Revoke Privileges • Grant-only • Distributed Delegation • Rules-Based Conditions • Proxy • Grant to Groups 9
Benefits • Standard user interface for users to grant privileges • Consistent, simplified policy definition via rolebased privileges • Improved visibility, understandability, and audit ability of privileges across the enterprise • Reduces latency in access privileges lifecycle events (activating/deactivating) 10
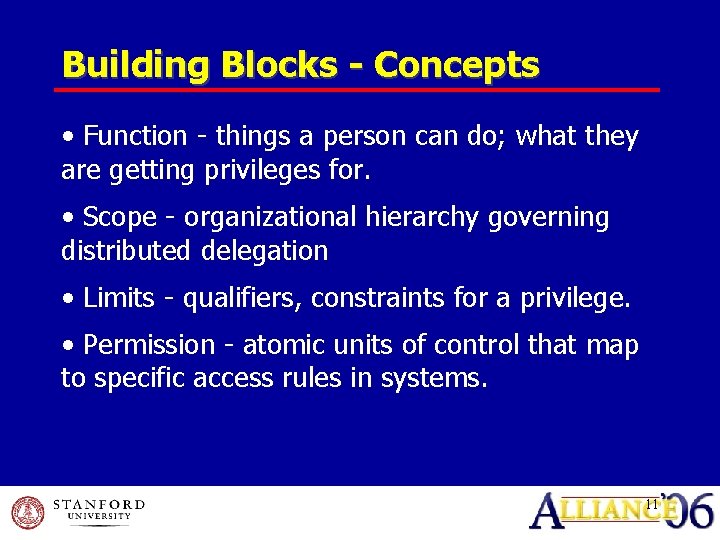
Building Blocks - Concepts • Function - things a person can do; what they are getting privileges for. • Scope - organizational hierarchy governing distributed delegation • Limits - qualifiers, constraints for a privilege. • Permission - atomic units of control that map to specific access rules in systems. 11
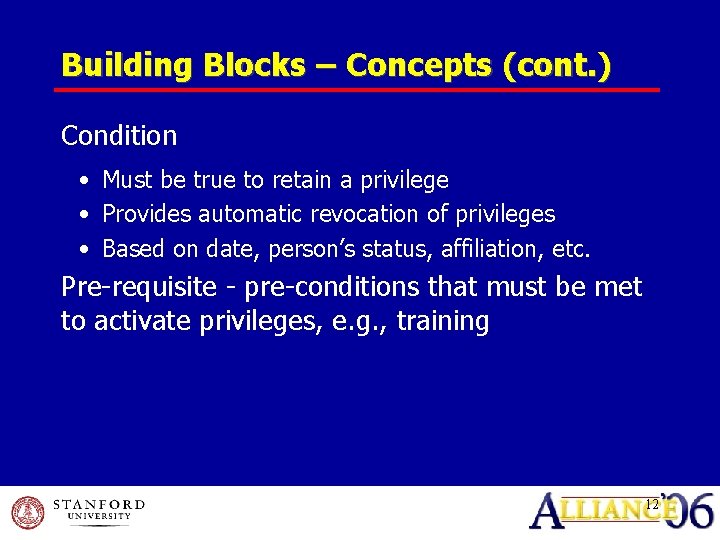
Building Blocks – Concepts (cont. ) Condition • Must be true to retain a privilege • Provides automatic revocation of privileges • Based on date, person’s status, affiliation, etc. Pre-requisite - pre-conditions that must be met to activate privileges, e. g. , training 12
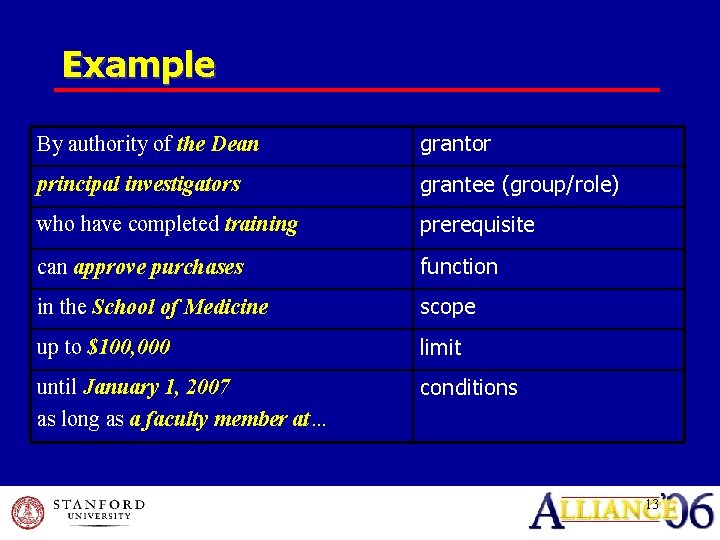
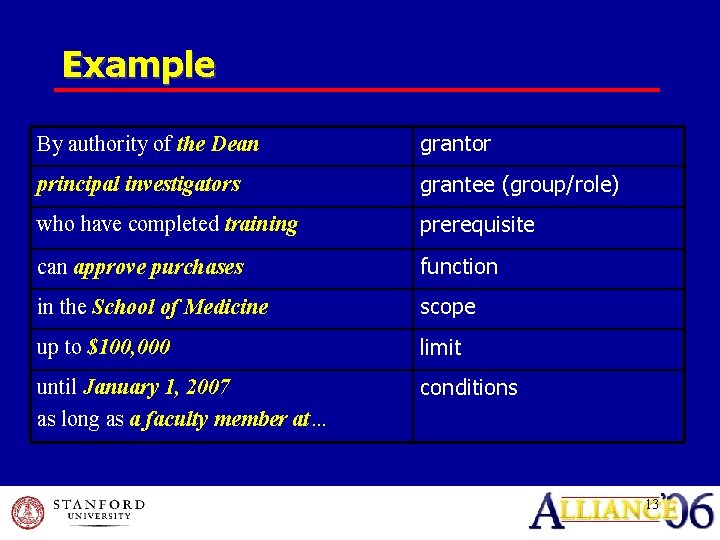
Example By authority of the Dean grantor principal investigators grantee (group/role) who have completed training prerequisite can approve purchases function in the School of Medicine scope up to $100, 000 limit until January 1, 2007 as long as a faculty member at… conditions 13
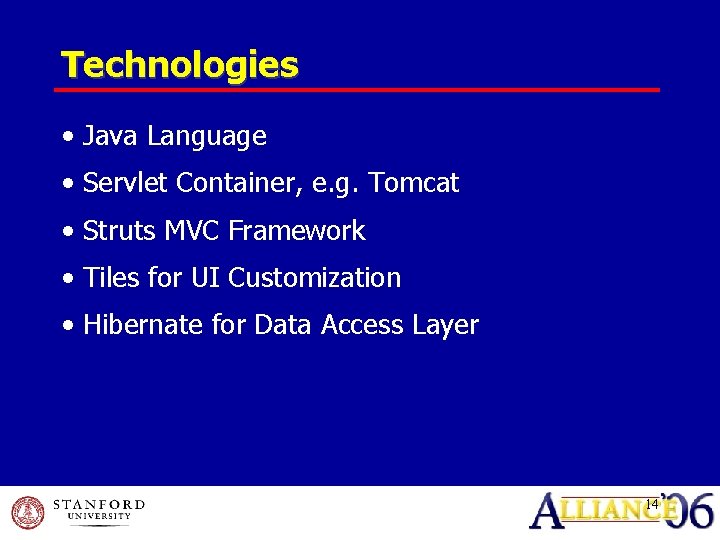
Technologies • Java Language • Servlet Container, e. g. Tomcat • Struts MVC Framework • Tiles for UI Customization • Hibernate for Data Access Layer 14
Resources • NMI-EDIT – http: //www. nmi-edit. org • MACE – http: //middleware. internet 2. edu/MACE • Signet – http: //middleware. internet 2. edu/signet 15
People. Soft & Authority Manager Kevin Dale
Before Automation • Totally Manual Process • Email • No Tracking • Potential for Incorrect Assignment • Delay in Assignment • No Audit / Validation Process 17
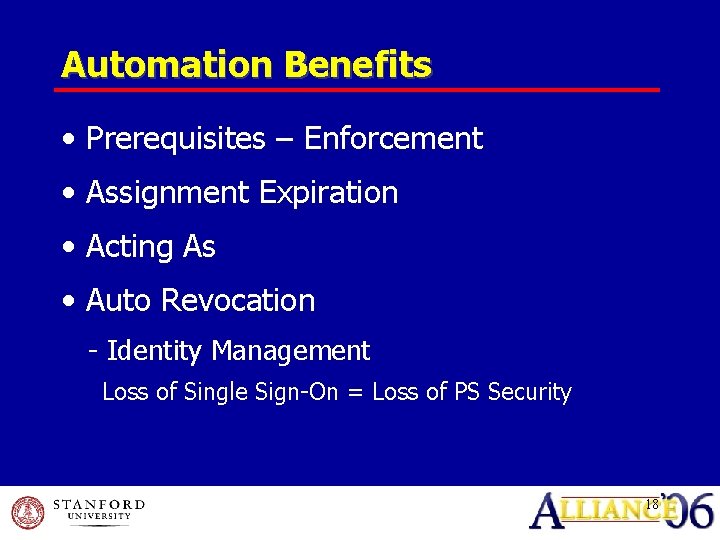
Automation Benefits • Prerequisites – Enforcement • Assignment Expiration • Acting As • Auto Revocation - Identity Management Loss of Single Sign-On = Loss of PS Security 18
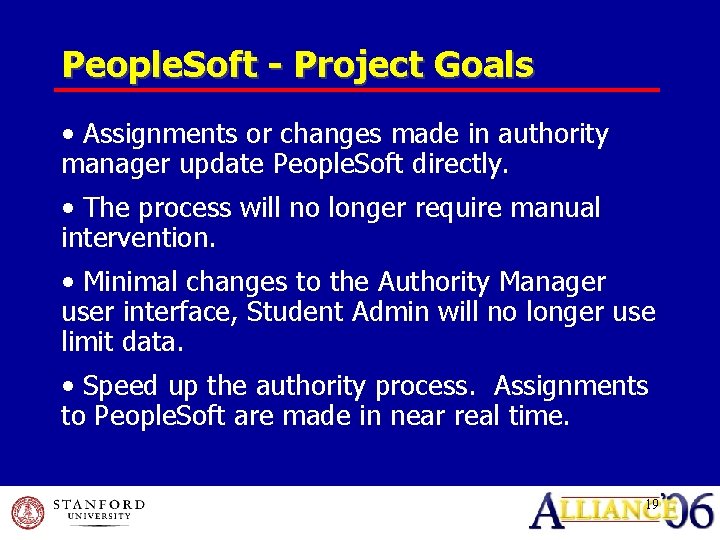
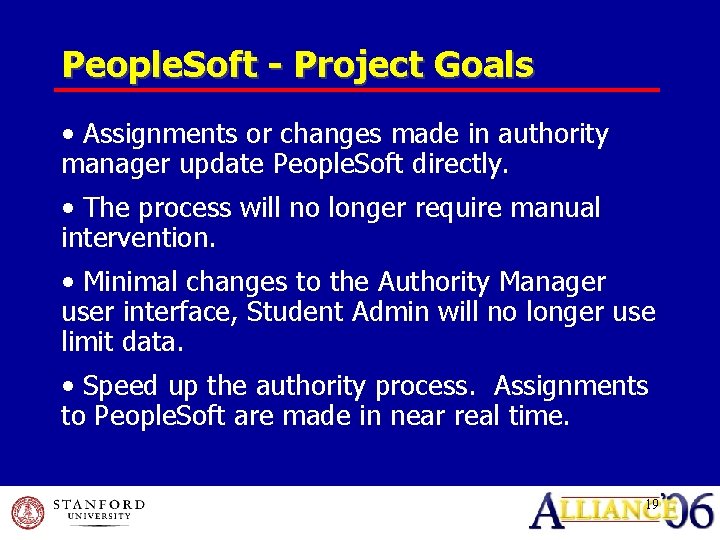
People. Soft - Project Goals • Assignments or changes made in authority manager update People. Soft directly. • The process will no longer require manual intervention. • Minimal changes to the Authority Manager user interface, Student Admin will no longer use limit data. • Speed up the authority process. Assignments to People. Soft are made in near real time. 19
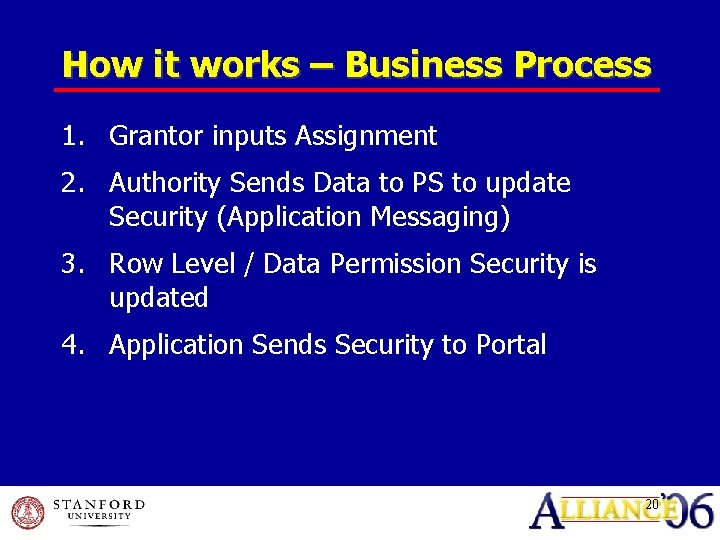
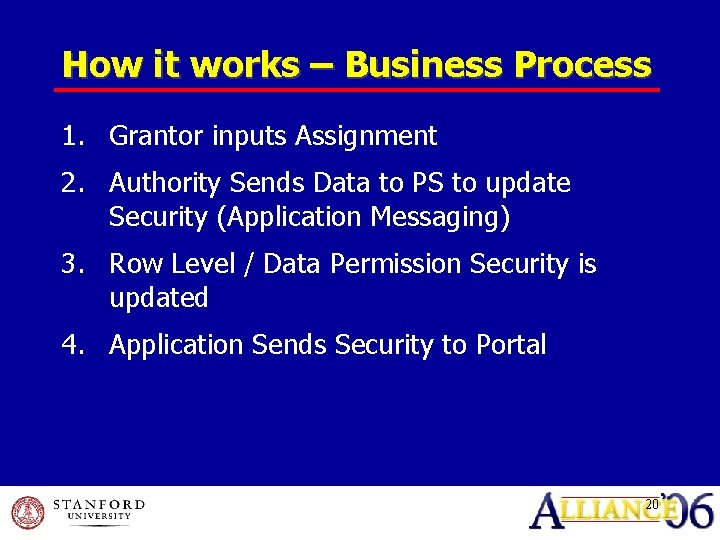
How it works – Business Process 1. Grantor inputs Assignment 2. Authority Sends Data to PS to update Security (Application Messaging) 3. Row Level / Data Permission Security is updated 4. Application Sends Security to Portal 20

Start Demo
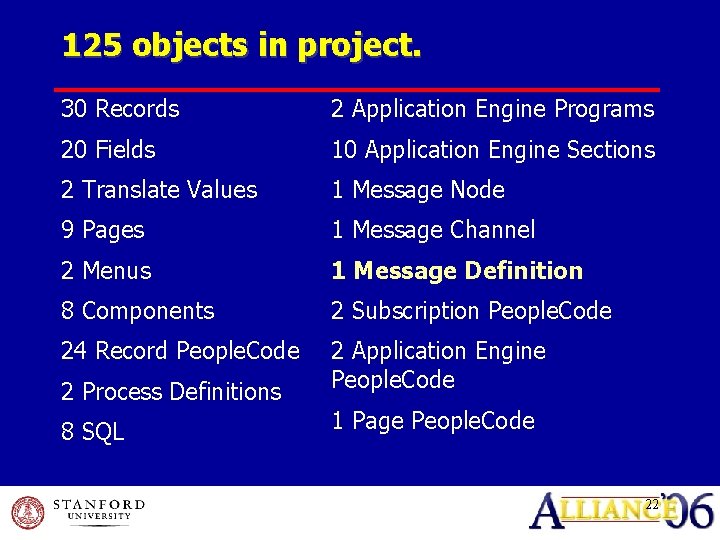
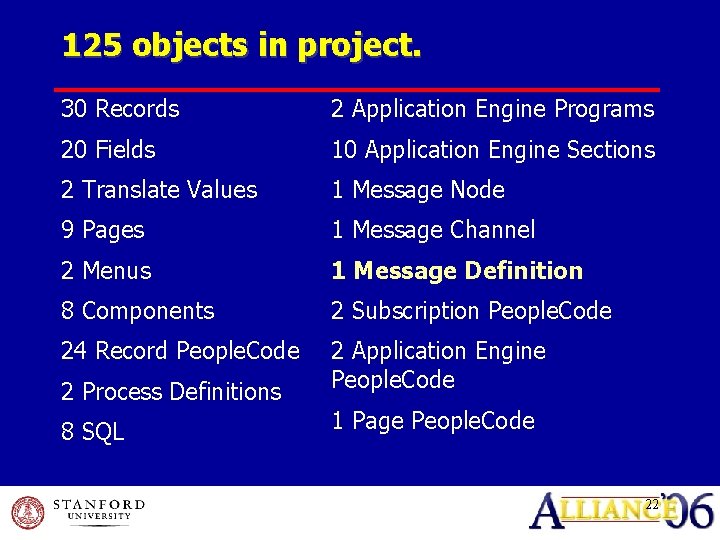
125 objects in project. 30 Records 2 Application Engine Programs 20 Fields 10 Application Engine Sections 2 Translate Values 1 Message Node 9 Pages 1 Message Channel 2 Menus 1 Message Definition 8 Components 2 Subscription People. Code 24 Record People. Code 2 Application Engine People. Code 2 Process Definitions 8 SQL 1 Page People. Code 22
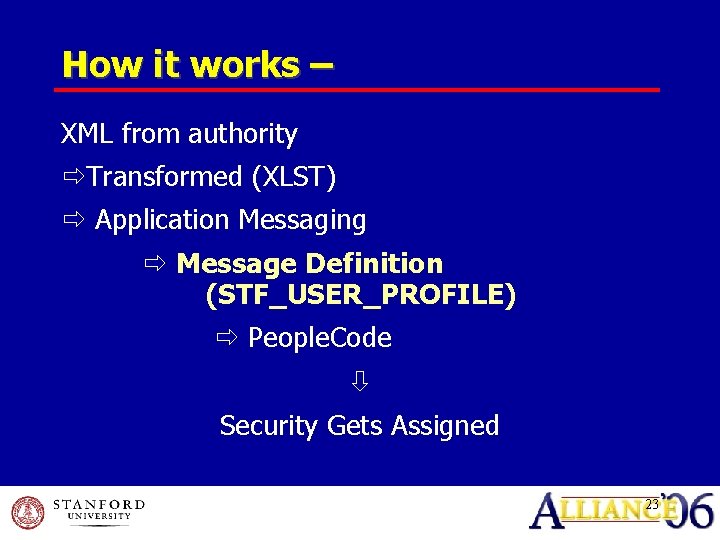
How it works – XML from authority Transformed (XLST) Application Messaging Message Definition (STF_USER_PROFILE) People. Code Security Gets Assigned 23
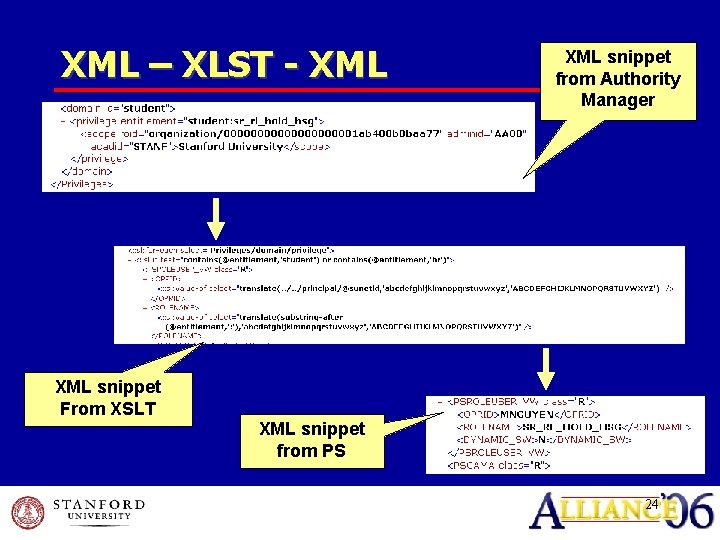
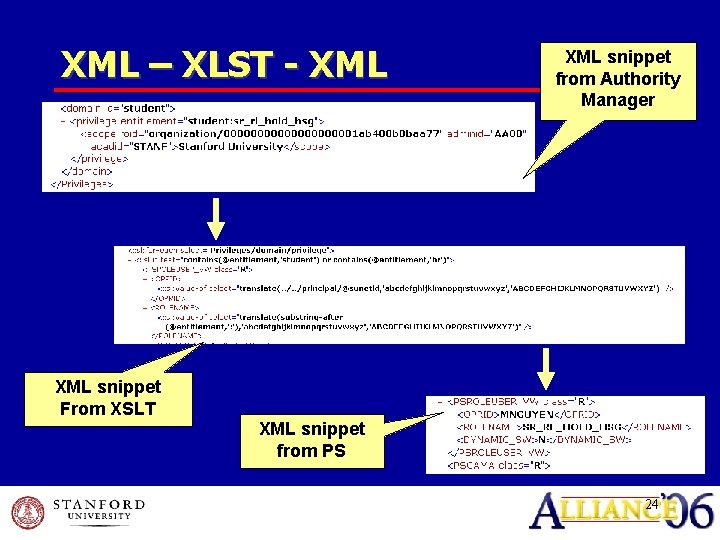
XML – XLST - XML snippet from Authority Manager XML snippet From XSLT XML snippet from PS 24
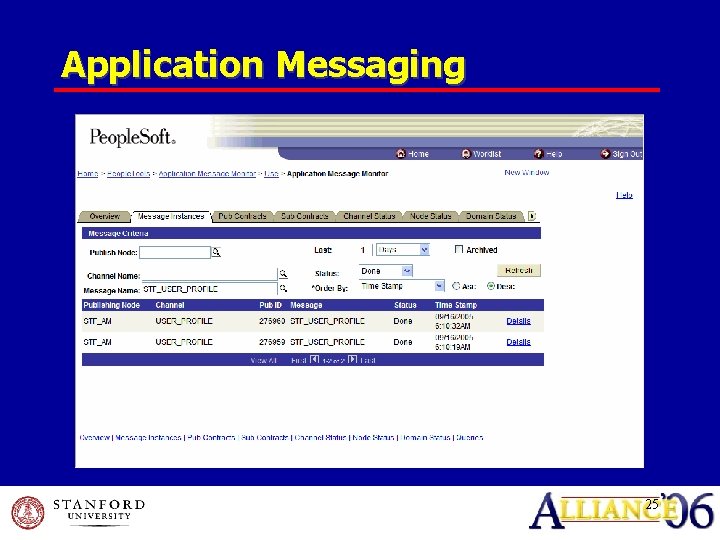
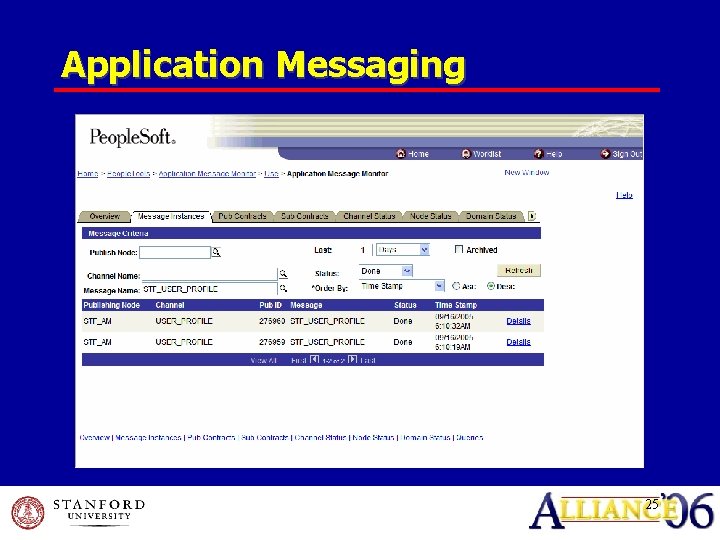
Application Messaging 25
Metrics Volume • On average 38 (includes HR, Student and Financials) new / changes to security assigned each day Latency • Events harvested every 10 minutes • All updates completed within 1 -2 minutes 26
End Demo

Questions?
Contacts Kevin Dale Information Systems Analyst, Administrative Systems Stanford University E-mail: kdale@stanford. edu Minh Nguyen Software Architect, Administrative Systems Stanford University E-mail: mnguyen@stanford. edu 29
This presentation and all Alliance 2006 presentations are available for download from the Conference Site Presentations from previous meetings are also available