Broadcast Encryption and Asymmetric MACs 11292020 Gene Itkis
Broadcast Encryption and Asymmetric MACs 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 1

Goal u Broadcast to a “privileged” subset (e. g. entitlement msg) u no group of t unprivileged colluders (hackers) can understand the msg Selection of the t hackers can be u “worst-case” (for broadcaster) u random (this appears more relevant) 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 2
Setting u Center can do only global broadcasts u No return path u Privileged set assumed known Three types of assumptions: u none u crypto: 1 -way f-ns (prg’s) exist u number-theoretic: hardness of factoring 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 3
Costs u Number of Keys u Computation overhead u Communication 11/29/2020 overhead Gene Itkis: BU CAS CS 591 - Topics in Internet Security 4
Naive estimates un = number of users n then number of possible subsets is 2 each must use a different key! (also need 2 n bits to specify subset/key) - ignored here u Idea: 11/29/2020 generate needed key (one of many), using a few stored keys Gene Itkis: BU CAS CS 591 - Topics in Internet Security 5
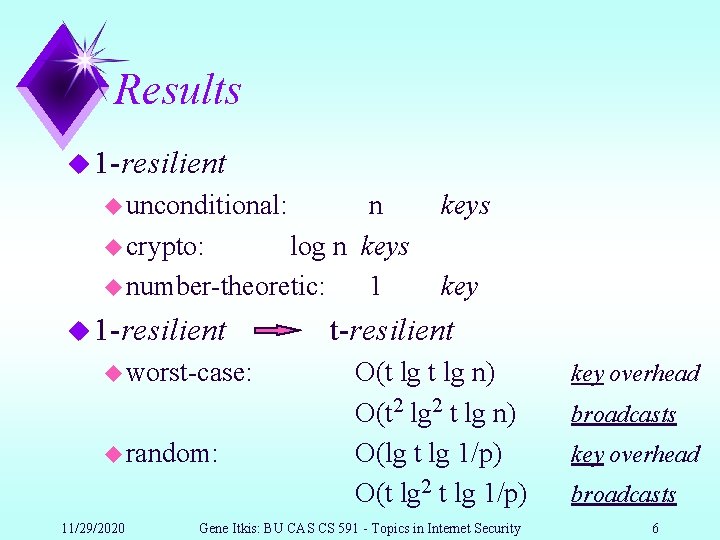
Results u 1 -resilient u unconditional: n u crypto: log n keys u number-theoretic: 1 u 1 -resilient u worst-case: u random: 11/29/2020 keys key t-resilient O(t lg n) O(t 2 lg 2 t lg n) O(lg t lg 1/p) O(t lg 2 t lg 1/p) Gene Itkis: BU CAS CS 591 - Topics in Internet Security key overhead broadcasts 6
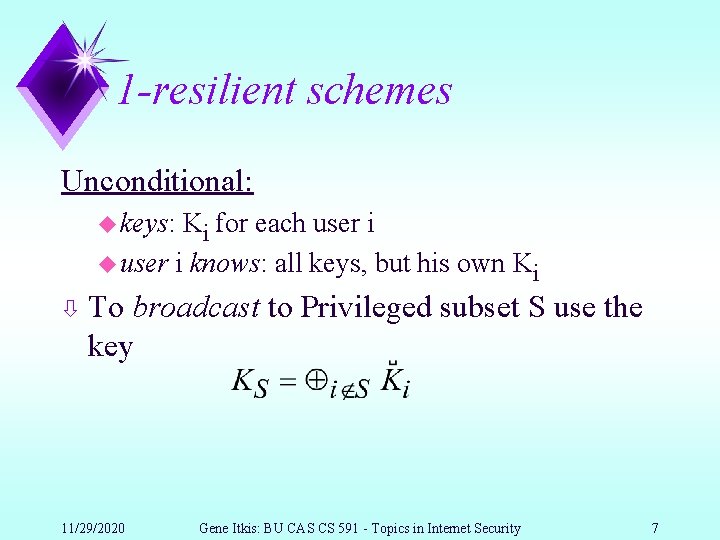
1 -resilient schemes Unconditional: u keys: Ki for each user i u user i knows: all keys, but his own Ki ò To broadcast to Privileged subset S use the key 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 7
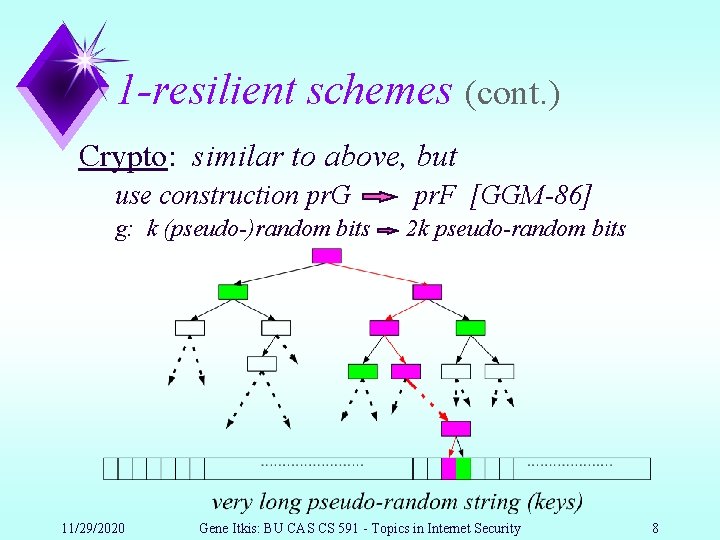
1 -resilient schemes (cont. ) Crypto: similar to above, but use construction pr. G g: k (pseudo-)random bits 11/29/2020 pr. F [GGM-86] 2 k pseudo-random bits Gene Itkis: BU CAS CS 591 - Topics in Internet Security 8
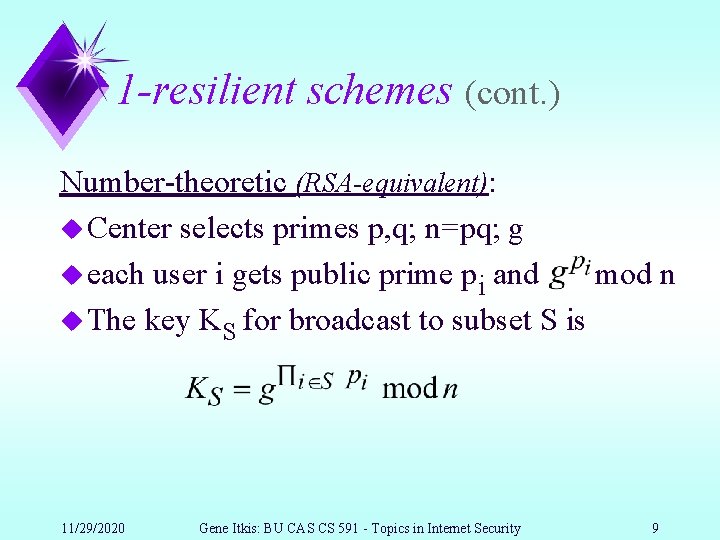
1 -resilient schemes (cont. ) Number-theoretic (RSA-equivalent): u Center selects primes p, q; n=pq; g u each user i gets public prime pi and mod n u The key KS for broadcast to subset S is 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 9
t-resilient schemes “direct” generalization of the above schemes is possible but expensive: exponential in t (simply consider each group of t users as a unit) 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 10
1 - to t-resilient transformation u To broadcast a msg M “break” it in m pieces M 1, . . . , Mm: u pieces are broadcast using independent schemes, each piece k times (each user has keys only for one of these k broadcasts) 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 11
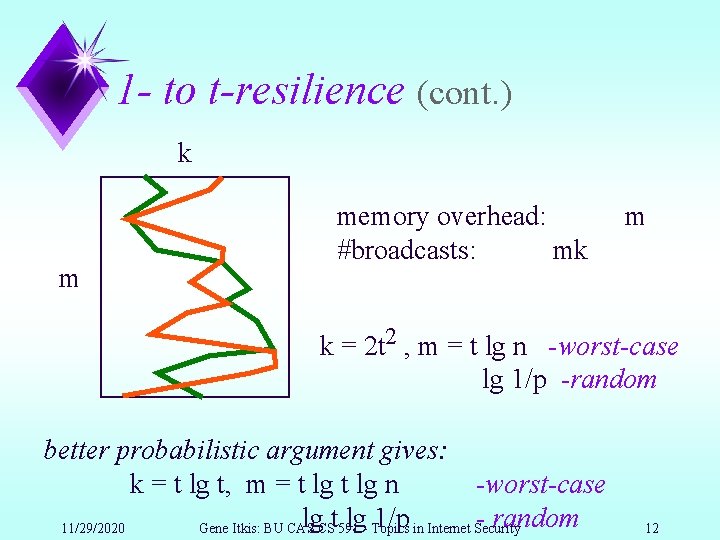
1 - to t-resilience (cont. ) k m memory overhead: #broadcasts: mk m k = 2 t 2 , m = t lg n -worst-case lg 1/p -random better probabilistic argument gives: k = t lg t, m = t lg n -worst-case lg. CSt 591 lg- Topics 1/p in Internet Security - random 11/29/2020 Gene Itkis: BU CAS 12
Conclusion t-resilient broadcast encryption u random: lg t lg 1/p keys t lg 2 t lg 1/p broadcasts u worst-case: t lg n keys t 2 lg 2 t lg nbroadcasts 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 13
Problems What makes these algorithms not practical (yet)? ua lot of computation -!!! u also, maybe could further reduce overheads for t-resilient schemes (is polylog in t possible? ) 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 14
Authentication M Alice Bill Bob 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 15
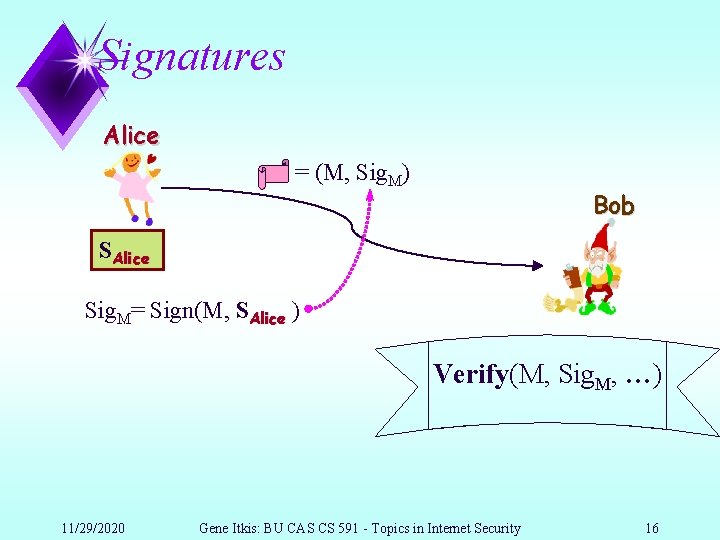
Signatures Alice = (M, Sig. M) Bob SAlice Sig. M= Sign(M, SAlice ) Verify(M, Sig. M, …) 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 16
Authentication: “public” Alice Bob • checks • contracts • love letters ? ? ? 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 17
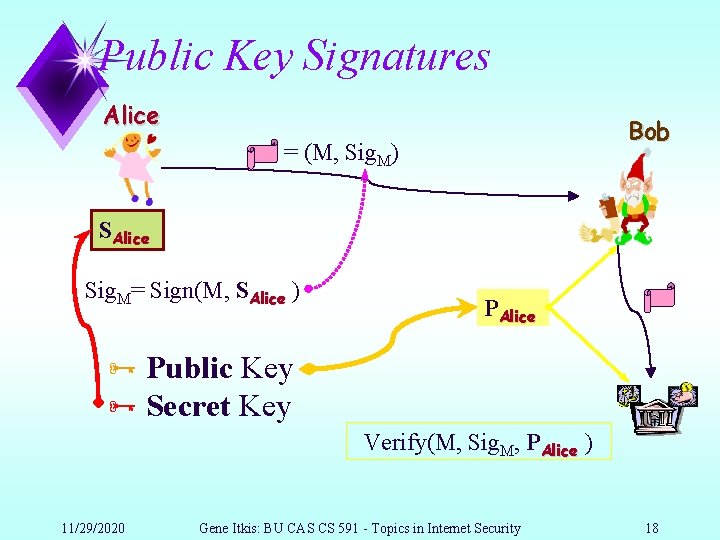
Public Key Signatures Alice Bob = (M, Sig. M) SAlice Sig. M= Sign(M, SAlice ) PAlice Ñ Public Key Ñ Secret Key Verify(M, Sig. M, PAlice ) 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 18
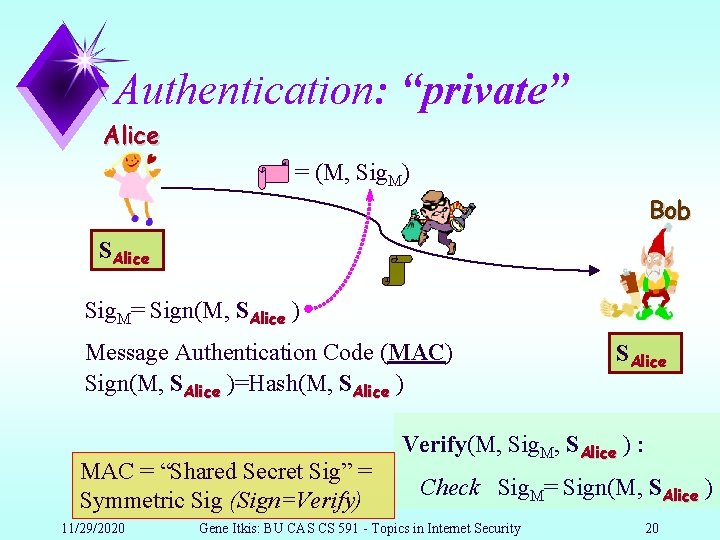
Authentication: “private” Alice = (M, Sig. M) Bob SAlice Sig. M= Sign(M, SAlice ) Message Authentication Code (MAC) Sign(M, SAlice )=Hash(M, SAlice ) MAC = “Shared Secret Sig” = Symmetric Sig (Sign=Verify) 11/29/2020 SAlice Verify(M, Sig. M, SAlice ) : Check Sig. M= Sign(M, SAlice ) Gene Itkis: BU CAS CS 591 - Topics in Internet Security 20
Authentication Alice Bob 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 21

Performance Secret Key (SK) algorithms beat Public Key (PK) ones by orders of magnitude u Speed u PK u Key size u PK 11/29/2020 100 -1000 times slower than SK 10 -50 times bigger than SK Gene Itkis: BU CAS CS 591 - Topics in Internet Security 24
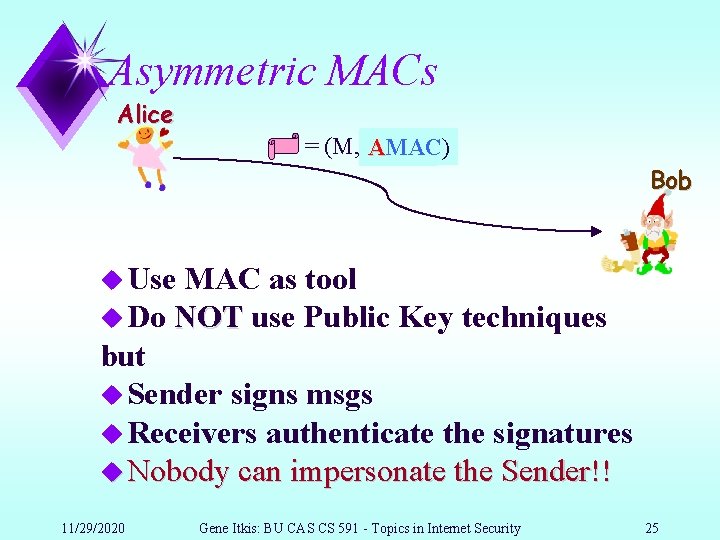
Asymmetric MACs Alice = (M, Sig AMAC) M) Bob u Use MAC as tool u Do NOT use Public Key techniques but u Sender signs msgs u Receivers authenticate the signatures u Nobody can impersonate the Sender!! 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 25
AMACs u How are AMACs different from Public Key Signatures? u Signer and Receivers may share some info u Authentic for A may not be Authentic for B u Big coalitions may break the scheme! u Idea u Each Receiver has a different subset of keys used by Sender for signing u Different subsets may overlap but not contain each other 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 26
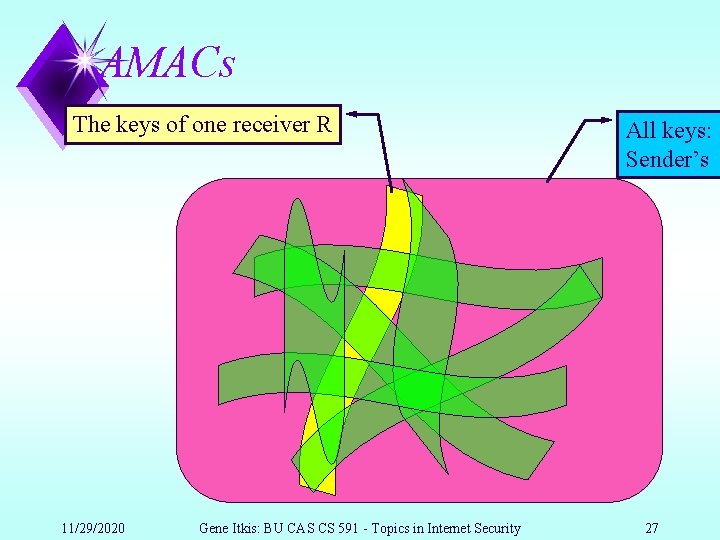
AMACs The keys of one receiver R 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security All keys: Sender’s 27
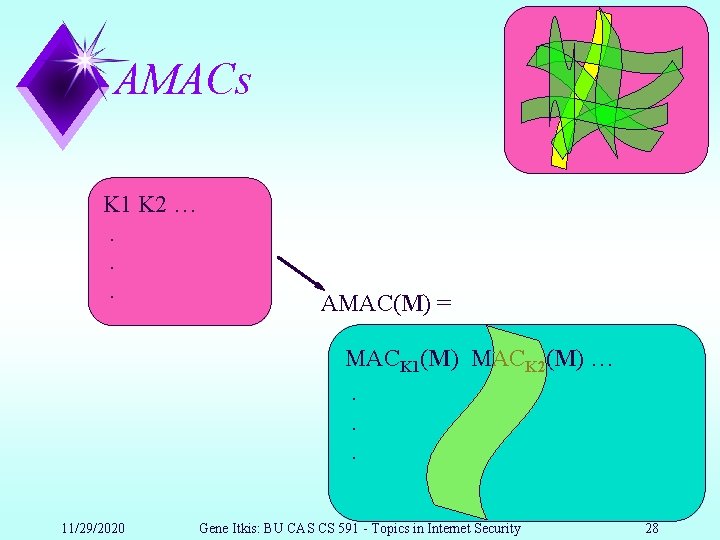
AMACs K 1 K 2 …. . . AMAC(M) = MACK 1(M) MACK 2(M) …. . . 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 28
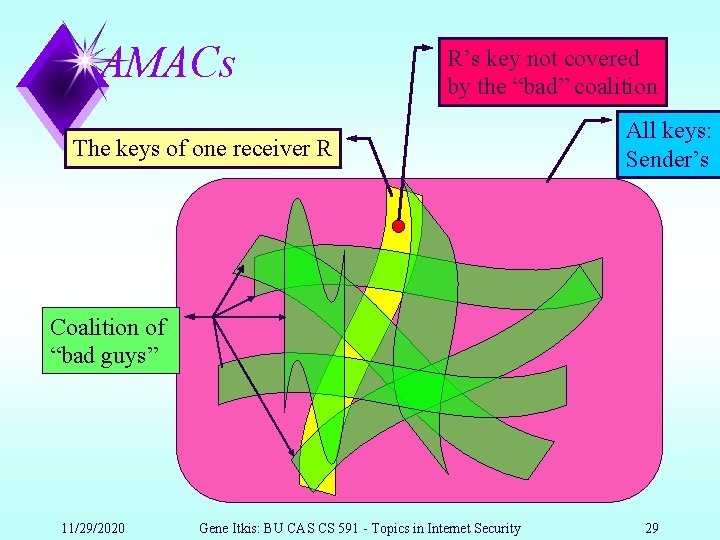
AMACs R’s key not covered by the “bad” coalition The keys of one receiver R All keys: Sender’s Coalition of “bad guys” 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 29
Goal u Given u. N (# of receivers) u b (# of “bad guys”) u Find smallest k (# of keys) and N subsets Si [1, …, k], such that for u deterministic: u any b+1 subsets Si 0 Si 1. . . Sik u probabilistic: u Prob[Si 0 11/29/2020 Si 1. . . Sik]<p Gene Itkis: BU CAS CS 591 - Topics in Internet Security 30
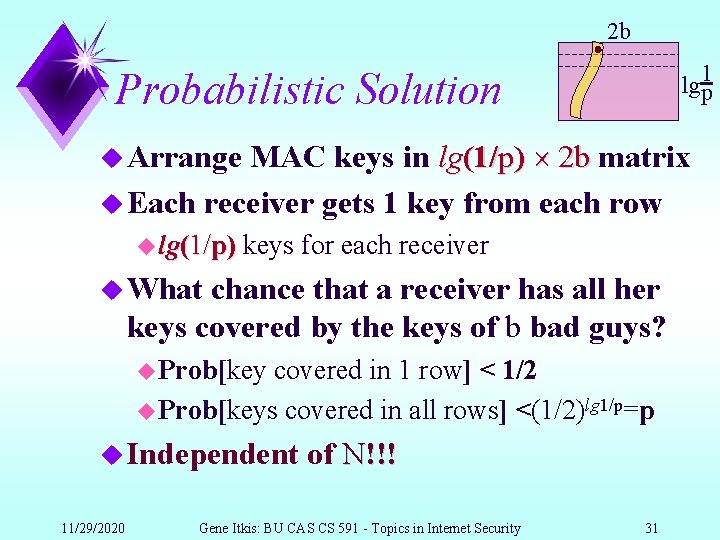
2 b lg 1 p Probabilistic Solution MAC keys in lg(1/p) 2 b matrix u Each receiver gets 1 key from each row u Arrange u lg(1/p) keys for each receiver u What chance that a receiver has all her keys covered by the keys of b bad guys? u Prob[key covered in 1 row] < 1/2 u Prob[keys covered in all rows] <(1/2)lg 1/p=p u Independent 11/29/2020 of N!!! Gene Itkis: BU CAS CS 591 - Topics in Internet Security 31
Performance u Sender MAC keys/computations: u 2 b lg (1/p) u Receivers u (each) MAC keys/computations: lg (1/p) u Alternative: u eb 11/29/2020 ln(1/p) sender; ln(1/p) each receiver Gene Itkis: BU CAS CS 591 - Topics in Internet Security 32
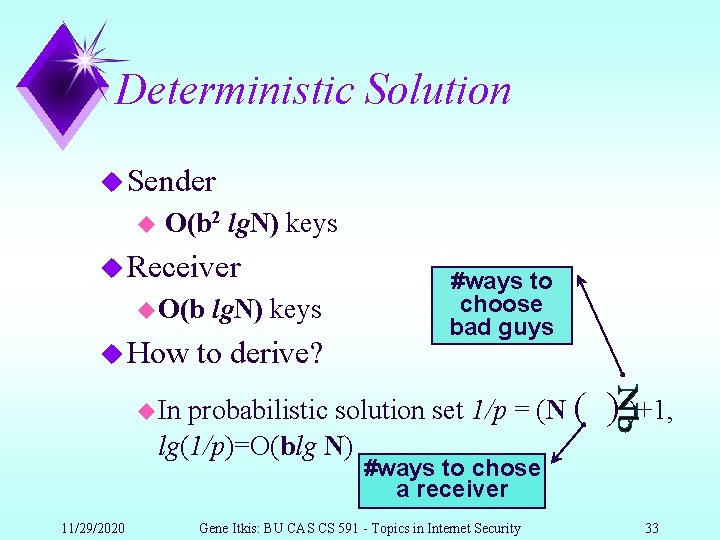
Deterministic Solution u Sender u O(b 2 lg. N) keys u Receiver u O(b u How lg. N) keys to derive? #ways to choose bad guys probabilistic solution set 1/p = (N ( lg(1/p)=O(blg N) u In ) )+1, #ways to chose a receiver 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 33
Bandwidth improvements u Security u need of individual MAC not be better than p MACs: |AMAC| 5 b lg(1/p) bits u Sender: 5· b lg(1/p) keys u Receiver: 2. 5·lg(1/p) keys u 1 bit 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 34
Multiple Sources u Each user can be a sender and receiver u Total: u each user: 2 b·lg(1/p) keys u check 11/29/2020 4 b 2·lg(1/p) keys MACs for common keys (~ lg(1/p)) Gene Itkis: BU CAS CS 591 - Topics in Internet Security 35
Multiple Sources (better way) u Same costs as Single Source! u Total keys & Receivers u as in single source: 2 blg(1/p) u Each potential Sender S: u for each key K, gets f(K, S) uf is a 1 way function u uses all f(K, S) to compute its AMACs u Receivers compute and use f(K, S) for those K which they have u Senders cannot impersonate!!! 11/29/2020 Gene Itkis: BU CAS CS 591 - Topics in Internet Security 36
![Related work u Broadcast u [Fiat u Some 11/29/2020 Encryption Naor], [Stinson], and others Related work u Broadcast u [Fiat u Some 11/29/2020 Encryption Naor], [Stinson], and others](http://slidetodoc.com/presentation_image_h/b9ddd48a99e682e10e781e9b40fdbbd3/image-34.jpg)
Related work u Broadcast u [Fiat u Some 11/29/2020 Encryption Naor], [Stinson], and others work in progress Gene Itkis: BU CAS CS 591 - Topics in Internet Security 37
- Slides: 34