Bosch Video Managment System Bosch Video Management Systems

Bosch Video Managment System Bosch Video Management Systems Cyber Security and IP Video Data and Cyber Security
Is anything safe? Funtenna was created by Dr AGN CUI (Red Balloon): • • • Rewrites Printers firmware via a Resume New firmware finds all network phones • Places phone to “off hook” Printer is now also a radio? Maxwell’s Equation This is a Physical and Software Takedown 2
Before We Begin What is the difference between the two objects below
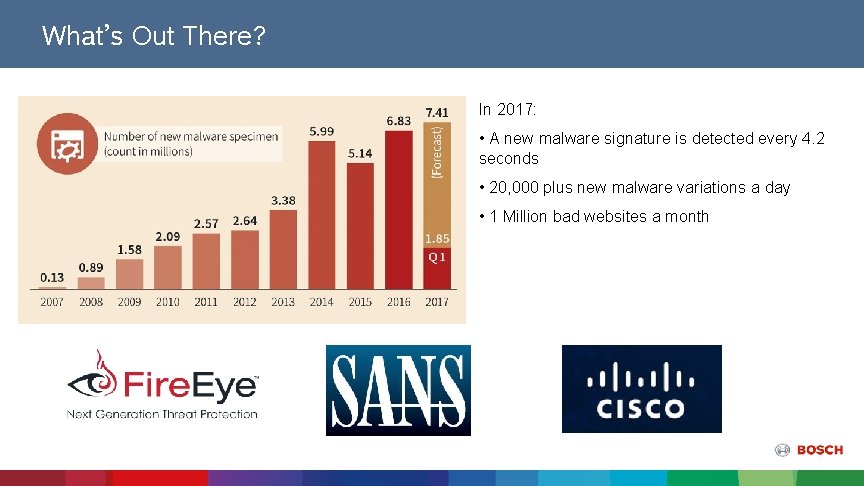
What’s Out There? In 2017: • A new malware signature is detected every 4. 2 seconds • 20, 000 plus new malware variations a day • 1 Million bad websites a month
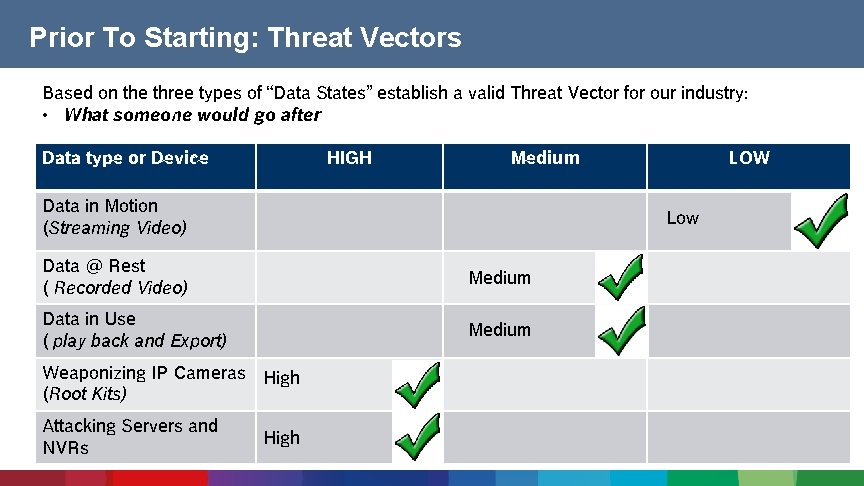
Prior To Starting: Threat Vectors Based on the three types of “Data States” establish a valid Threat Vector for our industry: • What someone would go after Data type or Device HIGH Medium Data in Motion (Streaming Video) Low Data @ Rest ( Recorded Video) Medium Data in Use ( play back and Export) Medium Weaponizing IP Cameras High (Root Kits) Attacking Servers and NVRs LOW High
Current Threats From a IP Video Aspect Where can I purchase Anti Virus Software for IP Video cameras? • Malware: Botnets, Trojans , Rootkits, • Privilege misuse: Insider access to VMS and Video • Physical Theft: SD cards, Hard Drives, Cameras taken • Web Attacks: Attacks on IP Device Web Interface ( example Cross Site Scripting)
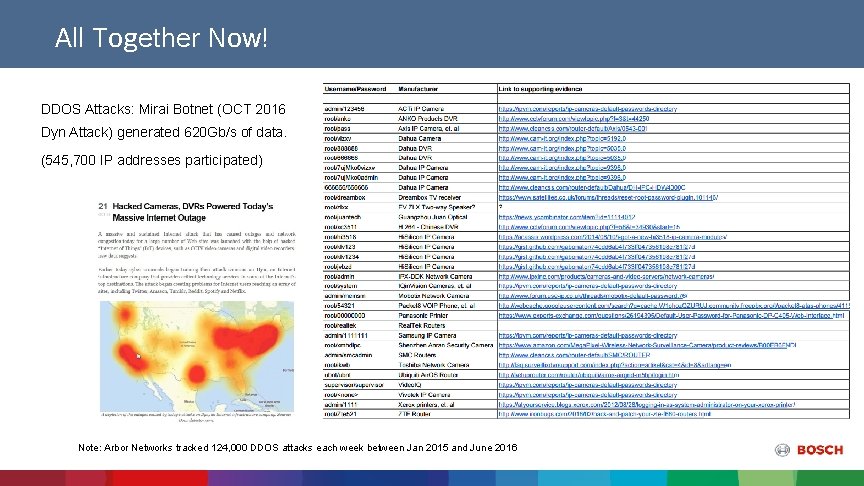
All Together Now! DDOS Attacks: Mirai Botnet (OCT 2016 Dyn Attack) generated 620 Gb/s of data. (545, 700 IP addresses participated) Note: Arbor Networks tracked 124, 000 DDOS attacks each week between Jan 2015 and June 2016
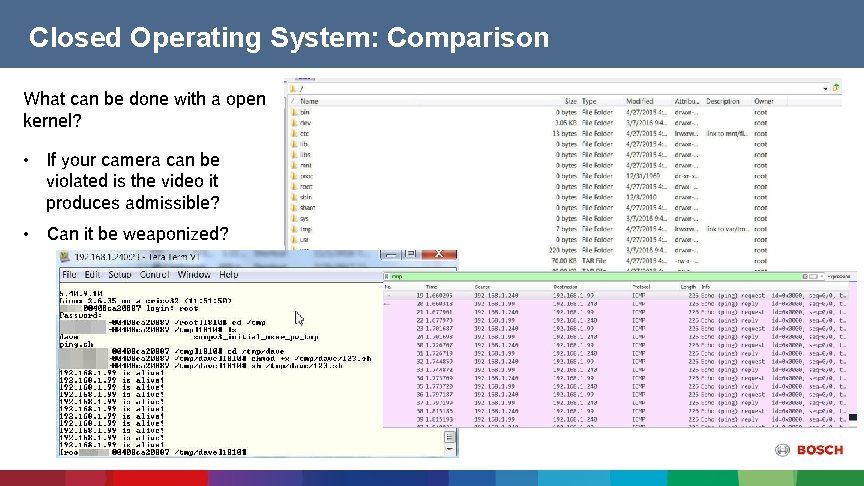
Closed Operating System: Comparison What can be done with a open kernel? • If your camera can be violated is the video it produces admissible? • Can it be weaponized?
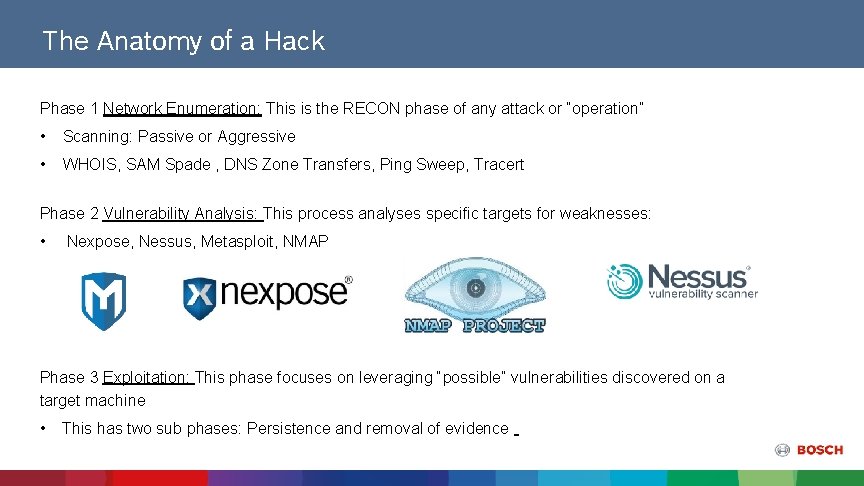
The Anatomy of a Hack Phase 1 Network Enumeration: This is the RECON phase of any attack or “operation” • Scanning: Passive or Aggressive • WHOIS, SAM Spade , DNS Zone Transfers, Ping Sweep, Tracert Phase 2 Vulnerability Analysis: This process analyses specific targets for weaknesses: • Nexpose, Nessus, Metasploit, NMAP Phase 3 Exploitation: This phase focuses on leveraging “possible” vulnerabilities discovered on a target machine • This has two sub phases: Persistence and removal of evidence

Vulnerability vs Penetration Are designed to yield a prioritized list of vulnerabilities and are typically for clients who already understand they are not where they want to be in terms of security 10 Are designed to achieve a specific, attackersimulated goal and should be requested by customers who are already at their desired security posture
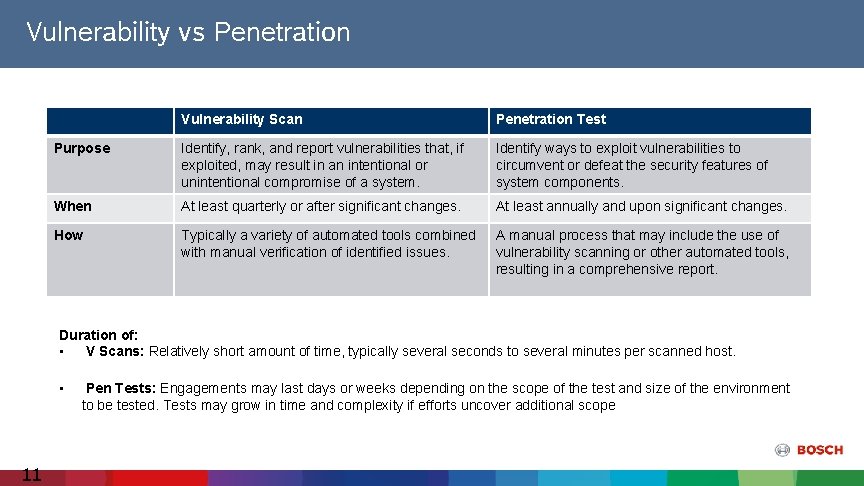
Vulnerability vs Penetration Vulnerability Scan Penetration Test Purpose Identify, rank, and report vulnerabilities that, if exploited, may result in an intentional or unintentional compromise of a system. Identify ways to exploit vulnerabilities to circumvent or defeat the security features of system components. When At least quarterly or after significant changes. At least annually and upon significant changes. How Typically a variety of automated tools combined with manual verification of identified issues. A manual process that may include the use of vulnerability scanning or other automated tools, resulting in a comprehensive report. Duration of: • V Scans: Relatively short amount of time, typically several seconds to several minutes per scanned host. • 11 Pen Tests: Engagements may last days or weeks depending on the scope of the test and size of the environment to be tested. Tests may grow in time and complexity if efforts uncover additional scope

Whiter Shades of Pale : Types of Pen Testing
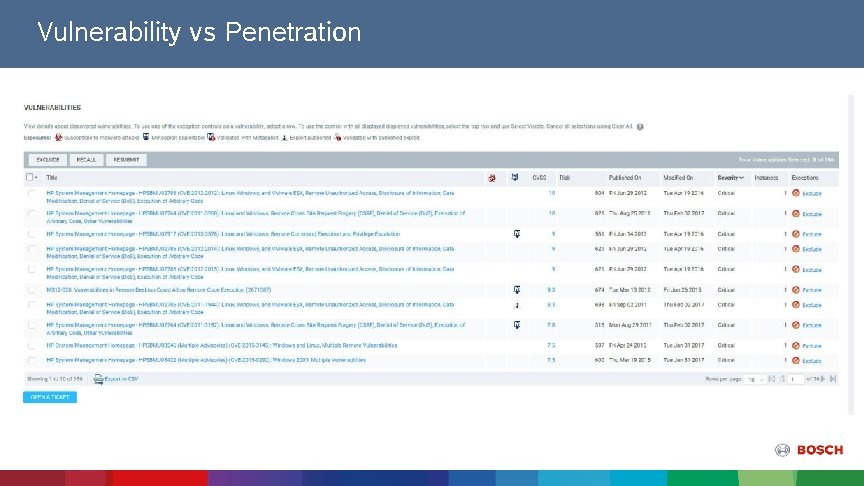
Vulnerability vs Penetration

Nexpose Scans CPP 7 Device after a basic “Lock Down” and applying IPv 4 Filtering or shifting the HTTPS Port

Closed Operating System? • Bosch encoders and cameras have a “Closed” OS that runs in limited memory space • Bosch encoders and cameras are manufactured in a controlled and secure environment that is continually audited. • Chain of Custody From Cradle to Customer • Devices can only be written to via a valid “signed” firmware upload, which is specific to hardware series and chipset.
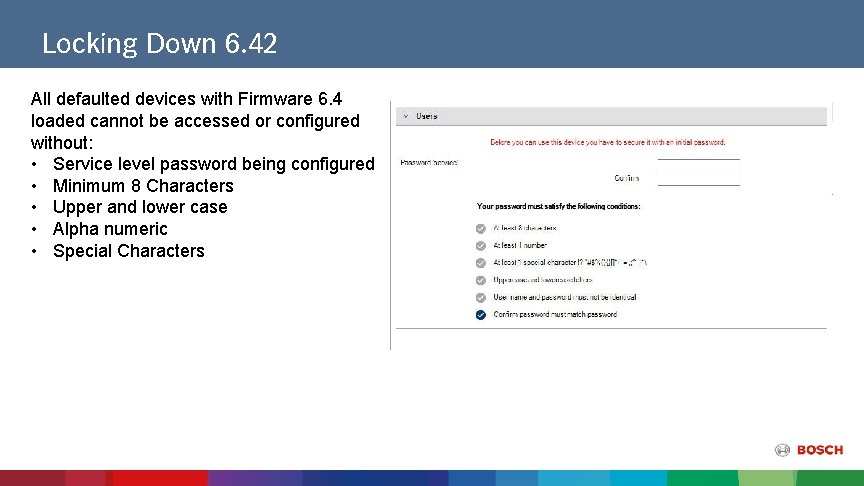
Locking Down 6. 42 All defaulted devices with Firmware 6. 4 loaded cannot be accessed or configured without: • Service level password being configured • Minimum 8 Characters • Upper and lower case • Alpha numeric • Special Characters
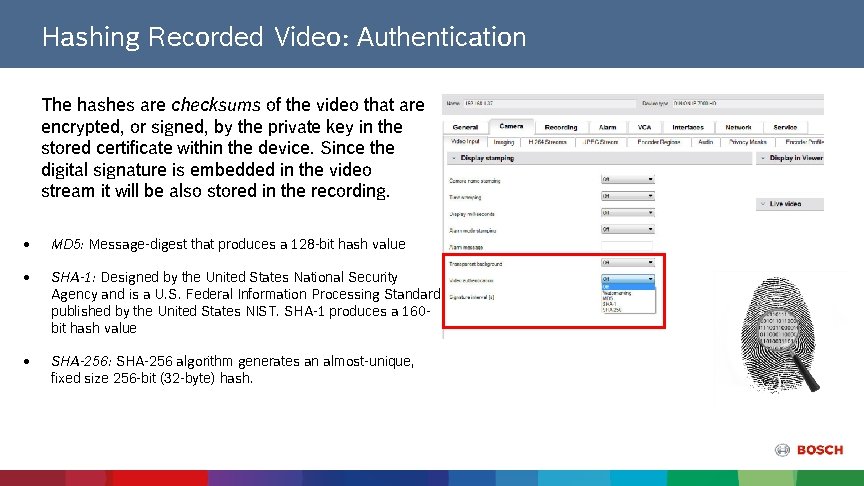
Hashing Recorded Video: Authentication The hashes are checksums of the video that are encrypted, or signed, by the private key in the stored certificate within the device. Since the digital signature is embedded in the video stream it will be also stored in the recording. MD 5: Message-digest that produces a 128 -bit hash value SHA-1: Designed by the United States National Security Agency and is a U. S. Federal Information Processing Standard published by the United States NIST. SHA-1 produces a 160 bit hash value SHA-256: SHA-256 algorithm generates an almost-unique, fixed size 256 -bit (32 -byte) hash.
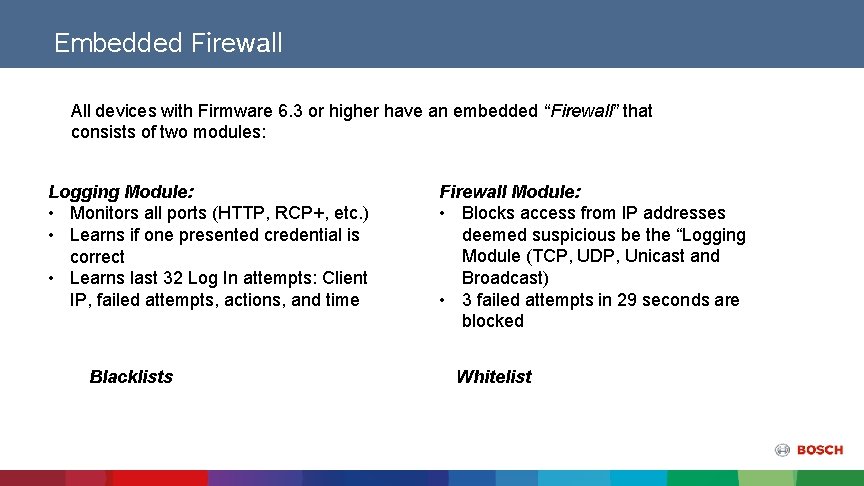
Embedded Firewall All devices with Firmware 6. 3 or higher have an embedded “Firewall” that consists of two modules: Logging Module: • Monitors all ports (HTTP, RCP+, etc. ) • Learns if one presented credential is correct • Learns last 32 Log In attempts: Client IP, failed attempts, actions, and time Blacklists Firewall Module: • Blocks access from IP addresses deemed suspicious be the “Logging Module (TCP, UDP, Unicast and Broadcast) • 3 failed attempts in 29 seconds are blocked Whitelist
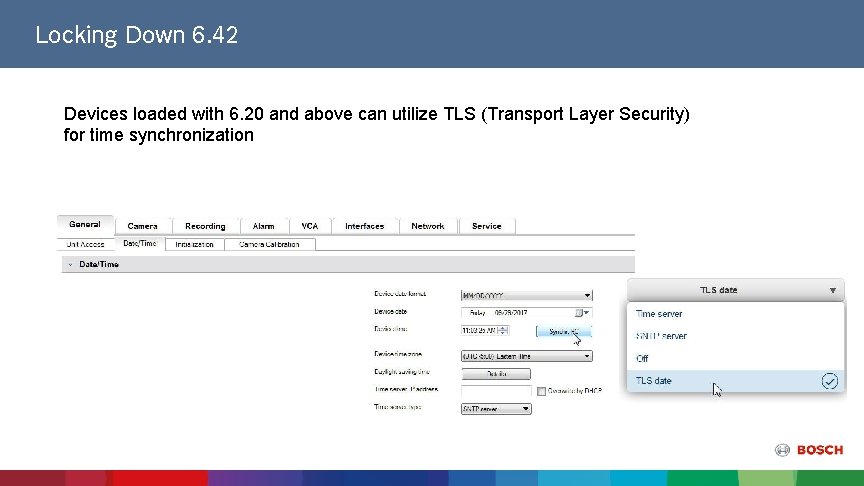
Locking Down 6. 42 Devices loaded with 6. 20 and above can utilize TLS (Transport Layer Security) for time synchronization
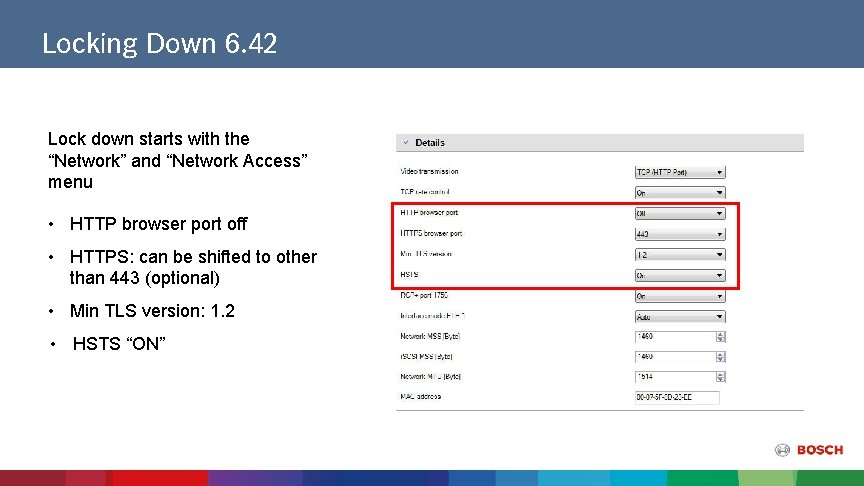
Locking Down 6. 42 Lock down starts with the “Network” and “Network Access” menu • HTTP browser port off • HTTPS: can be shifted to other than 443 (optional) • Min TLS version: 1. 2 • HSTS “ON”
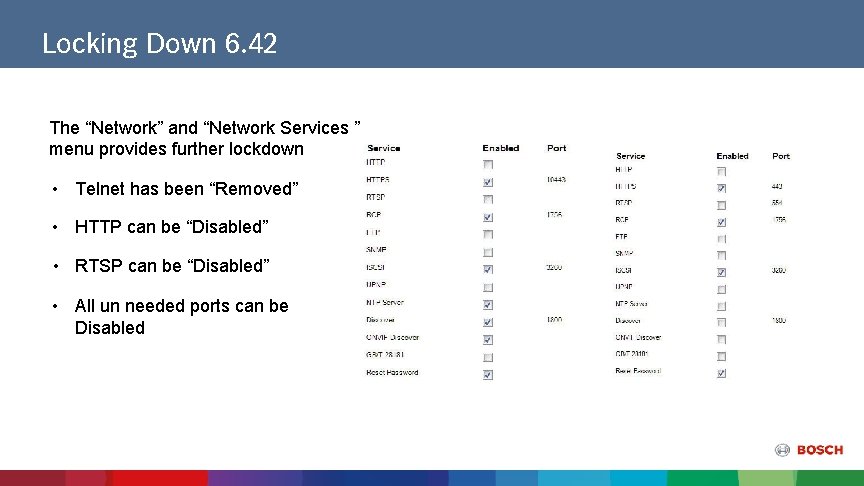
Locking Down 6. 42 The “Network” and “Network Services ” menu provides further lockdown • Telnet has been “Removed” • HTTP can be “Disabled” • RTSP can be “Disabled” • All un needed ports can be Disabled
Locking Down 6. 42 • • TTL Value 0 = Restricted to local host TTL Value 1 = Restricted to same subnet TTL Value 15 = Restricted to same site TTL Value 64 (Default) = Restricted to same region TTL Value 127 = Worldwide TTL Value 191 = Worldwide with limited bandwidth TTL Value 255 = Unrestricted Data
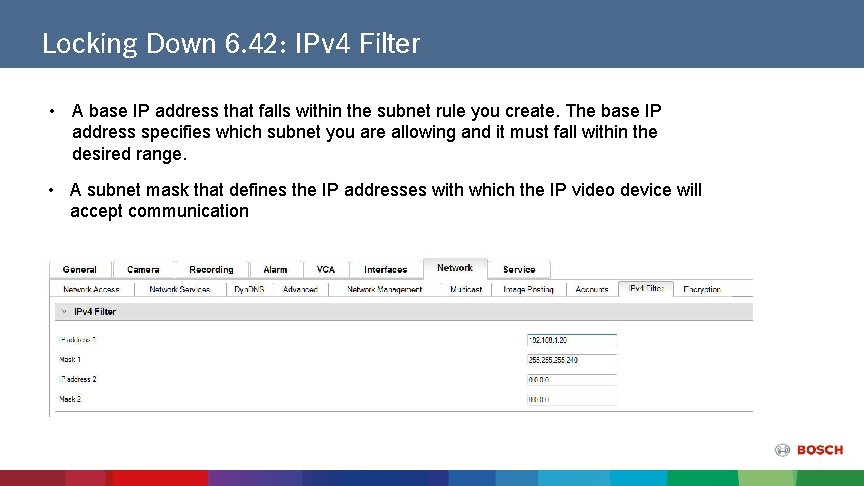
Locking Down 6. 42: IPv 4 Filter • A base IP address that falls within the subnet rule you create. The base IP address specifies which subnet you are allowing and it must fall within the desired range. • A subnet mask that defines the IP addresses with which the IP video device will accept communication
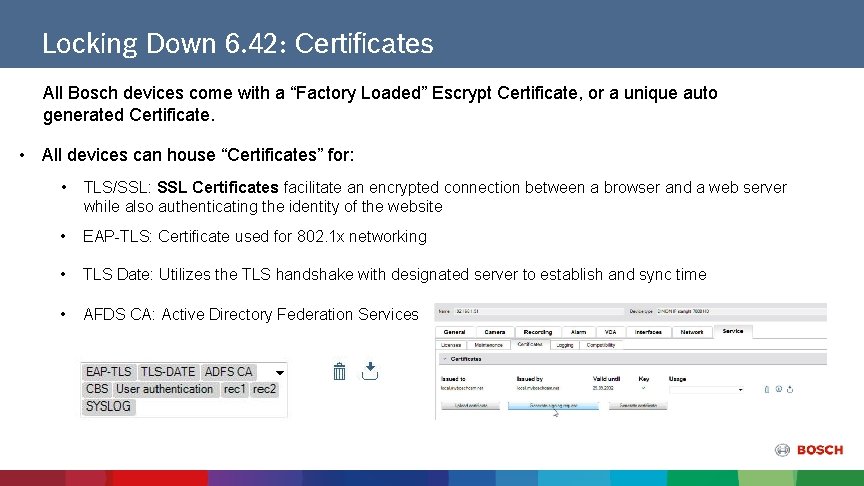
Locking Down 6. 42: Certificates All Bosch devices come with a “Factory Loaded” Escrypt Certificate, or a unique auto generated Certificate. • All devices can house “Certificates” for: • TLS/SSL: SSL Certificates facilitate an encrypted connection between a browser and a web server while also authenticating the identity of the website • EAP-TLS: Certificate used for 802. 1 x networking • TLS Date: Utilizes the TLS handshake with designated server to establish and sync time • AFDS CA: Active Directory Federation Services
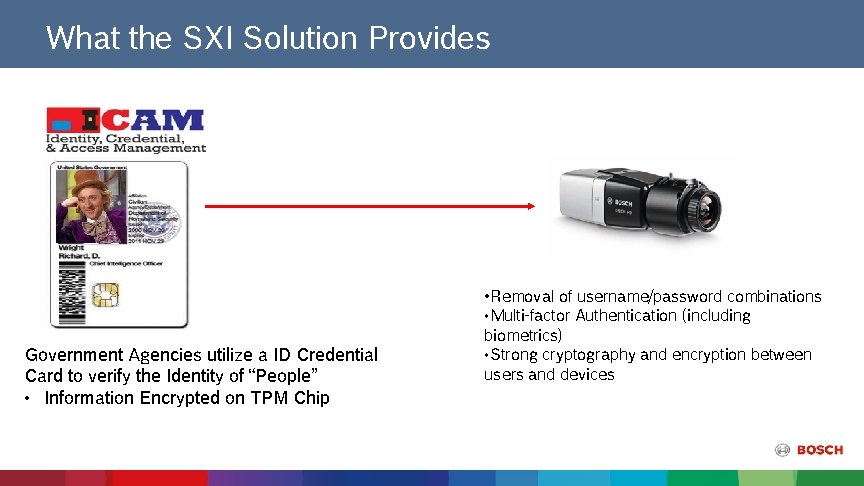
What the SXI Solution Provides Government Agencies utilize a ID Credential Card to verify the Identity of “People” • Information Encrypted on TPM Chip • Removal of username/password combinations • Multi-factor Authentication (including biometrics) • Strong cryptography and encryption between users and devices
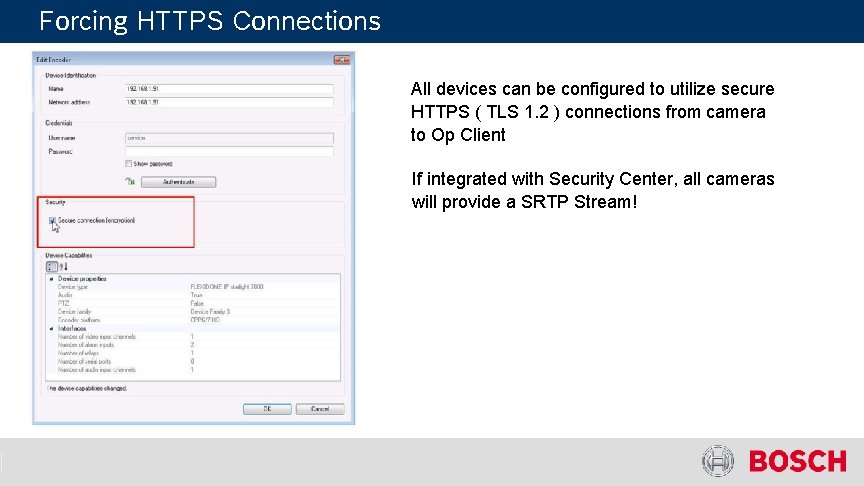
Forcing HTTPS Connections All devices can be configured to utilize secure HTTPS ( TLS 1. 2 ) connections from camera to Op Client If integrated with Security Center, all cameras will provide a SRTP Stream!
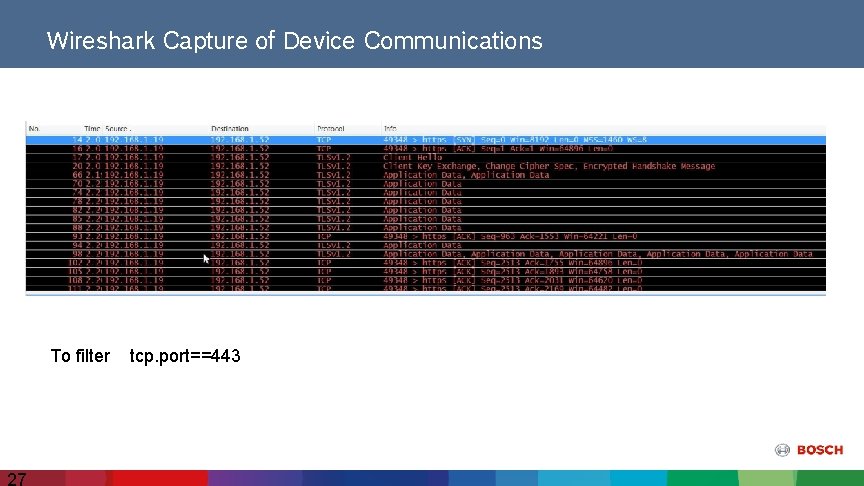
Wireshark Capture of Device Communications To filter 27 tcp. port==443
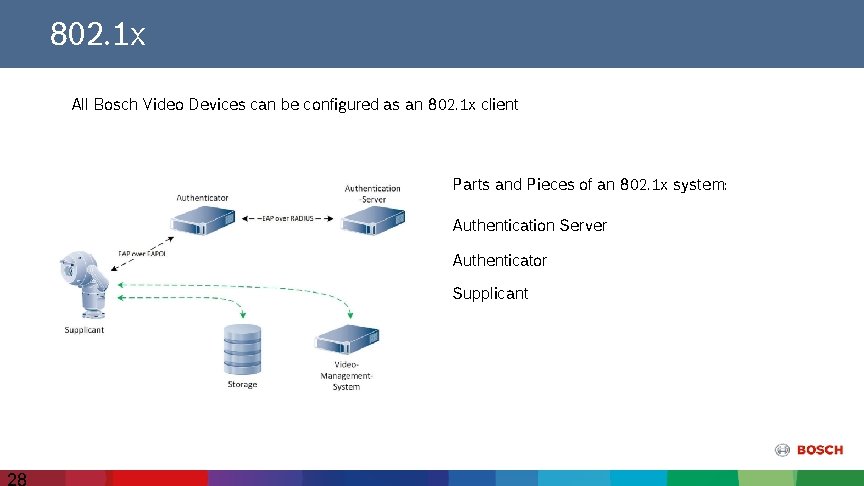
802. 1 x All Bosch Video Devices can be configured as an 802. 1 x client Parts and Pieces of an 802. 1 x system: Authentication Server Authenticator Supplicant 28
Questions
- Slides: 29