Heap Exploitation Techniques 2017 KUCIS Who am I



- Slides: 32

Heap Exploitation Techniques 2017 KUCIS 영남권 세미나
Who am I Name : 우동규 Age : 26 Interest : Pwnable E-mail : mrwoo 92@naver. com Blog : http: //woosunbi. tistory. com
INDEX 1. Glibc malloc Structure 2. Exploit with Unlink 3. House of Spirit 4. House of Force
Glibc malloc structure ㆍdlmalloc - General purpose allocator ㆍptmalloc 2 - Glibc ㆍjemalloc - Free. BSD and Firefox ㆍtcmalloc - Google ㆍlibumem - Solaris
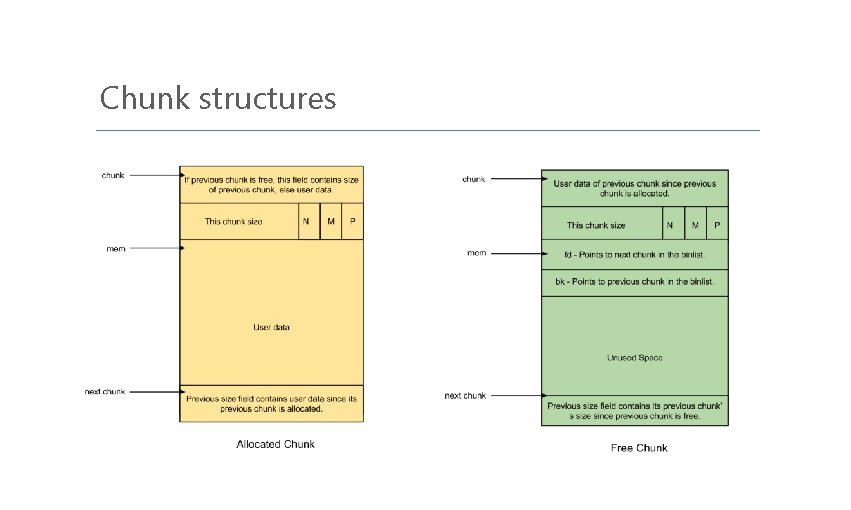
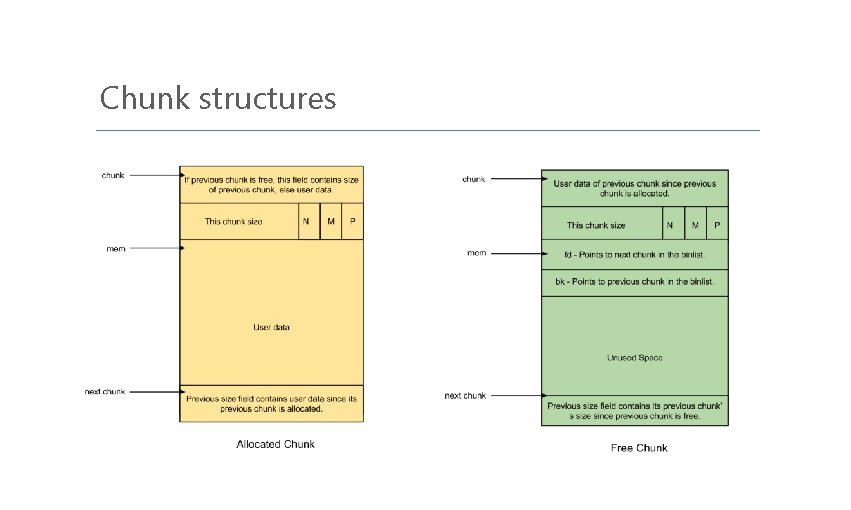
Chunk structures
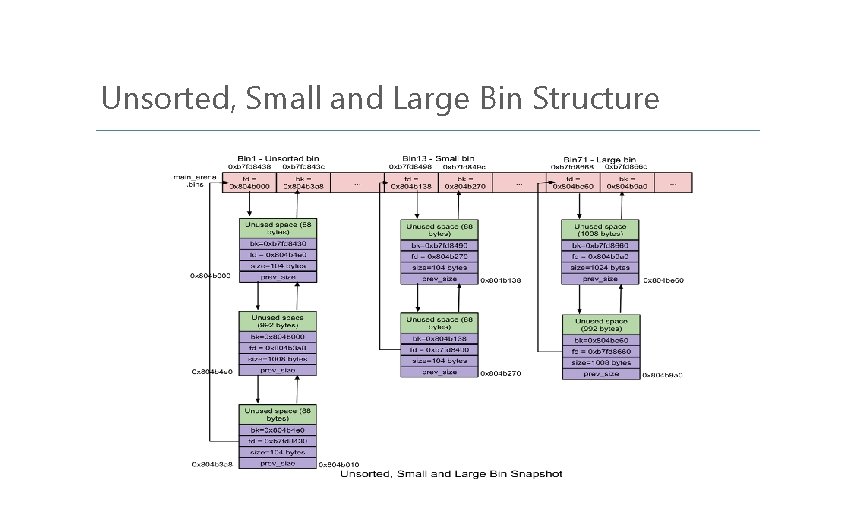
Bins (Total 126) ㆍFast bin (exact fit) ㆍUnsorted bin (Bin 1) ㆍSmall bin (Bin 2 to Bin 63, exact fit) ㆍLarge bin (Bin 64 to Bin 126)
Fast bin / Unsorted bin ㆍbin의 개수 - 10 ㆍSingle Linked list, LIFO(Last In First Out) ㆍ병합 없음 -> 속도가 빠르다. ㆍbin의 개수 - 1 ㆍDouble Linked List, FIFO(First In First Out) ㆍSmall / Large bin의 Chunk가 free 되었을 때 재사용의 기회를 주기 위함(속도 향상)
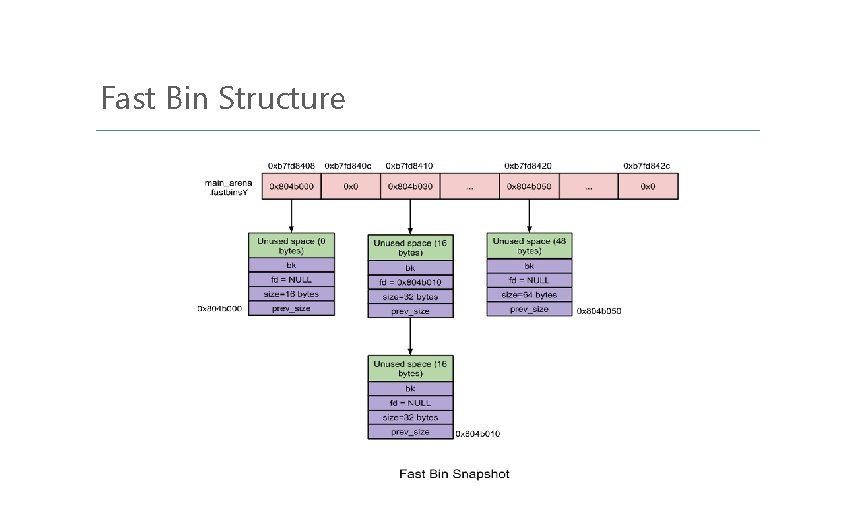
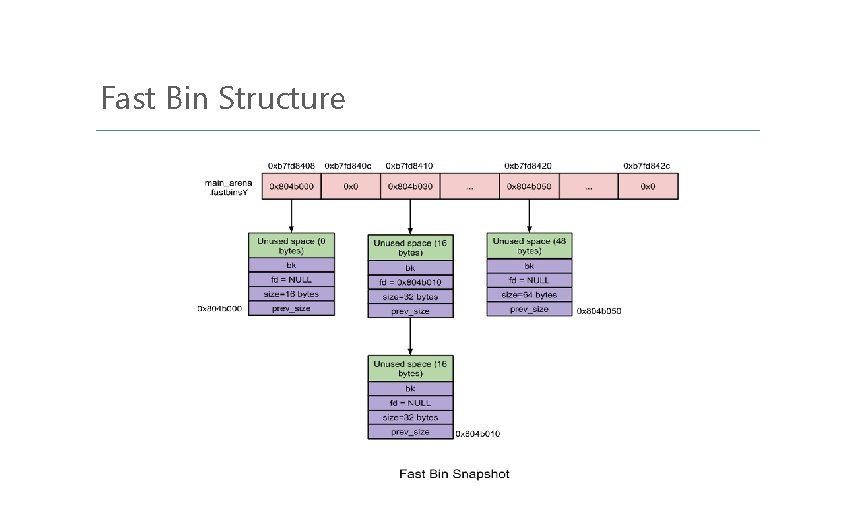
Fast Bin Structure

Small bin / Large bin ㆍbin의 개수 - 62 ㆍchunk size < 512 bytes ㆍDouble Linked List, FIFO(First In First Out) ㆍbin의 개수 - 63 ㆍchunk size >= 512 bytes ㆍ내림차순 정렬
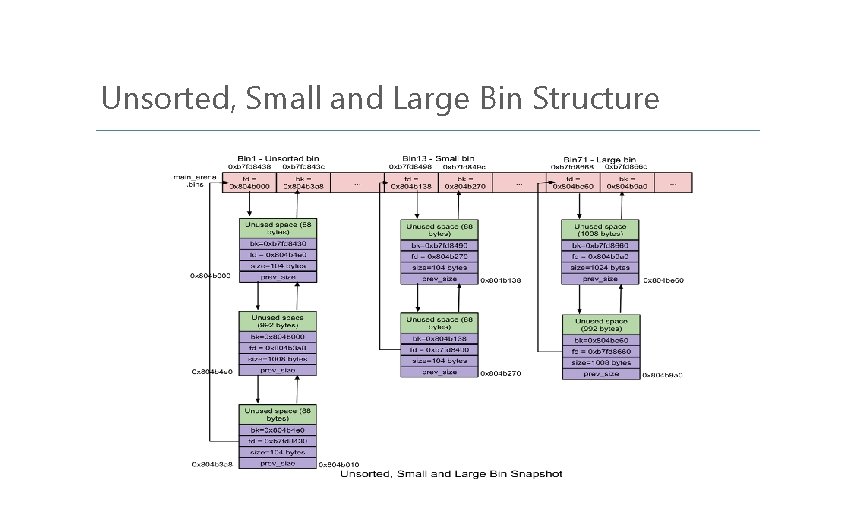
Unsorted, Small and Large Bin Structure
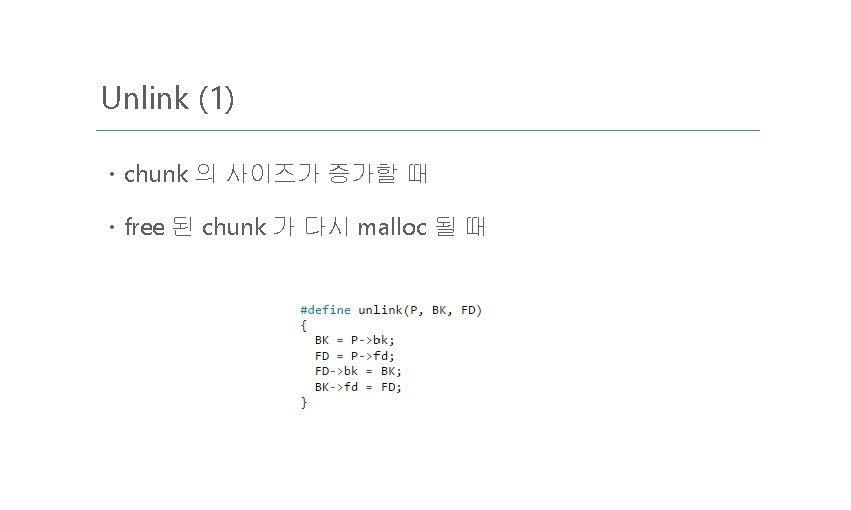
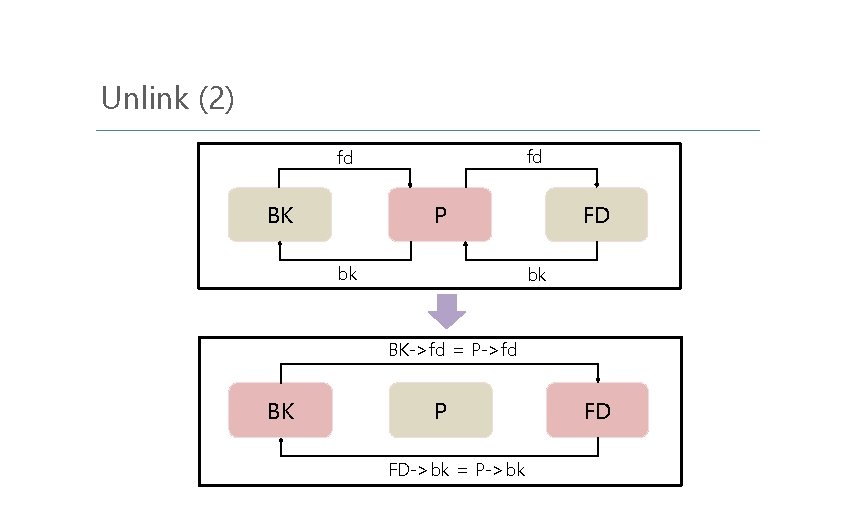
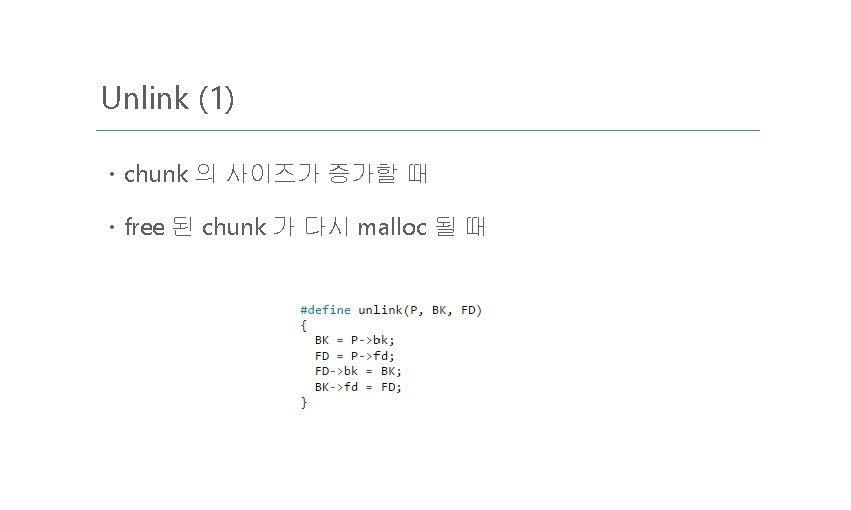
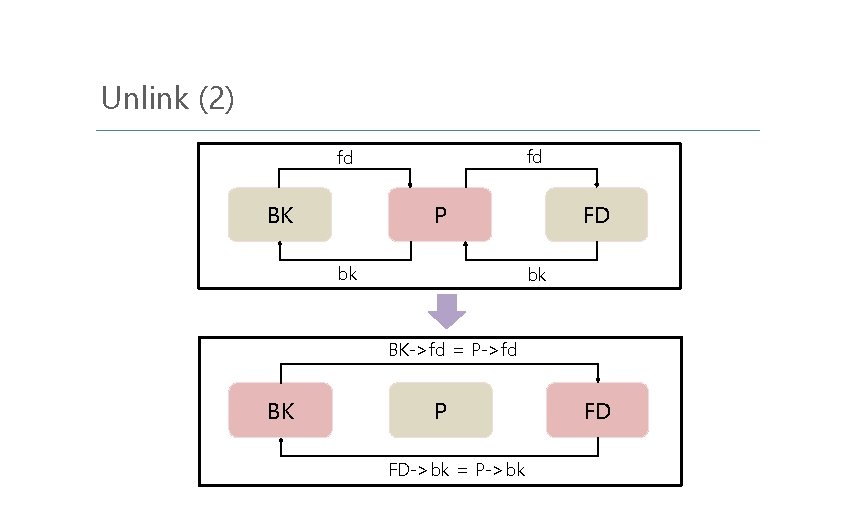
Unlink (2) fd fd BK P bk FD bk BK->fd = P->fd BK P FD->bk = P->bk FD
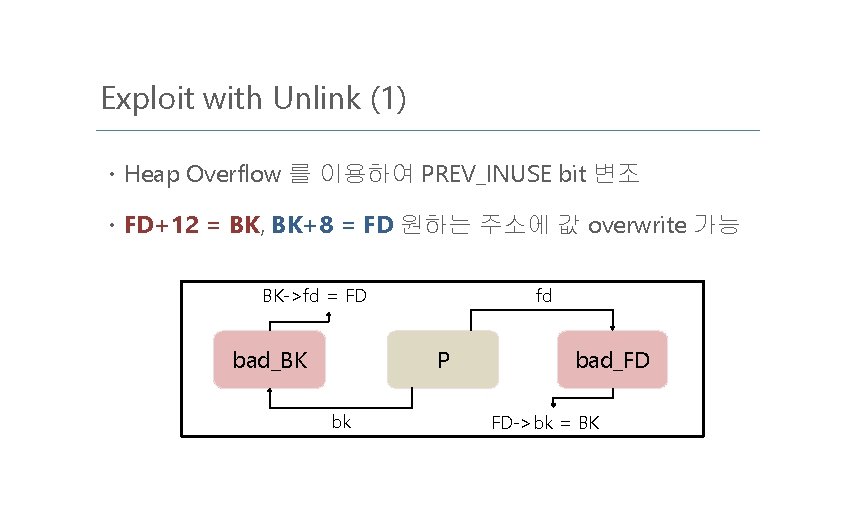
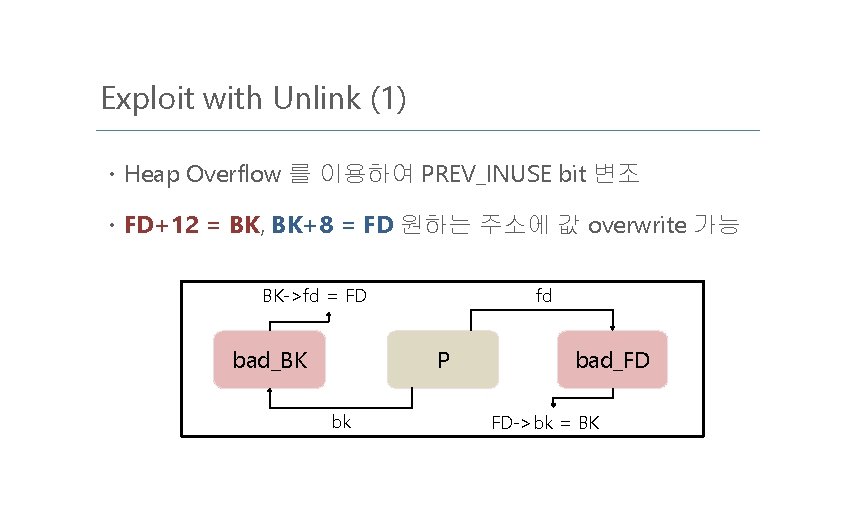
Exploit with Unlink (1) ㆍHeap Overflow 를 이용하여 PREV_INUSE bit 변조 ㆍFD+12 = BK, BK+8 = FD 원하는 주소에 값 overwrite 가능 BK->fd = FD bad_BK fd P bk bad_FD FD->bk = BK
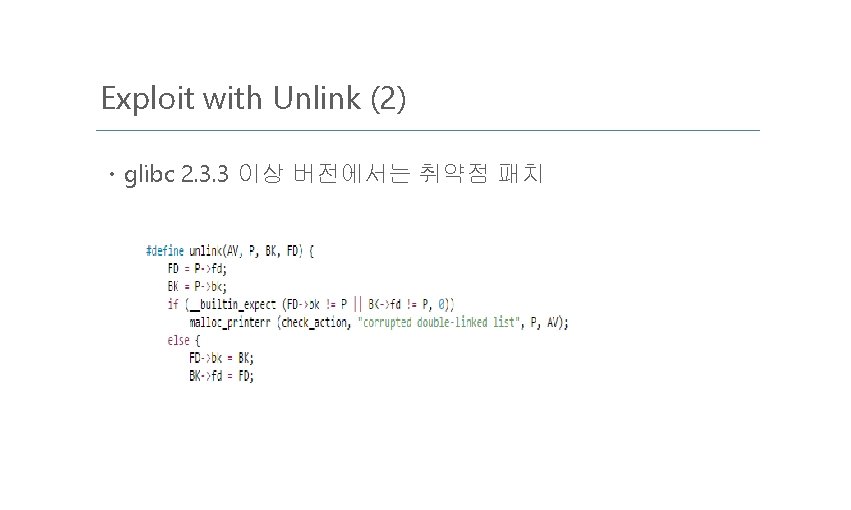
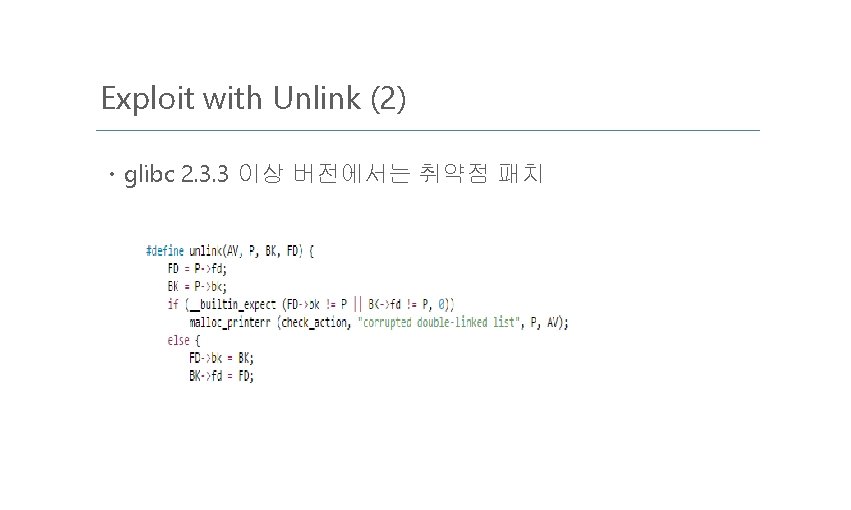
Exploit with Unlink (2) ㆍglibc 2. 3. 3 이상 버전에서는 취약점 패치
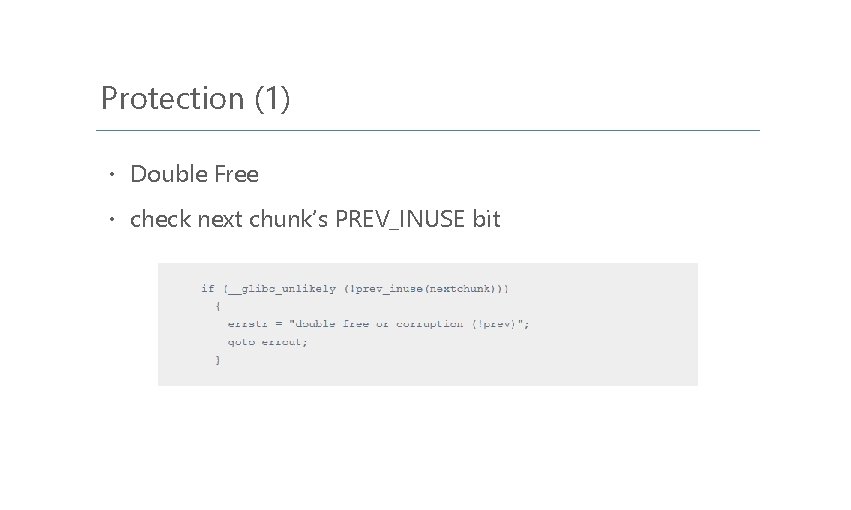
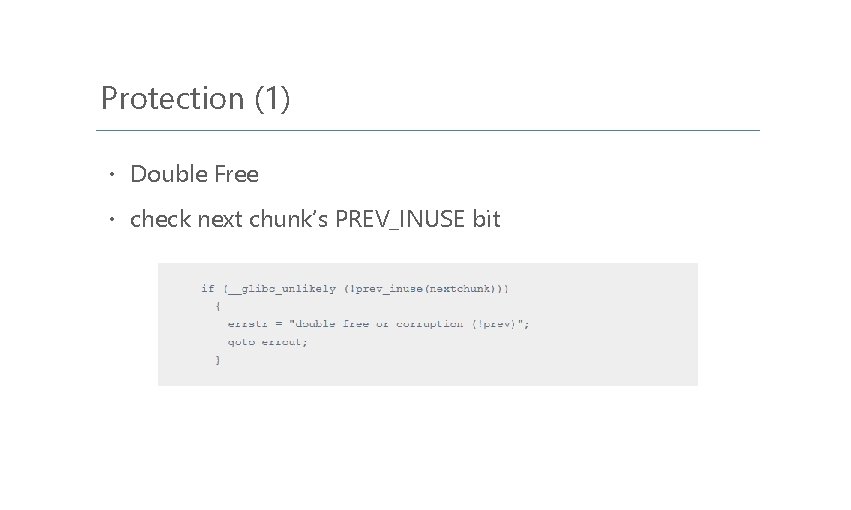
Protection (1) ㆍ Double Free ㆍ check next chunk’s PREV_INUSE bit
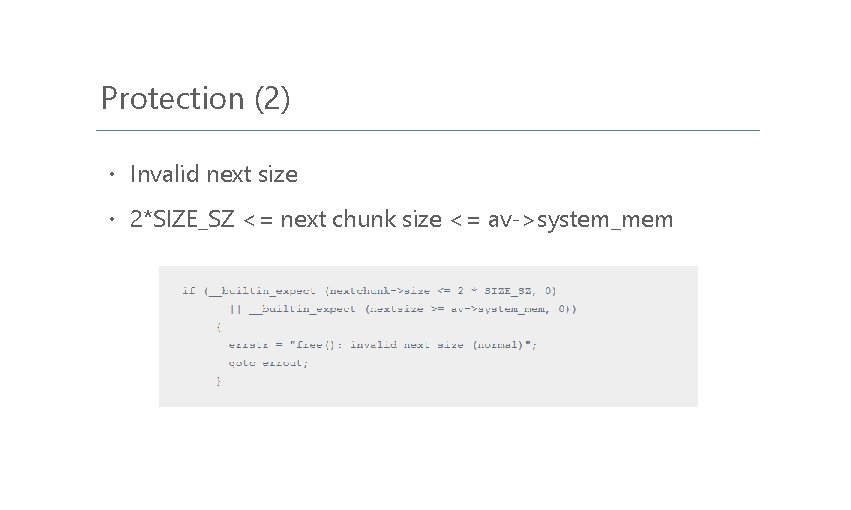
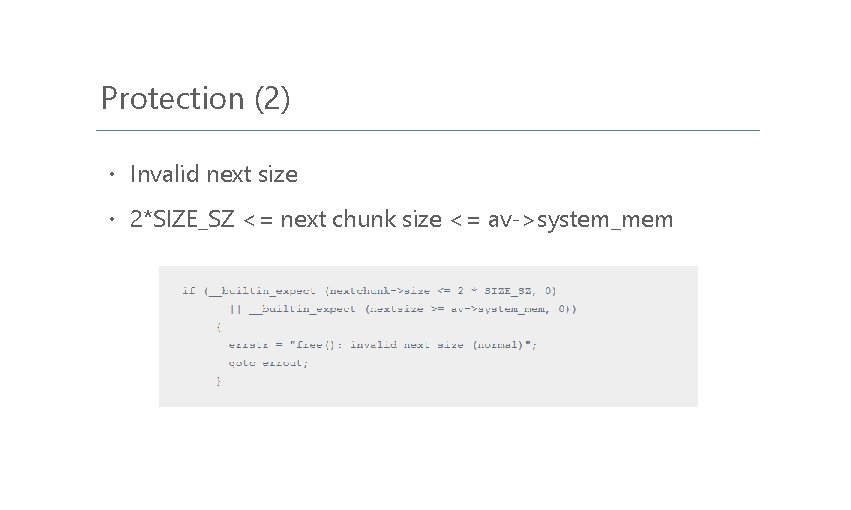
Protection (2) ㆍ Invalid next size ㆍ 2*SIZE_SZ <= next chunk size <= av->system_mem
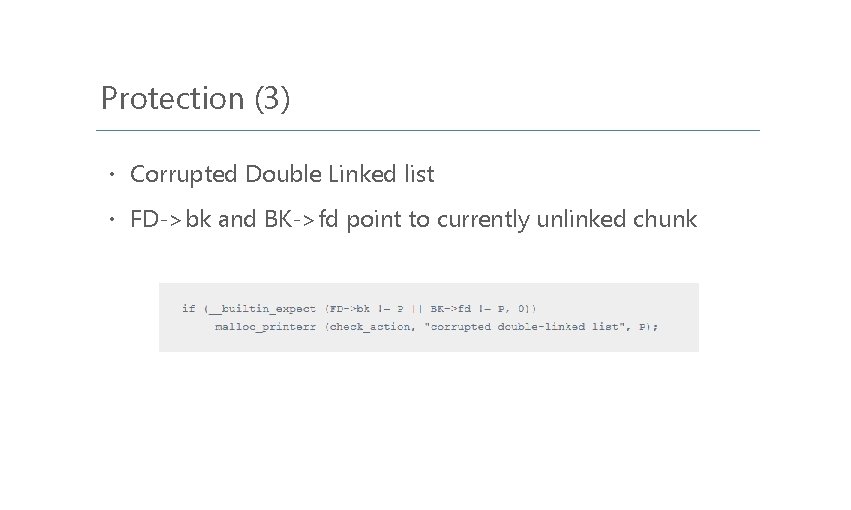
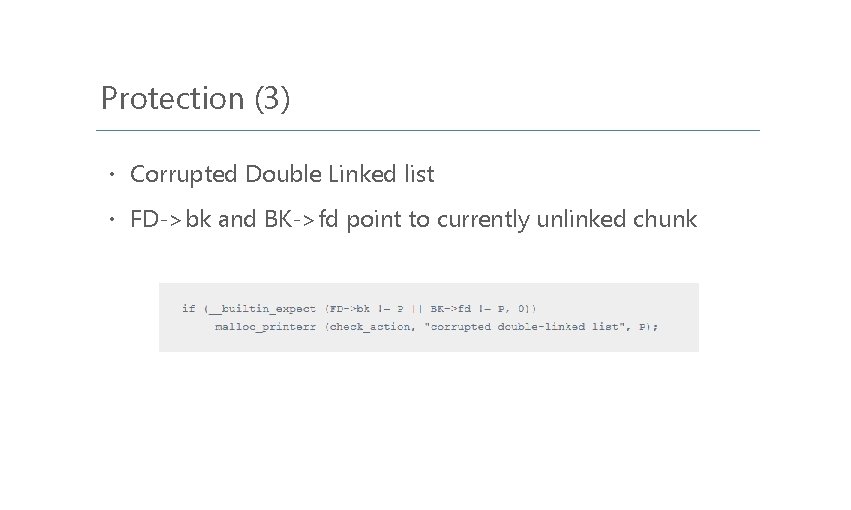
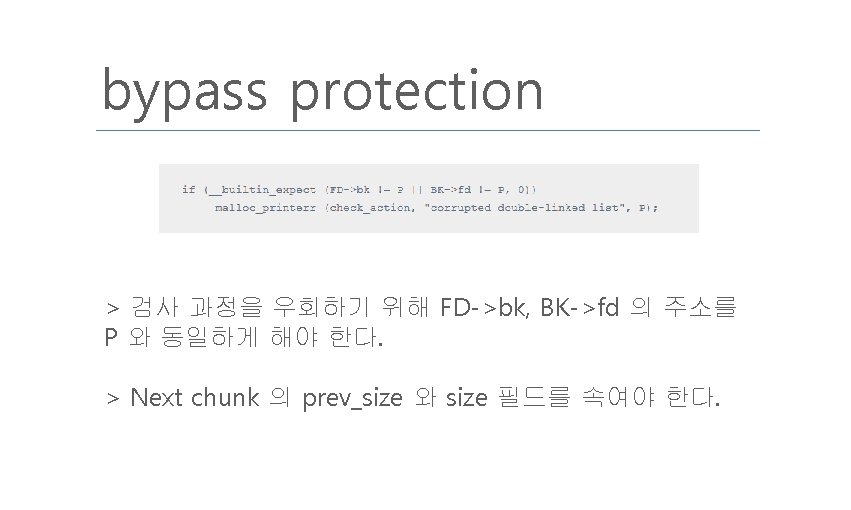
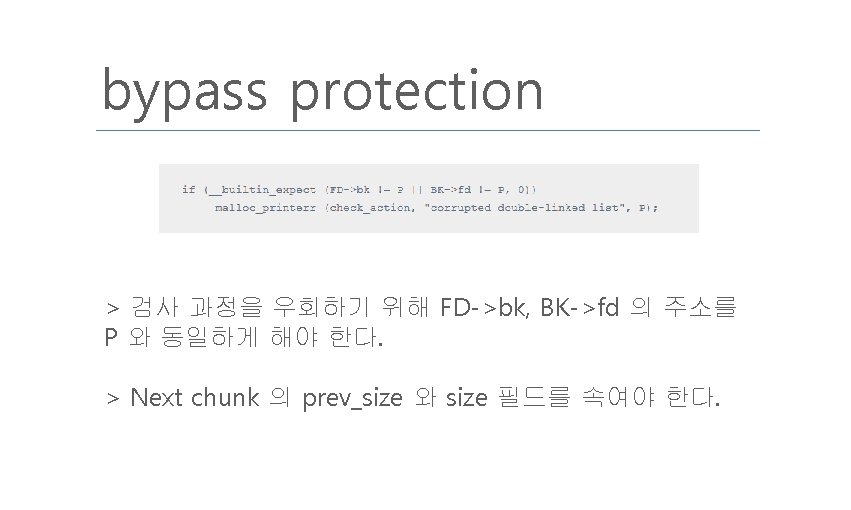
Protection (3) ㆍ Corrupted Double Linked list ㆍ FD->bk and BK->fd point to currently unlinked chunk
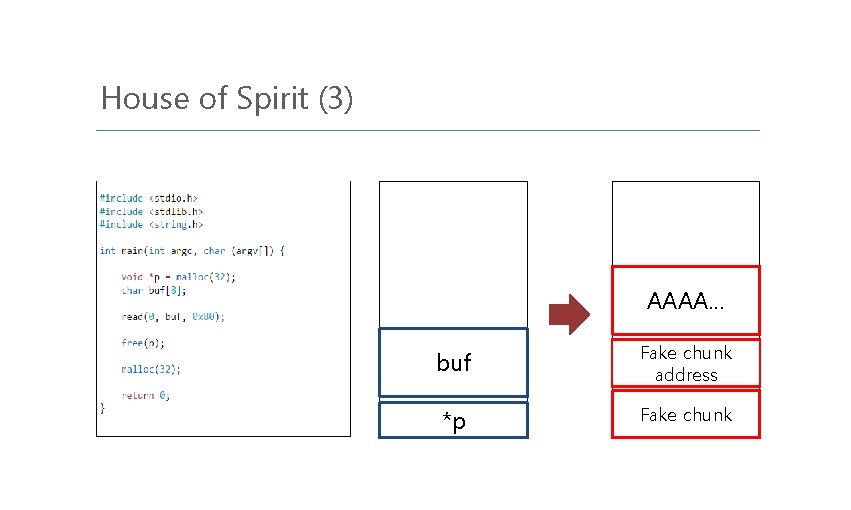
House of Spirit (1) Prerequisite : > chunk 주소를 저장하고 있는 변수를 overwrite 할 수 있어야 한다. > 위의 chunk 를 free 해야 한다. > free 한 chunk size 와 같은 chunk size 를 malloc 해야 한다. > user input 이 위의 chunk 에 복사되어야 한다.
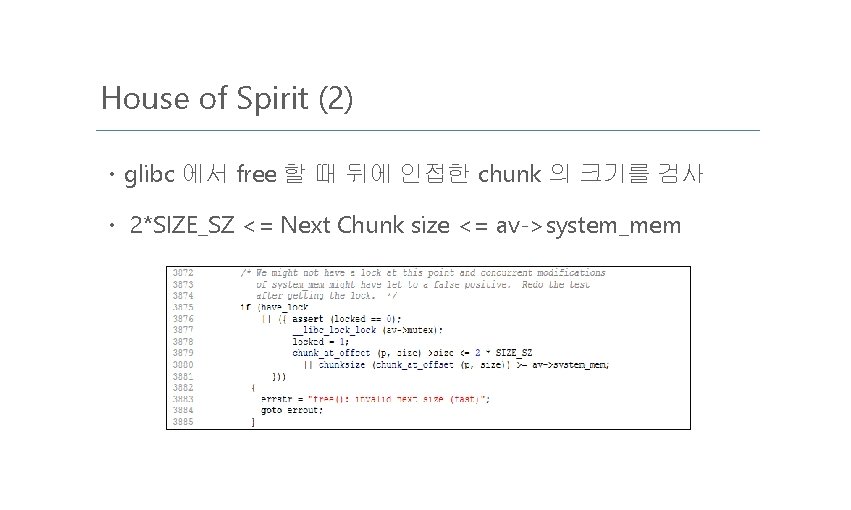
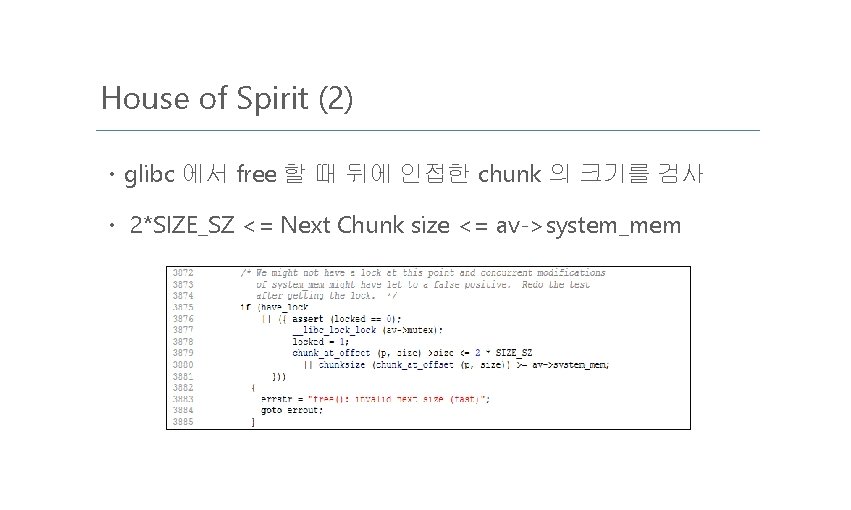
House of Spirit (2) ㆍglibc 에서 free 할 때 뒤에 인접한 chunk 의 크기를 검사 ㆍ 2*SIZE_SZ <= Next Chunk size <= av->system_mem
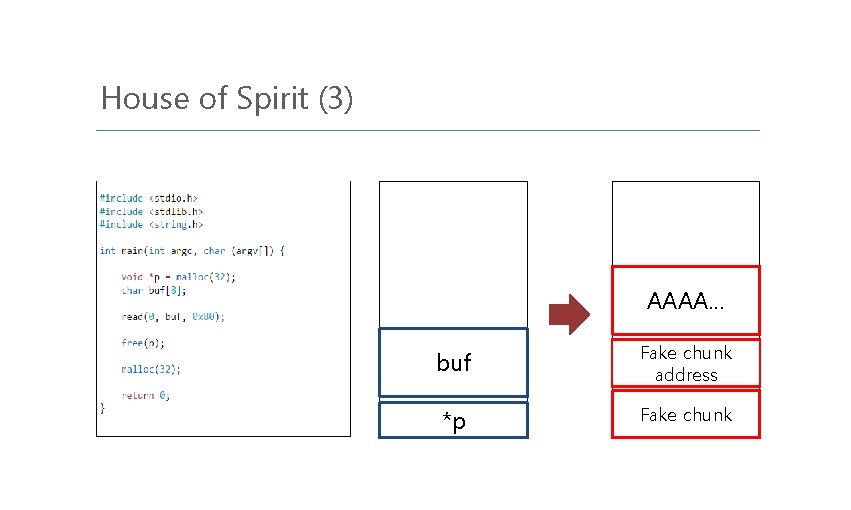
House of Spirit (3) AAAA… buf Fake chunk address *p Fake chunk
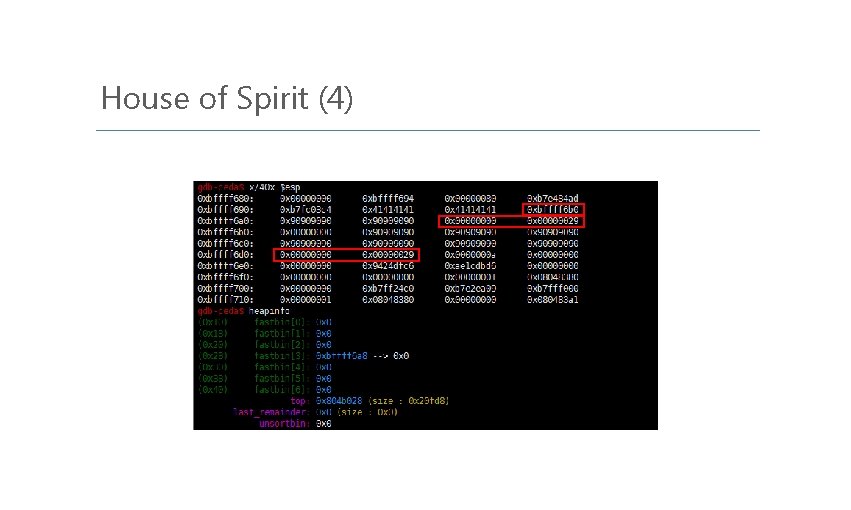
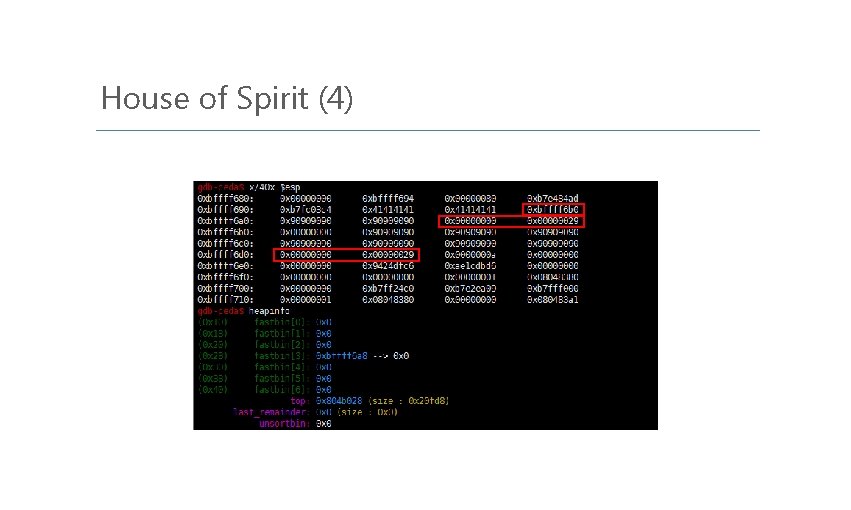
House of Spirit (4)
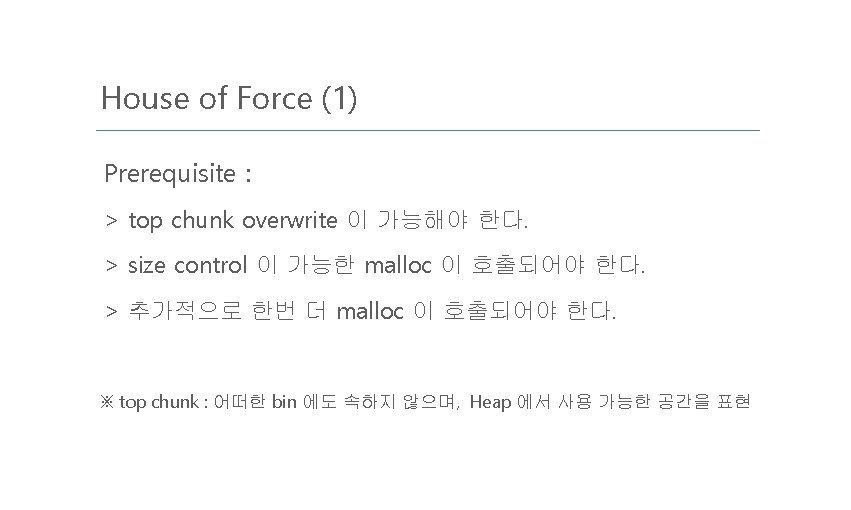
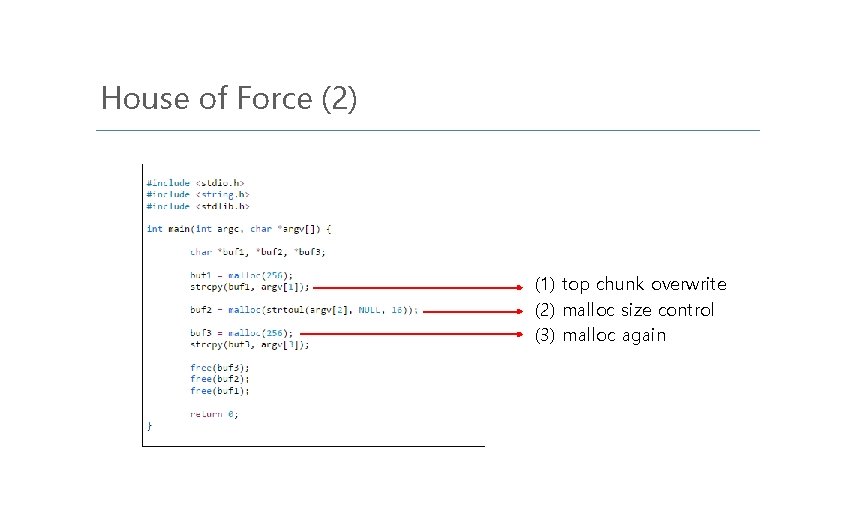
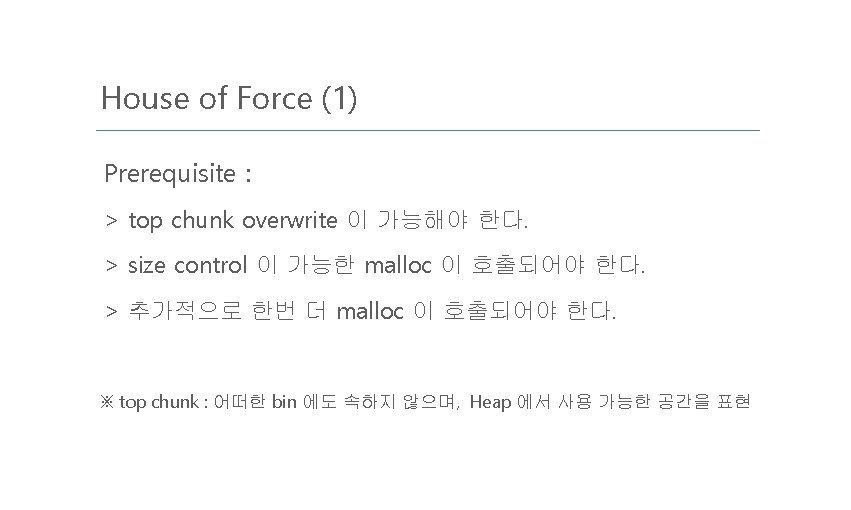
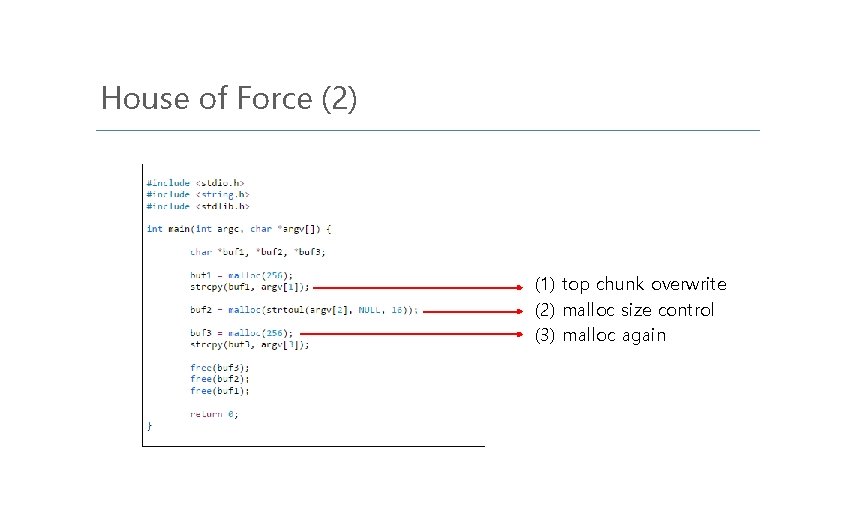
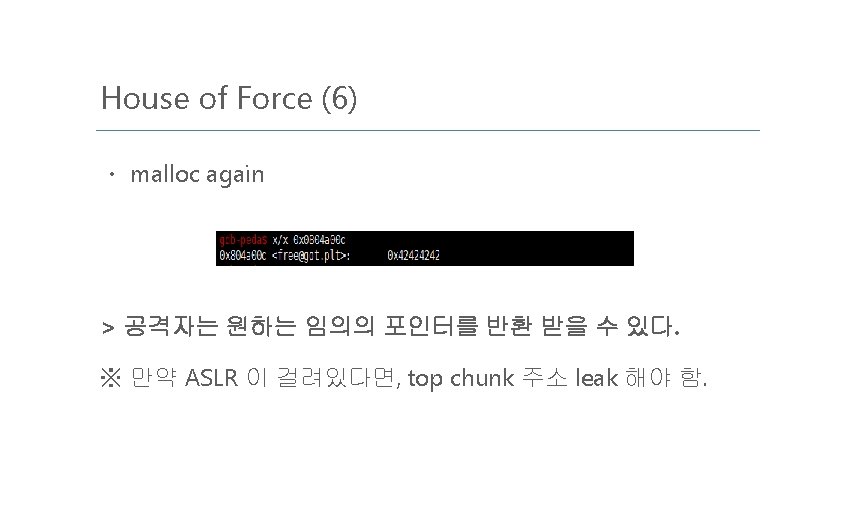
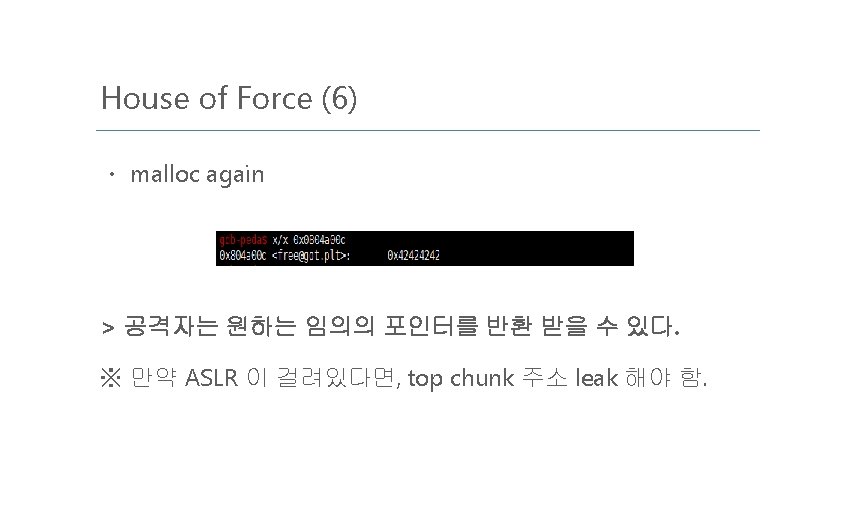
House of Force (2) (1) top chunk overwrite (2) malloc size control (3) malloc again
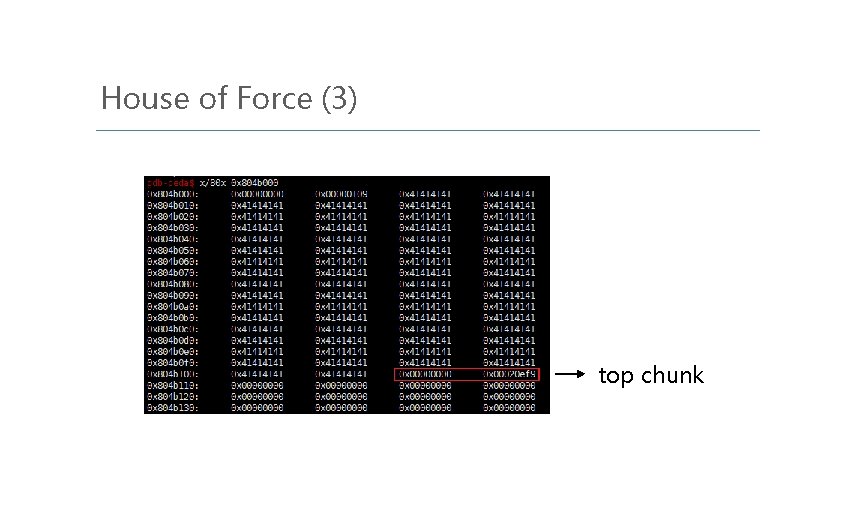
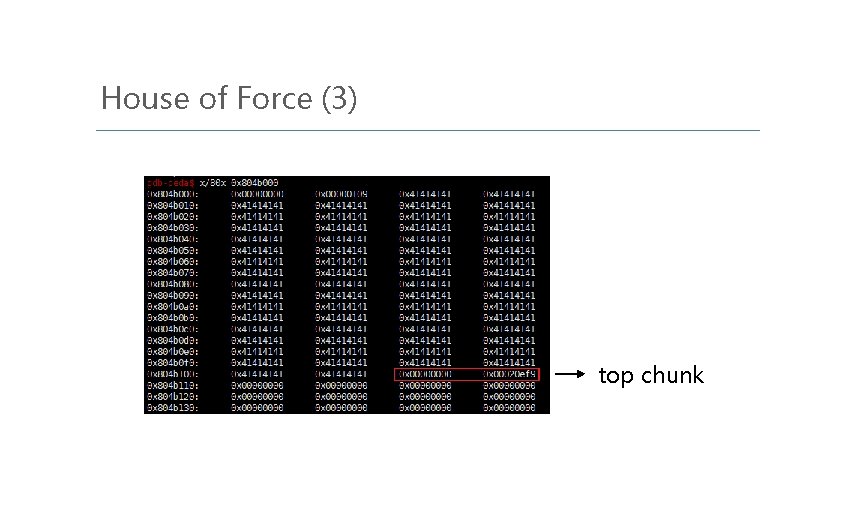
House of Force (3) top chunk
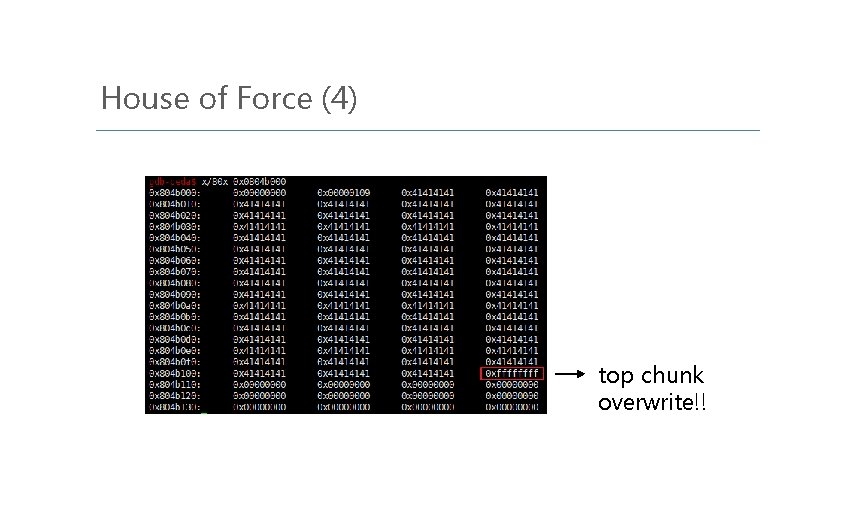
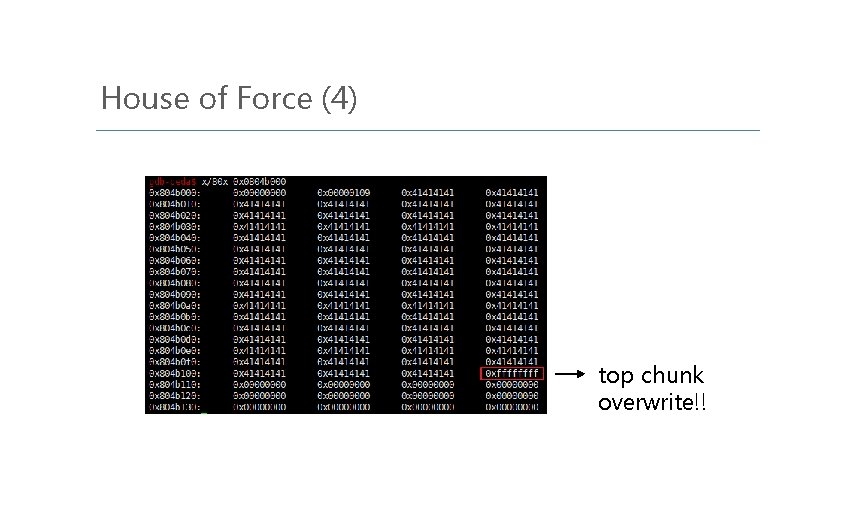
House of Force (4) top chunk overwrite!!
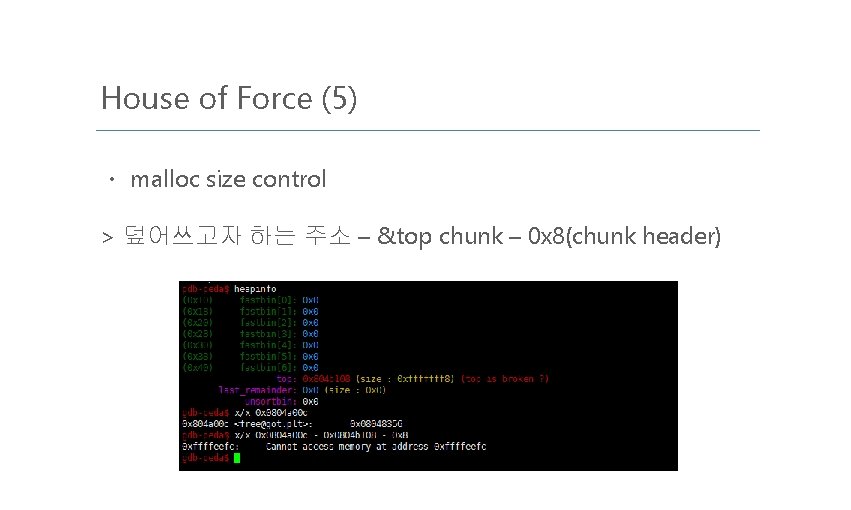
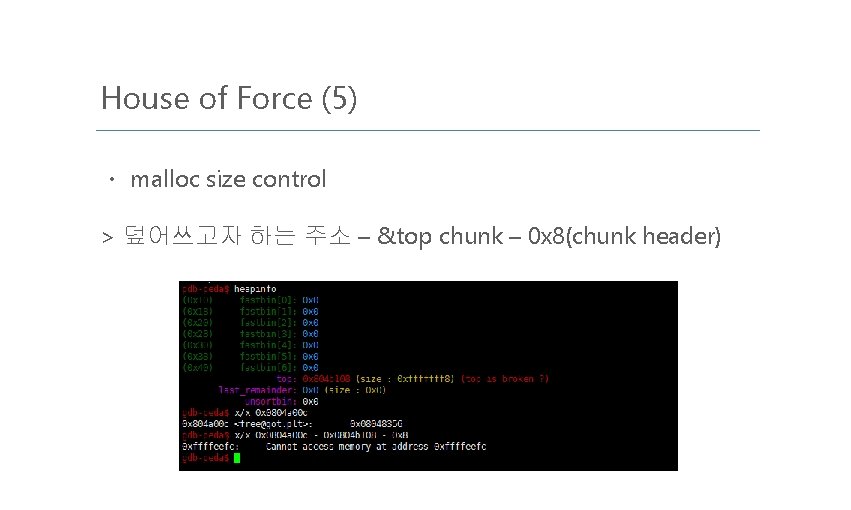
House of Force (5) ㆍ malloc size control > 덮어쓰고자 하는 주소 – &top chunk – 0 x 8(chunk header)
Reference https: //sploitfun. wordpress. com/2015/02/10/understanding-glibc-malloc/ https: //sploitfun. wordpress. com/2015/02/26/heap-overflow-using-unlink/ https: //github. com/shellphish/how 2 heap http: //phrack. org/issues/66/10. html https: //bpsecblog. wordpress. com/about/ http: //blog. naver. com/mathboy 7/220986657907