A lossless data hiding scheme based on threepixel
A lossless data hiding scheme based on threepixel block differences Ching-Chiuan Lin and Nien-Lin Hsueh Pattern Recognition, Vol. 41(4), April 2008 Pages 1415 -1425
Outline Introduction n Related Work n The Proposed Method n Experiments n Conclusions n Comments n 2
Introduction (1/3) Lossless data hiding Three-pixel block difference 3
Introduction (2/3) l Lossless data hiding l Application: l medical images, military photos, law enforcement l Challenges: l Capacity l Quality 4
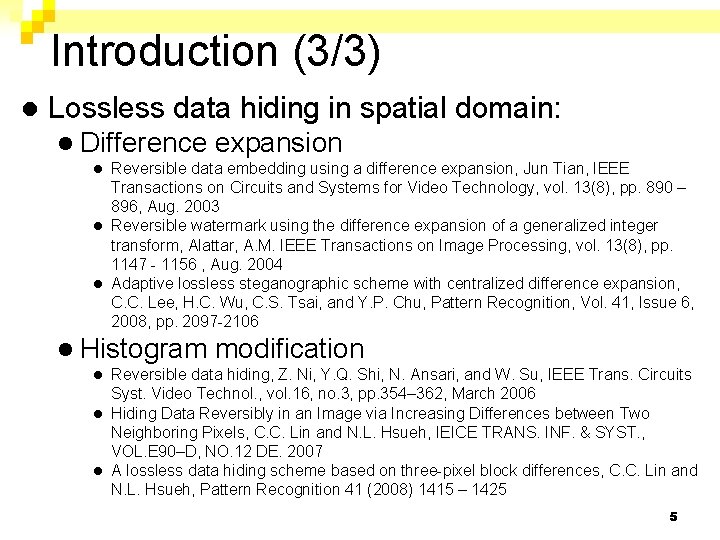
Introduction (3/3) l Lossless data hiding in spatial domain: l Difference expansion Reversible data embedding using a difference expansion, Jun Tian, IEEE Transactions on Circuits and Systems for Video Technology, vol. 13(8), pp. 890 – 896, Aug. 2003 l Reversible watermark using the difference expansion of a generalized integer transform, Alattar, A. M. IEEE Transactions on Image Processing, vol. 13(8), pp. 1147 - 1156 , Aug. 2004 l Adaptive lossless steganographic scheme with centralized difference expansion, C. C. Lee, H. C. Wu, C. S. Tsai, and Y. P. Chu, Pattern Recognition, Vol. 41, Issue 6, 2008, pp. 2097 -2106 l l Histogram modification Reversible data hiding, Z. Ni, Y. Q. Shi, N. Ansari, and W. Su, IEEE Trans. Circuits Syst. Video Technol. , vol. 16, no. 3, pp. 354– 362, March 2006 l Hiding Data Reversibly in an Image via Increasing Differences between Two Neighboring Pixels, C. C. Lin and N. L. Hsueh, IEICE TRANS. INF. & SYST. , VOL. E 90–D, NO. 12 DE. 2007 l A lossless data hiding scheme based on three-pixel block differences, C. C. Lin and N. L. Hsueh, Pattern Recognition 41 (2008) 1415 – 1425 l 5
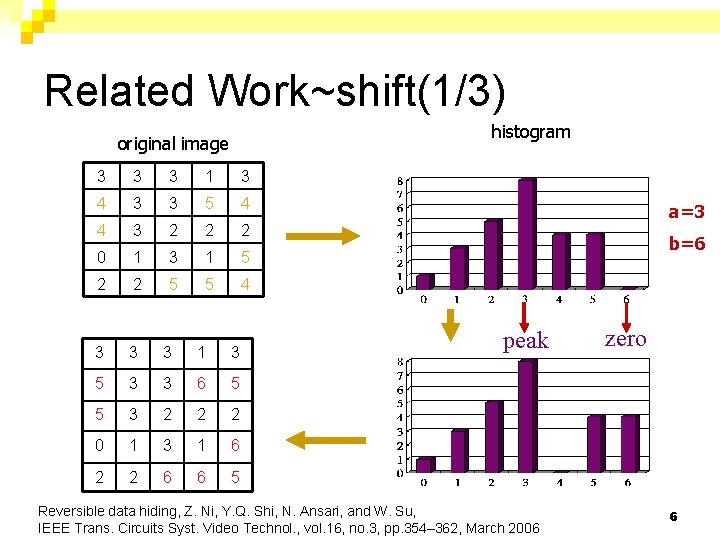
Related Work~shift(1/3) histogram original image 3 3 3 1 3 4 3 3 5 4 4 3 2 2 2 0 1 3 1 5 2 2 5 5 4 3 3 3 1 3 5 3 3 6 5 5 3 2 2 2 0 1 3 1 6 2 2 6 6 5 a=3 b=6 peak Reversible data hiding, Z. Ni, Y. Q. Shi, N. Ansari, and W. Su, IEEE Trans. Circuits Syst. Video Technol. , vol. 16, no. 3, pp. 354– 362, March 2006 zero 6
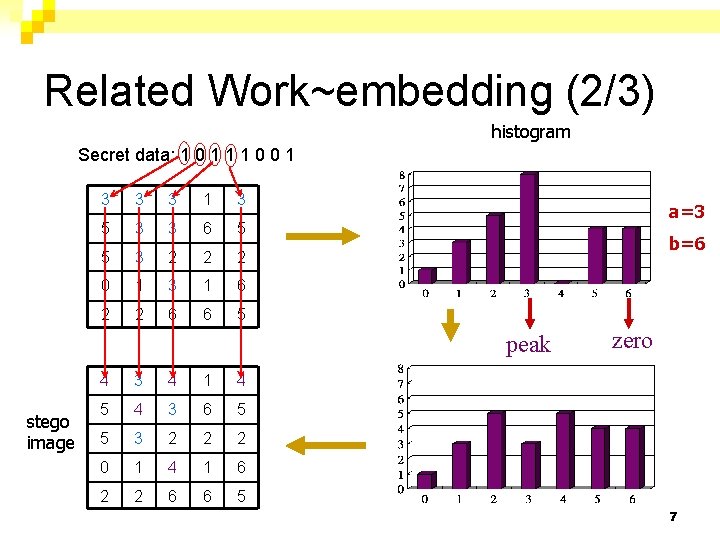
Related Work~embedding (2/3) histogram Secret data: 1 0 1 1 1 0 0 1 3 3 3 1 3 5 3 3 6 5 5 3 2 2 2 0 1 3 1 6 2 2 6 6 5 a=3 b=6 peak stego image 4 3 4 1 4 5 4 3 6 5 5 3 2 2 2 0 1 4 1 6 2 2 6 6 5 zero 7
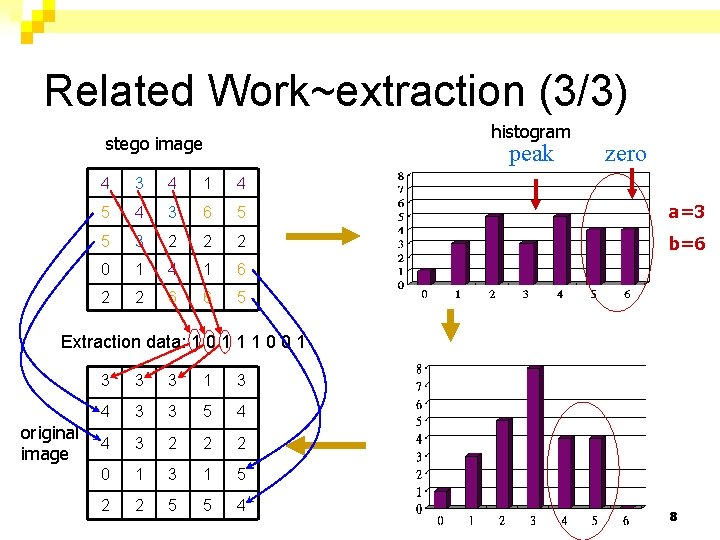
Related Work~extraction (3/3) histogram stego image peak zero 4 3 4 1 4 5 4 3 6 5 a=3 5 3 2 2 2 b=6 0 1 4 1 6 2 2 6 6 5 Extraction data: 1 0 1 1 1 0 0 1 original image 3 3 3 1 3 4 3 3 5 4 4 3 2 2 2 0 1 3 1 5 2 2 5 5 4 8
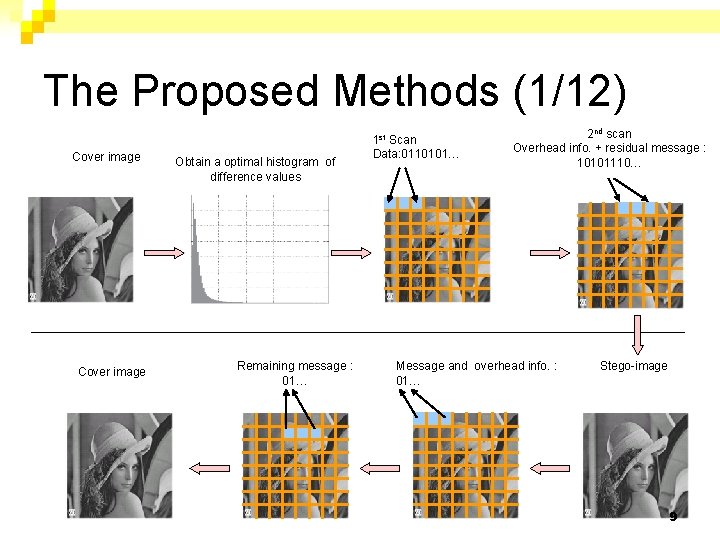
The Proposed Methods (1/12) Cover image Obtain a optimal histogram of difference values Remaining message : 01… 1 st Scan Data: 0110101… 2 nd scan Overhead info. + residual message : 10101110… Message and overhead info. : 01… Stego-image 9
10
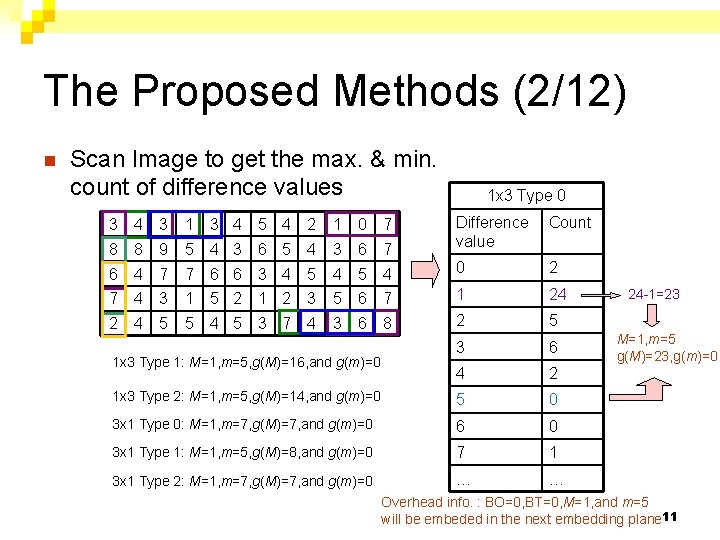
The Proposed Methods (2/12) n Scan Image to get the max. & min. count of difference values 1 x 3 Type 0 3 4 3 1 3 4 5 4 2 1 0 7 8 8 9 5 4 3 6 7 Difference Count value 6 4 7 7 6 6 3 4 5 4 0 2 7 4 3 1 5 2 1 2 3 5 6 7 1 24 2 4 5 5 4 5 3 7 4 3 6 8 2 5 3 6 4 2 1 x 3 Type 2: M=1, m=5, g(M)=14, and g(m)=0 5 0 3 x 1 Type 0: M=1, m=7, g(M)=7, and g(m)=0 6 0 3 x 1 Type 1: M=1, m=5, g(M)=8, and g(m)=0 7 1 3 x 1 Type 2: M=1, m=7, g(M)=7, and g(m)=0 … … 1 x 3 Type 1: M=1, m=5, g(M)=16, and g(m)=0 24 -1=23 M=1, m=5 g(M)=23, g(m)=0 Overhead info. : BO=0, BT=0, M=1, and m=5 will be embeded in the next embedding plane 11
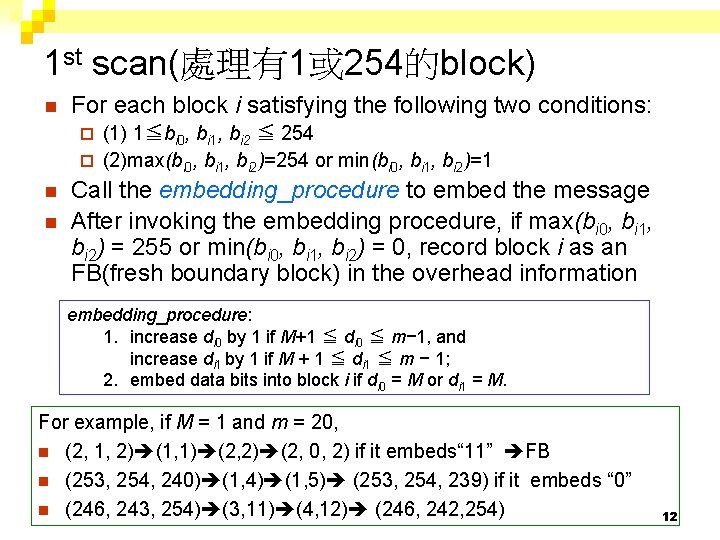
1 st scan(處理有1或 254的block) n For each block i satisfying the following two conditions: (1) 1≦bi 0, bi 1, bi 2 ≦ 254 ¨ (2)max(bi 0, bi 1, bi 2)=254 or min(bi 0, bi 1, bi 2)=1 ¨ n n Call the embedding_procedure to embed the message After invoking the embedding procedure, if max(bi 0, bi 1, bi 2) = 255 or min(bi 0, bi 1, bi 2) = 0, record block i as an FB(fresh boundary block) in the overhead information embedding_procedure: 1. increase di 0 by 1 if M+1 ≦ di 0 ≦ m− 1, and increase di 1 by 1 if M + 1 ≦ di 1 ≦ m − 1; 2. embed data bits into block i if di 0 = M or di 1 = M. For example, if M = 1 and m = 20, n (2, 1, 2) (1, 1) (2, 2) (2, 0, 2) if it embeds“ 11” FB n (253, 254, 240) (1, 4) (1, 5) (253, 254, 239) if it embeds “ 0” n (246, 243, 254) (3, 11) (4, 12) (246, 242, 254) 12
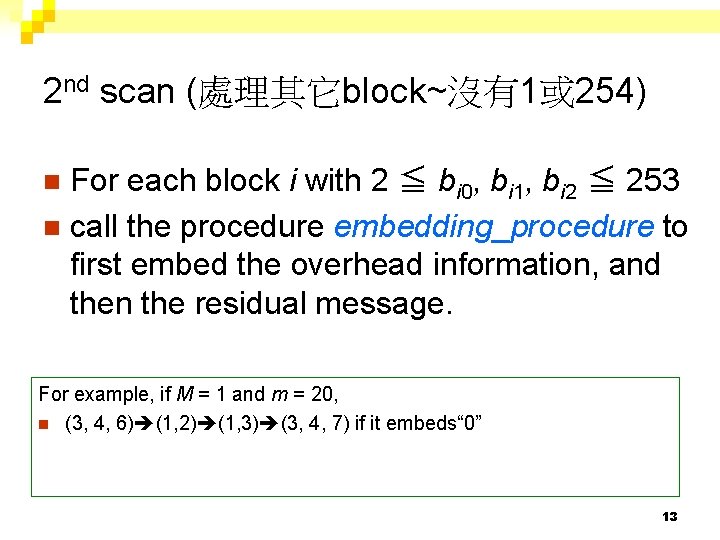
2 nd scan (處理其它block~沒有1或 254) For each block i with 2 ≦ bi 0, bi 1, bi 2 ≦ 253 n call the procedure embedding_procedure to first embed the overhead information, and then the residual message. n For example, if M = 1 and m = 20, n (3, 4, 6) (1, 2) (1, 3) (3, 4, 7) if it embeds“ 0” 13
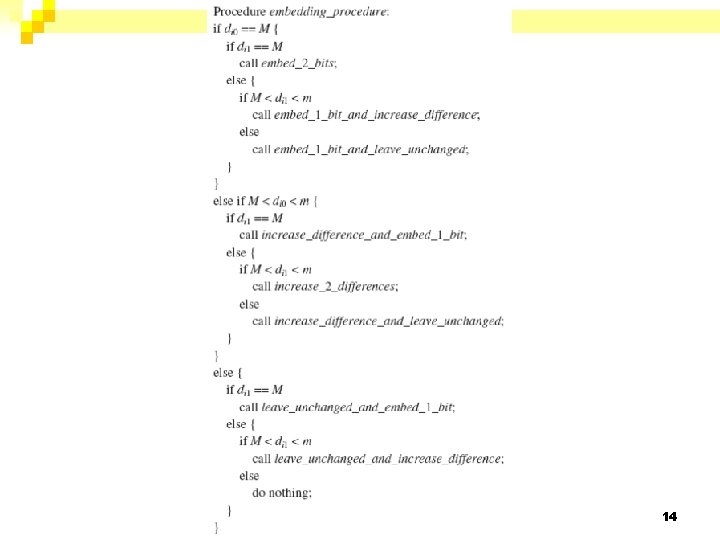
14
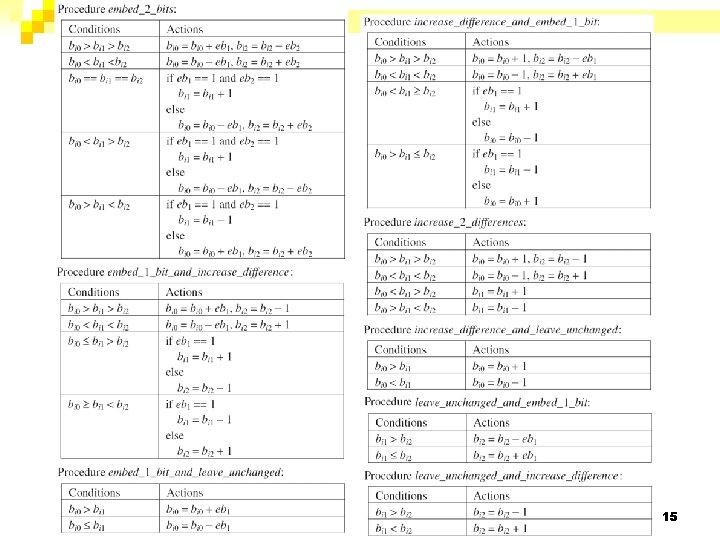
15
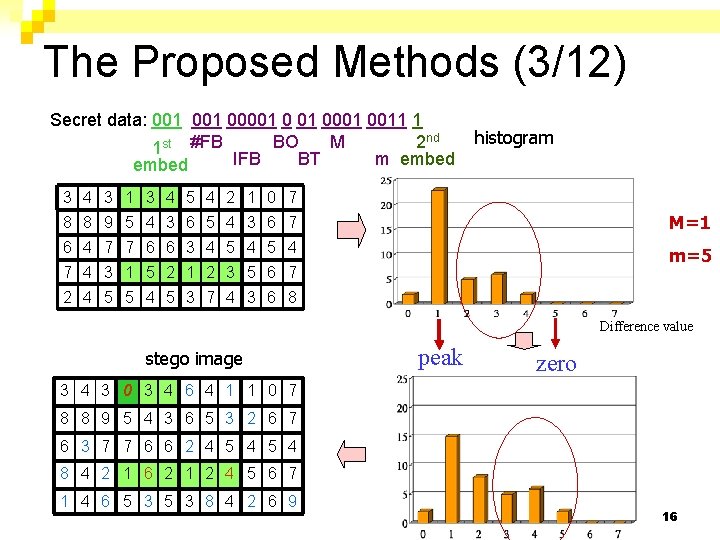
The Proposed Methods (3/12) Secret data: 001 00001 0011 1 M BO 2 nd 1 st #FB IFB BT m embed histogram 3 4 3 1 3 4 5 4 2 1 0 7 8 8 9 5 4 3 6 7 M=1 6 4 7 7 6 6 3 4 5 4 m=5 7 4 3 1 5 2 1 2 3 5 6 7 2 4 5 5 4 5 3 7 4 3 6 8 Difference value stego image peak zero 3 4 3 0 3 4 6 4 1 1 0 7 8 8 9 5 4 3 6 5 3 2 6 7 6 3 7 7 6 6 2 4 5 4 8 4 2 1 6 2 1 2 4 5 6 7 1 4 6 5 3 8 4 2 6 9 16
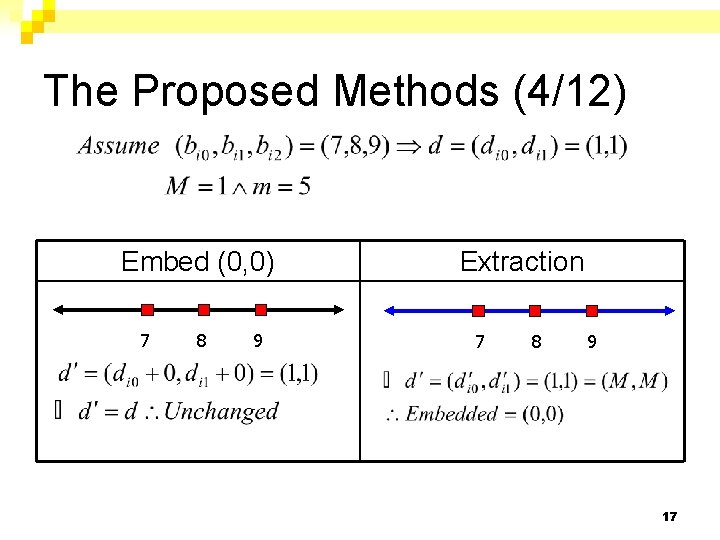
The Proposed Methods (4/12) Embed (0, 0) 7 8 9 Extraction 7 8 9 17
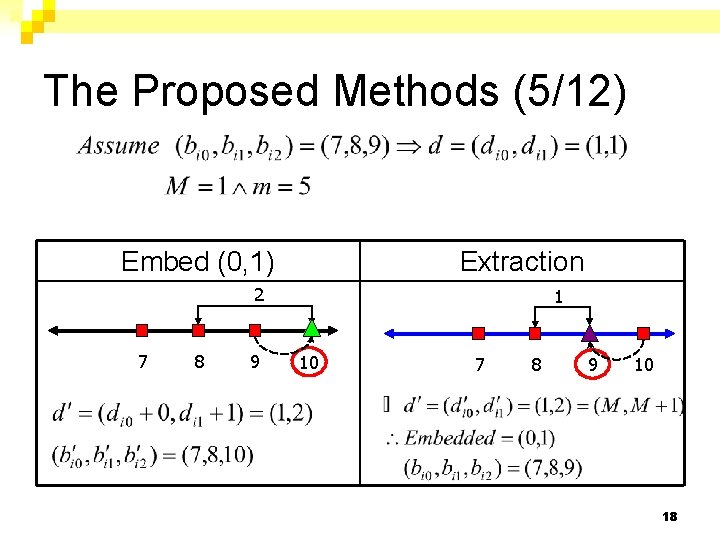
The Proposed Methods (5/12) Embed (0, 1) Extraction 2 7 8 9 1 10 7 8 9 10 18
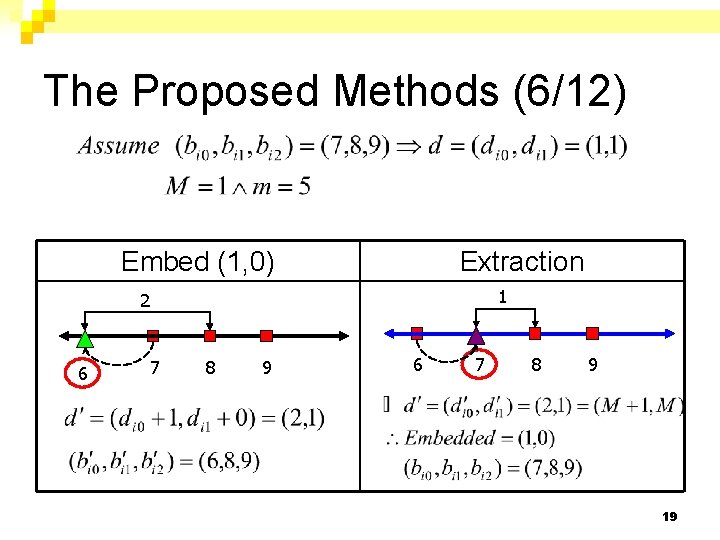
The Proposed Methods (6/12) Embed (1, 0) Extraction 1 2 6 7 8 9 19
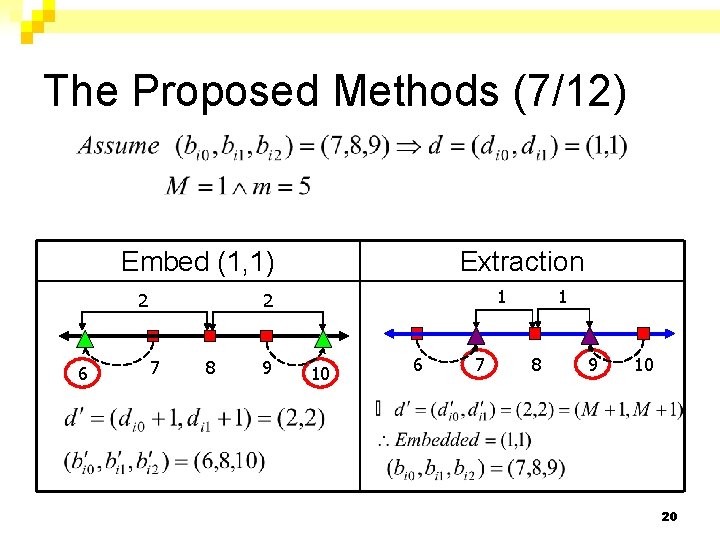
The Proposed Methods (7/12) Embed (1, 1) 1 2 2 6 Extraction 7 8 9 10 6 7 1 8 9 10 20
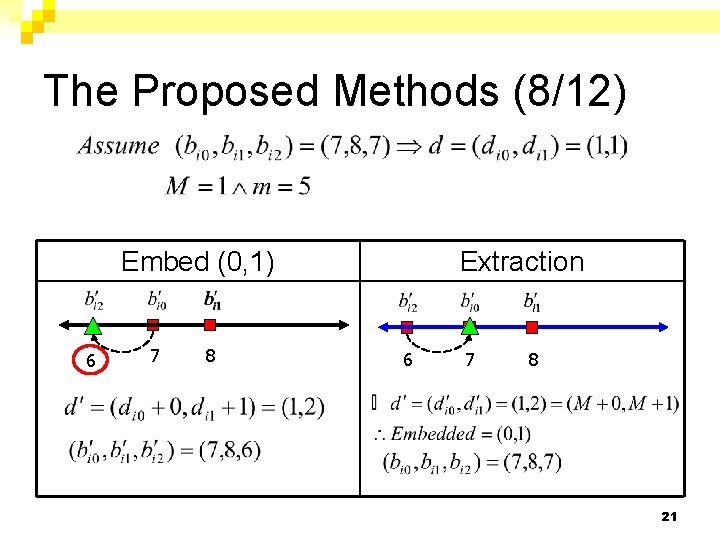
The Proposed Methods (8/12) Embed (0, 1) 6 7 8 Extraction 6 7 8 21
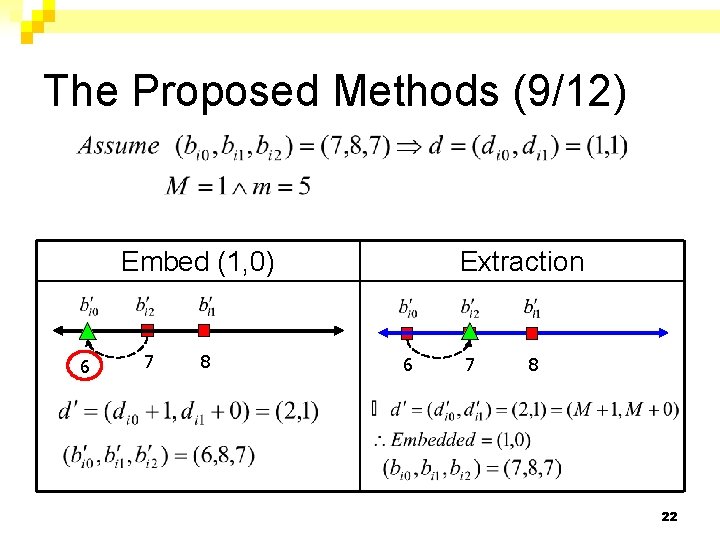
The Proposed Methods (9/12) Embed (1, 0) 6 7 8 Extraction 6 7 8 22
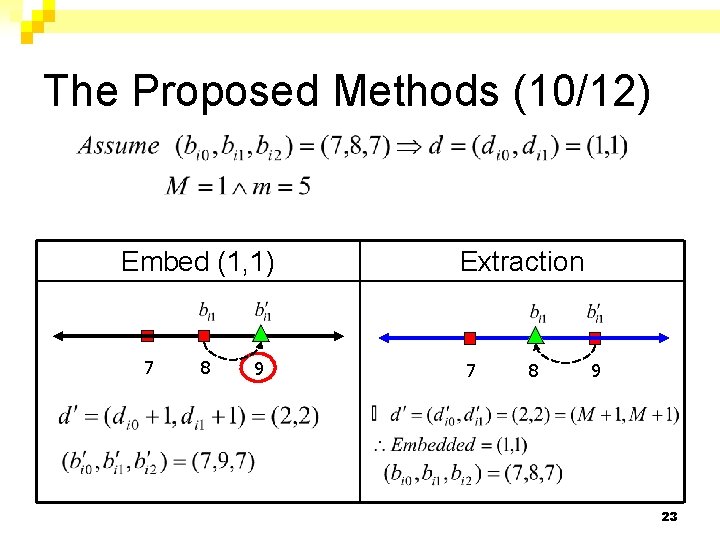
The Proposed Methods (10/12) Embed (1, 1) 7 8 9 Extraction 7 8 9 23
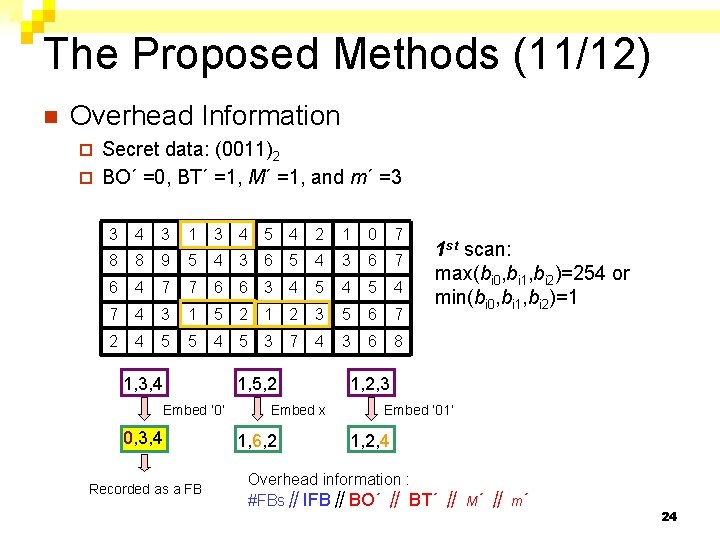
The Proposed Methods (11/12) n Overhead Information Secret data: (0011)2 ¨ BO´ =0, BT´ =1, M´ =1, and m´ =3 ¨ 3 4 3 1 3 4 5 4 2 1 0 7 8 8 9 5 4 3 6 7 6 4 7 7 6 6 3 4 5 4 7 4 3 1 5 2 1 2 3 5 6 7 2 4 5 5 4 5 3 7 4 3 6 8 1, 3, 4 Embed ‘ 0’ 0, 3, 4 Recorded as a FB 1, 5, 2 Embed x 1, 6, 2 1 st scan: max(bi 0, bi 1, bi 2)=254 or min(bi 0, bi 1, bi 2)=1 1, 2, 3 Embed ’ 01’ 1, 2, 4 Overhead information : #FBs∥IFB∥BO´ ∥ BT´ ∥ M´ ∥ m´ 24
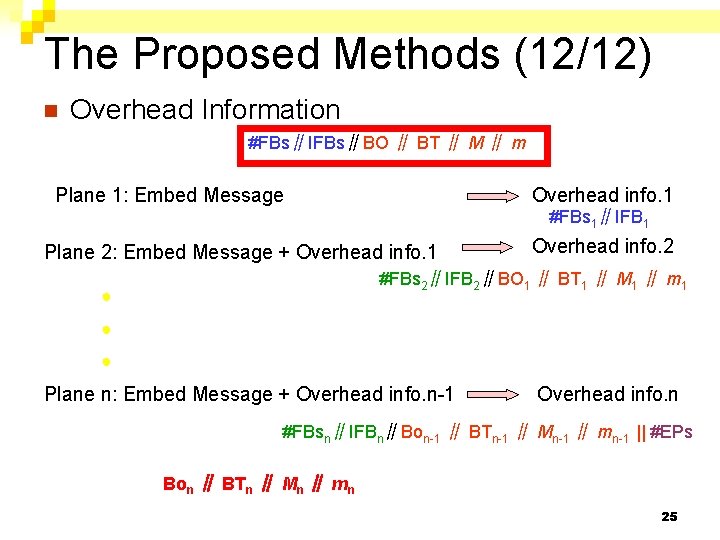
The Proposed Methods (12/12) n Overhead Information #FBs∥IFBs∥BO ∥ BT ∥ M ∥ m Plane 1: Embed Message Overhead info. 1 #FBs 1∥IFB 1 Plane 2: Embed Message + Overhead info. 1 Overhead info. 2 #FBs 2∥IFB 2∥BO 1 ∥ BT 1 ∥ M 1 ∥ m 1 ● ● ● Plane n: Embed Message + Overhead info. n-1 Overhead info. n #FBsn∥IFBn∥Bon-1 ∥ BTn-1 ∥ Mn-1 ∥ mn-1 || #EPs Bon ∥ BTn ∥ Mn ∥ mn 25
26
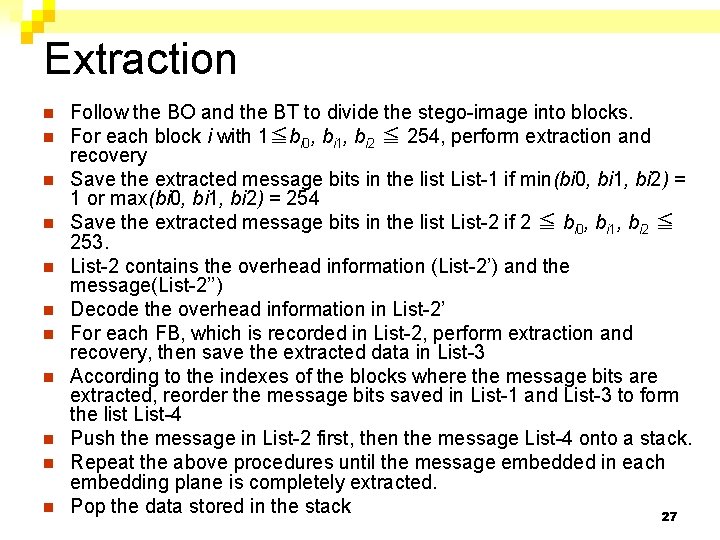
Extraction n n Follow the BO and the BT to divide the stego-image into blocks. For each block i with 1≦bi 0, bi 1, bi 2 ≦ 254, perform extraction and recovery Save the extracted message bits in the list List-1 if min(bi 0, bi 1, bi 2) = 1 or max(bi 0, bi 1, bi 2) = 254 Save the extracted message bits in the list List-2 if 2 ≦ bi 0, bi 1, bi 2 ≦ 253. List-2 contains the overhead information (List-2’) and the message(List-2’’) Decode the overhead information in List-2’ For each FB, which is recorded in List-2, perform extraction and recovery, then save the extracted data in List-3 According to the indexes of the blocks where the message bits are extracted, reorder the message bits saved in List-1 and List-3 to form the list List-4 Push the message in List-2 first, then the message List-4 onto a stack. Repeat the above procedures until the message embedded in each embedding plane is completely extracted. Pop the data stored in the stack 27
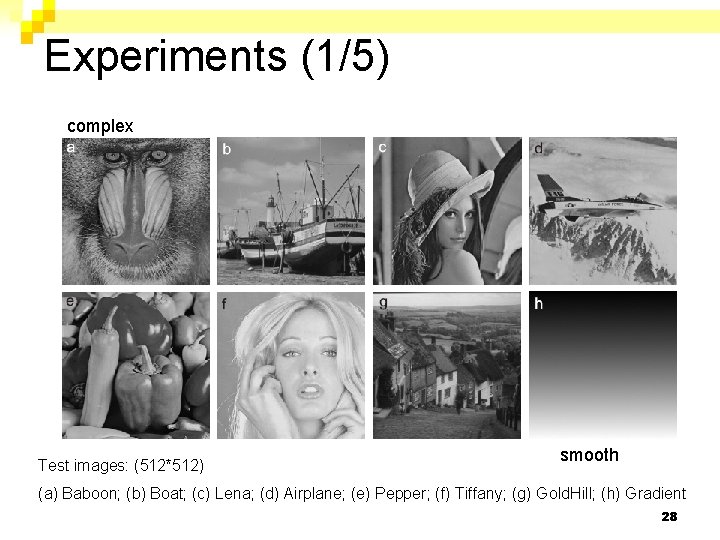
Experiments (1/5) complex Test images: (512*512) smooth (a) Baboon; (b) Boat; (c) Lena; (d) Airplane; (e) Pepper; (f) Tiffany; (g) Gold. Hill; (h) Gradient 28
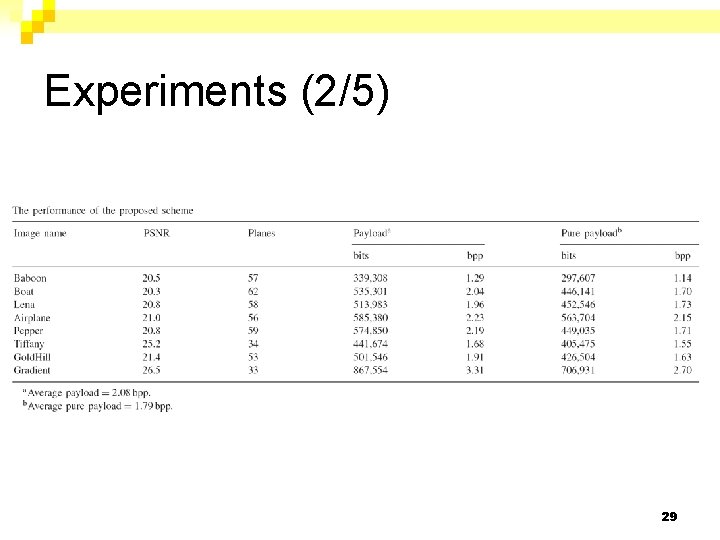
Experiments (2/5) 29
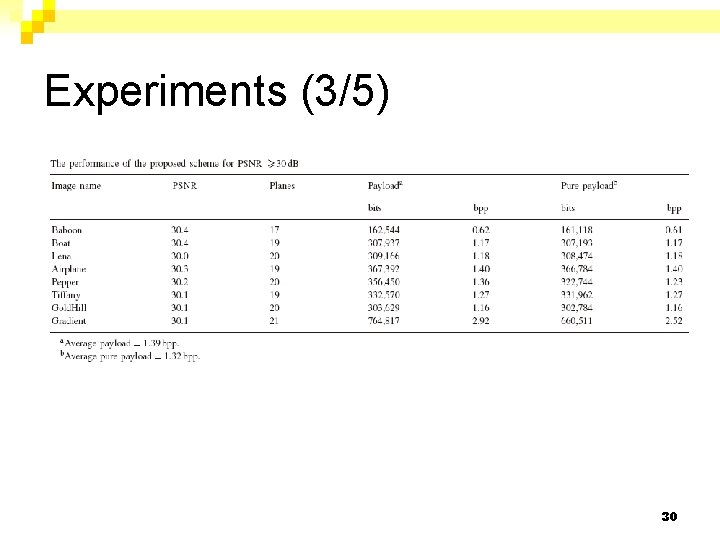
Experiments (3/5) 30
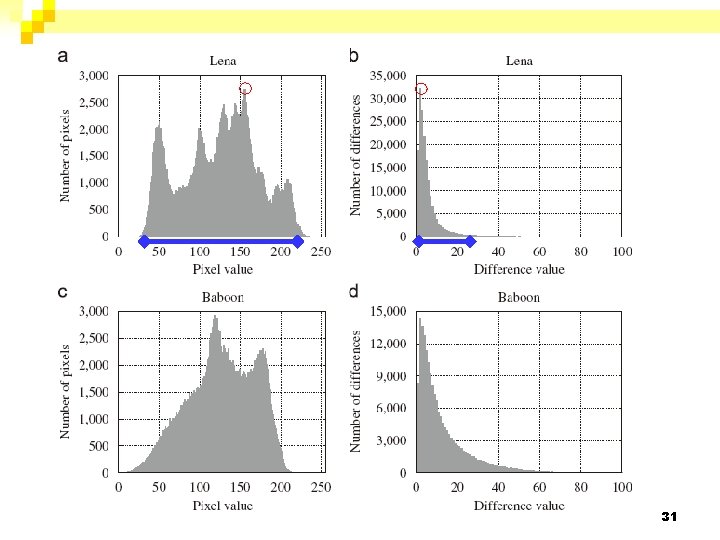
31
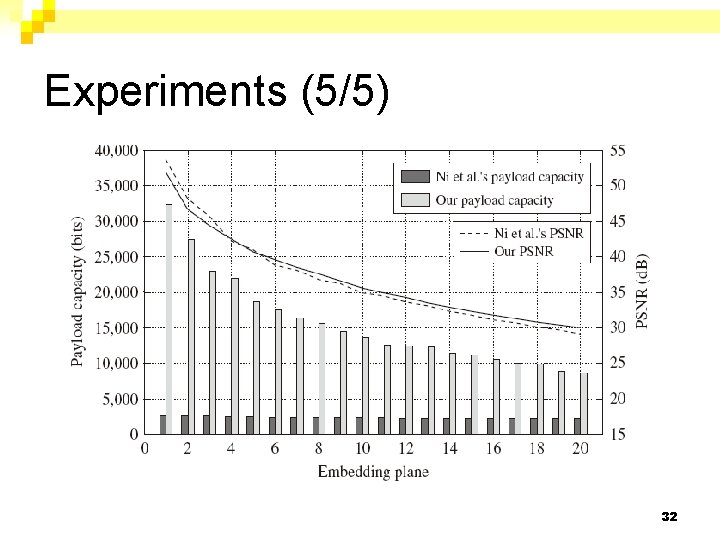
Experiments (5/5) 32
Conclusions For PSNR≧ 30 d. B, the pure payload can be up to 1. 32 bpp, among the test images. n The payload capacity of the proposed scheme is about six to ten times higher than that of Ni et al. ’s algorithm. n The proposed scheme can provide a high payload capacity and better image quality for applications that losslessly embed a message in a cover image. n 33
Comments n Generalized ¨ 3 -pexel block(2/3) 4 -pexel block(3/4) n- pexel block(n/n-1) n Difference between two neighbor pixels take the medium value as a reference value while calculating the difference values 34
35
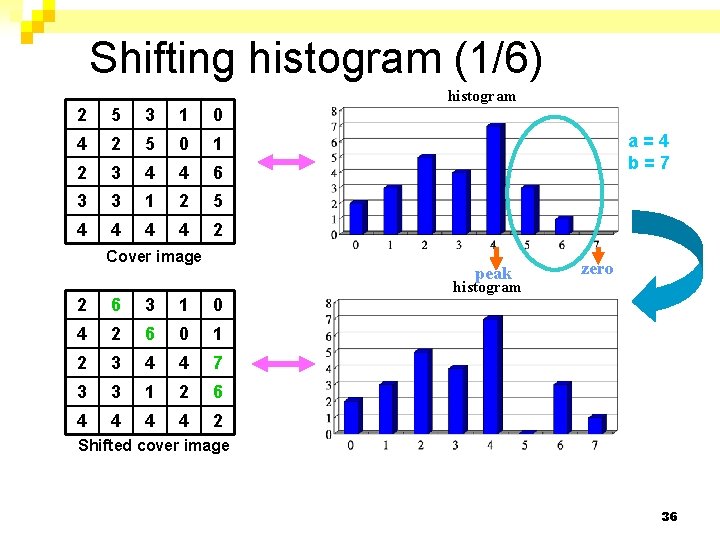
Shifting histogram (1/6) 2 5 3 1 0 4 2 5 0 1 2 3 4 4 6 3 3 1 2 5 4 4 2 Cover image histogram a=4 b=7 peak 2 6 3 1 0 4 2 6 0 1 2 3 4 4 7 3 3 1 2 6 4 4 2 zero histogram Shifted cover image 36 36
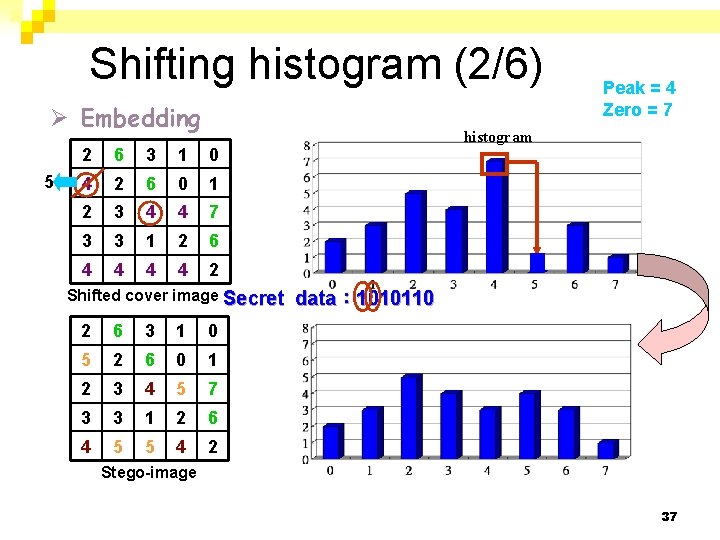
Shifting histogram (2/6) Ø Embedding 5 2 6 3 1 0 4 2 6 0 1 2 3 4 4 7 3 3 1 2 6 4 4 2 Shifted cover image Secret 2 6 3 1 0 5 2 6 0 1 2 3 4 5 7 3 3 1 2 6 4 5 5 4 2 Peak = 4 Zero = 7 histogram data: 1010110 Stego-image 37 37
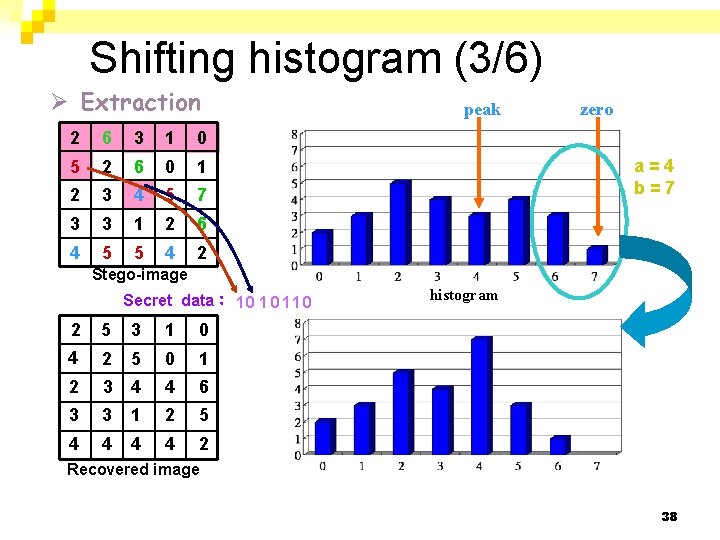
Shifting histogram (3/6) Ø Extraction 2 6 3 1 0 5 2 6 0 1 2 3 4 5 7 3 3 1 2 6 4 5 5 4 2 peak zero a=4 b=7 Stego-image Secret data: 10 1 0 11 0 2 5 3 1 0 4 2 5 0 1 2 3 4 4 6 3 3 1 2 5 4 4 2 histogram Recovered image 38 38
Shifting histogram (4/6) l Total hiding capacity = # of peak point pixels = 7 bits. l Needs to keep a pair of pixel values on peak point and zero point for extraction and image recovery. 39 39
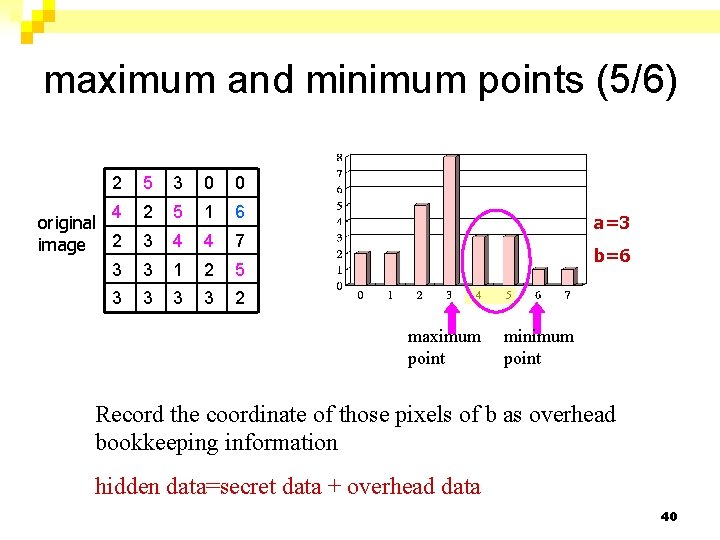
maximum and minimum points (5/6) 2 5 3 0 0 4 original image 2 3 2 5 1 6 3 4 4 7 3 1 2 5 3 3 2 a=3 b=6 maximum point minimum point Record the coordinate of those pixels of b as overhead bookkeeping information hidden data=secret data + overhead data 40
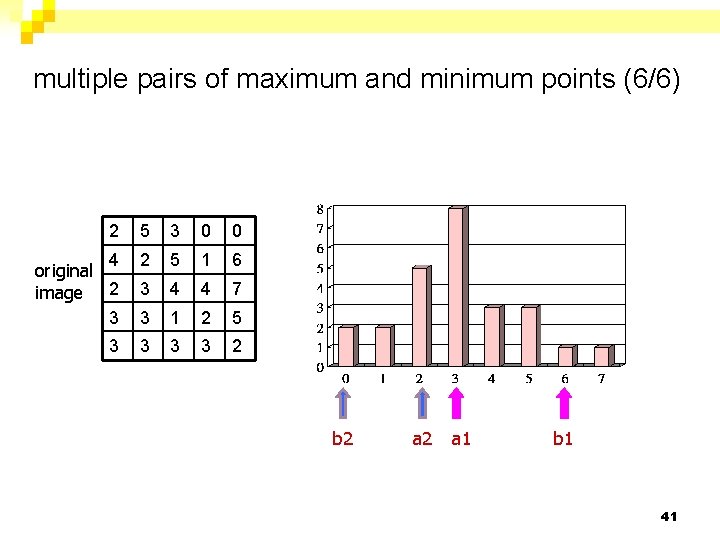
multiple pairs of maximum and minimum points (6/6) 2 5 3 0 0 4 original image 2 3 2 5 1 6 3 4 4 7 3 1 2 5 3 3 2 b 2 a 1 b 1 41
- Slides: 41