Lossless Data Hiding Based on Histogram Modification for
多媒體網路安全實驗室 Lossless Data Hiding Based on Histogram Modification for Image Authentication Source: IEEE/IFIP International Conference on Embedded and Ubiquitous Computing, EUC, 2008, Vol. 1, pp. 506 – 511. Authors: Chin-Chen Chang, Wei-Liang Tai, and Kuo-Nan Chen Speaker: Cheng Hsu Date: 2011/06/02
多媒體網路安全實驗室 Outline 1. 2. 3. 4. 5. Introduction Related work Proposed scheme Experimental results Conclusions 2
多媒體網路安全實驗室 1. Introduction v. In this paper, they present a lossless data hiding technique based on histogram modification for image authentication. v. Performance comparisons with other existing lossless data hiding schemes are provided to demonstrate the superiority of the proposed scheme. 3
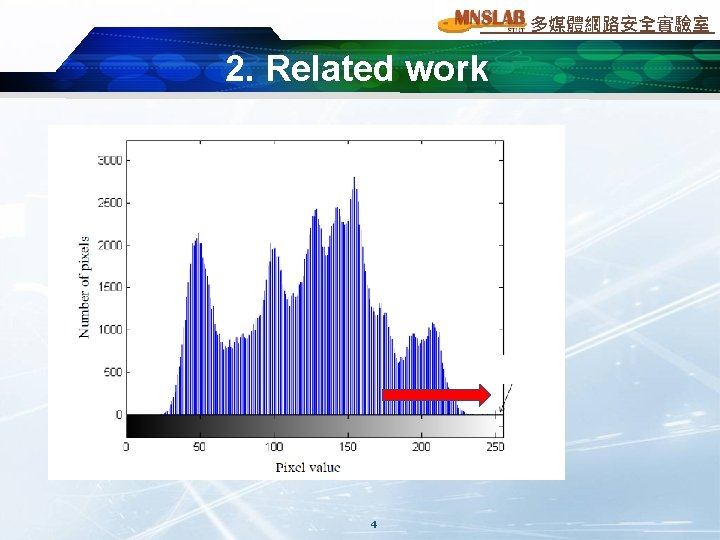
多媒體網路安全實驗室 2. Related work P+1, Z-1 Shift right 1 Embed 1 154+1 Embed 0 154+0 4
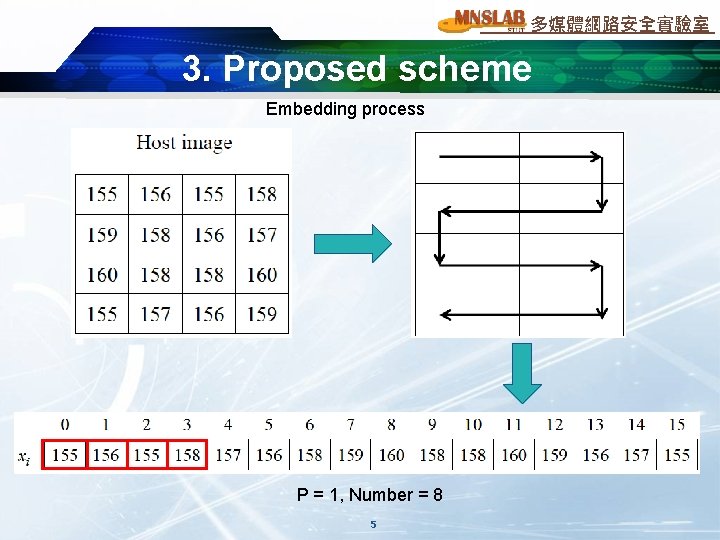
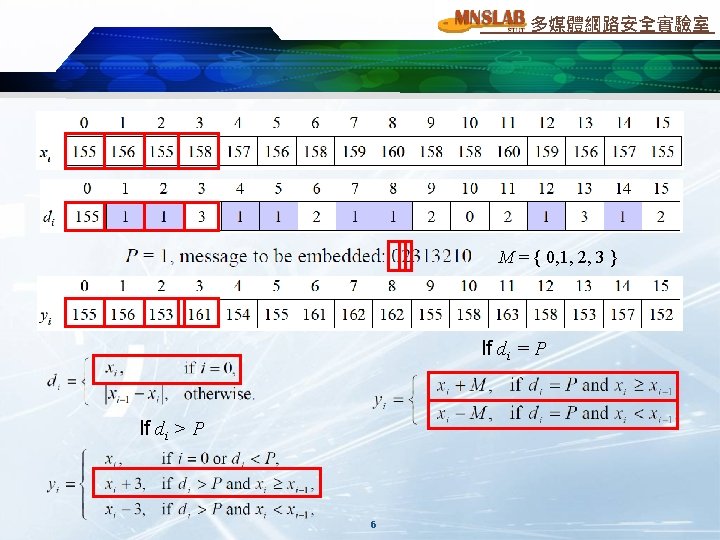
多媒體網路安全實驗室 3. Proposed scheme Embedding process P = 1, Number = 8 5
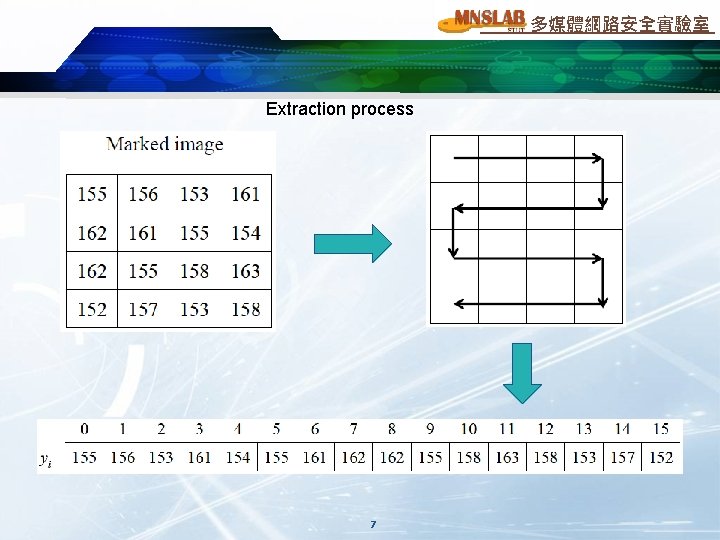
多媒體網路安全實驗室 Extraction process 7
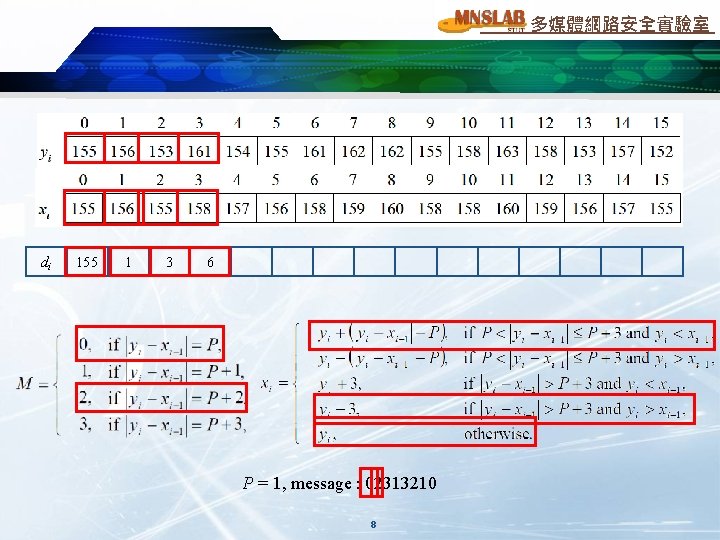
多媒體網路安全實驗室 di 155 1 3 6 P = 1, message : 02313210 8
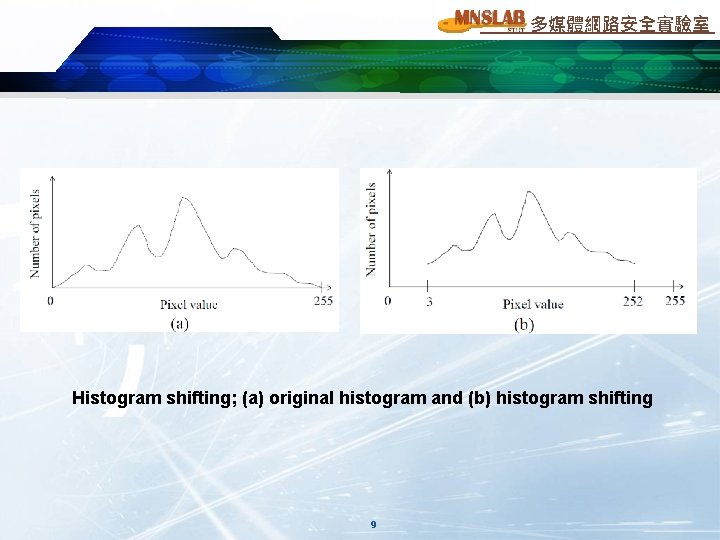
多媒體網路安全實驗室 Histogram shifting; (a) original histogram and (b) histogram shifting 9
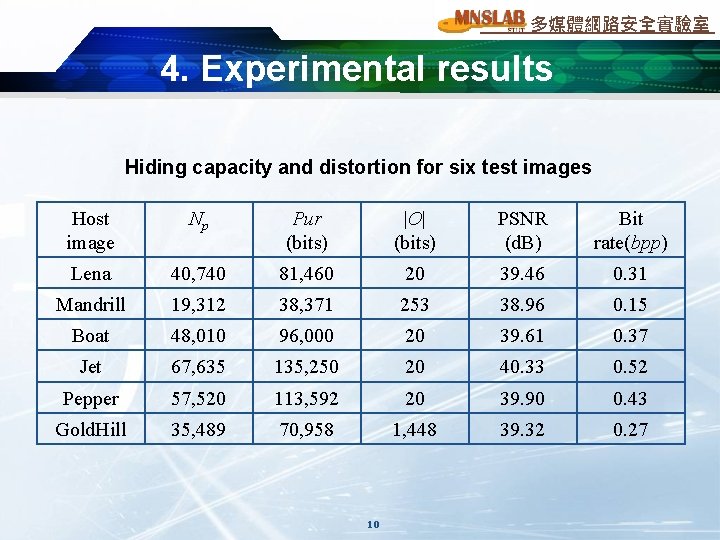
多媒體網路安全實驗室 4. Experimental results Hiding capacity and distortion for six test images Host image Np Pur (bits) |O| (bits) PSNR (d. B) Bit rate(bpp) Lena 40, 740 81, 460 20 39. 46 0. 31 Mandrill 19, 312 38, 371 253 38. 96 0. 15 Boat 48, 010 96, 000 20 39. 61 0. 37 Jet 67, 635 135, 250 20 40. 33 0. 52 Pepper 57, 520 113, 592 20 39. 90 0. 43 Gold. Hill 35, 489 70, 958 1, 448 39. 32 0. 27 10
![多媒體網路安全實驗室 Performance comparison for the “Lena” image with existing reversible schemes [5 -7] based 多媒體網路安全實驗室 Performance comparison for the “Lena” image with existing reversible schemes [5 -7] based](http://slidetodoc.com/presentation_image_h2/6526ace4d1968e942ee8bb34dc8b81aa/image-11.jpg)
多媒體網路安全實驗室 Performance comparison for the “Lena” image with existing reversible schemes [5 -7] based on histogram modification 11
多媒體網路安全實驗室 5. Conclusions v. They present an efficient extension of the histogram modification technique by considering the difference between adjacent pixels instead of simple pixel value. v. This scheme can be easily modified for compressed image formats, such as JPEG, MPEG, and JPEG 2000. 12
- Slides: 13